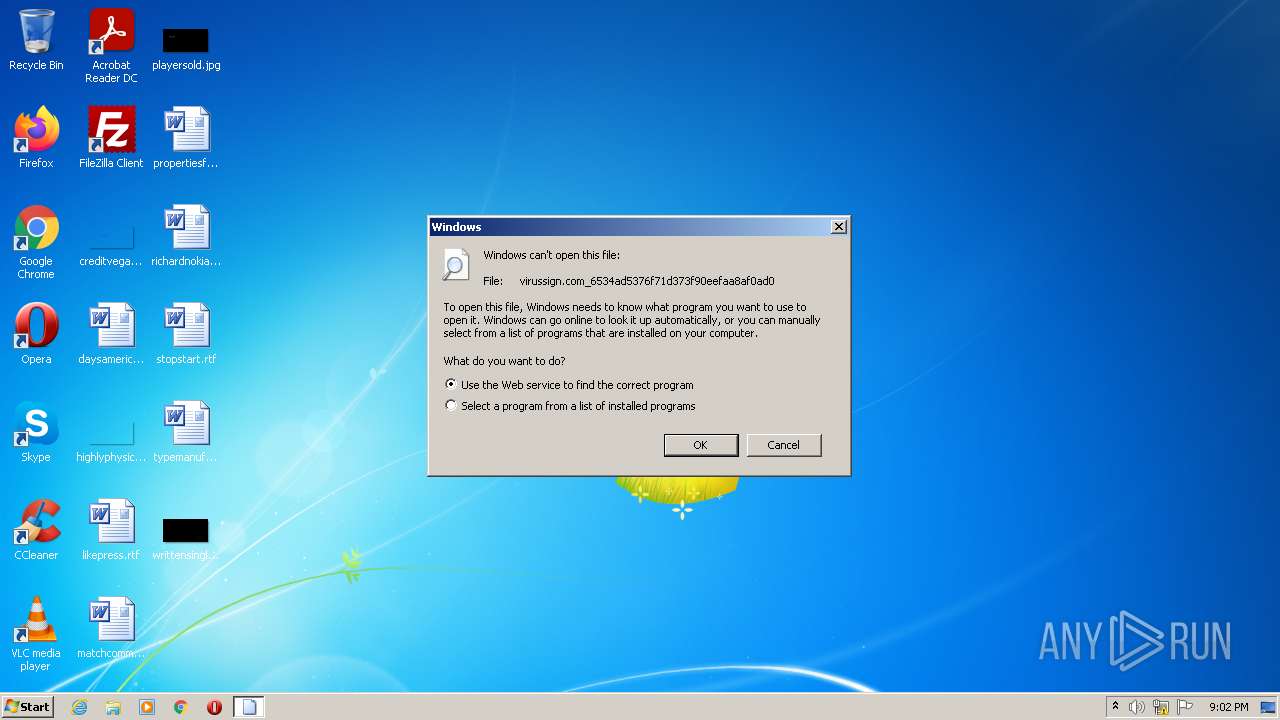
| File name: | virussign.com_6534ad5376f71d373f90eefaa8af0ad0 |
| Full analysis: | https://app.any.run/tasks/f5a791c5-a43e-41d5-9881-0601c5758e67 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2022, 20:02:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6534AD5376F71D373F90EEFAA8AF0AD0 |
| SHA1: | AAFAD089388AEC06C3E0541DD1449EDEF8DED646 |
| SHA256: | 585D5D965E8C88226504BF222617EC6AB0641087D38438F603DCE5102E87FD58 |
| SSDEEP: | 12288:UCVjn0fYQWFjDLUC5MKx4ZnF69Xt1/0HbKhr4b:UCV2YjPIKx46Xz/MbKhr6 |
MALICIOUS
Changes the autorun value in the registry
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
- GaIgEEkI.exe (PID: 1236)
Drops executable file immediately after starts
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
Application was dropped or rewritten from another process
- GaIgEEkI.exe (PID: 1236)
- TosAYMEI.exe (PID: 3212)
Modifies files in Chrome extension folder
- TosAYMEI.exe (PID: 3212)
SUSPICIOUS
Reads the computer name
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
- GaIgEEkI.exe (PID: 1236)
- cscript.exe (PID: 2376)
- cmd.exe (PID: 3612)
Checks supported languages
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
- GaIgEEkI.exe (PID: 1236)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 1404)
- cscript.exe (PID: 2376)
Creates files in the program directory
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
Executable content was dropped or overwritten
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
Uses REG.EXE to modify Windows registry
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
Starts CMD.EXE for commands execution
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
Drops a file with a compile date too recent
- virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe (PID: 120)
- TosAYMEI.exe (PID: 3212)
Executes scripts
- cmd.exe (PID: 1404)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3612)
INFO
Checks supported languages
- reg.exe (PID: 1272)
- reg.exe (PID: 3288)
- reg.exe (PID: 1032)
- rundll32.exe (PID: 2056)
Checks Windows Trust Settings
- cscript.exe (PID: 2376)
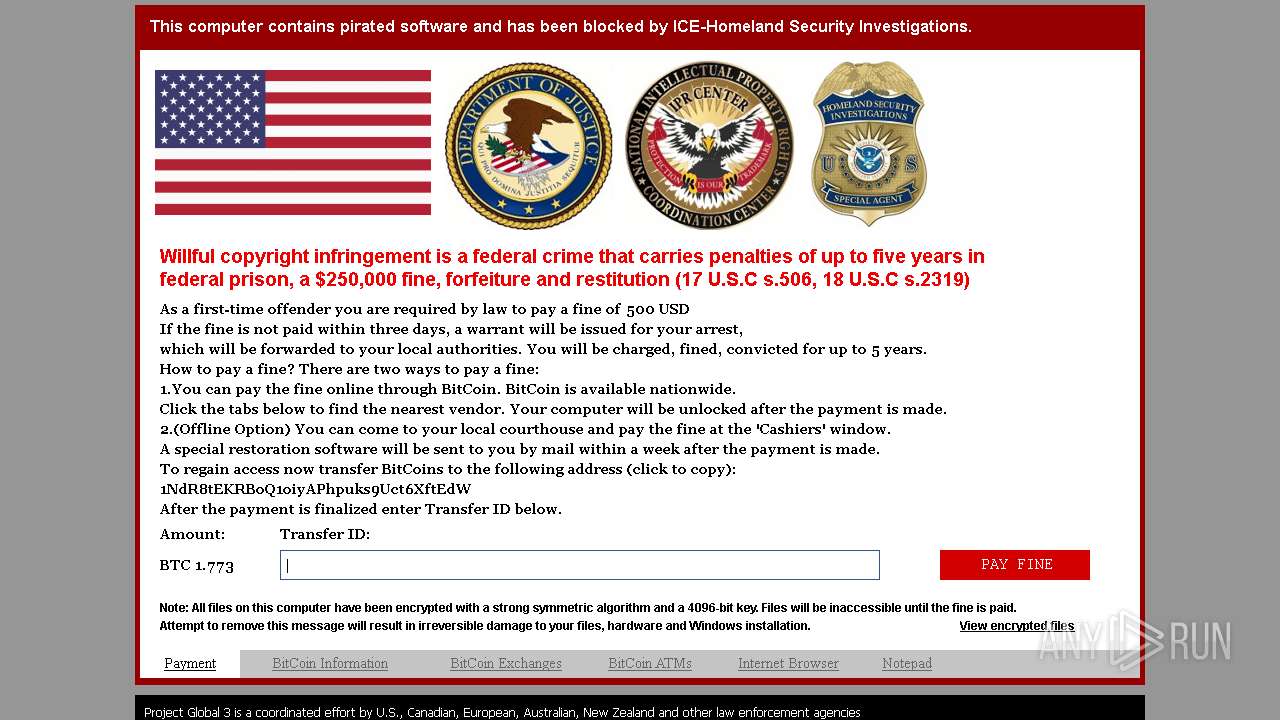
Dropped object may contain Bitcoin addresses
- TosAYMEI.exe (PID: 3212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 5632 |
| CodeSize: | 445952 |
| LinkerVersion: | 5.12 |
| PEType: | PE32 |
| TimeStamp: | 2015:01:06 01:36:08+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jan-2015 00:36:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 06-Jan-2015 00:36:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006D000 | 0x0006CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95263 |
.rdata | 0x0006E000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.1246 |
.data | 0x0006F000 | 0x00000084 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.38707 |
.rsrc | 0x00070000 | 0x0000115C | 0x00001200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_LOCKED, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.50104 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.94375 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
48
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe" | C:\Users\admin\AppData\Local\Temp\virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1032 | reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /d 0 /t REG_DWORD /f | C:\Windows\system32\reg.exe | — | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\ProgramData\bmoYUQYo\GaIgEEkI.exe" | C:\ProgramData\bmoYUQYo\GaIgEEkI.exe | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1272 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v HideFileExt /t REG_DWORD /d 1 | C:\Windows\system32\reg.exe | — | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\REwowUQk.bat" "C:\Users\admin\AppData\Local\Temp\virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe"" | C:\Windows\system32\cmd.exe | — | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2056 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\virussign.com_6534ad5376f71d373f90eefaa8af0ad0 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | cscript C:\Users\admin\AppData\Local\Temp/file.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\ksIsgQoE\TosAYMEI.exe" | C:\Users\admin\ksIsgQoE\TosAYMEI.exe | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3288 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v Hidden /t REG_DWORD /d 2 | C:\Windows\system32\reg.exe | — | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3612 | C:\Windows\system32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\virussign.com_6534ad5376f71d373f90eefaa8af0ad0" | C:\Windows\system32\cmd.exe | — | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 280
Read events
2 274
Write events
6
Delete events
0
Modification events
| (PID) Process: | (120) virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TosAYMEI.exe |
Value: C:\Users\admin\ksIsgQoE\TosAYMEI.exe | |||
| (PID) Process: | (120) virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GaIgEEkI.exe |
Value: C:\ProgramData\bmoYUQYo\GaIgEEkI.exe | |||
| (PID) Process: | (3212) TosAYMEI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TosAYMEI.exe |
Value: C:\Users\admin\ksIsgQoE\TosAYMEI.exe | |||
| (PID) Process: | (1272) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | HideFileExt |
Value: 1 | |||
| (PID) Process: | (3288) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 2 | |||
| (PID) Process: | (1236) GaIgEEkI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GaIgEEkI.exe |
Value: C:\ProgramData\bmoYUQYo\GaIgEEkI.exe | |||
Executable files
879
Suspicious files
0
Text files
248
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\Temp\ckoS.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\VirtualStore\RCXAED4.tmp | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\Temp\OsEi.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\VirtualStore\RCXAFF0.tmp | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\DW20.EXE.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\Temp\sIQy.exe | executable | |
MD5:— | SHA256:— | |||
| 120 | virussign.com_6534ad5376f71d373f90eefaa8af0ad0.exe | C:\Users\admin\ksIsgQoE\TosAYMEI.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | TosAYMEI.exe | C:\Users\admin\AppData\Local\VirtualStore\RCXAF62.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3212 | TosAYMEI.exe | GET | 301 | 142.250.186.142:80 | http://google.com/ | US | html | 219 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | TosAYMEI.exe | 142.250.185.142:80 | — | Google Inc. | US | whitelisted |
1236 | GaIgEEkI.exe | 142.250.185.142:80 | — | Google Inc. | US | whitelisted |
3212 | TosAYMEI.exe | 142.250.186.142:80 | google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3212 | TosAYMEI.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |