| File name: | windowsdesktop-runtime-8.0.13-win-x64.exe.exe |
| Full analysis: | https://app.any.run/tasks/1347a157-17cf-4e8d-9b47-268637e2b512 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 19:25:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 11FB74010F9B3BFDD6F1D5EDE3C59299 |
| SHA1: | E0BAC395ECC713041227BD40B2C88976DBADF58D |
| SHA256: | 58134B4D729CDB7B4EE16F7D565ACBA38C1BED3559A2E5B9D72A975C51509FB2 |
| SSDEEP: | 393216:4g8/FC44a4wDj4h4KpMjmFXOeChtueFaJroDcK9MZRaiqGHg8pN:4g8tC44aN4h4Kp2uXOeOwRaDfCg5CFp |
MALICIOUS
No malicious indicators.SUSPICIOUS
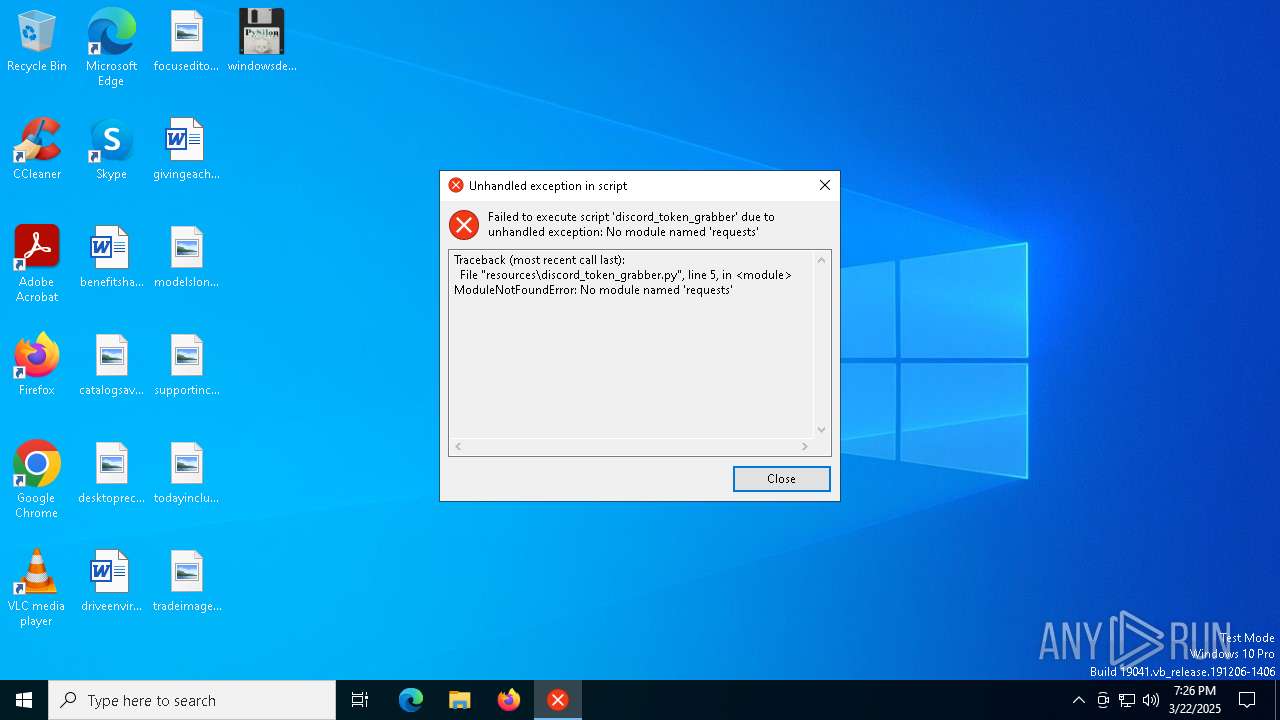
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
Process drops python dynamic module
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
Process drops legitimate windows executable
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
Loads Python modules
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 4300)
Application launched itself
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
The process drops C-runtime libraries
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
There is functionality for taking screenshot (YARA)
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
INFO
Checks supported languages
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 4300)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
The sample compiled with english language support
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
Reads the computer name
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 4300)
PyInstaller has been detected (YARA)
- windowsdesktop-runtime-8.0.13-win-x64.exe.exe (PID: 5956)
Checks proxy server information
- slui.exe (PID: 6112)
Reads the software policy settings
- slui.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:22 19:01:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 173568 |
| InitializedDataSize: | 285184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
120
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4300 | "C:\Users\admin\Desktop\windowsdesktop-runtime-8.0.13-win-x64.exe.exe" | C:\Users\admin\Desktop\windowsdesktop-runtime-8.0.13-win-x64.exe.exe | — | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 5956 | "C:\Users\admin\Desktop\windowsdesktop-runtime-8.0.13-win-x64.exe.exe" | C:\Users\admin\Desktop\windowsdesktop-runtime-8.0.13-win-x64.exe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6112 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 405
Read events
3 405
Write events
0
Delete events
0
Modification events
Executable files
330
Suspicious files
4
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:2141B6675C8734B2391E002B466C54C4 | SHA256:8D2276881B7C2F92EFD8E0589F71E63CC9719705C2A65AA21B812159C90E347F | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:AE4857C6864168901F6D4AE3B8192335 | SHA256:7A6D91CA6502E52DAB6C5EB13A62C758DC6CBBA47975F017A14C26CC28C76EEB | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:3FB1829E74C246D8D5AB74E9127CD04B | SHA256:5102215E2804454073A969297E46782DEFE6A2500C21EB2E9E8C0F05A9626B8E | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_cbc.pyd | executable | |
MD5:270FD535F94A87B973874B33F35E5AF8 | SHA256:B7AB0516B698A9F4EF50F08EF53AF907C83D841D117AF16CA742B7E186D3EF51 | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:5289590E846458681AB5F88EA5C0E794 | SHA256:C1B02D5892DF640CB390A4295B37BED1BD7ADBF8DB79298FC3CECA228FB99612 | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:F0FC554452175C0A3B0DBD0C1C1DB0A6 | SHA256:2CFFB2CA371F4203C450FDC6DAB0E5AD3EAC4C3B6CF1996C6C1F63F162CF1F39 | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_raw_des.pyd | executable | |
MD5:5FCBAC3D5D9CA624668AB53268501727 | SHA256:6CD87174EA725886F0FFF820603C5D5D08E4E4D258B0DBEAABE7E6F19D21C398 | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:0EB877FF760104BF41C8721E2B3B3B81 | SHA256:E4ED586FBAD65BDC2294EB5025C6148D3EBE29246C44EB4B1B1D32076A9E9B6B | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Cipher\_pkcs1_decode.pyd | executable | |
MD5:F946AD7040ACE3C5E98C42A0F957C448 | SHA256:53A3C6101DA3607EE25F46F4EE38DA15C5D3B6C95A0CD02648D0998198B842AC | |||
| 5956 | windowsdesktop-runtime-8.0.13-win-x64.exe.exe | C:\Users\admin\AppData\Local\Temp\_MEI59562\Crypto\Hash\_BLAKE2s.pyd | executable | |
MD5:E8DFFE7BF8A762CC6163BC6D724A61F3 | SHA256:8DC9ECD1DF282C67CC25FDDCD4DF515C1E12DDC566A4A4F2825A1B883DFEFAF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
22
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5968 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6112 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
activation-v2.sls.microsoft.com |
| unknown |