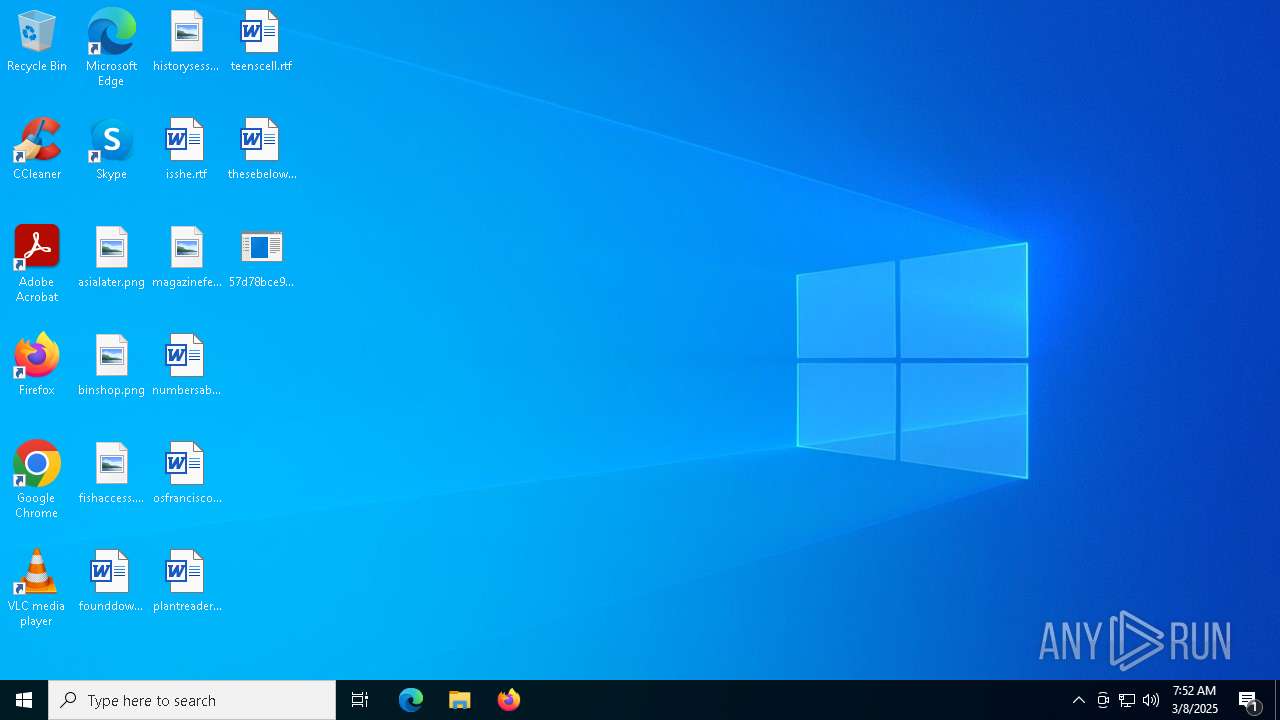
| File name: | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe |
| Full analysis: | https://app.any.run/tasks/240cf4f2-c4ed-4c71-9006-f69555841715 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2025, 07:52:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | A6258362E7CE0F27DC1CE085E891E2A0 |
| SHA1: | 0D6AEFAD6648DFB7AC101D4C1D287B93107B5A9B |
| SHA256: | 57D78BCE936C22B62291E2B13868B7513E174EEDE90DDB40A0D8D5609D041E78 |
| SSDEEP: | 98304:OnxU6hehLyAfvs6b0uWTCVO0qSg8aUsL8GYdCY6J2UGFnlx4bo53ancWE2kHL61X:CRuL0 |
MALICIOUS
Changes the autorun value in the registry
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
UAC/LUA settings modification
- powershell.exe (PID: 8152)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 5416)
SUSPICIOUS
Application launched itself
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
Reads security settings of Internet Explorer
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
- ShellExperienceHost.exe (PID: 7440)
Executable content was dropped or overwritten
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
The process creates files with name similar to system file names
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
Starts itself from another location
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
Starts POWERSHELL.EXE for commands execution
- TextInputHost.exe (PID: 8068)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 8152)
There is functionality for taking screenshot (YARA)
- TextInputHost.exe (PID: 8068)
INFO
Checks supported languages
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
- TextInputHost.exe (PID: 8068)
- ShellExperienceHost.exe (PID: 7440)
Reads the machine GUID from the registry
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
- TextInputHost.exe (PID: 8068)
Reads the computer name
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
- TextInputHost.exe (PID: 8068)
- ShellExperienceHost.exe (PID: 7440)
Process checks computer location settings
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7752)
Creates files in the program directory
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
Create files in a temporary directory
- 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe (PID: 7888)
Drops encrypted JS script (Microsoft Script Encoder)
- TextInputHost.exe (PID: 8068)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8152)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8152)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8152)
UPX packer has been detected
- TextInputHost.exe (PID: 8068)
Application based on Golang
- TextInputHost.exe (PID: 8068)
Detects GO elliptic curve encryption (YARA)
- TextInputHost.exe (PID: 8068)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- TextInputHost.exe (PID: 8068)
Found Base64 encoded access to environment variables via PowerShell (YARA)
- TextInputHost.exe (PID: 8068)
Checks proxy server information
- slui.exe (PID: 6668)
Reads the software policy settings
- slui.exe (PID: 6668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 3276800 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 8761344 |
| EntryPoint: | 0xb7acb0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
Total processes
137
Monitored processes
8
Malicious processes
2
Suspicious processes
3
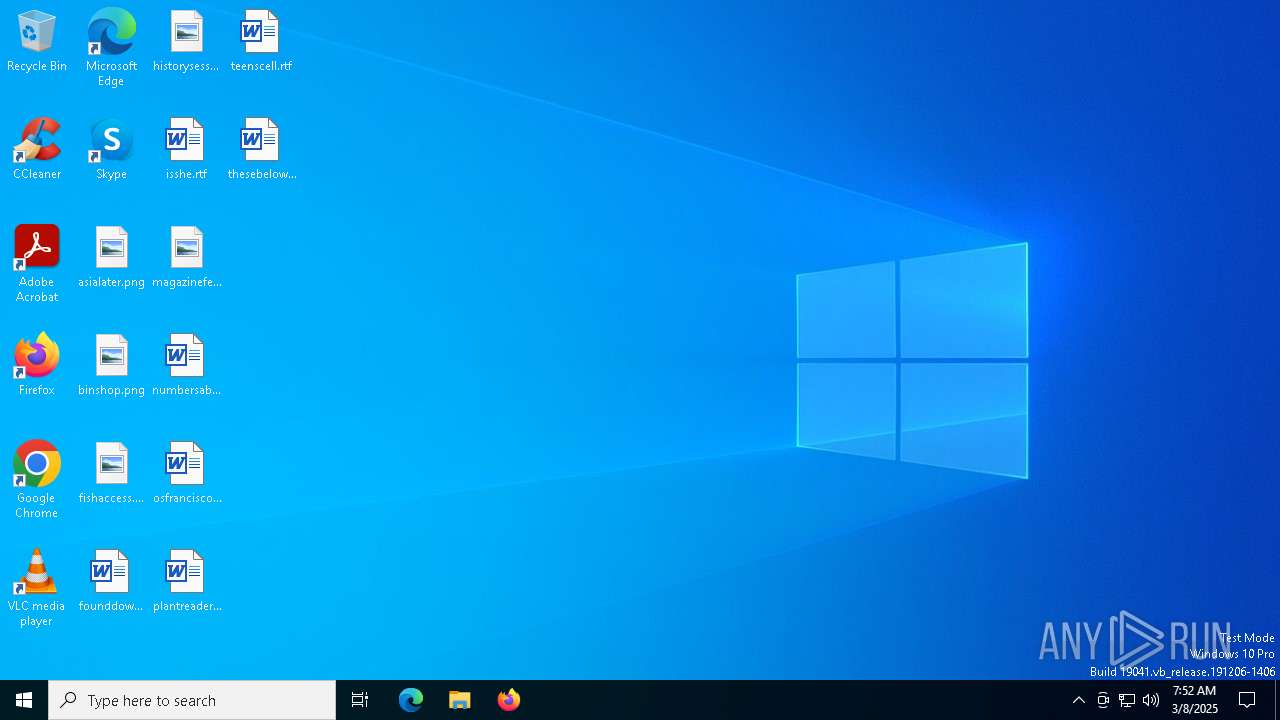
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5416 | "C:\WINDOWS\system32\ReAgentc.exe" /disable | C:\Windows\SysWOW64\ReAgentc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7440 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7752 | "C:\Users\admin\Desktop\57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe" | C:\Users\admin\Desktop\57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 7888 | "C:\Users\admin\Desktop\57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe" | C:\Users\admin\Desktop\57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8068 | C:\Users\admin\AppData\Local\Temp\TextInputHost.exe | C:\Users\admin\AppData\Local\Temp\TextInputHost.exe | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 8152 | powershell.exe | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | TextInputHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 043
Read events
13 968
Write events
15
Delete events
60
Modification events
| (PID) Process: | (7888) 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | uhssvc |
Value: C:\Program Files (x86)\Windows Sidebar\uhssvc.exe | |||
| (PID) Process: | (7888) 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TextInputHost |
Value: C:\Users\admin\AppData\Local\Temp\TextInputHost.exe | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5416) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Boot\Loader.efi | |||
Executable files
2
Suspicious files
2
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5416 | ReAgentc.exe | C:\Windows\SysWOW64\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 7888 | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | C:\Program Files (x86)\Windows Sidebar\uhssvc.exe | executable | |
MD5:A6258362E7CE0F27DC1CE085E891E2A0 | SHA256:57D78BCE936C22B62291E2B13868B7513E174EEDE90DDB40A0D8D5609D041E78 | |||
| 8152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a0nky41w.ky4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7888 | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | C:\Users\admin\AppData\Local\Temp\TextInputHost.exe | executable | |
MD5:A6258362E7CE0F27DC1CE085E891E2A0 | SHA256:57D78BCE936C22B62291E2B13868B7513E174EEDE90DDB40A0D8D5609D041E78 | |||
| 5416 | ReAgentc.exe | \\?\Volume{2f5c5e71-85a9-11eb-90a8-9a9b76358421}\EFI\Microsoft\Recovery\BCD | binary | |
MD5:F10AB4B2BA89A2B5CBEEB79A75FA47E4 | SHA256:7EBC43C9BFEC9107E80B77EC6F8075A5D7EA6A2DE5E6E8BBE32EFF1BC94B8043 | |||
| 5416 | ReAgentc.exe | C:\Windows\SysWOW64\Recovery\ReAgent.xml | xml | |
MD5:7BA1A1AE453E18669377CBD6EB101109 | SHA256:0F7D35D68A237B9C7D6D24C736E9A758761BB0840C113686B81E2CE33928EF65 | |||
| 5416 | ReAgentc.exe | C:\Windows\Logs\ReAgent\ReAgent.log | csv | |
MD5:5EA9493A4B629465E7B376BBF083CD80 | SHA256:888B7C3180F03E83BAB9E799A9FC1501764D3E9EF53C11B7BFB6F2AEDFE79CCC | |||
| 8152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hq4cjvg0.opq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8152 | powershell.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:06FE005B34CAA320F1B8781EEF053F7D | SHA256:36DA4EDB7AAC7C61074636C11334812496E970373802407393D1134C3596B4E9 | |||
| 8152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_okvnm2vy.54d.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
29
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7888 | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | 1.1.1.1:443 | — | — | — | malicious |
7888 | 57d78bce936c22b62291e2b13868b7513e174eede90ddb40a0d8d5609d041e78.exe | 188.114.97.2:443 | — | — | — | unknown |
8068 | TextInputHost.exe | 188.114.96.2:443 | — | — | — | unknown |
8068 | TextInputHost.exe | 1.1.1.1:443 | — | — | — | malicious |
7512 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6668 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |