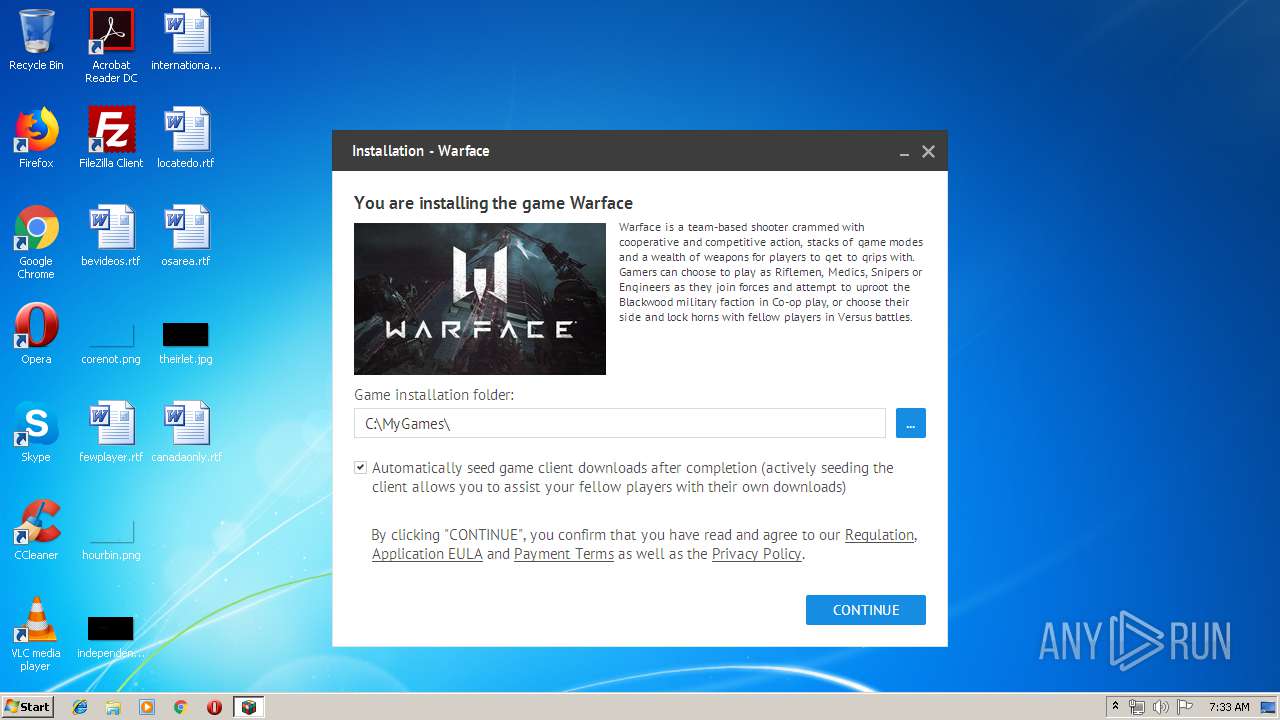
| File name: | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe |
| Full analysis: | https://app.any.run/tasks/9c4afa0c-2a37-446e-aa98-0c40708028c3 |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2019, 06:33:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 837001C0F1118D5F2B3364F71F043D89 |
| SHA1: | D031A4EE37AD7A54B9C8EBEC1CCF45508928EFCF |
| SHA256: | 57D0E6B989602FC0680F092AF9A66AF62D52ED6DE7BEF393265B3E1BAD7F83D9 |
| SSDEEP: | 196608:d155AE7kgT0kq8EKjk7RecAytE8SKfmtObZFW9PYVy5NRWD:d15SE7T/q8xkNeN0mtMPy5NR6 |
MALICIOUS
Application was dropped or rewritten from another process
- GameCenter.exe (PID: 3024)
Loads dropped or rewritten executable
- GameCenter.exe (PID: 3024)
Changes the autorun value in the registry
- GameCenter.exe (PID: 3024)
SUSPICIOUS
Creates files in the user directory
- GameCenter.exe (PID: 3024)
Creates a software uninstall entry
- GameCenter.exe (PID: 3024)
Executable content was dropped or overwritten
- WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe (PID: 3240)
Modifies the open verb of a shell class
- GameCenter.exe (PID: 3024)
Searches for installed software
- GameCenter.exe (PID: 3024)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:16 13:37:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 7057408 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 17649664 |
| EntryPoint: | 0x178f4c0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.1498.49404 |
| ProductVersionNumber: | 4.0.1498.49404 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
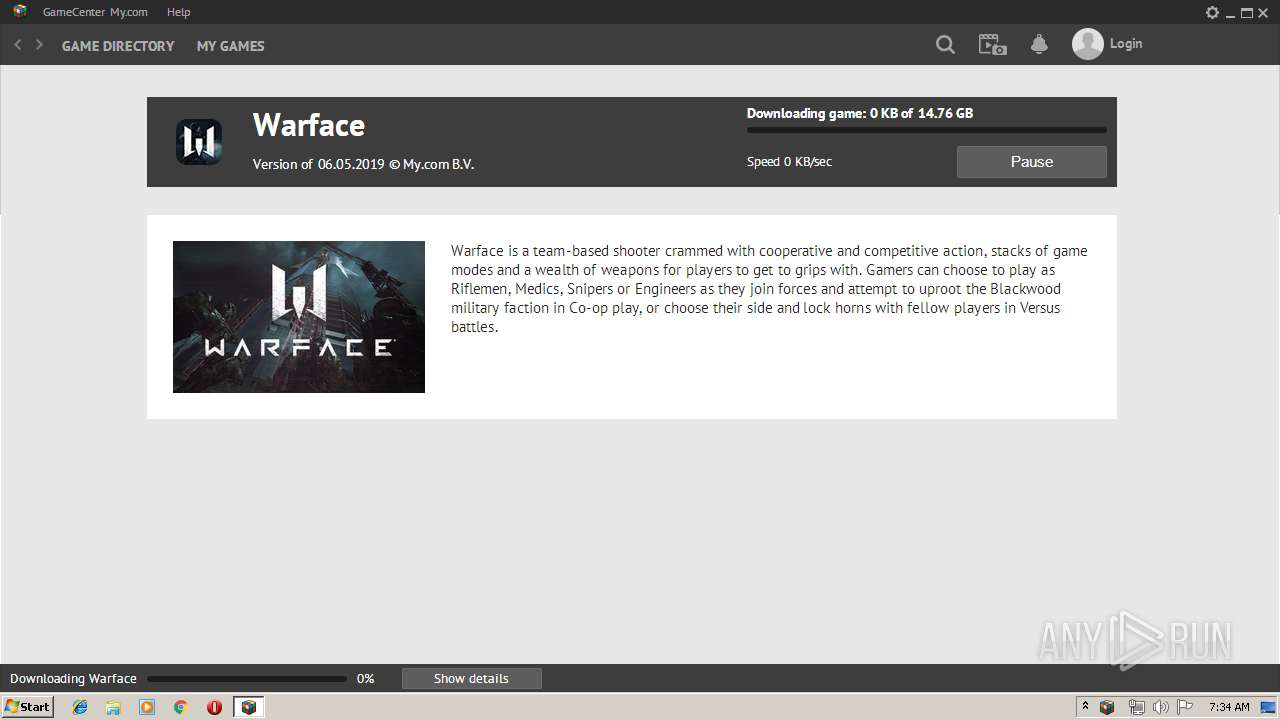
| CompanyName: | MY.COM B.V. |
| FileDescription: | GameCenter |
| FileVersion: | 4.0.1498.49404 |
| ProductVersion: | 4.0.1498.49404 |
| InternalName: | GameCenterInstaller.exe |
| LegalCopyright: | Copyright (C) 2019 MY.COM B.V. |
| LegalTrademarks: | - |
| OriginalFileName: | GameCenter.exe |
| ProductName: | GameCenter |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Apr-2019 11:37:18 |
| Detected languages: |
|
| CompanyName: | MY.COM B.V. |
| FileDescription: | GameCenter |
| FileVersion: | 4.0.1498.49404 |
| ProductVersion: | 4.0.1498.49404 |
| InternalName: | GameCenterInstaller.exe |
| LegalCopyright: | Copyright (C) 2019 MY.COM B.V. |
| LegalTrademarks: | - |
| OriginalFilename: | GameCenter.exe |
| ProductName: | GameCenter |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Apr-2019 11:37:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x010D5000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x010D6000 | 0x006BB000 | 0x006BA200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99997 |
.rsrc | 0x01791000 | 0x00005000 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.04449 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33711 | 1287 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.91183 | 3056 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 7.68353 | 983 | Latin 1 / Western European | English - United States | RT_ICON |
4088 | 7.17796 | 256 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 7.69125 | 752 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 7.76107 | 848 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 7.0054 | 208 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 6.76965 | 160 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 7.73832 | 768 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 7.78479 | 952 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
wininet.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0005F628 |
__dbk_fcall_wrapper | 2 | 0x0000BB00 |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
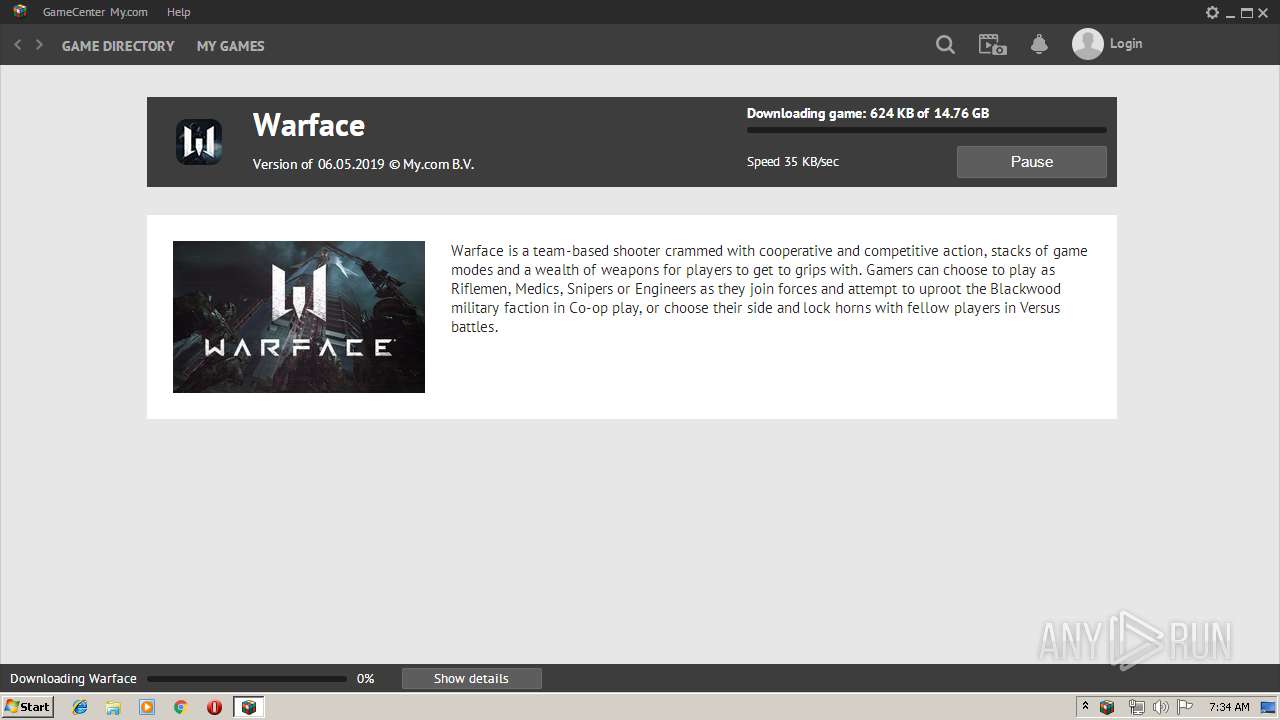
| 3024 | "C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe" -startedbysetup "installer=C:\Users\admin\AppData\Local\Temp\WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe" game=13.2000076 -removeifinstallcanceled | C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe" | C:\Users\admin\AppData\Local\Temp\WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 437
Read events
1 386
Write events
51
Delete events
0
Modification events
| (PID) Process: | (3240) WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3240) WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mycomgames |
| Operation: | write | Name: | |
Value: URL:MyComGames Protocol | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mycomgames |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mycomgames\DefaultIcon |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe",0 | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mycomgames\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe" "%1" | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\ProtocolExecute\mycomgames |
| Operation: | write | Name: | WarnOnOpen |
Value: 0 | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mailrugames |
| Operation: | write | Name: | |
Value: URL:MailRuGames Protocol | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mailrugames |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3024) GameCenter.exe | Key: | HKEY_CLASSES_ROOT\mailrugames\DefaultIcon |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe",0 | |||
Executable files
13
Suspicious files
28
Text files
59
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\writefiletest_3240 | — | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\bigup2.dll | executable | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\gclay.dll | executable | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\main.log | text | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe | executable | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\GCLay64.dll | executable | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\GameIcon13.2000076.ico | image | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe.sig | pi2 | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\HG64.exe | executable | |
MD5:— | SHA256:— | |||
| 3240 | WarfaceMycomLoader_db5a3c477a283ebbd879fe29df9c1fba_.exe | C:\Users\admin\AppData\Local\GameCenter\lightupdate.dll.sig | pi2 | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
107
TCP/UDP connections
4 260
DNS requests
35
Threats
82
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | GameCenter.exe | GET | 200 | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&distrib_id=2000076&type_id=13&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1&event_id=923&ses_cnt=1&l=1&tag=528&cl_ts=1557210833&line=0&srv_resp=0 | RU | — | — | suspicious |
— | — | GET | 200 | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&distrib_id=2000076&type_id=13&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1&event_id=1&ses_cnt=4&l=1&tag=498&tag3=528&cl_ts=1557210842&line=0&ext_info=C%3A\Users\admin\AppData\Local\GameCenter\GameCenter.exe&srv_resp=200 | RU | — | — | suspicious |
3024 | GameCenter.exe | GET | 200 | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&distrib_id=2000076&type_id=13&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1&event_id=541&ses_cnt=2&l=1&cl_ts=1557210840&line=0&srv_resp=200 | RU | — | — | suspicious |
3024 | GameCenter.exe | GET | — | 188.93.63.129:80 | http://pkg.dl.mail.ru/packages/chromeresources17/bin.7z | RU | — | — | suspicious |
3024 | GameCenter.exe | GET | — | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&distrib_id=2000076&type_id=13&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1&event_id=352&ses_cnt=3&l=1&tag=2&cl_ts=1557210842&line=0&mrrs=http%3A%2F%2Fchi.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fchi2.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fchi3.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Flos.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fsea.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fmia.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fmia2.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fmsk.pkg.gc.my.com%2Fpackages%2F%3Bhttp%3A%2F%2Fkr.pkg.gc.my.com%2Fpackages%2F&srv_resp=200 | RU | — | — | suspicious |
3024 | GameCenter.exe | GET | 200 | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1 | RU | — | — | suspicious |
— | — | GET | — | 192.31.179.14:80 | http://p2p.gc.my.com/announce.php?info_hash=%8a%c2Y0%c7%2c%a4%b3%f4%e0%acB%16v%dcw%3d%e7%23%f8&peer_id=-BU12F0-DPI~omOWXh97&port=6881&uploaded=0&downloaded=0&left=16599&corrupt=0&key=0B532B67&event=started&numwant=200&compact=1&no_peer_id=1&supportcrypto=1&redundant=0 | US | — | — | suspicious |
3024 | GameCenter.exe | GET | — | 178.22.88.34:80 | http://stat.gc.my.com/stat.php?&user_id=7974070130954217413&user_id2=15742307191278540529&build_id=1498&revision_id=49404&stand=1&channel_id=35&1l=_1lp%3D1%26_1ld%3D300%26_1lnh%3D1&event_id=900&ses_cnt=6&l=1&tag=625&cl_ts=1557210842&line=0&ext_info=mlresources&srv_resp=200 | RU | — | — | suspicious |
— | — | GET | — | 188.93.63.21:80 | http://p2p.dl.mail.ru/announce.php?info_hash=%d7%b1lO%3f%c81%5d0%a5%e8%ab%c86%96%3f0F%1e7&peer_id=-BU12F0-KWIev7iiS~A*&port=6881&uploaded=0&downloaded=0&left=484081&corrupt=0&key=31F60A19&event=started&numwant=200&compact=1&no_peer_id=1&supportcrypto=1&redundant=0 | RU | — | — | suspicious |
3024 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/ipspec.xml?_c_8710186 | NL | xml | 6.89 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.30.176.134:80 | static.gc.my.com | MRG Hosting B.V. | NL | suspicious |
3024 | GameCenter.exe | 185.30.176.64:443 | authdl.my.com | MRG Hosting B.V. | NL | unknown |
3024 | GameCenter.exe | 67.215.246.10:6881 | router.bittorrent.com | QuadraNet, Inc | US | suspicious |
— | — | 82.221.103.244:6881 | router.utorrent.com | Thor Data Center ehf | IS | suspicious |
— | — | 192.3.31.116:25401 | dht.libtorrent.org | ColoCrossing | US | suspicious |
— | — | 179.98.31.99:34544 | — | TELEFÔNICA BRASIL S.A | BR | unknown |
— | — | 97.112.250.225:6883 | — | Qwest Communications Company, LLC | US | suspicious |
— | — | 185.153.132.35:41921 | — | Lancom Ltd. | RU | unknown |
— | — | 178.22.88.34:80 | stat.gc.my.com | Limited liability company Mail.Ru | RU | suspicious |
— | — | 106.220.182.201:2819 | — | Bharti Airtel Ltd. AS for GPRS Service | IN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
authdl.my.com |
| unknown |
router.utorrent.com |
| whitelisted |
router.bittorrent.com |
| shared |
router.bitcomet.com |
| unknown |
dht.libtorrent.org |
| suspicious |
static.gc.my.com |
| suspicious |
stat.gc.my.com |
| suspicious |
dl.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-aigl6ned.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent transfer |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent transfer |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent transfer |
3024 | GameCenter.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |