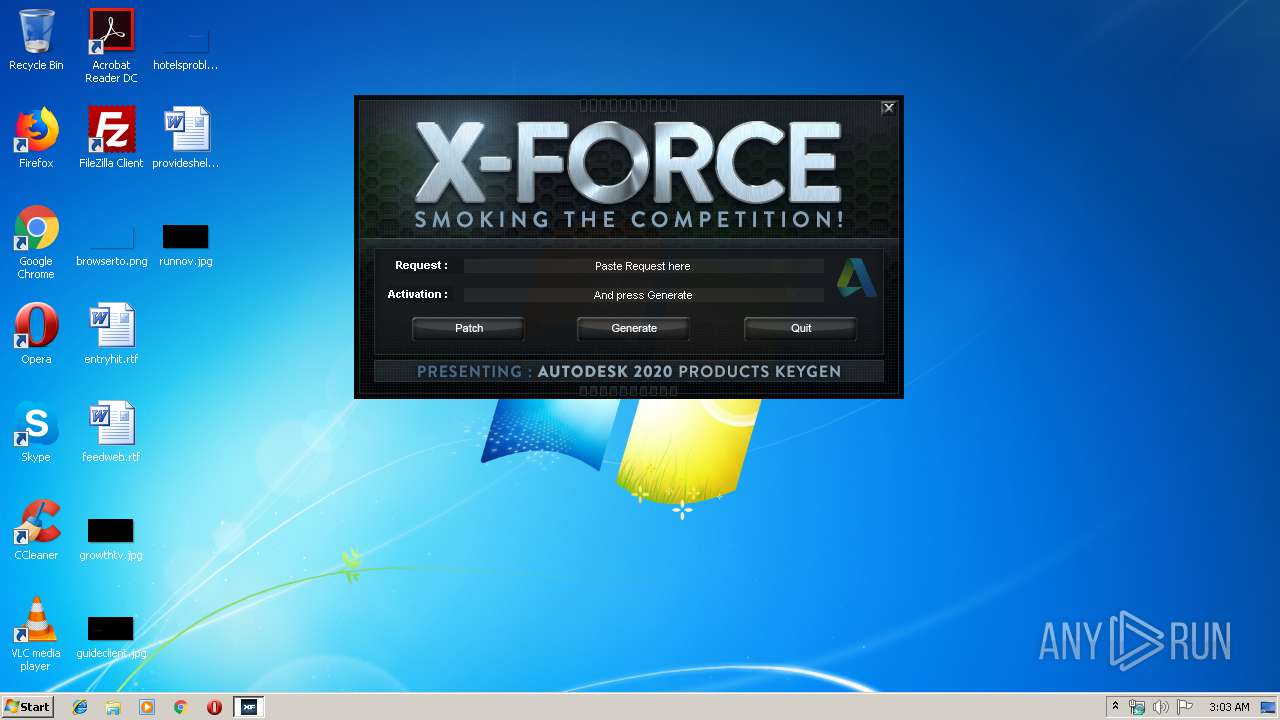
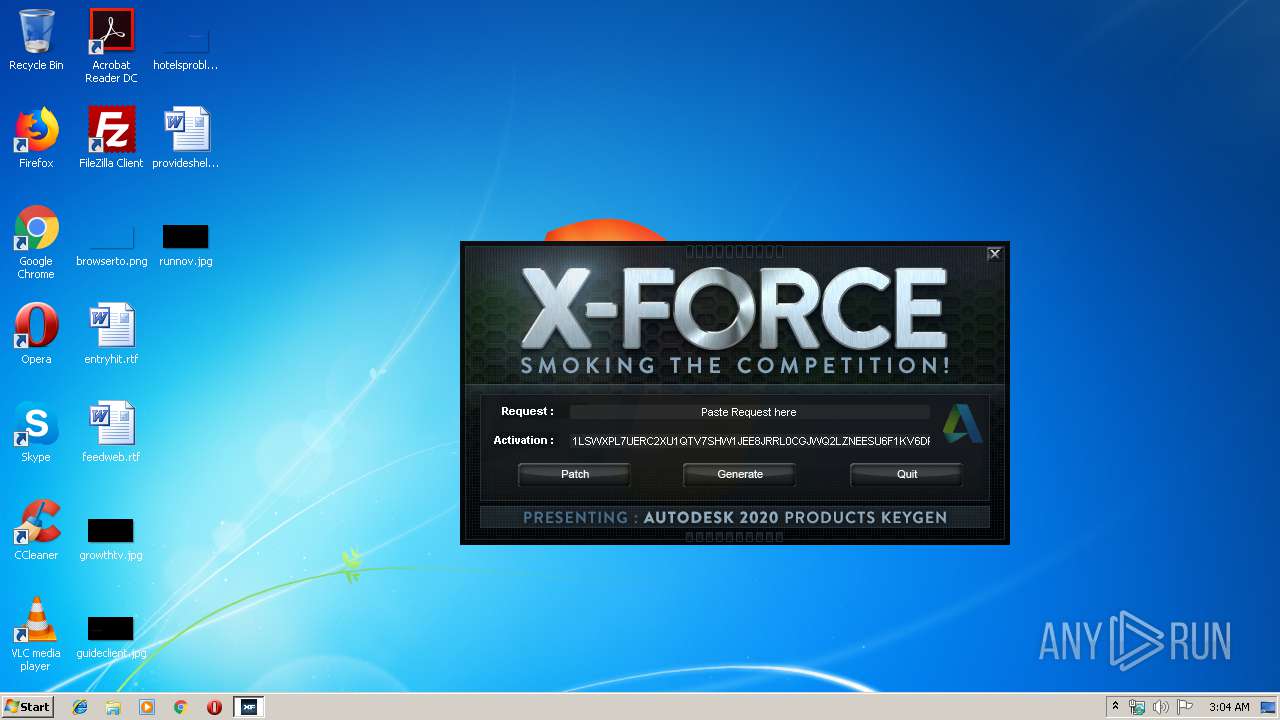
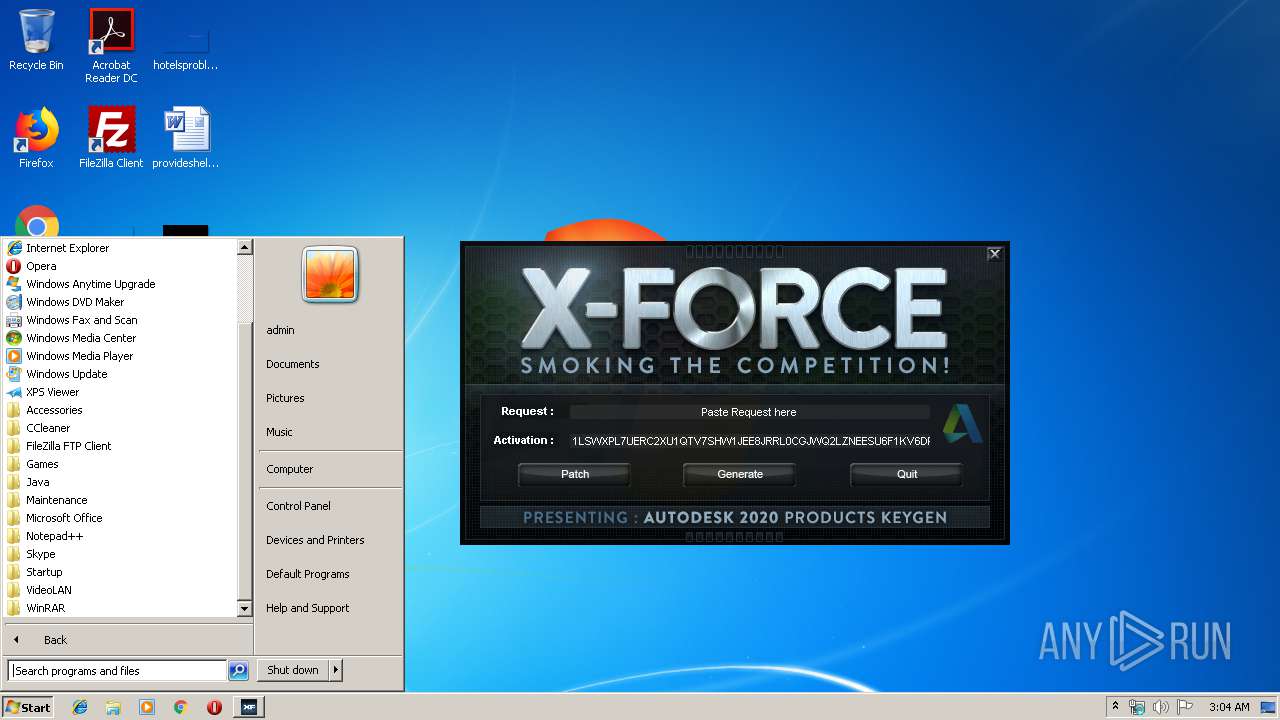
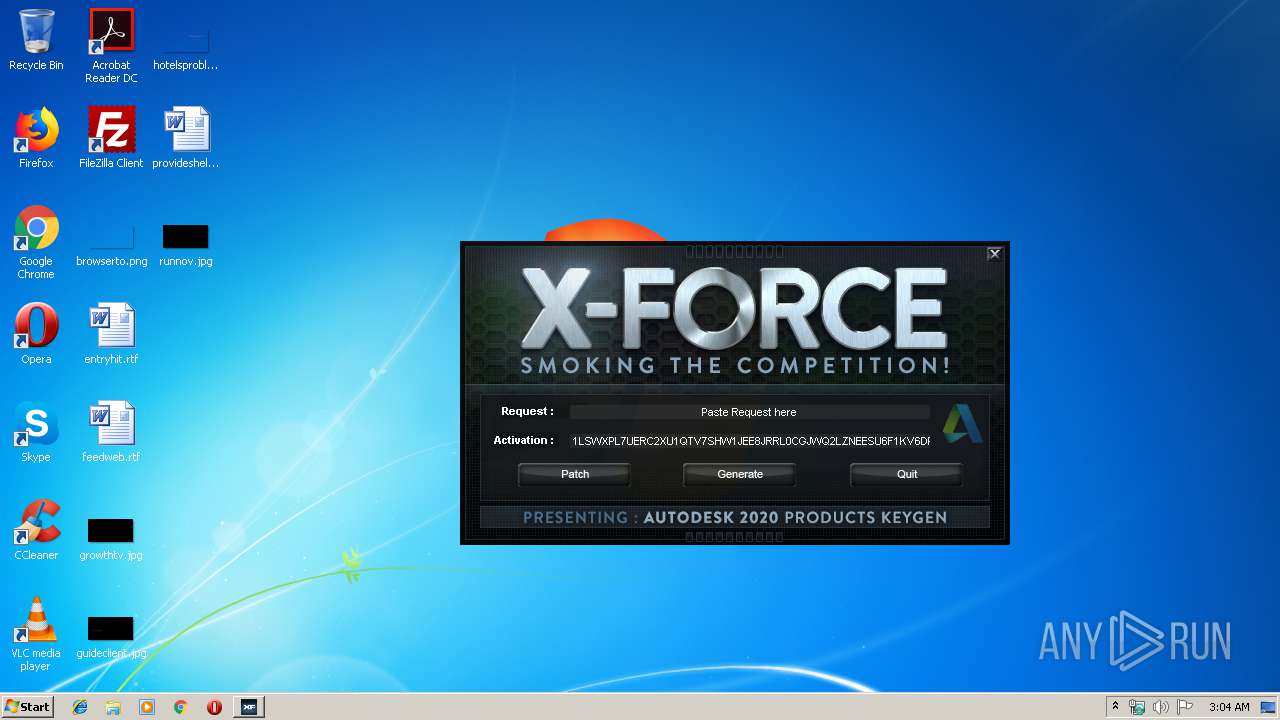
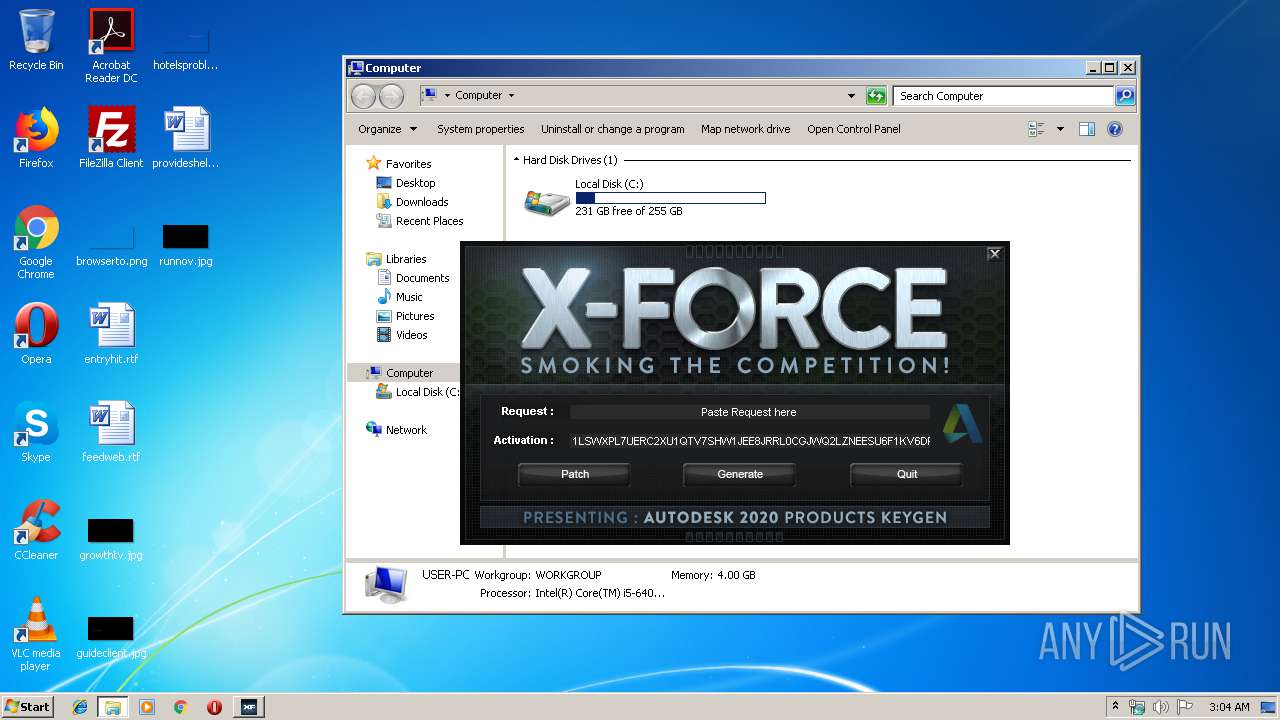
| File name: | xf-adesk20_v2.exe |
| Full analysis: | https://app.any.run/tasks/aaec3a87-b104-4543-8db1-79300b817e73 |
| Verdict: | No threats detected |
| Analysis date: | August 23, 2019, 02:03:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 45051225E4E19832BDAB5C82F2B4ECCB |
| SHA1: | 0B8DB6591161E5D00B2EF521DD062BF59AC49D63 |
| SHA256: | 586612D325F9D2D219DC0DFAA8CCDC38F73B13BCCAF1157CB191580DECEA3539 |
| SSDEEP: | 12288:R4sWe/ZY0q9HV1+TgcB0UasIlXQCkpkHTrlpJ9fUvu4vSoS:RVWuYLNODOjNg0TvV+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:30 22:11:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 561152 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 1728512 |
| EntryPoint: | 0x22f020 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2019 21:11:41 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Mar-2019 21:11:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001A6000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001A7000 | 0x00089000 | 0x00088E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99913 |
.rsrc | 0x00230000 | 0x00003000 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.85871 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.93643 | 8500 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 7.18212 | 276 | UNKNOWN | UNKNOWN | RT_DIALOG |
102 | 7.9989 | 168874 | UNKNOWN | UNKNOWN | RT_BITMAP |
103 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
105 | 7.94699 | 3848 | UNKNOWN | UNKNOWN | RT_BITMAP |
106 | 7.94395 | 3846 | UNKNOWN | UNKNOWN | RT_BITMAP |
107 | 7.95245 | 3848 | UNKNOWN | UNKNOWN | RT_BITMAP |
108 | 7.95479 | 3846 | UNKNOWN | UNKNOWN | RT_BITMAP |
111 | 7.69449 | 750 | UNKNOWN | UNKNOWN | RT_BITMAP |
112 | 7.76009 | 854 | UNKNOWN | UNKNOWN | RT_BITMAP |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
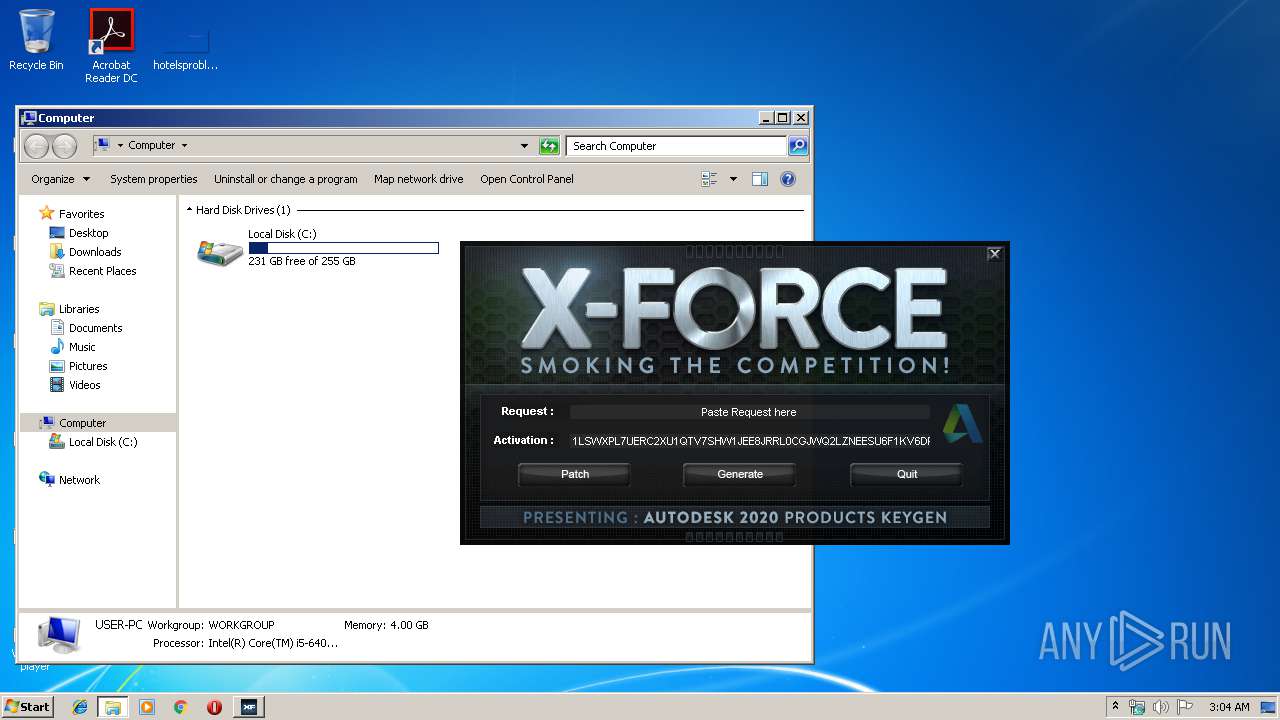
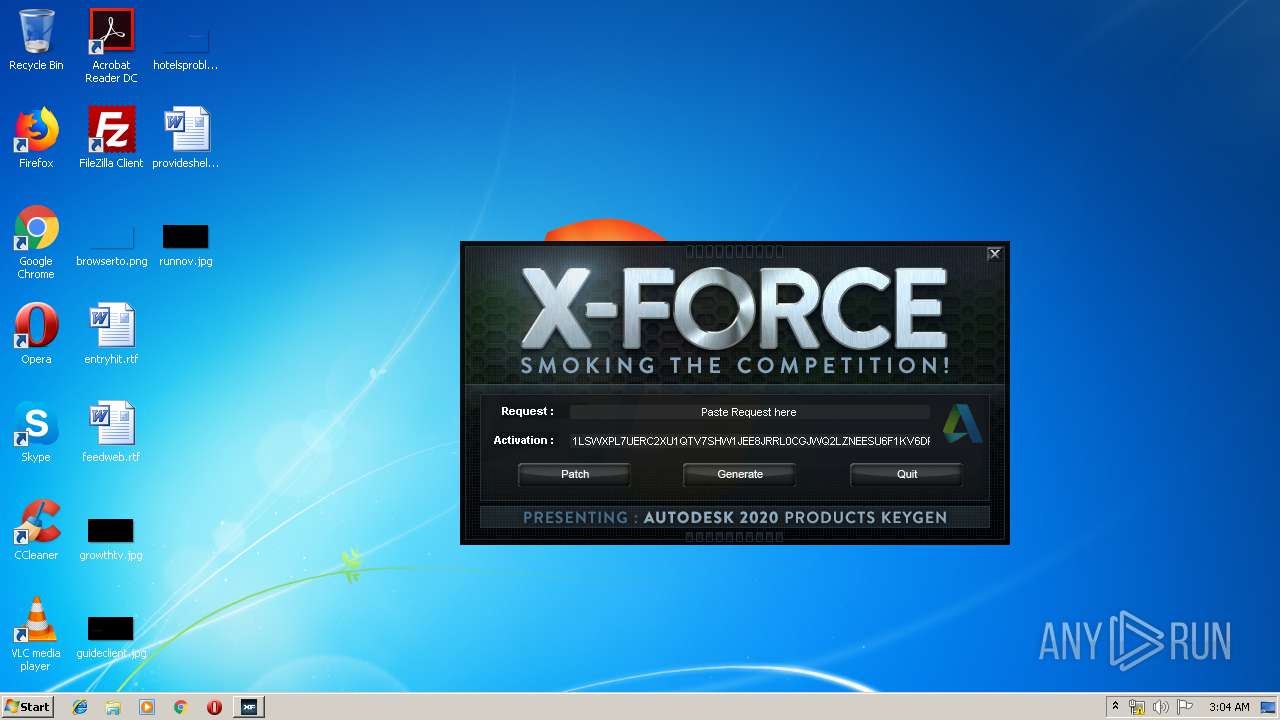
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
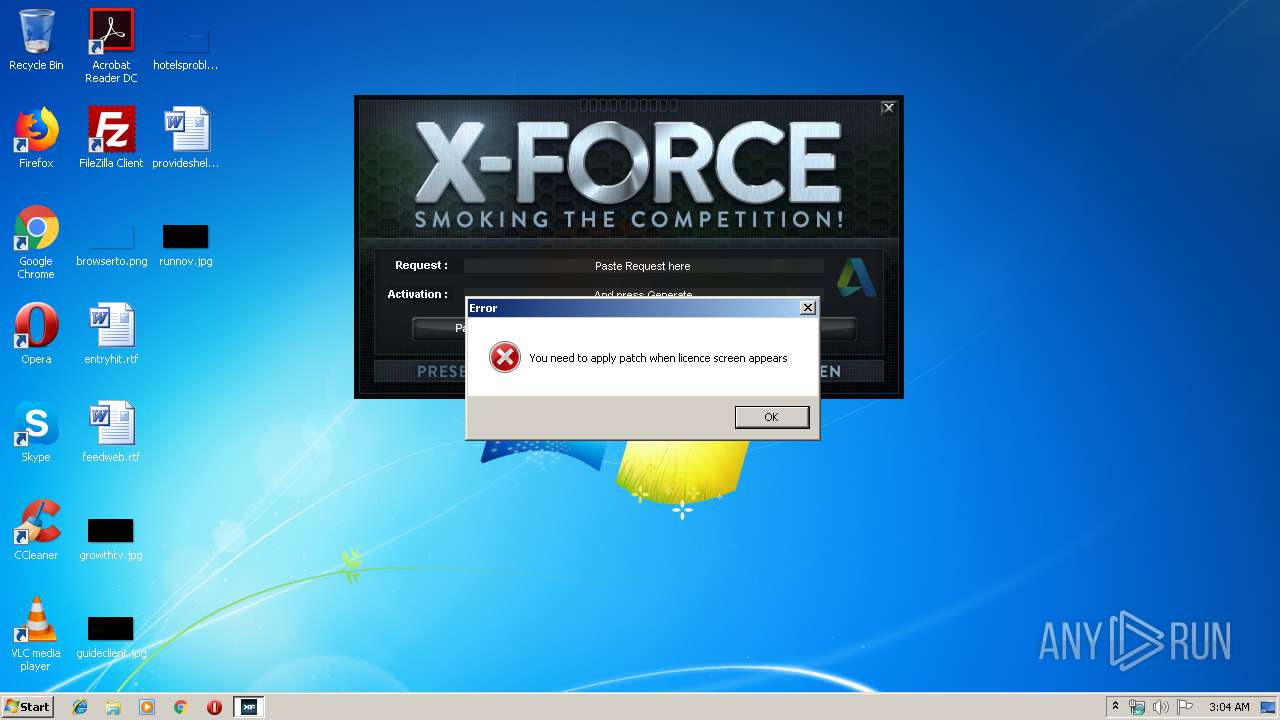
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3676 | "C:\Users\admin\AppData\Local\Temp\xf-adesk20_v2.exe" | C:\Users\admin\AppData\Local\Temp\xf-adesk20_v2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
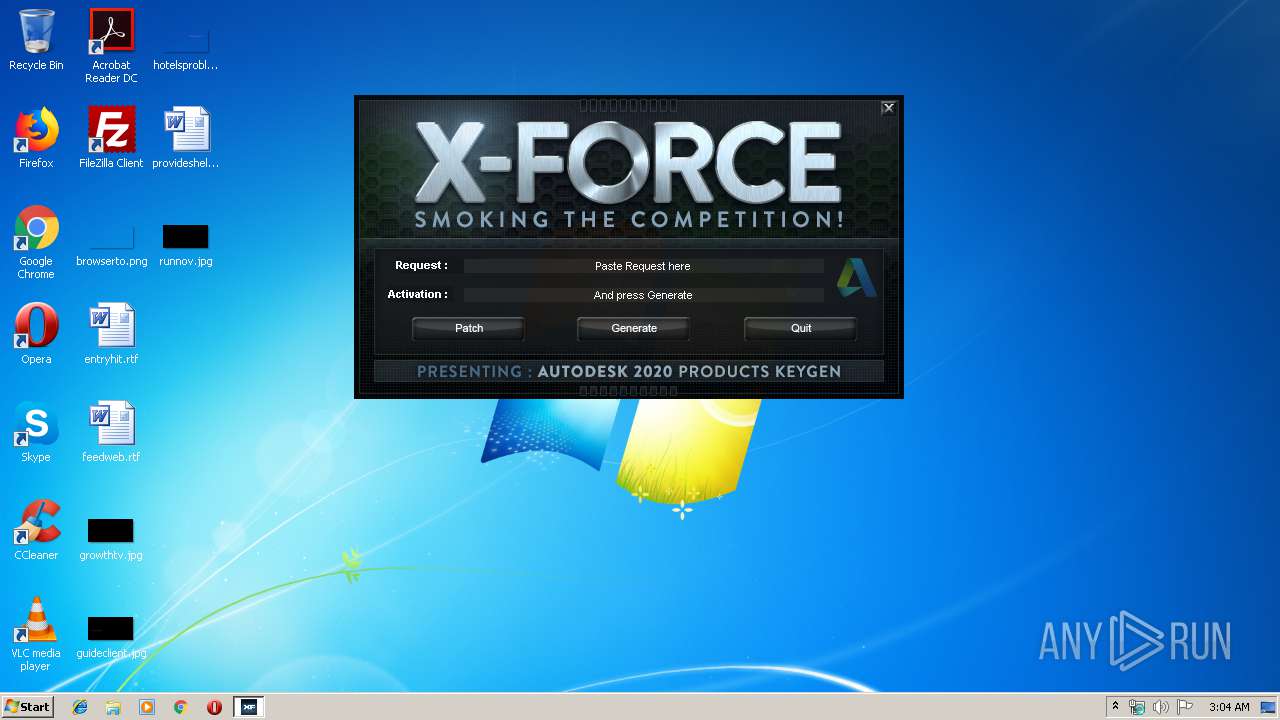
Total events
12
Read events
12
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
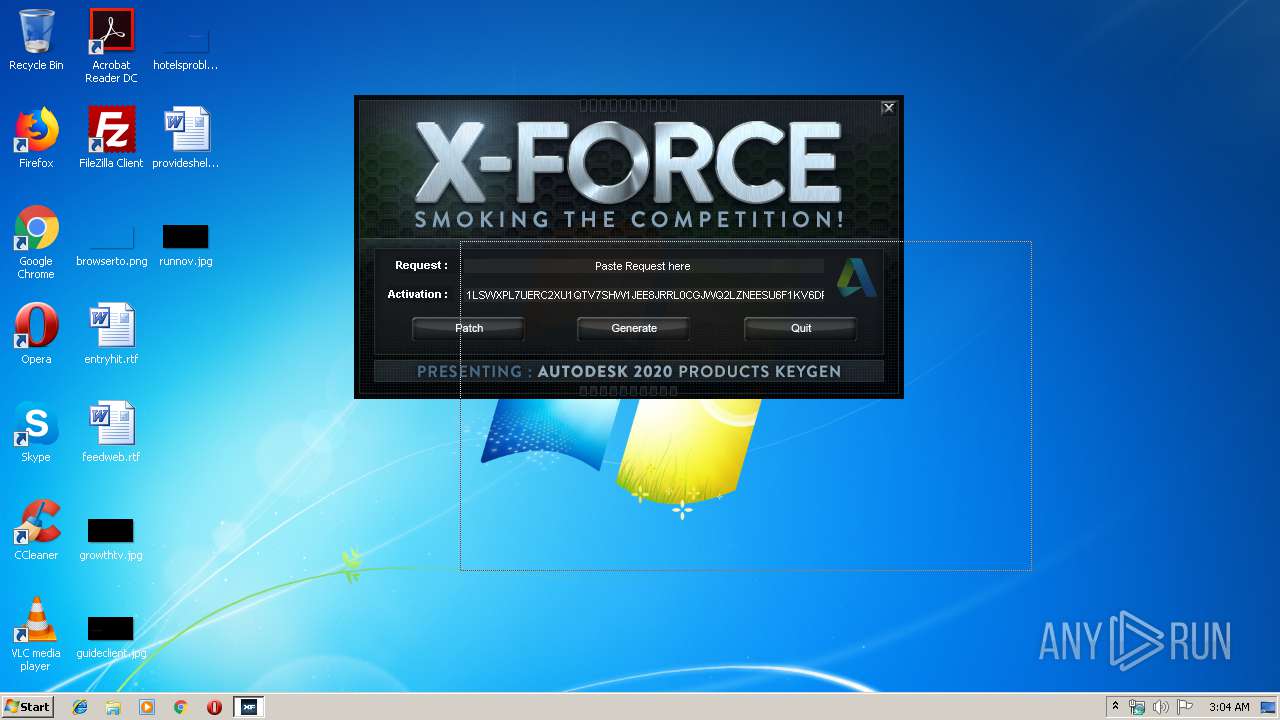
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report