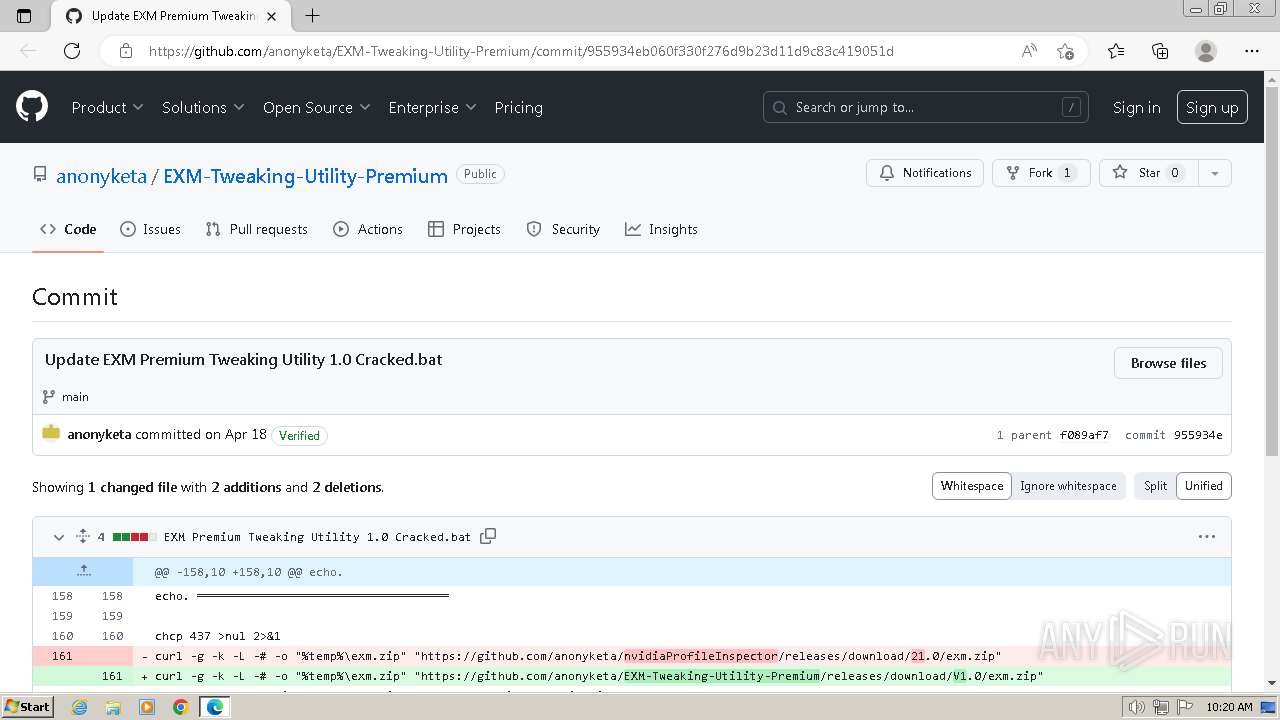
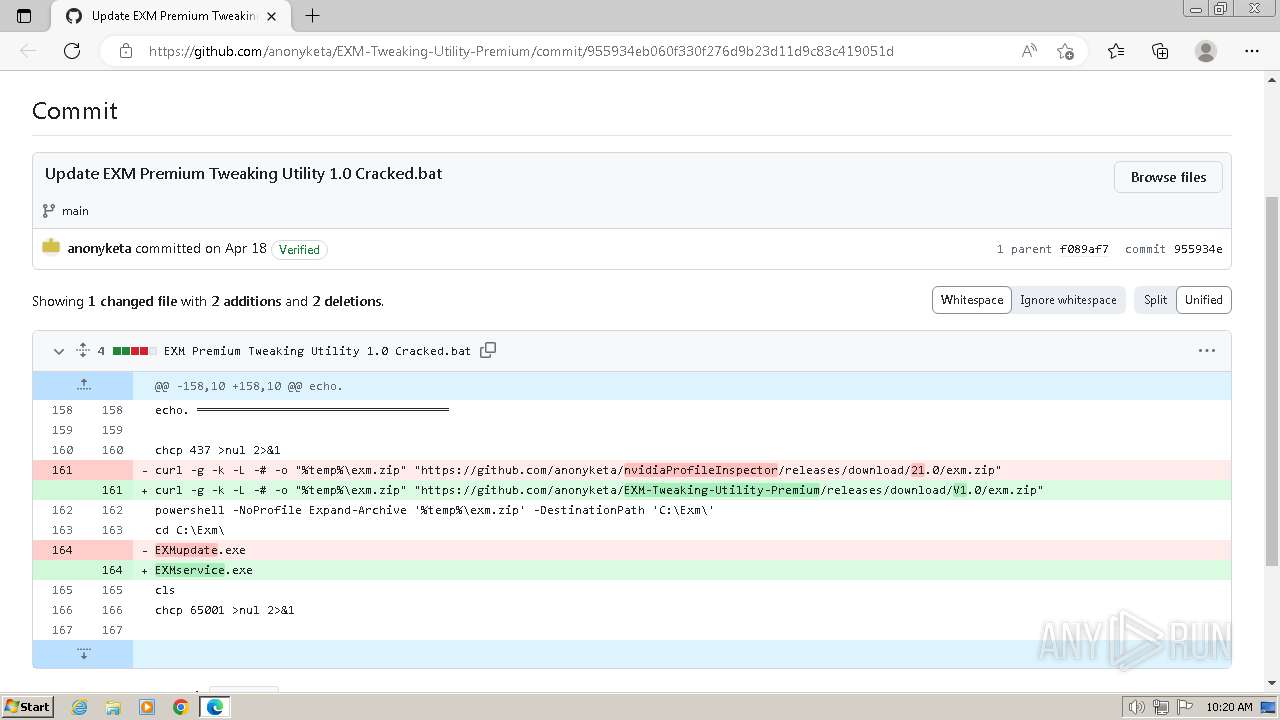
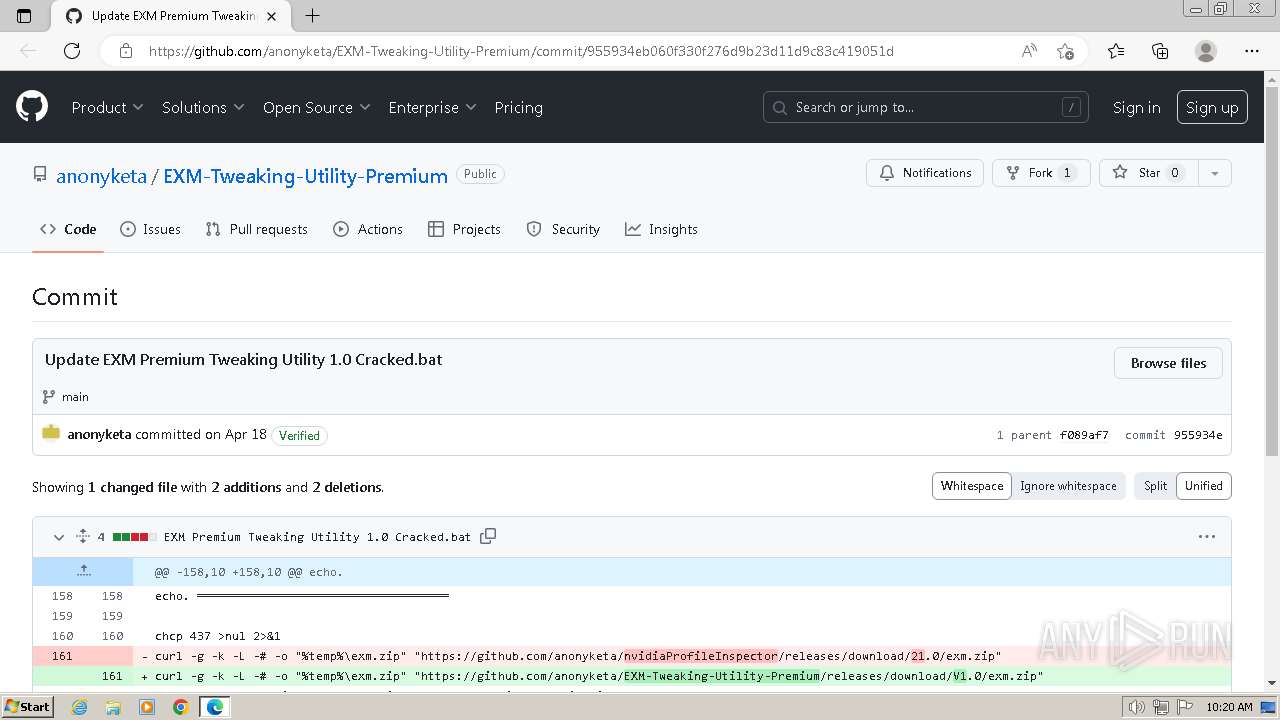
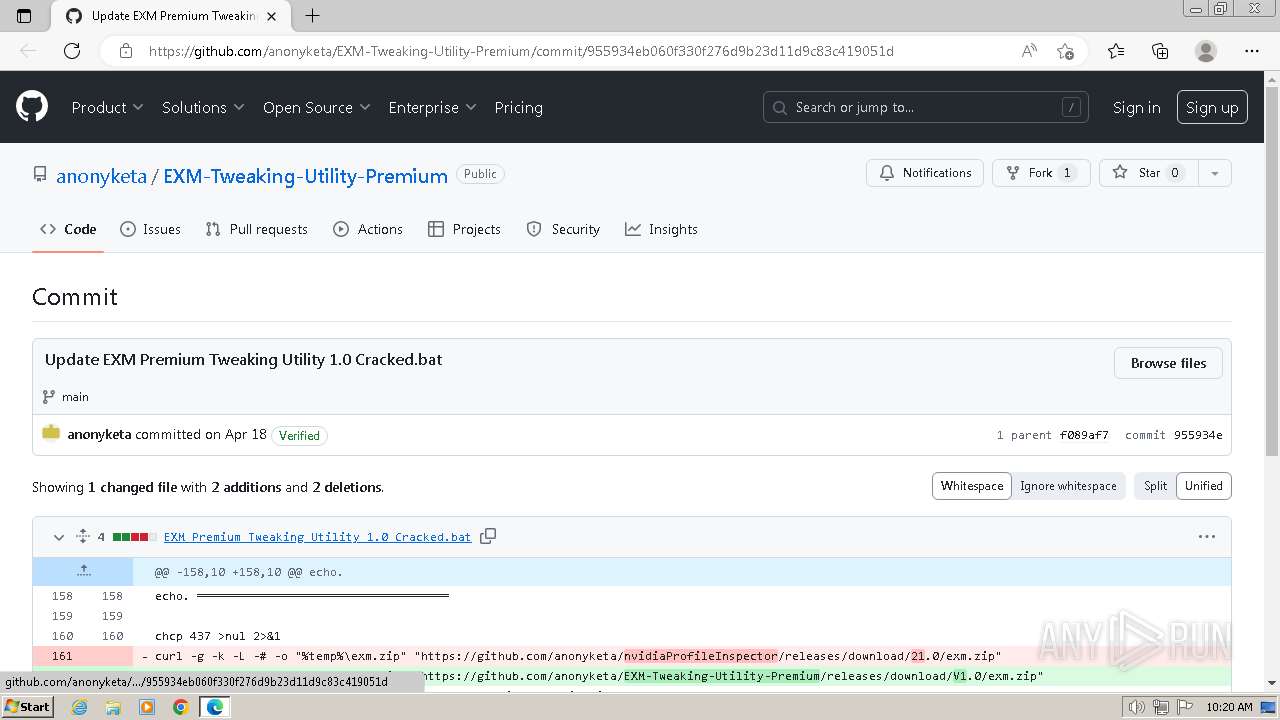
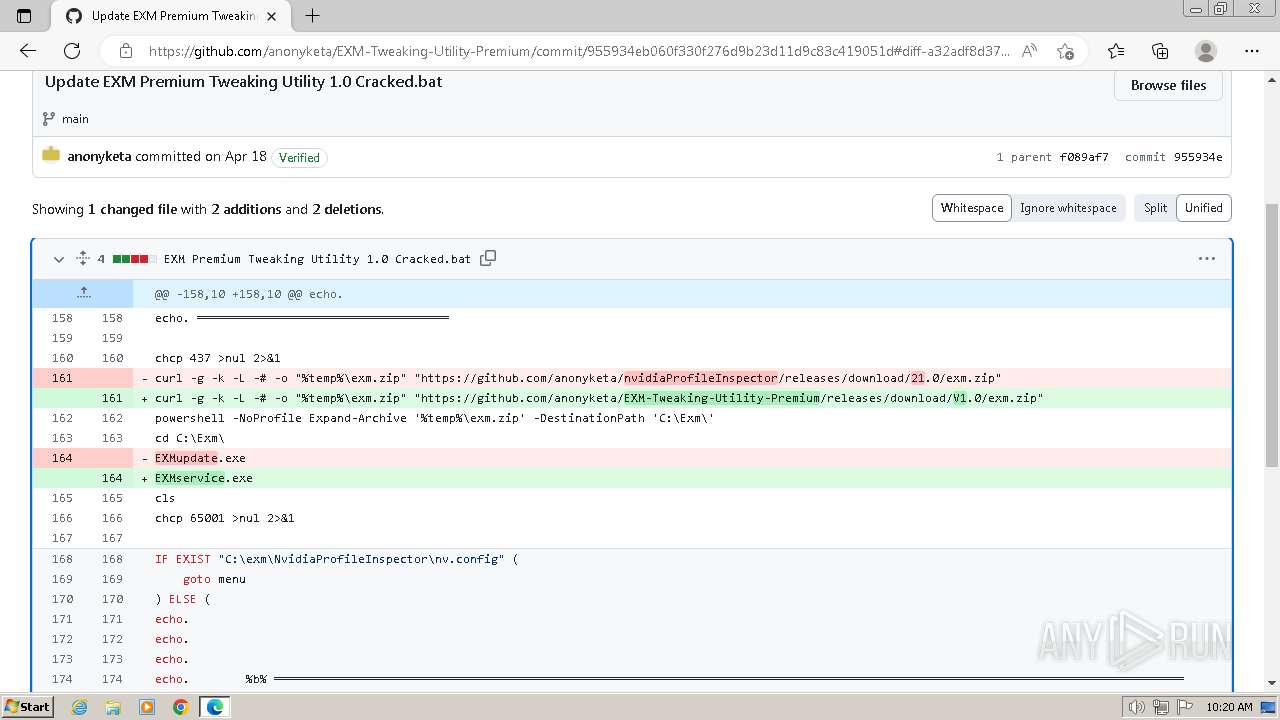
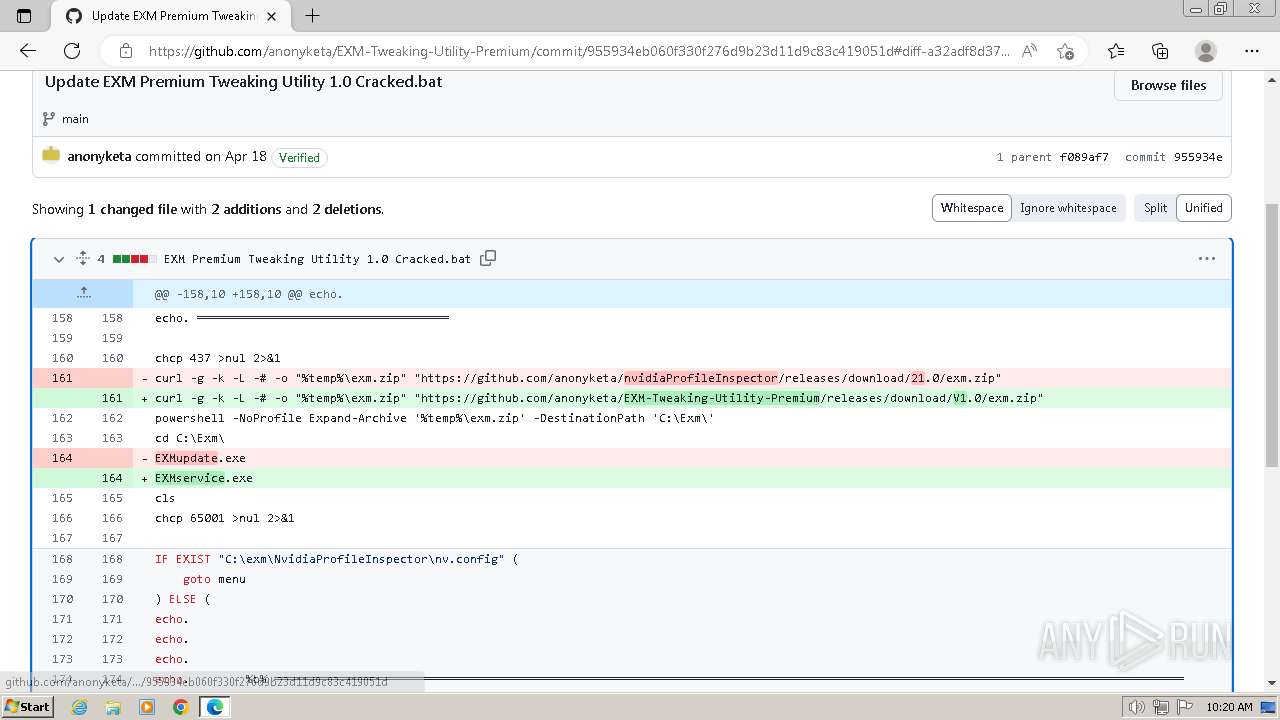
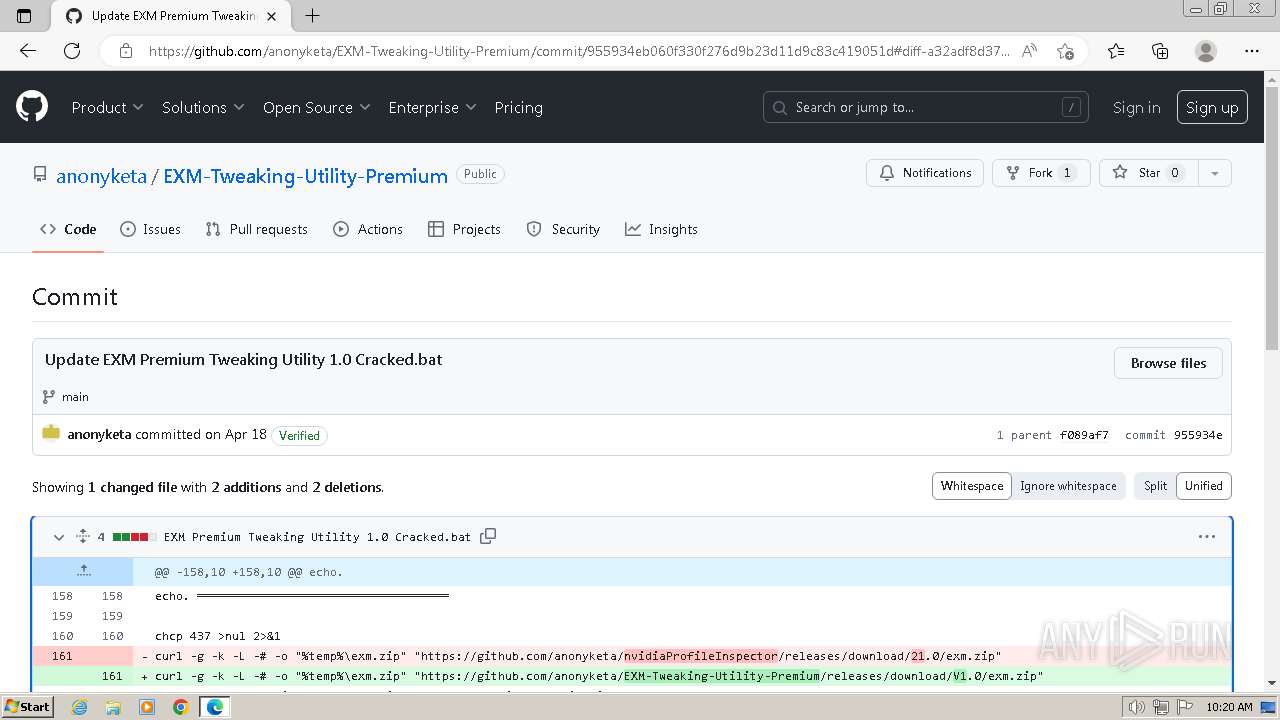
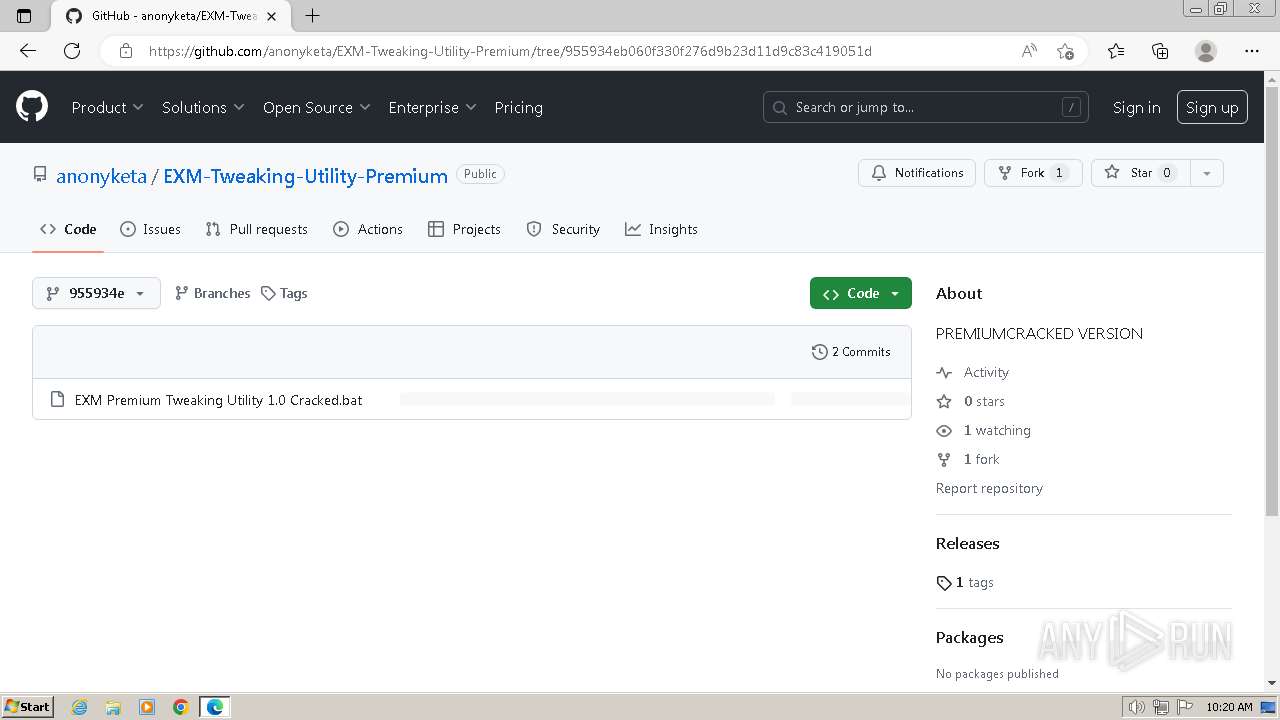
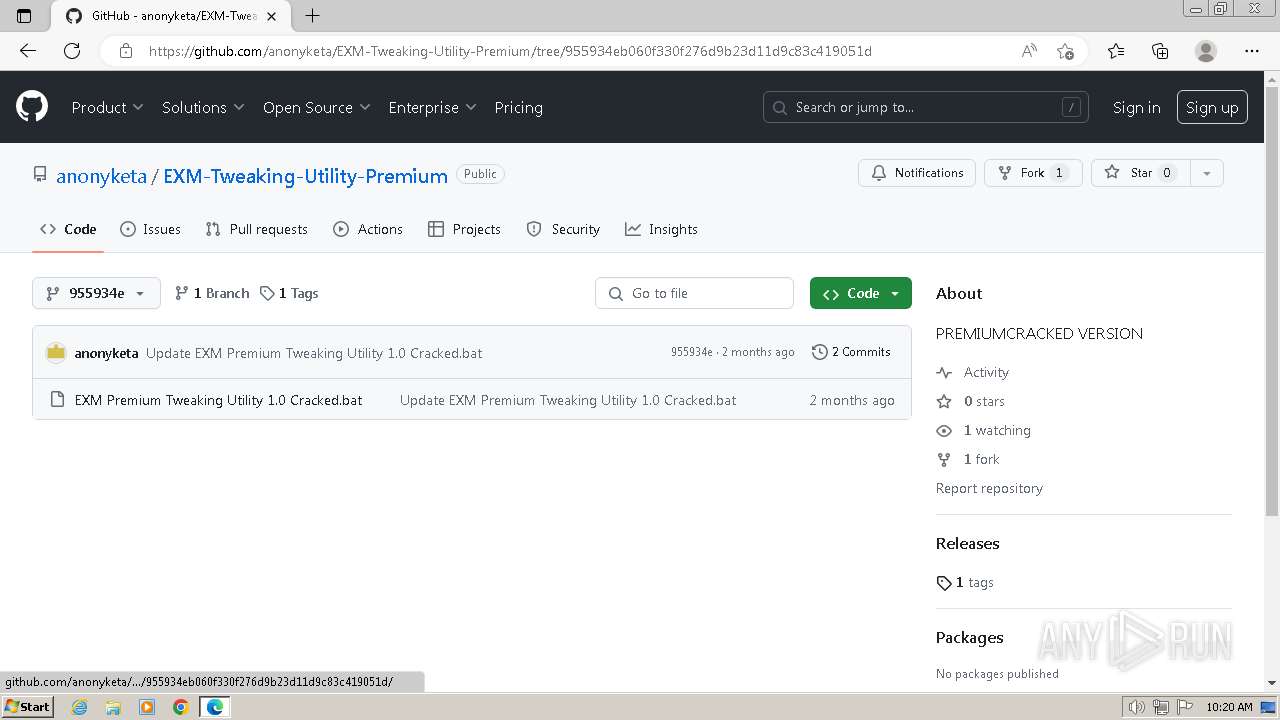
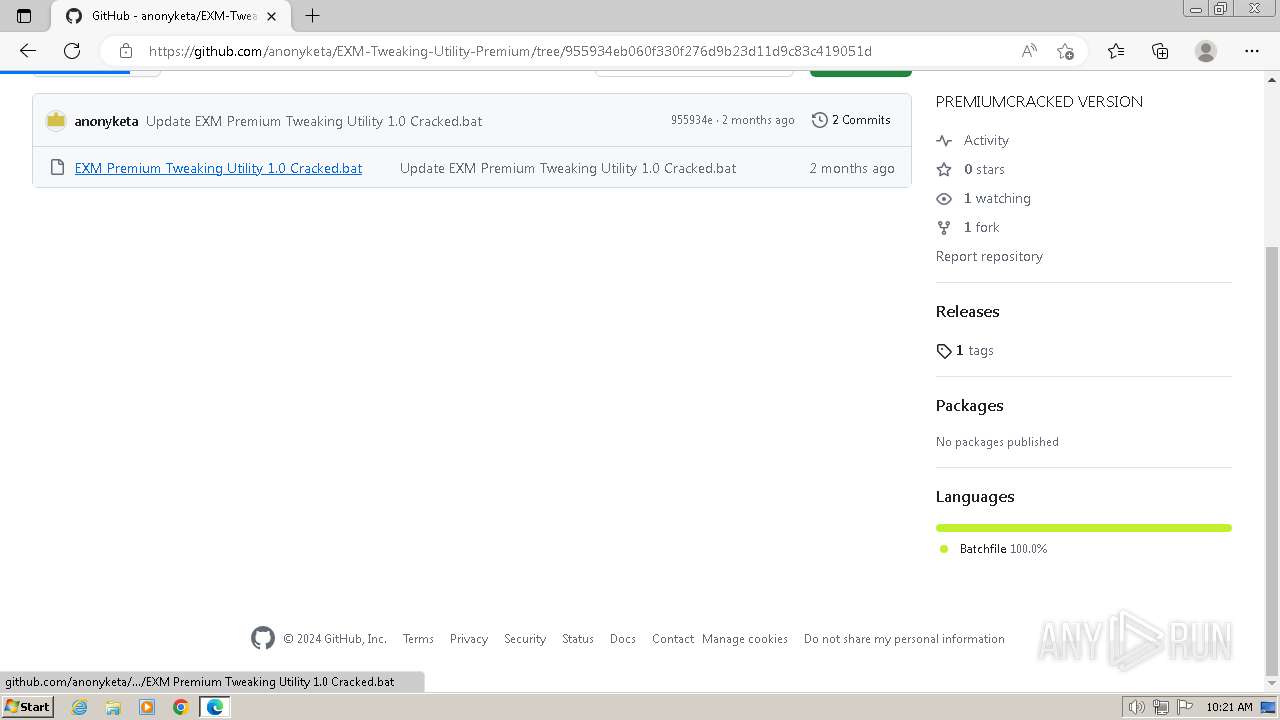
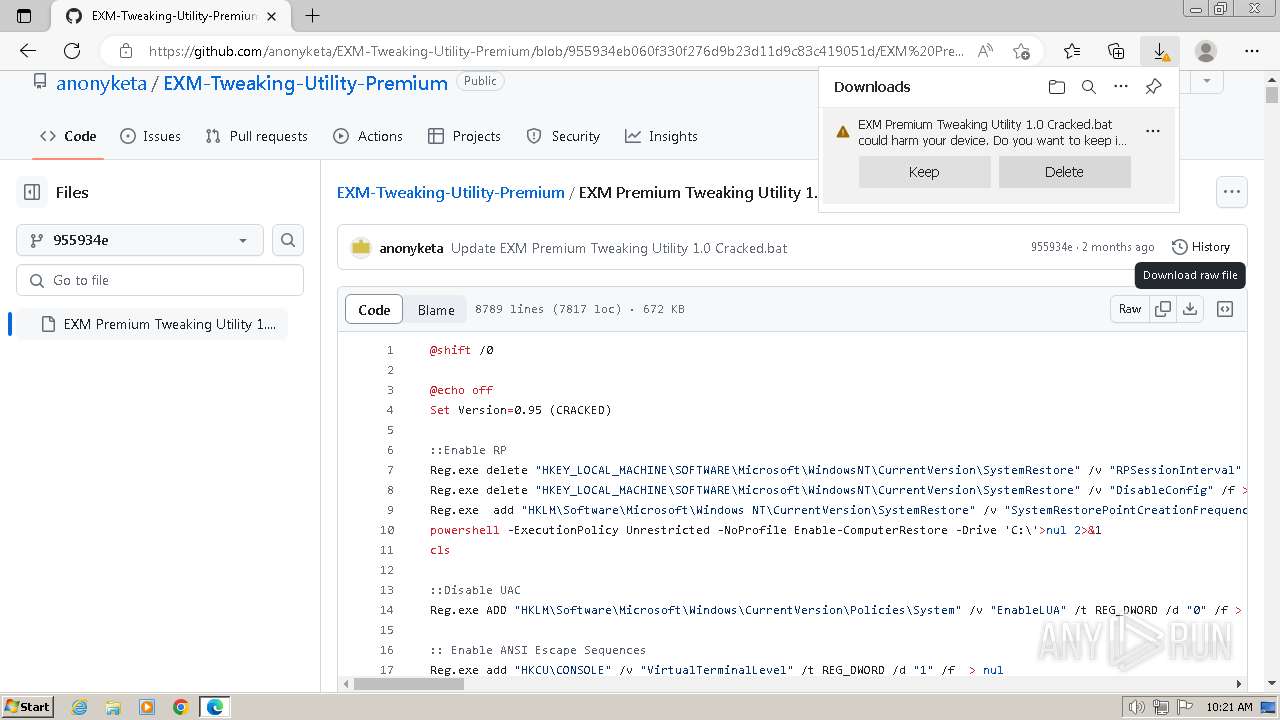
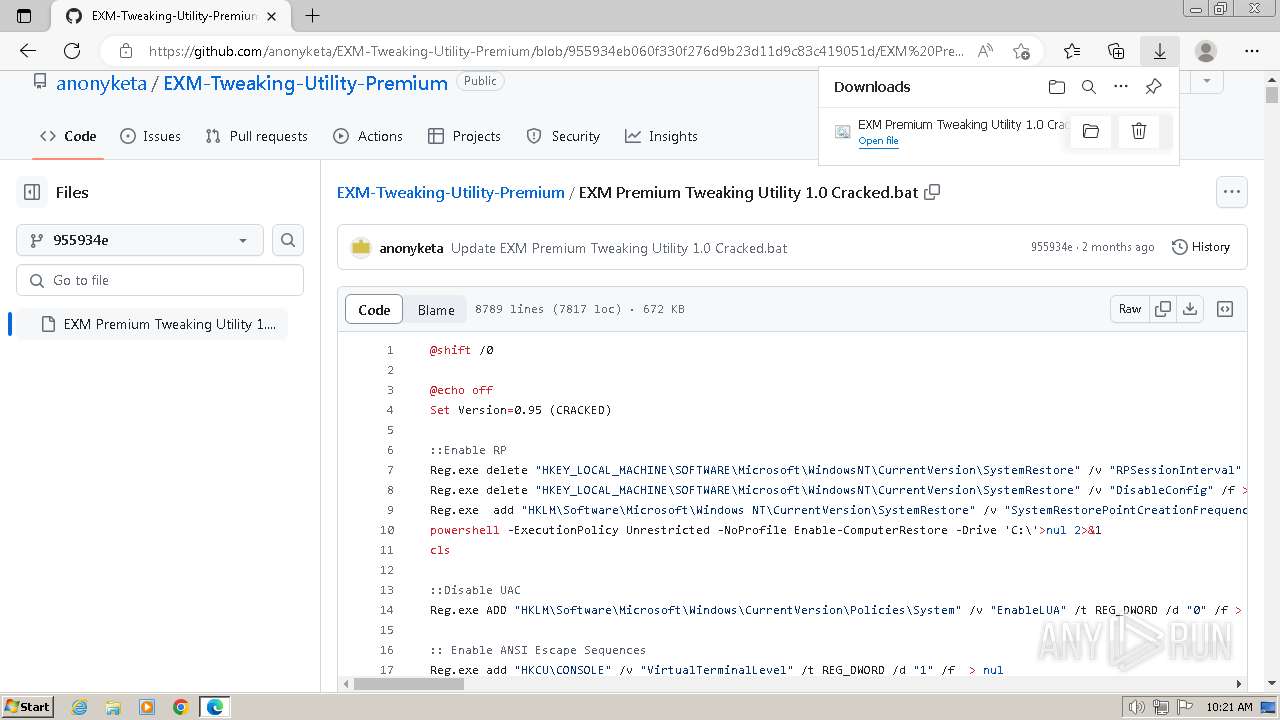
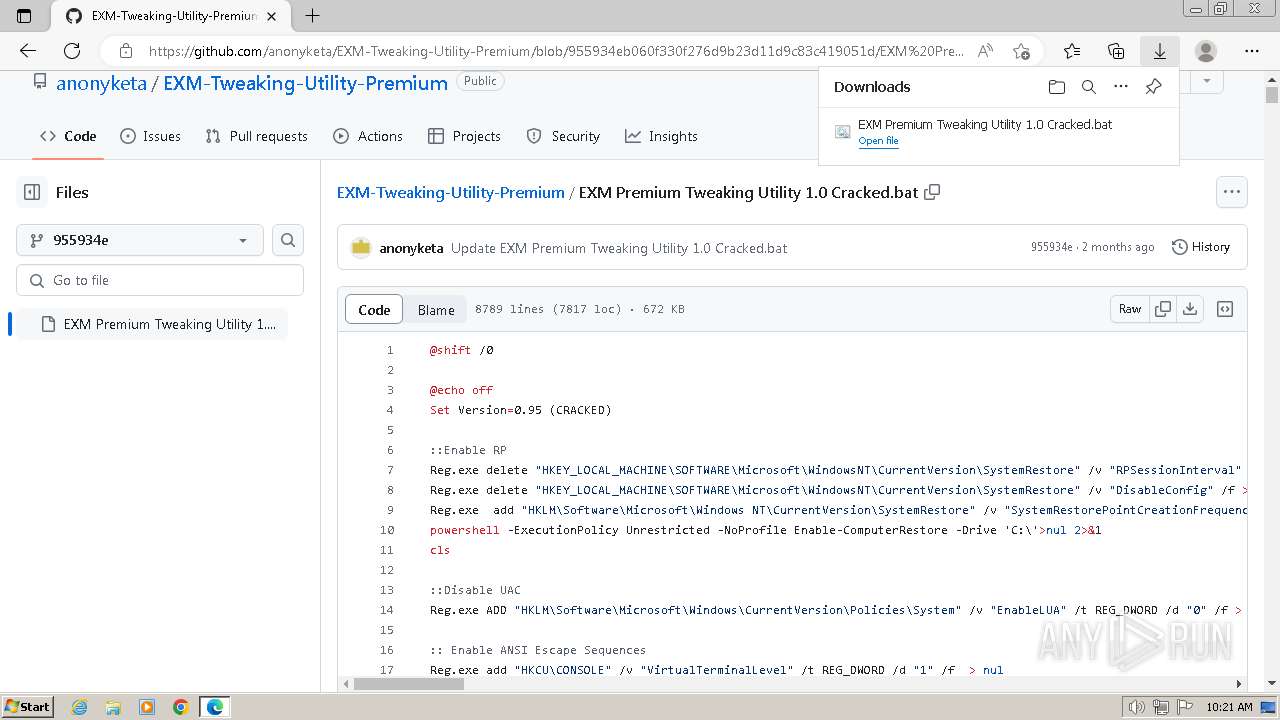
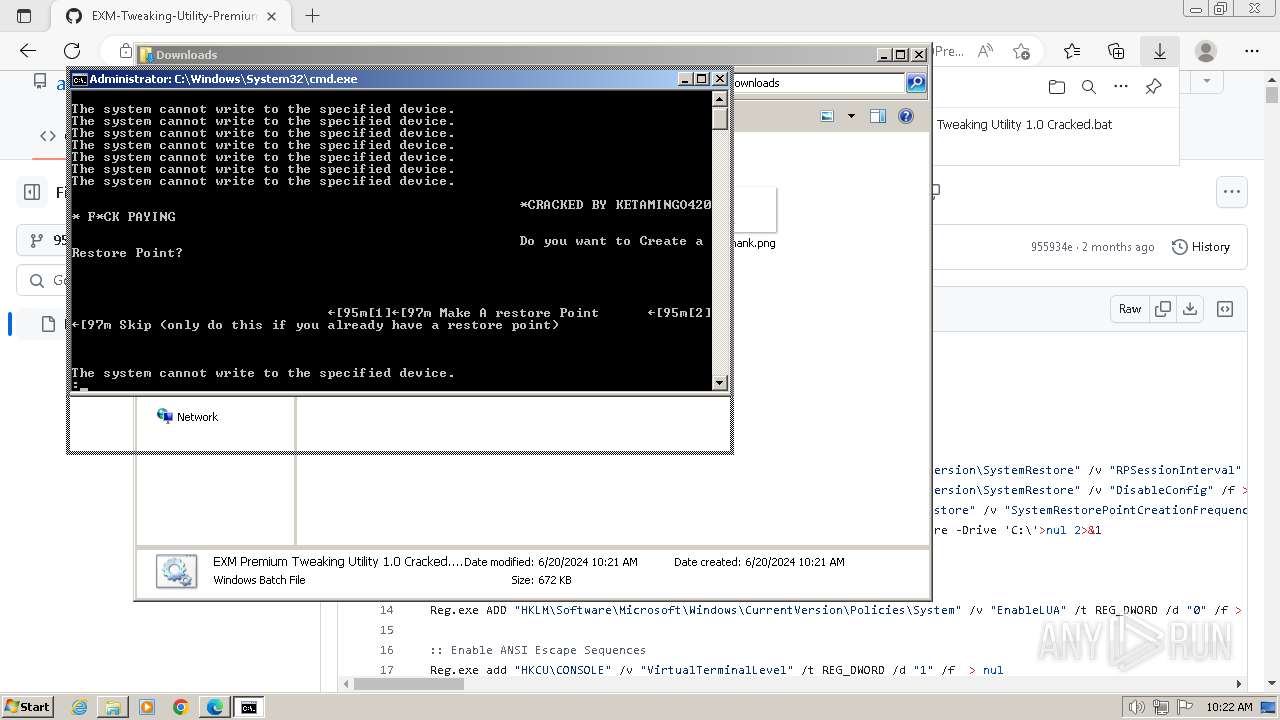
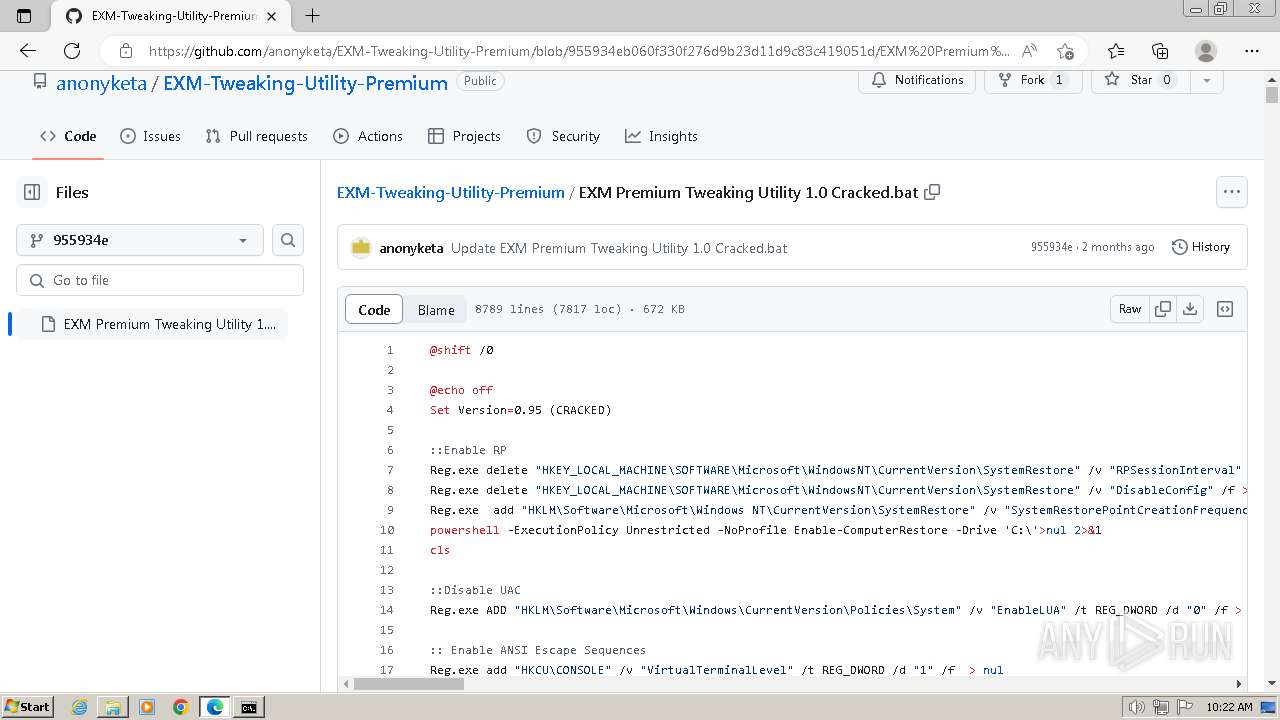
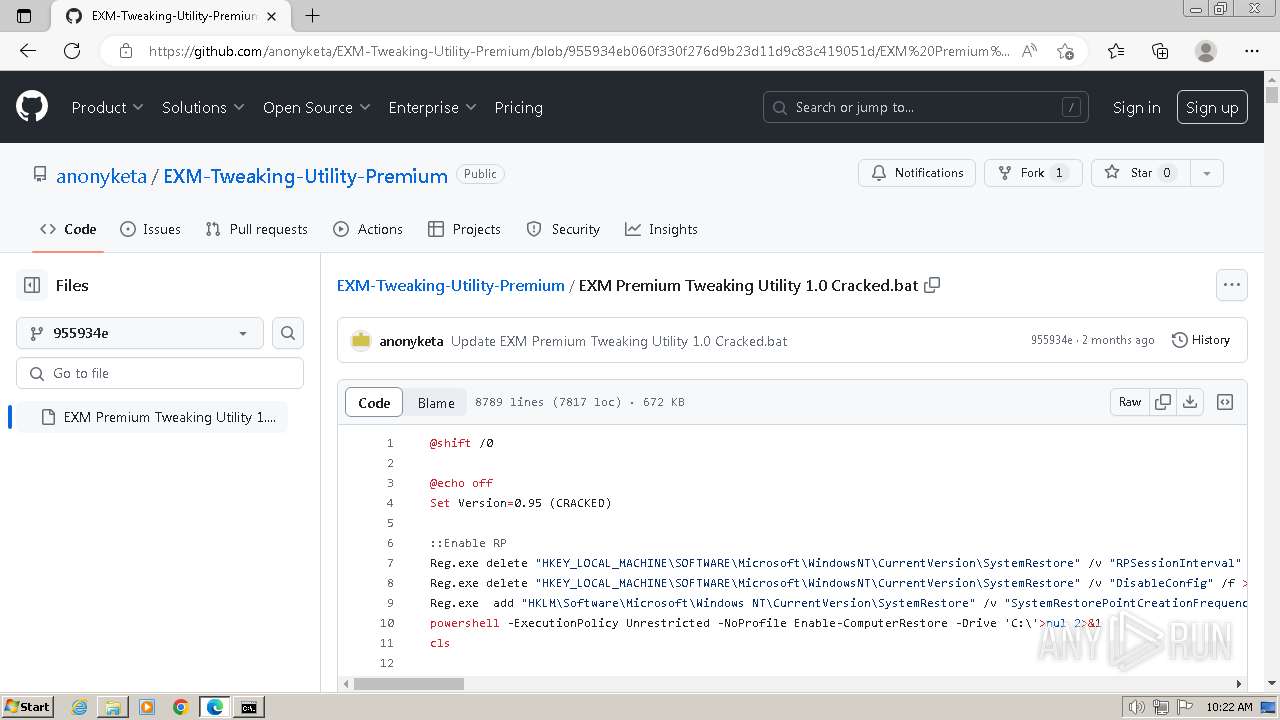
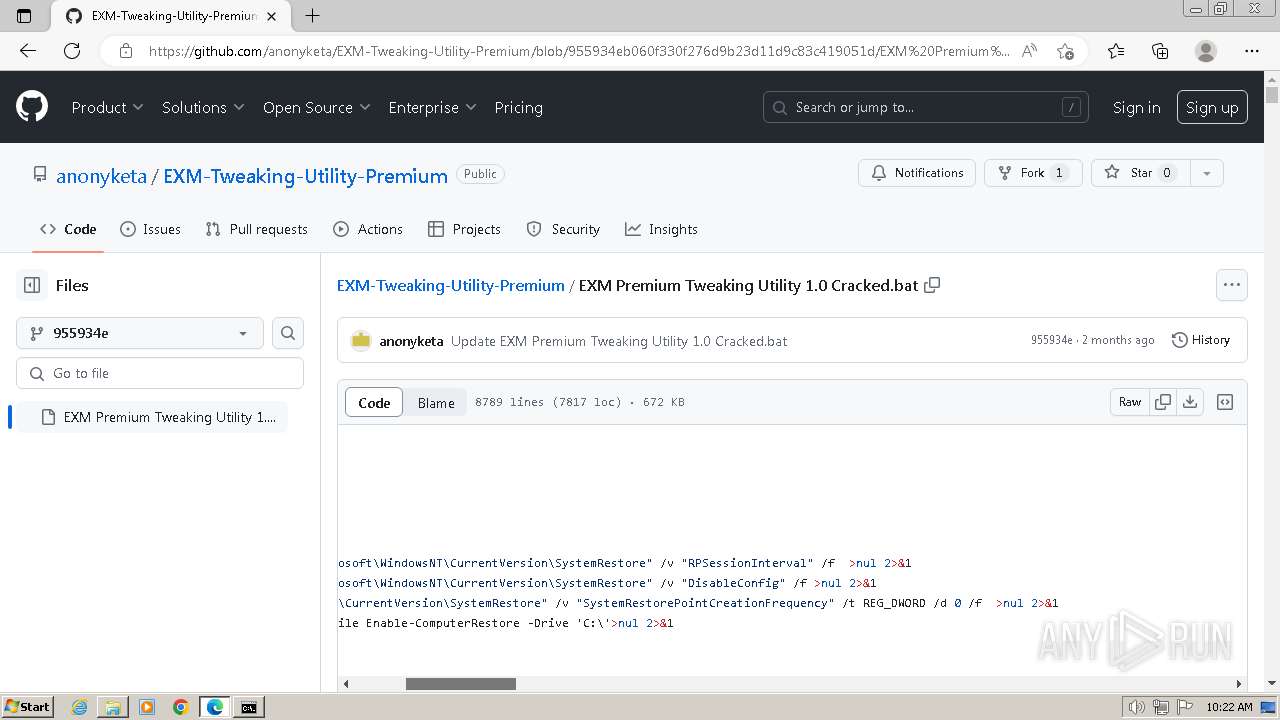
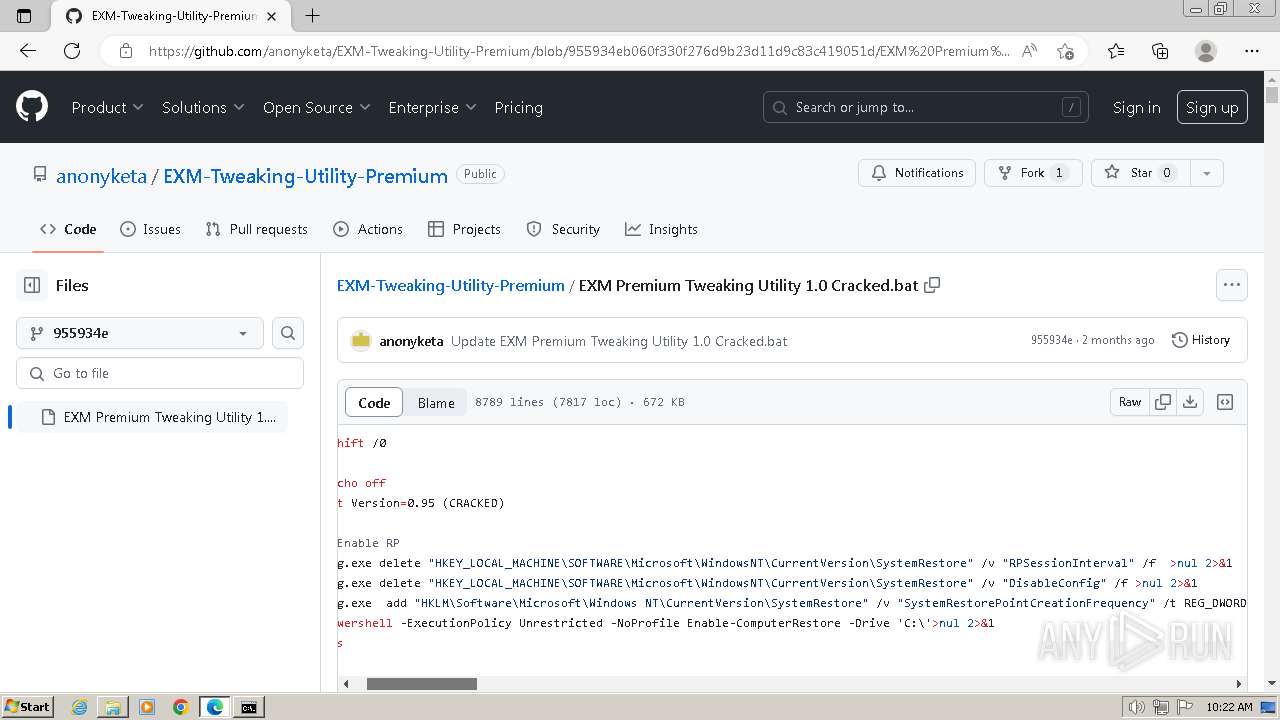
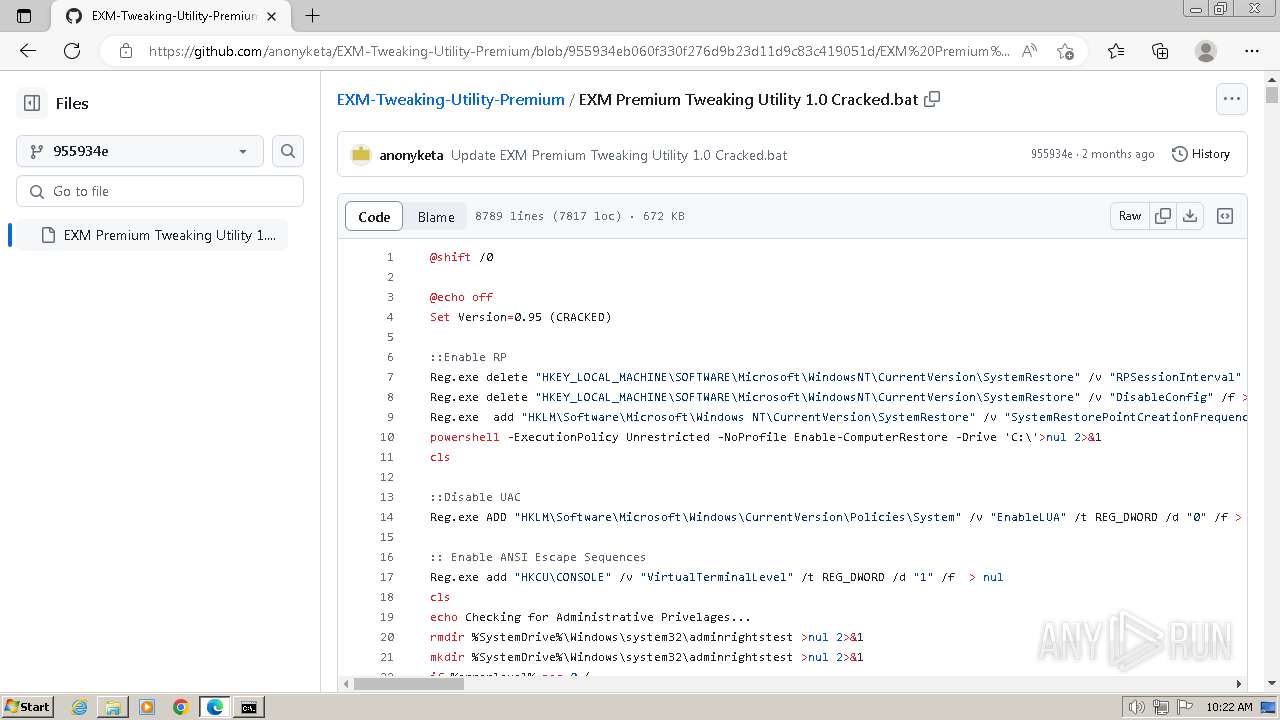
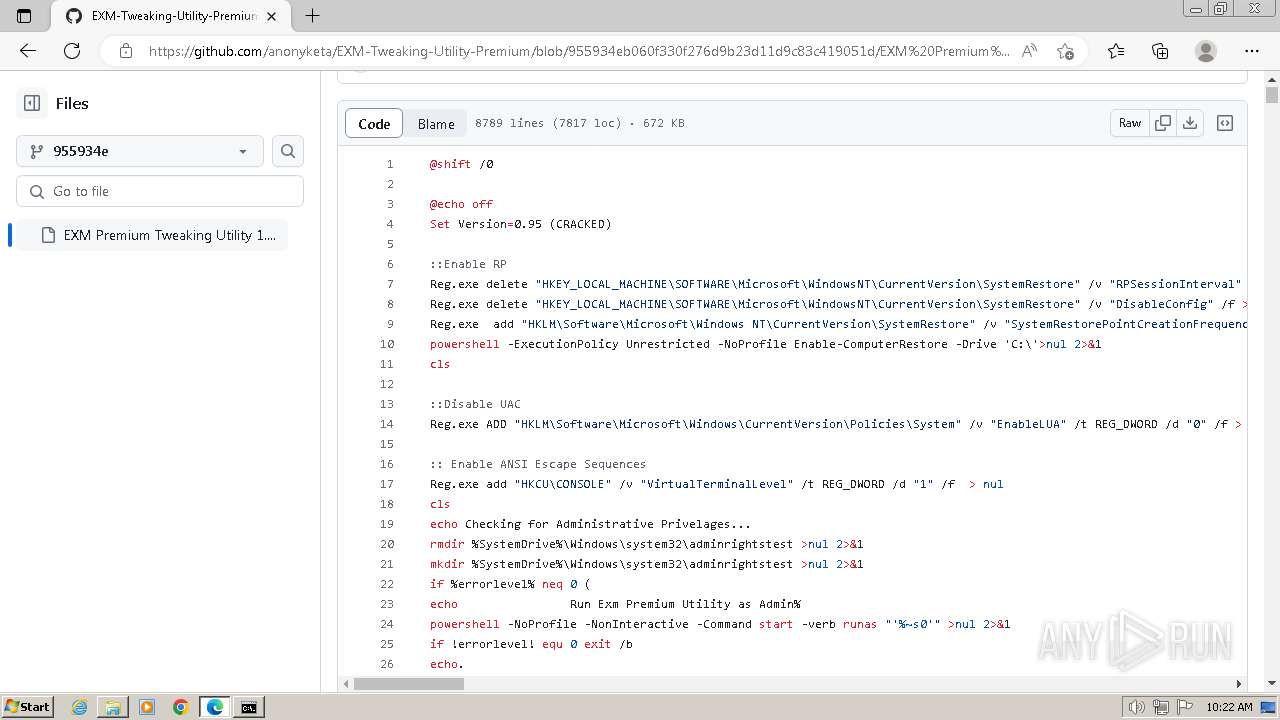
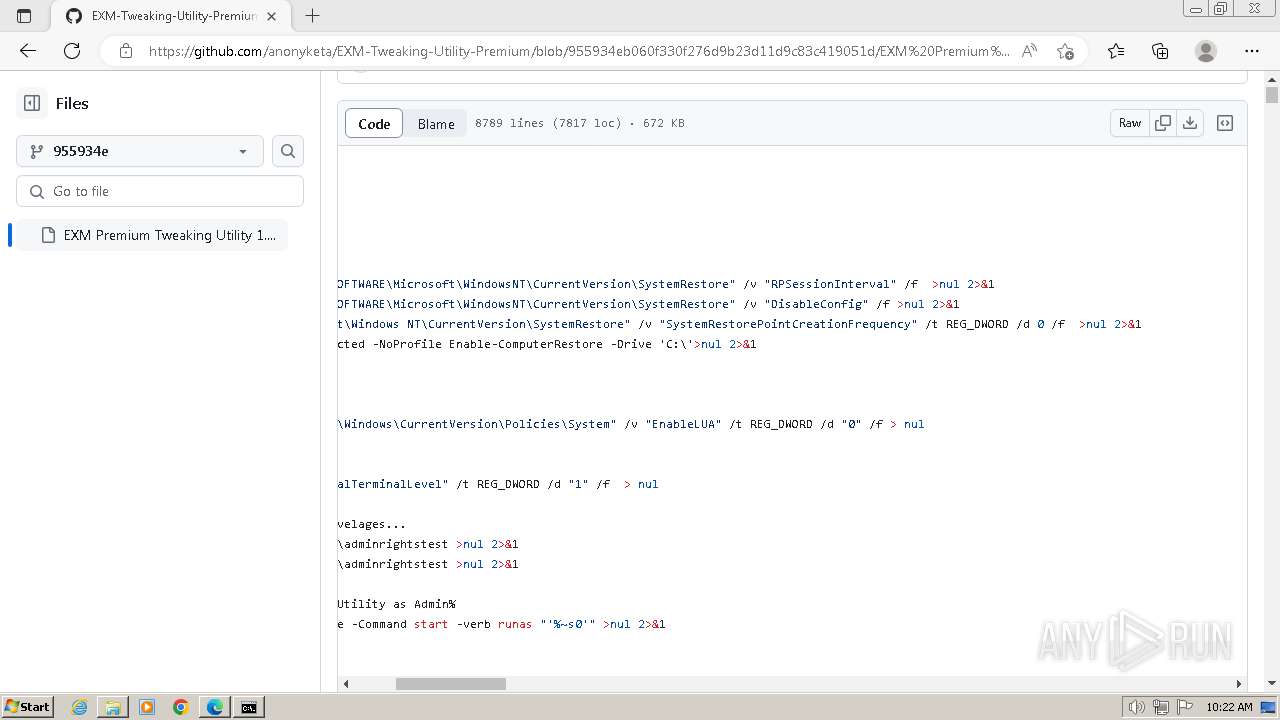
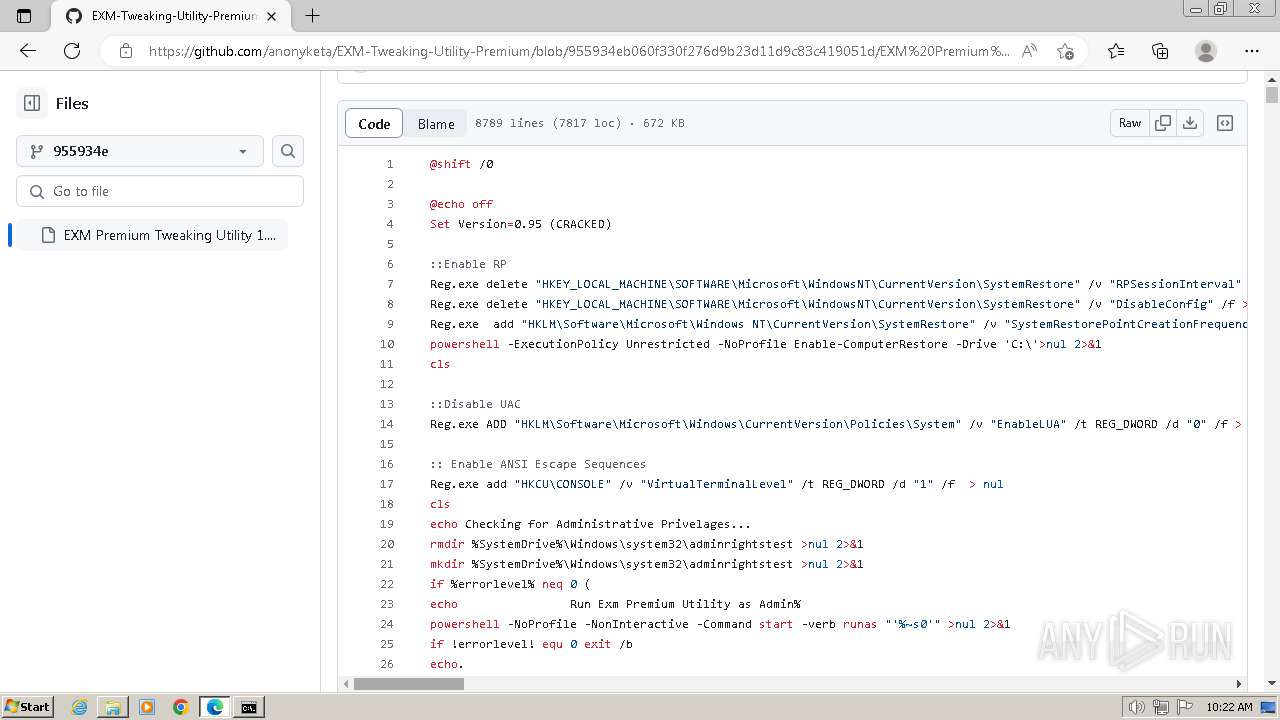
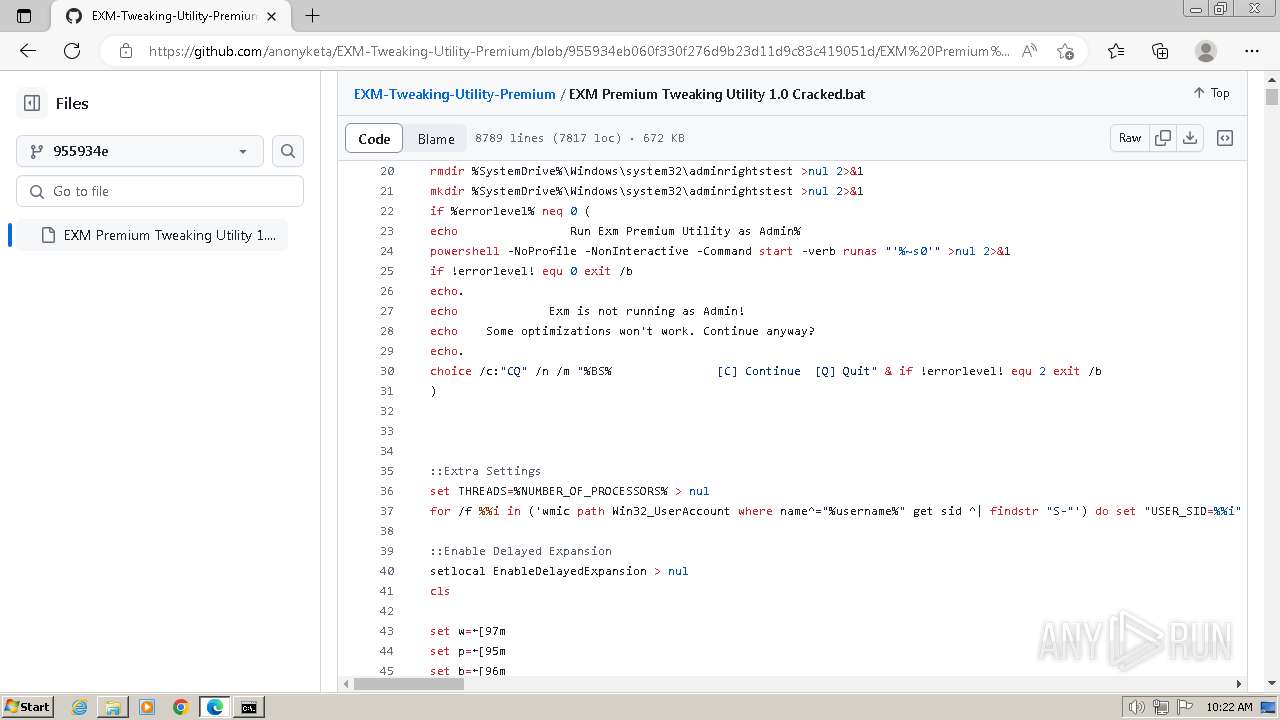
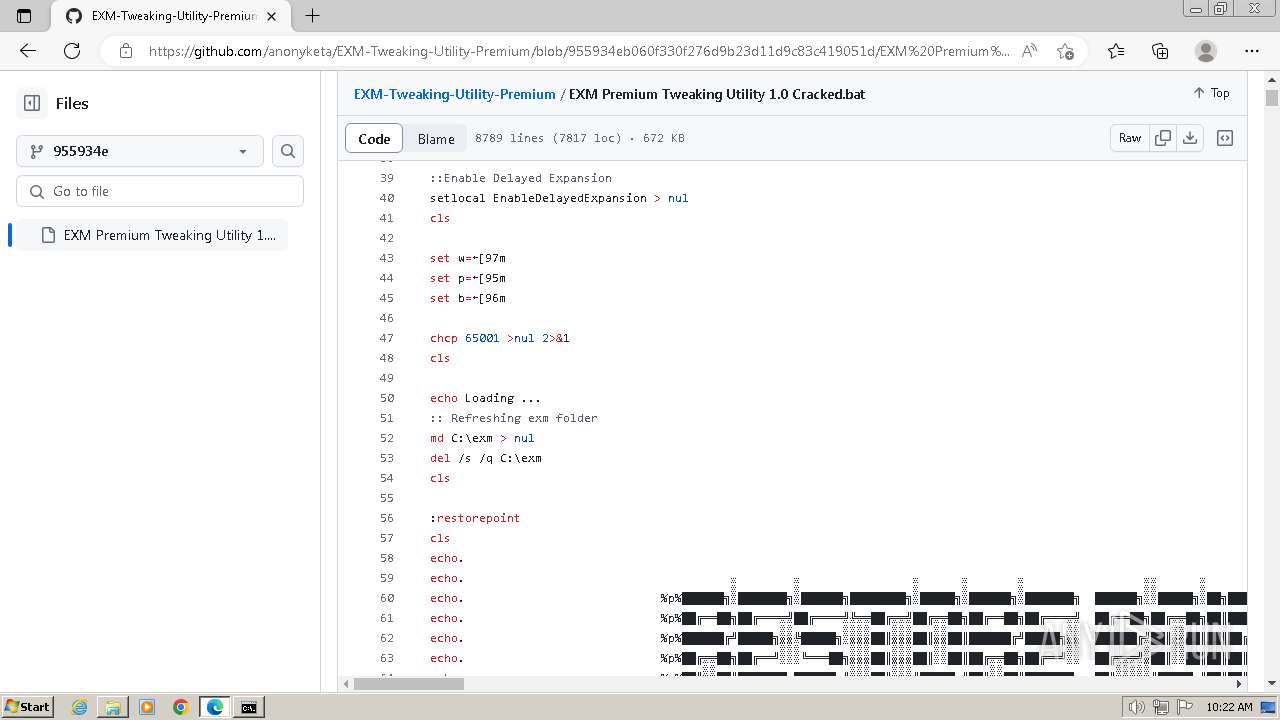
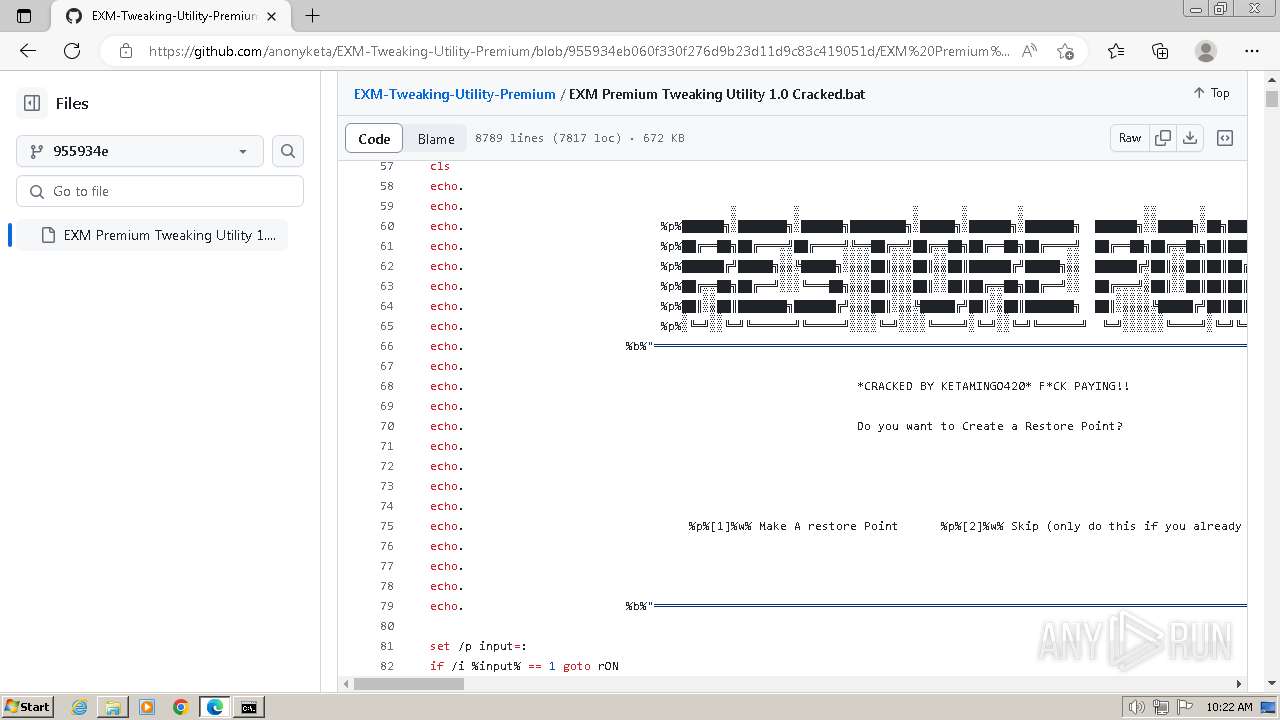
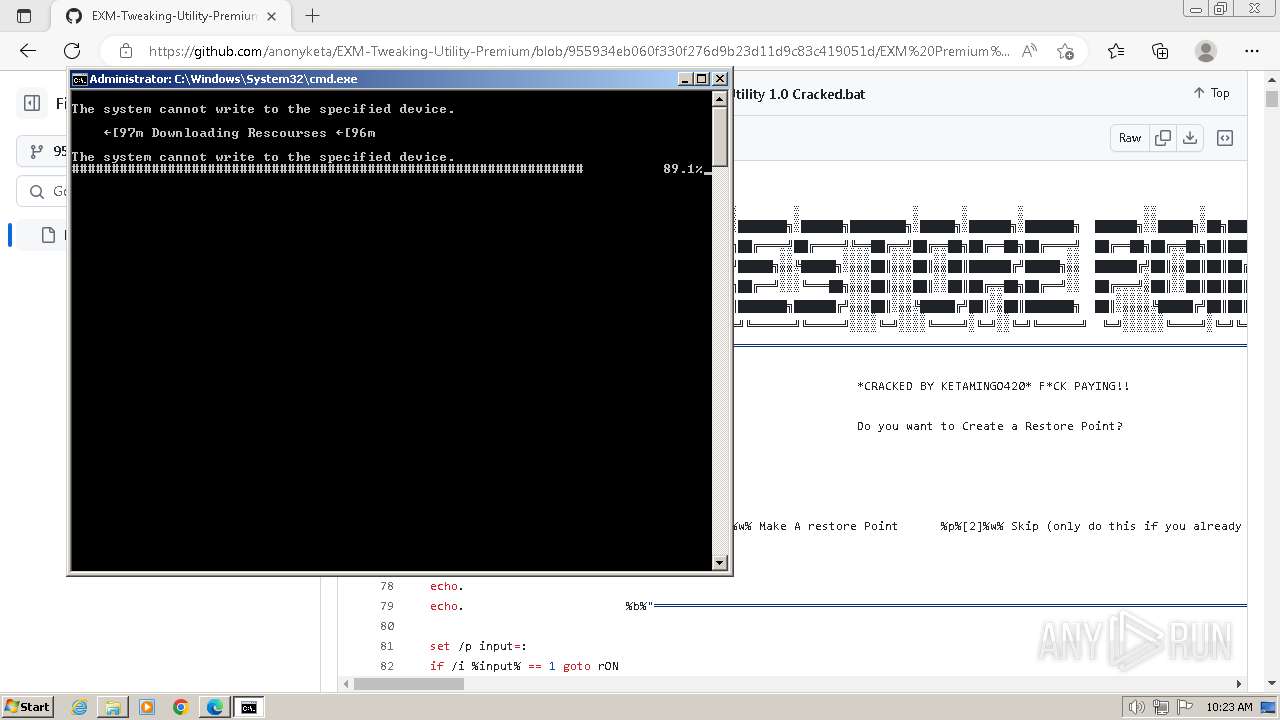
| URL: | https://github.com/anonyketa/EXM-Tweaking-Utility-Premium/commit/955934eb060f330f276d9b23d11d9c83c419051d |
| Full analysis: | https://app.any.run/tasks/9ffd9917-4cac-4f70-903a-5b7dc02b4037 |
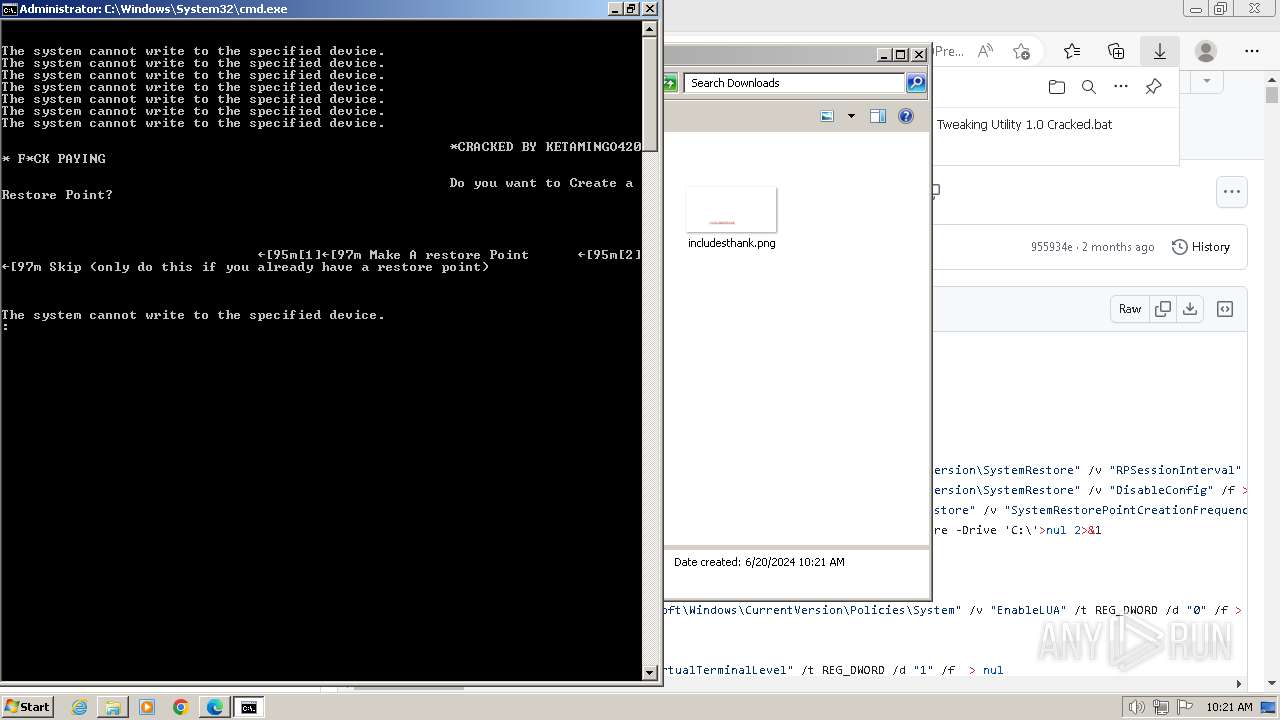
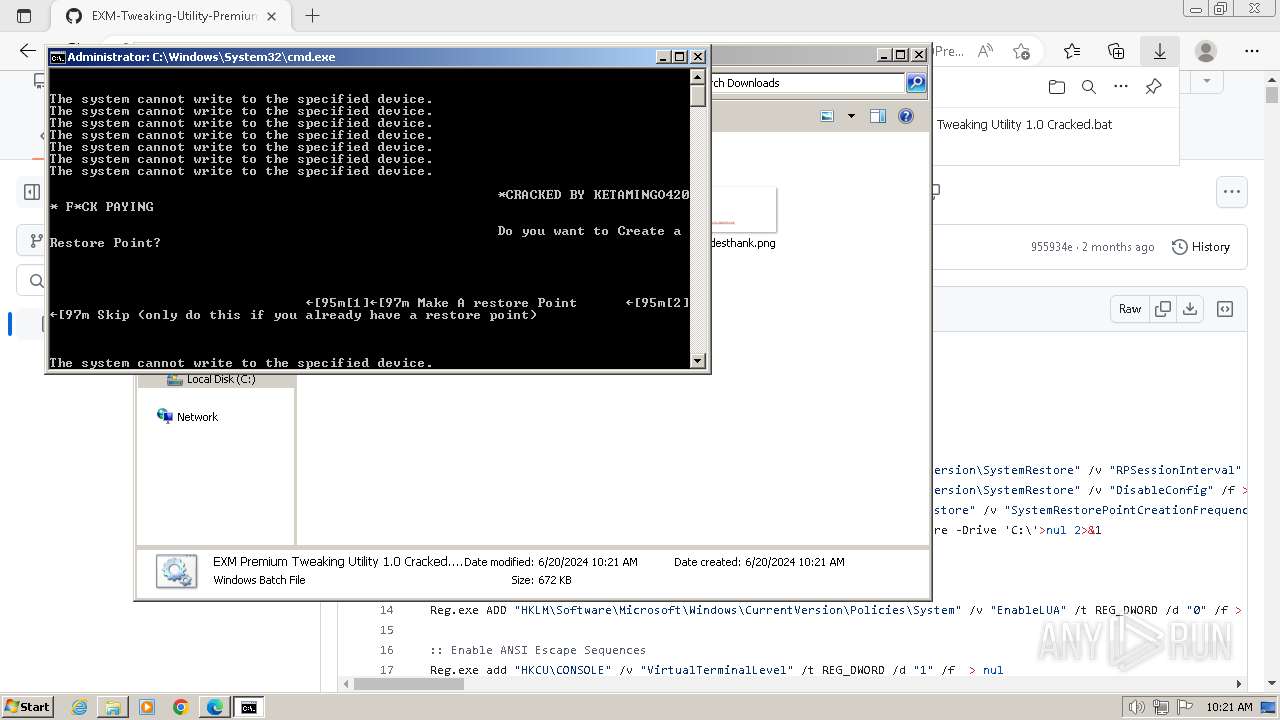
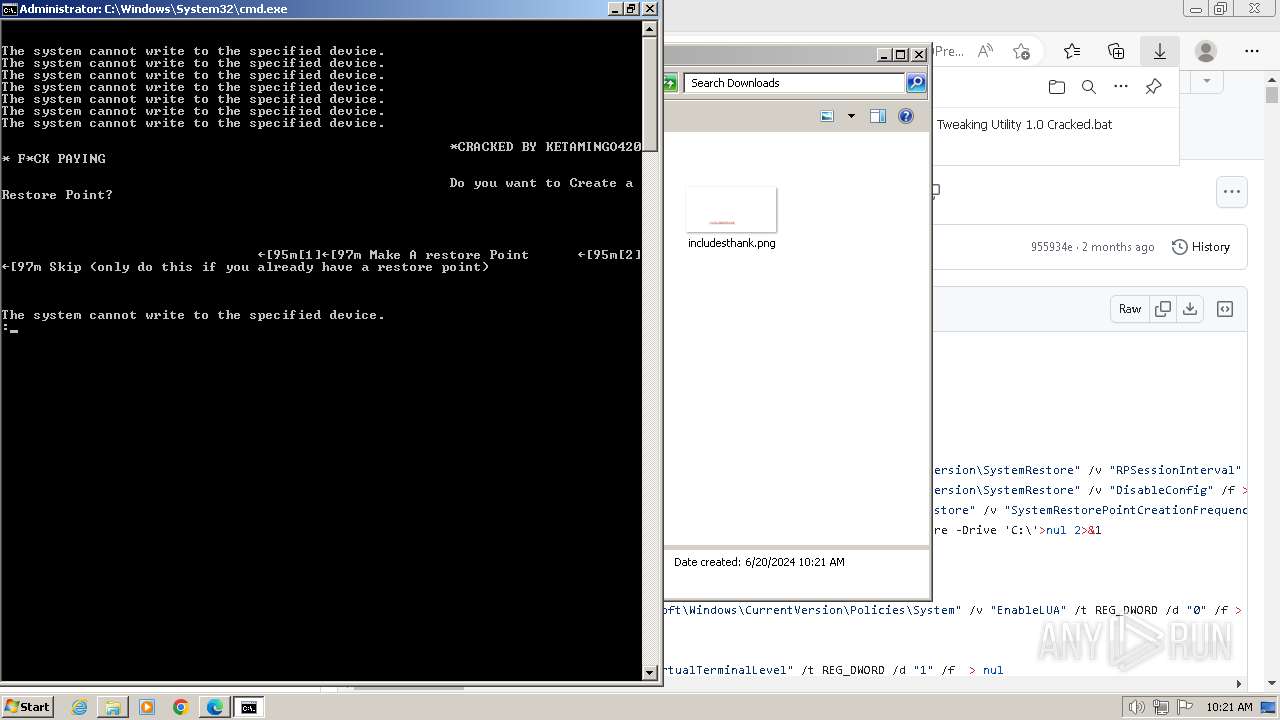
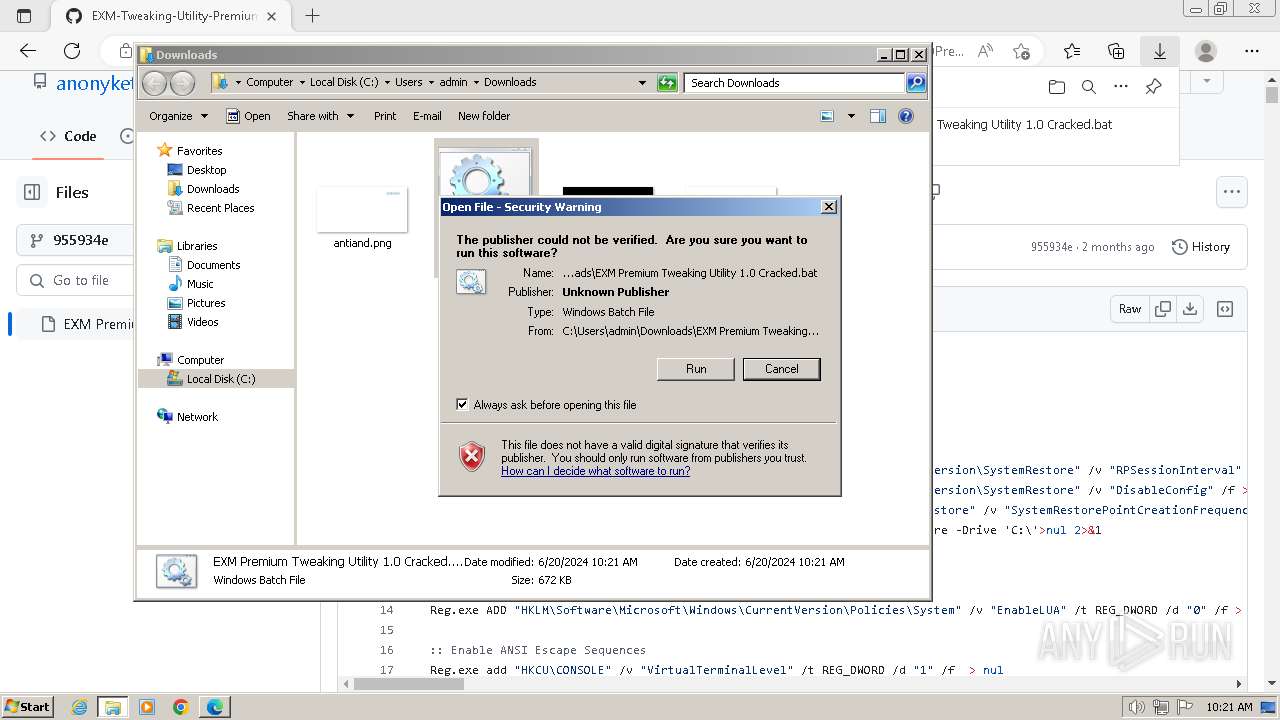
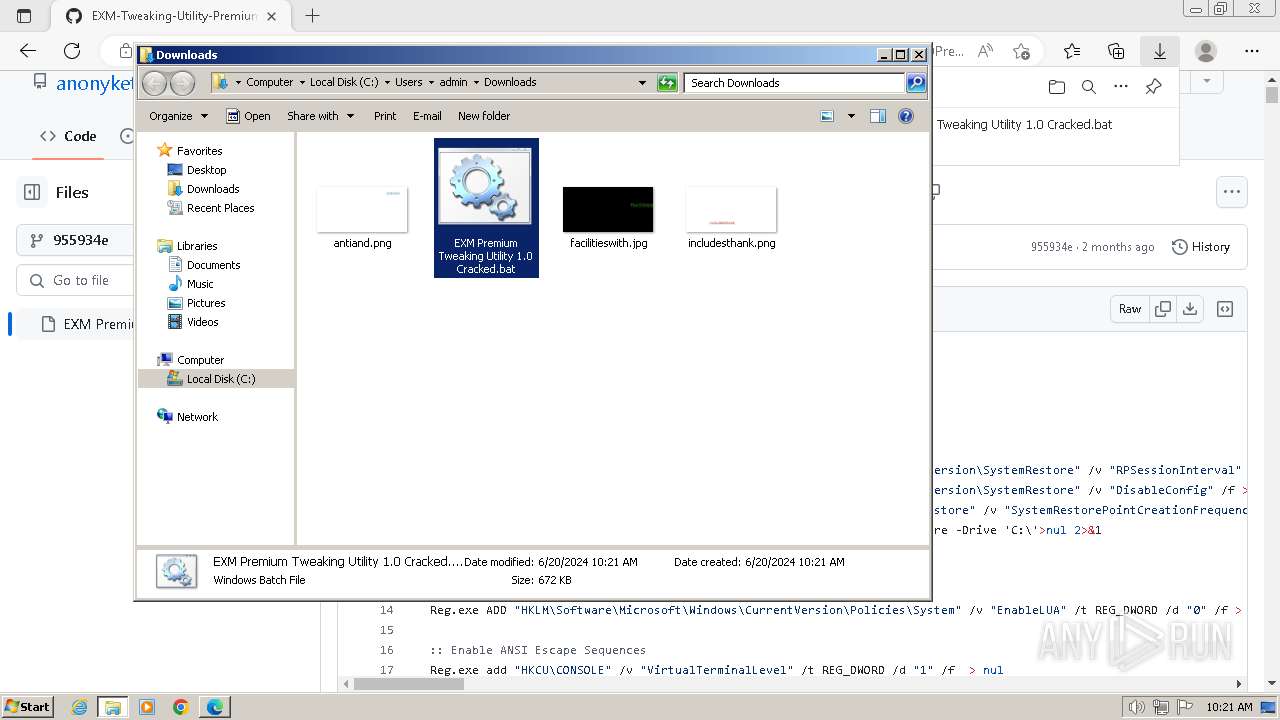
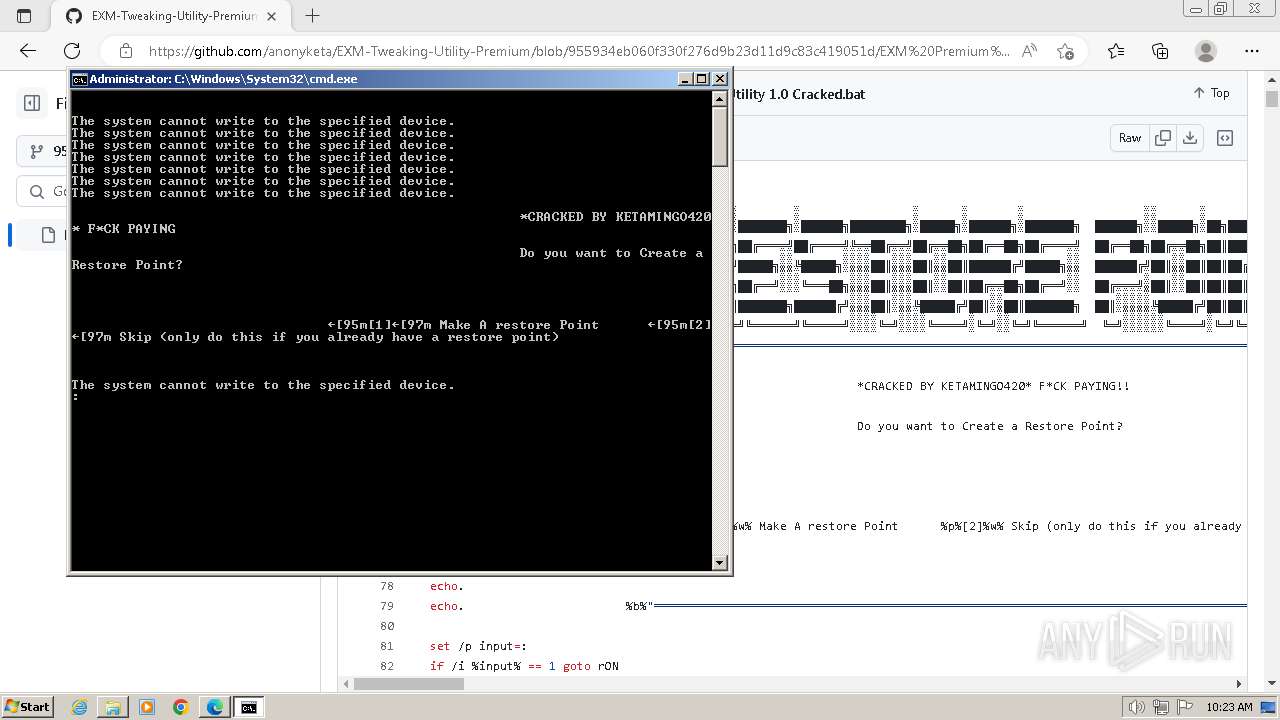
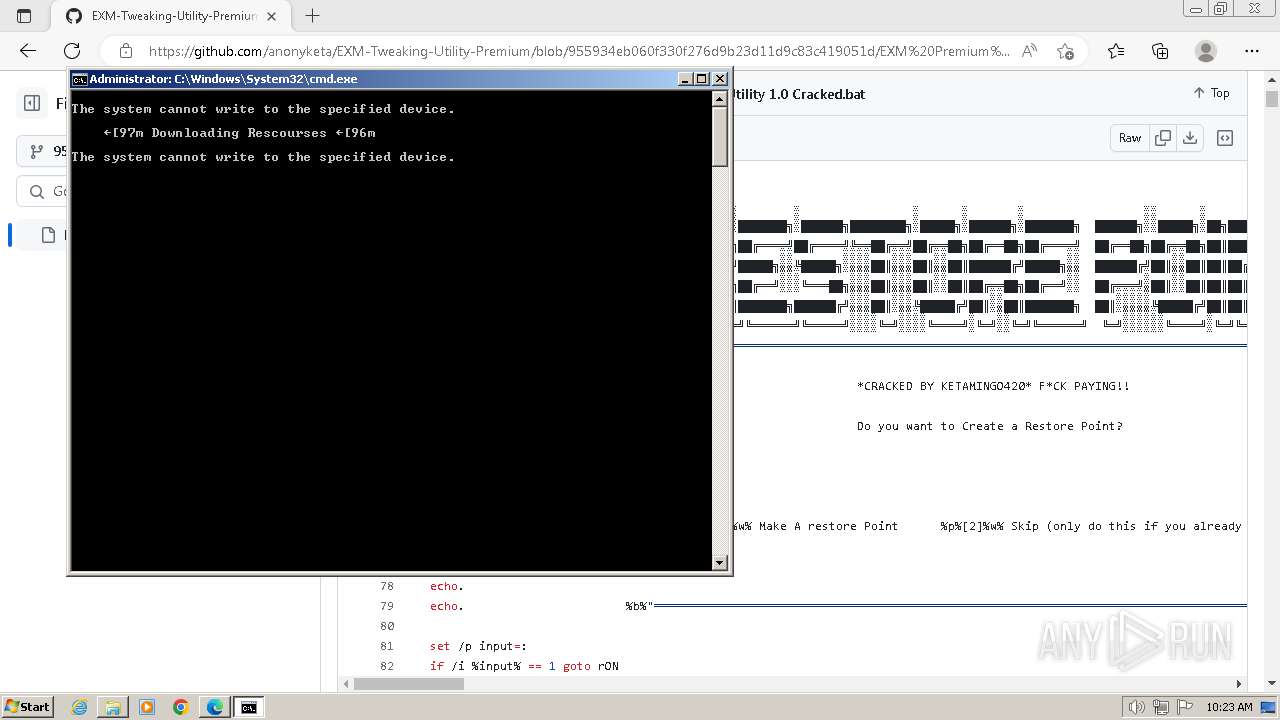
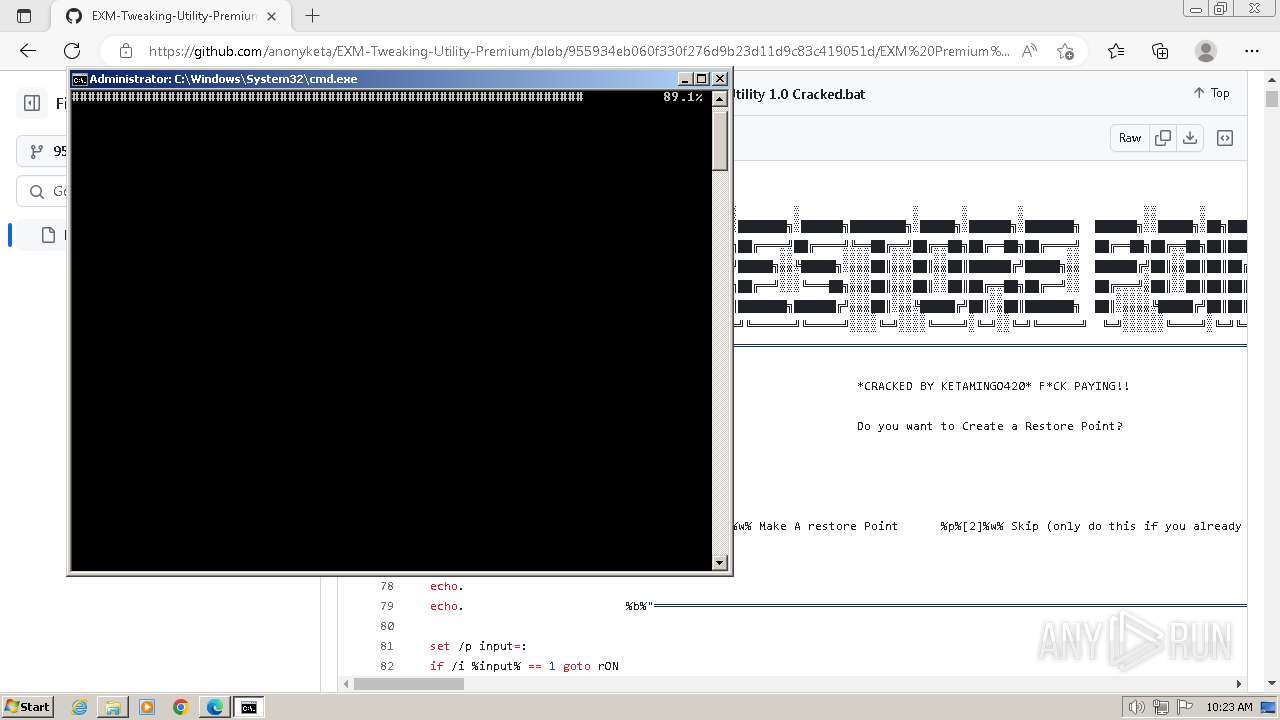
| Verdict: | Malicious activity |
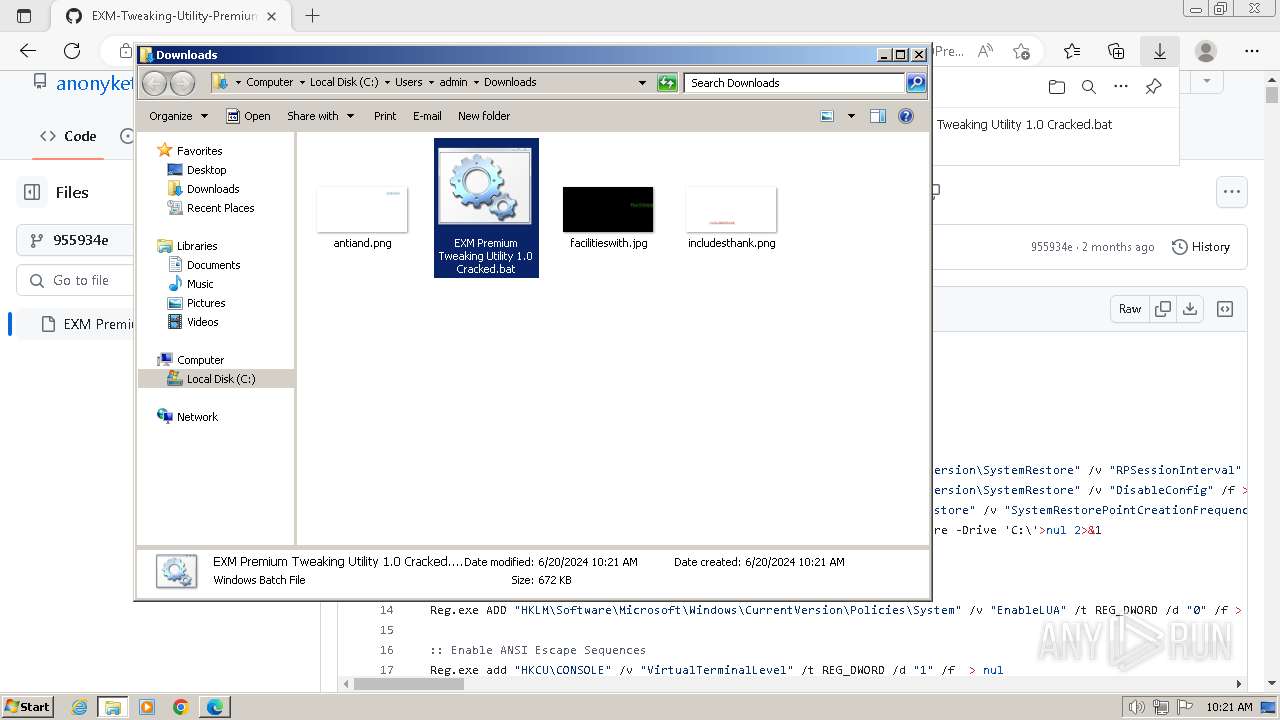
| Analysis date: | June 20, 2024, 09:20:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 40CB9BD32A8E3E7572C78EE0B35329E5 |
| SHA1: | 904CCB9BF5071ABF7D31F032B7A53D794D393E08 |
| SHA256: | 57C7FB8F6FE383A358634B5D9FF49F82B43C21ABCC2CFE722581D34D1AE7D84A |
| SSDEEP: | 3:N8tEd0+TAsZM2NRJMXlnqpCKGTfiY:2ui+bM2NRJMXK1GTfiY |
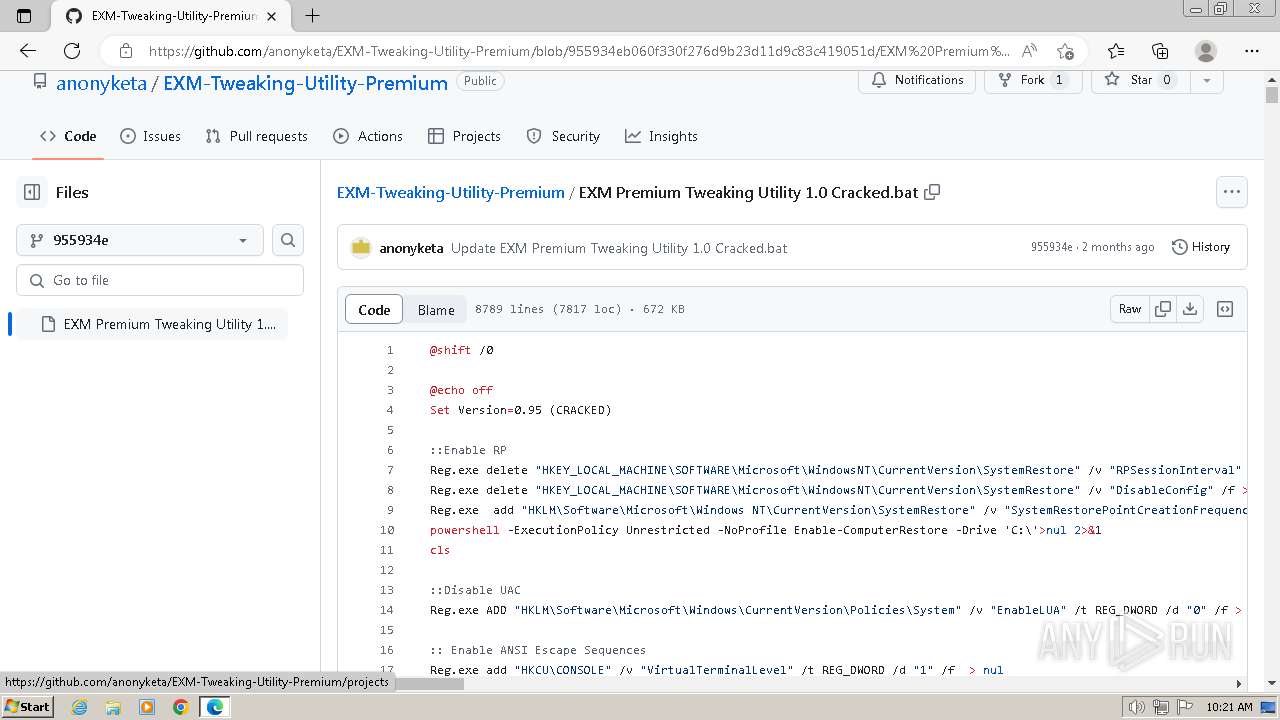
MALICIOUS
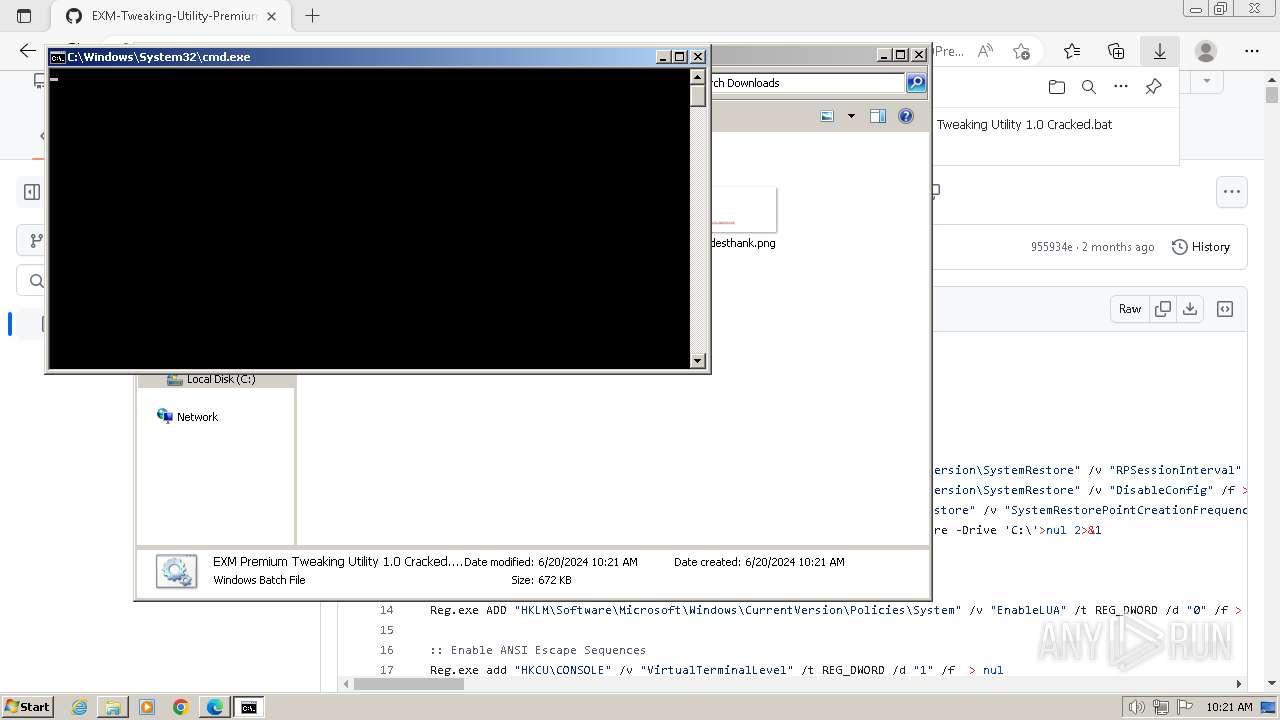
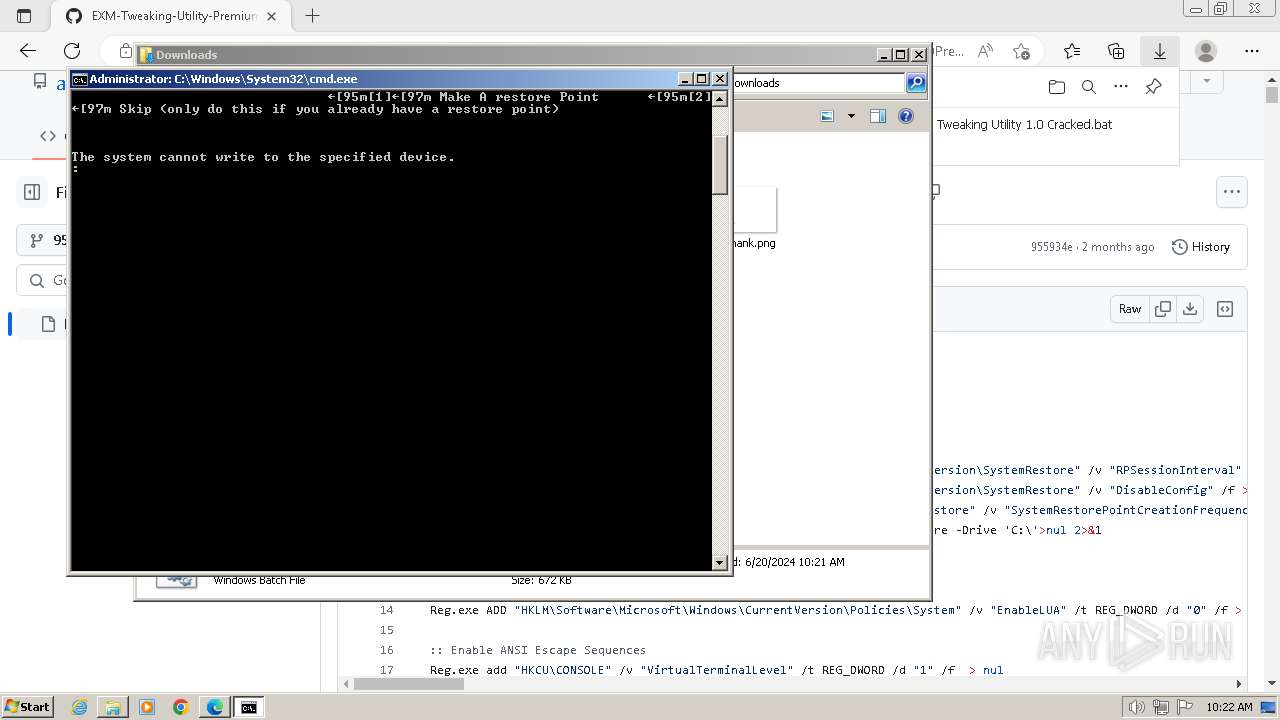
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
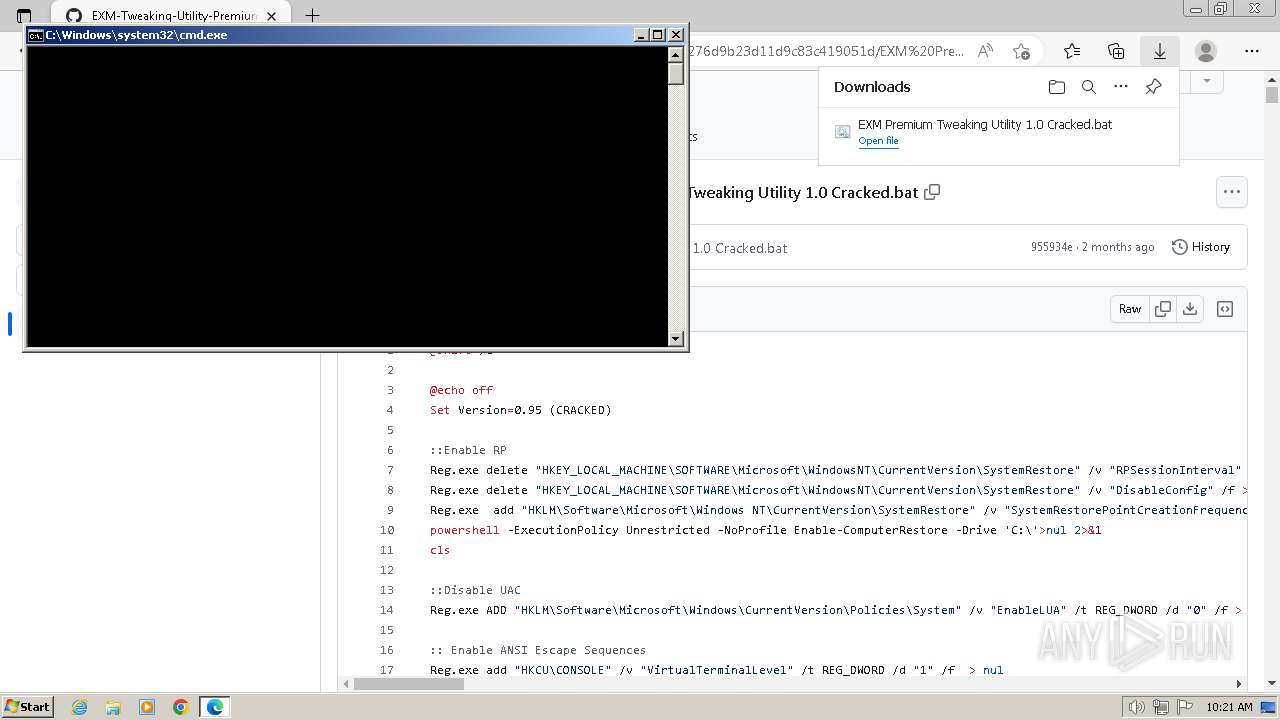
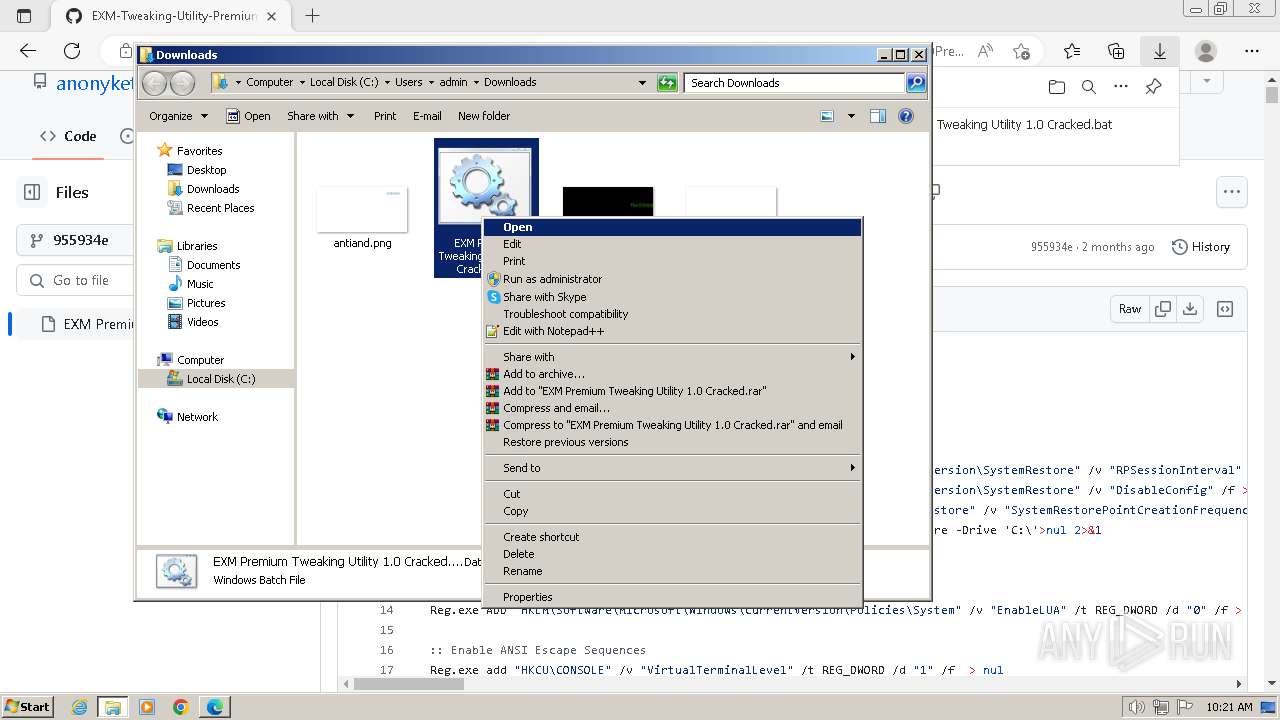
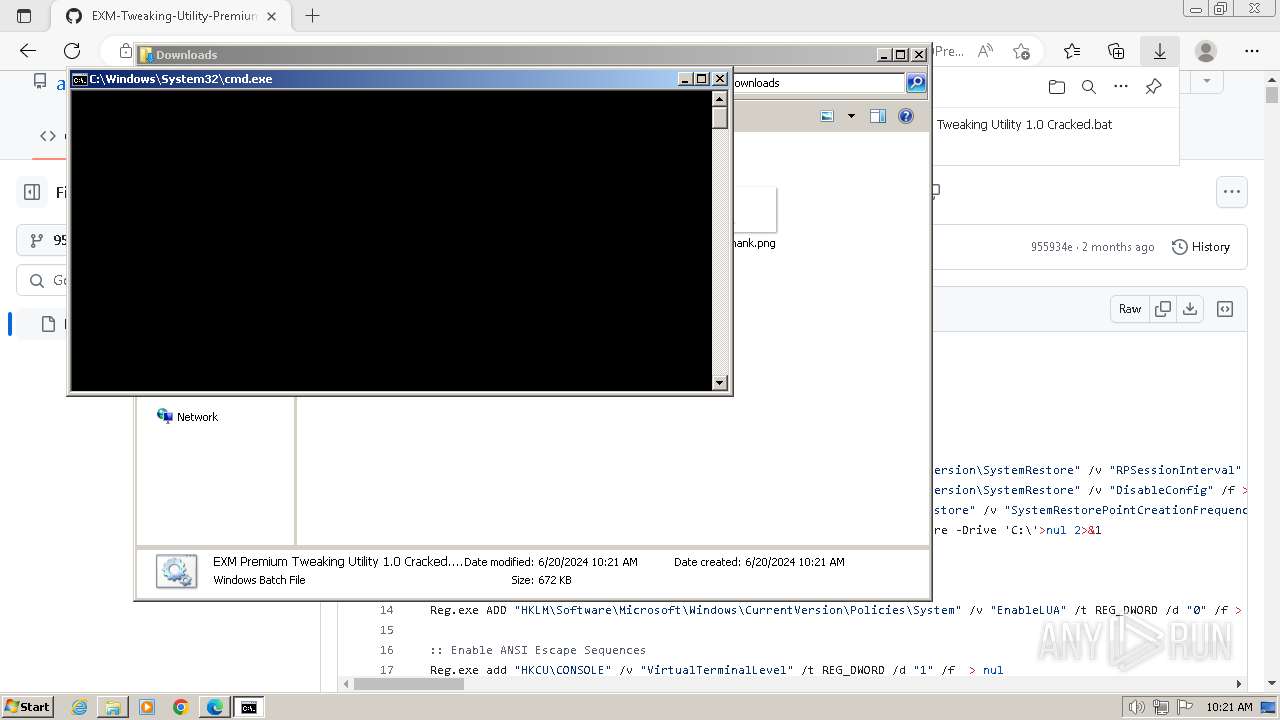
Starts CMD.EXE for commands execution
- msedge.exe (PID: 3268)
UAC/LUA settings modification
- reg.exe (PID: 568)
- reg.exe (PID: 3816)
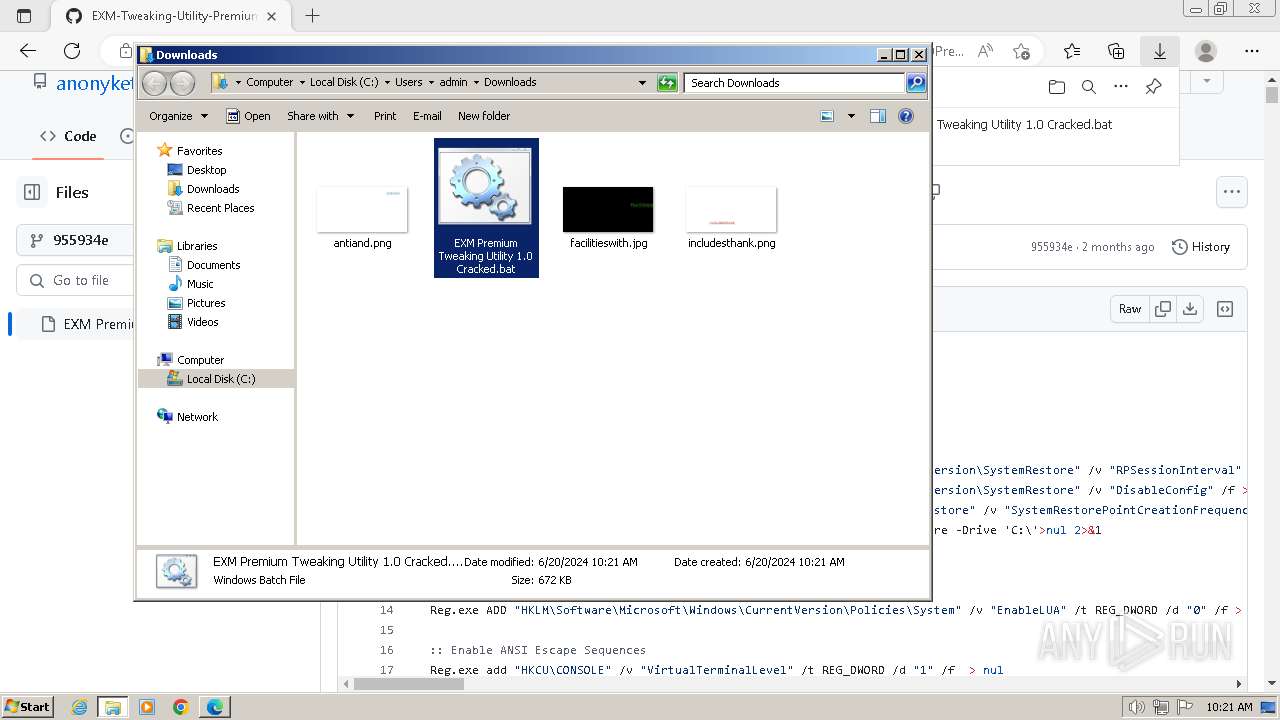
Drops the executable file immediately after the start
- curl.exe (PID: 3564)
SUSPICIOUS
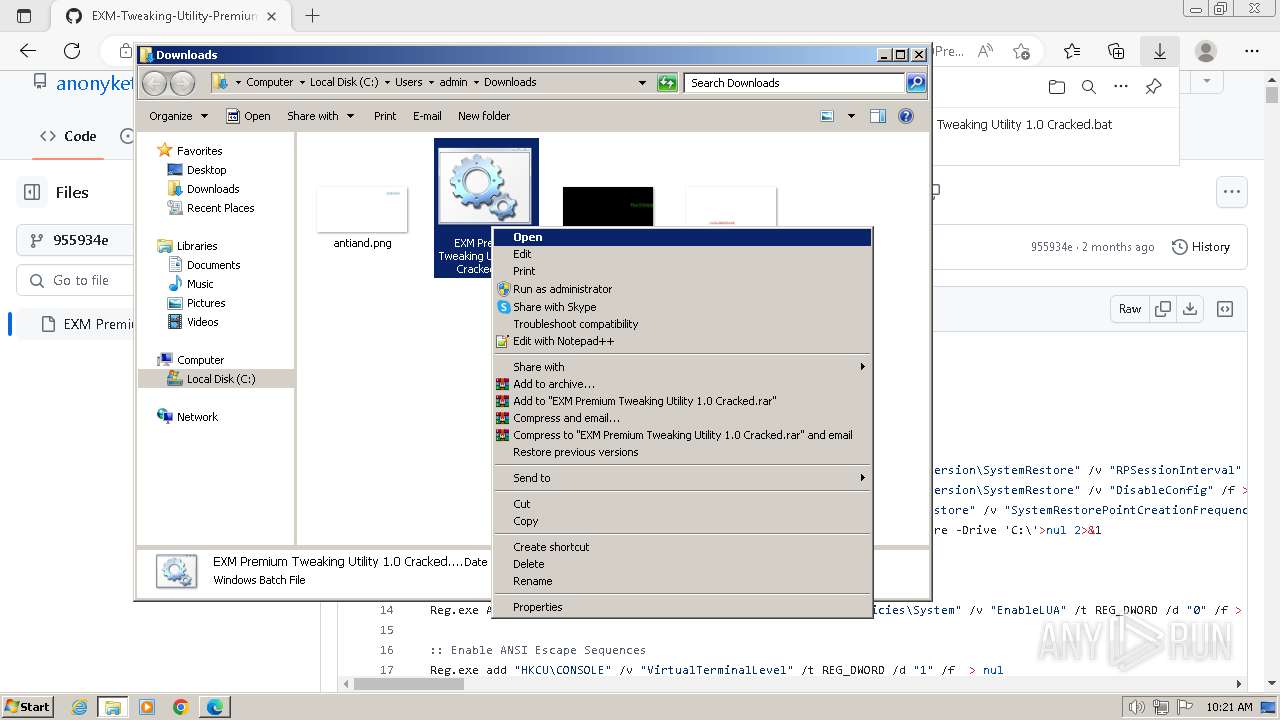
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2284)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2284)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
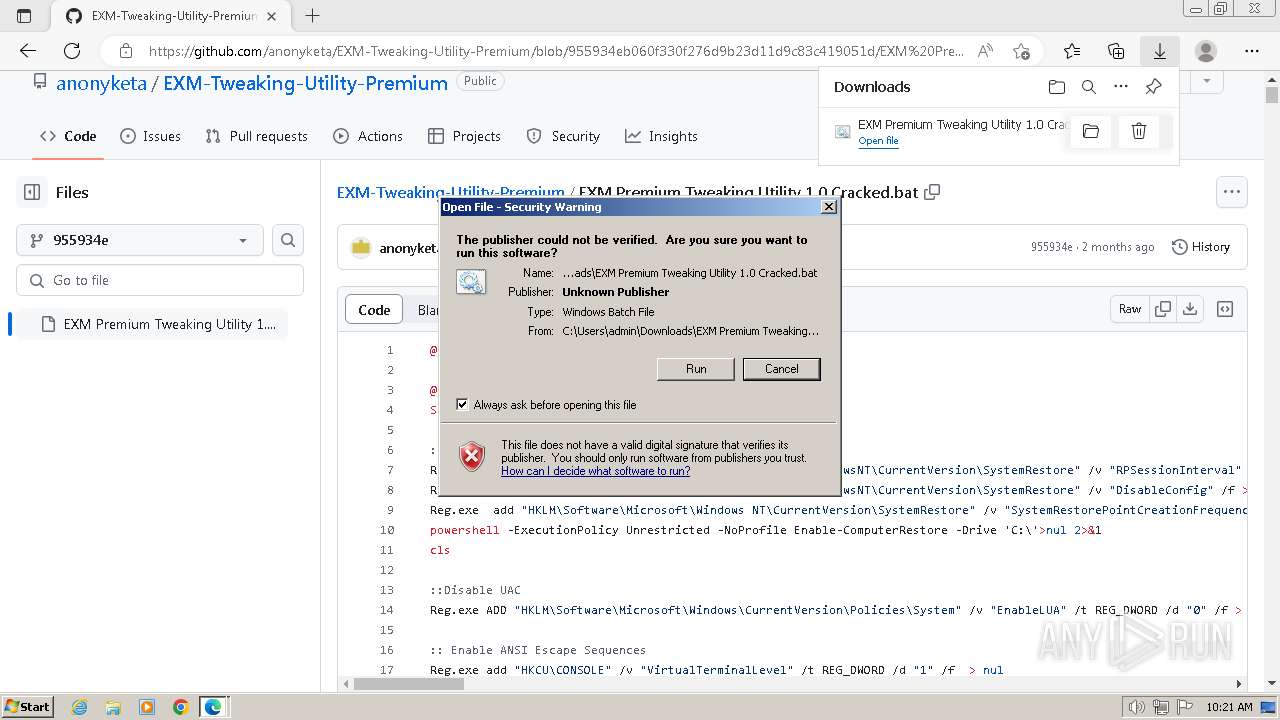
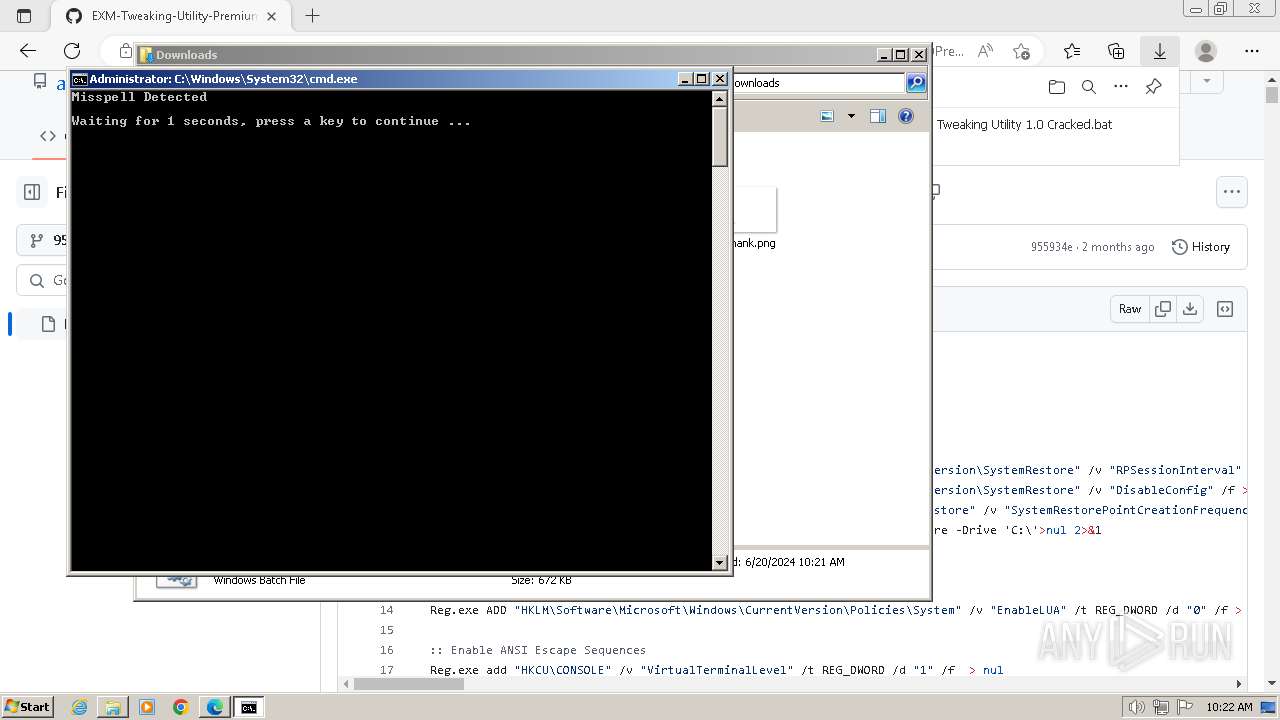
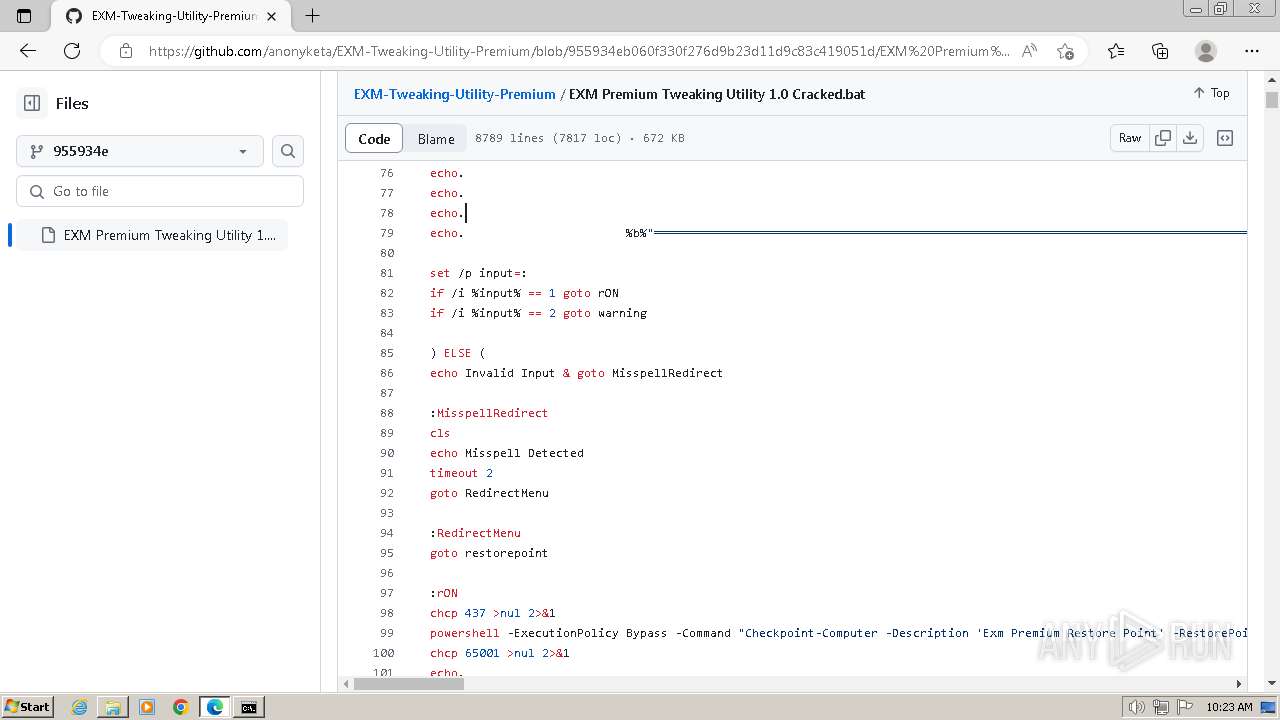
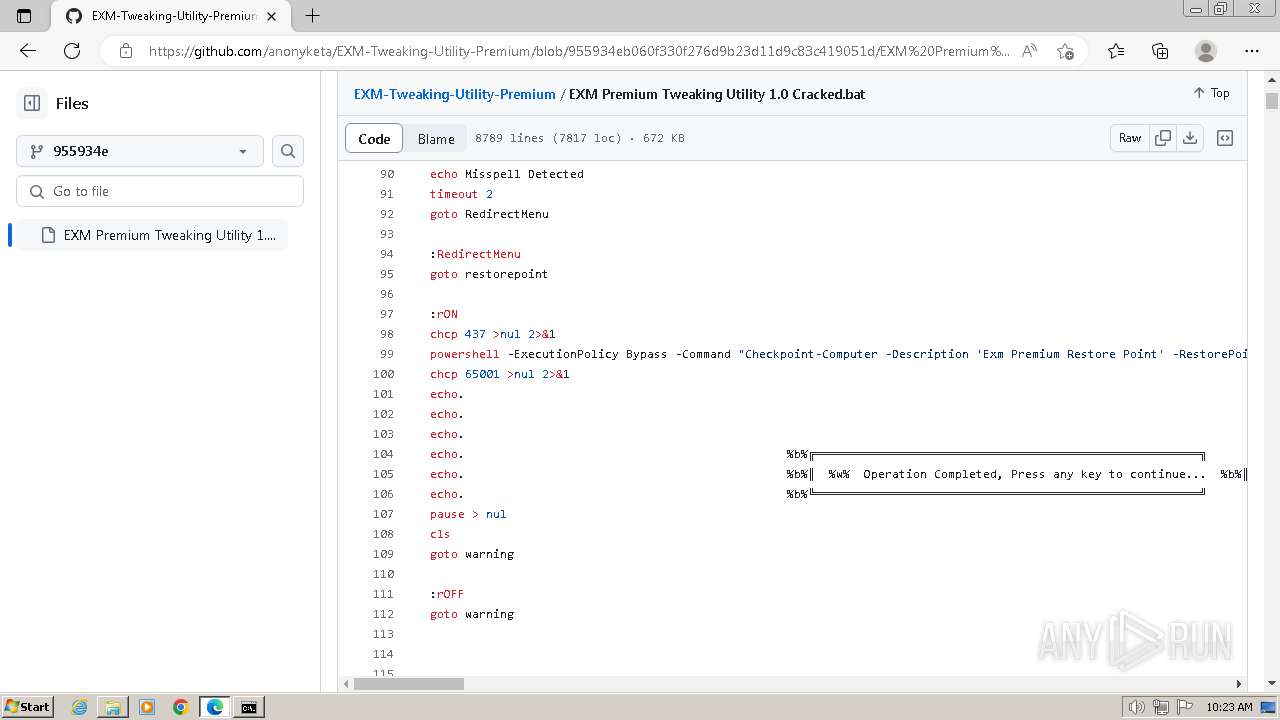
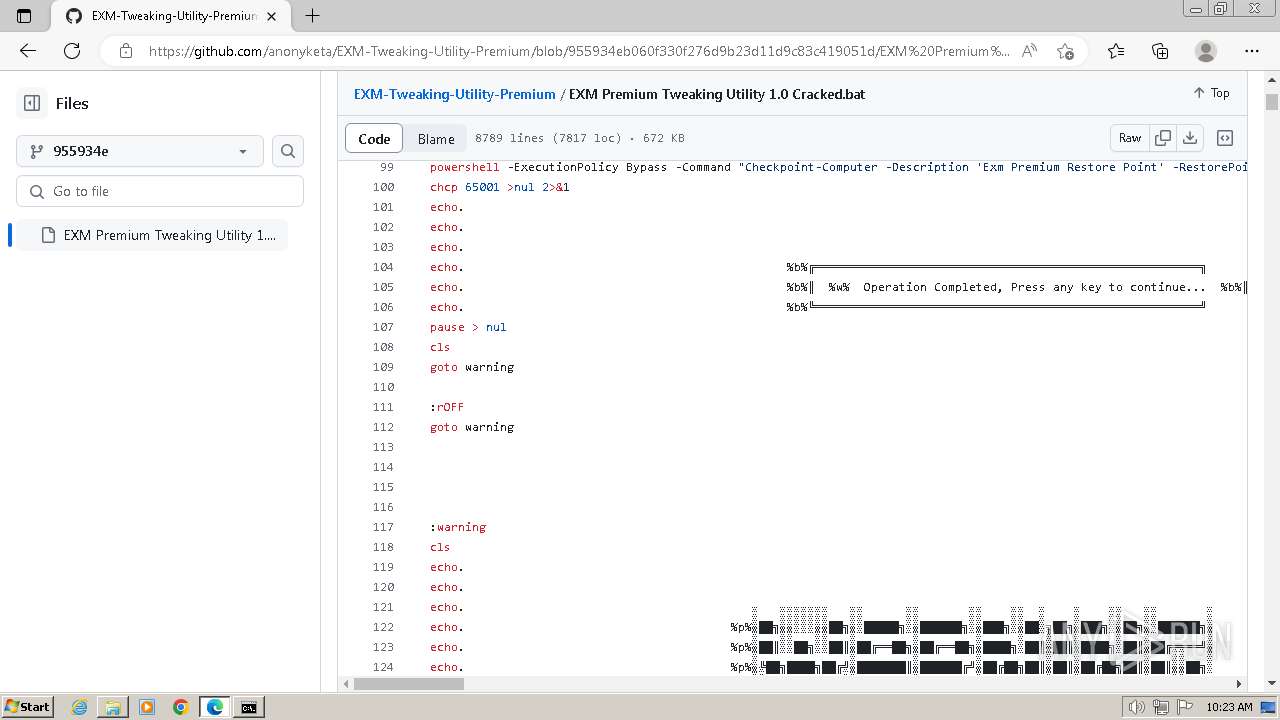
Executing commands from a ".bat" file
- msedge.exe (PID: 3268)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2284)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
The process hide an interactive prompt from the user
- cmd.exe (PID: 2284)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 3840)
- cmd.exe (PID: 1468)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3840)
- cmd.exe (PID: 1468)
Reads the Internet Settings
- WMIC.exe (PID: 4048)
- WMIC.exe (PID: 1000)
Starts application with an unusual extension
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2672)
Application launched itself
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2672)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1648)
INFO
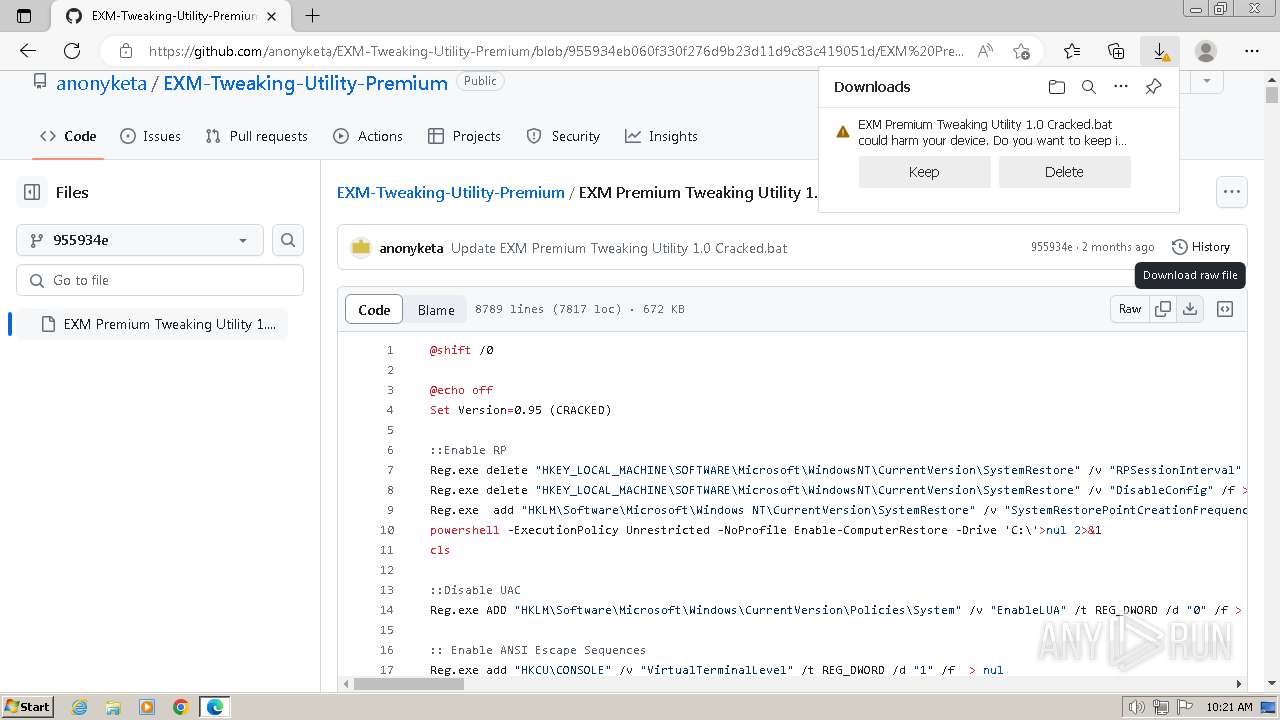
The process uses the downloaded file
- msedge.exe (PID: 1284)
- msedge.exe (PID: 3268)
Application launched itself
- msedge.exe (PID: 3268)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2716)
- powershell.exe (PID: 2400)
Manual execution by a user
- cmd.exe (PID: 2672)
- cmd.exe (PID: 1648)
Checks supported languages
- chcp.com (PID: 2424)
- curl.exe (PID: 3564)
- chcp.com (PID: 2396)
- chcp.com (PID: 2112)
Create files in a temporary directory
- curl.exe (PID: 3564)
Reads the computer name
- curl.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
104
Monitored processes
57
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | Reg.exe add "HKCU\CONSOLE" /v "VirtualTerminalLevel" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1340,i,3669849255326638165,18271220898256931940,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 568 | Reg.exe ADD "HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t REG_DWORD /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2180 --field-trial-handle=1340,i,3669849255326638165,18271220898256931940,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1000 | wmic path Win32_UserAccount where name="admin" get sid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | Reg.exe delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\SystemRestore" /v "DisableConfig" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3560 --field-trial-handle=1340,i,3669849255326638165,18271220898256931940,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4336 --field-trial-handle=1340,i,3669849255326638165,18271220898256931940,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1468 | C:\Windows\system32\cmd.exe /c wmic path Win32_UserAccount where name="admin" get sid | findstr "S-" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1648 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\Downloads\EXM Premium Tweaking Utility 1.0 Cracked.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
27 771
Read events
27 683
Write events
76
Delete events
12
Modification events
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 7E0DCF1BE5792F00 | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3268) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
0
Suspicious files
258
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4dd9b.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4ddaa.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4ddba.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4dde9.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:4B74C392839DDD59792975091A30DB00 | SHA256:7A5A3B8CC4D5BB579FA5E6C6A831964FB245A5CFF9AD3B80F5E9DC34DA4A7D53 | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C58936C151151A55BE239180C023FBA1 | SHA256:EAC76E0907364A6317E231CFA2D62D50A3BE020D95BAB3541A41123BF93544E0 | |||
| 3268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:599EE96A37069C802B2B7AF08E7A22FA | SHA256:496E41B4DB940FD3A078BD07EF2FA13C7F9E272A214AFD673E51502E7BCD63CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
49
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 72.247.153.162:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3268 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2956 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2956 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2956 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
1372 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2956 | msedge.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |