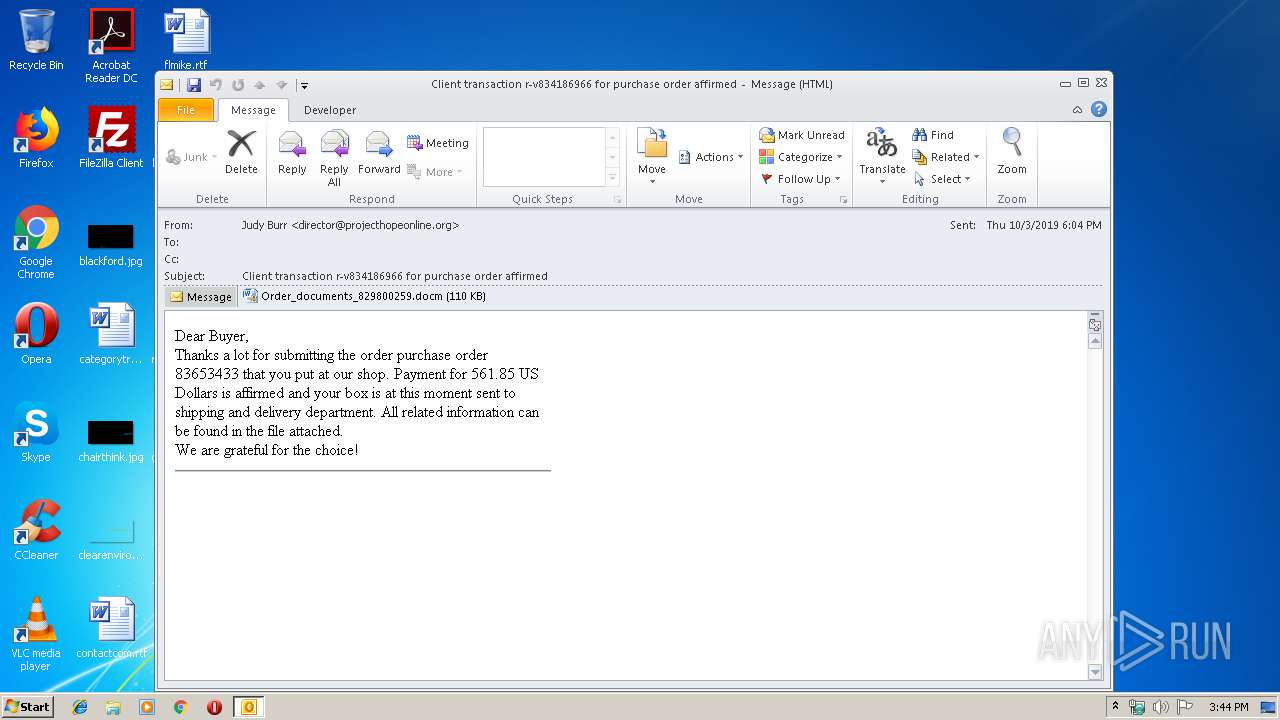
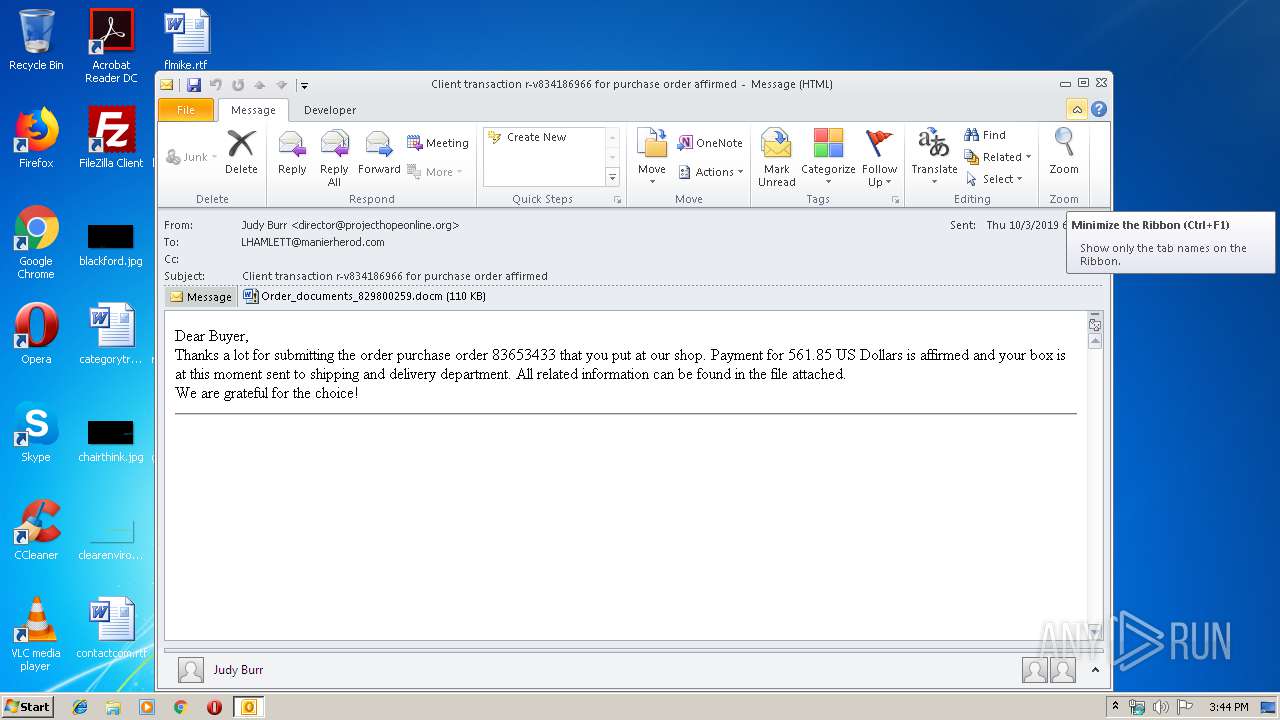
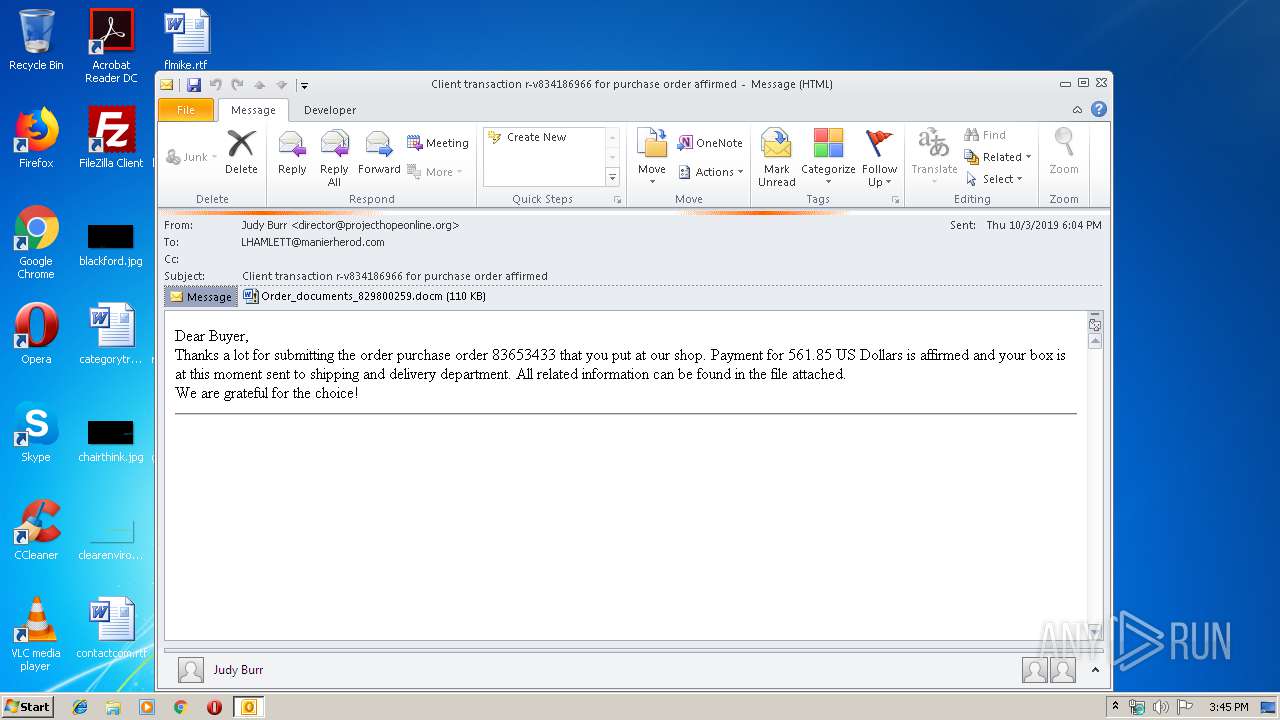
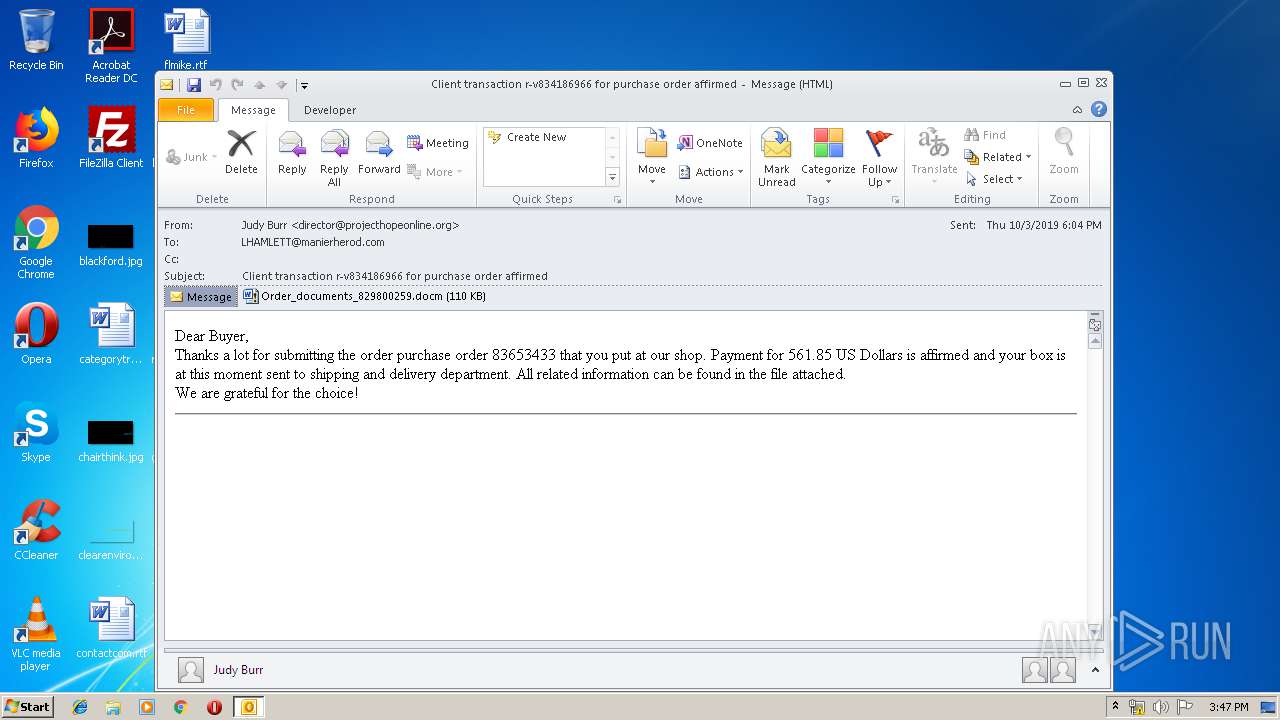
| File name: | source (1).eml |
| Full analysis: | https://app.any.run/tasks/80978b69-18ce-41c4-9574-2597d86dcb85 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 14:44:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | AA2CFE4D0E9FED3362E14DB238982668 |
| SHA1: | 26437E80E72A943986159B07B261DE893DBCB599 |
| SHA256: | 57FE29F318041D17FC5A6856C091052CDFE6B1146447258FCC55D4611F97A2C2 |
| SSDEEP: | 3072:xF6Kvwfs6rI+MVvEZnPssOD+qwelcAWyAYML3xUUghJWMPdB1j7mhQ:f6KvwfBrXrnoD+qMAWNFL3xUbhJLB1n |
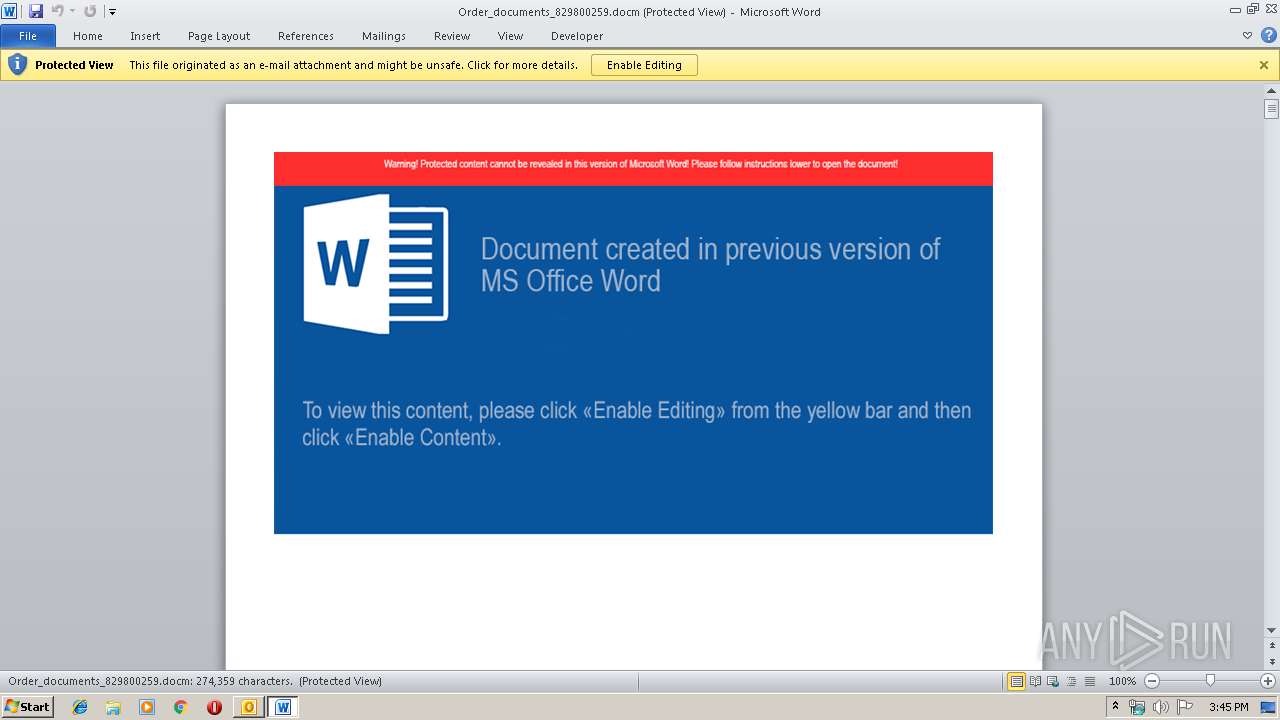
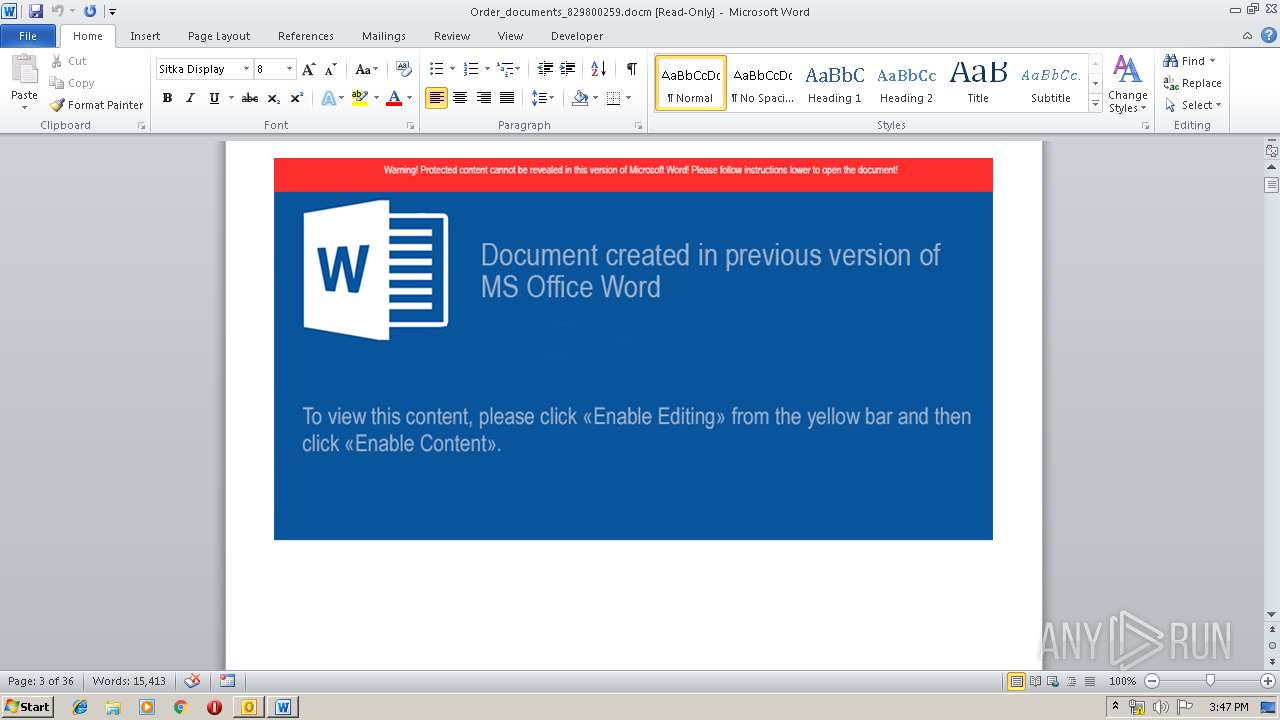
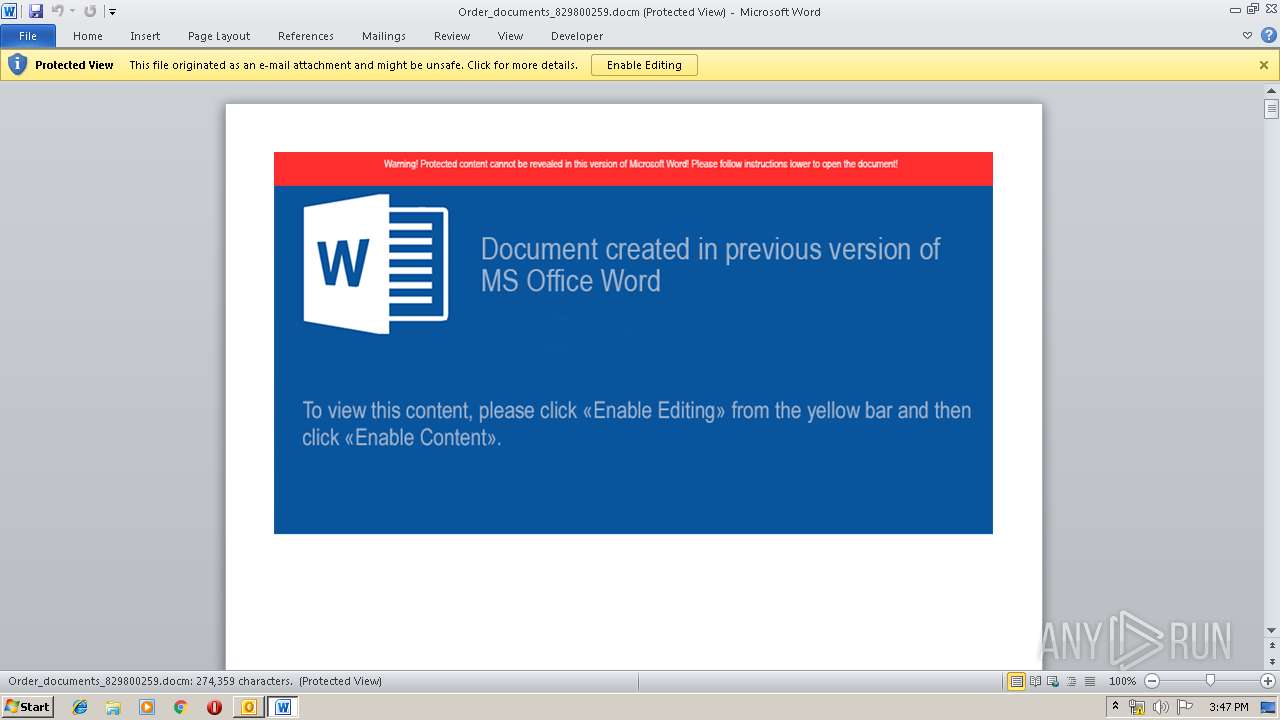
MALICIOUS
Writes file to Word startup folder
- WINWORD.EXE (PID: 680)
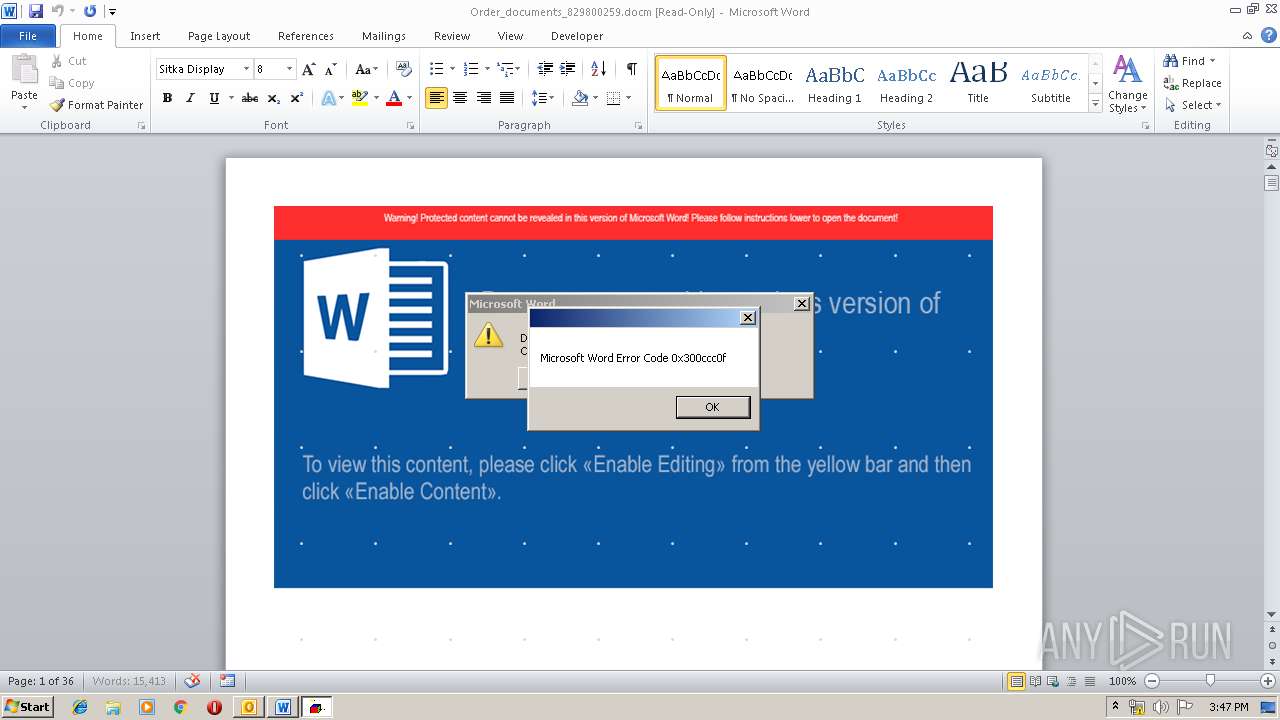
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 680)
Executes PowerShell scripts
- WINWORD.EXE (PID: 680)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2648)
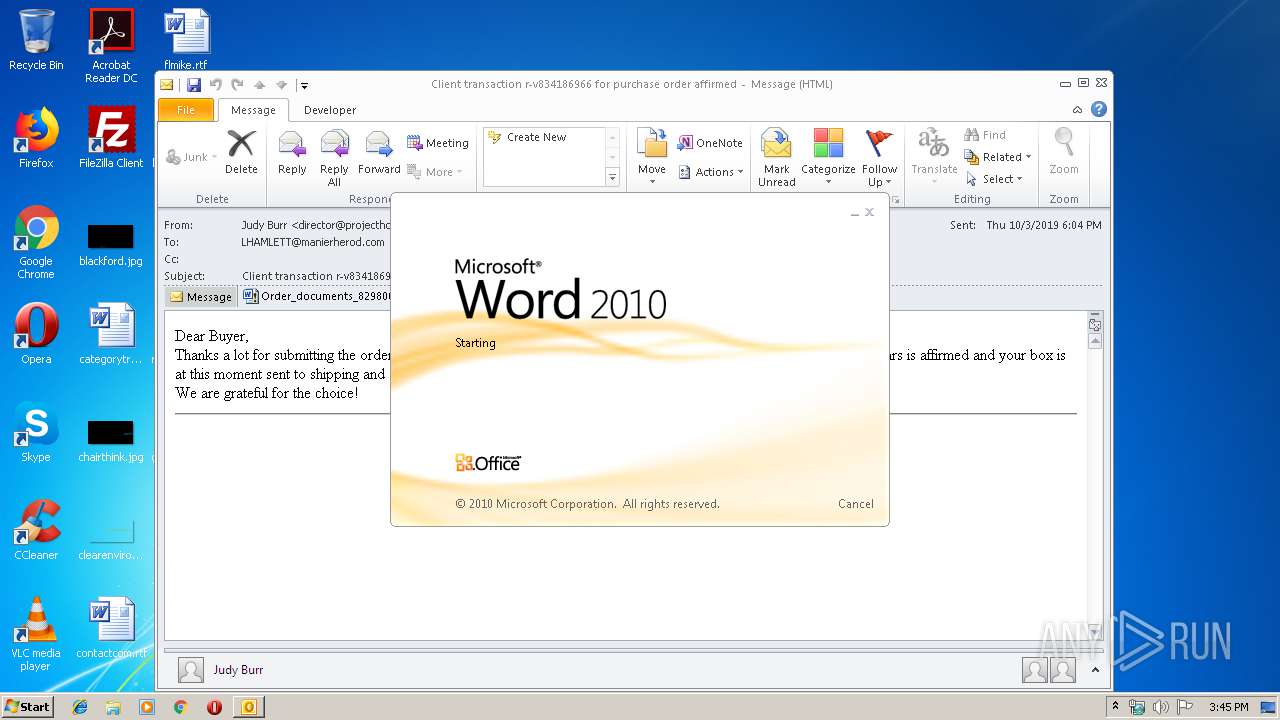
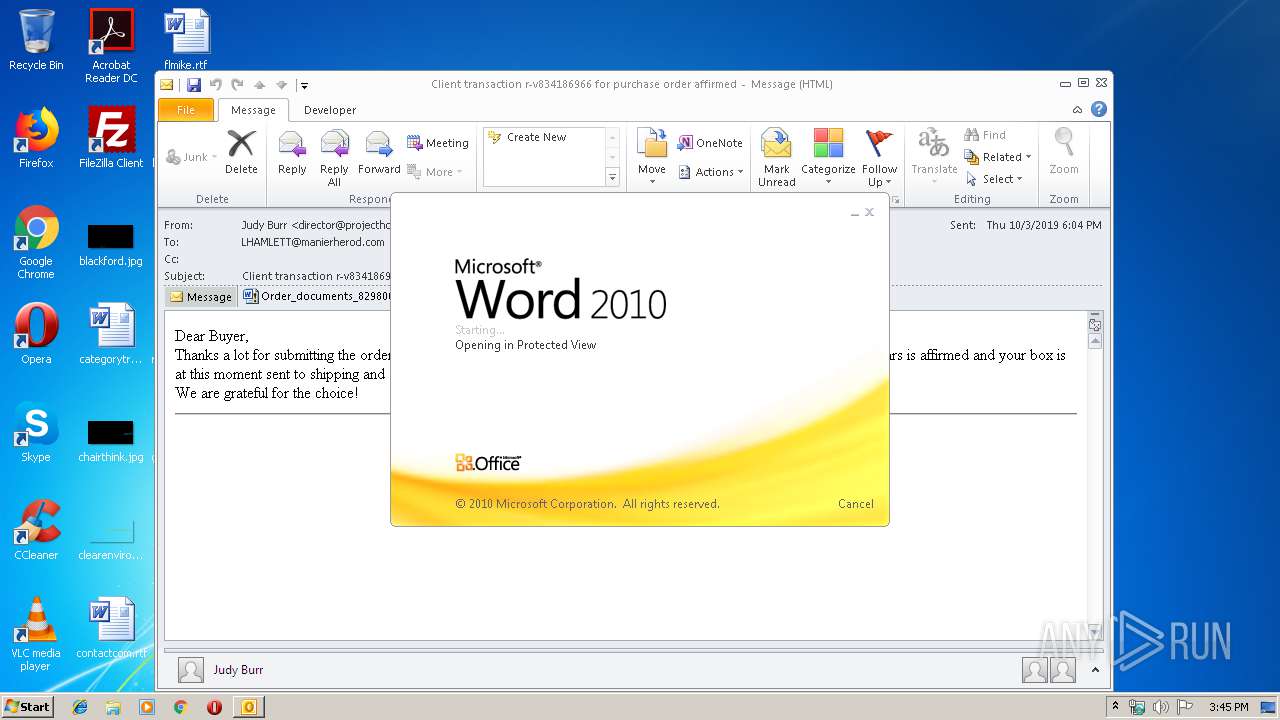
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2648)
- WINWORD.EXE (PID: 680)
- WINWORD.EXE (PID: 2992)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2648)
- powershell.exe (PID: 3264)
Application launched itself
- WINWORD.EXE (PID: 680)
- WINWORD.EXE (PID: 2992)
Executes scripts
- powershell.exe (PID: 3264)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2648)
- WINWORD.EXE (PID: 768)
- WINWORD.EXE (PID: 680)
- WINWORD.EXE (PID: 2992)
- WINWORD.EXE (PID: 2216)
Creates files in the user directory
- WINWORD.EXE (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
42
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
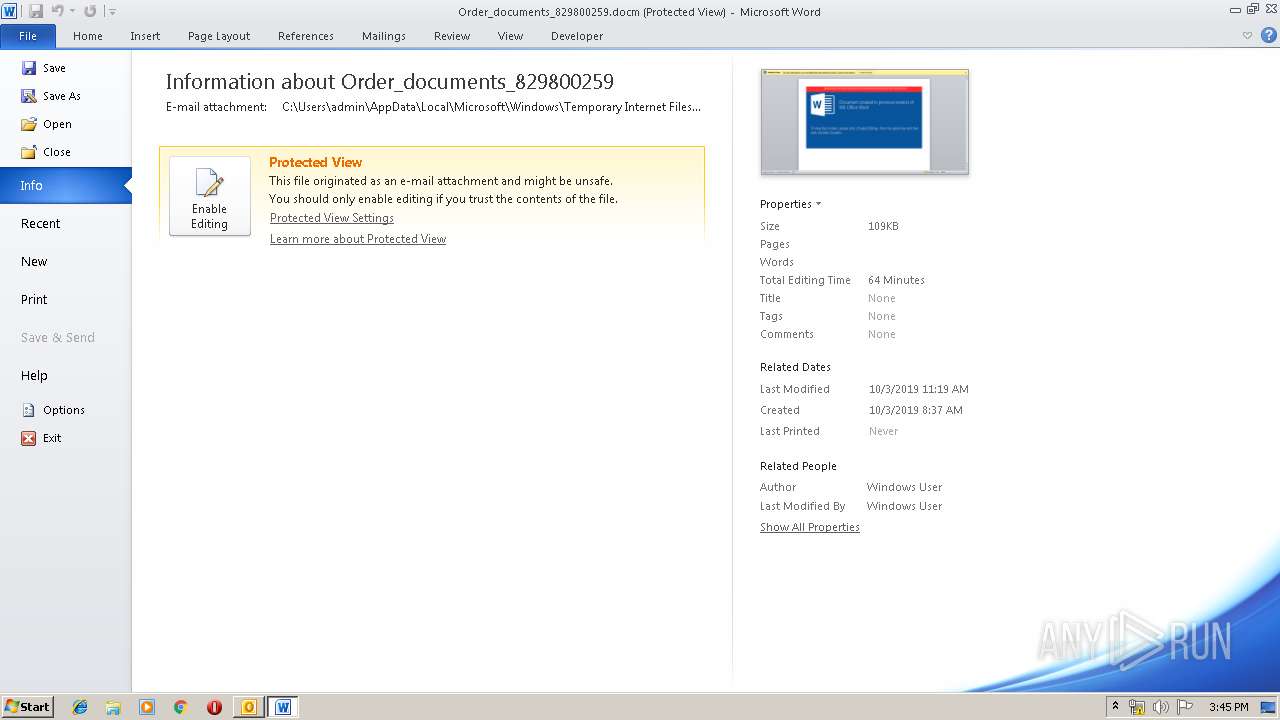
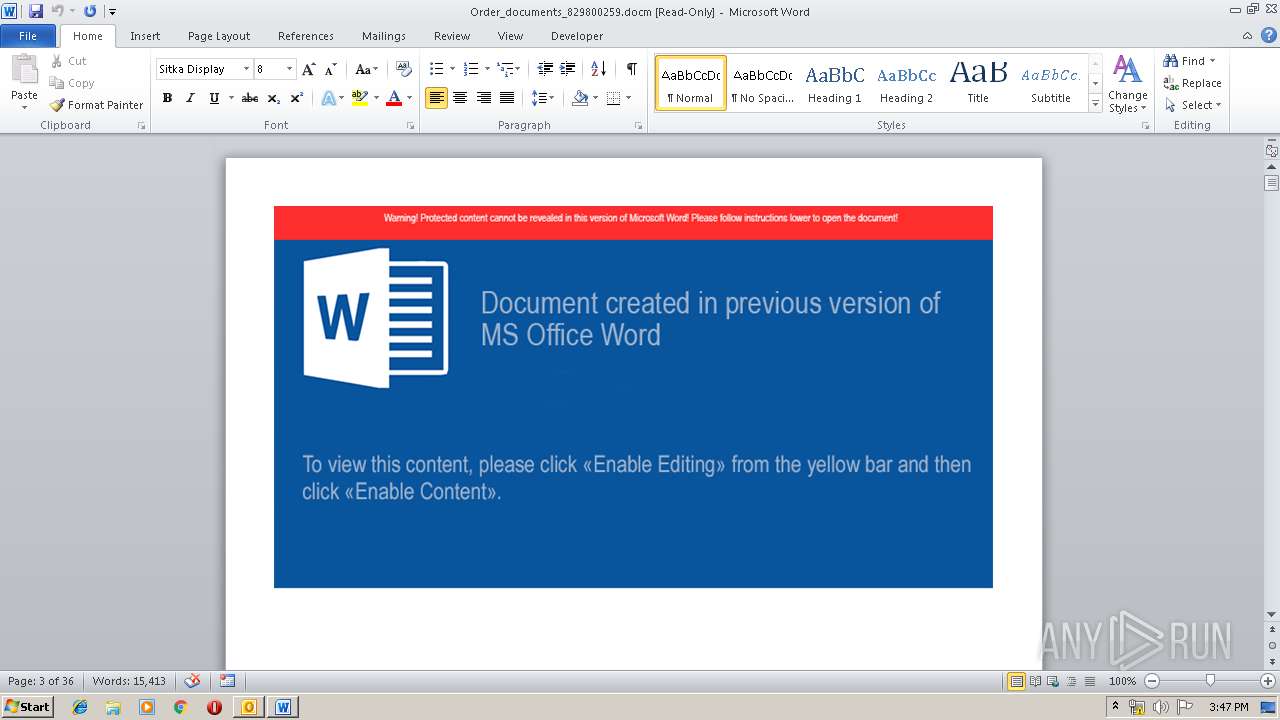
| 680 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H6ESEY7K\Order_documents_829800259.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1952 | "C:\Windows\system32\wscript.exe" /e:Jscript "c:\users\admin\appdata\roaming\microsoft\word\startup\margee:14.0 | C:\Windows\system32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2648 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\source (1).eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H6ESEY7K\Order_documents_829800259.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3264 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Start-process -FilePath "wscript" -ArgumentList @('/e:Jscript','\"c:\users\admin\appdata\roaming\microsoft\word\startup\margee:14.0"') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 399
Read events
4 836
Write events
1 494
Delete events
69
Modification events
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | &!< |
Value: 26213C00580A0000010000000000000000000000 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 580A00007229B909B07ED50100000000 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2648) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
0
Suspicious files
8
Text files
26
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6126.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2648 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H6ESEY7K\Order_documents_829800259 (2).docm\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9F9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8C2FA181-20B3-4FD4-814C-6E3C2DE594FC.0\EA2D86CE.docm\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8C2FA181-20B3-4FD4-814C-6E3C2DE594FC.0\32DEA33A.png | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8C2FA181-20B3-4FD4-814C-6E3C2DE594FC.0\~WRS{DF47C1F1-FAED-49E8-8068-4AC7C9705F33}.tmp | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8C2FA181-20B3-4FD4-814C-6E3C2DE594FC.0\~WRF{B24E8314-7DE0-454A-854F-C94987C8677C}.tmp | — | |
MD5:— | SHA256:— | |||
| 3264 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0T4CY33SGO2Q0LL8Z67Z.temp | — | |
MD5:— | SHA256:— | |||
| 2648 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H6ESEY7K\Order_documents_829800259.docm | document | |
MD5:— | SHA256:— | |||
| 2648 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H6ESEY7K\Order_documents_829800259 (2).docm | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |