| File name: | JEk8Z6QFD7pxNkiPM0vuR4jQQrU4Pk2x3N3lVuYEZWU-PU0jj_3_reTBxV6PwRNPGmsttF6iXrUYAMoGPL_hoVvU9xmHgJ7jbdmVh99ySlGMn-sRLOMjVz1EbC36wuhK4mYQJUHR8IyMXREgXUXuFHYa4WmCQfXXx9XCqSKXzBrX0dWXkT3qlL3wFtRnncm1PJs_dPvBIfpRd3J2XutpWSwux84lb6v8Asz4eObLV0DXsv-Puio6FBzknBQzFLMp3W9lGrvEqcFxb0y7duvRUa36DVUvjYB1zMRPU4tLttVRokcxNk8_4oZzZ3g31vhOAxjkfRr3E3CbcDFOcpn7Wkpa7YL0U4xivtwgvOz7elIZn2O8aI3Nv_DhoNGTAR9R.exe |
| Full analysis: | https://app.any.run/tasks/2d89b839-e379-4f05-9e15-3ea7ab236690 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2019, 19:43:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0E64E8ACBC688D2860A252642A94F462 |
| SHA1: | EFF8F9EA7FC477CA5C44191B5534CE4CCBF6DB4B |
| SHA256: | 57E07BAFFAF9CD9108E7399080237B5CCD529165C3CBA4B1D1C49E58ADE80A0D |
| SSDEEP: | 49152:TfrjbGmiMehbTDgLzii91RV2yd1njKDlres/UuBbN43Rldc6:TfrjbLipWii/RV26Ts/XN23Rldc6 |
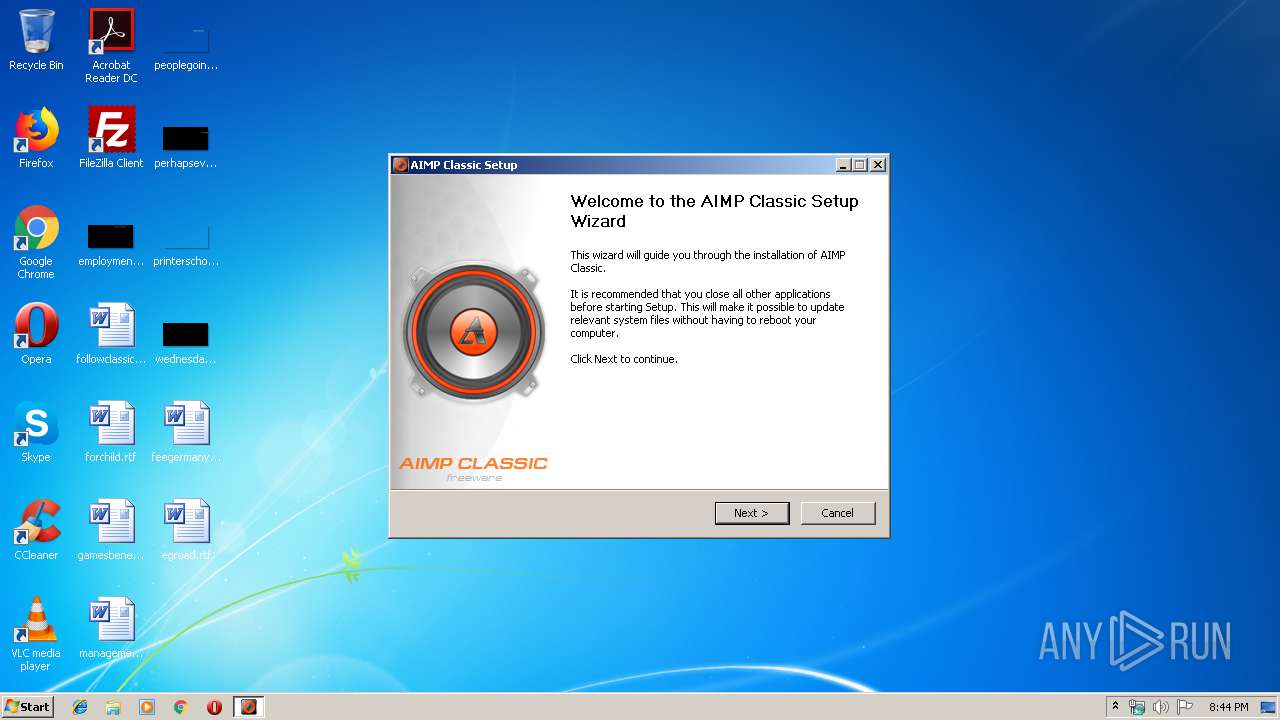
MALICIOUS
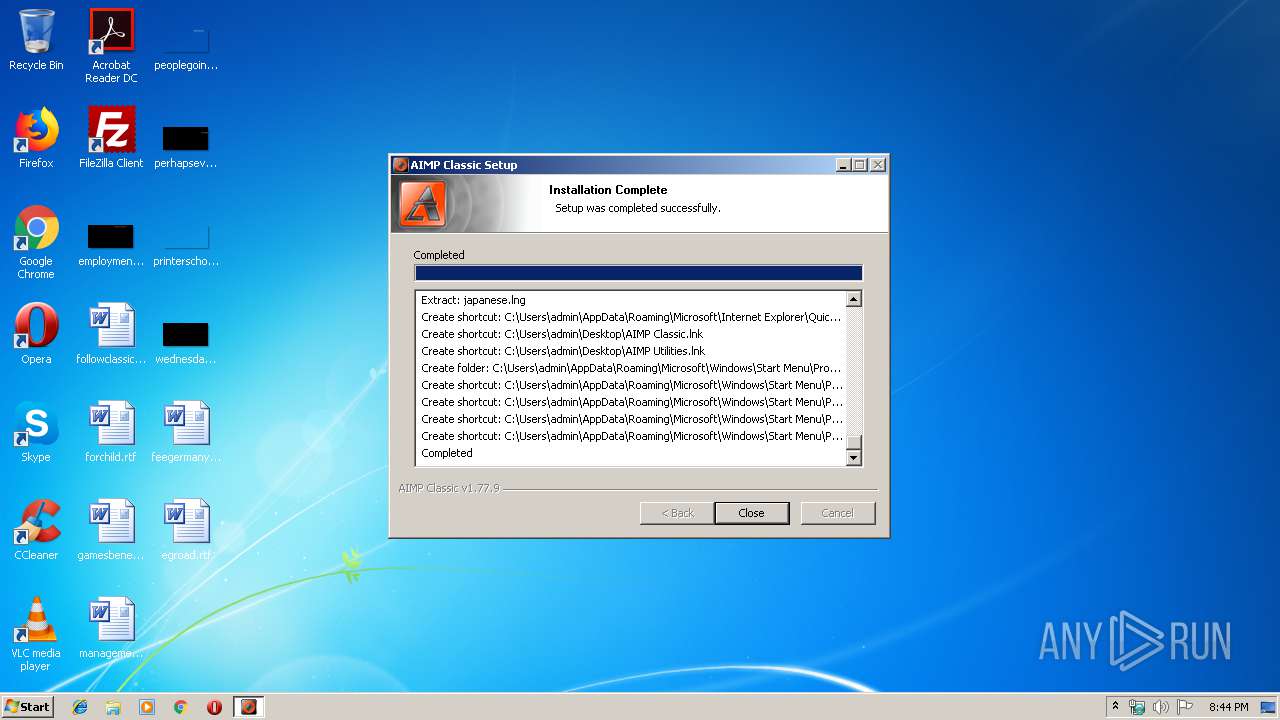
Loads dropped or rewritten executable
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
- cAIMP.exe (PID: 2860)
Application was dropped or rewritten from another process
- cAIMP.exe (PID: 2860)
SUSPICIOUS
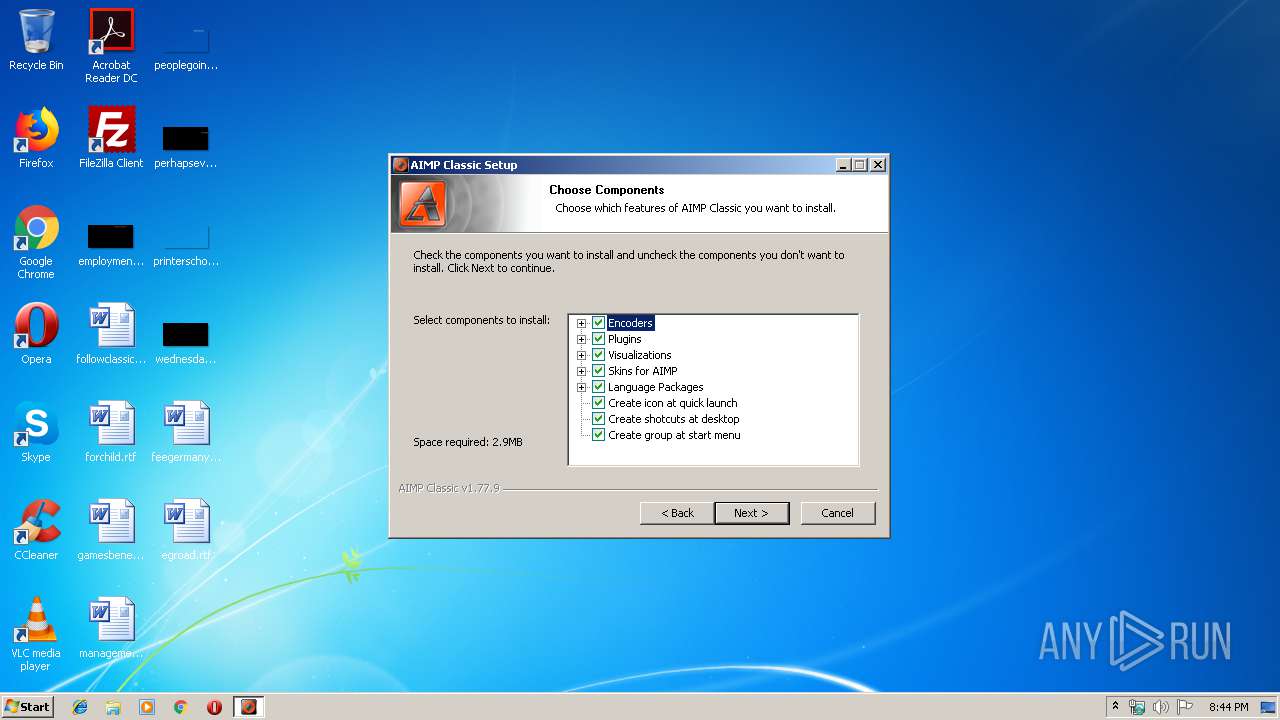
Executable content was dropped or overwritten
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
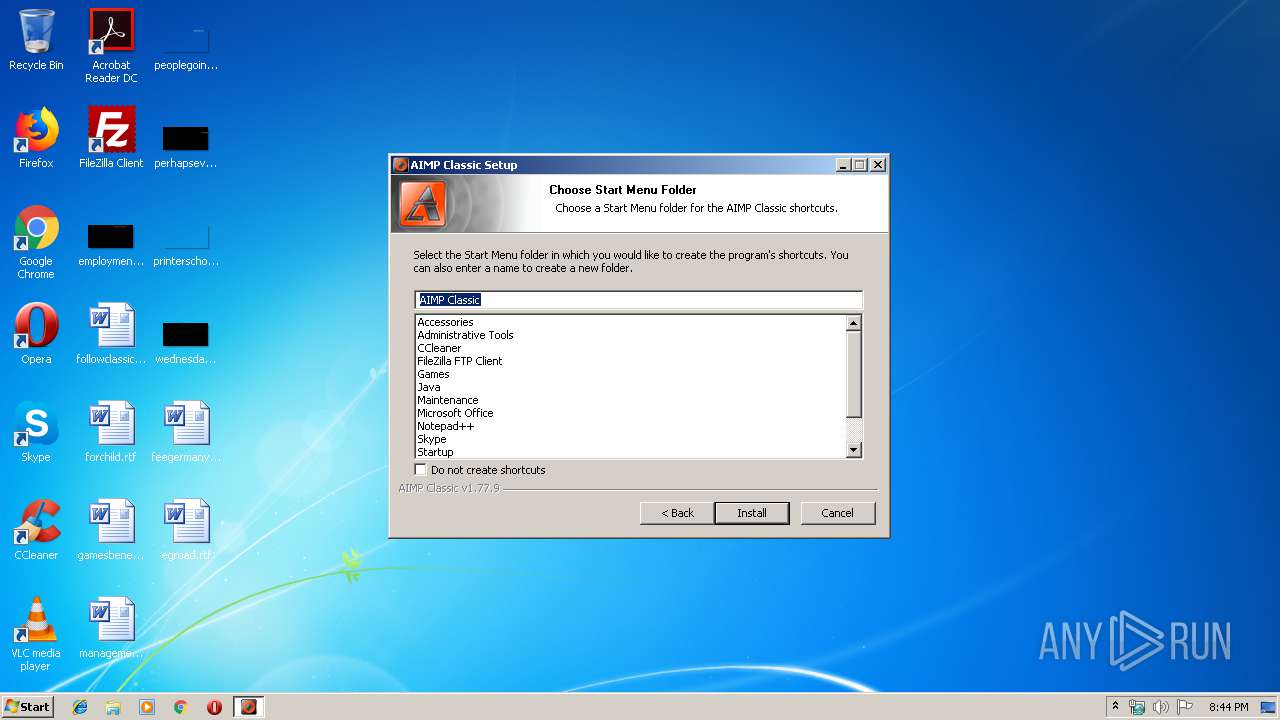
Creates a software uninstall entry
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
Creates COM task schedule object
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
- cAIMP.exe (PID: 2860)
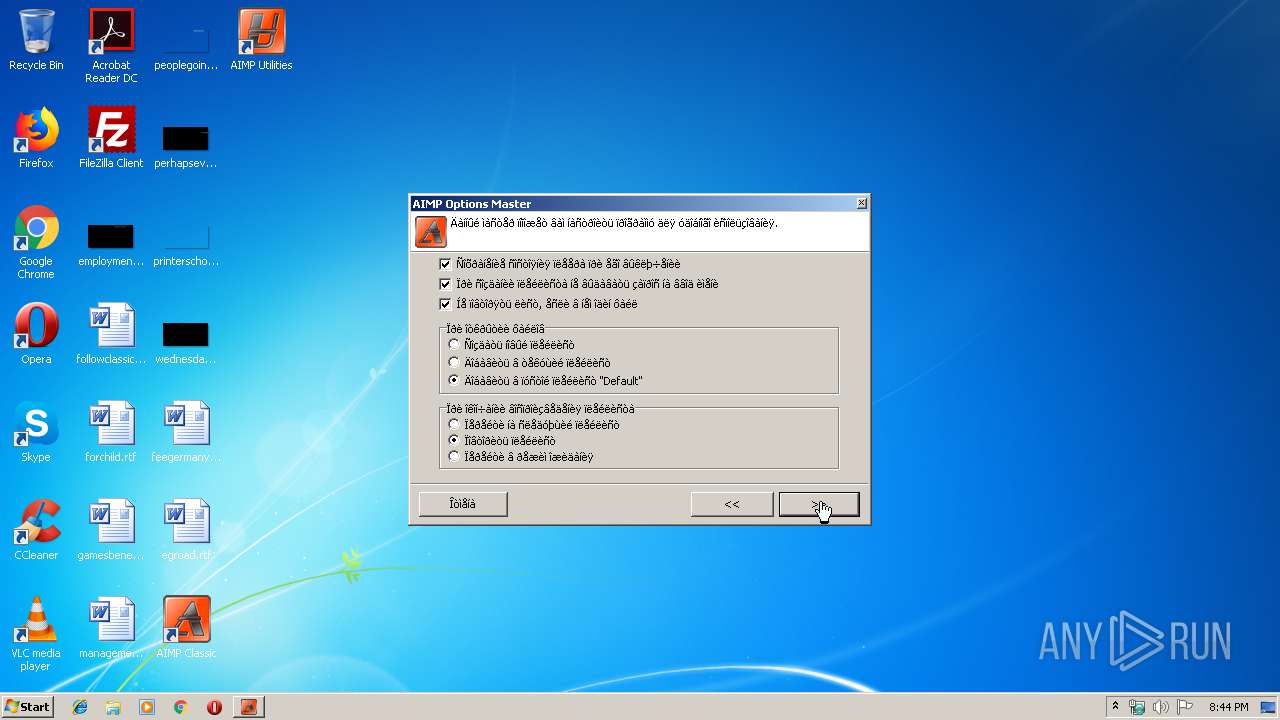
Creates files in the program directory
- cAIMP.exe (PID: 2860)
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
Creates files in the user directory
- 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe (PID: 2552)
INFO
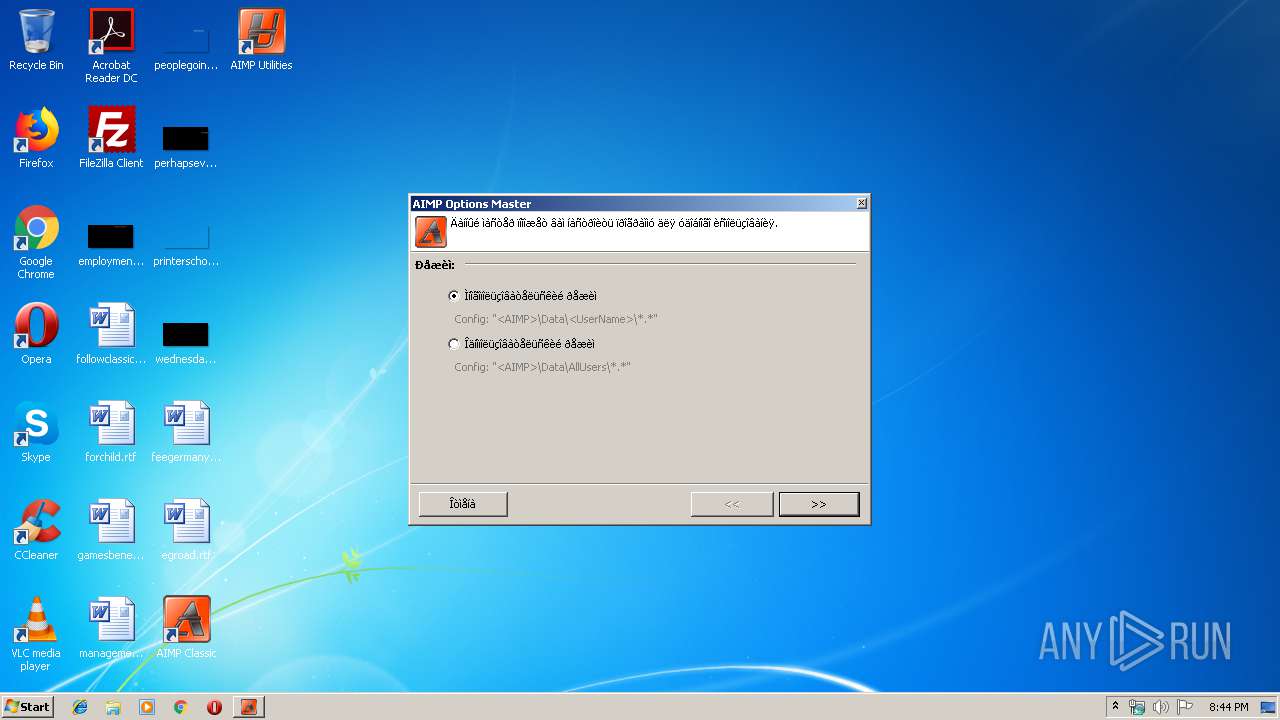
Manual execution by user
- cAIMP.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:06:08 23:48:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x32fa |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
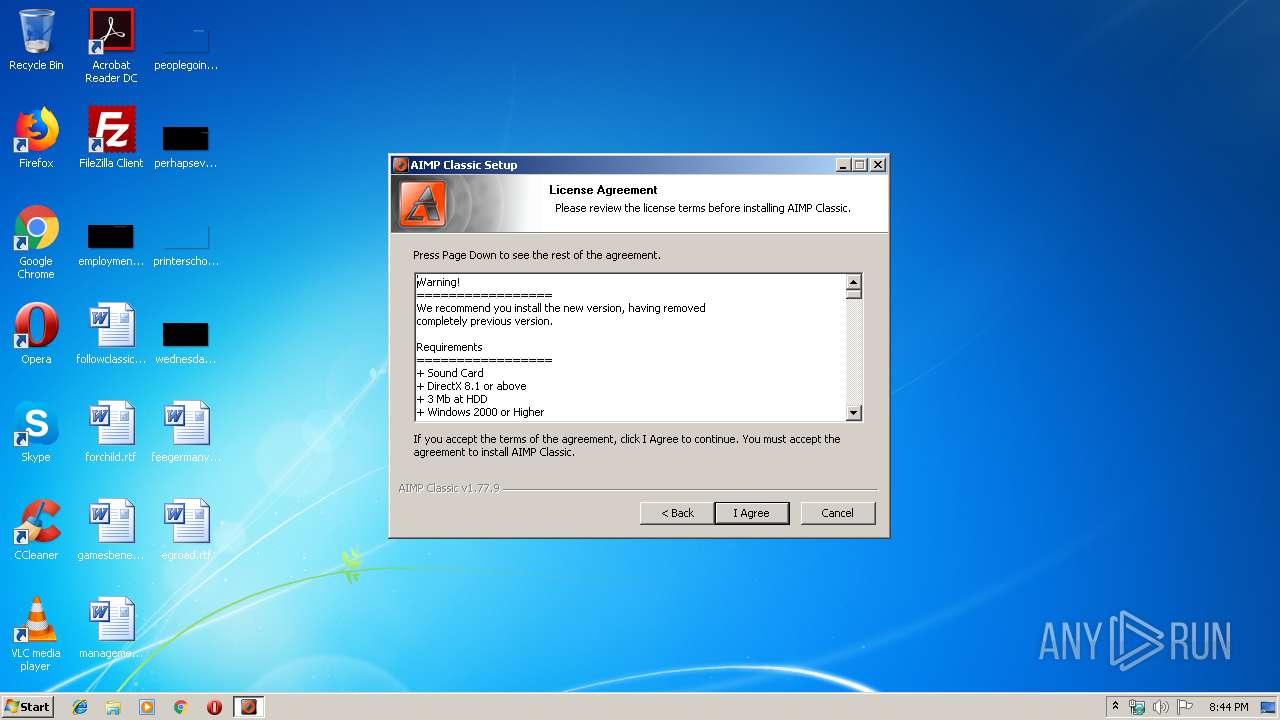
| FileVersionNumber: | 1.77.9.0 |
| ProductVersionNumber: | 1.77.9.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | AIMP DevTeam |
| FileDescription: | AIMP Classic |
| FileVersion: | 1.77.9 |
| LegalCopyright: | © AIMP DevTeam |
| ProductName: | AIMP Classic |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2007 21:48:38 |
| Detected languages: |
|
| CompanyName: | AIMP DevTeam |
| FileDescription: | AIMP Classic |
| FileVersion: | 1.77.9 |
| LegalCopyright: | © AIMP DevTeam |
| ProductName: | AIMP Classic |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Jun-2007 21:48:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000059AC | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45808 |
.rdata | 0x00007000 | 0x0000117A | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17514 |
.data | 0x00009000 | 0x0001AFD8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98111 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000078D8 | 0x00007A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.01323 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10517 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.88511 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.06674 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 6.00121 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.03747 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 6.44928 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.24987 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 6.47061 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 6.45009 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
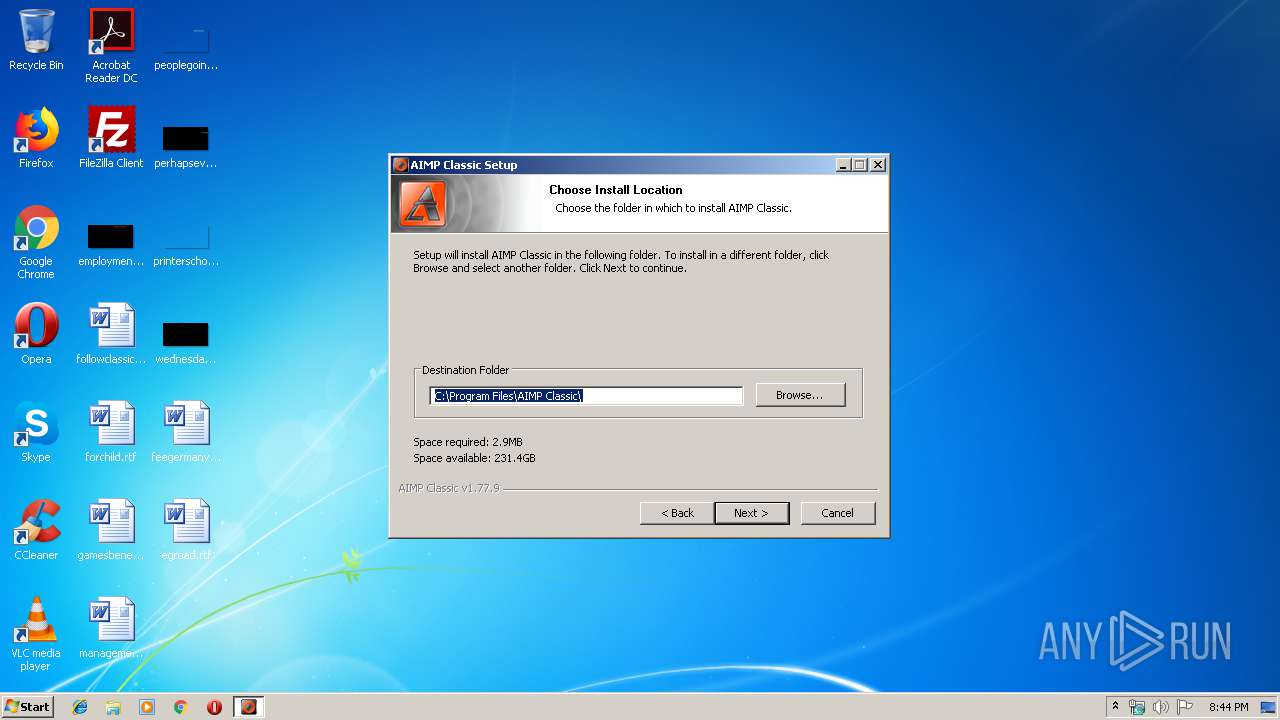
| 1828 | "C:\Users\admin\AppData\Local\Temp\997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe" | C:\Users\admin\AppData\Local\Temp\997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | — | explorer.exe | |||||||||||
User: admin Company: AIMP DevTeam Integrity Level: MEDIUM Description: AIMP Classic Exit code: 3221226540 Version: 1.77.9 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Temp\997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe" | C:\Users\admin\AppData\Local\Temp\997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | explorer.exe | ||||||||||||
User: admin Company: AIMP DevTeam Integrity Level: HIGH Description: AIMP Classic Exit code: 0 Version: 1.77.9 Modules
| |||||||||||||||
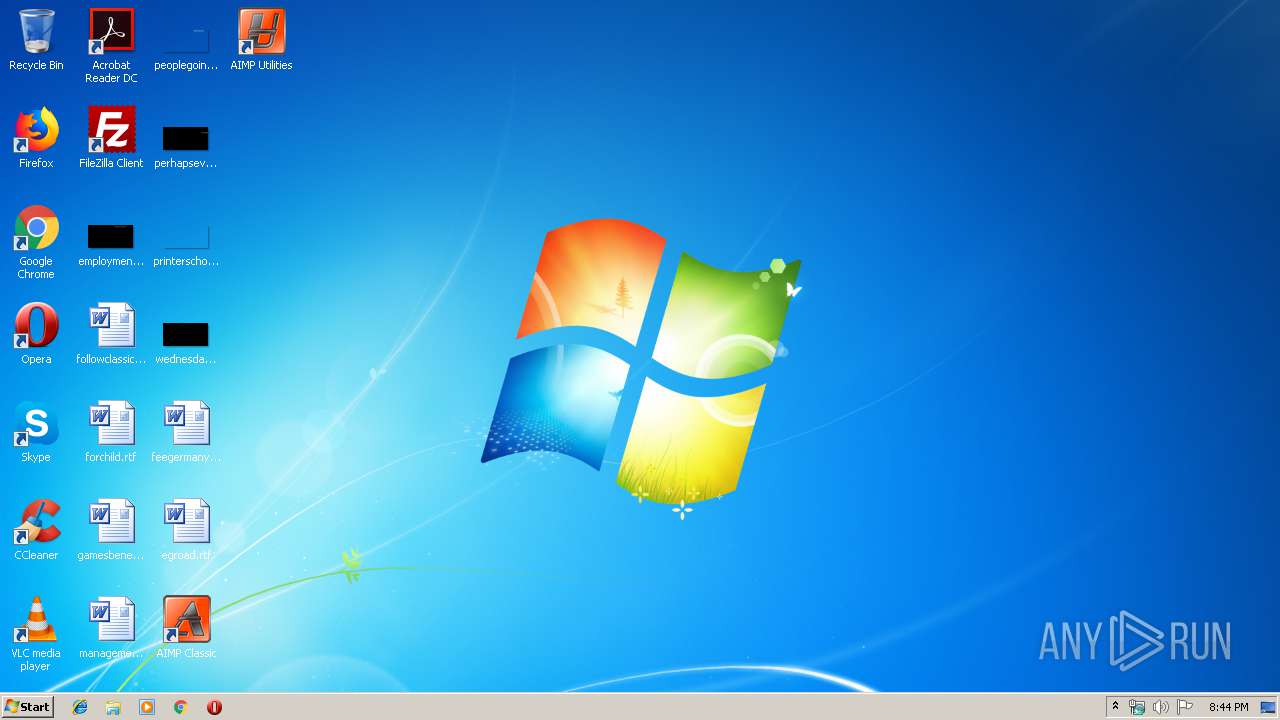
| 2860 | "C:\Program Files\AIMP Classic\cAIMP.exe" | C:\Program Files\AIMP Classic\cAIMP.exe | — | explorer.exe | |||||||||||
User: admin Company: AIMP DevTeam Integrity Level: MEDIUM Description: AIMP Classic Exit code: 0 Version: 1.77.9.0 Modules
| |||||||||||||||
Total events
451
Read events
405
Write events
34
Delete events
12
Modification events
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{7CC1B085-B763-4F68-8D15-4C454D202ECA} |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{7CC1B085-B763-4F68-8D15-4C454D202ECA}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\PROGRA~1\AIMPCL~1\System\AIMP_S~1.DLL | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{7CC1B085-B763-4F68-8D15-4C454D202ECA}\InprocServer32 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{7CC1B085-B763-4F68-8D15-4C454D202ECA} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{1F77B17B-F531-44DB-ACA4-76ABB5010A28} |
| Operation: | write | Name: | |
Value: AIMP Classic Shell | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{1F77B17B-F531-44DB-ACA4-76ABB5010A28}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\PROGRA~1\AIMPCL~1\System\AIMP_S~1.DLL | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\aimp_shell.ContextMenu |
| Operation: | write | Name: | |
Value: AIMP Classic Shell | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\aimp_shell.ContextMenu\Clsid |
| Operation: | write | Name: | |
Value: {1F77B17B-F531-44DB-ACA4-76ABB5010A28} | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{1F77B17B-F531-44DB-ACA4-76ABB5010A28}\ProgID |
| Operation: | write | Name: | |
Value: aimp_shell.ContextMenu | |||
| (PID) Process: | (2552) 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shellex\ContextMenuHandlers\AIMPClassic |
| Operation: | write | Name: | |
Value: {1F77B17B-F531-44DB-ACA4-76ABB5010A28} | |||
Executable files
28
Suspicious files
0
Text files
38
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
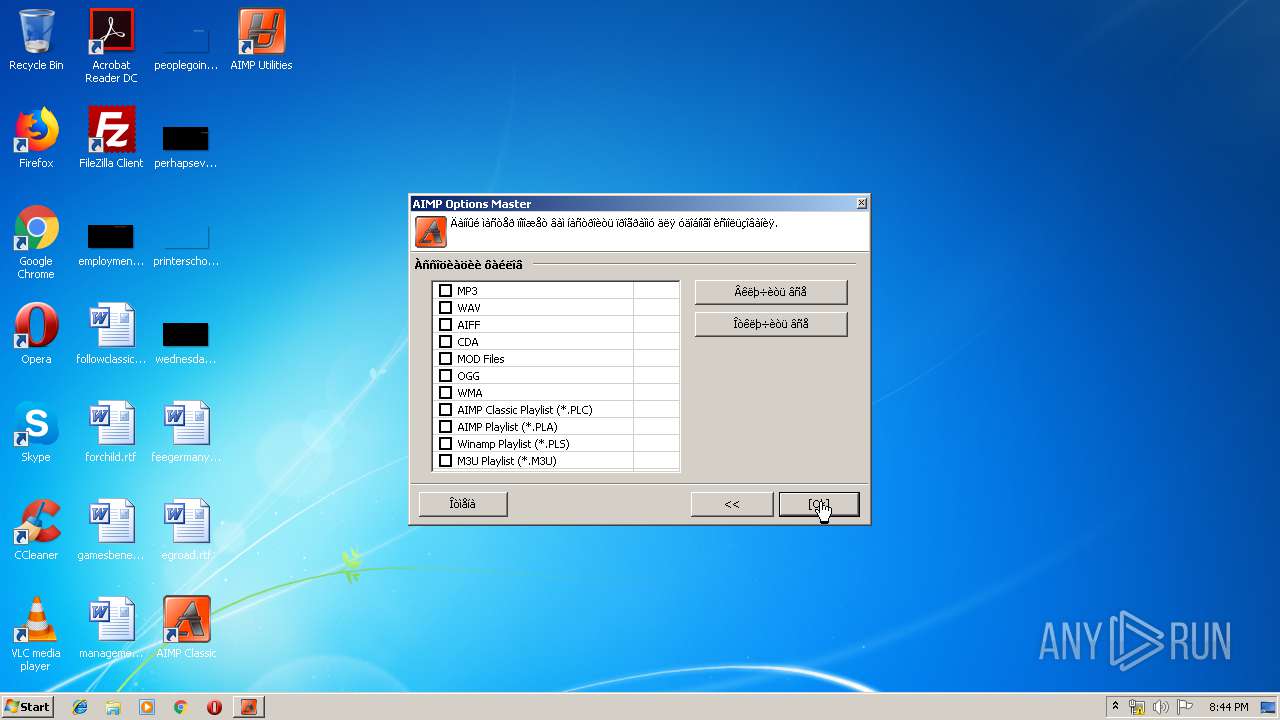
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Program Files\AIMP Classic\cAIMP.exe | executable | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Users\admin\AppData\Local\Temp\nsx6B79.tmp\LangDLL.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Users\admin\AppData\Local\Temp\nsx6B79.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
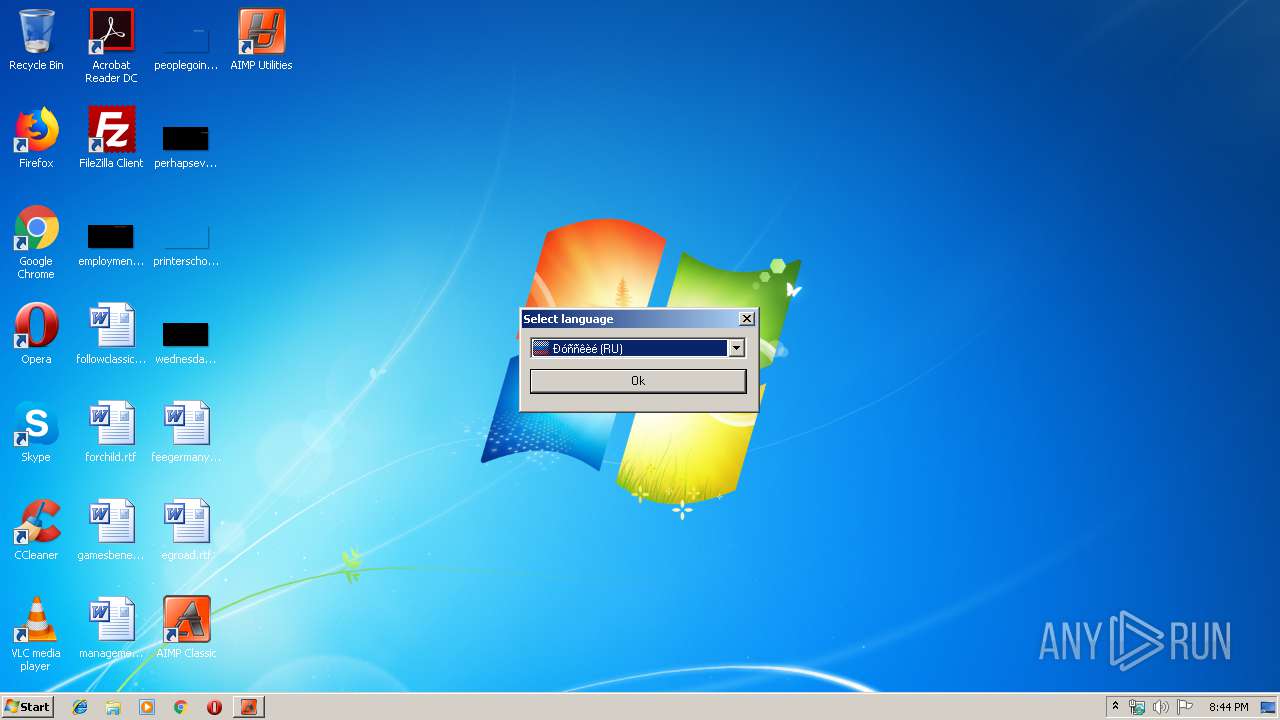
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Program Files\AIMP Classic\Langs\russian.lng | text | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Program Files\AIMP Classic\AIMP.chm | chm | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Program Files\AIMP Classic\AIMP_Utils.exe | executable | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Users\admin\AppData\Local\Temp\nsx6B79.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Users\admin\AppData\Local\Temp\nsx6B79.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Users\admin\AppData\Local\Temp\nsx6B79.tmp\StartMenu.dll | executable | |
MD5:E2A32B7677BC80F6E71E42EC5A2753CC | SHA256:547C8EDB38BF227AFE084562F9FE6E82D13AB17650ADF3A3DD5460AEA928E9EF | |||
| 2552 | 997b32e0-7a29-4e9e-a6a9-2d4b8d8e7047.exe | C:\Program Files\AIMP Classic\System\bass.dll | executable | |
MD5:048E4659465B2F39511CF2E81A7E5A3B | SHA256:FDA6A046CCAA6BBB1A5F7C75E9FF7D936AAF841D1FBCED495141604DCAC081A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report