| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/21e5fe13-9fec-4091-9bb2-64552788dc08 |
| Verdict: | Suspicious activity |
| Analysis date: | September 15, 2019, 19:09:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9BB8413B48D35F4FAD2F599FC765303 |
| SHA1: | EC62264DFFCE237ADE19C0830371C2C4764C1CAE |
| SHA256: | 57F3FC8963C840CECBCE60BC8D71B6985B75A854E8F9E7EF3FA870E00BE5CF1C |
| SSDEEP: | 49152:czmoK+GcFFyK94CnAle0zY7MzzmnEOM+/3:+moKRcFFviCX0zY7Mz6t |
MALICIOUS
Application was dropped or rewritten from another process
- _iu14D2N.tmp (PID: 3560)
- unins000.exe (PID: 2996)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 3560)
SUSPICIOUS
Reads Windows owner or organization settings
- setup.tmp (PID: 3608)
- _iu14D2N.tmp (PID: 3560)
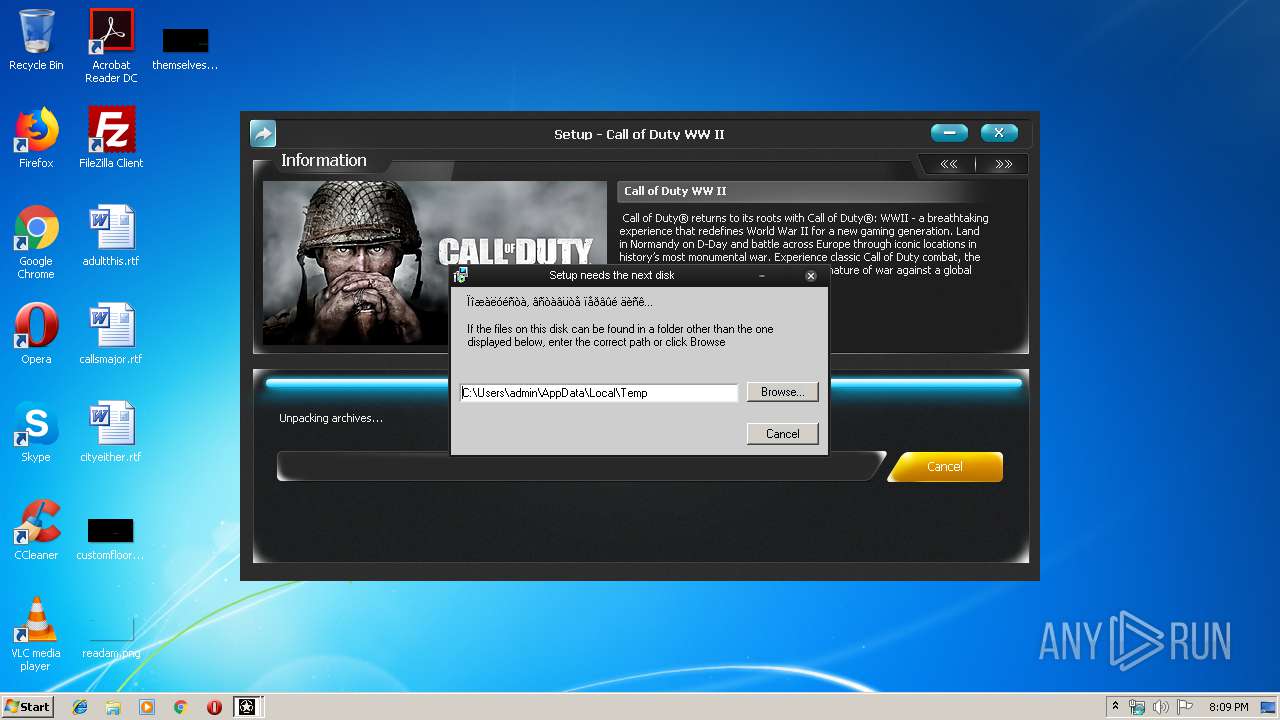
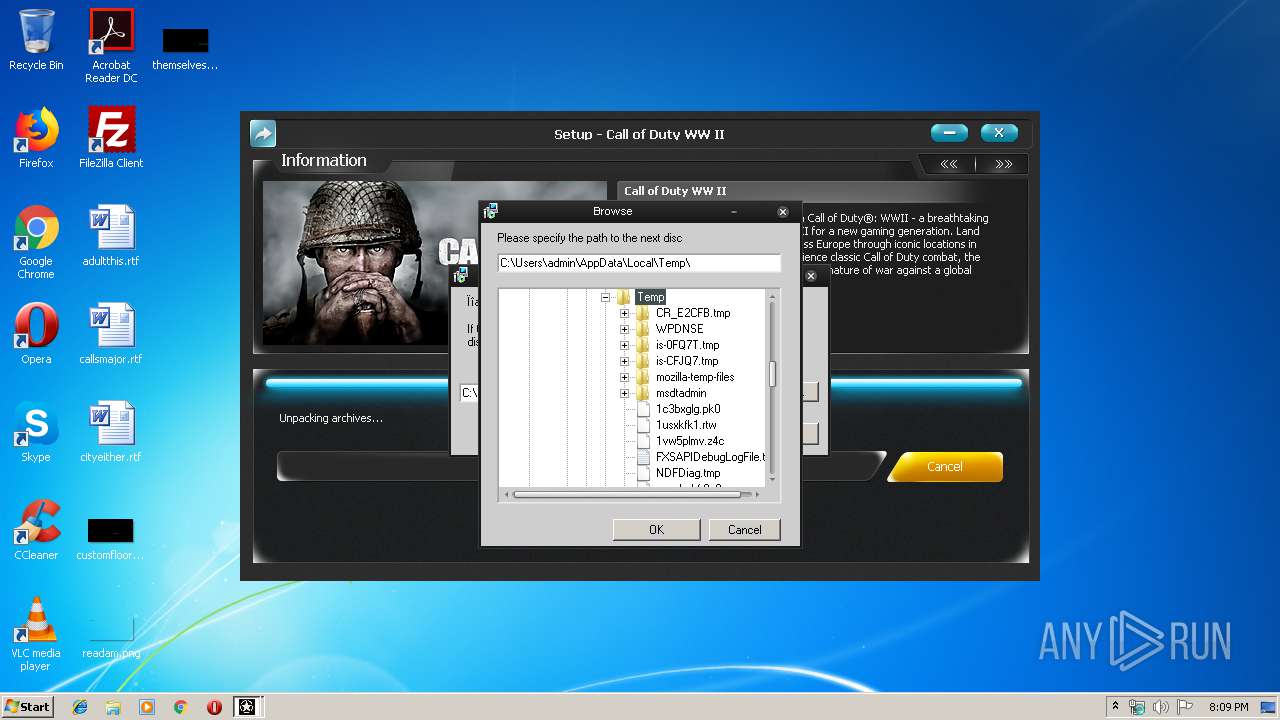
Executable content was dropped or overwritten
- setup.exe (PID: 3148)
- setup.tmp (PID: 3608)
- unins000.exe (PID: 2996)
- _iu14D2N.tmp (PID: 3560)
Reads the Windows organization settings
- setup.tmp (PID: 3608)
- _iu14D2N.tmp (PID: 3560)
Starts application with an unusual extension
- unins000.exe (PID: 2996)
INFO
Loads dropped or rewritten executable
- setup.tmp (PID: 3608)
Application was dropped or rewritten from another process
- setup.tmp (PID: 3608)
Creates a software uninstall entry
- setup.tmp (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 336896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
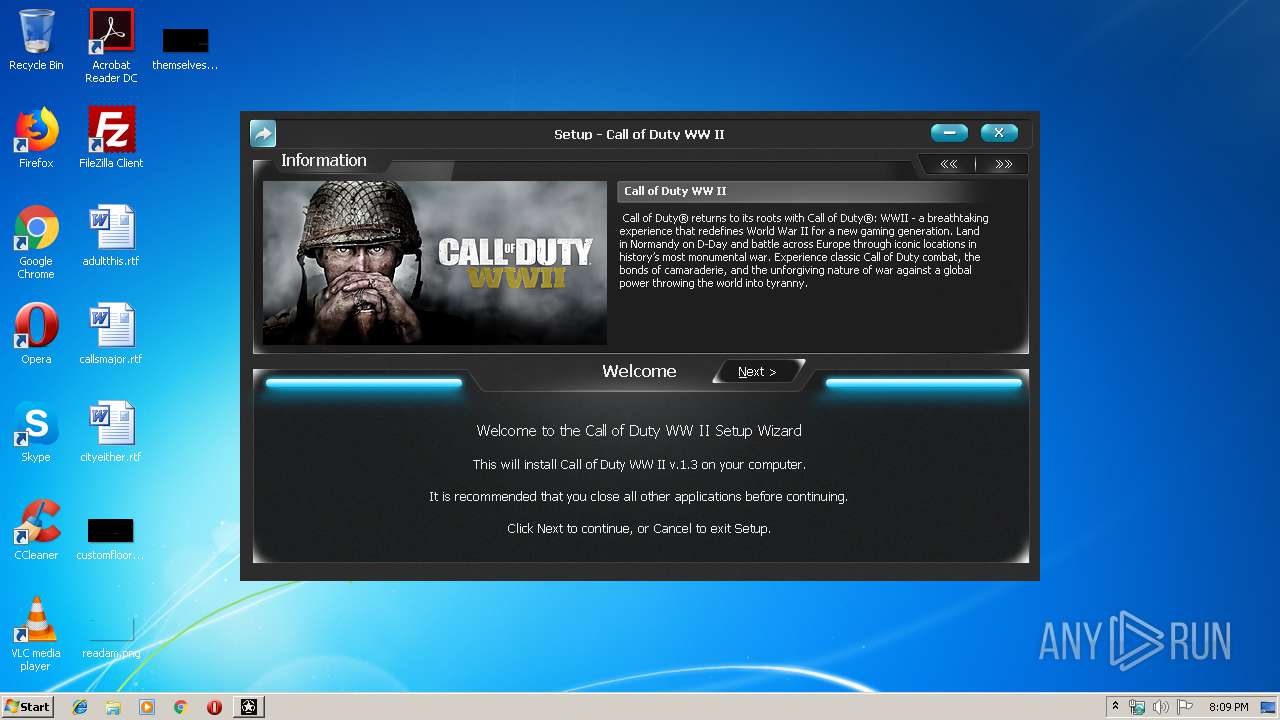
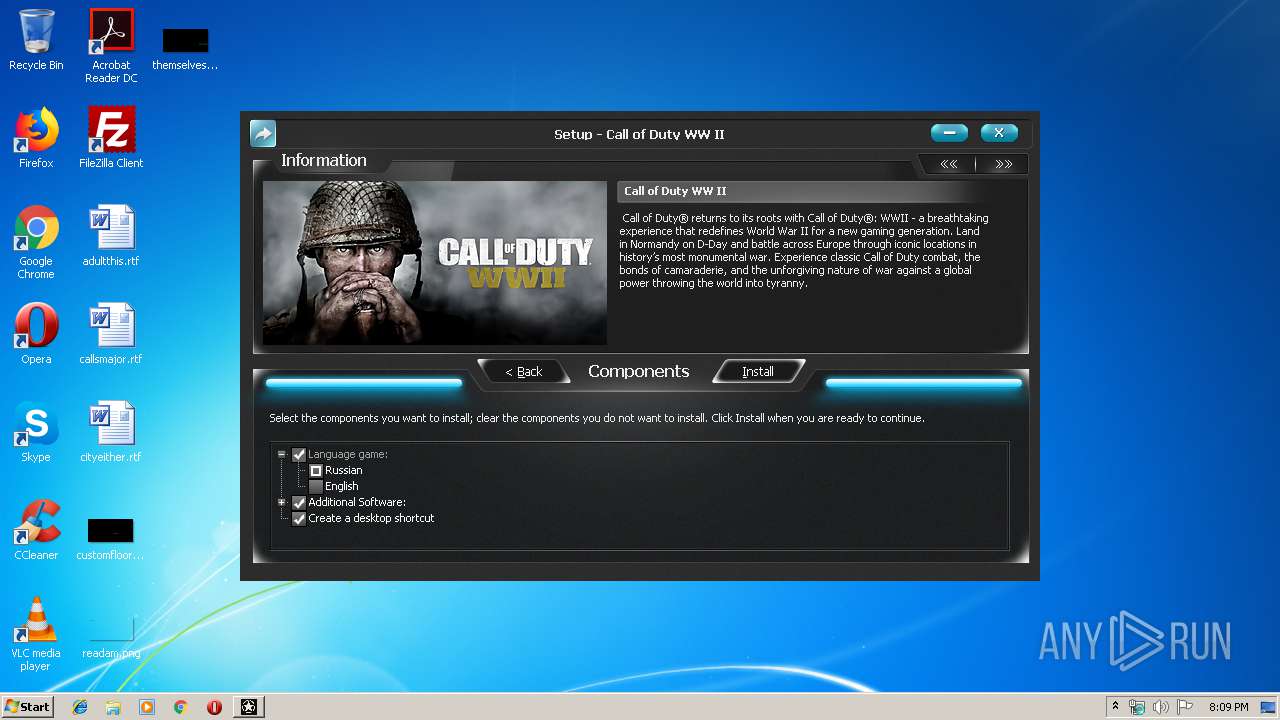
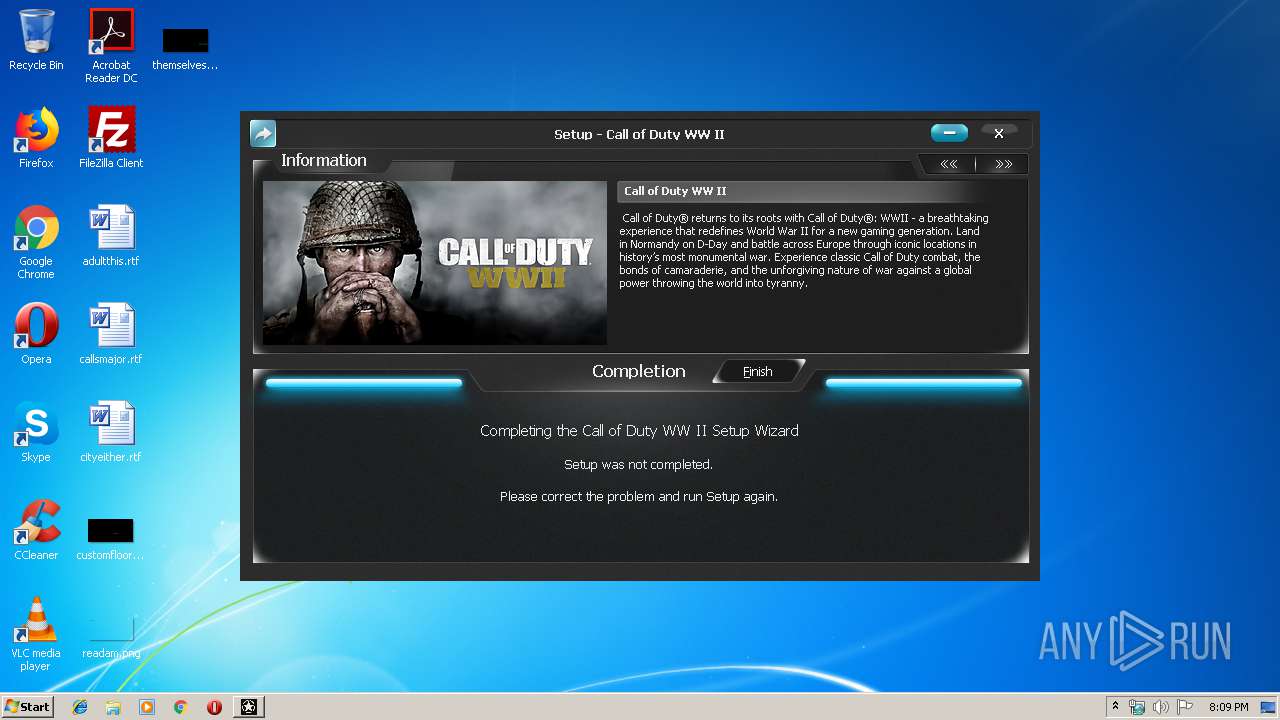
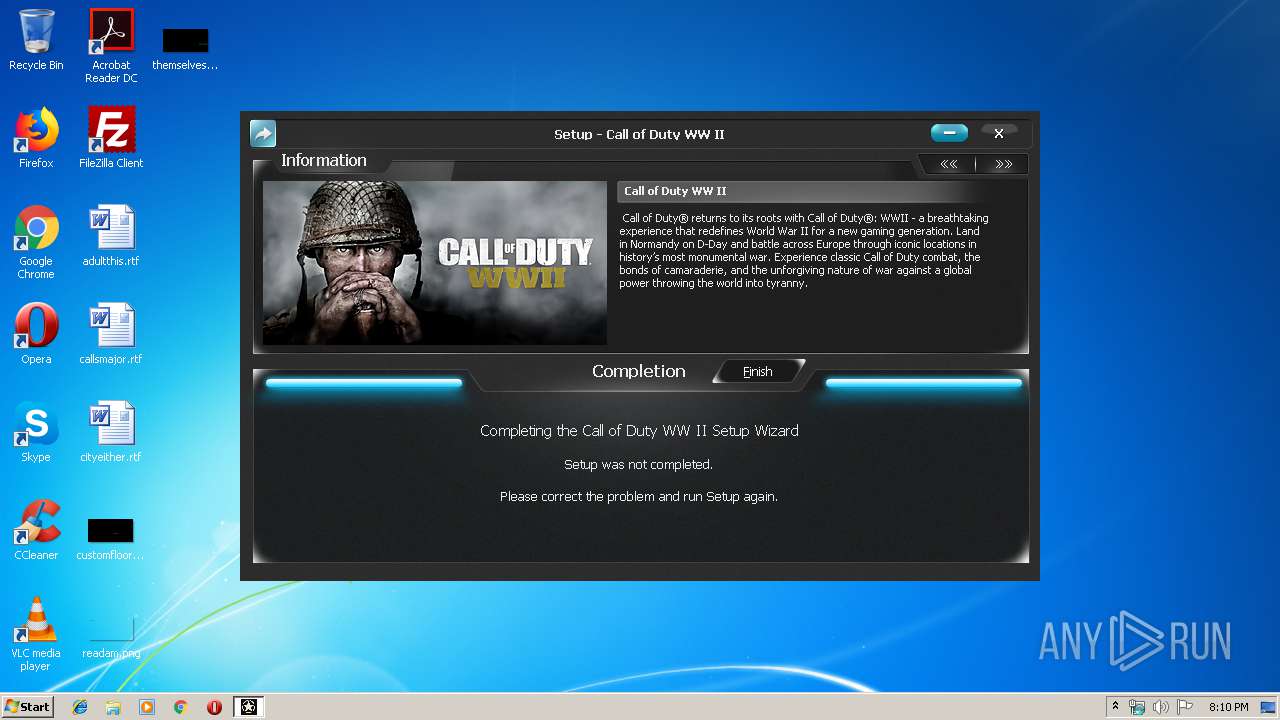
| FileDescription: | Call of Duty WW II Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Call of Duty WW II |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Call of Duty WW II Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Call of Duty WW II |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x00050228 | 0x00050400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.88697 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06505 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.62462 | 12840 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.57924 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.56199 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 3.13038 | 196 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2996 | "C:\Games\Call of Duty WW II\unins000.exe" /VERYSILENT | C:\Games\Call of Duty WW II\unins000.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Call of Duty WW II Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3148 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Call of Duty WW II Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3560 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Games\Call of Duty WW II\unins000.exe" /FIRSTPHASEWND=$20180 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
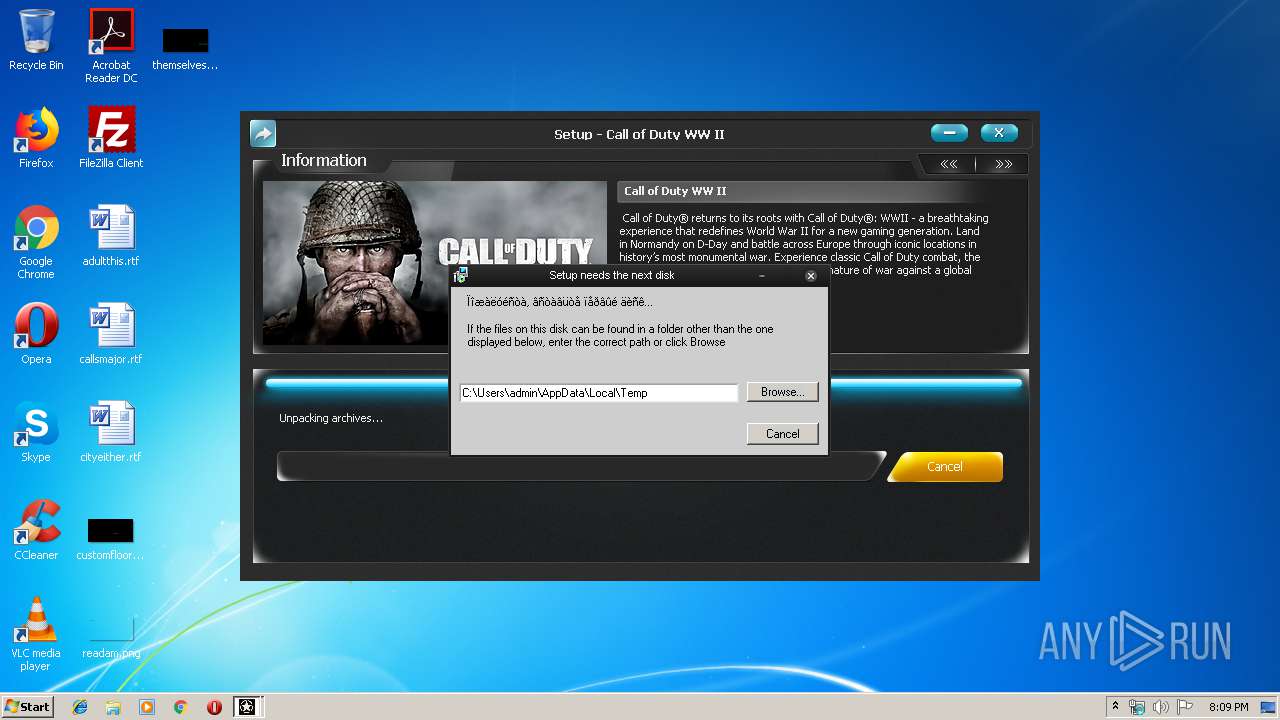
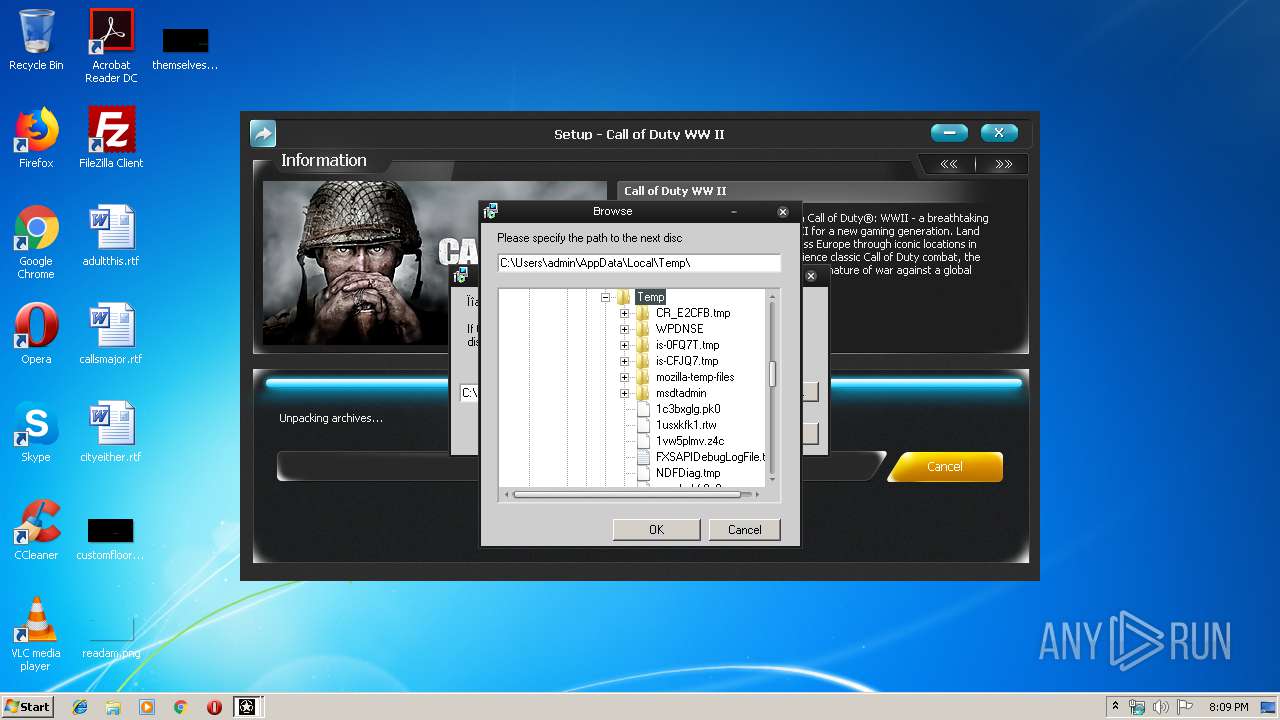
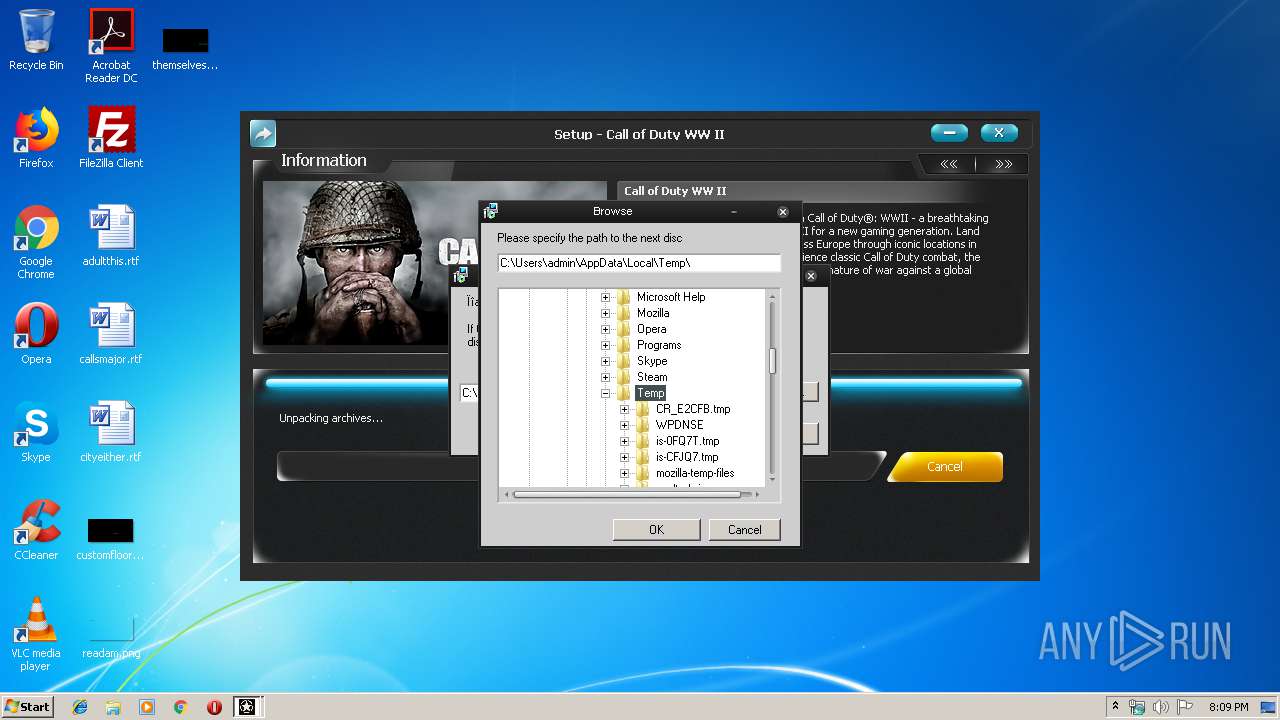
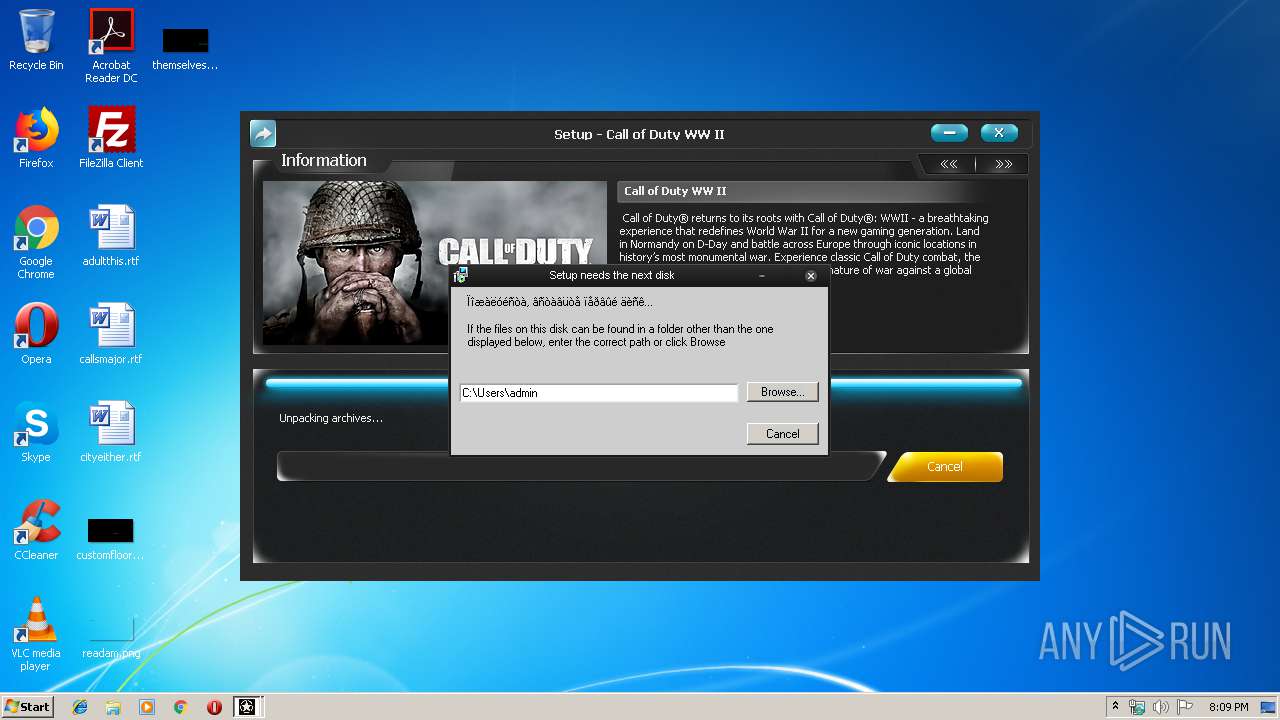
| 3608 | "C:\Users\admin\AppData\Local\Temp\is-CFJQ7.tmp\setup.tmp" /SL5="$30134,1848337,423936,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-CFJQ7.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 3221225547 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
428
Read events
399
Write events
24
Delete events
5
Modification events
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180E00003407AF10F96BD501 | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E683FF10A004CDFF35A76D59830CFB25D0A5CE41881D94394574A4A342BA4CB0 | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2996) unins000.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | |||
| (PID) Process: | (3560) _iu14D2N.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Call of Duty WW II_is1 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Call of Duty WW II_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Call of Duty WW II_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Games\Call of Duty WW II | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Call of Duty WW II_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Games\Call of Duty WW II\ | |||
| (PID) Process: | (3608) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Call of Duty WW II_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: by.xatab | |||
Executable files
14
Suspicious files
0
Text files
11
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | setup.tmp | C:\Games\Call of Duty WW II\is-T36M1.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\WizImg3.bmp | image | |
MD5:— | SHA256:— | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\WizImg2.bmp | image | |
MD5:— | SHA256:— | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\records.inf | text | |
MD5:— | SHA256:— | |||
| 3608 | setup.tmp | C:\Games\Call of Duty WW II\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 3560 | _iu14D2N.tmp | C:\Games\Call of Duty WW II\unins000.dat | — | |
MD5:— | SHA256:— | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\b2p.dll | executable | |
MD5:AB35386487B343E3E82DBD2671FF9DAB | SHA256:C3729545522FCFF70DB61046C0EFD962DF047D40E3B5CCD2272866540FC872B2 | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\botva2.dll | executable | |
MD5:67965A5957A61867D661F05AE1F4773E | SHA256:450B9B0BA25BF068AFBC2B23D252585A19E282939BF38326384EA9112DFD0105 | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\facompress.dll | executable | |
MD5:FB5ECB3F135465AC61A78CA3C177485C | SHA256:148FA9A255BFFF3F7D8A74F25394944F20611AF31F26EF9700CBC0EDC19A3483 | |||
| 3608 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0FQ7T.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report