| File name: | registry-cleaner-setup.exe |
| Full analysis: | https://app.any.run/tasks/8bf89cf6-97b9-42fc-8abd-361aec65aa40 |
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2019, 20:05:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0397F99570D52C8888E6DB61DF1325B3 |
| SHA1: | E5C2F60614F0147A7CB756A4F355DF71909C605A |
| SHA256: | 57B14980590B0342DDCFBFB387A8401B035BA2F8BB2AC3E26142C71291F3A017 |
| SSDEEP: | 393216:OAn7dMByO1Yp3npuMuMaDL2XAmLDKwPCMmuNMIaQuNOi:xn72r1Yk9DKAm6e8XJci |
MALICIOUS
No malicious indicators.SUSPICIOUS
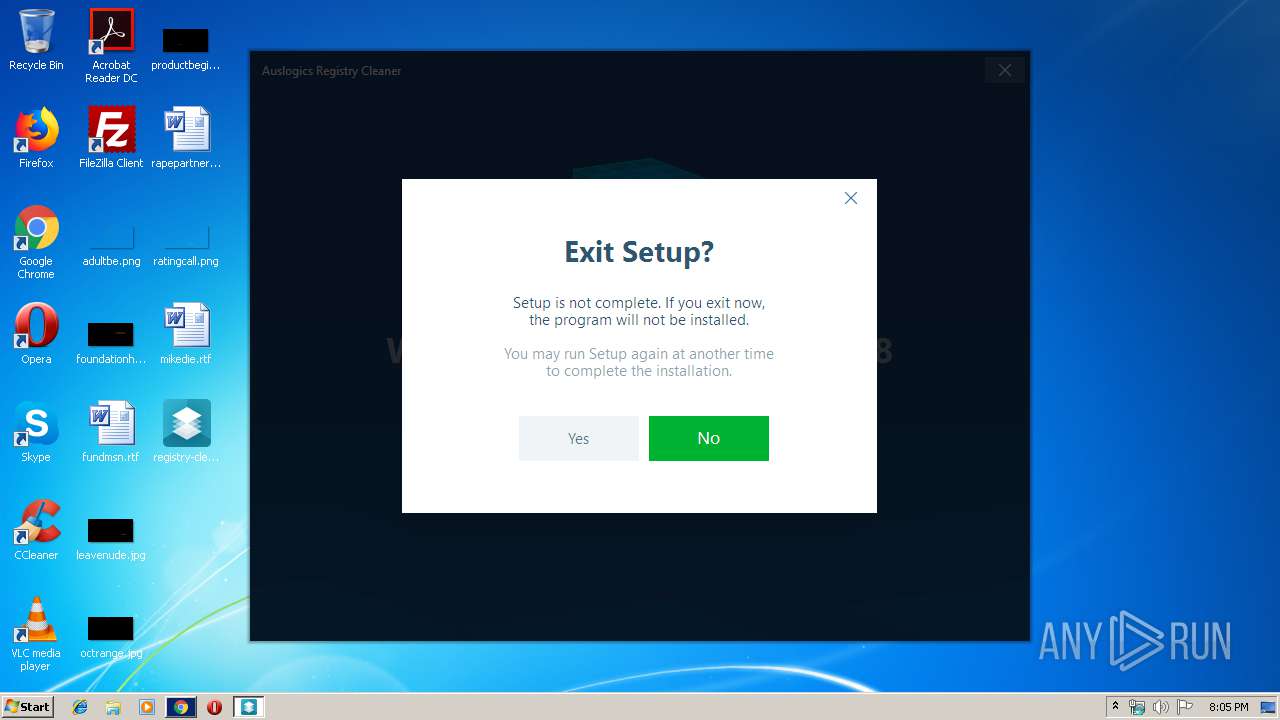
Executable content was dropped or overwritten
- registry-cleaner-setup.exe (PID: 492)
- registry-cleaner-setup.exe (PID: 3984)
- registry-cleaner-setup.tmp (PID: 600)
Reads Windows owner or organization settings
- registry-cleaner-setup.tmp (PID: 600)
Reads the Windows organization settings
- registry-cleaner-setup.tmp (PID: 600)
Reads Windows Product ID
- registry-cleaner-setup.tmp (PID: 600)
Reads the machine GUID from the registry
- registry-cleaner-setup.tmp (PID: 600)
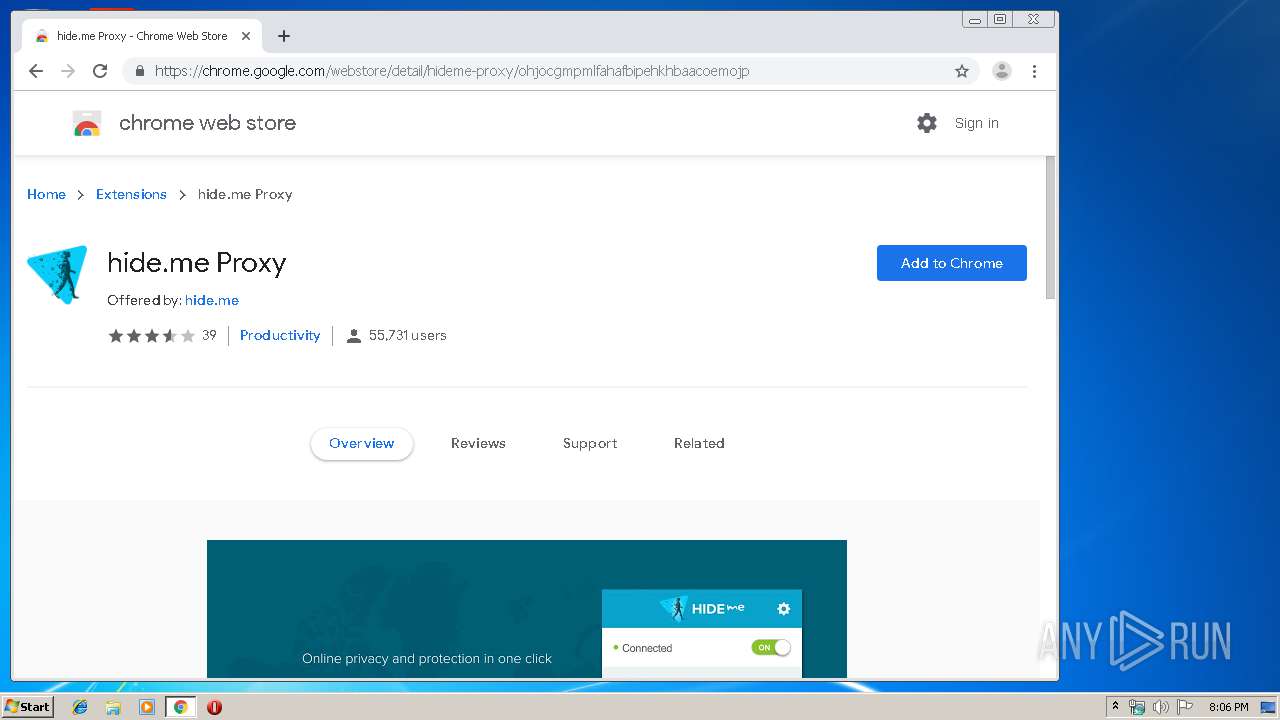
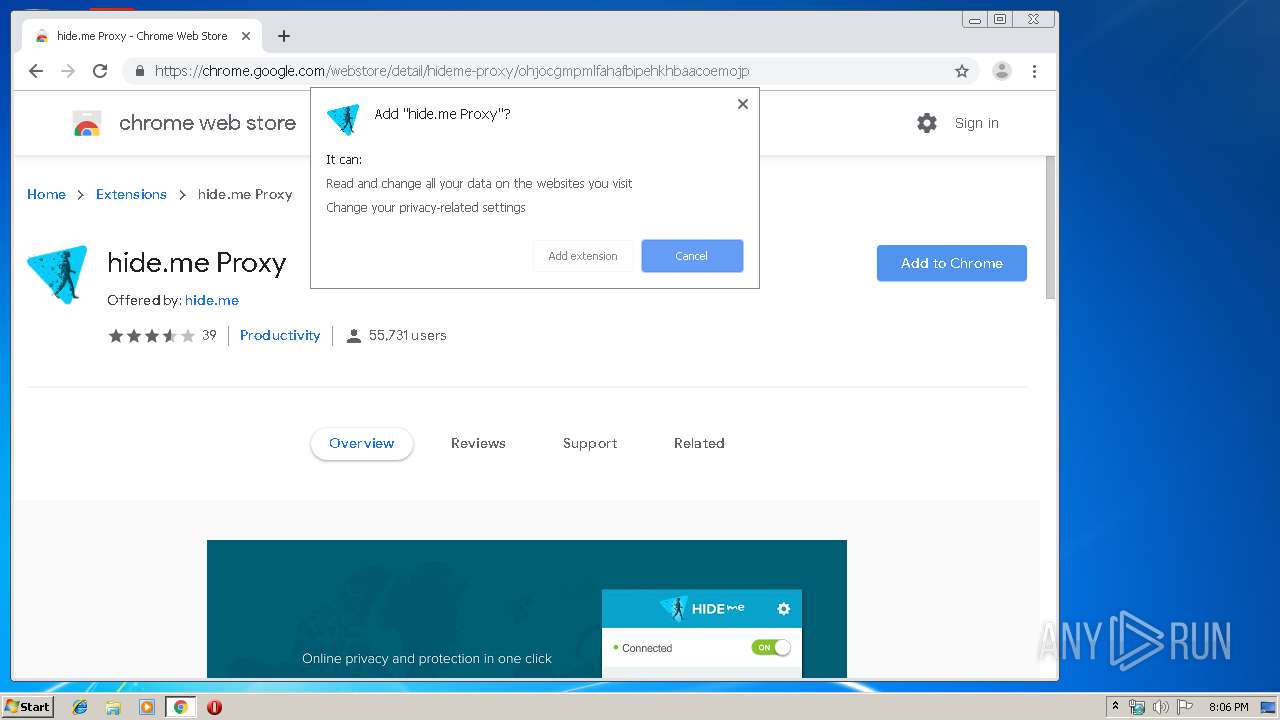
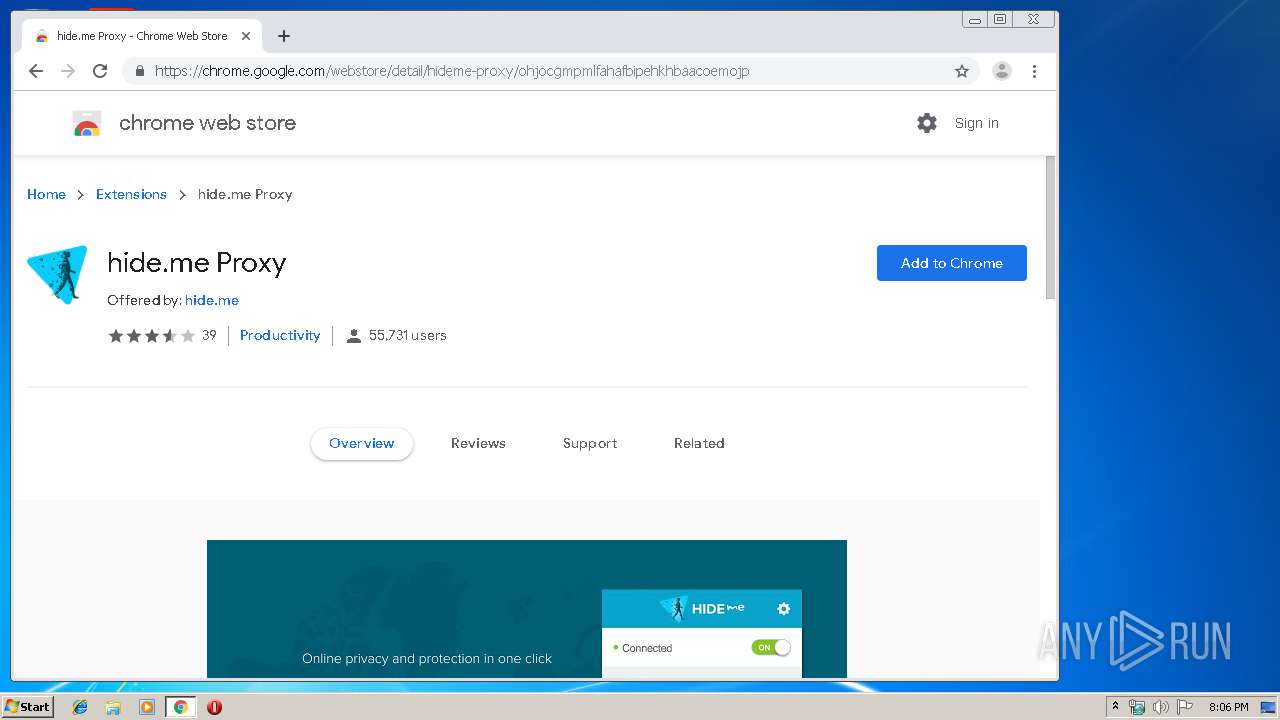
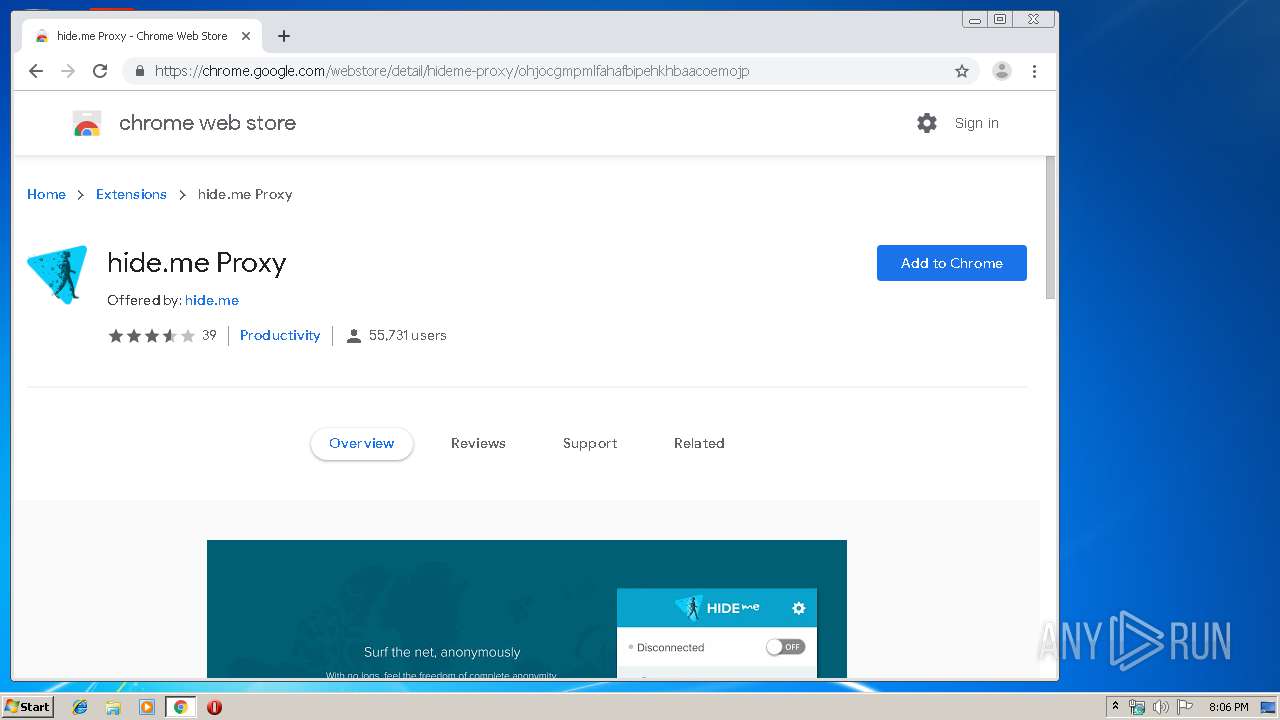
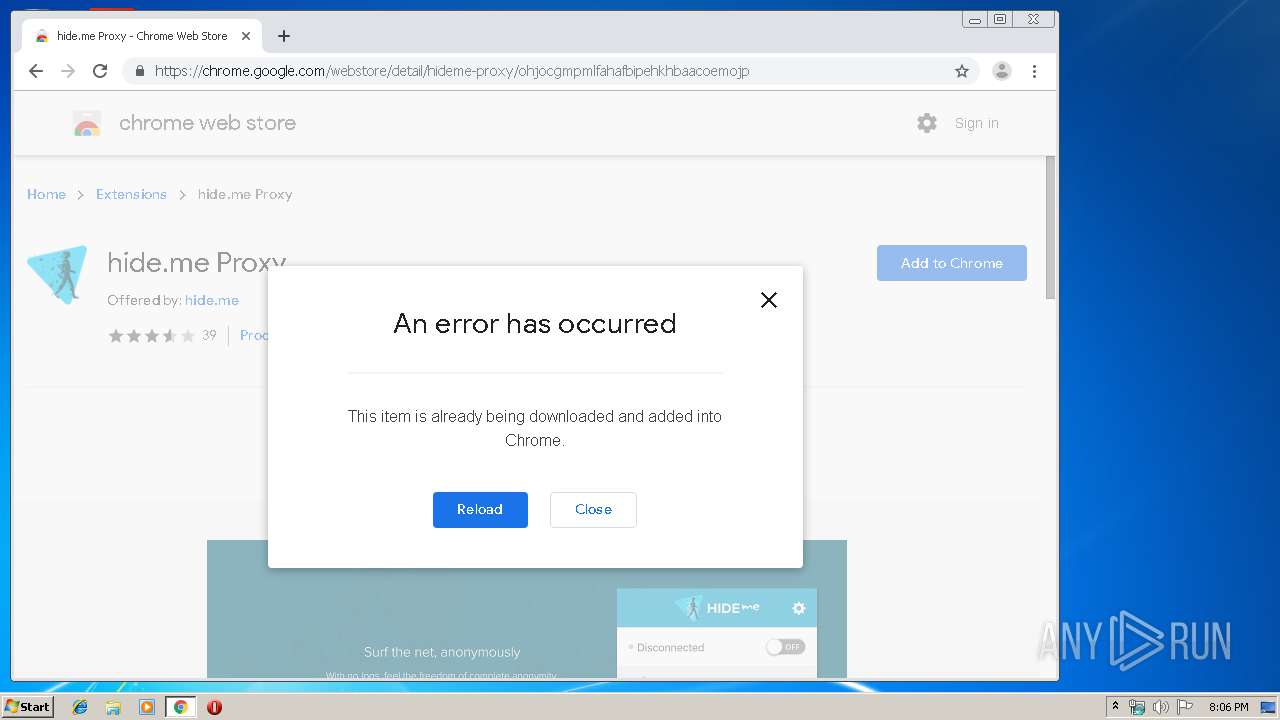
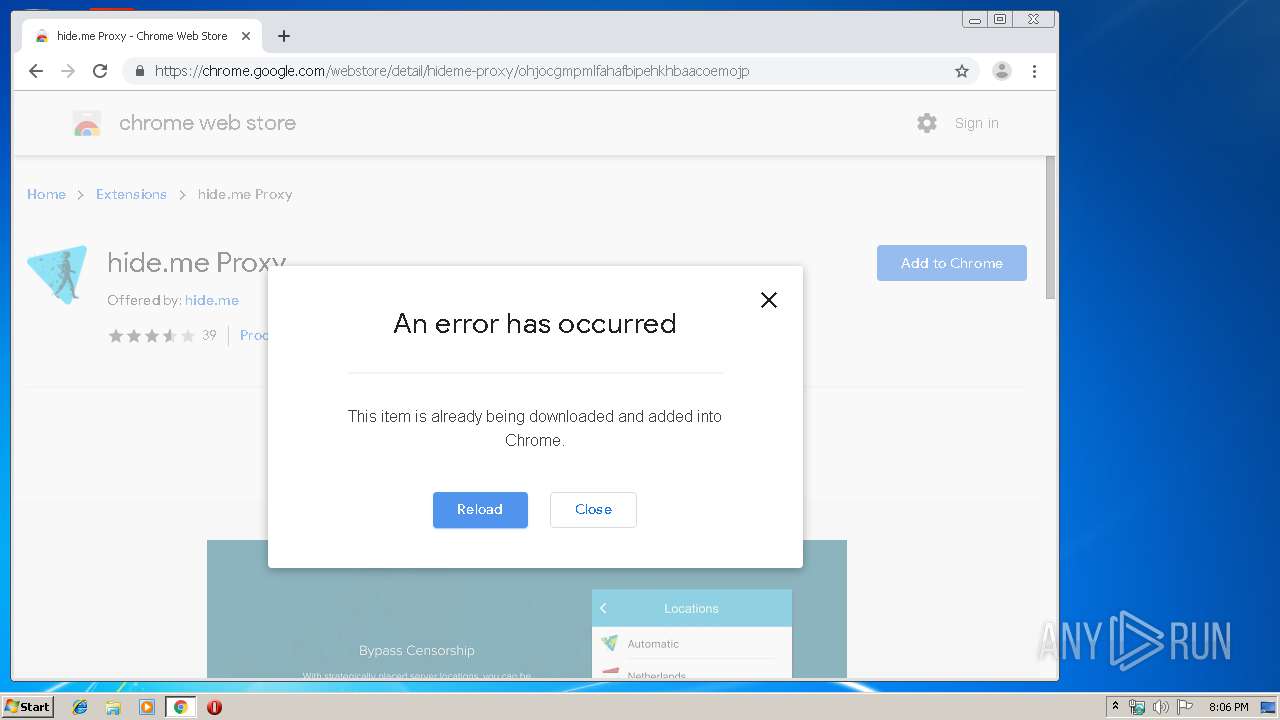
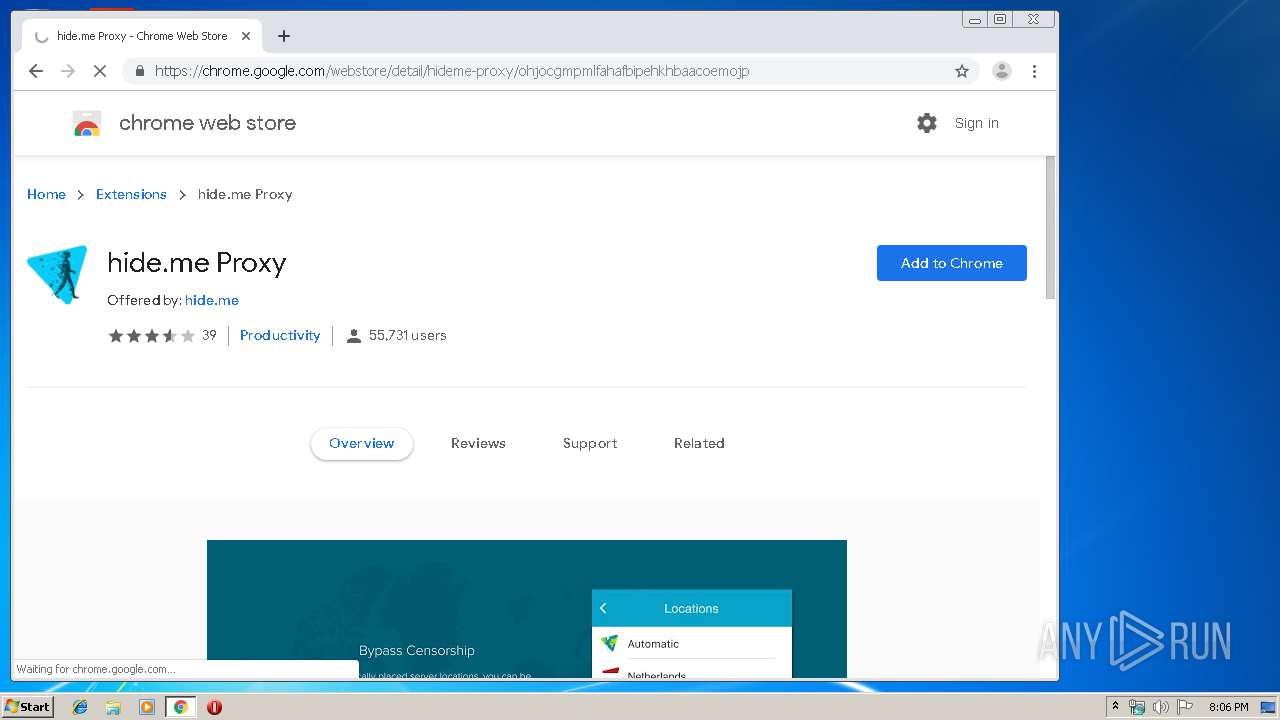
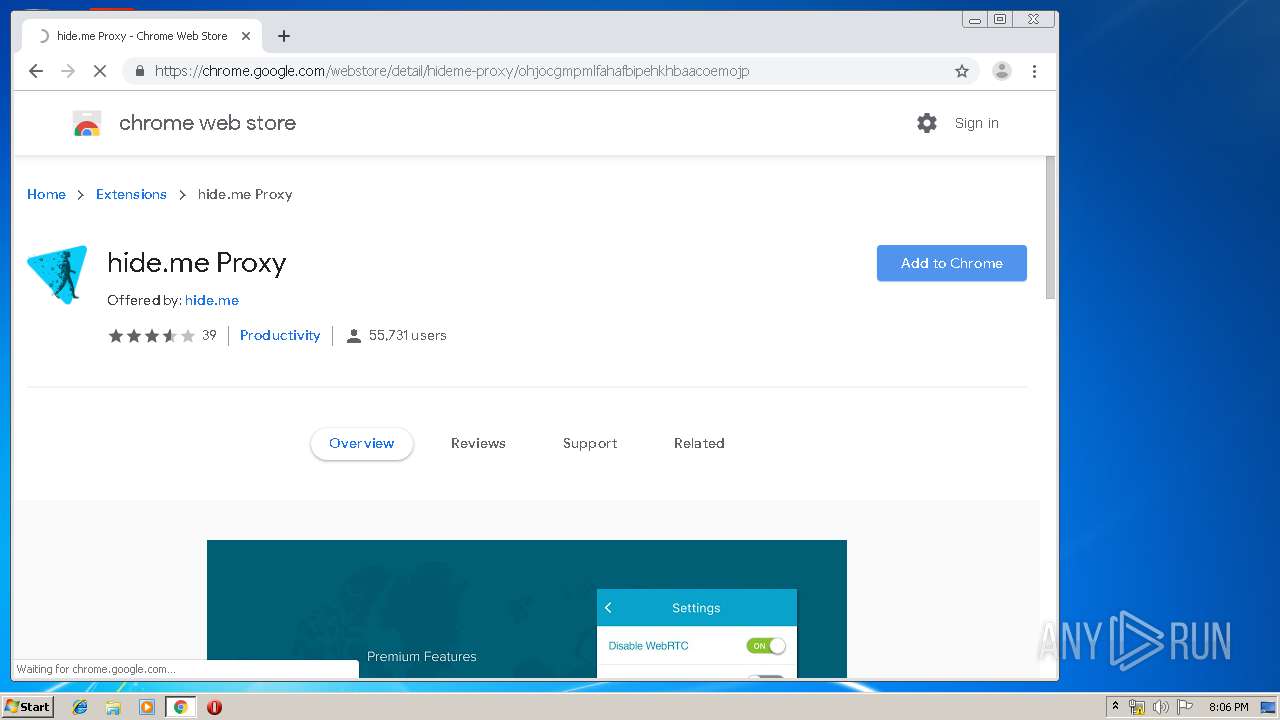
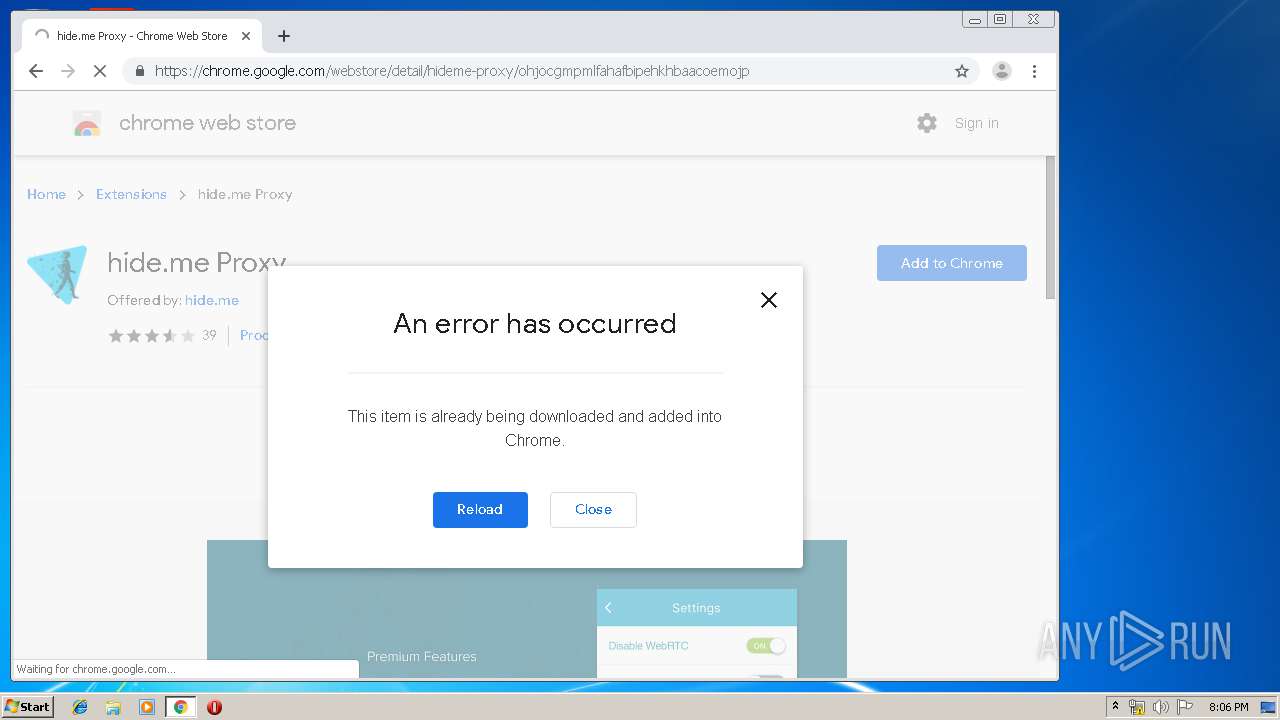
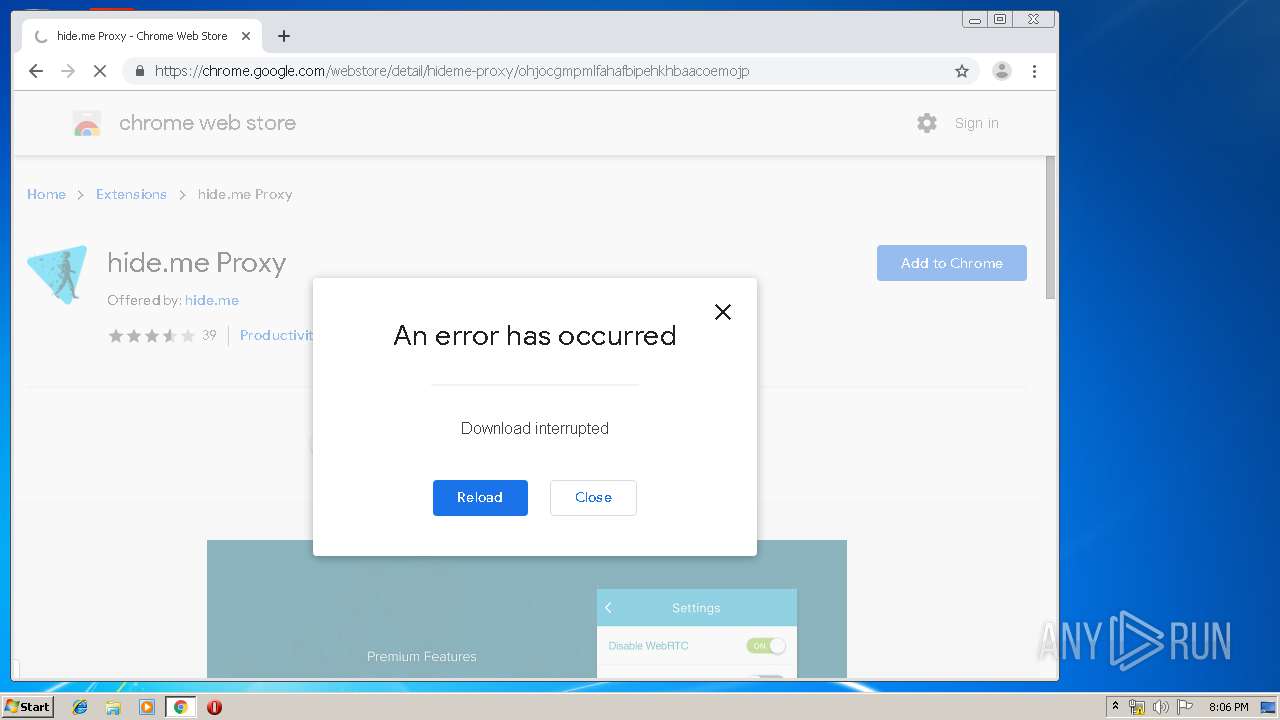
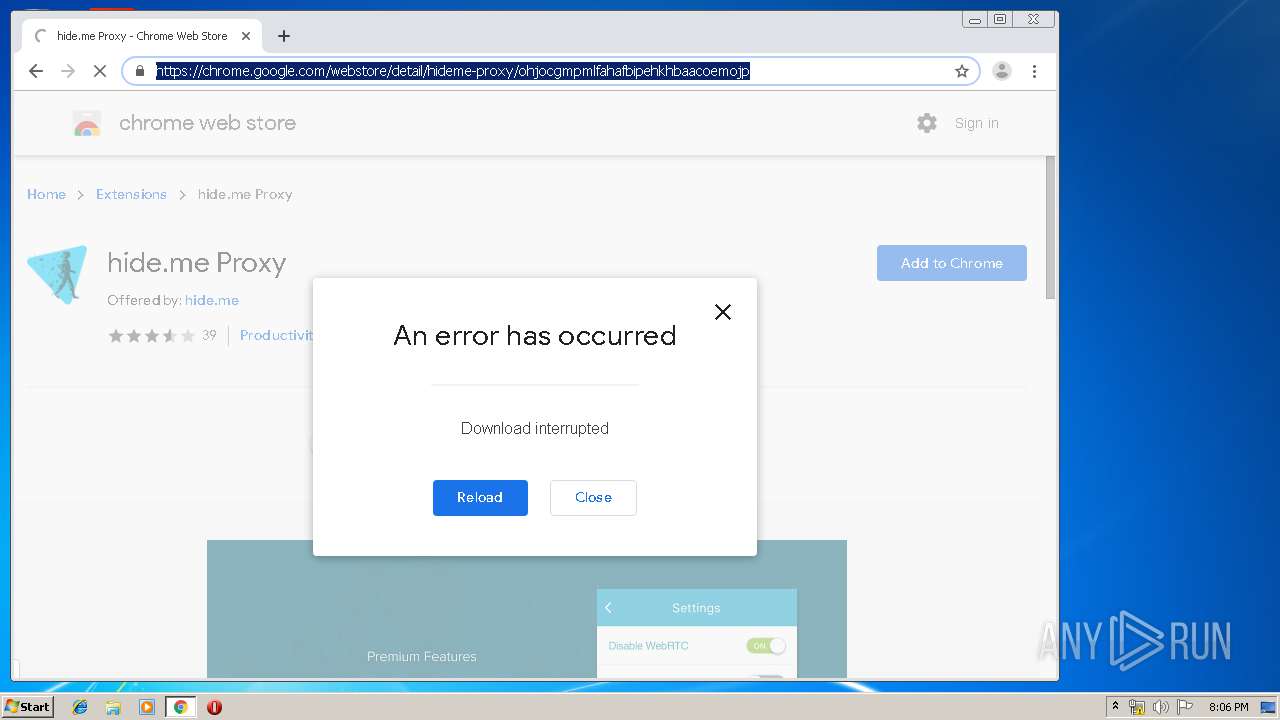
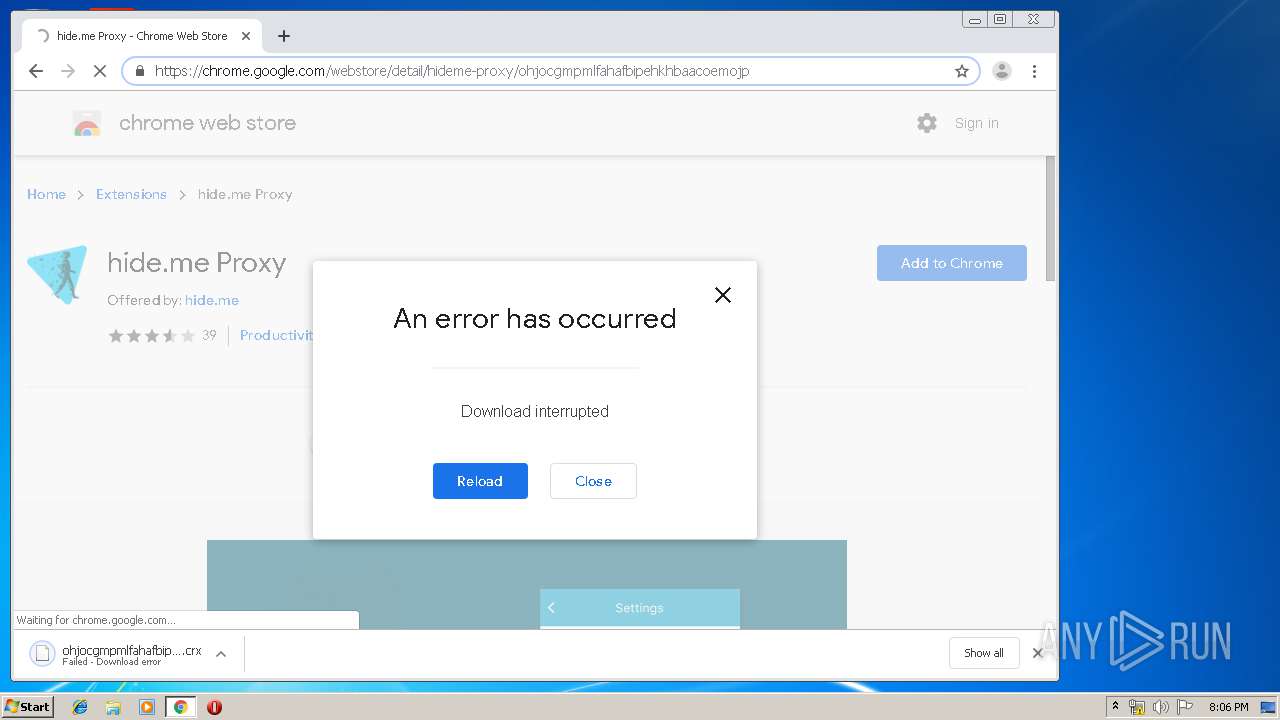
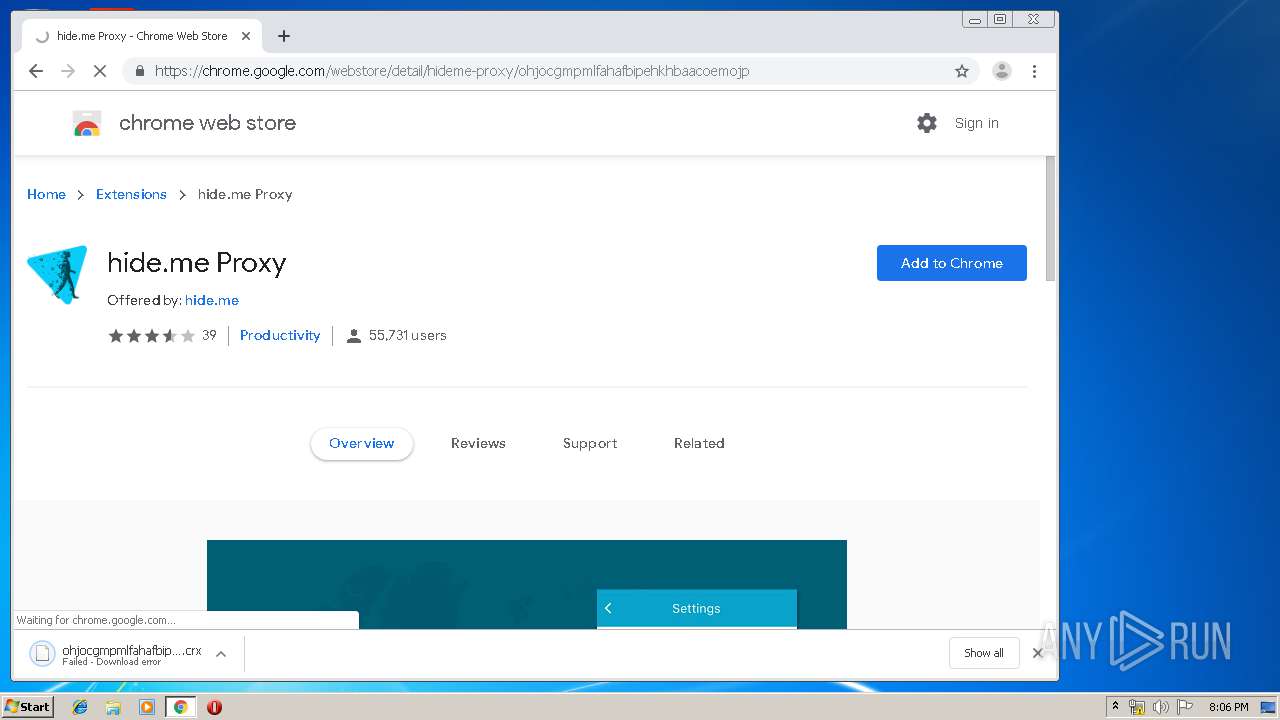
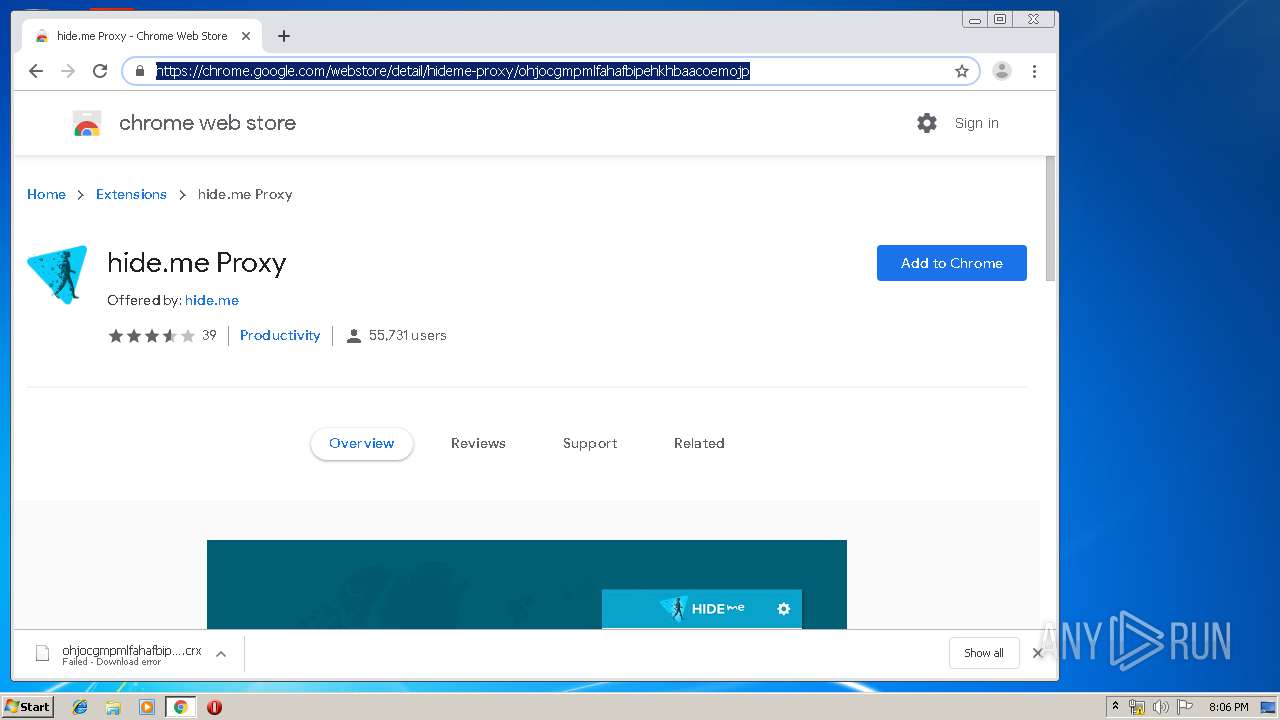
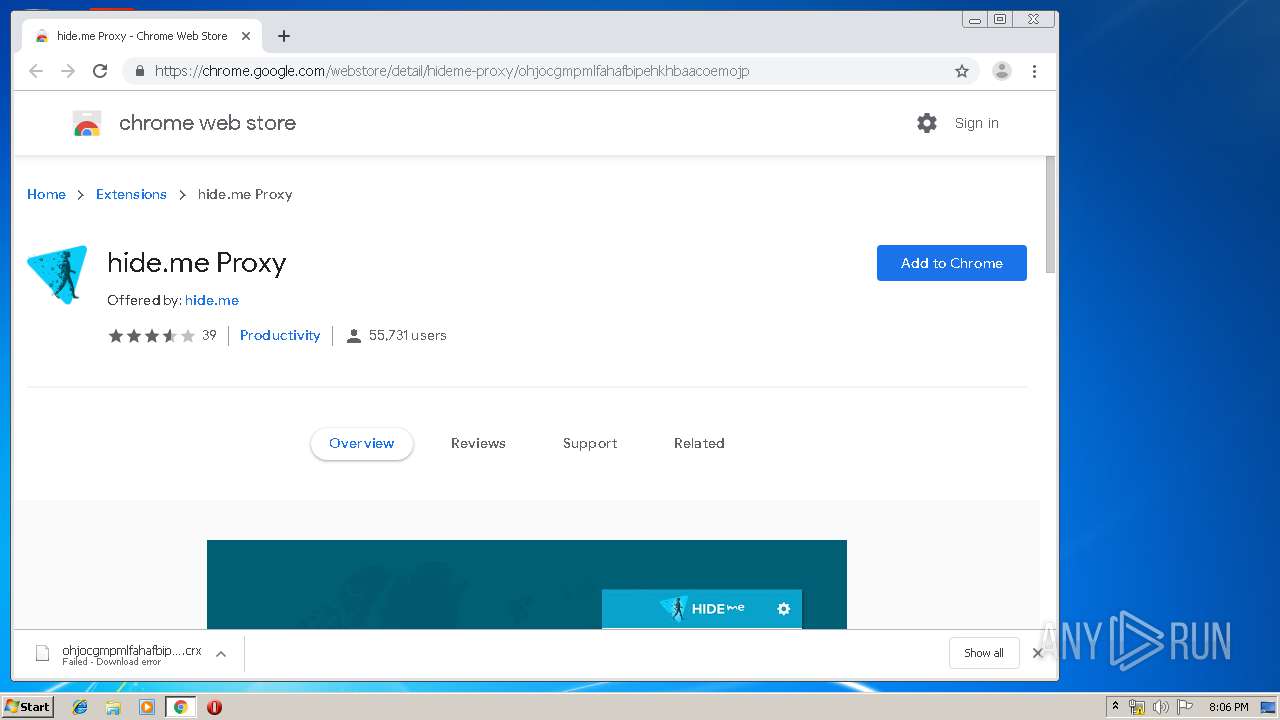
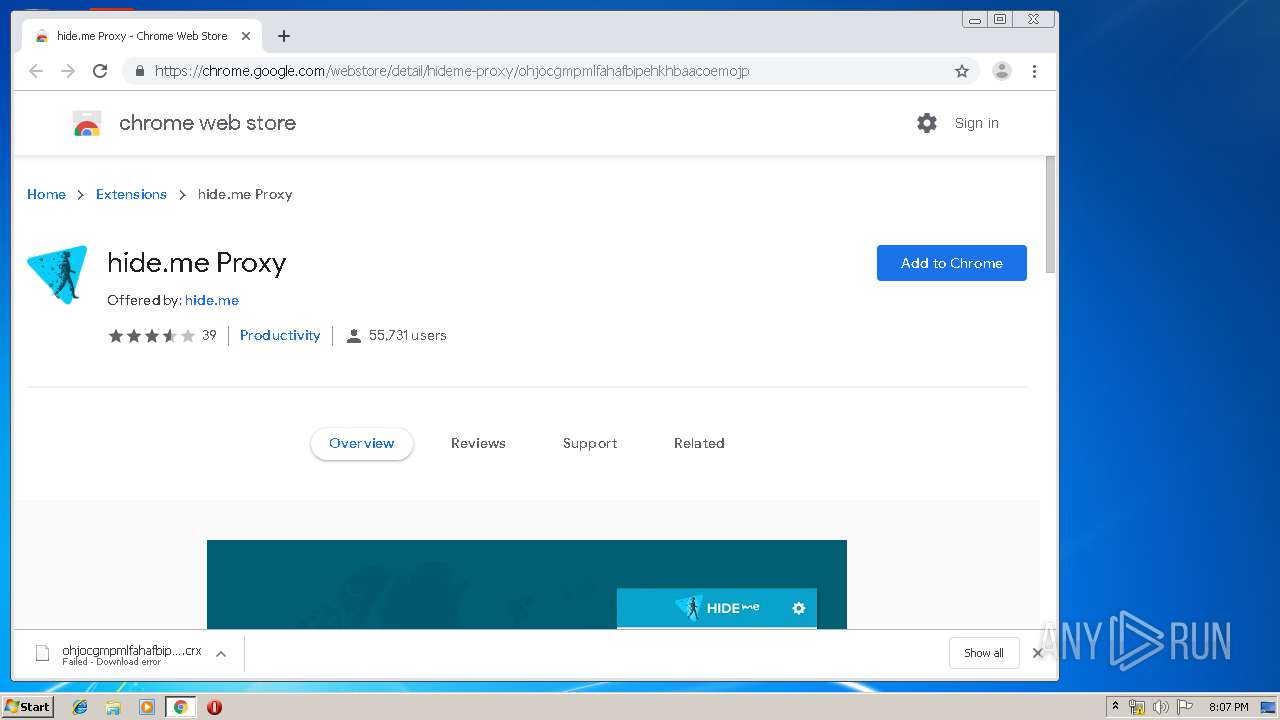
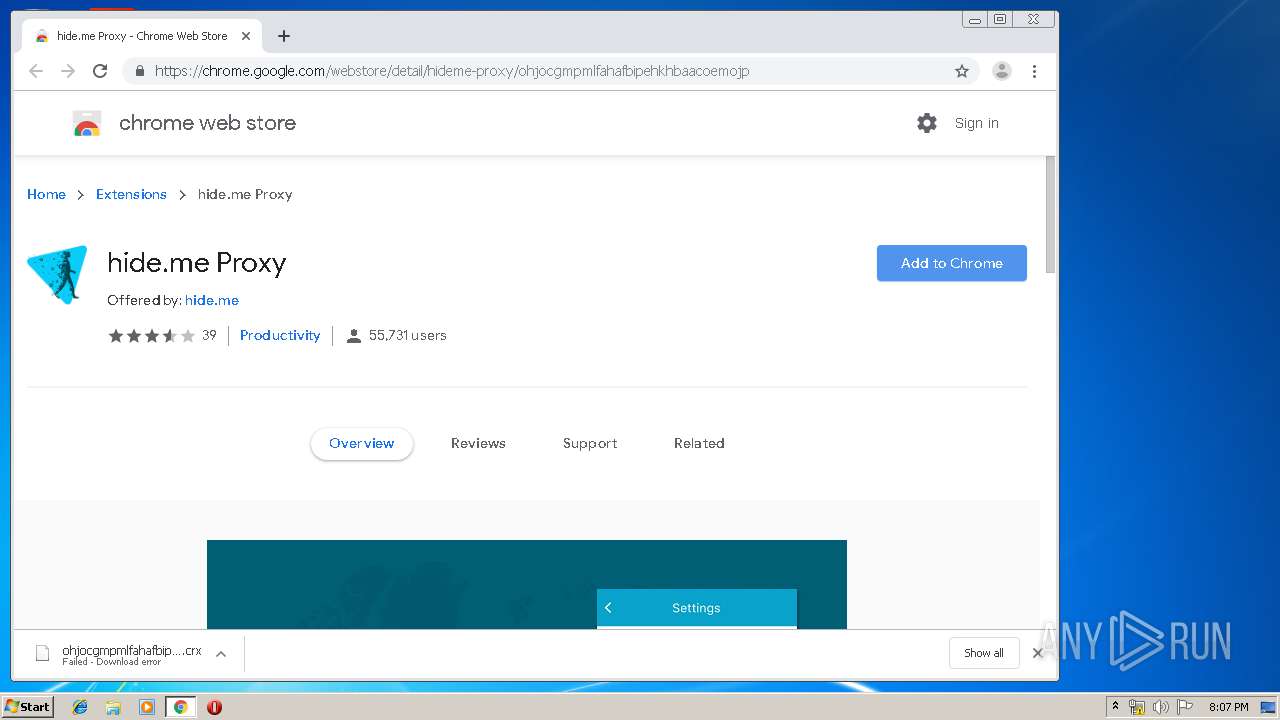
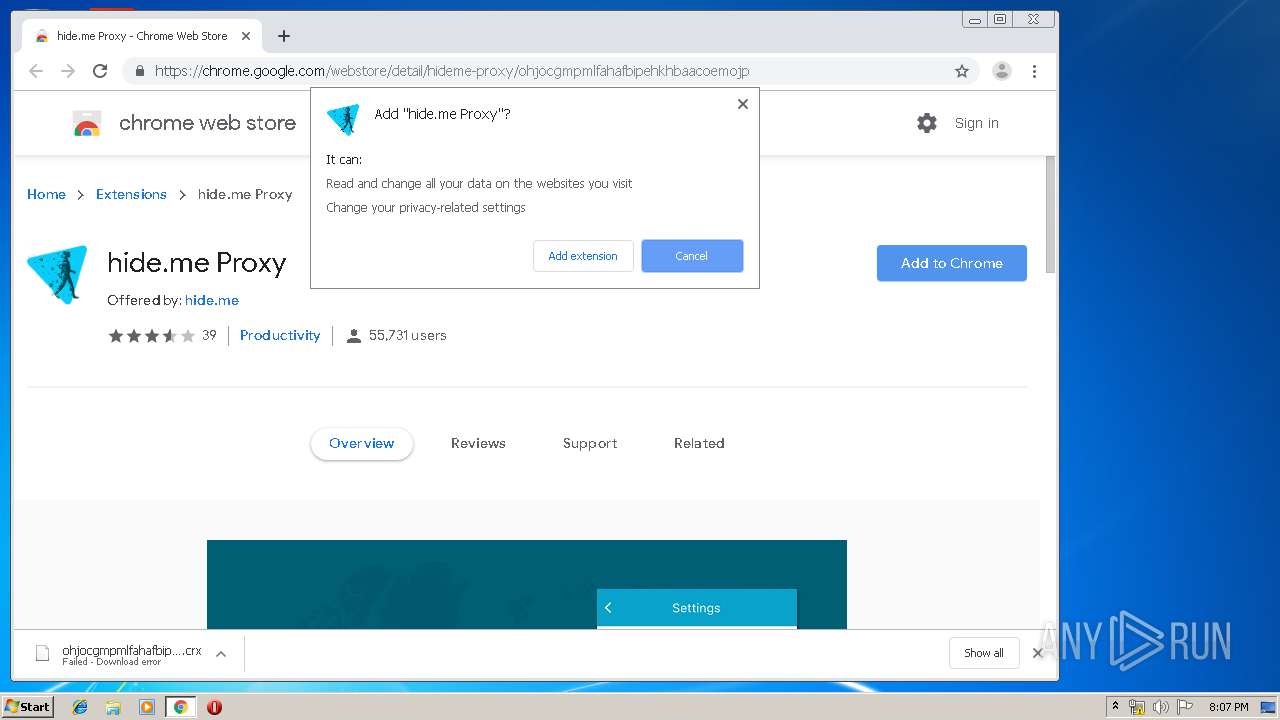
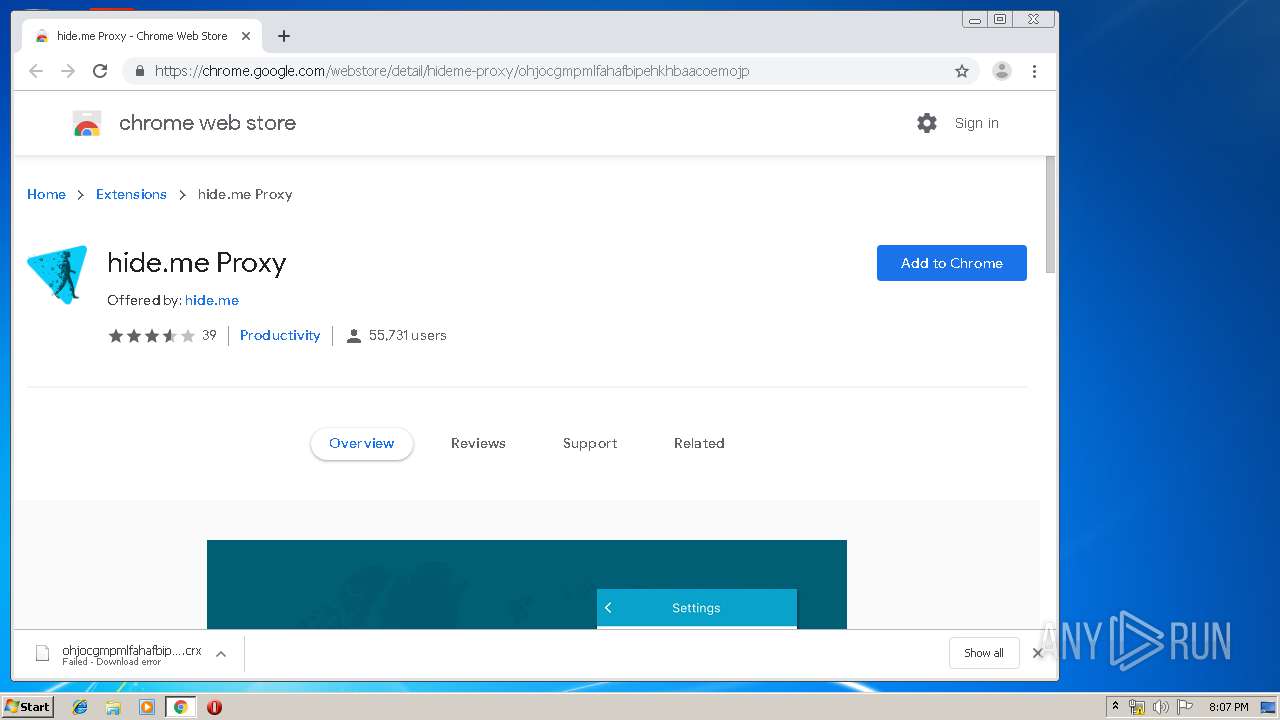
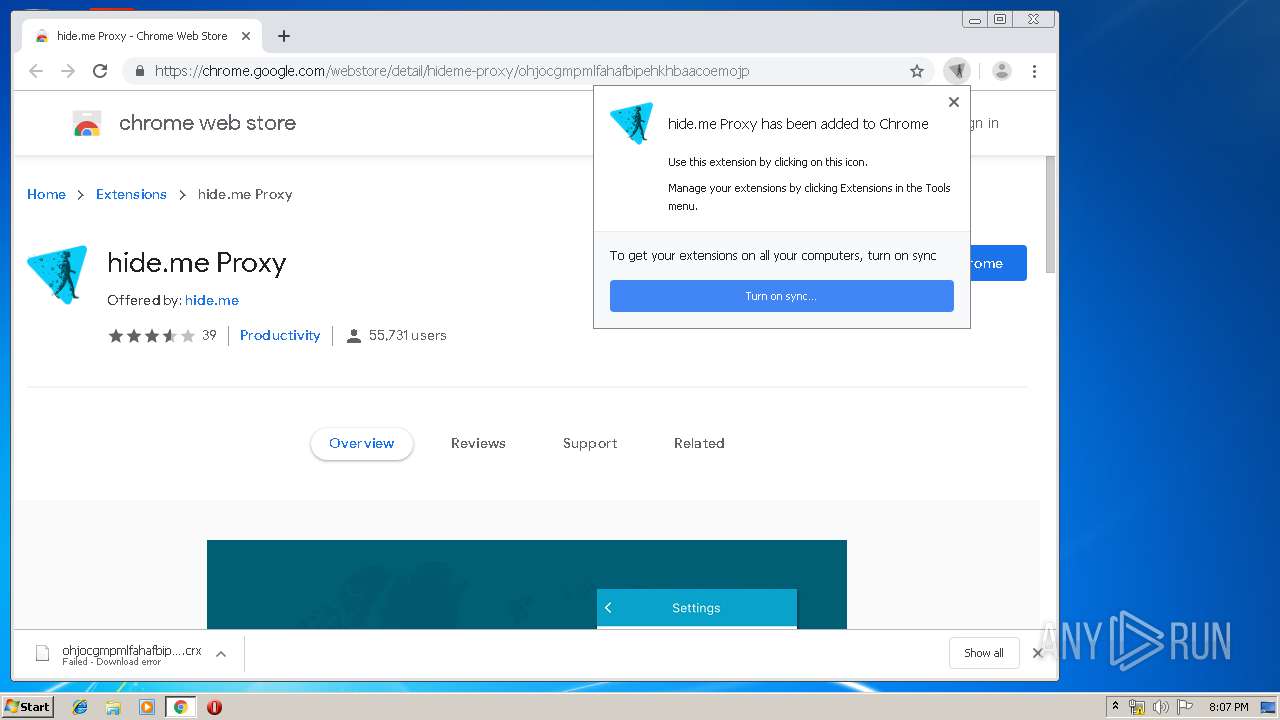
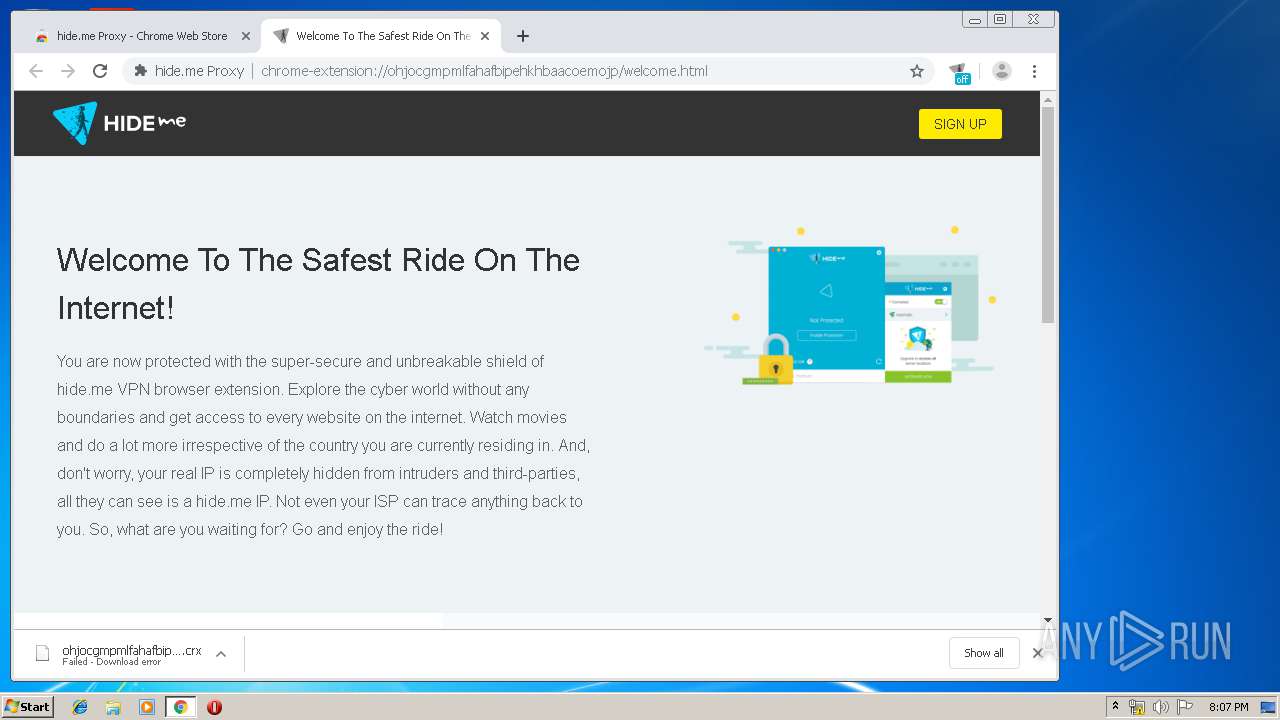
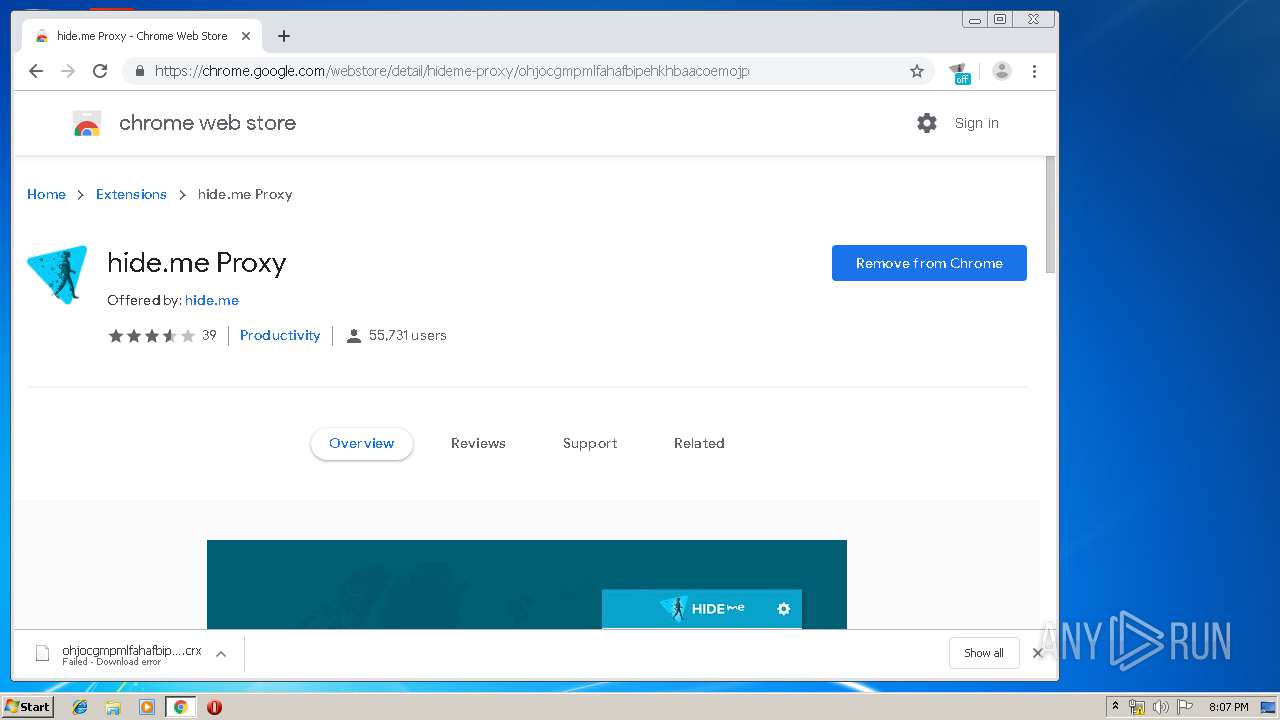
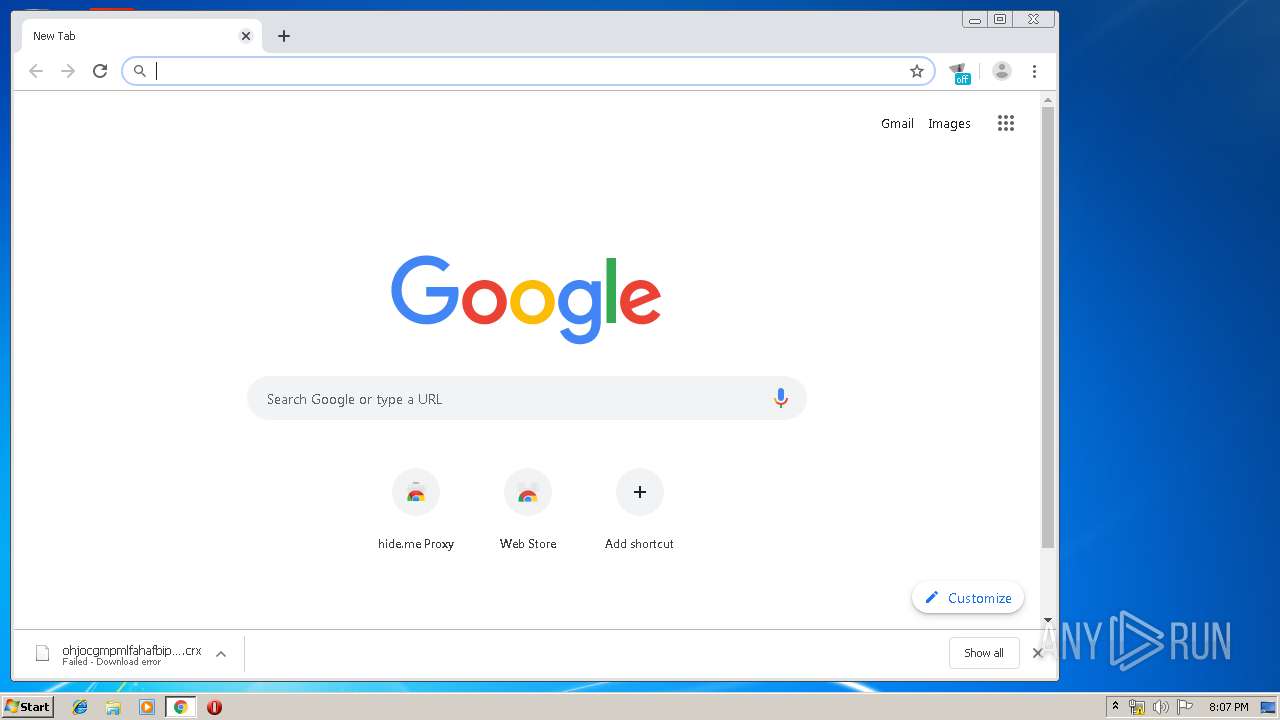
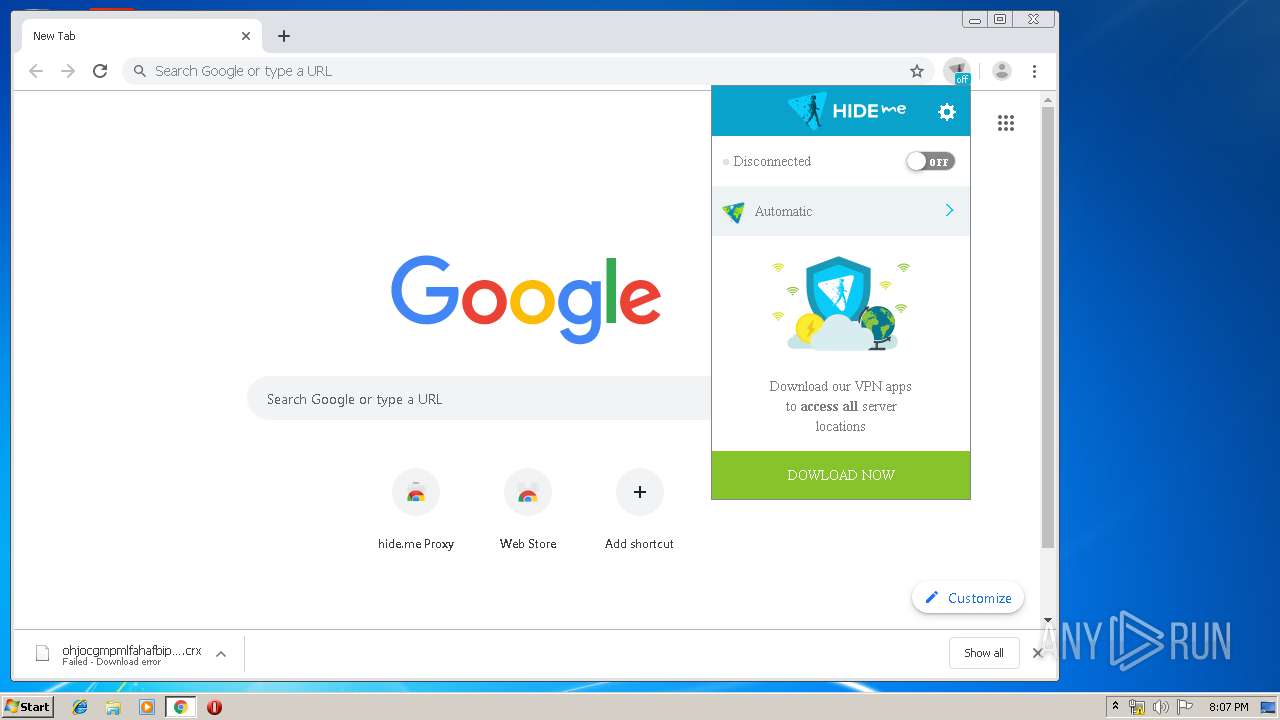
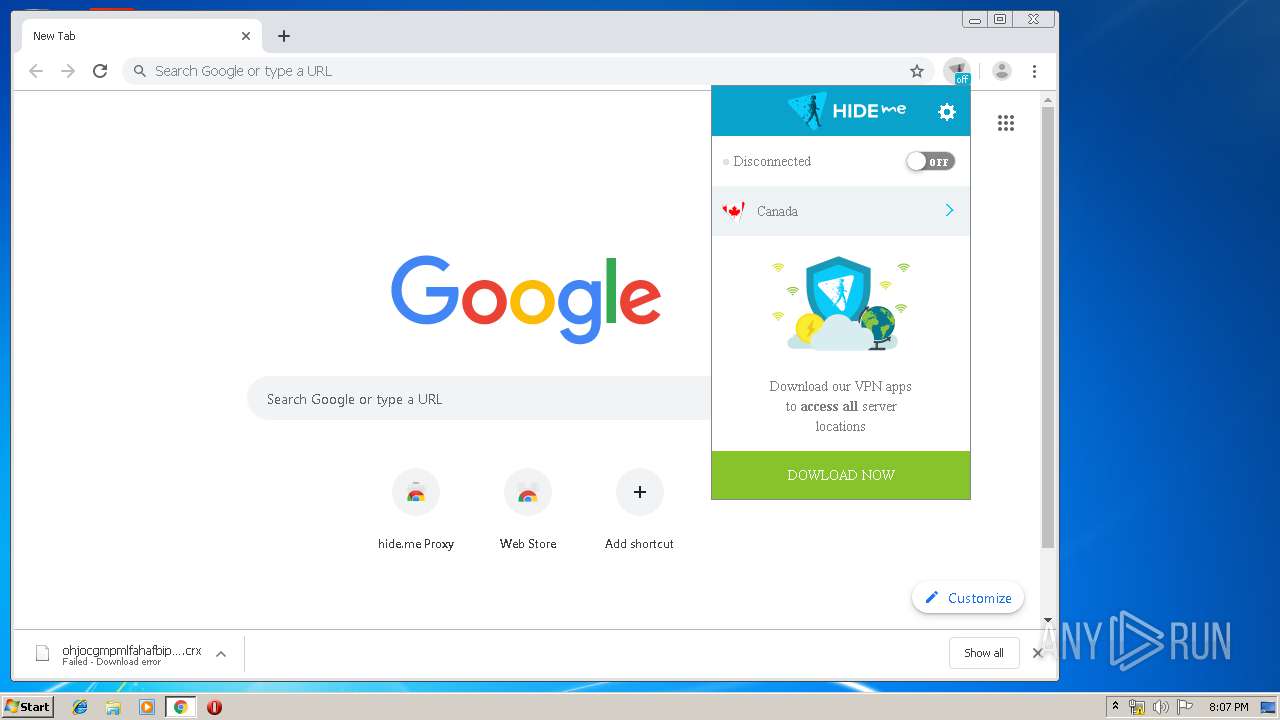
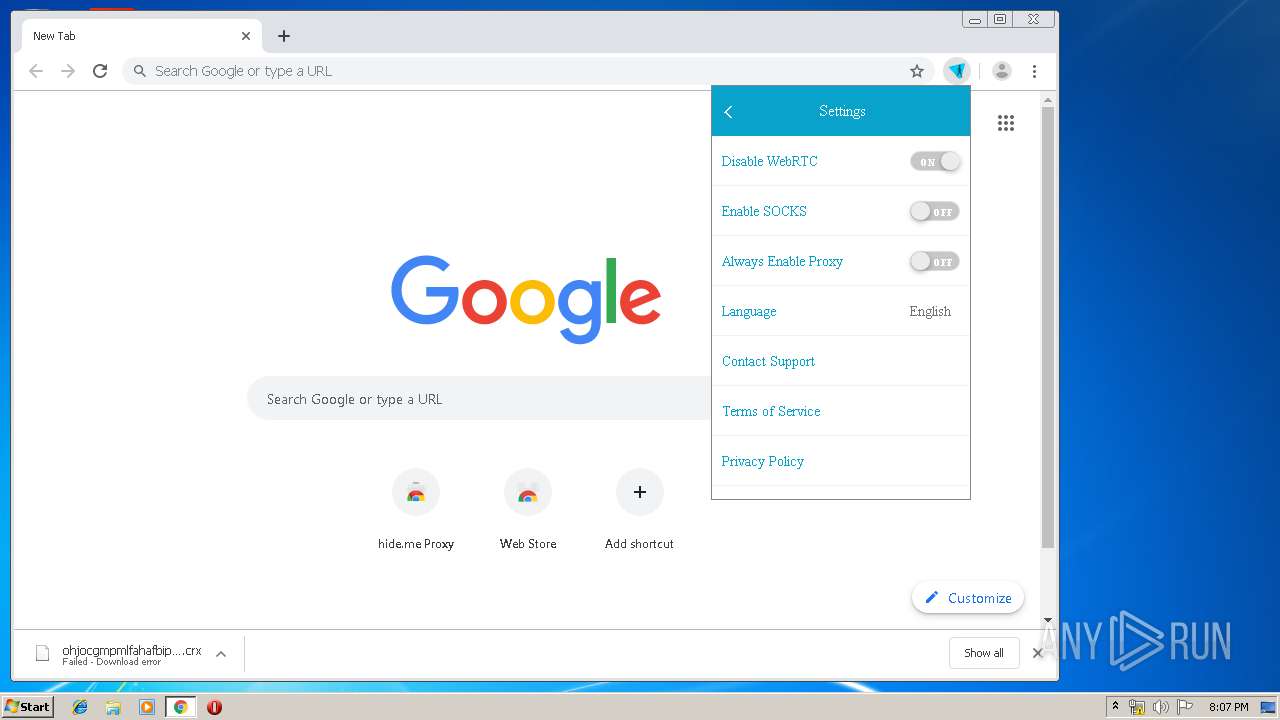
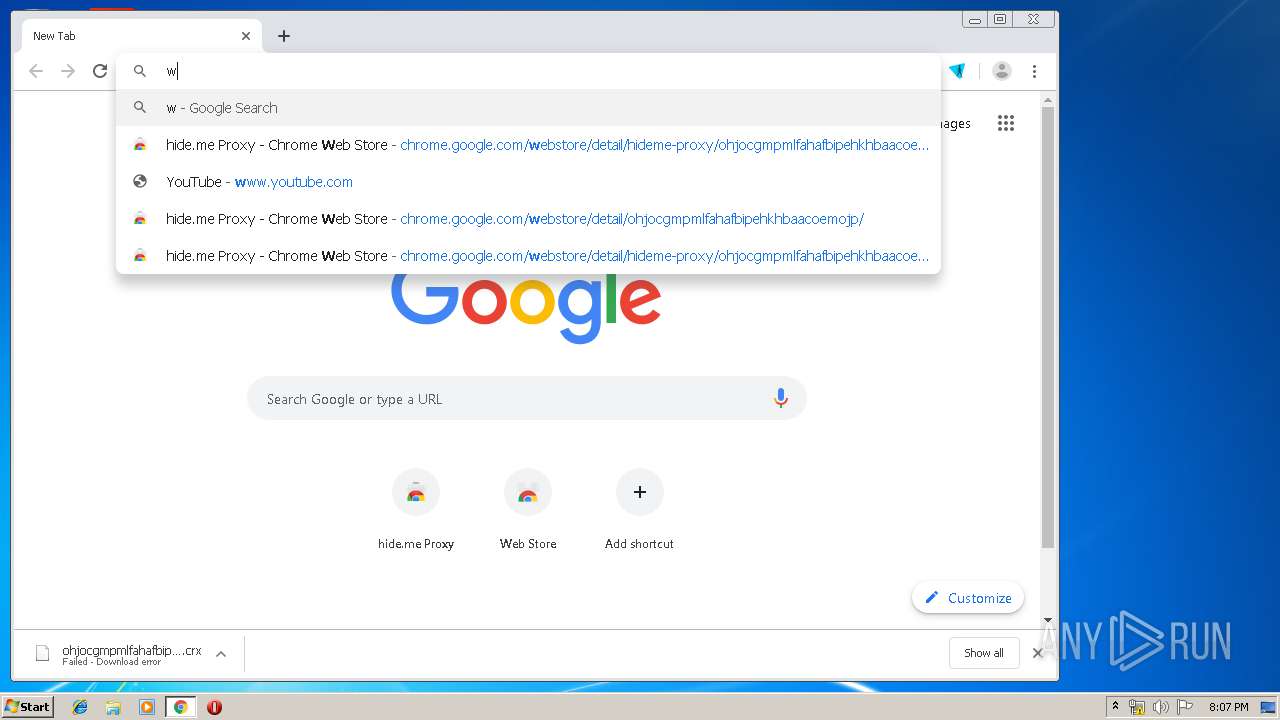
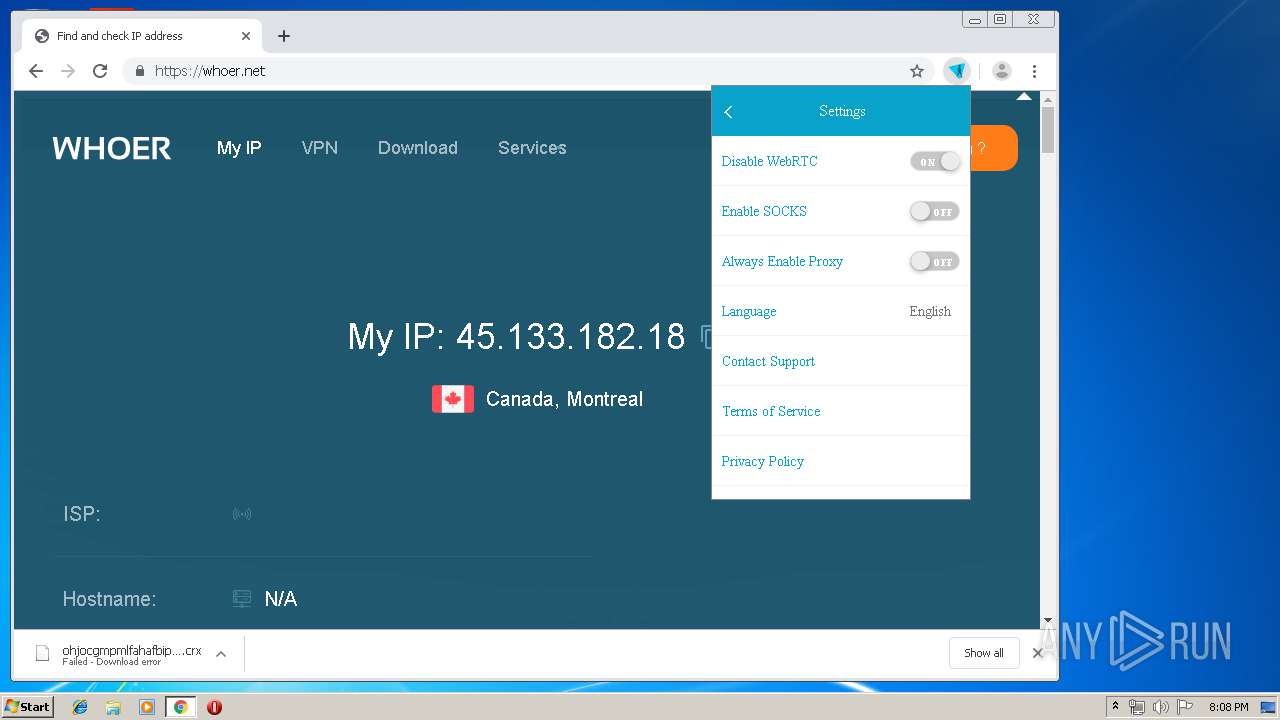
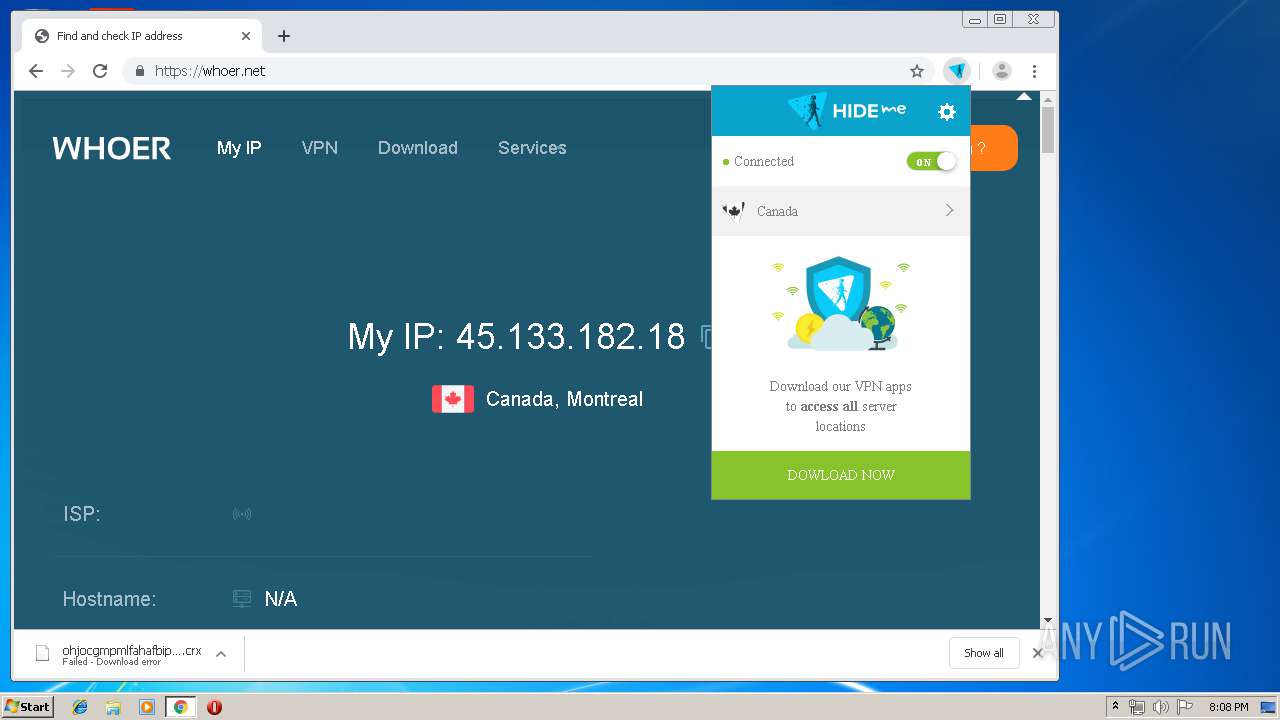
Modifies files in Chrome extension folder
- chrome.exe (PID: 3988)
INFO
Application was dropped or rewritten from another process
- registry-cleaner-setup.tmp (PID: 960)
- registry-cleaner-setup.tmp (PID: 600)
Loads dropped or rewritten executable
- registry-cleaner-setup.tmp (PID: 600)
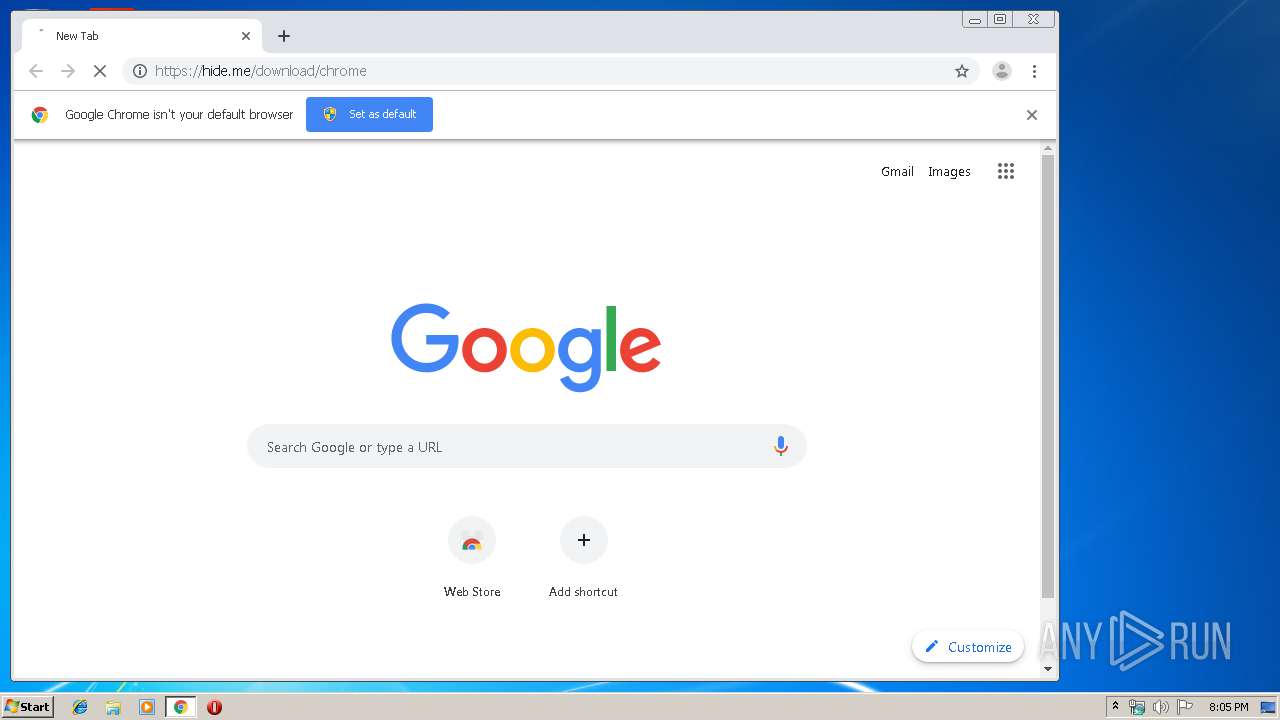
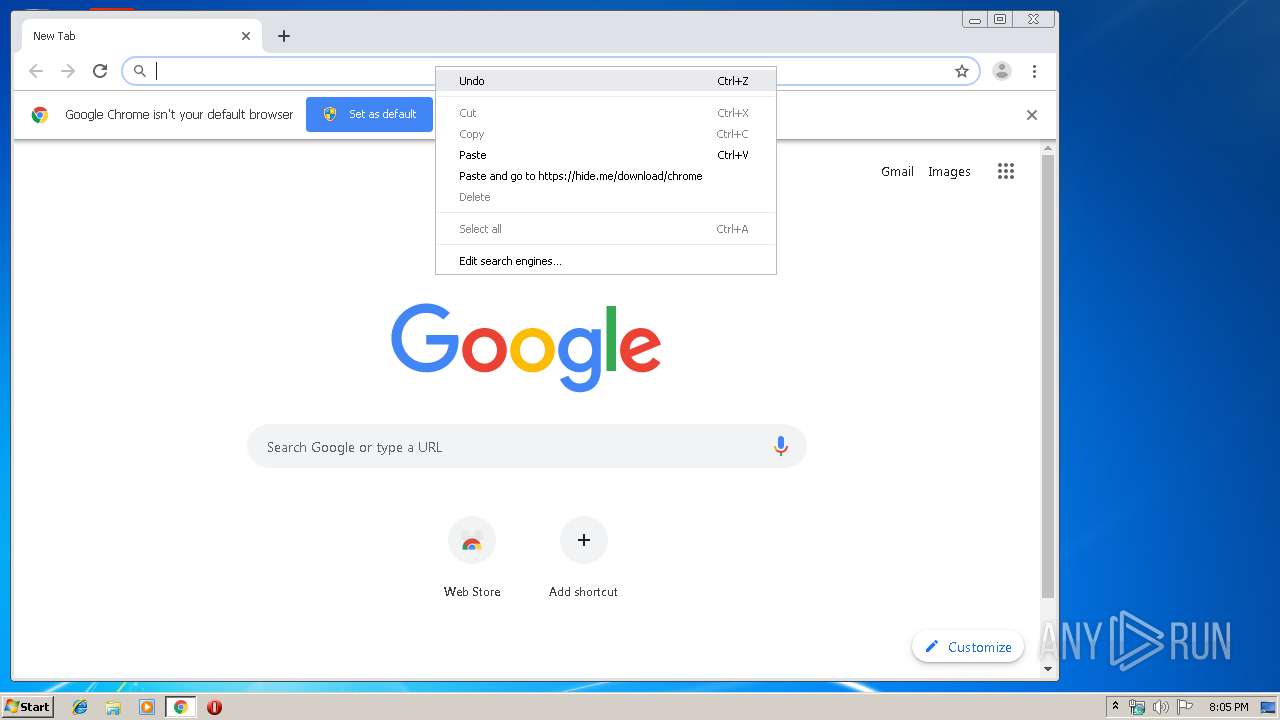
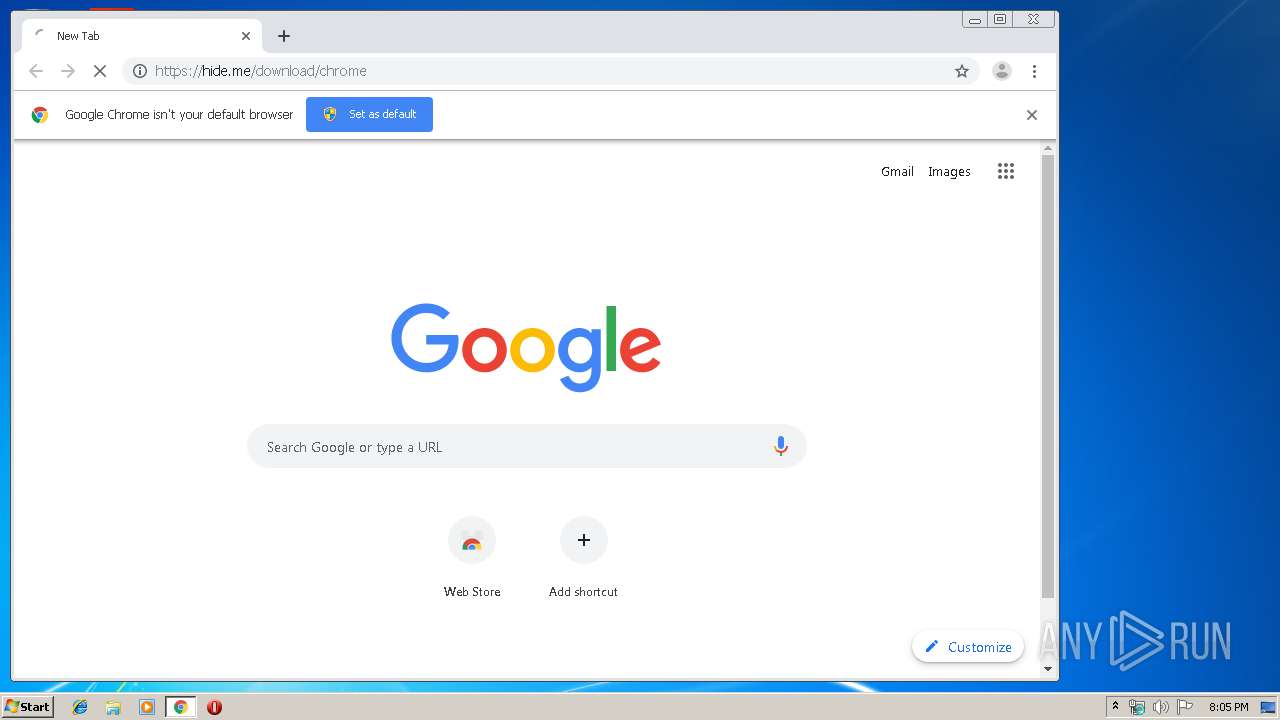
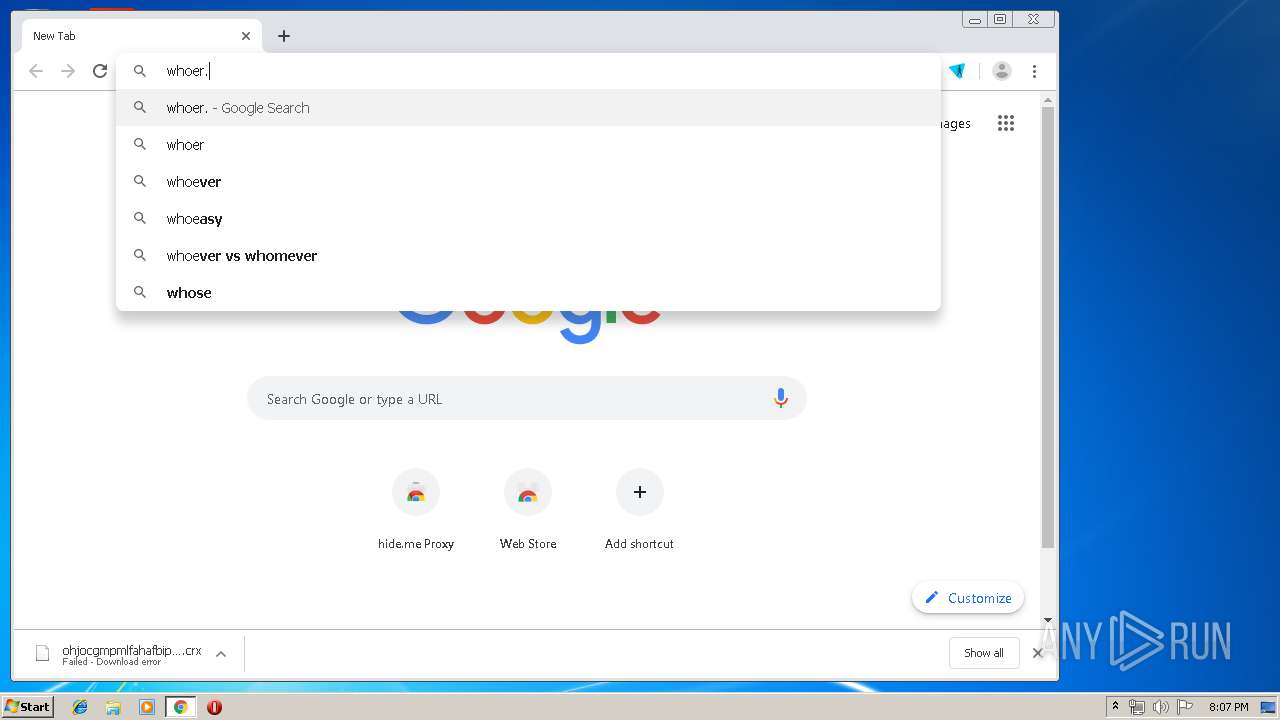
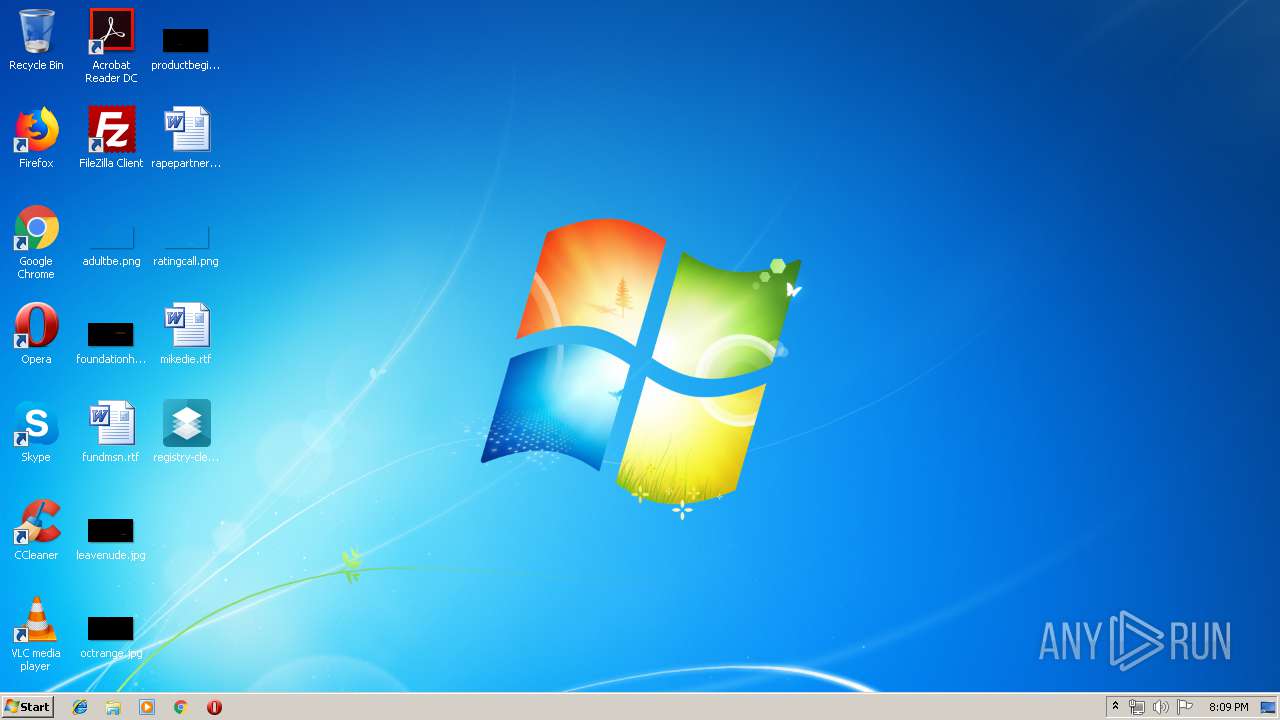
Manual execution by user
- chrome.exe (PID: 3988)
Reads the hosts file
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2832)
Reads Internet Cache Settings
- chrome.exe (PID: 3988)
Application launched itself
- chrome.exe (PID: 3988)
Creates files in the user directory
- chrome.exe (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 100352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.2.0.2 |
| ProductVersionNumber: | 8.2.0.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics Registry Cleaner Installation File |
| FileVersion: | 8.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics Registry Cleaner |
| ProductVersion: | 8.2.0.2 |
| OriginalFileName: | registry-cleaner-setup.exe |
| InternalName: | registry-cleaner-setup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics Registry Cleaner Installation File |
| FileVersion: | 8.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics Registry Cleaner |
| ProductVersion: | 8.2.0.2 |
| OriginalFilename: | registry-cleaner-setup.exe |
| InternalName: | registry-cleaner-setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0001669C | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.74985 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.78021 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.82908 | 2848 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.73014 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.79725 | 4936 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.79455 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.73831 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.71431 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
94
Monitored processes
54
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18322249683063254561 --mojo-platform-channel-handle=3060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Users\admin\Desktop\registry-cleaner-setup.exe" | C:\Users\admin\Desktop\registry-cleaner-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: MEDIUM Description: Auslogics Registry Cleaner Installation File Exit code: 2 Version: 8.x Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14268961605078036570 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17053610392664484490 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Users\admin\AppData\Local\Temp\is-M42UM.tmp\registry-cleaner-setup.tmp" /SL5="$40136,14868332,167936,C:\Users\admin\Desktop\registry-cleaner-setup.exe" /SPAWNWND=$30128 /NOTIFYWND=$4013A | C:\Users\admin\AppData\Local\Temp\is-M42UM.tmp\registry-cleaner-setup.tmp | registry-cleaner-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2132383798546832991 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6147921536936412235 --mojo-platform-channel-handle=3356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\is-L2Q39.tmp\registry-cleaner-setup.tmp" /SL5="$4013A,14868332,167936,C:\Users\admin\Desktop\registry-cleaner-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-L2Q39.tmp\registry-cleaner-setup.tmp | — | registry-cleaner-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6259554535068944676 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14800945125659099412,14632759020013894861,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7004194718989175019 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
971
Read events
764
Write events
195
Delete events
12
Modification events
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 58020000DE10148C4B9ED501 | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 0CDECE0443E8A17815BDDEA0BA1C01001A23553A5D057637F5836FB61E9F6455 | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\Registry Cleaner\8.x\Settings |
| Operation: | write | Name: | General.Tracking.URLMarkers |
Value: registrycleanernosid | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\Registry Cleaner\8.x\Settings |
| Operation: | write | Name: | General.Language |
Value: ENU | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics |
| Operation: | write | Name: | ClientID |
Value: {70167C3D-536E-4EB6-B499-8486D6B8D9A1} | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\registry-cleaner-setup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (600) registry-cleaner-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\registry-cleaner-setup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
14
Suspicious files
70
Text files
398
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\CommonForms.Site.dll | executable | |
MD5:3E6FDC120A59D8C9D43BD5491129DB0B | SHA256:66701D1F754B575A9D3F26A9734D6FBC547C26491EE2ECA77BCAD657964A7B40 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\SetupCustom.dll | executable | |
MD5:8FA93E2641234C34637739B72DF4FC8E | SHA256:FE4D13460020CBF8A638439ADEE0716B83A4638216F2DDED1516AD3D26C0A692 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\CFAHelper.dll | executable | |
MD5:8903CF85747B2BA59C1DDA980F30497D | SHA256:CED1C6EF906DF862065EC2C41C71AA6BC1788CF4DA17AF35B947750052281C5B | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\Localizer.dll | executable | |
MD5:B20CB261CC19CD16B5DD8DC0A8B8D930 | SHA256:02EAB6877429837772F499790F6C9DA149A3DC8F7F768054E1551DAFE14B2ED7 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\sqlite3.dll | executable | |
MD5:C2E9750EC9F907D77A804FF9EB009F9A | SHA256:D937C1078ACE9EBCA21AA52B89ABAD883FC1200B5D815B020FC4535E2DDDFC5C | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\vclimg250.bpl | executable | |
MD5:163F093E39C16D52E3B9667C955C1FA1 | SHA256:C1DE812AC4E1AAE0A0C0340A1A2ECEBFFFF4A8099F66A3697B89EF812BCBCDC1 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\EULA.rtf | text | |
MD5:910E74D4395B4142B0073CF025EE645E | SHA256:F2663844A5130B70A7F3E9BD4A5F4D0C6DE540CA1DB384F6536D72D0EC2C2FD8 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\BrowserHelper.dll | executable | |
MD5:1443FECB551CDF092BD6B4ADB35F19A7 | SHA256:28074758ECD62FCAF320CB75289497DAFCE1DBDC317E47874D0DD771F4A68305 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\main.ini | text | |
MD5:609916C6DE8F9DDDB8FD238CCCA6597B | SHA256:4081CBE3C2C20BC958CD71667CB0489EFDDD02E2E5D412F114D139A3859EADD6 | |||
| 600 | registry-cleaner-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S2O3F.tmp\fra.lng | scd | |
MD5:E203AF16DC71EC4746852193F1723905 | SHA256:193C0481D015575AE332B21AD7F6D7635212CCAC5BA681E59BE2685BD434850D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
88
DNS requests
33
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | chrome.exe | GET | 200 | 173.194.5.216:80 | http://r2---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.17&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1574107515&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2832 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
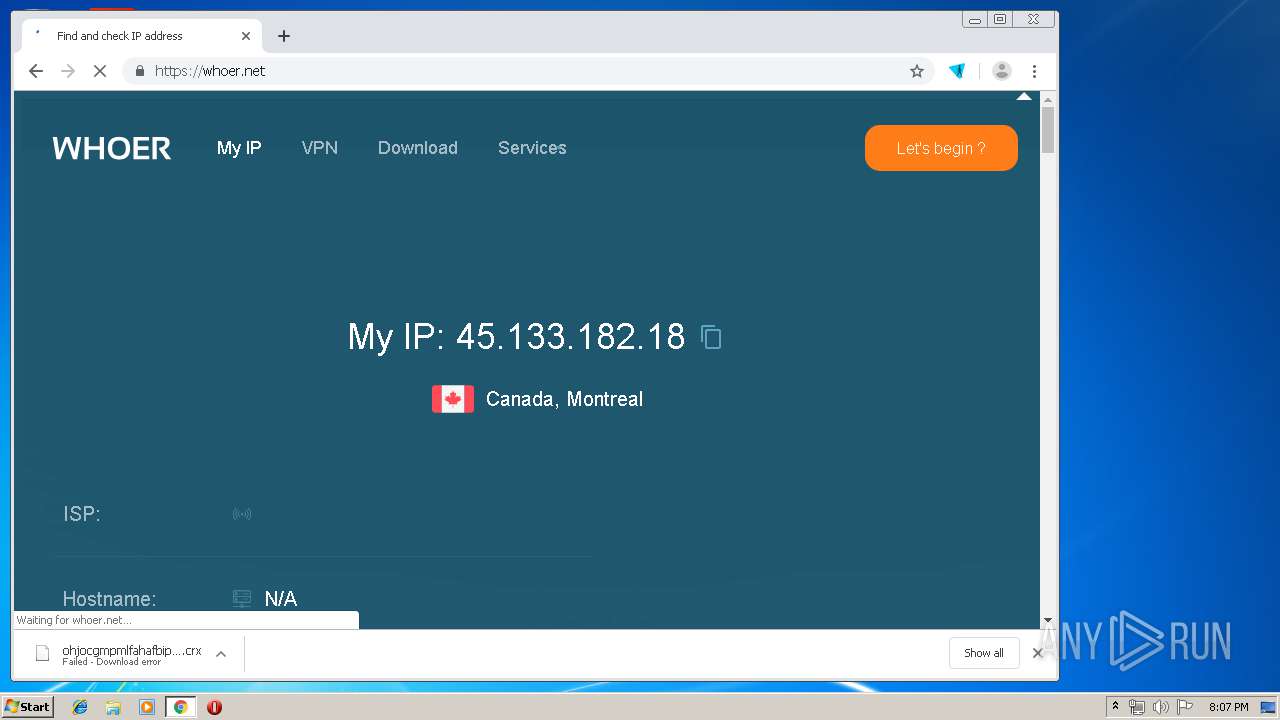
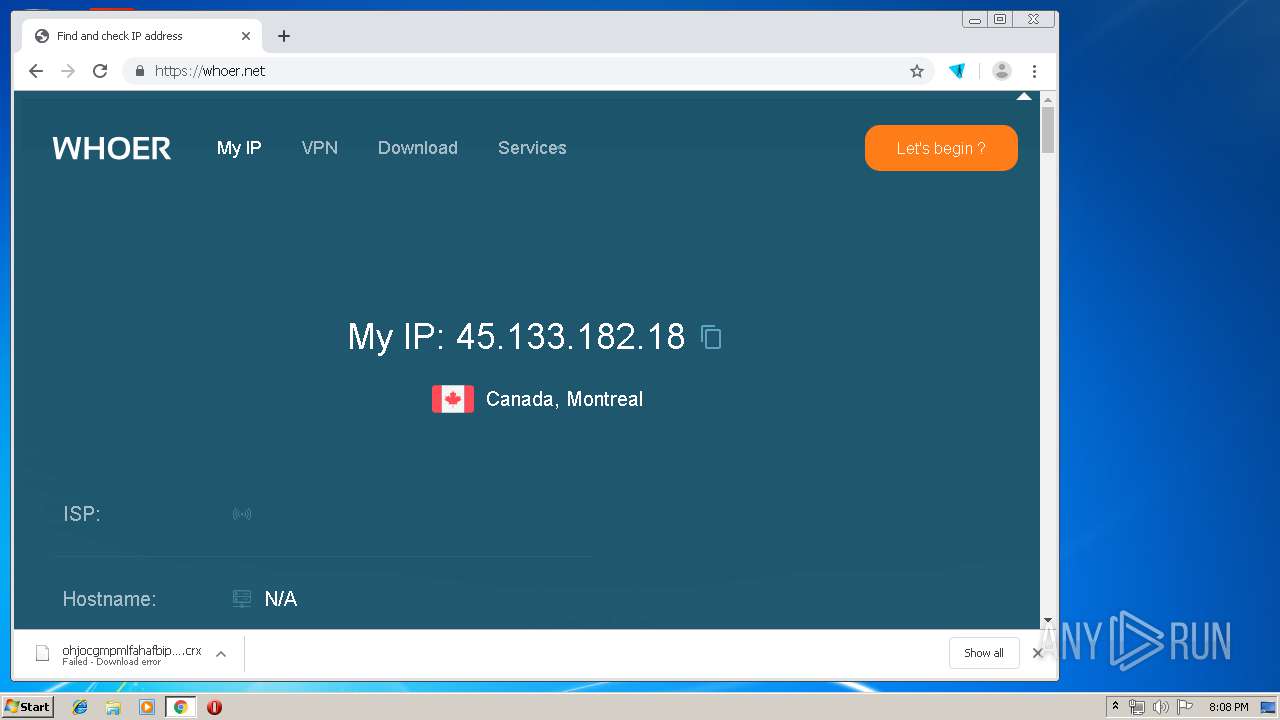
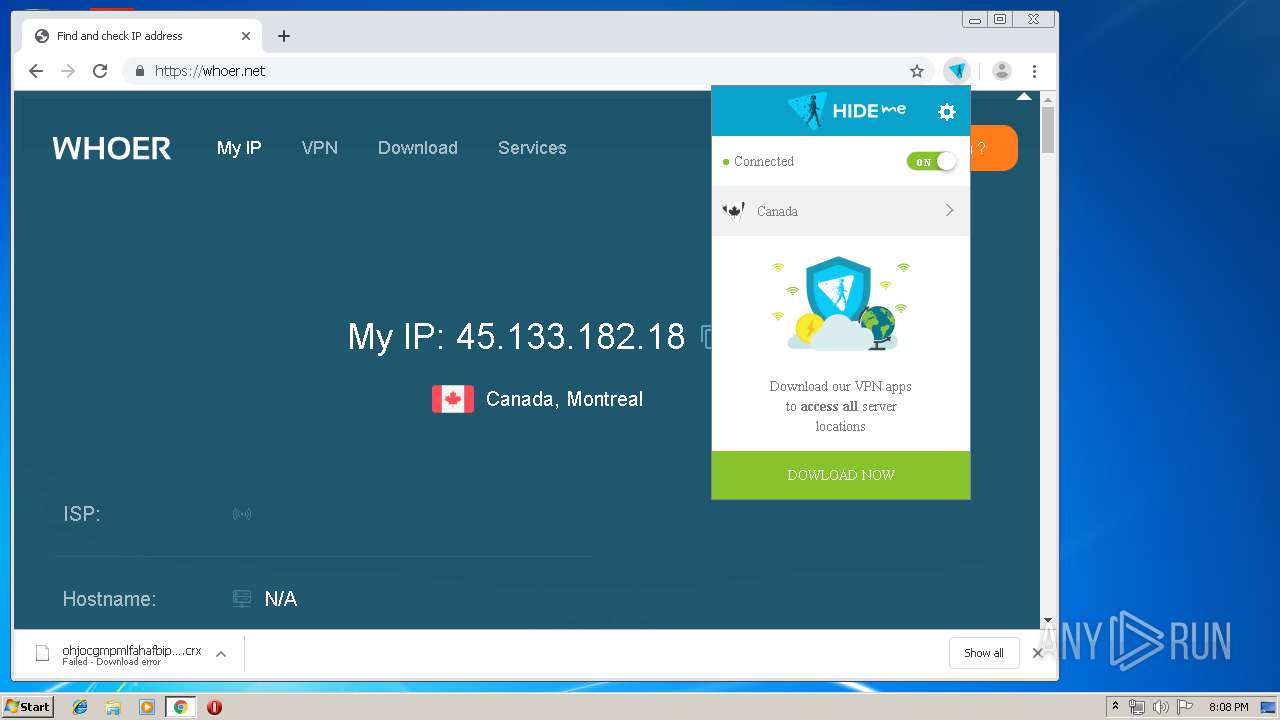
2832 | chrome.exe | GET | 200 | 188.166.142.39:80 | http://188.166.142.39/servers/list | NL | text | 247 b | unknown |
2832 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2832 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2832 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.17&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1574107515&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
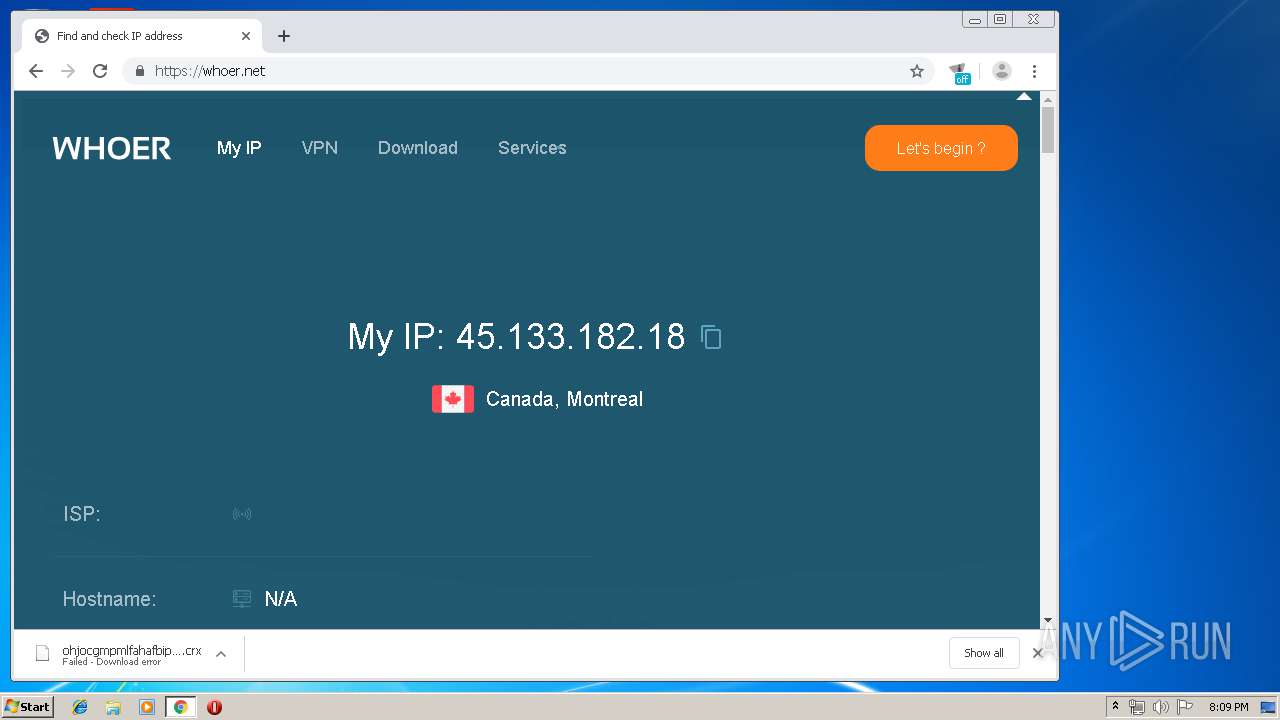
2832 | chrome.exe | 178.62.194.172:443 | hide.me | Digital Ocean, Inc. | NL | malicious |
2832 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
600 | registry-cleaner-setup.tmp | 45.33.8.241:443 | www.auslogics.com | Linode, LLC | US | malicious |
2832 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.16.131:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.18.110:80 | apis.google.com | Google Inc. | US | whitelisted |
600 | registry-cleaner-setup.tmp | 216.58.205.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
hide.me |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2832 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1 ETPRO signatures available at the full report