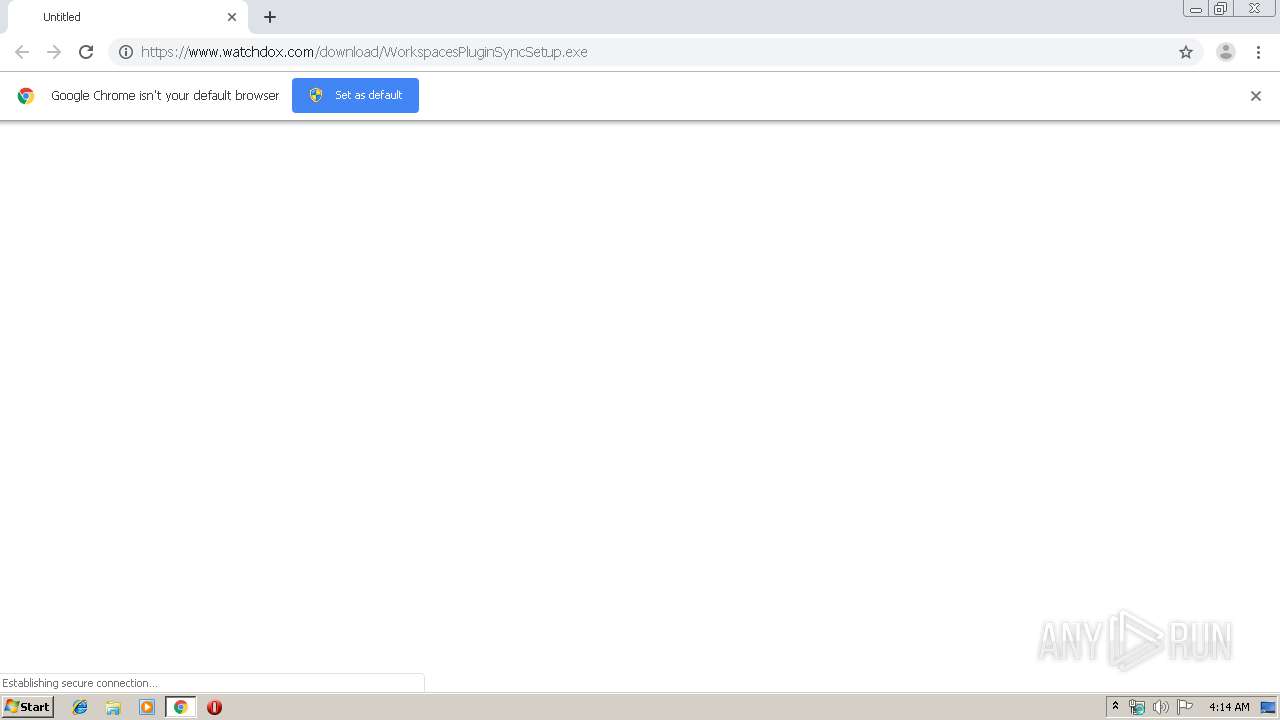
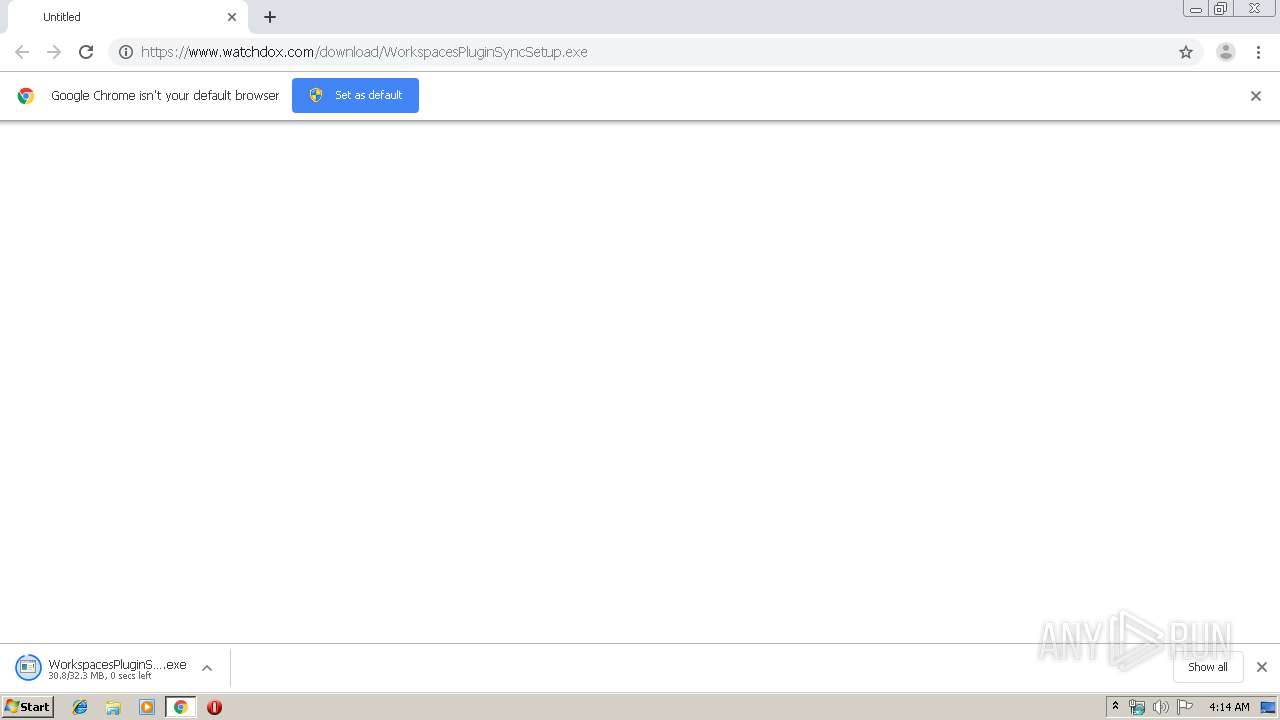
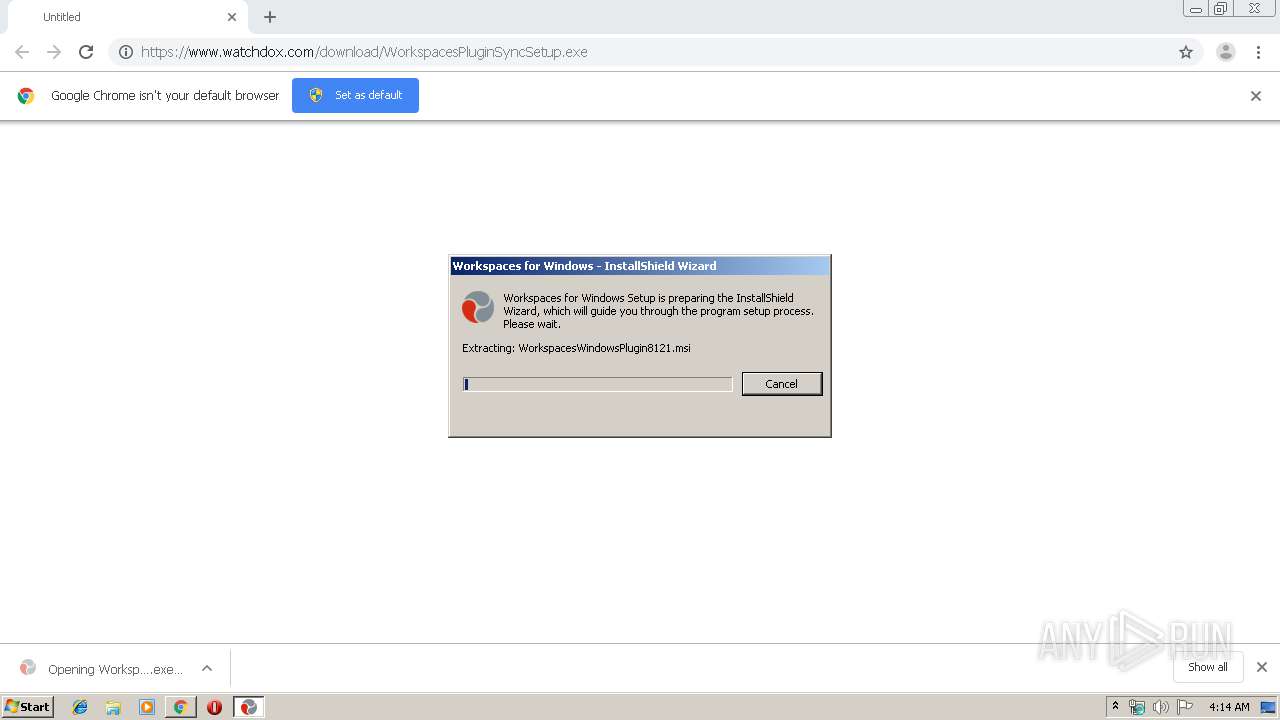
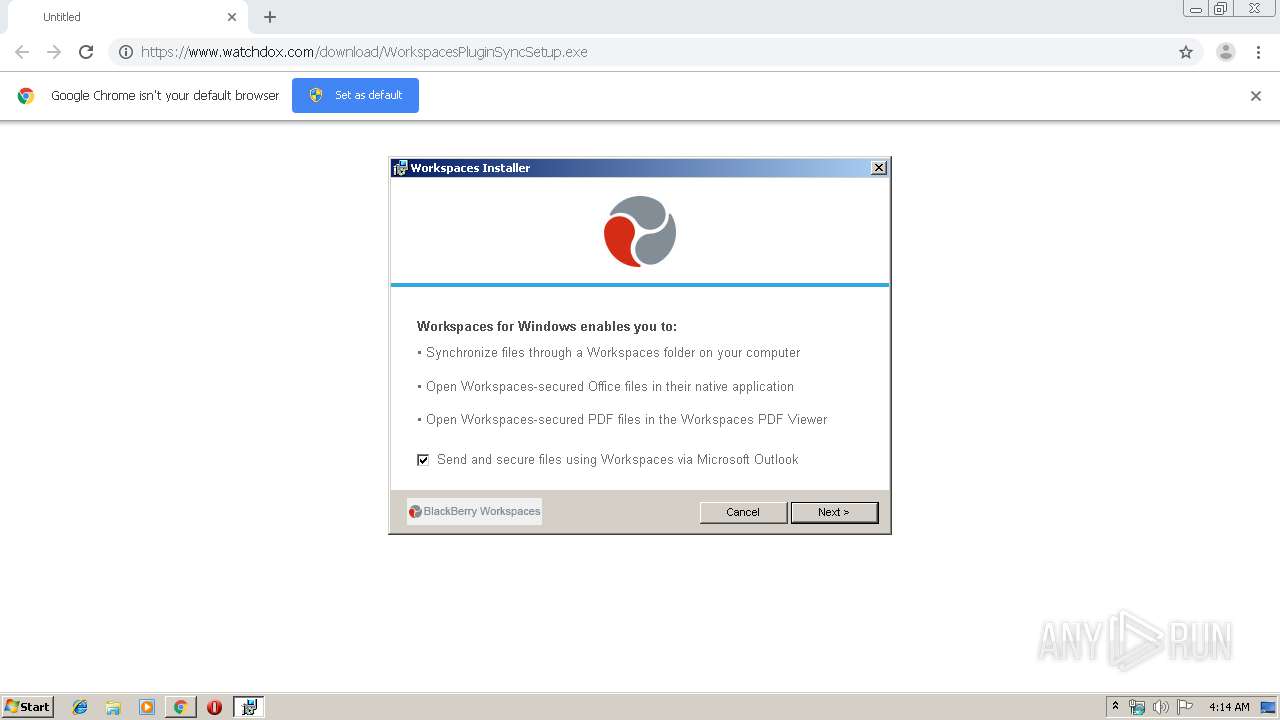
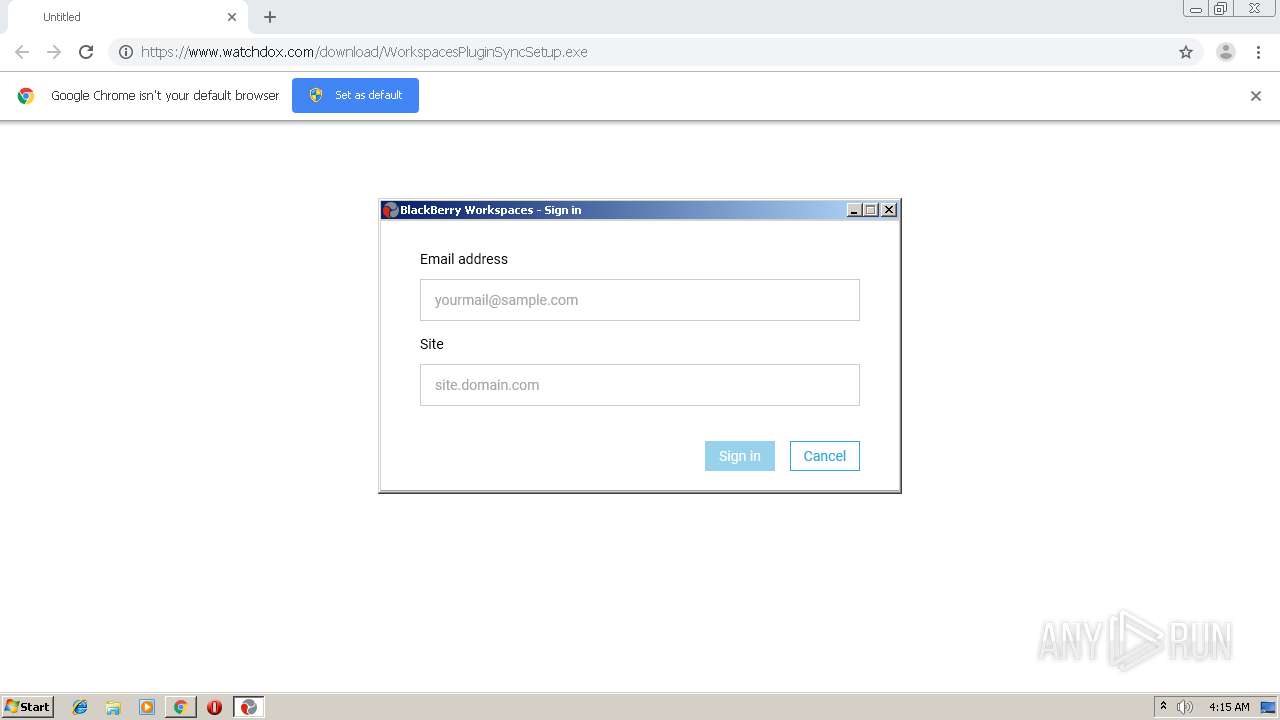
| URL: | https://www.watchdox.com/download/WorkspacesPluginSyncSetup.exe |
| Full analysis: | https://app.any.run/tasks/55dd22ce-d360-4c02-9a61-a5026b279029 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 03:13:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 82321739322AF31EED1258F9CFF21600 |
| SHA1: | AA618ACC1A8C8D9E1D393C86CE4846B318839CA1 |
| SHA256: | 57B8F33AB9592FA9BD7F555F0AA999E277F775107EFE29F39AA340843663C141 |
| SSDEEP: | 3:N8DSLY8dzKLZgidMCpY4A:2OLrdmdgWMCY4A |
MALICIOUS
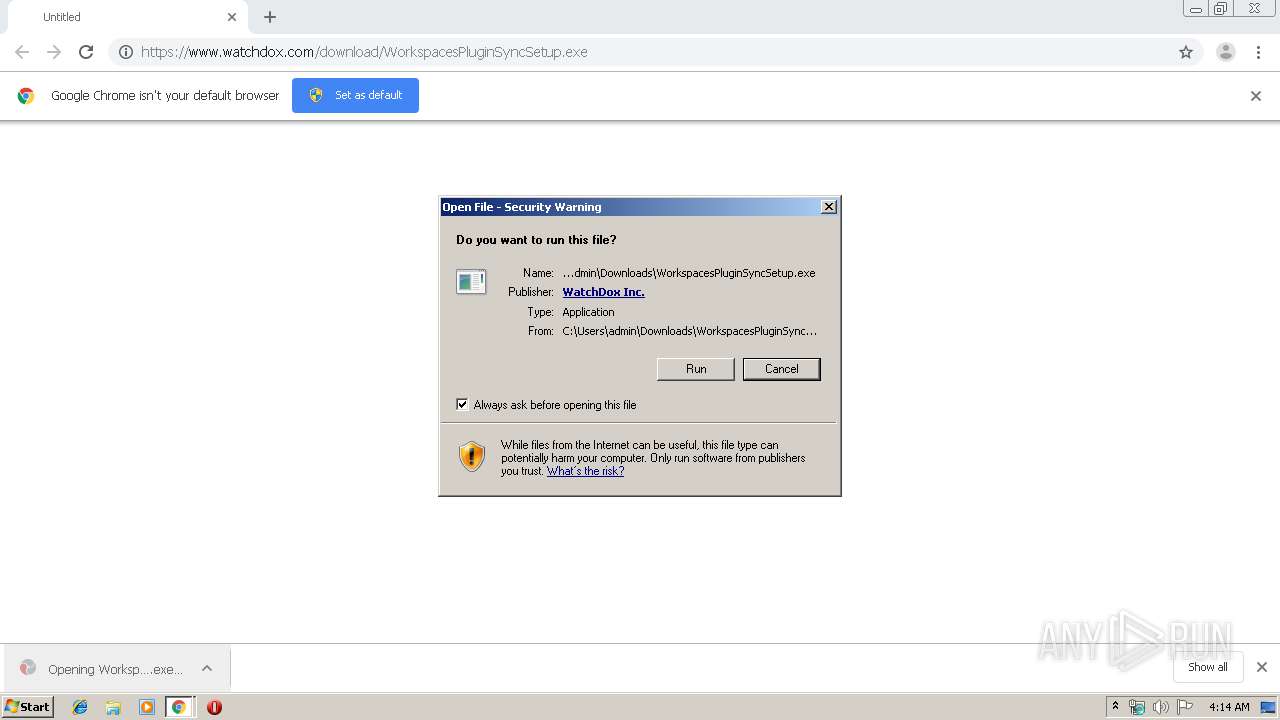
Application was dropped or rewritten from another process
- WorkspacesPluginSyncSetup.exe (PID: 1024)
- adxregistrator.exe (PID: 2648)
- adxregistrator.exe (PID: 3224)
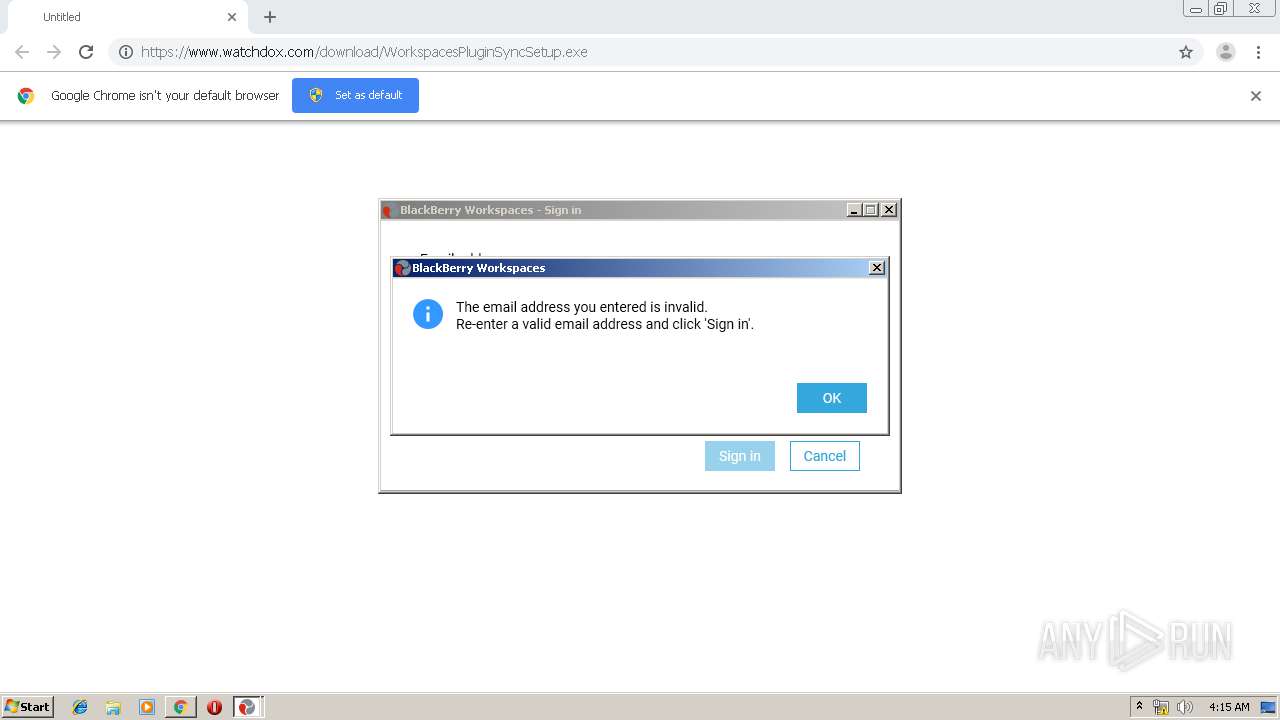
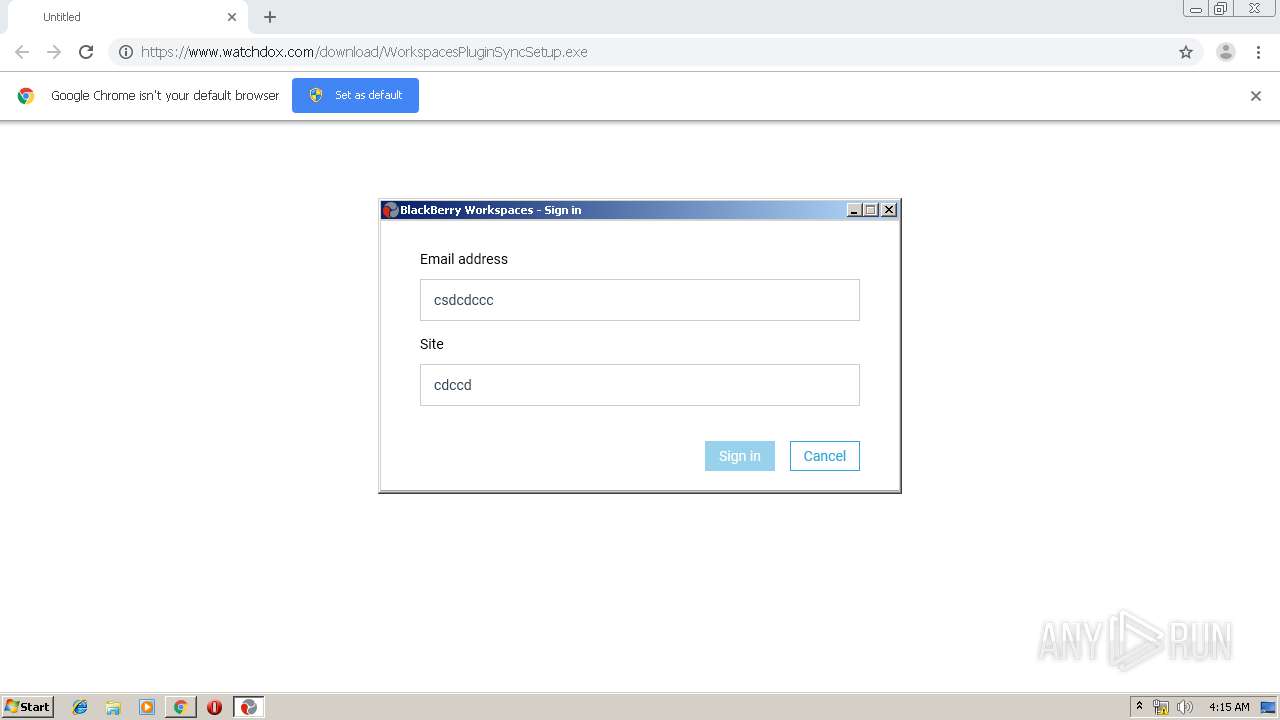
- WatchDoxEngine.exe (PID: 1160)
- WDServiceStarter_32.exe (PID: 3792)
- WDServiceStarterSetup.exe (PID: 2892)
- WorkspacesServices.exe (PID: 956)
- OutlookQueryUtil.exe (PID: 1476)
Loads dropped or rewritten executable
- adxregistrator.exe (PID: 2648)
- adxregistrator.exe (PID: 3224)
- WatchDoxEngine.exe (PID: 1160)
- WDServiceStarter_32.exe (PID: 3792)
- explorer.exe (PID: 3944)
- WorkspacesServices.exe (PID: 956)
- conhost.exe (PID: 2444)
- MSIEXEC.EXE (PID: 928)
- OutlookQueryUtil.exe (PID: 1476)
- chrome.exe (PID: 884)
- WorkspacesPluginSyncSetup.exe (PID: 1024)
Changes the autorun value in the registry
- WDServiceStarterSetup.exe (PID: 2892)
Loads the Task Scheduler COM API
- explorer.exe (PID: 3944)
SUSPICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 1504)
Executable content was dropped or overwritten
- chrome.exe (PID: 884)
- MSIEXEC.EXE (PID: 928)
- MsiExec.exe (PID: 1916)
- msiexec.exe (PID: 1504)
- WDServiceStarterSetup.exe (PID: 2892)
Starts Microsoft Installer
- WorkspacesPluginSyncSetup.exe (PID: 1024)
Modifies the open verb of a shell class
- msiexec.exe (PID: 1504)
- adxregistrator.exe (PID: 3224)
Executed as Windows Service
- vssvc.exe (PID: 3352)
Creates files in the user directory
- MSIEXEC.EXE (PID: 928)
- msiexec.exe (PID: 1504)
- WatchDoxEngine.exe (PID: 1160)
Creates COM task schedule object
- adxregistrator.exe (PID: 3224)
- MsiExec.exe (PID: 1916)
- adxregistrator.exe (PID: 2648)
- WatchDoxEngine.exe (PID: 1160)
- msiexec.exe (PID: 1504)
Reads Environment values
- WatchDoxEngine.exe (PID: 1160)
Changes IE settings (feature browser emulation)
- WatchDoxEngine.exe (PID: 1160)
Reads Microsoft Outlook installation path
- OutlookQueryUtil.exe (PID: 1476)
Modifies files in Chrome extension folder
- chrome.exe (PID: 884)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3352)
Application launched itself
- msiexec.exe (PID: 1504)
- chrome.exe (PID: 884)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3800)
- MsiExec.exe (PID: 1916)
Reads the hosts file
- chrome.exe (PID: 1796)
- chrome.exe (PID: 884)
Searches for installed software
- msiexec.exe (PID: 1504)
Reads Internet Cache Settings
- chrome.exe (PID: 884)
Reads settings of System Certificates
- chrome.exe (PID: 1796)
Reads Microsoft Office registry keys
- adxregistrator.exe (PID: 2648)
- adxregistrator.exe (PID: 3224)
- OutlookQueryUtil.exe (PID: 1476)
- WatchDoxEngine.exe (PID: 1160)
Creates a software uninstall entry
- msiexec.exe (PID: 1504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
44
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1757169039080285710 --mojo-platform-channel-handle=2484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7506032982232138033 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.watchdox.com/download/WorkspacesPluginSyncSetup.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Downloaded Installations\{F2D75F5C-2A7D-4BC9-92EE-574567EE3491}\WorkspacesWindowsPlugin8121.msi" /L*V+X "C:\Users\admin\AppData\Roaming\WatchDoxSetup.log" D=0 TRANSFORMS="C:\Users\admin\AppData\Local\Downloaded Installations\{F2D75F5C-2A7D-4BC9-92EE-574567EE3491}\1033.MST" SETUPEXEDIR="C:\Users\admin\Downloads" SETUPEXENAME="WorkspacesPluginSyncSetup.exe" | C:\Windows\system32\MSIEXEC.EXE | WorkspacesPluginSyncSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\WorkspacesServices.exe" | C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\WorkspacesServices.exe | WDServiceStarterSetup.exe | ||||||||||||
User: admin Company: BlackBerry Integrity Level: MEDIUM Description: Workspaces Services Exit code: 0 Version: 8.1.2.1 Modules
| |||||||||||||||
| 1024 | "C:\Users\admin\Downloads\WorkspacesPluginSyncSetup.exe" | C:\Users\admin\Downloads\WorkspacesPluginSyncSetup.exe | — | chrome.exe | |||||||||||
User: admin Company: BlackBerry Integrity Level: MEDIUM Description: Workspaces Windows Plug-in Exit code: 0 Version: 8.1.2.1 Modules
| |||||||||||||||
| 1160 | "C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\WatchDoxEngine.exe" /firsttime | C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\WatchDoxEngine.exe | msiexec.exe | ||||||||||||
User: admin Company: BlackBerry Integrity Level: MEDIUM Description: Workspaces Exit code: 0 Version: 8.1.2.1 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4165510676898744354 --mojo-platform-channel-handle=4988 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\OutlookQueryUtil.exe" "C:\Users\admin\AppData\Local\Temp\tmpFCD4.tmp" | C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\OutlookQueryUtil.exe | — | WatchDoxEngine.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OutlookQueryUtil Exit code: 4294967295 Version: 8.1.2.1 Modules
| |||||||||||||||
| 1504 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 220
Read events
3 829
Write events
2 369
Delete events
22
Modification events
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 884-13215496440791750 |
Value: 259 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
175
Suspicious files
109
Text files
334
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\89d3e019-2040-418f-ab71-bf90929b2440.tmp | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a8ec.TMP | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
50
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | chrome.exe | GET | 301 | 208.65.75.22:80 | http://www.blackberry.com/workspaces | CA | html | 245 b | whitelisted |
1796 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
1796 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
1796 | chrome.exe | GET | 301 | 208.65.75.22:80 | http://www.blackberry.com/workspaces/ | CA | html | 290 b | whitelisted |
1796 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
1796 | chrome.exe | GET | 200 | 13.35.254.176:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
1796 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1796 | chrome.exe | GET | 200 | 74.125.155.199:80 | http://r1---sn-p5qs7n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qs7n7z&ms=nvh&mt=1571022739&mv=u&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1796 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1571022739&mv=u&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | chrome.exe | 54.243.198.28:443 | www.watchdox.com | Amazon.com, Inc. | US | unknown |
1796 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 93.184.220.178:443 | cdn.bizible.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
1796 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 208.65.75.22:443 | www.blackberry.com | BlackBerry Limited | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.watchdox.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.blackberry.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WatchDoxEngine.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\x86\SQLite.Interop.dll"...
|
WatchDoxEngine.exe | SQLite error (1): no such table: Settings in "select * from Settings where name = 'EmailServer'"
|
WatchDoxEngine.exe | SQLite error (1): no such table: Settings in "select * from Settings where name = 'EmailServer'"
|
WorkspacesServices.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Roaming\WatchDox\Windows Plugin\x86\SQLite.Interop.dll"...
|