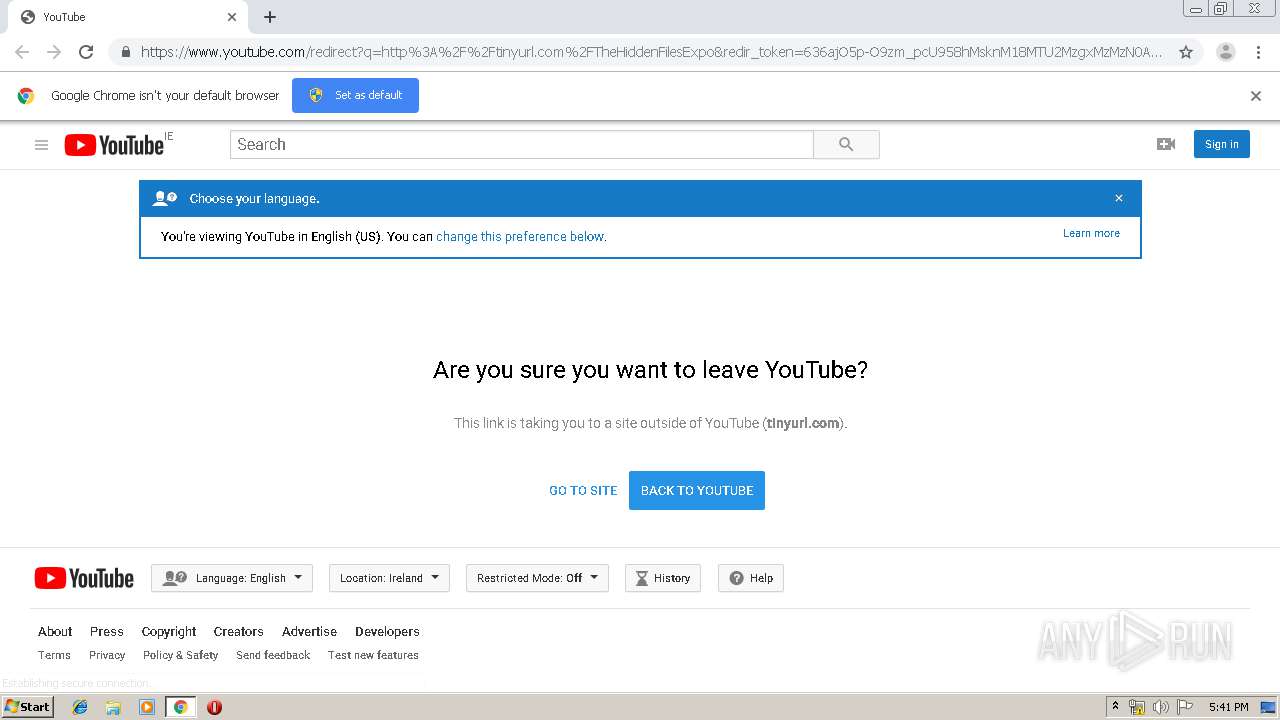
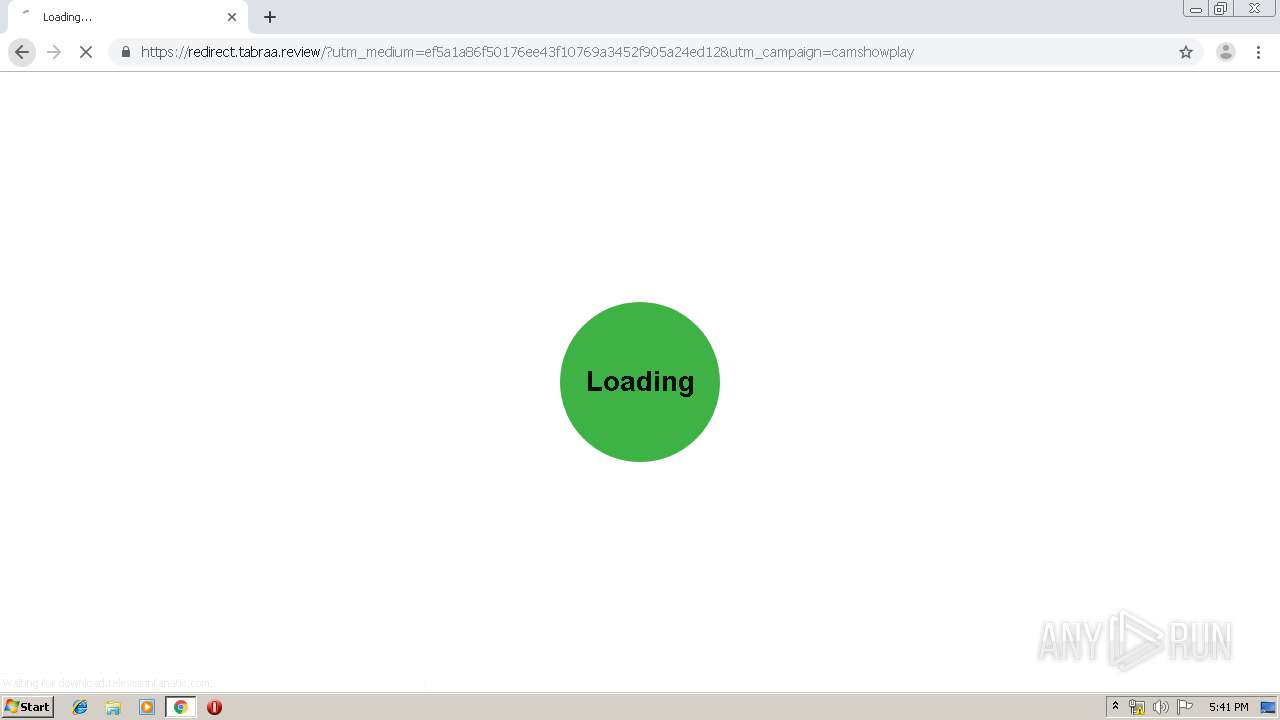
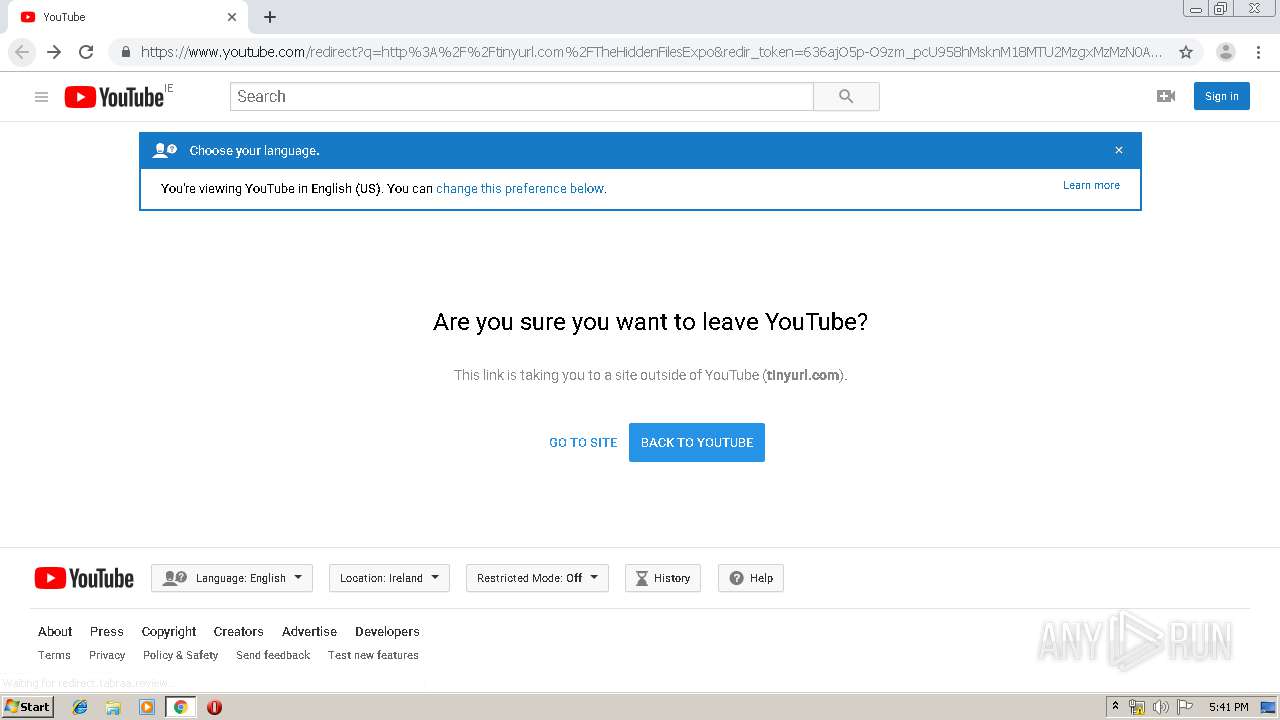
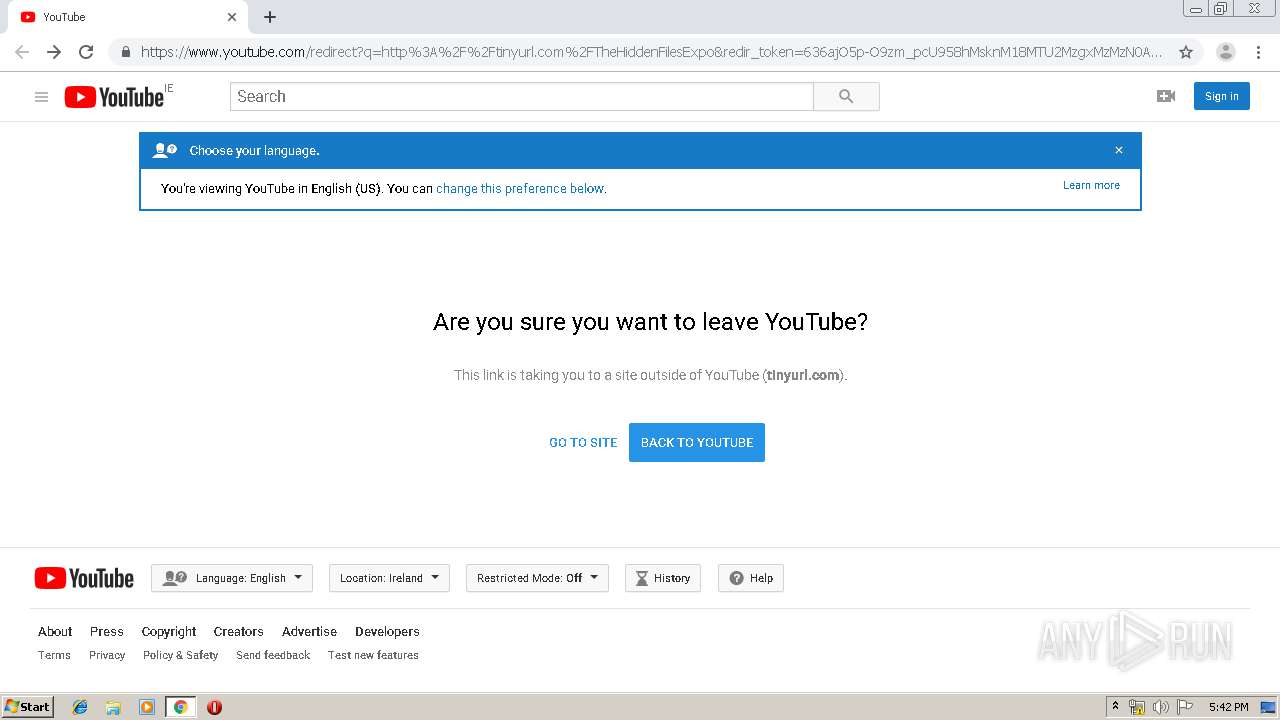
| URL: | https://www.youtube.com/redirect?q=http%3A%2F%2Ftinyurl.com%2FTheHiddenFilesExpo&redir_token=636ajO5p-O9zm_pcU958hMsknM18MTU2MzgxMzMzN0AxNTYzNzI2OTM3&event=video_description&v=GQHGRh6iUHM |
| Full analysis: | https://app.any.run/tasks/1547c452-6fbe-43a4-a04e-580c50b77db2 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2019, 16:41:04 |
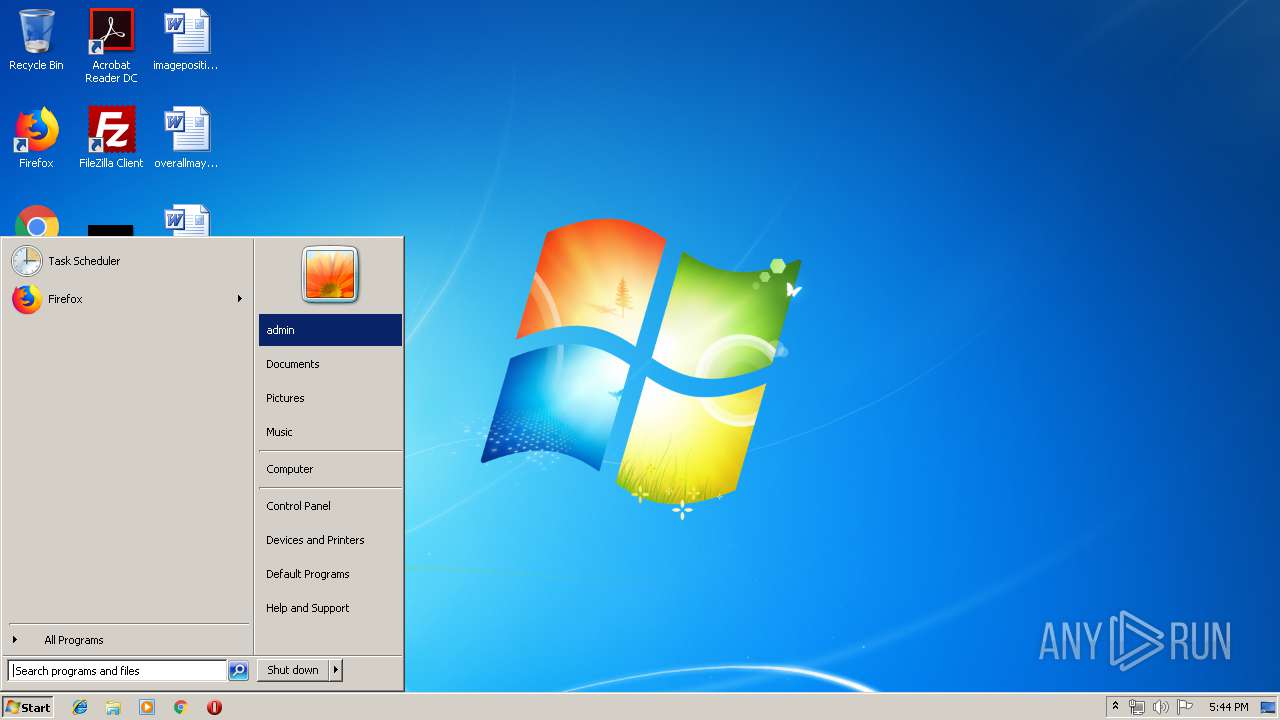
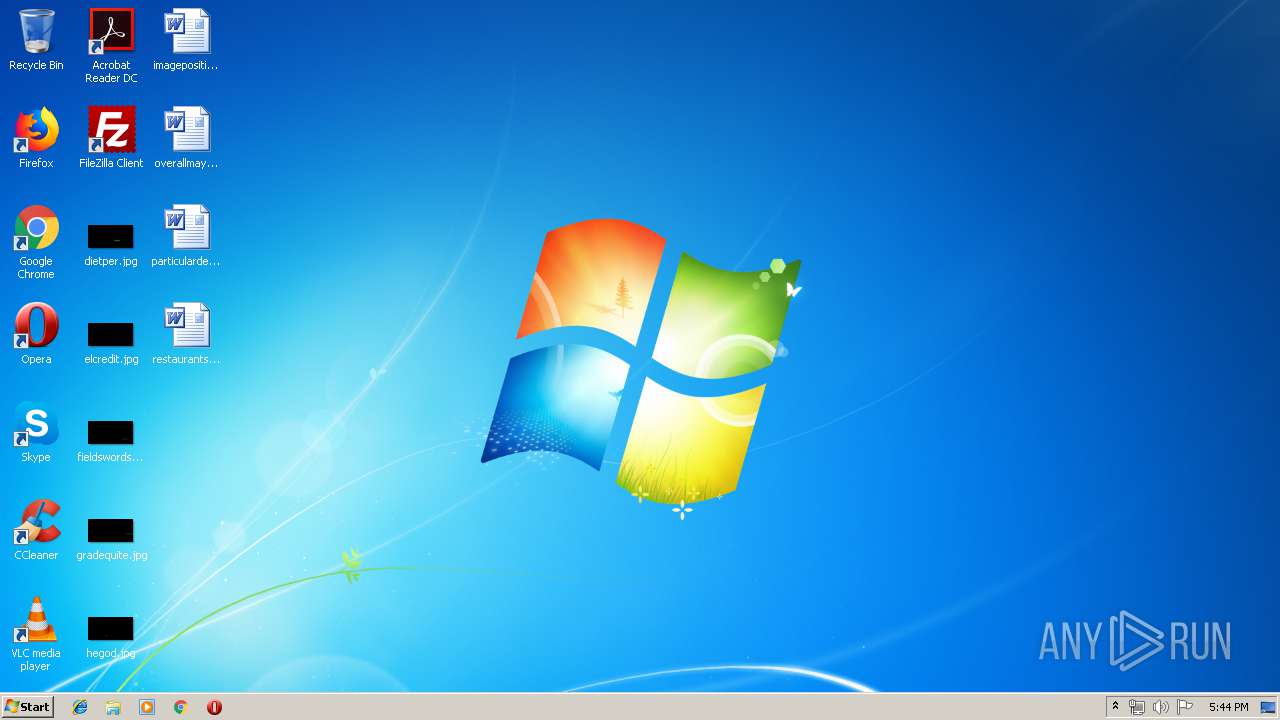
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5A476BA316A65BE892DA08F2BAEF1CD5 |
| SHA1: | E11B18C672B671FEC2479876BDA1FC5320522E38 |
| SHA256: | 583B0A3268EF4B82FD427EBDC043FF4D23925F009489AB9BD8C8DDFD759FDD25 |
| SSDEEP: | 3:N8DSLUxGTKXtWNtJsXjwcQZLdIEN24Adl6qZVqs+dNLOcUdQvofrVykwTALRYABl:2OLUxGKWdszpQ1dE4chrJWOwvofKK+RI |
MALICIOUS
No malicious indicators.SUSPICIOUS
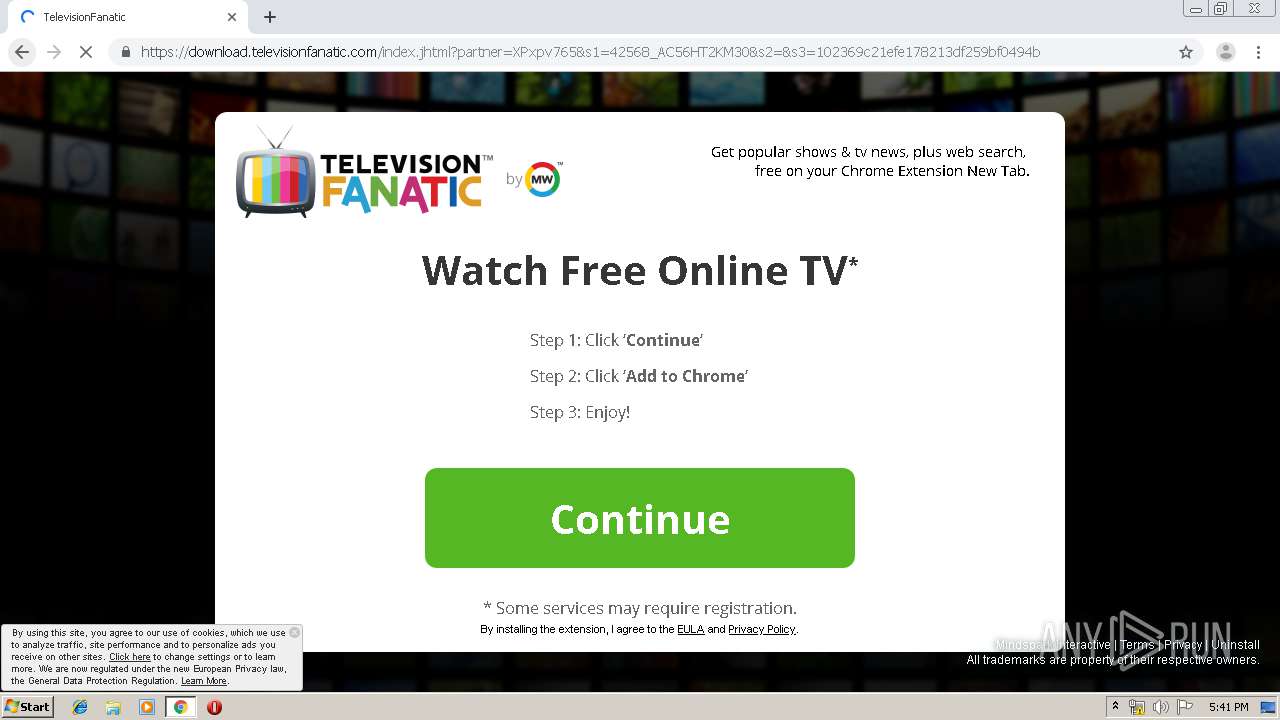
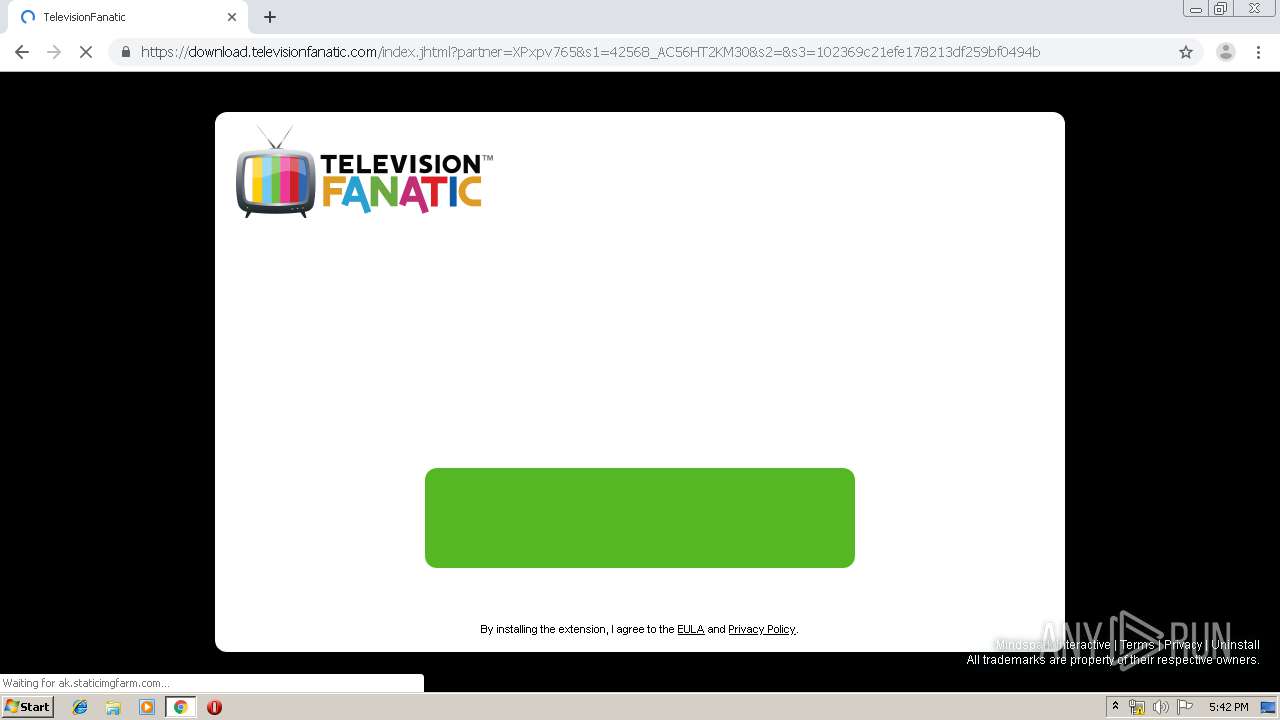
Modifies files in Chrome extension folder
- chrome.exe (PID: 3884)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3504)
Application launched itself
- chrome.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
61
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9480644356267948830 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18051690960170001629 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14263672739296677811 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2137289579284253185 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6139777146855377726 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2233924749418037634 --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7062930675842249094 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12029895531041549084 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,2814359568626462875,2177250766779393432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10289522434789694751 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e55a9d0,0x6e55a9e0,0x6e55a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
688
Read events
556
Write events
127
Delete events
5
Modification events
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3884-13208200887921875 |
Value: 259 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 572-13197843609579101 |
Value: 0 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
119
Text files
266
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f9ab2387-2e7e-4932-8728-c4670e99e7d6.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000022.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF186d7a.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF186ba5.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
342
DNS requests
63
Threats
1 238
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
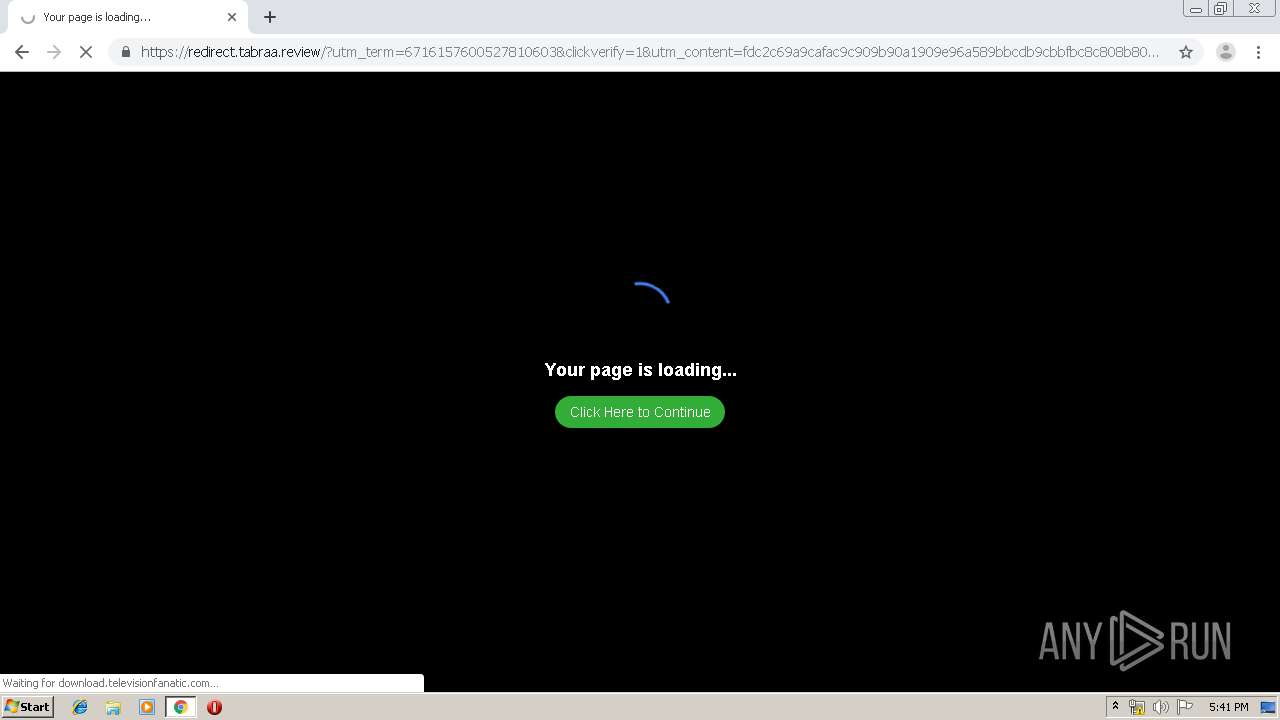
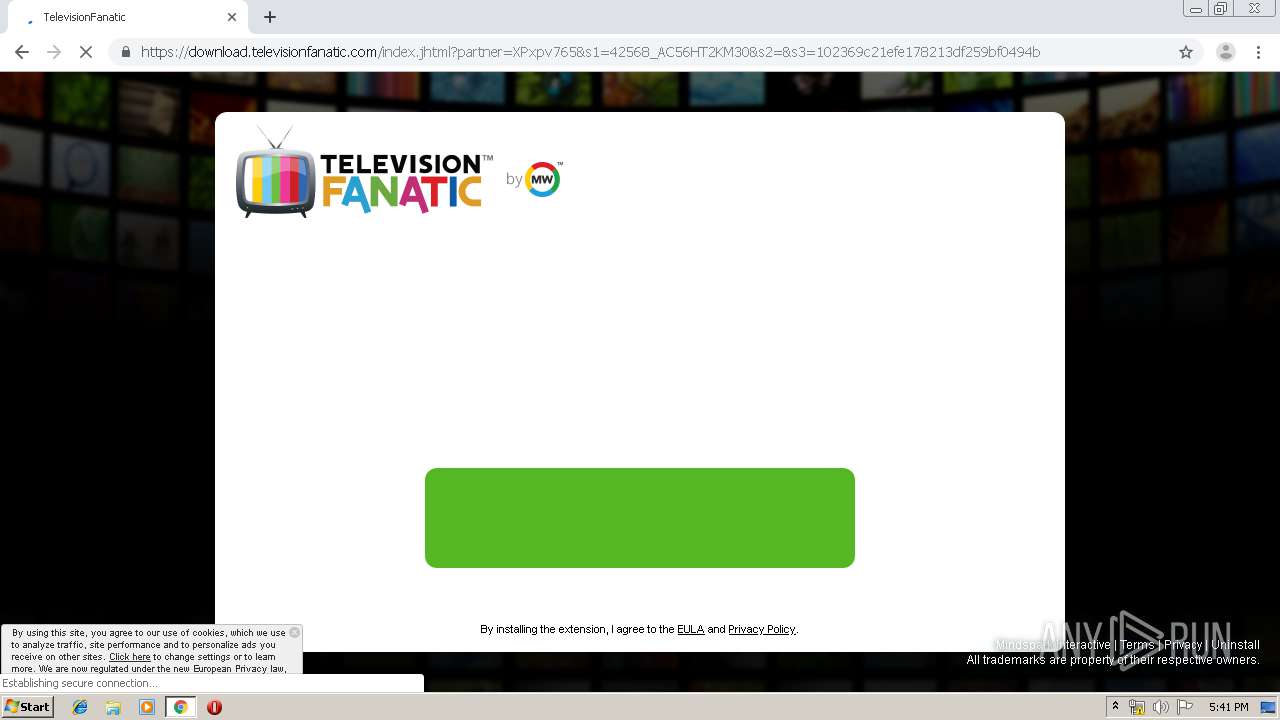
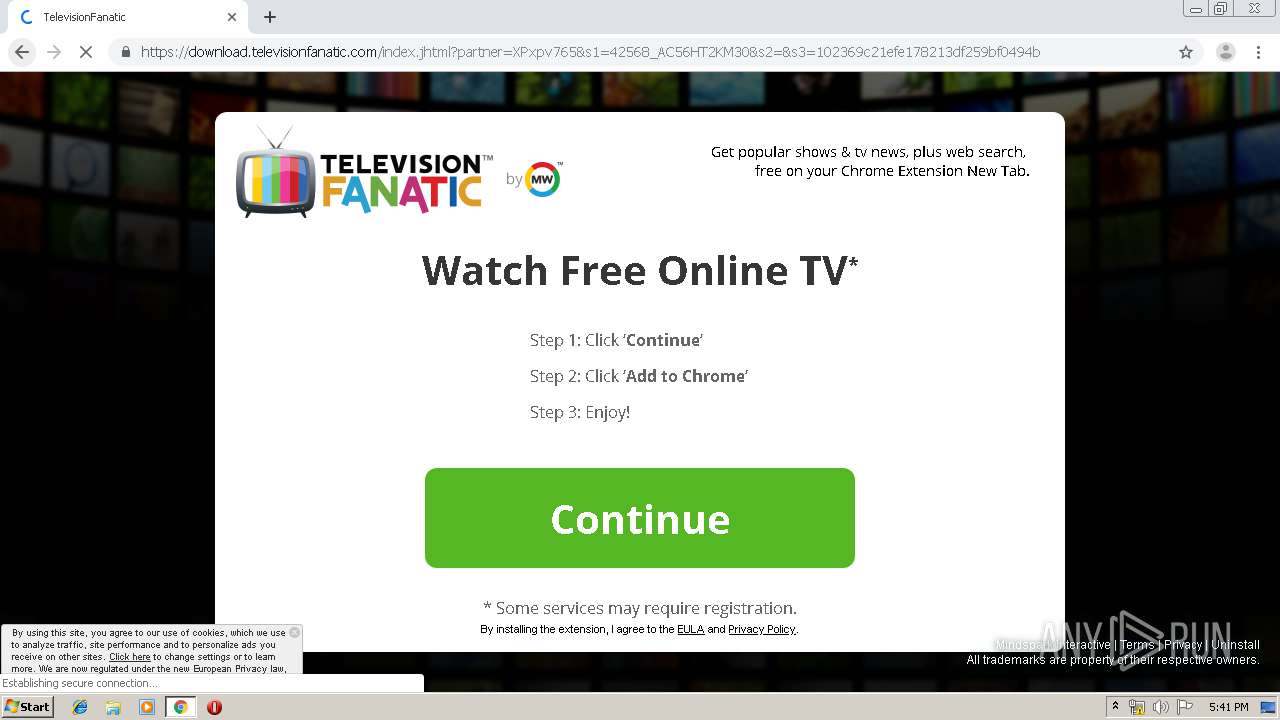
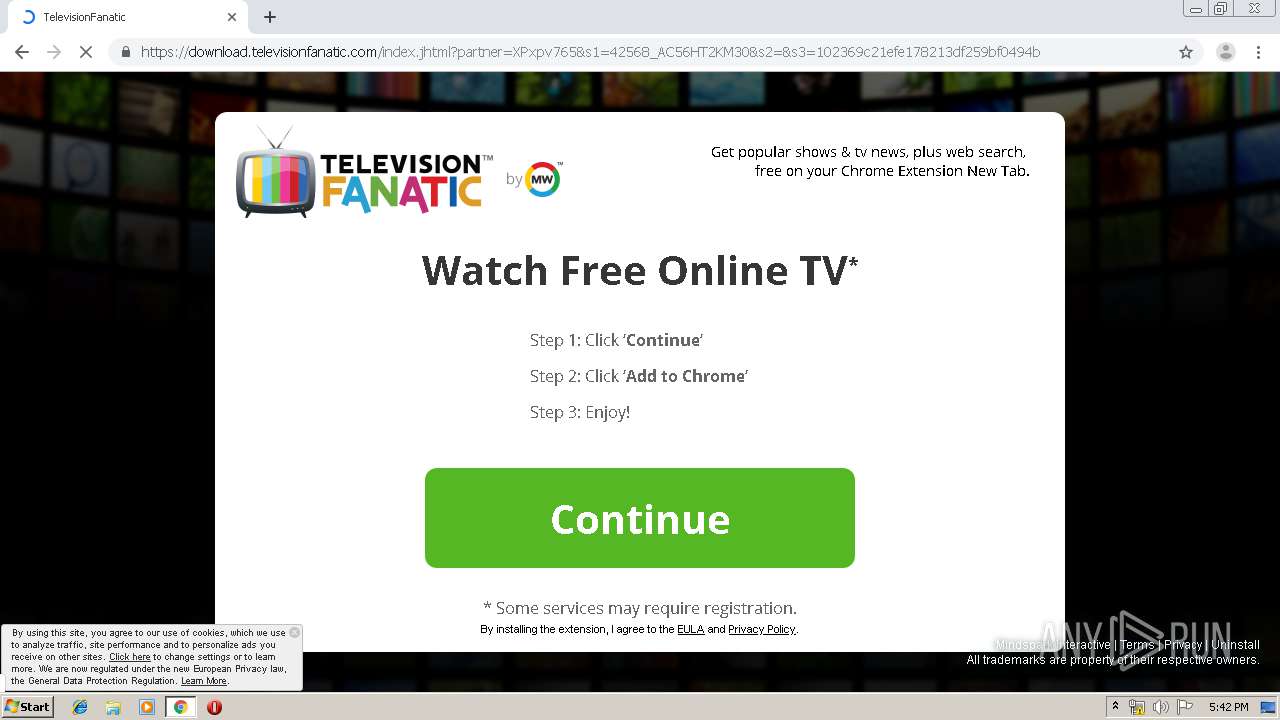
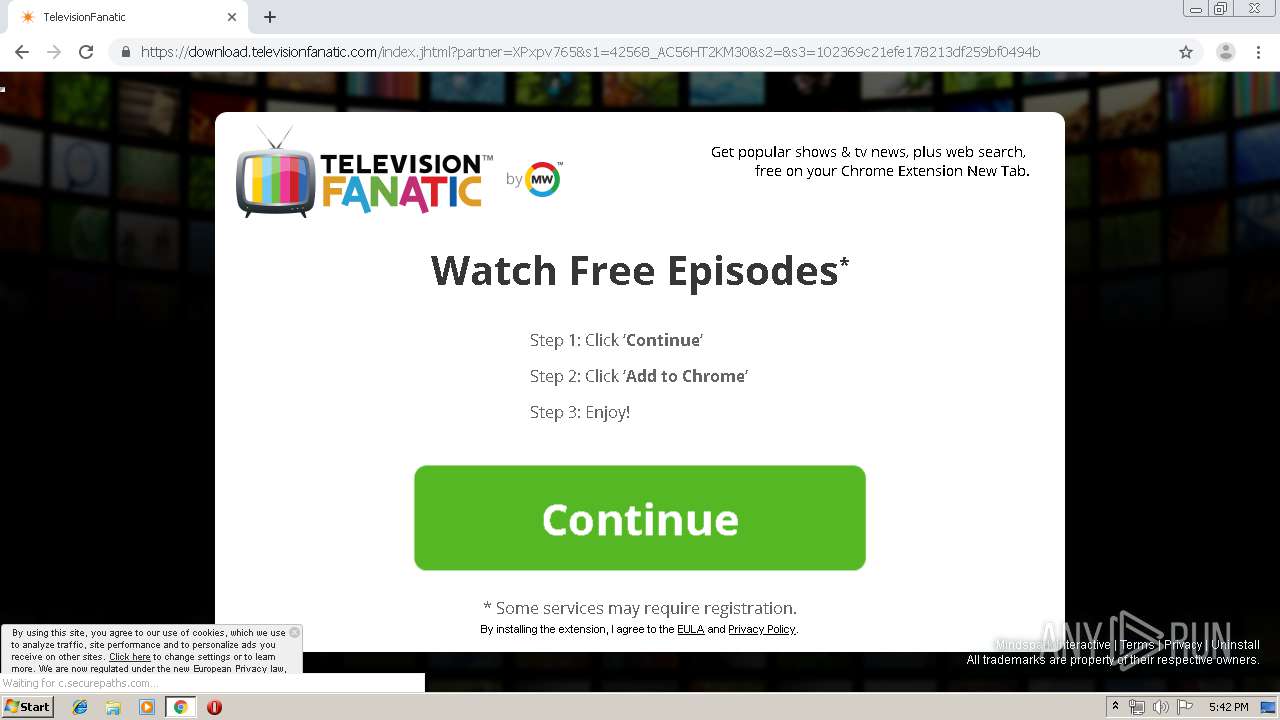
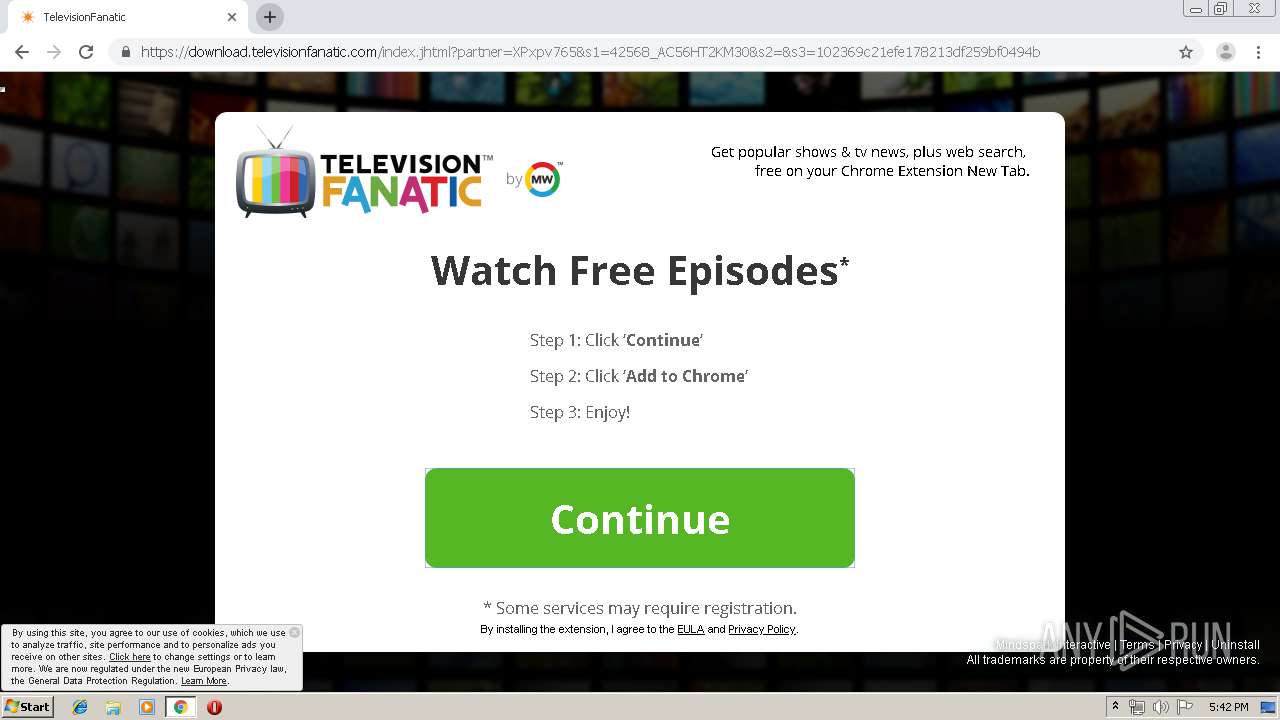
3504 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://download.televisionfanatic.com/index.jhtml?partner=XPxpv765&s1=42568_AC56HT2KM30&s2=&s3=102369c21efe178213df259bf0494b | US | — | — | whitelisted |
3504 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://download.televisionfanatic.com/index.jhtml?partner=XPxpv765&s1=42568_AC56HT2KM30&s2=&s3=102369c21efe178213df259bf0494b | US | — | — | whitelisted |
3504 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://download.televisionfanatic.com/index.jhtml?partner=XPxpv765&s1=42568_AC56HT2KM30&s2=&s3=102369c21efe178213df259bf0494b | US | — | — | whitelisted |
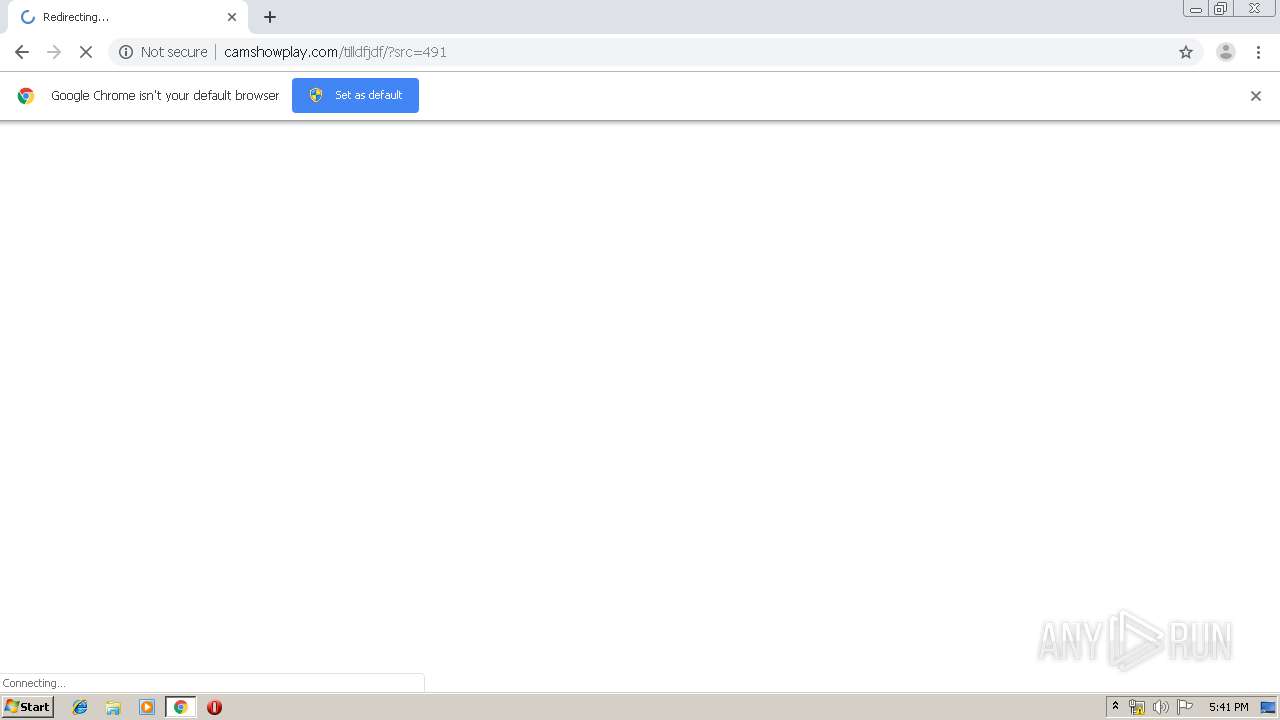
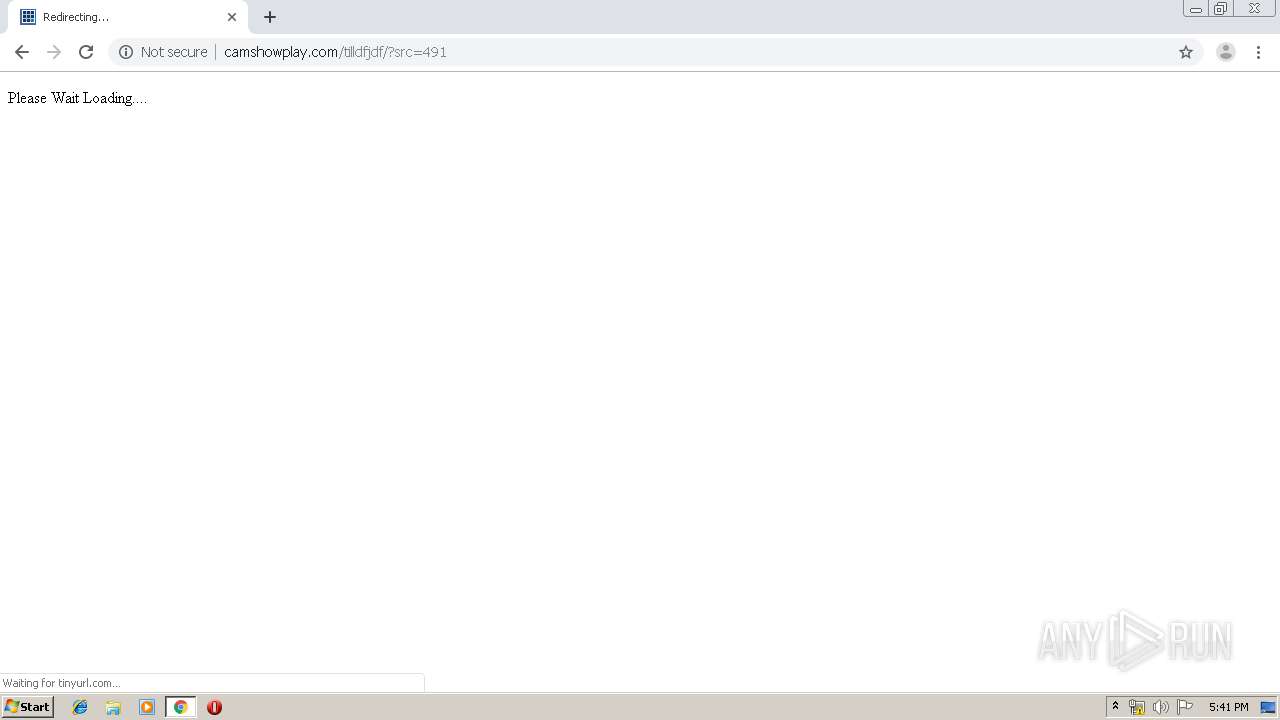
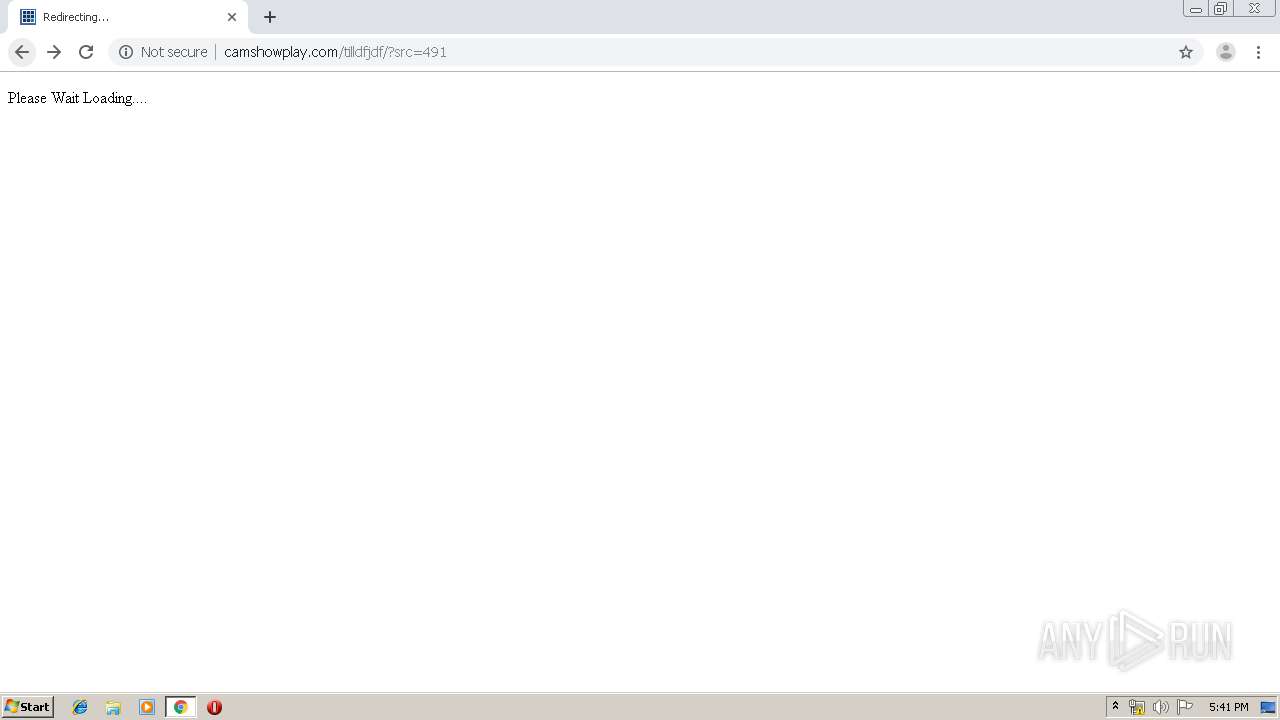
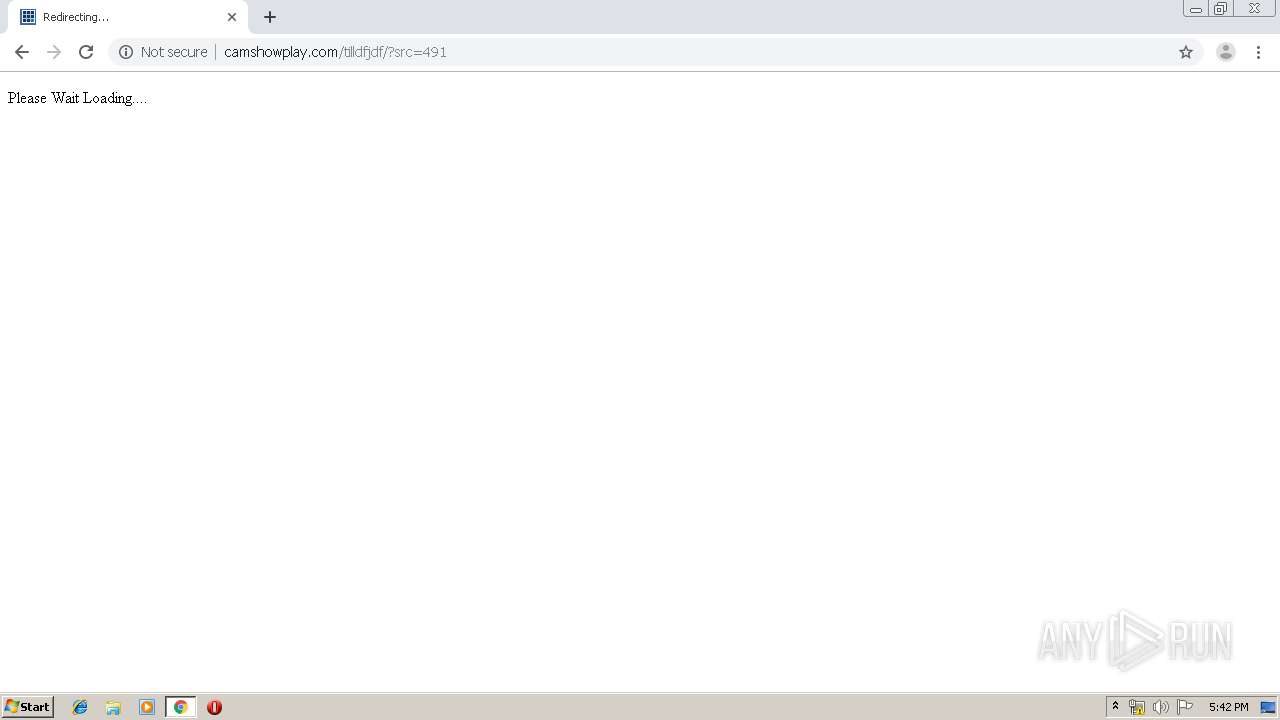
3504 | chrome.exe | GET | 200 | 69.89.31.169:80 | http://camshowplay.com/tilldfjdf/?src=491 | US | html | 601 b | suspicious |
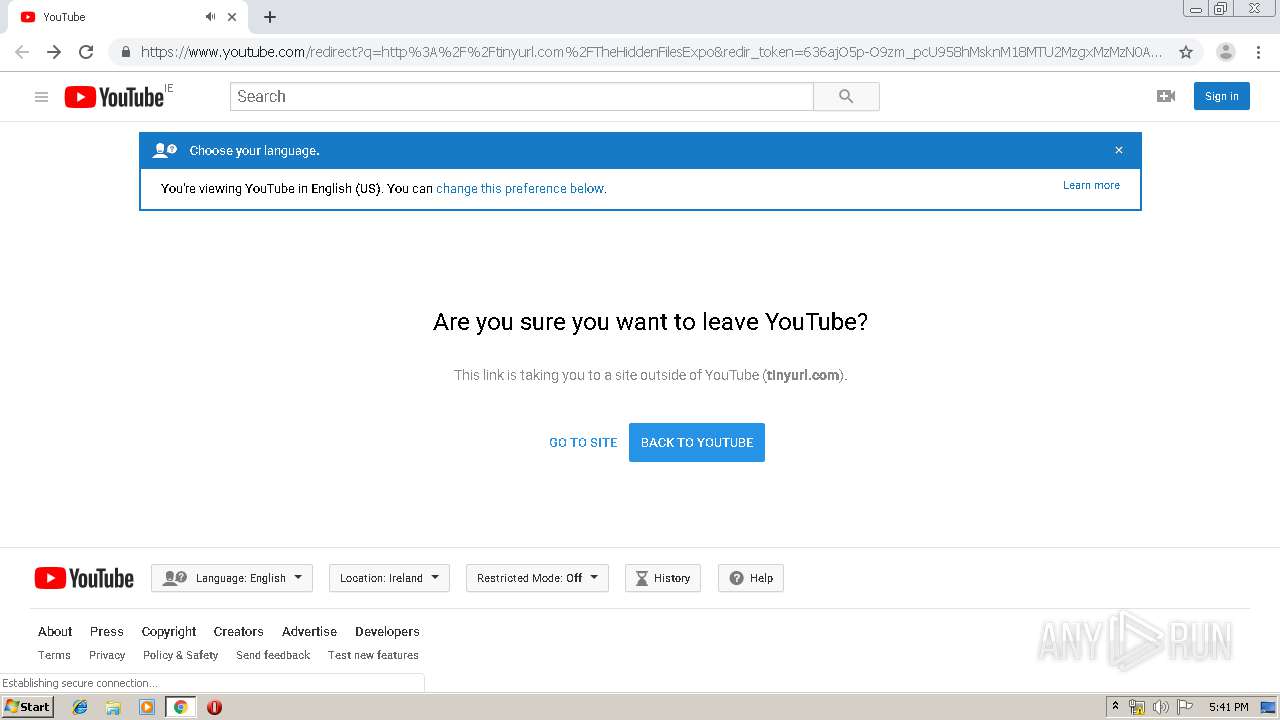
3504 | chrome.exe | GET | 301 | 104.20.219.42:80 | http://tinyurl.com/TheHiddenFilesExpo | US | html | 408 b | shared |
3504 | chrome.exe | GET | 301 | 104.20.219.42:80 | http://tinyurl.com/TheHiddenFilesExpo | US | html | 408 b | shared |
3504 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
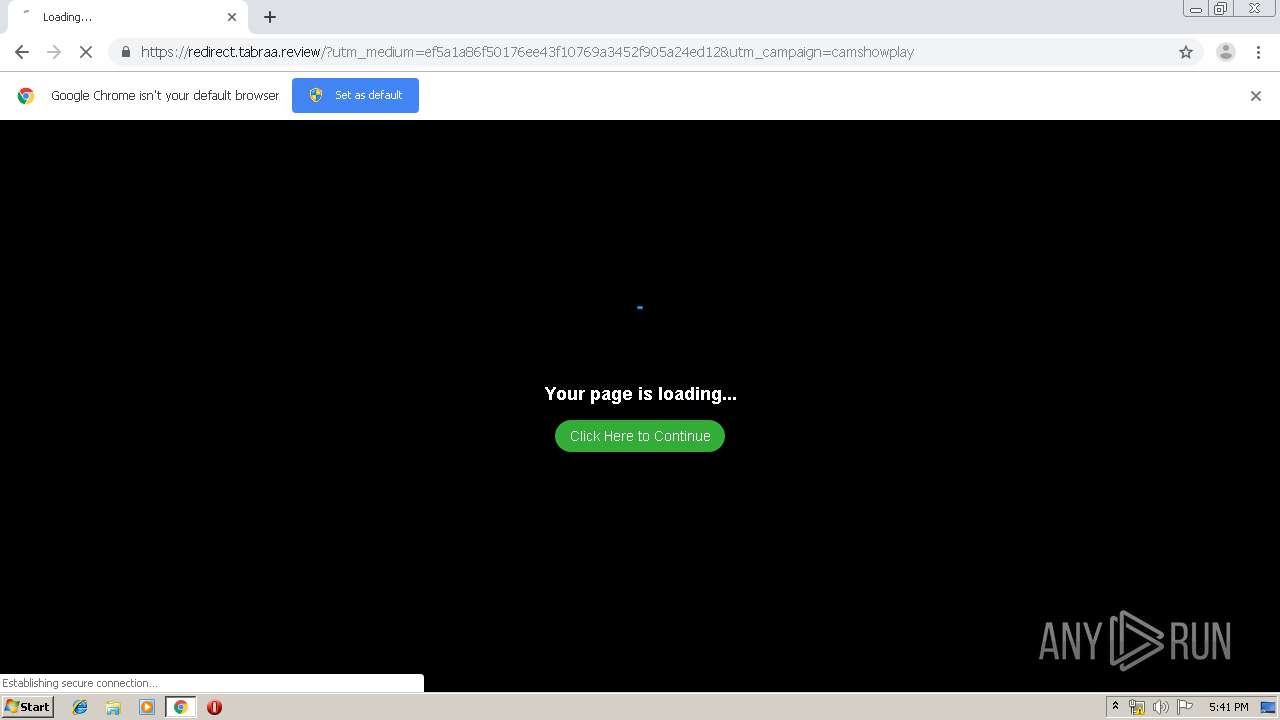
3504 | chrome.exe | GET | 302 | 54.76.219.112:80 | http://track.knlob.com/aff_c?offer_id=22356&aff_id=42568&aff_click_id=wB1V2E7576BCOG2O1LGAHVMS&aff_sub=AC56HT2KM30 | IE | html | 321 b | unknown |
3504 | chrome.exe | GET | 302 | 54.76.219.112:80 | http://track.knlob.com/aff_c?offer_id=22356&aff_id=42568&aff_click_id=w8PRJ04PA7C1AG2OHAGKQHP0&aff_sub=AC56HT2KM30 | IE | html | 321 b | unknown |
3504 | chrome.exe | GET | 302 | 54.76.219.112:80 | http://track.knlob.com/aff_c?offer_id=22356&aff_id=42568&aff_click_id=wED4DGSLUADCUG2OHS3COMD6&aff_sub=AC56HT2KM30 | IE | html | 321 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 69.89.31.169:80 | camshowplay.com | Unified Layer | US | suspicious |
3504 | chrome.exe | 172.217.22.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3504 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 104.20.3.47:80 | www.statcounter.com | Cloudflare Inc | US | shared |
3504 | chrome.exe | 104.20.2.47:80 | www.statcounter.com | Cloudflare Inc | US | shared |
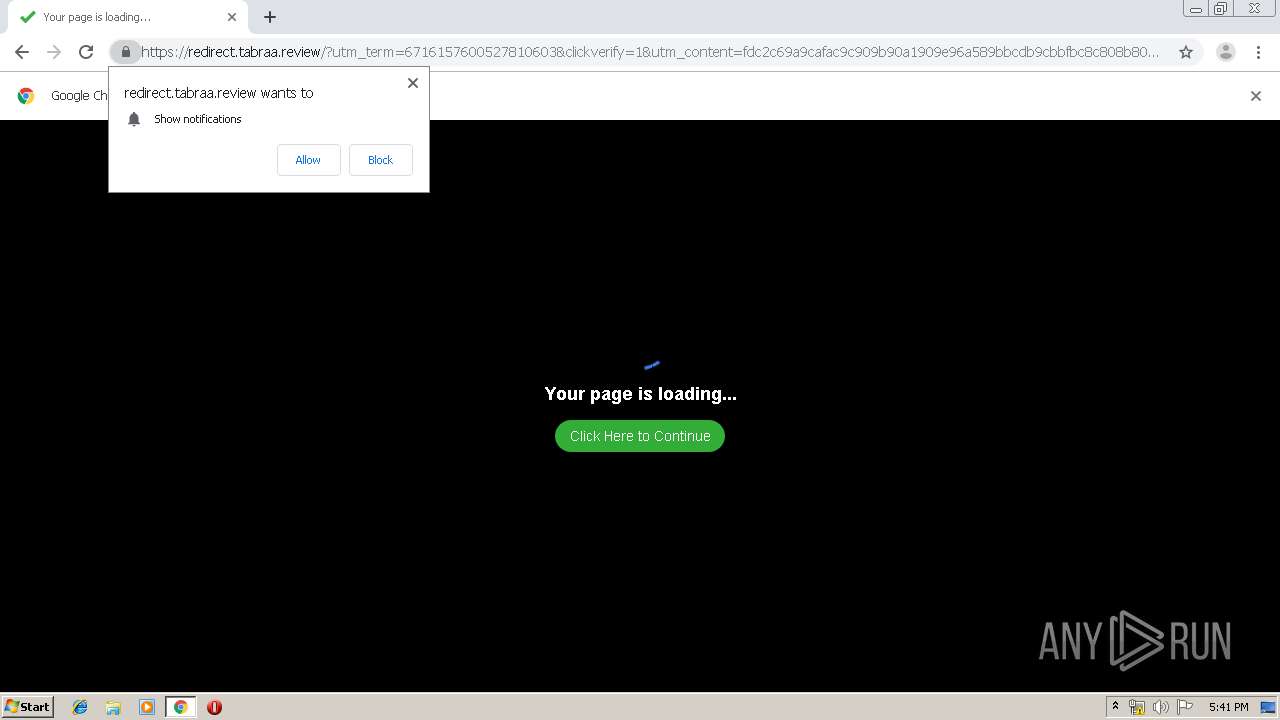
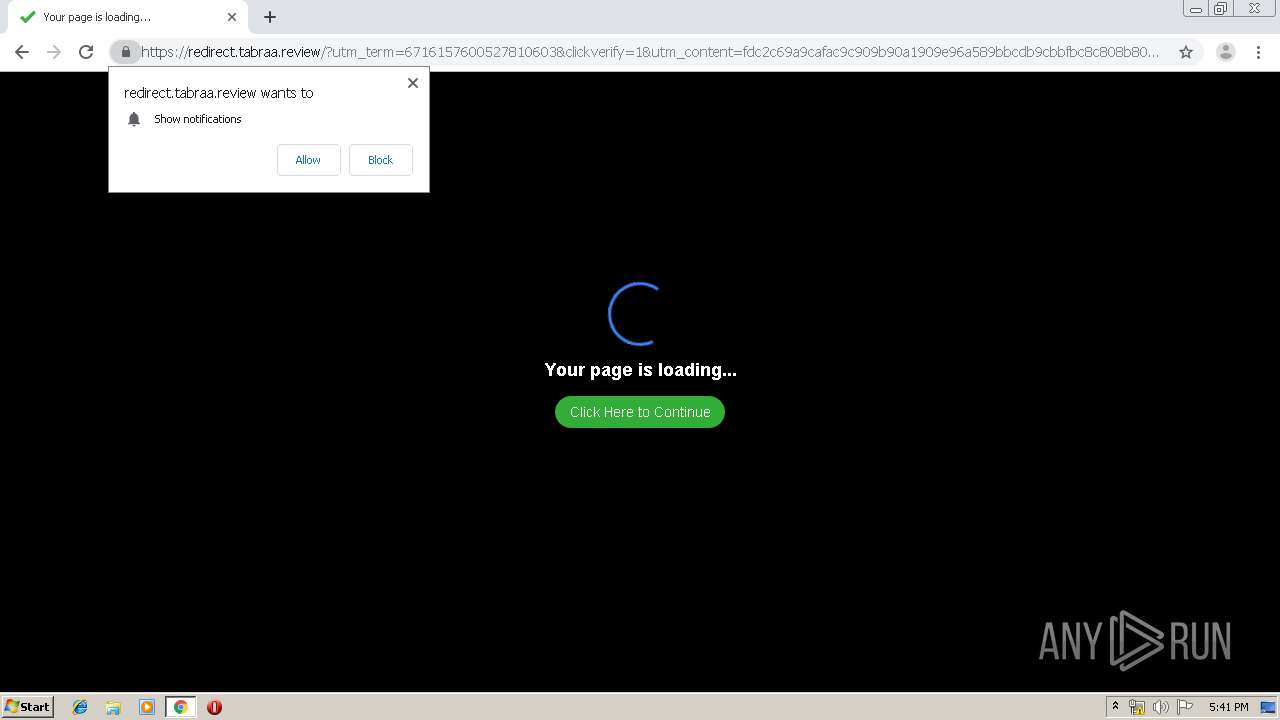
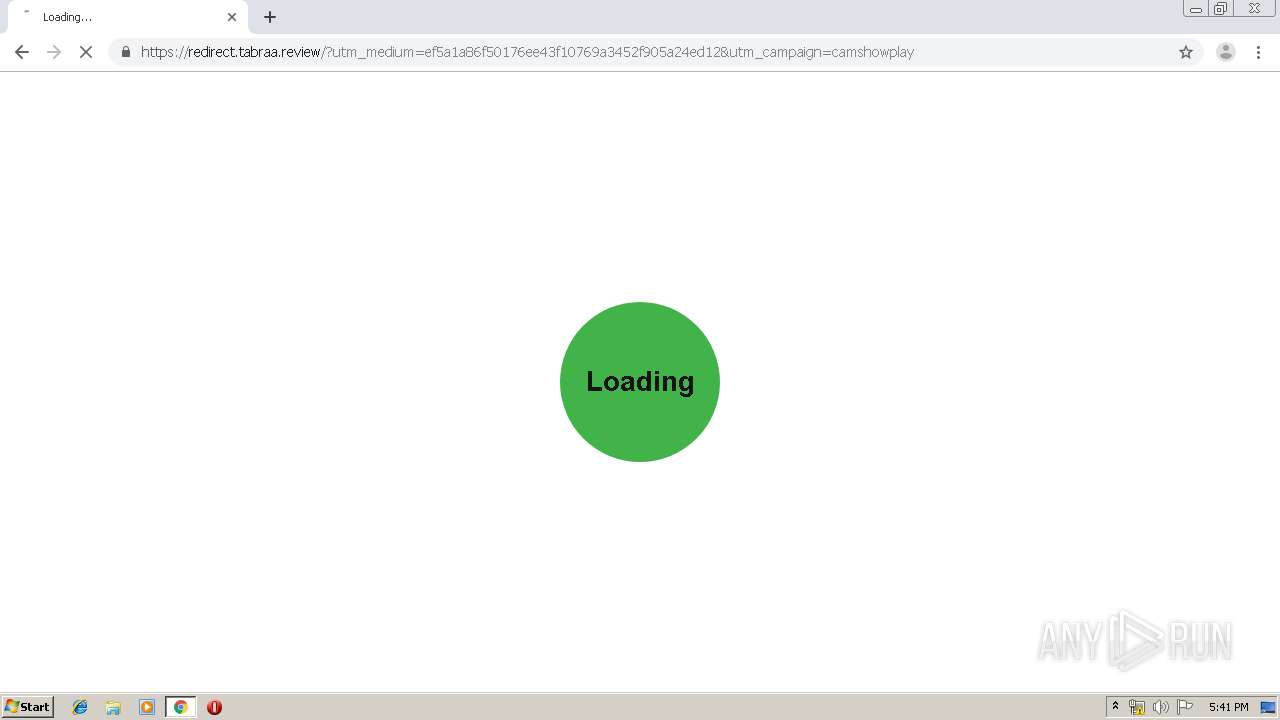
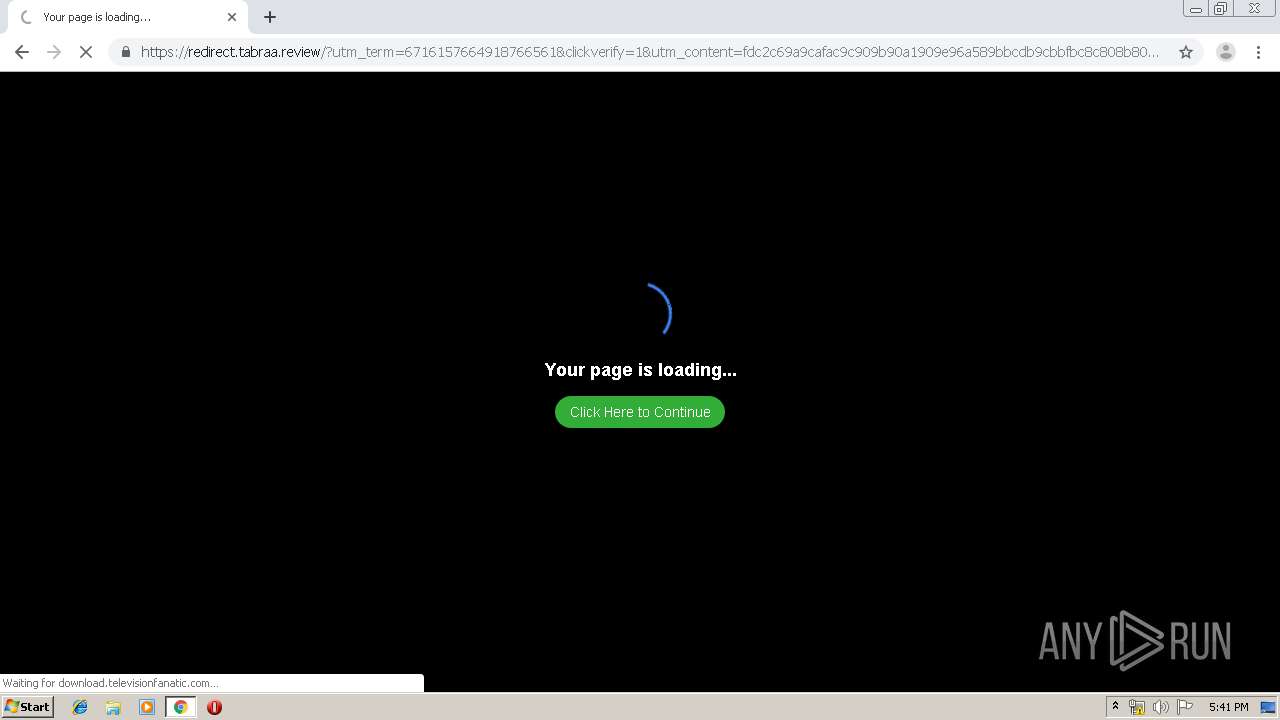
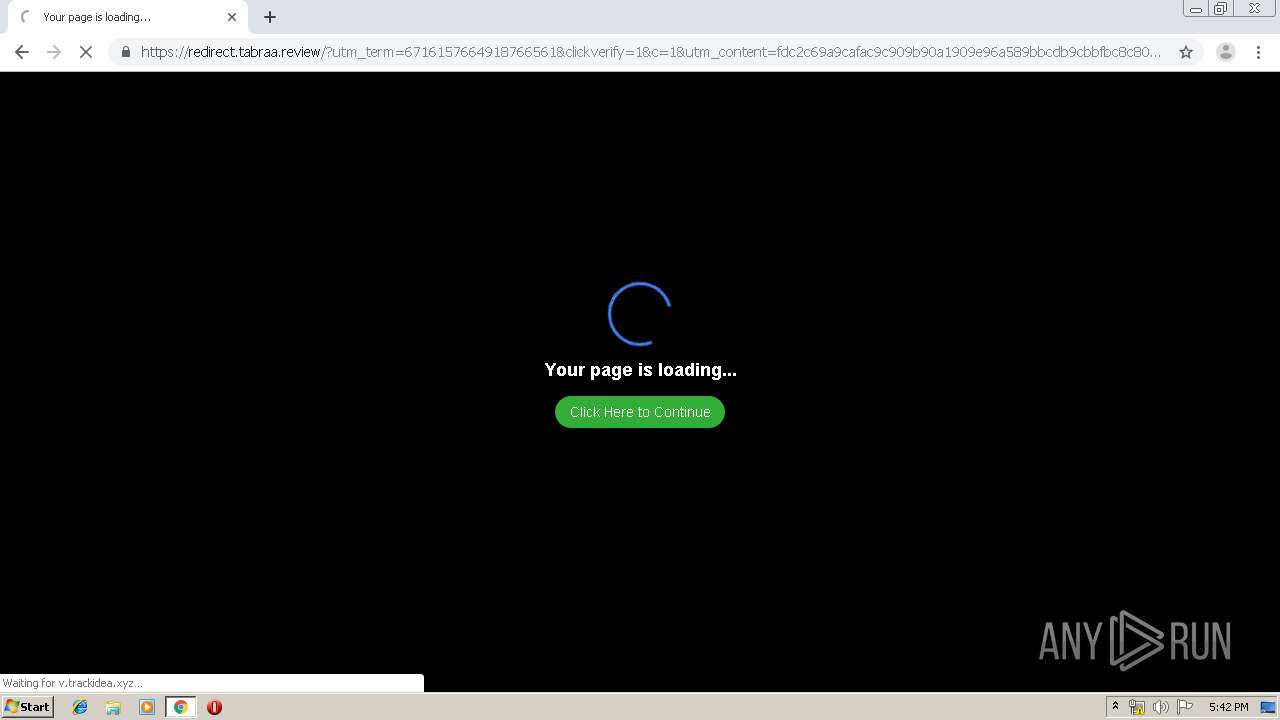
3504 | chrome.exe | 99.198.108.195:443 | redirect.tabraa.review | SingleHop, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
tinyurl.com |
| shared |
camshowplay.com |
| unknown |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3504 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |