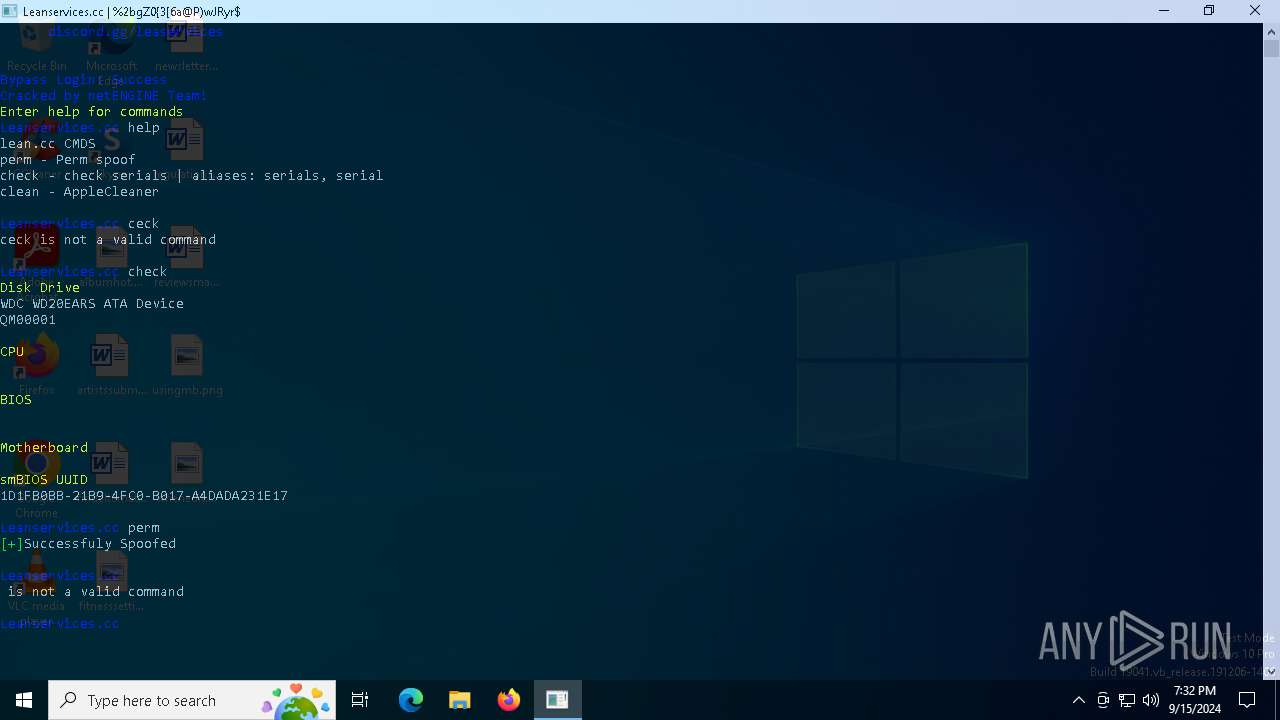
| File name: | Cracked Loader.exe |
| Full analysis: | https://app.any.run/tasks/379da5bc-75cf-4f3b-b9bc-96b915690265 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2024, 19:31:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 587A806EC4C7A1FD79E3AC46C782570A |
| SHA1: | 8B8C1FBEAC5425A033F54B5C435DB2A2A02A0922 |
| SHA256: | 584665CF081767A6BCB07636FBB70CFF7FA960DA5C5AC9C997C5C8D925D8CDB4 |
| SSDEEP: | 1536:eMfqP542p5b4hzB+wFFimSvbrf+/5BfIyKvT8kceU:FS542Tb4hzB+wFFi/XoBfIy4/zU |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 2224)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 4292)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 376)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 5148)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 5492)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 7012)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 368)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 3328)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 1060)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 232)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 5944)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 892)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 4104)
Starts NET.EXE for service management
- net.exe (PID: 5900)
- cmd.exe (PID: 5888)
- net.exe (PID: 6776)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 2224)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 6992)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 5516)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 448)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 4392)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 6224)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 5940)
- cmd.exe (PID: 4292)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 5152)
- cmd.exe (PID: 788)
- cmd.exe (PID: 644)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 5388)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 4404)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 376)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 4392)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 2624)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 6196)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 5612)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 788)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 6568)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 5184)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 644)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 5148)
- cmd.exe (PID: 5492)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 4404)
- cmd.exe (PID: 4644)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 4192)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 7160)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 6000)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5944)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 6420)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 7012)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 5940)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 5888)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 4160)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 5212)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 368)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 2464)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 5144)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 3328)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 6680)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 5880)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 5184)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 752)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 5708)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 6728)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 1060)
- cmd.exe (PID: 4364)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 5612)
- cmd.exe (PID: 780)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 888)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6180)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 6196)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 6484)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 6312)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 788)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 736)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 1372)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 6720)
- cmd.exe (PID: 1156)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 6728)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 232)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 3328)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 5944)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 7028)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 5516)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 740)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 888)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6968)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 232)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 892)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 4104)
- cmd.exe (PID: 6968)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 6180)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 6992)
- cmd.exe (PID: 2608)
- cmd.exe (PID: 4444)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 448)
- cmd.exe (PID: 6224)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 788)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 5152)
- cmd.exe (PID: 5940)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 5388)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 4392)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 5612)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 6568)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 4644)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 4404)
- cmd.exe (PID: 4192)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 6000)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 5944)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 5888)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 4160)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 5212)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 2464)
- cmd.exe (PID: 5144)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 2016)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 6680)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 5880)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 5184)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 5708)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 6728)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 4364)
- cmd.exe (PID: 888)
- cmd.exe (PID: 6180)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 6196)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 6312)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 788)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 1156)
- cmd.exe (PID: 6728)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 3328)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 7028)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 5516)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 740)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 6968)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 6968)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 6992)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 3268)
Starts CMD.EXE for commands execution
- Cracked Loader.exe (PID: 5244)
Drops a system driver (possible attempt to evade defenses)
- Cracked Loader.exe (PID: 5244)
Executable content was dropped or overwritten
- Cracked Loader.exe (PID: 5244)
INFO
Checks supported languages
- Cracked Loader.exe (PID: 5244)
Disables trace logs
- Cracked Loader.exe (PID: 5244)
Reads the machine GUID from the registry
- Cracked Loader.exe (PID: 5244)
Reads the computer name
- Cracked Loader.exe (PID: 5244)
Checks proxy server information
- Cracked Loader.exe (PID: 5244)
Reads the software policy settings
- Cracked Loader.exe (PID: 5244)
Themida protector has been detected
- Cracked Loader.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:19 08:26:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 83968 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1673e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Malaia.cc |
| FileVersion: | 1.0.0.0 |
| InternalName: | Hollow.cc.exe |
| LegalCopyright: | Copyright ©Malaia.cc 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Hollow.cc.exe |
| ProductName: | Malaia.cc |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
1 244
Monitored processes
1 122
Malicious processes
1
Suspicious processes
60
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | sc stop wireshark | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | taskkill /f /im Ida64.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 232 | "cmd.exe" /c taskkill /f /im HTTPDebuggerUI.exe >nul 2>&1 | C:\Windows\SysWOW64\cmd.exe | — | Cracked Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 232 | "cmd.exe" /c sc stop wireshark >nul 2>&1 | C:\Windows\SysWOW64\cmd.exe | — | Cracked Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "cmd.exe" /c taskkill /f /im HTTPDebuggerSvc.exe >nul 2>&1 | C:\Windows\SysWOW64\cmd.exe | — | Cracked Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | taskkill /FI "IMAGENAME eq ollydbg*" /IM * /F /T | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
22 919
Read events
22 905
Write events
14
Delete events
0
Modification events
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5244) Cracked Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Cracked Loader_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5244 | Cracked Loader.exe | C:\Malaia.cc\AMIFLDRV64.SYS | executable | |
MD5:59EAA18CC962AA39135A7DBA3CA42415 | SHA256:2EF33B2D4DC30FE97A7273C3309C864A7901FA9ED7C2E5377AEB524539457FCD | |||
| 5244 | Cracked Loader.exe | C:\Malaia.cc\zhjers.exe | executable | |
MD5:C9E17AC0C684C93AF1FF8EDF3C50C791 | SHA256:6E7CF8A300B855E53F68CEEFFF89AEB6EFDD71CDAABD8798A206618CF2DA5DC6 | |||
| 5244 | Cracked Loader.exe | C:\Malaia.cc\dvlwwwdrv64.sys | executable | |
MD5:376A4C8AB24A1BED04CF2A78EB38177D | SHA256:DE49C0D079431740EEE0657B2F7C5845AF77399F3EB49CF7E88E26CC075C3C9A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
29
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3036 | SIHClient.exe | GET | 200 | 2.22.25.220:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3036 | SIHClient.exe | GET | 200 | 2.22.25.220:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 20.7.1.246:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4164 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
keyauth.win |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
5244 | Cracked Loader.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |