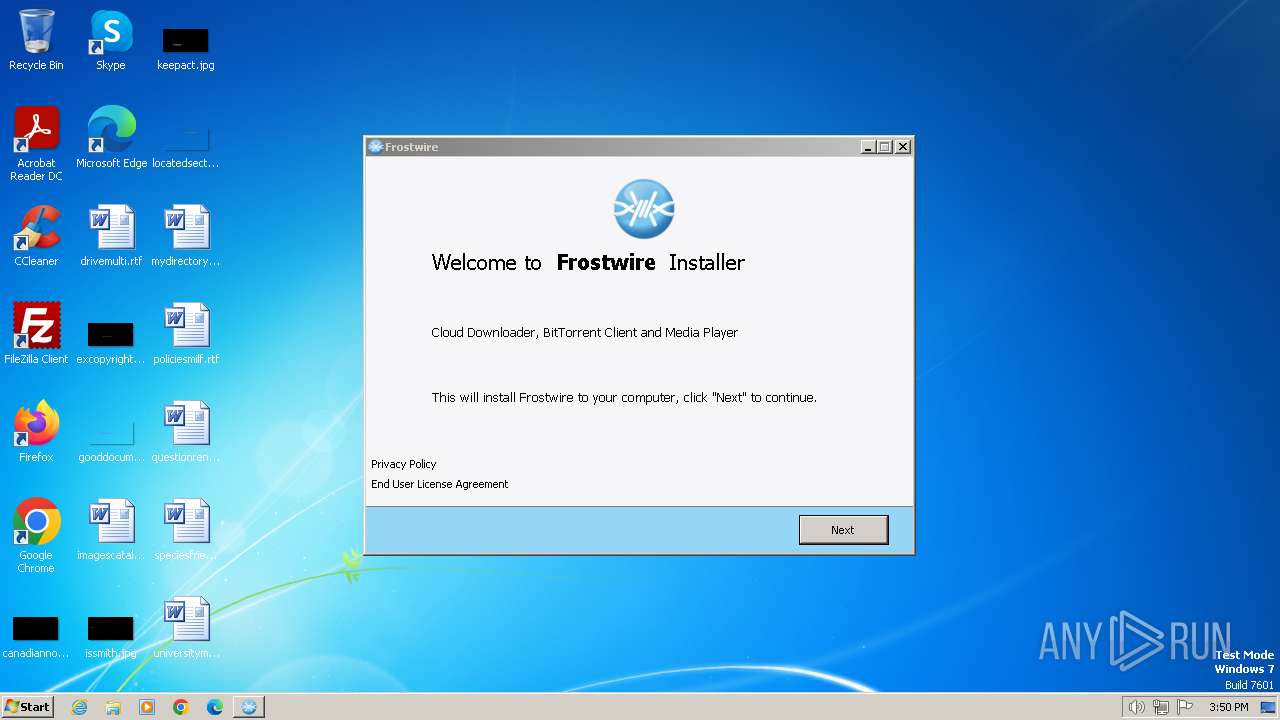
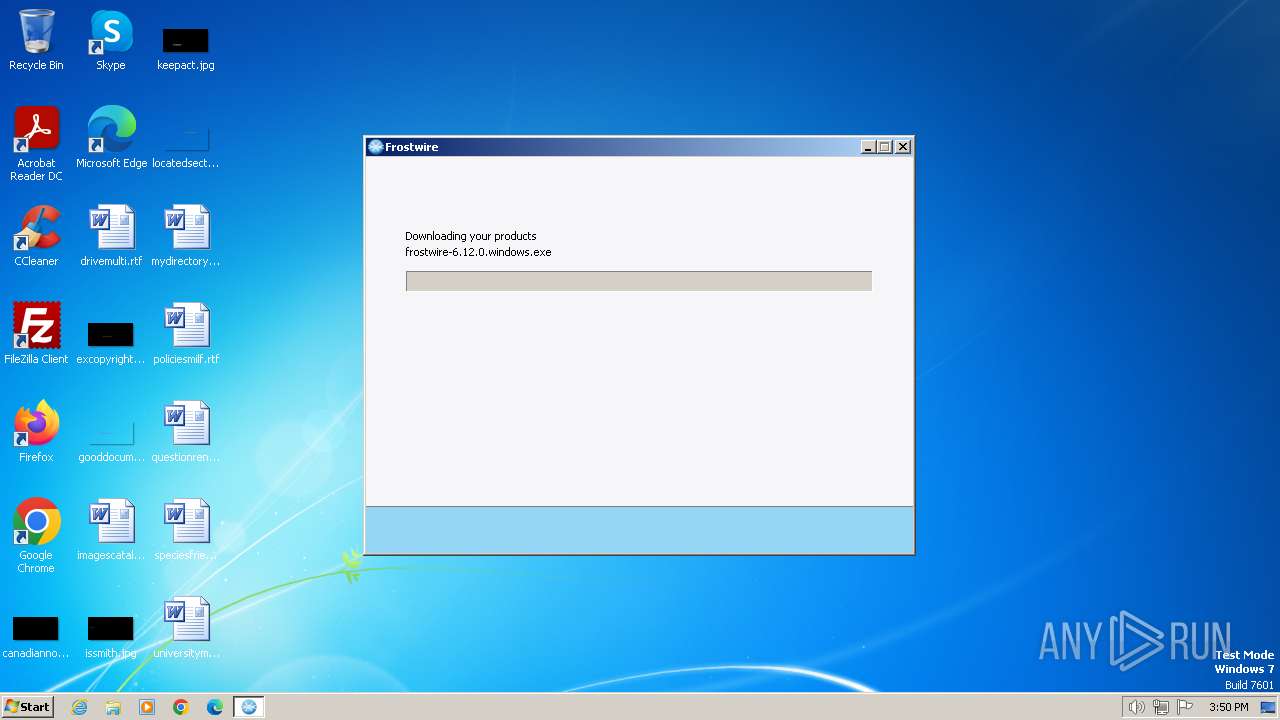
| File name: | frostwire-6.12.0.windows.exe |
| Full analysis: | https://app.any.run/tasks/bfce7321-aebd-43d8-9f2f-3532e360b1a0 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2024, 15:49:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 102995A5B58DE2CFC017D677ECC049F7 |
| SHA1: | 5AA25CAA49EF2CFFC1032DB01F9C3FFCD811DB41 |
| SHA256: | 57FAD42313274C164223C20CBB1483BD40218D0A614B78E5618A02B83892405F |
| SSDEEP: | 98304:W+QqZ8fkSGBj9XuL0EiEkOPATc+YiEQTPqMW4XrVSrkWIeU+dhsmBQqpCAwGn3En:L/WA |
MALICIOUS
Drops the executable file immediately after the start
- frostwire-6.12.0.windows.exe (PID: 4052)
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 3228)
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 2468)
- icarus.exe (PID: 2808)
Deletes shadow copies
- ns74BC.tmp (PID: 2672)
- ns7693.tmp (PID: 1860)
- ns7615.tmp (PID: 2072)
Creates a writable file in the system directory
- icarus.exe (PID: 2808)
SUSPICIOUS
Executable content was dropped or overwritten
- frostwire-6.12.0.windows.exe (PID: 3228)
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- frostwire-6.12.0.windows.exe (PID: 4052)
- icarus.exe (PID: 2468)
- icarus.exe (PID: 2808)
Reads the Windows owner or organization settings
- frostwire-6.12.0.windows.tmp (PID: 1876)
Reads the Internet Settings
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 2232)
- WMIC.exe (PID: 2148)
- WMIC.exe (PID: 1496)
- WMIC.exe (PID: 3400)
Reads settings of System Certificates
- frostwire-6.12.0.windows.tmp (PID: 1876)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 2468)
The process creates files with name similar to system file names
- frostwire-6.12.0.windows.exe (PID: 2232)
- icarus.exe (PID: 2808)
Malware-specific behavior (creating "System.dll" in Temp)
- frostwire-6.12.0.windows.exe (PID: 2232)
Reads security settings of Internet Explorer
- frostwire-6.12.0.windows.exe (PID: 2232)
- frostwire-6.12.0.windows.tmp (PID: 1876)
Starts application with an unusual extension
- frostwire-6.12.0.windows.exe (PID: 2232)
Uses WMIC.EXE to obtain data on processes
- ns74BC.tmp (PID: 2672)
- ns7693.tmp (PID: 1860)
- ns7615.tmp (PID: 2072)
Process drops legitimate windows executable
- frostwire-6.12.0.windows.exe (PID: 2232)
The process drops C-runtime libraries
- frostwire-6.12.0.windows.exe (PID: 2232)
Starts itself from another location
- icarus.exe (PID: 2468)
The process verifies whether the antivirus software is installed
- icarus.exe (PID: 2808)
INFO
Create files in a temporary directory
- frostwire-6.12.0.windows.exe (PID: 4052)
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- frostwire-6.12.0.windows.exe (PID: 3228)
- icarus.exe (PID: 2468)
- icarus.exe (PID: 2808)
- icarus.exe (PID: 984)
Checks supported languages
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 4052)
- frostwire-6.12.0.windows.exe (PID: 2232)
- ns74BC.tmp (PID: 2672)
- ns7615.tmp (PID: 2072)
- ns7693.tmp (PID: 1860)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 2468)
- frostwire-6.12.0.windows.tmp (PID: 3652)
- icarus.exe (PID: 2808)
- icarus.exe (PID: 984)
- frostwire-6.12.0.windows.exe (PID: 3228)
Reads the machine GUID from the registry
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 984)
- icarus.exe (PID: 2808)
- icarus.exe (PID: 2468)
Reads the software policy settings
- frostwire-6.12.0.windows.tmp (PID: 1876)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 2468)
Reads the computer name
- frostwire-6.12.0.windows.tmp (PID: 1876)
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_setup.exe (PID: 2112)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- frostwire-6.12.0.windows.tmp (PID: 3652)
- icarus.exe (PID: 2808)
- icarus.exe (PID: 984)
- icarus.exe (PID: 2468)
Checks proxy server information
- frostwire-6.12.0.windows.exe (PID: 2232)
Creates files in the program directory
- frostwire-6.12.0.windows.exe (PID: 2232)
- avg_antivirus_free_online_setup.exe (PID: 3800)
- icarus.exe (PID: 2468)
- icarus.exe (PID: 2808)
Creates a software uninstall entry
- frostwire-6.12.0.windows.exe (PID: 2232)
Creates files or folders in the user directory
- frostwire-6.12.0.windows.exe (PID: 2232)
Reads CPU info
- icarus.exe (PID: 2468)
- icarus.exe (PID: 984)
- icarus.exe (PID: 2808)
Dropped object may contain TOR URL's
- icarus.exe (PID: 2468)
- icarus.exe (PID: 2808)
Reads Environment values
- icarus.exe (PID: 2808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.12.0.0 |
| ProductVersionNumber: | 6.12.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Frostwire Installer |
| FileVersion: | 6.12.0 |
| LegalCopyright: | © Frostwire |
| OriginalFileName: | |
| ProductName: | Frostwire |
| ProductVersion: | 6.12.0 |
Total processes
62
Monitored processes
16
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 984 | C:\Windows\Temp\asw-3703872a-b09a-4820-83bb-3112bd96c202\avg-av-vps\icarus.exe /silent /ws /psh:92pTu5f8VukIH5HOXCfncbsAfTalm2Fk7J05p7hVTyAsL8x84C8QRwVOSMpkLyuMyjQowT2PZ5yX0q /cookie:mmm_irs_ppi_902_451_o /track-guid:513d3a01-a889-4ba9-8efc-29b58acfd312 /edat_dir:C:\Windows\Temp\asw.11e9c9828948547b /er_master:master_ep_7b093ac4-643a-4dca-9d4d-c1066fc91353 /er_ui:ui_ep_b0597f4f-307f-4cc3-95ed-dcd03f480e3f /er_slave:avg-av-vps_slave_ep_839adad6-b4f4-4b4f-b986-366aee275c80 /slave:avg-av-vps | C:\Windows\Temp\asw-3703872a-b09a-4820-83bb-3112bd96c202\avg-av-vps\icarus.exe | — | icarus.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Exit code: 0 Version: 24.1.6758.0 Modules
| |||||||||||||||
| 1496 | wmic process where name='fwplayer.exe' delete | C:\Windows\System32\wbem\WMIC.exe | — | ns74BC.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7693.tmp" wmic process where name='FrostWire.exe' delete | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7693.tmp | — | frostwire-6.12.0.windows.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\is-D1DOL.tmp\frostwire-6.12.0.windows.tmp" /SL5="$100130,1716697,917504,C:\Users\admin\AppData\Local\Temp\frostwire-6.12.0.windows.exe" /SPAWNWND=$18013E /NOTIFYWND=$E0170 | C:\Users\admin\AppData\Local\Temp\is-D1DOL.tmp\frostwire-6.12.0.windows.tmp | frostwire-6.12.0.windows.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7615.tmp" wmic process where name='telluride.exe' delete | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7615.tmp | — | frostwire-6.12.0.windows.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\prod0_extract\avg_antivirus_free_setup.exe" /silent /ws /psh:92pTu5f8VukIH5HOXCfncbsAfTalm2Fk7J05p7hVTyAsL8x84C8QRwVOSMpkLyuMyjQowT2PZ5yX0q | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\prod0_extract\avg_antivirus_free_setup.exe | frostwire-6.12.0.windows.tmp | ||||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Installer Exit code: 0 Version: 2.1.99.0 Modules
| |||||||||||||||
| 2148 | wmic process where name='telluride.exe' delete | C:\Windows\System32\wbem\WMIC.exe | — | ns7615.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\frostwire-6.12.0.windows.exe" /S | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\frostwire-6.12.0.windows.exe | frostwire-6.12.0.windows.tmp | ||||||||||||
User: admin Company: FrostWire LLC Integrity Level: HIGH Description: FrostWire - Search, Download, Play, Share. Exit code: 0 Version: 6.12.0.318 Modules
| |||||||||||||||
| 2468 | C:\Windows\Temp\asw-3703872a-b09a-4820-83bb-3112bd96c202\common\icarus.exe /icarus-info-path:C:\Windows\Temp\asw-3703872a-b09a-4820-83bb-3112bd96c202\icarus-info.xml /install /silent /ws /psh:92pTu5f8VukIH5HOXCfncbsAfTalm2Fk7J05p7hVTyAsL8x84C8QRwVOSMpkLyuMyjQowT2PZ5yX0q /cookie:mmm_irs_ppi_902_451_o /track-guid:513d3a01-a889-4ba9-8efc-29b58acfd312 /edat_dir:C:\Windows\Temp\asw.11e9c9828948547b | C:\Windows\Temp\asw-3703872a-b09a-4820-83bb-3112bd96c202\common\icarus.exe | avg_antivirus_free_online_setup.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Exit code: 0 Version: 24.1.6758.0 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns74BC.tmp" wmic process where name='fwplayer.exe' delete | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns74BC.tmp | — | frostwire-6.12.0.windows.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
23 003
Read events
22 856
Write events
133
Delete events
14
Modification events
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 540700001672D1243967DA01 | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 406FFE6ABEC5CE84D349DA3C58366E6EF72B80F7277FD079A1B2CB658ED69E5A | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D80300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 1400000001000000140000005D6CA352CEFC713CBBC5E21F663C3639FD19D4D70300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB60F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D8200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (1876) frostwire-6.12.0.windows.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000BCC80DAA2F98A4692805BFF4CBB372EB0F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D80300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB61400000001000000140000005D6CA352CEFC713CBBC5E21F663C3639FD19D4D7200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (2232) frostwire-6.12.0.windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2232) frostwire-6.12.0.windows.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
Executable files
162
Suspicious files
42
Text files
201
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\is-IKTPL.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\frostwire-6.12.0.windows.exe | — | |
MD5:— | SHA256:— | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\is-M1U03.tmp | image | |
MD5:5EF5291810C454A35F76D976105F37CC | SHA256:03E69E8C87732C625DF2F628AC63BD145268F9DEA9C5F3DD3670B1CF349A995C | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\zbShieldUtils.dll | executable | |
MD5:E1F18A22199C6F6AA5D87B24E5B39EF1 | SHA256:62C56C8CF2AC6521CE047B73AA99B6D3952CA53F11D34B00E98D17674A2FC10D | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\AVG_AV.png | image | |
MD5:5EF5291810C454A35F76D976105F37CC | SHA256:03E69E8C87732C625DF2F628AC63BD145268F9DEA9C5F3DD3670B1CF349A995C | |||
| 2232 | frostwire-6.12.0.windows.exe | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7693.tmp | executable | |
MD5:08E9796CA20C5FC5076E3AC05FB5709A | SHA256:8165C7AEF7DE3D3E0549776535BEDC380AD9BE7BB85E60AD6436F71528D092AF | |||
| 2232 | frostwire-6.12.0.windows.exe | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\inetc.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
| 2232 | frostwire-6.12.0.windows.exe | C:\Users\admin\AppData\Local\Temp\nsk6FBA.tmp\ns7615.tmp | executable | |
MD5:08E9796CA20C5FC5076E3AC05FB5709A | SHA256:8165C7AEF7DE3D3E0549776535BEDC380AD9BE7BB85E60AD6436F71528D092AF | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\finish.png | image | |
MD5:7AFAF9E0E99FD80FA1023A77524F5587 | SHA256:760B70612BB9BD967C2D15A5133A50CCCE8C0BD46A6464D76875298DCC45DEA0 | |||
| 1876 | frostwire-6.12.0.windows.tmp | C:\Users\admin\AppData\Local\Temp\is-NGEQ7.tmp\prod0 | compressed | |
MD5:56B0D3E1B154AE65682C167D25EC94A6 | SHA256:434BFC9E005A7C8EE249B62F176979F1B4CDE69484DB1683EA07A63E6C1E93DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
48
DNS requests
29
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | frostwire-6.12.0.windows.exe | GET | 404 | 54.172.26.106:80 | http://logs.frostwire.com/ctr/?fwversion=6.12.0.318&id=297058199&state=start&fpc=-1 | unknown | html | 1.00 Kb | unknown |
2232 | frostwire-6.12.0.windows.exe | GET | 404 | 54.172.26.106:80 | http://logs.frostwire.com/ctr/?fwversion=6.12.0.318&id=297058199&state=update&fpc=-1 | unknown | html | 1.00 Kb | unknown |
2112 | avg_antivirus_free_setup.exe | POST | 403 | 34.117.223.223:80 | http://v7event.stats.avast.com/cgi-bin/iavsevents.cgi | unknown | html | 317 b | unknown |
2112 | avg_antivirus_free_setup.exe | POST | 200 | 172.217.165.142:80 | http://www.google-analytics.com/collect | unknown | image | 35 b | unknown |
2112 | avg_antivirus_free_setup.exe | POST | 403 | 34.117.223.223:80 | http://v7event.stats.avast.com/cgi-bin/iavsevents.cgi | unknown | html | 317 b | unknown |
2112 | avg_antivirus_free_setup.exe | POST | 200 | 172.217.165.142:80 | http://www.google-analytics.com/collect | unknown | image | 35 b | unknown |
2468 | icarus.exe | GET | 403 | 34.160.176.28:80 | http://shepherd.avcdn.net/?p_age=0&p_bld=mmm_irs_ppi_902_451_o&p_cpua=x86&p_edi=15&p_icar=1&p_lng=en&p_midex=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&p_ost=0&p_osv=6.1&p_pro=111&p_prod=avg-av&p_ram=3071&p_vbd=8821&p_vep=24&p_ves=1&p_vre=1479&repoid=release& | unknown | html | 295 b | unknown |
2468 | icarus.exe | GET | 403 | 34.160.176.28:80 | http://shepherd.avcdn.net/?p_age=0&p_bld=mmm_irs_ppi_902_451_o&p_cpua=x86&p_edi=15&p_icar=1&p_lng=en&p_midex=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&p_ost=0&p_osv=6.1&p_pro=111&p_prod=avg-av&p_ram=3071&p_vbd=8821&p_vep=24&p_ves=1&p_vre=1479&repoid=release& | unknown | html | 295 b | unknown |
2468 | icarus.exe | GET | 403 | 34.160.176.28:80 | http://shepherd.avcdn.net/?p_age=0&p_bld=mmm_irs_ppi_902_451_o&p_cpua=x86&p_icar=1&p_lng=en&p_midex=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&p_ost=0&p_osv=6.1&p_pro=111&p_prod=avg-av-vps&p_ram=3071&p_vbd=2402&p_vep=24&p_ves=2&p_vre=5051&repoid=release& | unknown | html | 295 b | unknown |
2468 | icarus.exe | GET | 403 | 34.160.176.28:80 | http://shepherd.avcdn.net/?p_age=0&p_bld=mmm_irs_ppi_902_451_o&p_cpua=x86&p_icar=1&p_lng=en&p_midex=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&p_ost=0&p_osv=6.1&p_pro=111&p_prod=avg-av-vps&p_ram=3071&p_vbd=2402&p_vep=24&p_ves=2&p_vre=5051&repoid=release& | unknown | html | 295 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1876 | frostwire-6.12.0.windows.tmp | 18.238.59.155:443 | dhtp8kjtzng5s.cloudfront.net | — | US | unknown |
2232 | frostwire-6.12.0.windows.exe | 54.172.26.106:80 | logs.frostwire.com | AMAZON-AES | US | unknown |
2112 | avg_antivirus_free_setup.exe | 172.217.165.142:80 | www.google-analytics.com | GOOGLE | US | whitelisted |
2112 | avg_antivirus_free_setup.exe | 34.117.223.223:80 | v7event.stats.avast.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
2112 | avg_antivirus_free_setup.exe | 23.62.173.33:443 | honzik.avcdn.net | AKAMAI-AS | US | unknown |
3800 | avg_antivirus_free_online_setup.exe | 23.62.173.33:443 | honzik.avcdn.net | AKAMAI-AS | US | unknown |
3800 | avg_antivirus_free_online_setup.exe | 34.117.223.223:443 | v7event.stats.avast.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dhtp8kjtzng5s.cloudfront.net |
| whitelisted |
logs.frostwire.com |
| unknown |
v7event.stats.avast.com |
| whitelisted |
honzik.avcdn.net |
| unknown |
www.google-analytics.com |
| whitelisted |
analytics.avcdn.net |
| unknown |
shepherd.avcdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | frostwire-6.12.0.windows.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2232 | frostwire-6.12.0.windows.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2232 | frostwire-6.12.0.windows.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
Process | Message |
|---|---|
icarus.exe | [2024-02-24 15:52:39.466] [error ] [avg-av ] [ 2808: 1592] [75044A:2697] Execution of 'class asw::repository::ActionHttp' failed with:'403(193)'
|