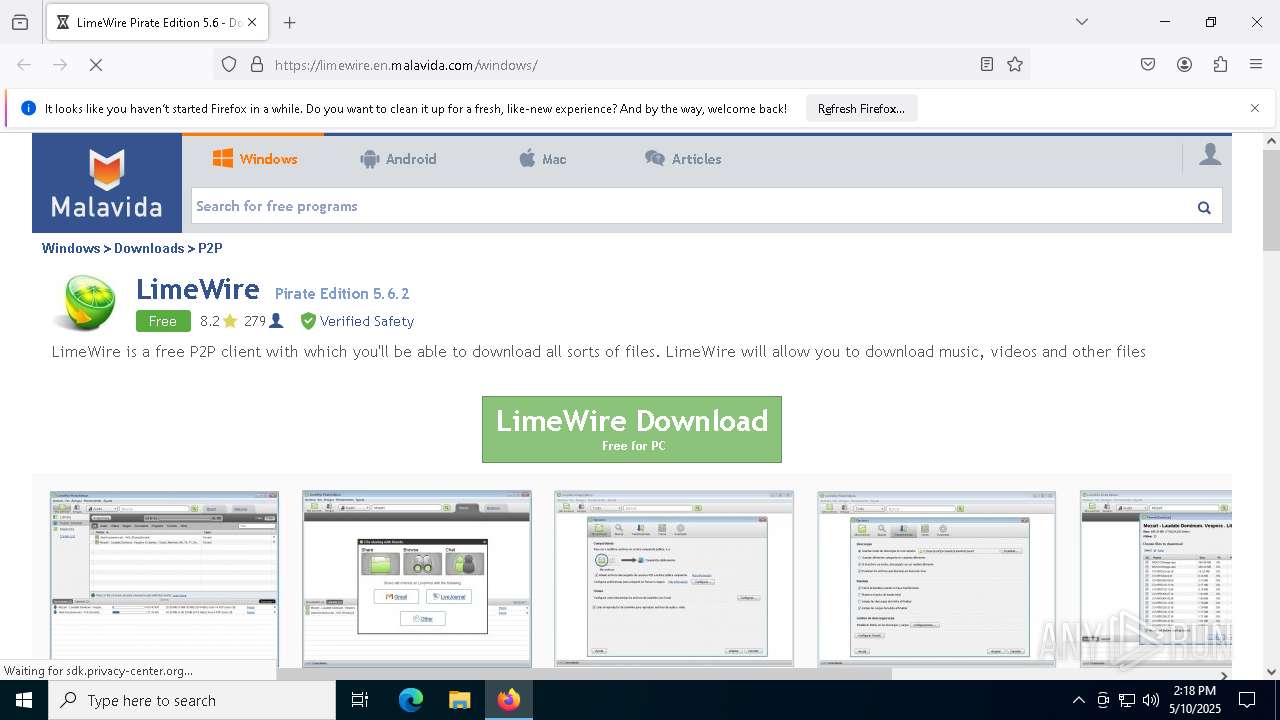
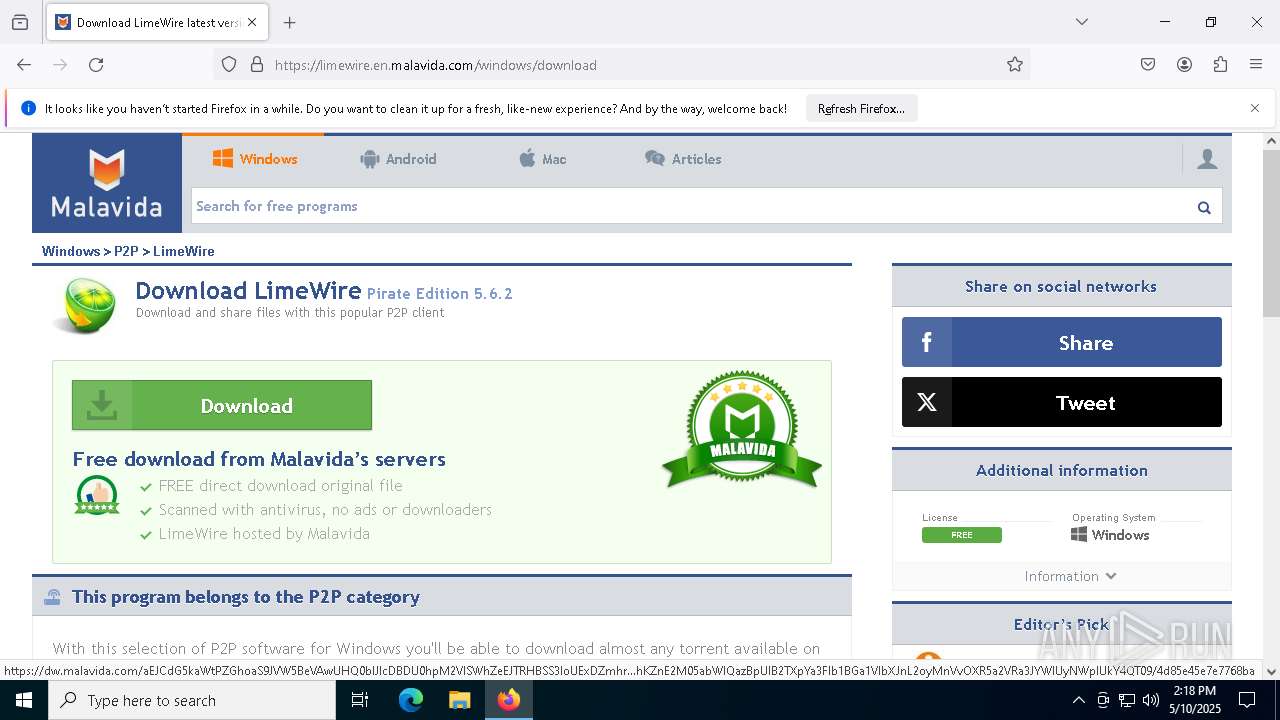
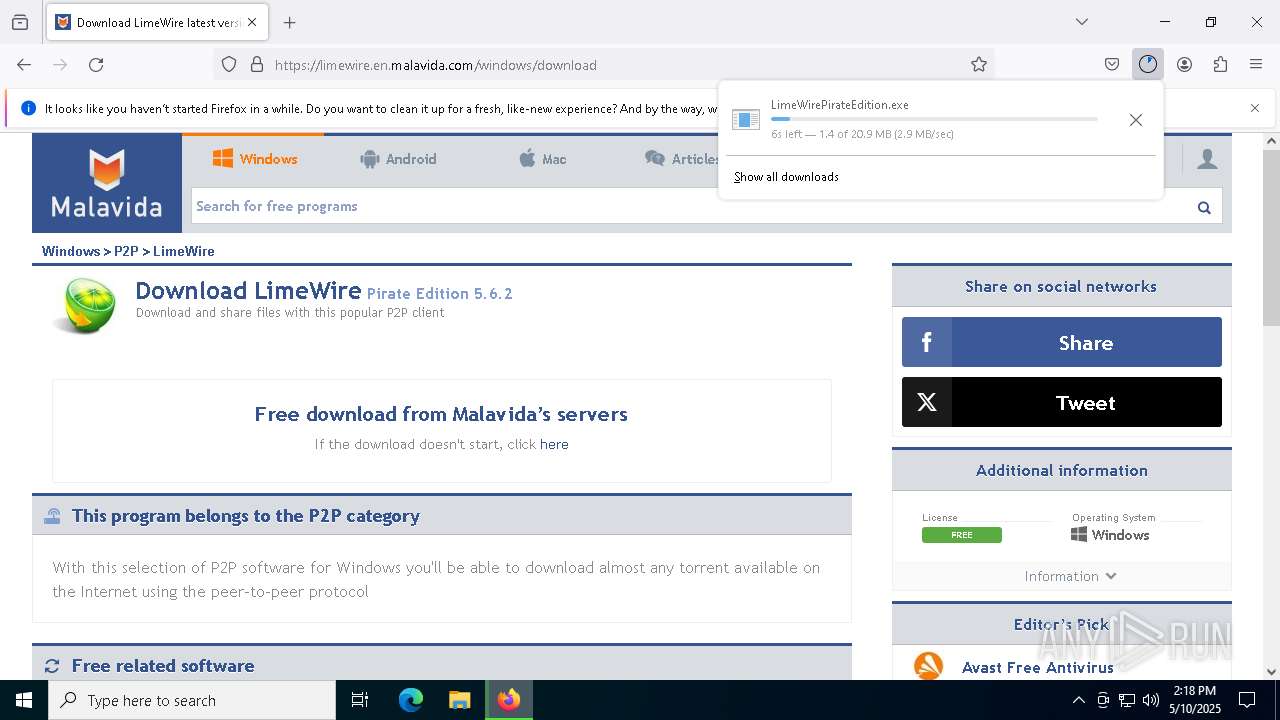
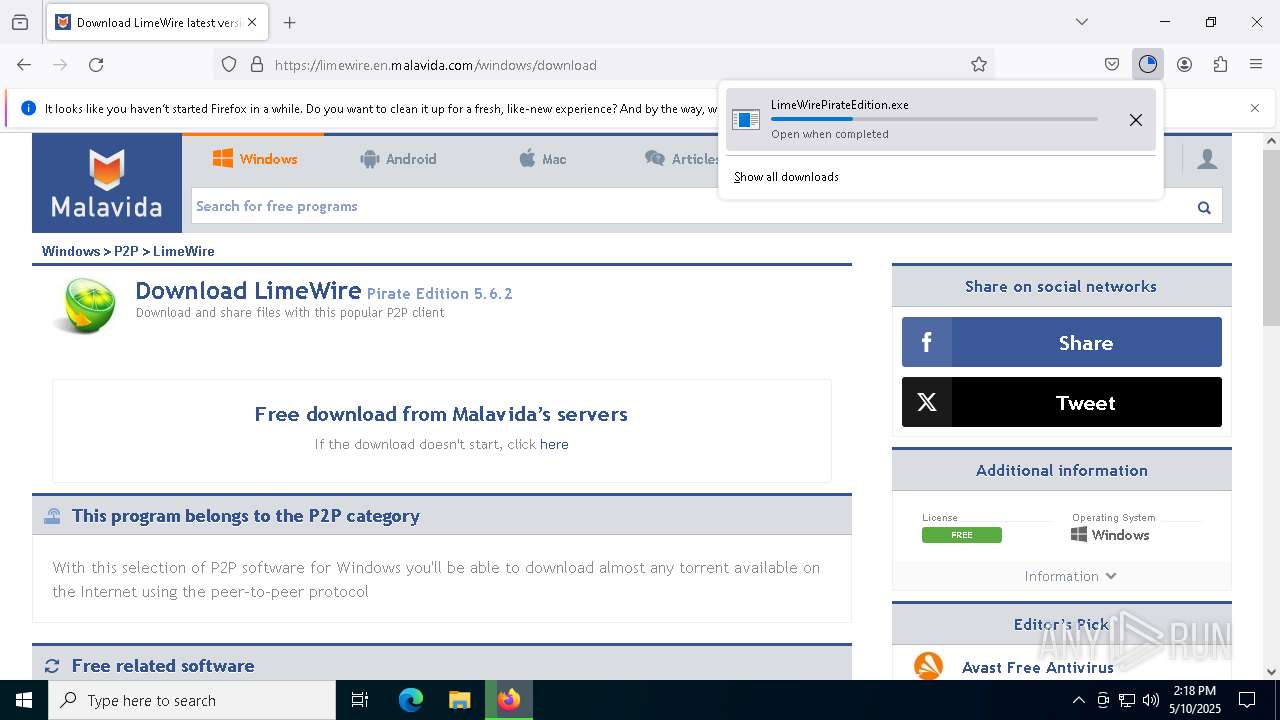
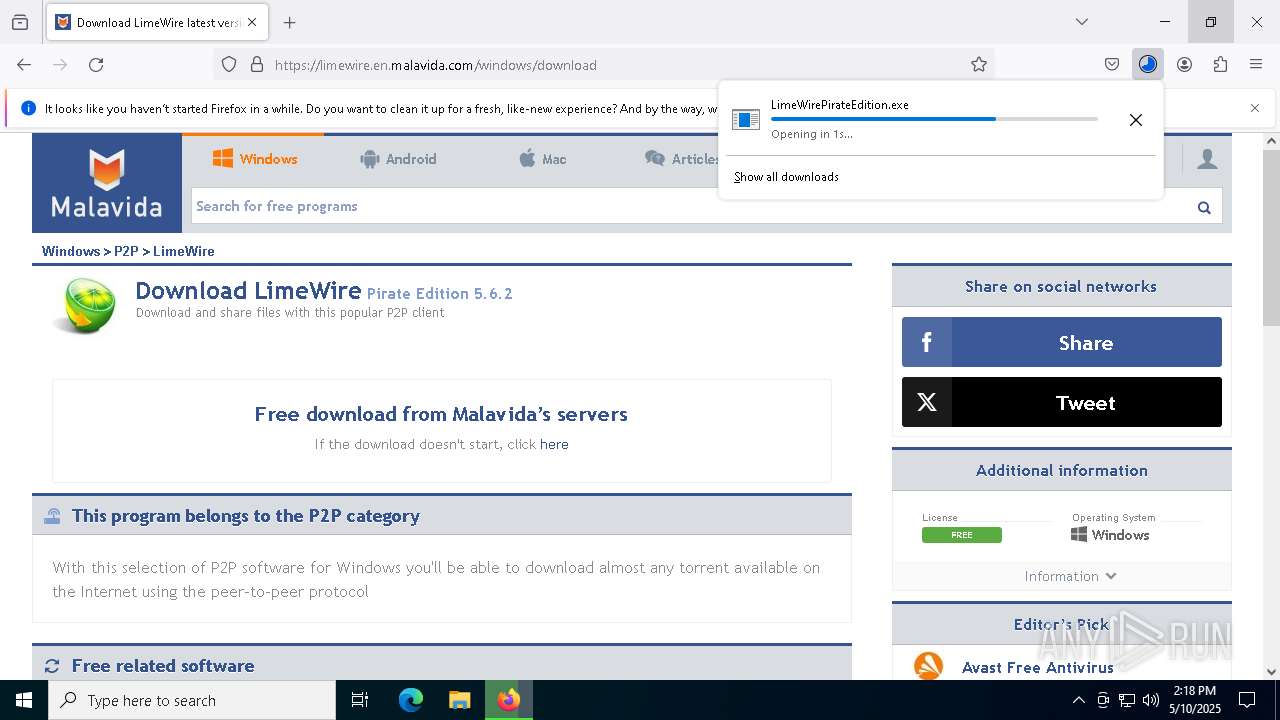
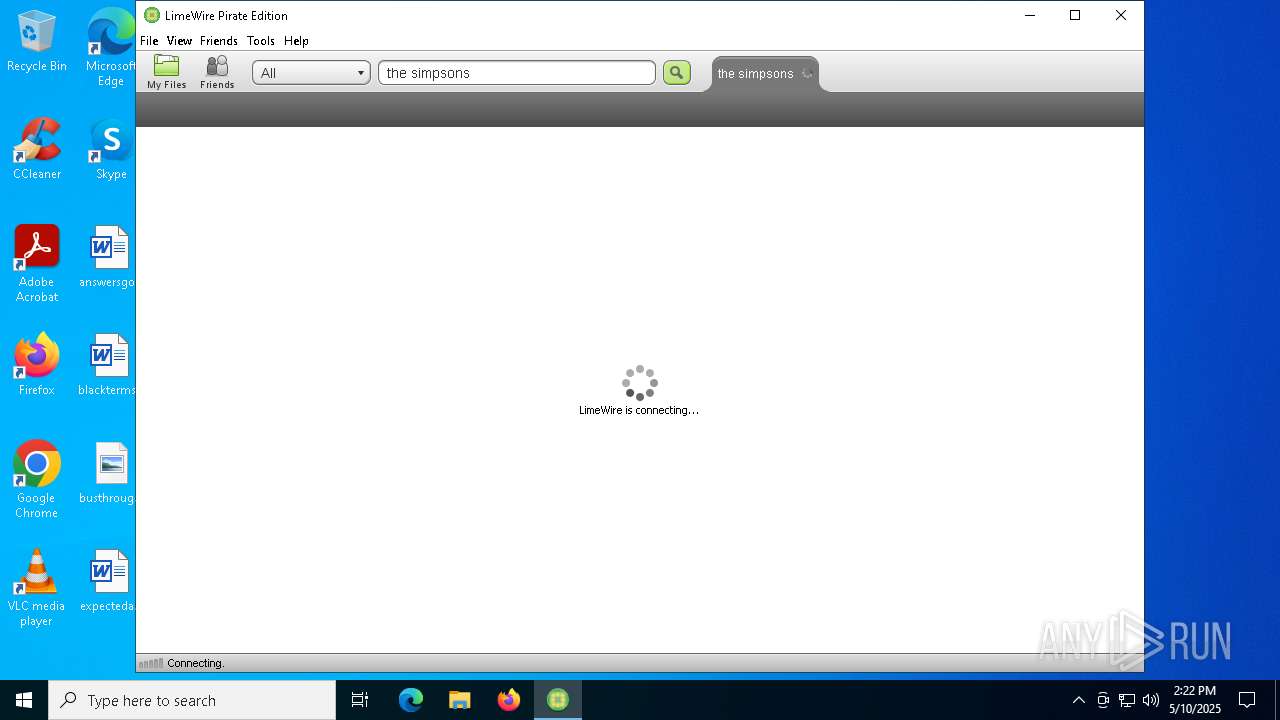
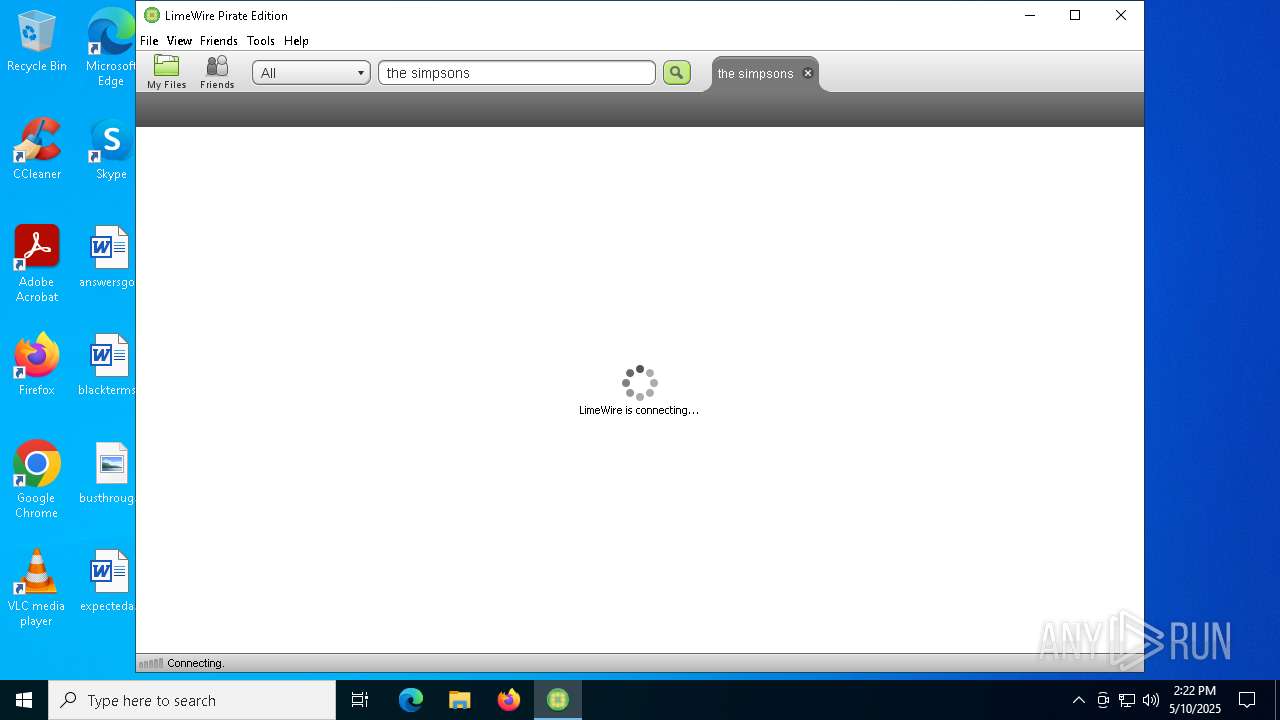
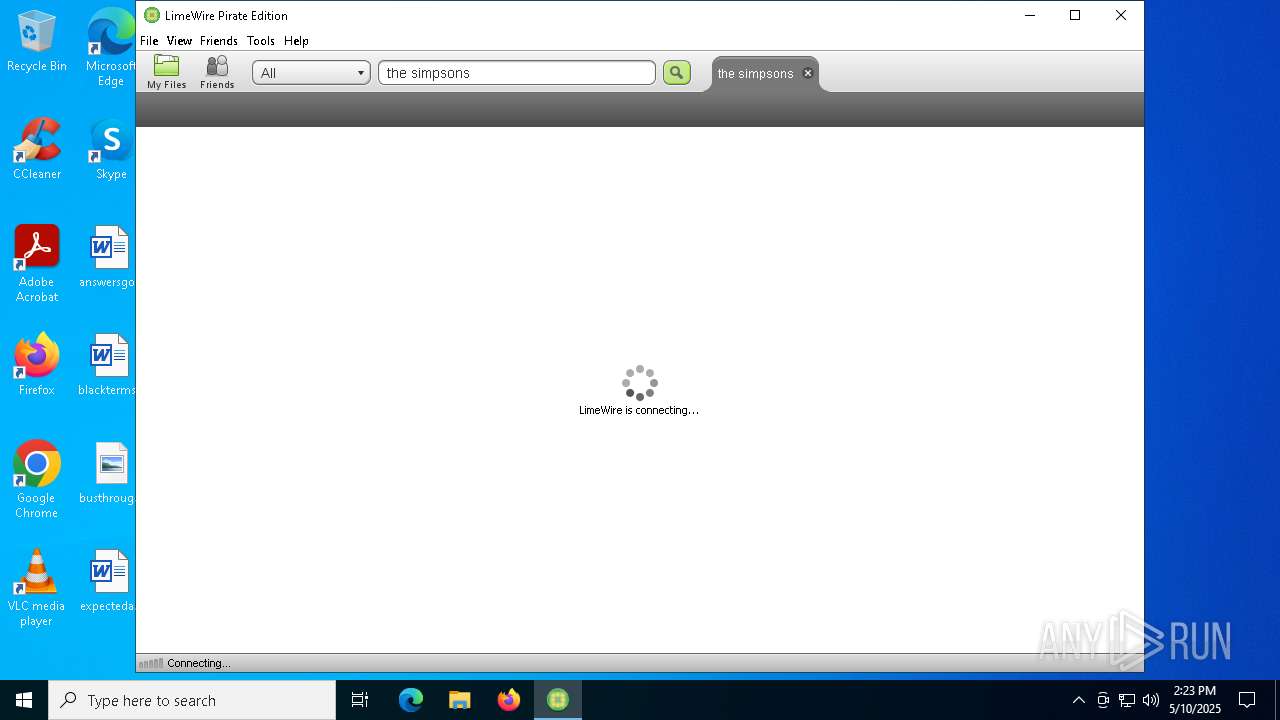
| URL: | https://limewire.en.malavida.com/windows/ |
| Full analysis: | https://app.any.run/tasks/a6b35e39-5ea0-462f-8e80-31f4b78fa173 |
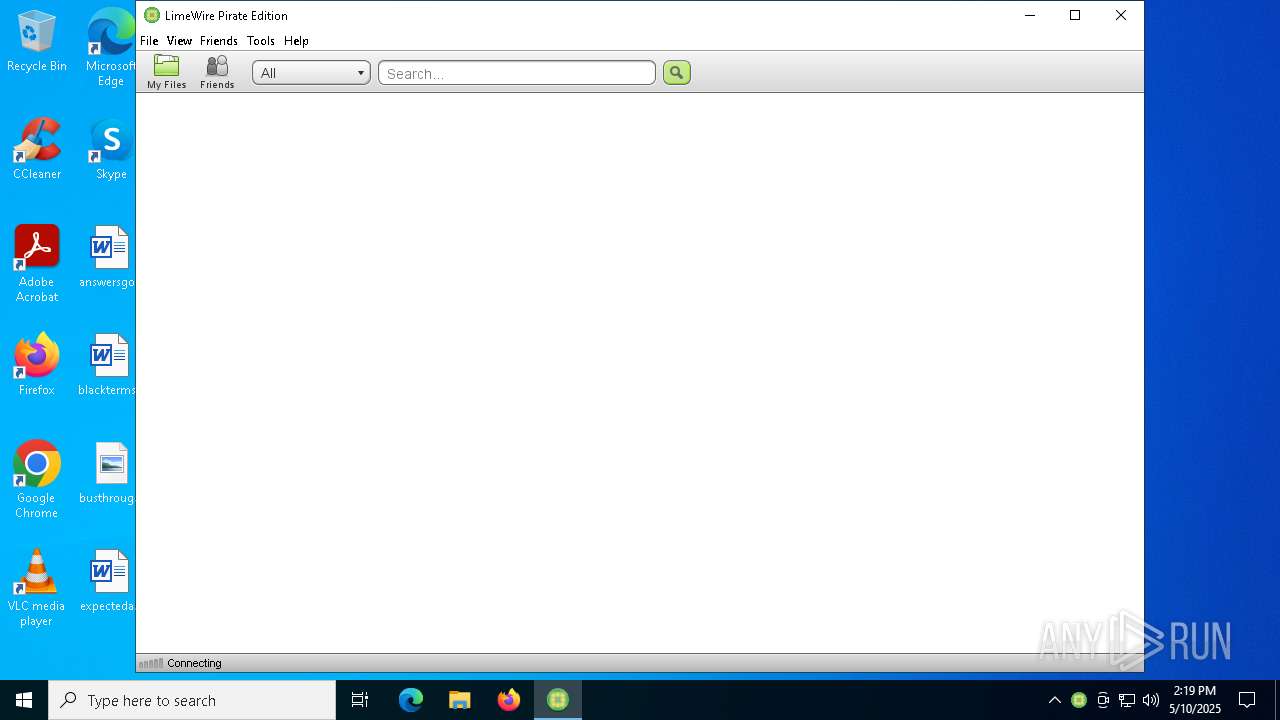
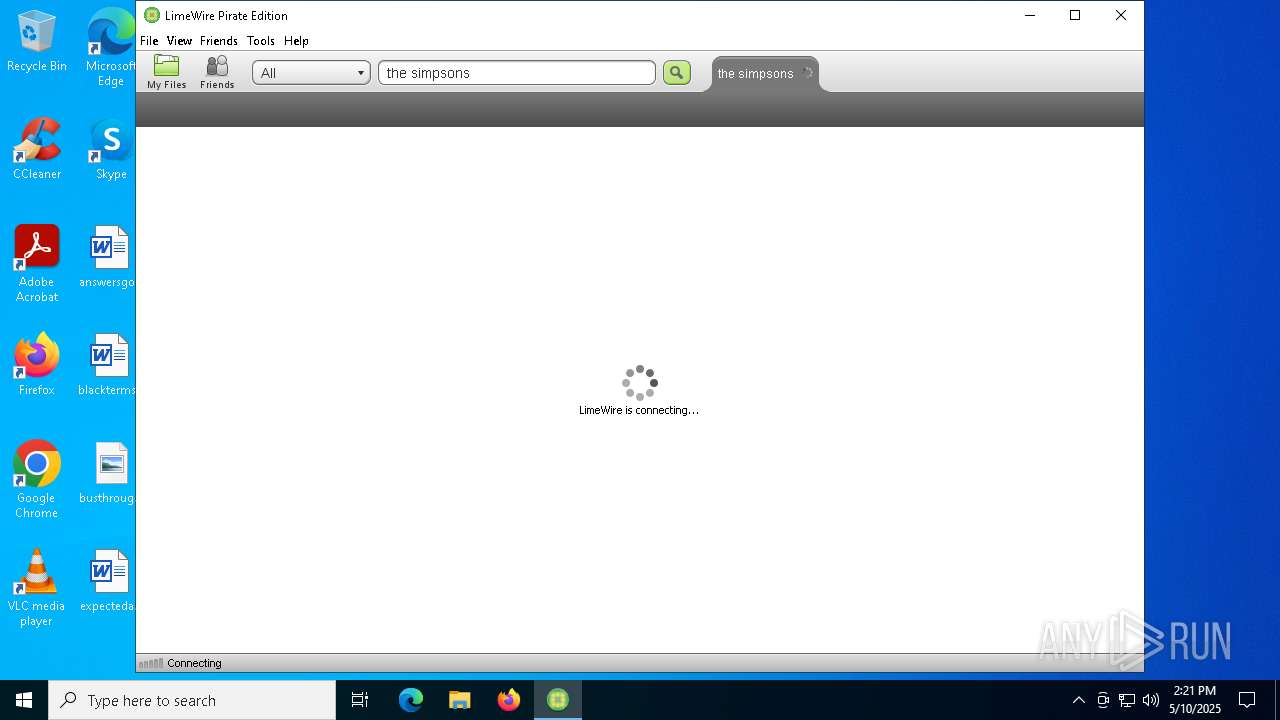
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 14:18:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC26864F2716DF2ACDCAF0B9E6D0A898 |
| SHA1: | 449763FE9B0698EC74B064C71DA73AECADD89E50 |
| SHA256: | 57C7F16BC30944EA6C1ACB9FF10FC8F1506D29261988F1AA04D64215C3782201 |
| SSDEEP: | 3:N8MIA/euez9:2MIA/euY |
MALICIOUS
Executing a file with an untrusted certificate
- jrestub.exe (PID: 7564)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 8732)
- unpack200.exe (PID: 896)
- unpack200.exe (PID: 8804)
- unpack200.exe (PID: 2100)
- unpack200.exe (PID: 8760)
- unpack200.exe (PID: 8768)
- javaw.exe (PID: 9056)
- javaw.exe (PID: 9112)
Changes the autorun value in the registry
- msiexec.exe (PID: 4200)
SUSPICIOUS
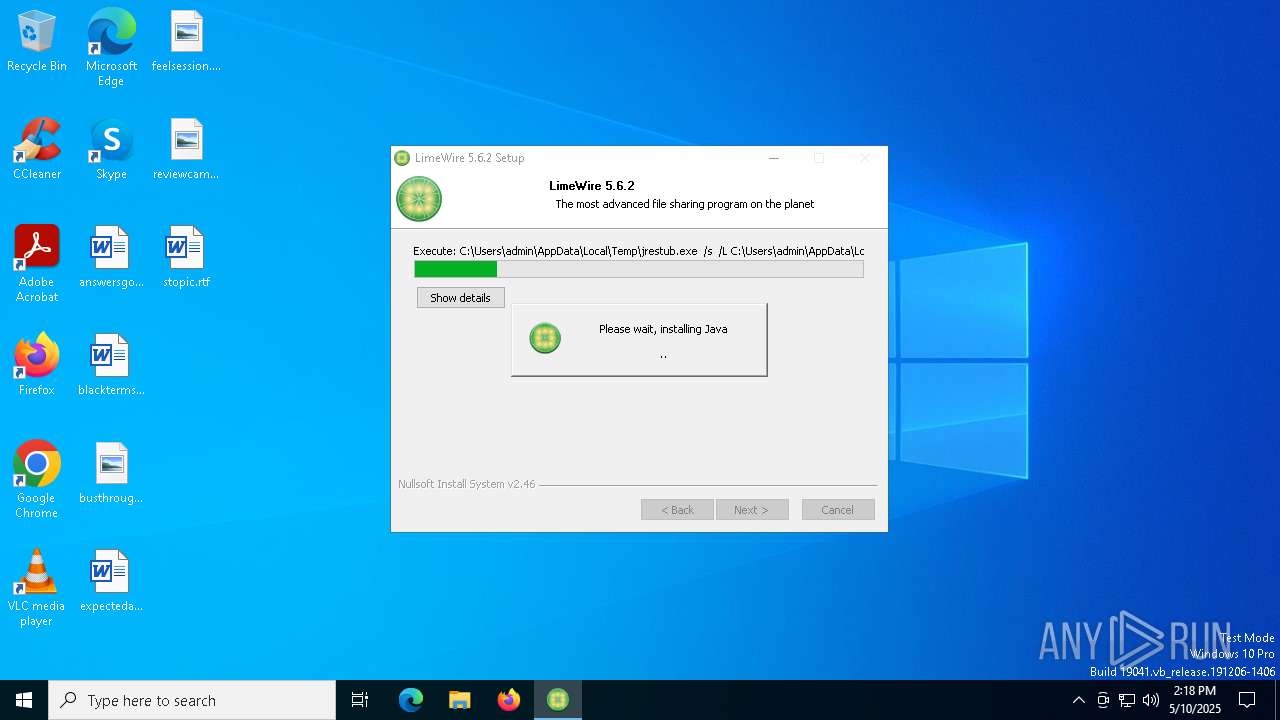
Adds/modifies Windows certificates
- jrestub.exe (PID: 7564)
Reads security settings of Internet Explorer
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 4200)
- msiexec.exe (PID: 8580)
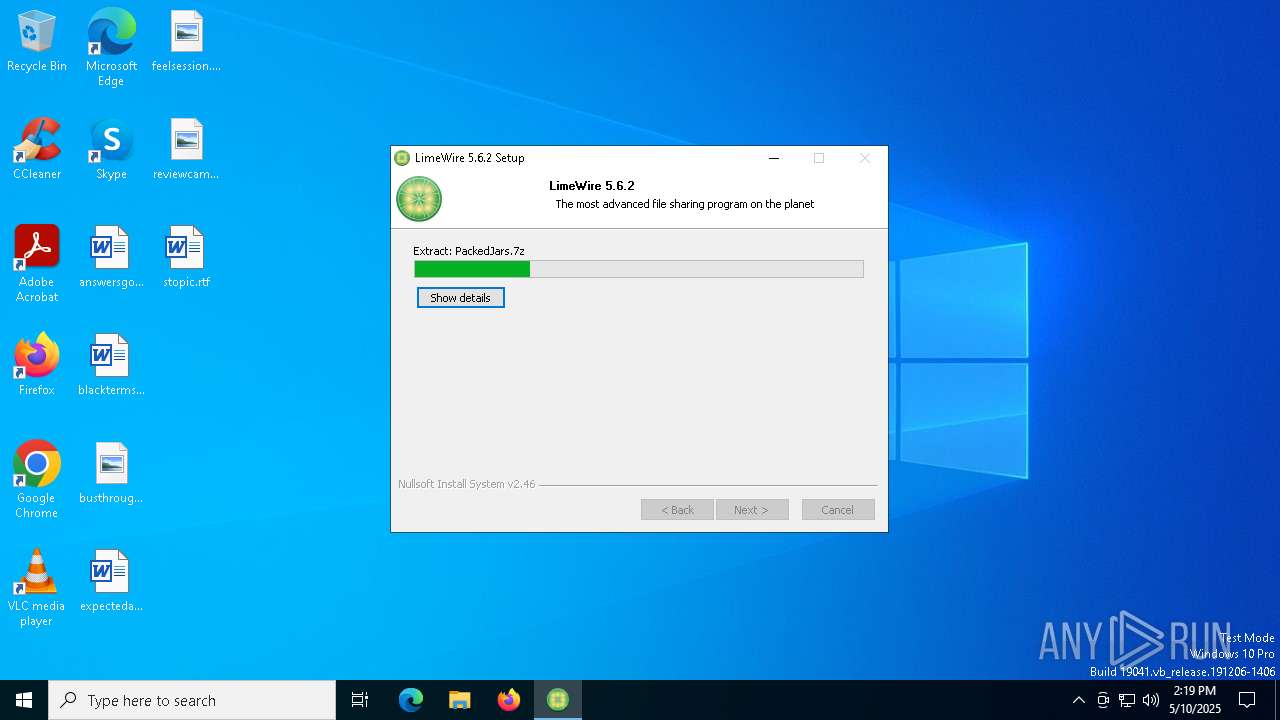
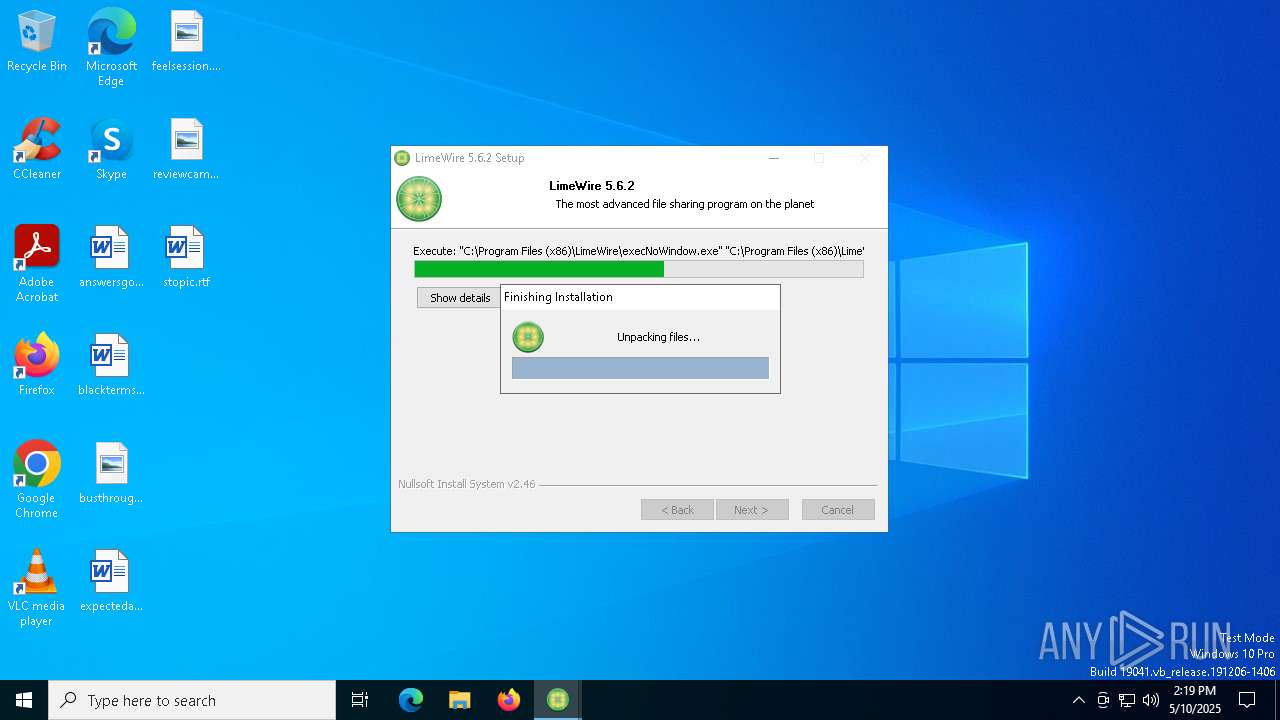
Executable content was dropped or overwritten
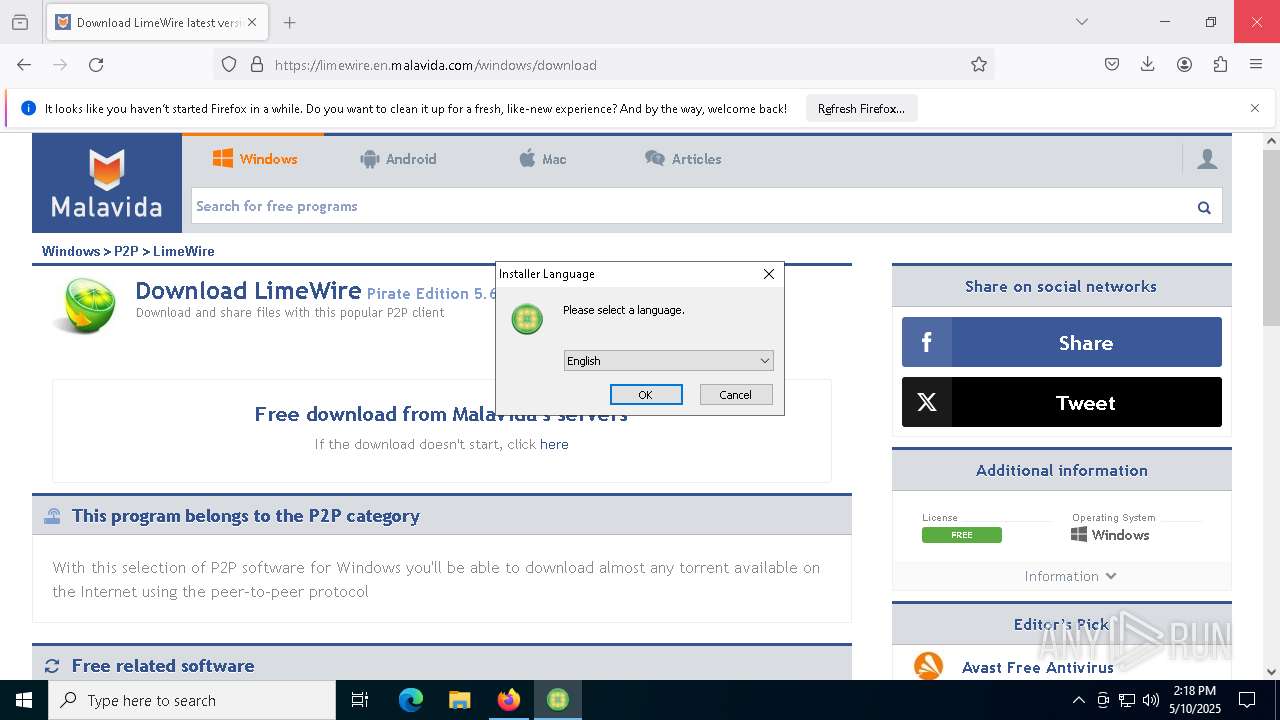
- LimeWirePirateEdition.exe (PID: 9120)
- jrestub.exe (PID: 7564)
- zipper.exe (PID: 4208)
- LimeWire.exe (PID: 7848)
Checks for Java to be installed
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5436)
- msiexec.exe (PID: 4200)
- msiexec.exe (PID: 8580)
- LimeWirePirateEdition.exe (PID: 9120)
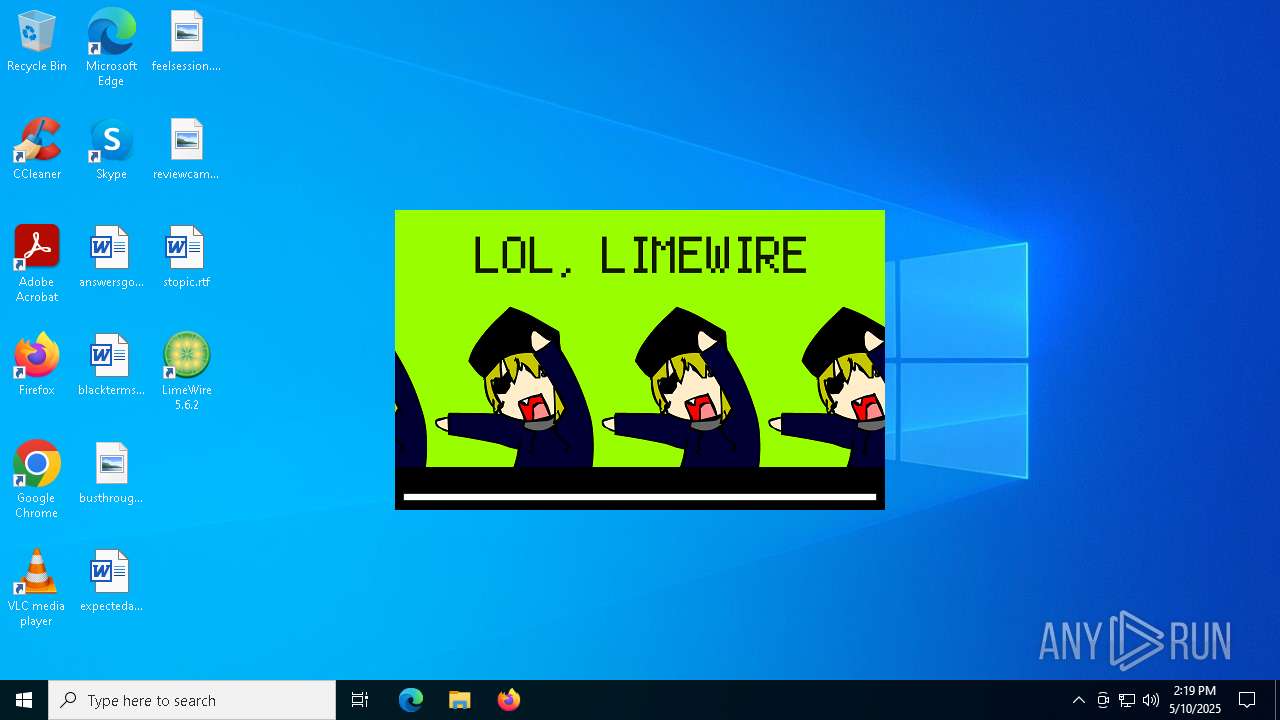
There is functionality for taking screenshot (YARA)
- LimeWirePirateEdition.exe (PID: 9120)
- jrestub.exe (PID: 7564)
- LimeWire.exe (PID: 7848)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5436)
Process drops legitimate windows executable
- zipper.exe (PID: 4208)
- msiexec.exe (PID: 4200)
- LimeWirePirateEdition.exe (PID: 9120)
- LimeWire.exe (PID: 7848)
The process drops C-runtime libraries
- zipper.exe (PID: 4208)
- msiexec.exe (PID: 4200)
- LimeWirePirateEdition.exe (PID: 9120)
- LimeWire.exe (PID: 7848)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 4200)
- LimeWirePirateEdition.exe (PID: 9120)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 9112)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8468)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 7612)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 8224)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 5968)
The process creates files with name similar to system file names
- LimeWirePirateEdition.exe (PID: 9120)
Malware-specific behavior (creating "System.dll" in Temp)
- LimeWirePirateEdition.exe (PID: 9120)
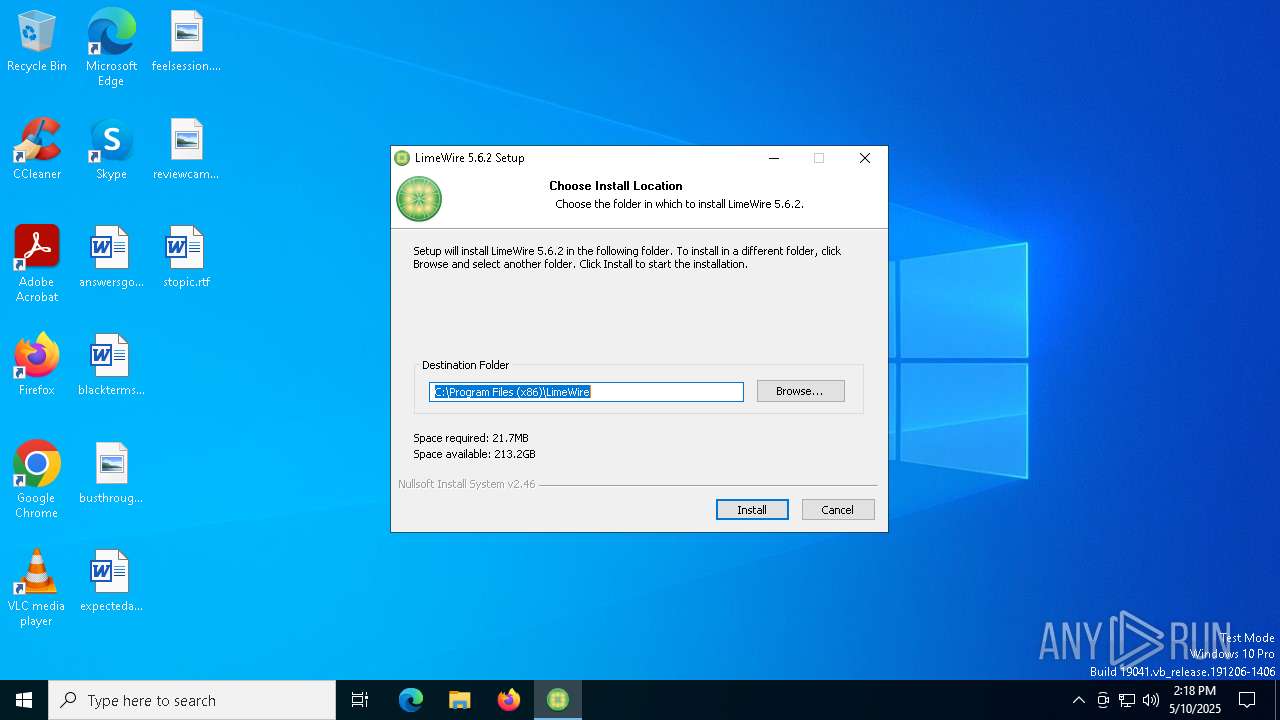
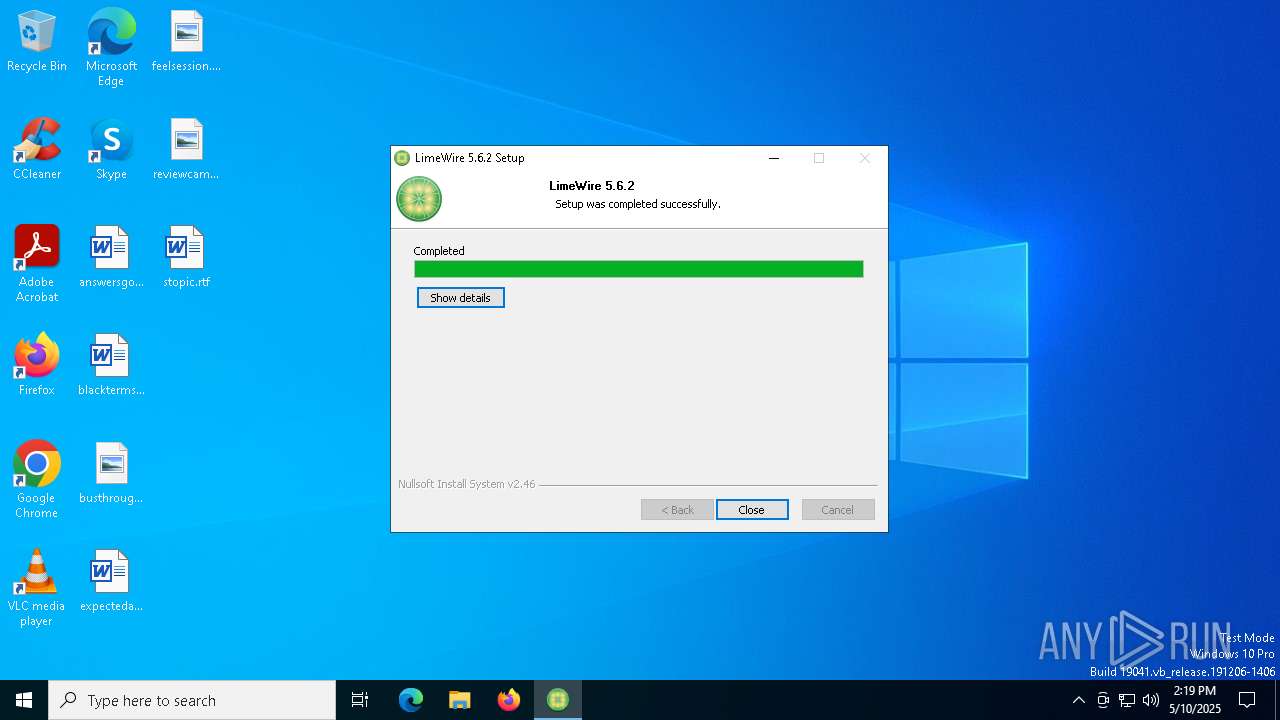
Creates a software uninstall entry
- LimeWirePirateEdition.exe (PID: 9120)
Connects to unusual port
- LimeWire.exe (PID: 7848)
There is functionality for communication over UDP network (YARA)
- LimeWire.exe (PID: 7848)
INFO
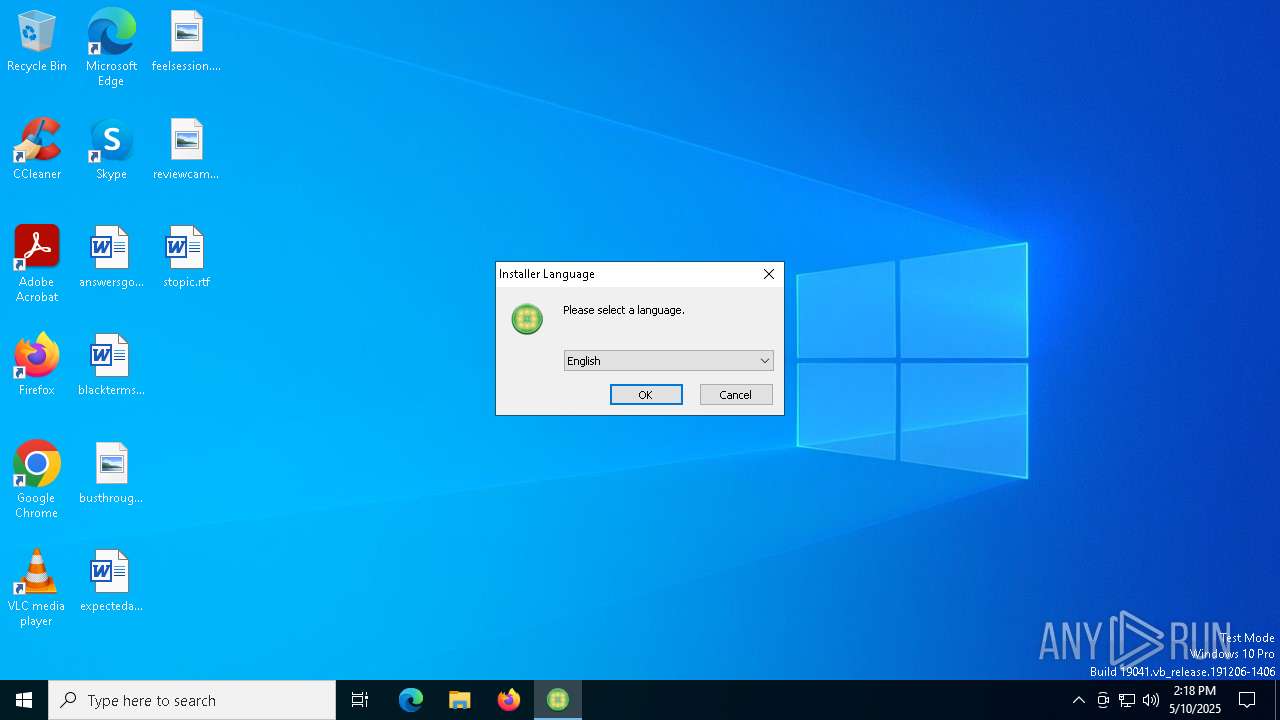
Checks supported languages
- LimeWirePirateEdition.exe (PID: 9120)
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5436)
- msiexec.exe (PID: 8580)
- msiexec.exe (PID: 4200)
- zipper.exe (PID: 4208)
- unpack200.exe (PID: 8732)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 896)
- unpack200.exe (PID: 8804)
- unpack200.exe (PID: 2100)
- unpack200.exe (PID: 8768)
- unpack200.exe (PID: 8760)
- javaw.exe (PID: 9056)
- javaw.exe (PID: 9112)
- jaureg.exe (PID: 7808)
- execNoWindow.exe (PID: 8200)
- unpack200.exe (PID: 8196)
Executable content was dropped or overwritten
- firefox.exe (PID: 5960)
- msiexec.exe (PID: 5436)
- msiexec.exe (PID: 4200)
Application launched itself
- firefox.exe (PID: 1272)
- firefox.exe (PID: 5960)
Creates files or folders in the user directory
- jrestub.exe (PID: 7564)
- javaw.exe (PID: 9112)
- msiexec.exe (PID: 8580)
- LimeWirePirateEdition.exe (PID: 9120)
Reads the software policy settings
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5436)
- msiexec.exe (PID: 8580)
Reads the machine GUID from the registry
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5436)
- javaw.exe (PID: 9112)
- msiexec.exe (PID: 8580)
Creates files in the program directory
- LimeWirePirateEdition.exe (PID: 9120)
- zipper.exe (PID: 4208)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 8732)
- unpack200.exe (PID: 896)
- unpack200.exe (PID: 8804)
- unpack200.exe (PID: 2100)
- unpack200.exe (PID: 8768)
- unpack200.exe (PID: 8760)
- javaw.exe (PID: 9056)
- javaw.exe (PID: 9112)
- unpack200.exe (PID: 8196)
Create files in a temporary directory
- LimeWirePirateEdition.exe (PID: 9120)
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 4200)
- javaw.exe (PID: 9056)
- javaw.exe (PID: 9112)
The sample compiled with english language support
- LimeWirePirateEdition.exe (PID: 9120)
- msiexec.exe (PID: 5436)
- zipper.exe (PID: 4208)
- msiexec.exe (PID: 4200)
- LimeWire.exe (PID: 7848)
Reads the computer name
- LimeWirePirateEdition.exe (PID: 9120)
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 5436)
- msiexec.exe (PID: 8580)
- msiexec.exe (PID: 4200)
- javaw.exe (PID: 9112)
Checks proxy server information
- jrestub.exe (PID: 7564)
- msiexec.exe (PID: 8580)
Reads CPU info
- msiexec.exe (PID: 5436)
Creates a software uninstall entry
- msiexec.exe (PID: 5436)
UPX packer has been detected
- jrestub.exe (PID: 7564)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7636)
- WMIC.exe (PID: 7700)
- WMIC.exe (PID: 8636)
- WMIC.exe (PID: 8280)
- WMIC.exe (PID: 8404)
Reads the time zone
- javaw.exe (PID: 9112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
52
Malicious processes
7
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files (x86)\Java\jre6\bin\unpack200.exe" -r -v -l "C:\Users\admin\AppData\Local\Temp\java_install.log" "C:\Program Files (x86)\Java\jre6\lib\plugin.pack" "C:\Program Files (x86)\Java\jre6\lib\plugin.jar" | C:\Program Files (x86)\Java\jre6\bin\unpack200.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Sun Microsystems, Inc. Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 6.0.180.7 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://limewire.en.malavida.com/windows/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2100 | "C:\Program Files (x86)\Java\jre6\bin\unpack200.exe" -r -v -l "C:\Users\admin\AppData\Local\Temp\java_install.log" "C:\Program Files (x86)\Java\jre6\lib\deploy.pack" "C:\Program Files (x86)\Java\jre6\lib\deploy.jar" | C:\Program Files (x86)\Java\jre6\bin\unpack200.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Sun Microsystems, Inc. Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 6.0.180.7 Modules
| |||||||||||||||
| 3140 | "C:\Program Files (x86)\Java\jre6\bin\unpack200.exe" -r -v -l "C:\Users\admin\AppData\Local\Temp\java_install.log" "C:\Program Files (x86)\Java\jre6\lib\rt.pack" "C:\Program Files (x86)\Java\jre6\lib\rt.jar" | C:\Program Files (x86)\Java\jre6\bin\unpack200.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Sun Microsystems, Inc. Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 6.0.180.7 Modules
| |||||||||||||||
| 4200 | C:\Windows\syswow64\MsiExec.exe -Embedding 93882953277E72E0121329A57E99764D E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | "C:\Program Files (x86)\Java\jre6\zipper.exe" "C:\Program Files (x86)\Java\jre6\core.zip" "C:\Program Files (x86)\Java\jre6\" "C:\Users\admin\AppData\Local\Temp\java_install.log" | C:\Program Files (x86)\Java\jre6\zipper.exe | msiexec.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 4996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5260 -childID 5 -isForBrowser -prefsHandle 5152 -prefMapHandle 5124 -prefsLen 38183 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c78d7c8c-4d62-4adb-ad9a-134c6c2941af} 5960 "\\.\pipe\gecko-crash-server-pipe.5960" 209e20e5310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5436 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5252 -childID 4 -isForBrowser -prefsHandle 5172 -prefMapHandle 5176 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2d38841f-ee3a-4584-a90f-1134e2670196} 5960 "\\.\pipe\gecko-crash-server-pipe.5960" 209e20e5d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5960 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://limewire.en.malavida.com/windows/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
29 564
Read events
28 627
Write events
864
Delete events
73
Modification events
| (PID) Process: | (5960) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5960) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | VisitorId |
Value: 1138df681-f60531d8c | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Method |
Value: jother | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | PostStatusUrl |
Value: https://sjremetrics.java.com/b/ss//6 | |||
| (PID) Process: | (7564) jrestub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Country |
Value: DE | |||
Executable files
219
Suspicious files
823
Text files
238
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:BAD406480E50FEC8956978F7FE331991 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 5960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:5ED7B2DFD892AA92F0508BF791FFCE31 | SHA256:8DCAC108993CECF602E06641E9E6B63B8BB13D944210762802B9DE162E7A1802 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
334
DNS requests
153
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.157:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5960 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5960 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 184.24.77.77:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 184.24.77.77:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5960 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.157:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5960 | firefox.exe | 23.50.131.142:443 | limewire.en.malavida.com | Akamai International B.V. | DE | suspicious |
5960 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5960 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5960 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
limewire.en.malavida.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
e185695.dscb.akamaiedge.net |
| unknown |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |