| download: | hidaihfa |
| Full analysis: | https://app.any.run/tasks/5cfa4183-852a-4711-87f8-8d22dc86ff81 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 18, 2019, 08:09:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24F030B17DD8152A3CD04253DD648690 |
| SHA1: | 456FB8F627C1E28745C9F63FAF2615E1A0CC1D66 |
| SHA256: | 57ACEA19D6B84C350A6C9CF2B55794377C7D12491B65AF1D06C7F857316F1D7B |
| SSDEEP: | 12288:QasyKZffHK7s1cLOhTpOfekiImLZGMn55aYEO:AH+LOF8ek6fn5I7 |
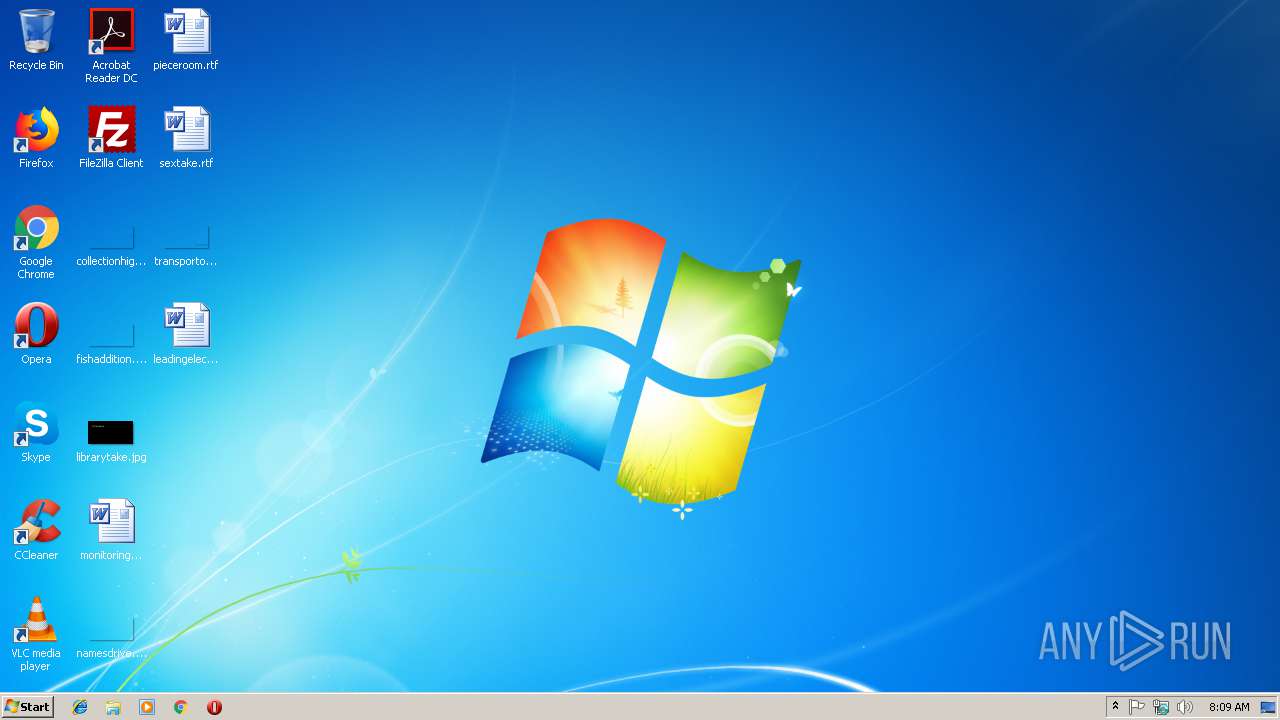
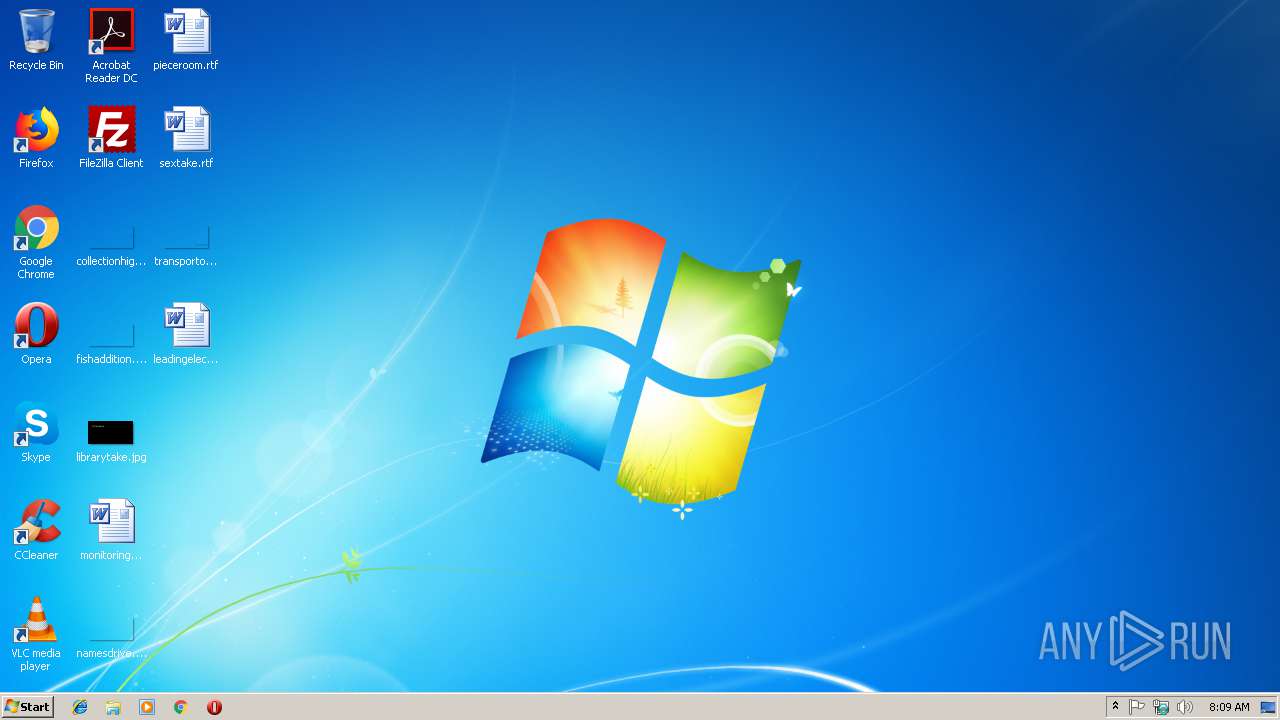
MALICIOUS
Actions looks like stealing of personal data
- hidaihfa.exe (PID: 2984)
GandCrab keys found
- hidaihfa.exe (PID: 2984)
Writes file to Word startup folder
- hidaihfa.exe (PID: 2984)
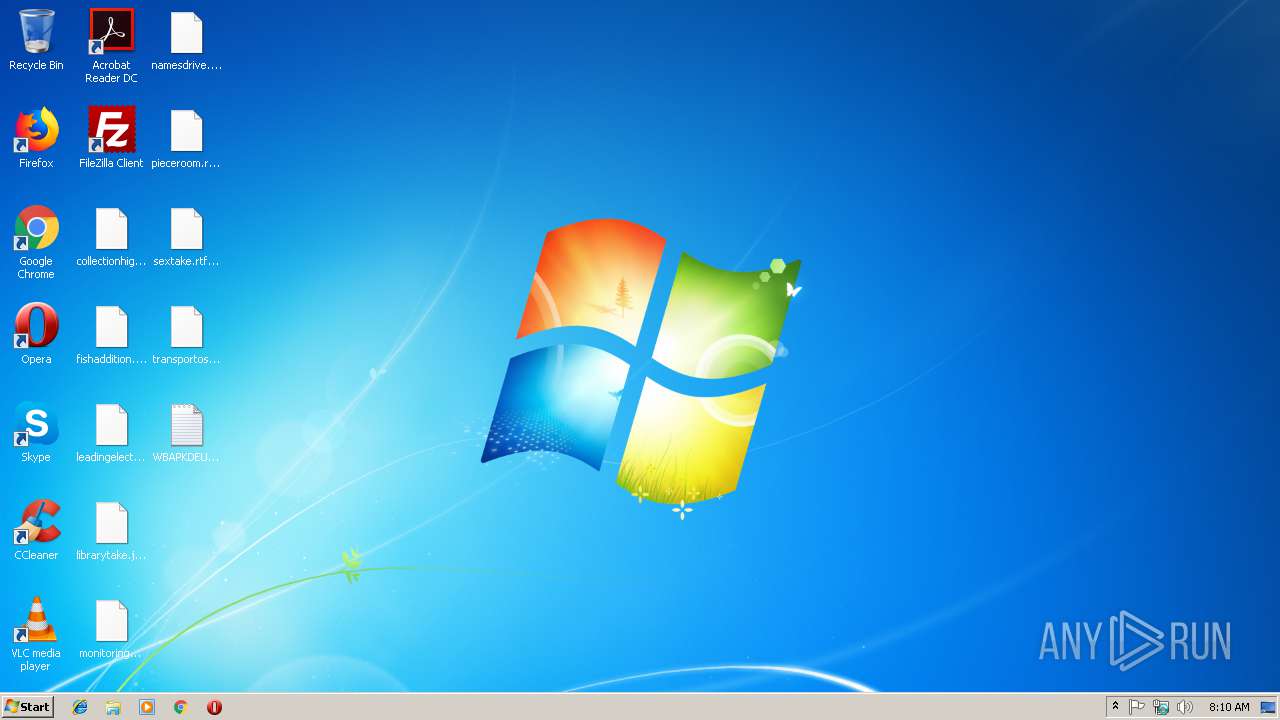
Renames files like Ransomware
- hidaihfa.exe (PID: 2984)
Deletes shadow copies
- hidaihfa.exe (PID: 2984)
Dropped file may contain instructions of ransomware
- hidaihfa.exe (PID: 2984)
SUSPICIOUS
Creates files in the program directory
- hidaihfa.exe (PID: 2984)
Reads the cookies of Mozilla Firefox
- hidaihfa.exe (PID: 2984)
Creates files like Ransomware instruction
- hidaihfa.exe (PID: 2984)
Creates files in the user directory
- hidaihfa.exe (PID: 2984)
INFO
Dropped object may contain TOR URL's
- hidaihfa.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Clipper DOS Executable (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:17 16:14:17+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 189952 |
| InitializedDataSize: | 290304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16d5a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.9.7.6 |
| ProductVersionNumber: | 6.9.7.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Vbprj Feed Folderbrowserdialog Livermre |
| LegalCopyright: | Copyright © 1995-Present Domo Technologies |
| InternalName: | Protection |
| OriginalFileName: | Protection.exe |
| CompanyName: | Domo Technologies |
| Comments: | Vbprj Feed Folderbrowserdialog Livermre |
| ProductName: | Protection |
| ProductVersion: | 6.9.7.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2019 15:14:17 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | Vbprj Feed Folderbrowserdialog Livermre |
| LegalCopyright: | Copyright © 1995-Present Domo Technologies |
| InternalName: | Protection |
| OriginalFilename: | Protection.exe |
| CompanyName: | Domo Technologies |
| Comments: | Vbprj Feed Folderbrowserdialog Livermre |
| ProductName: | Protection |
| ProductVersion: | 6.9.7.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Jan-2019 15:14:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E536 | 0x0002E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.73045 |
.rdata | 0x00030000 | 0x0000BAB6 | 0x0000BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8855 |
.data | 0x0003C000 | 0x00004A64 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91848 |
.rsrc | 0x00041000 | 0x000348AC | 0x00034A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.32468 |
.reloc | 0x00076000 | 0x00003B94 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.09054 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11681 | 530 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.18613 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.37186 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.74274 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 1.74461 | 10344 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.22704 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.76051 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
179 | 7.9558 | 7951 | Latin 1 / Western European | English - United States | PNG |
285 | 7.94932 | 11390 | Latin 1 / Western European | English - United States | TYPELIB |
1229 | 6.50383 | 128 | Latin 1 / Western European | English - United States | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DWrite.dll |
GDI32.dll |
GLU32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
MSVFW32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2860 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | hidaihfa.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\Temp\hidaihfa.exe" | C:\Users\admin\AppData\Local\Temp\hidaihfa.exe | explorer.exe | ||||||||||||
User: admin Company: Domo Technologies Integrity Level: MEDIUM Description: Vbprj Feed Folderbrowserdialog Livermre Exit code: 0 Modules
| |||||||||||||||
| 3308 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
80
Read events
73
Write events
7
Delete events
0
Modification events
| (PID) Process: | (2984) hidaihfa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E0077006200610070006B00640065007500670063000000 | |||
| (PID) Process: | (2984) hidaihfa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A4000052534131000800000100010025559BAD9D10EE5C1BA978FB1FBE10C9BF7A980EB96EE543BD23D77B777C9DCE514F43535275509BD3C8092C755225B483B3C540B56C1FD4149928CCB93150E107B0365E6E700A39A15AD51921D67BB0BAFF34BD663409137844A7114D4F9C74128344434532BA42ECA886AC7F7B7CA3040ABC90295FB730426829DD35A0FE694D842C02EEF1DB7B3E775D9DF819382FA0EDF1F628005A06D3FED81DC09475ECE97C96DC13DAEA546416BC8C4956ABB0B1B0BA55DE26CC6C9AB49787D72D85B299D91700E0CD69594EF95A62AE6841B40569B423A31C37CE298DCF09F8AAE2C4BCEF1E3BA36F7C7FEE567BAFC43ADA7BEB0789EF62C822EAF3CA6BB9F2DE0EC5 | |||
| (PID) Process: | (2984) hidaihfa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 940400004AA8FCB4C1E74EAB7F1E32BC669DDE07E959AA4C5374DBD5BC6C26666EE3910F516560FCD588614F558B7A3F9B9C9AC72BAFEC12F0494ADA9BB420777AE6071983D00B788EBAC04DEE9A9C13F67044749D07A41E538D7B97F928E4DA447DCD24C199531D938668F6BFE6BD94040785CE11A195F0F1F8343C2499243029A205288ACC04D81D105EDA74B08011DF168E440EFA5A01B159D6CD00F0DB0243AA6B85CA7B5E15DA210F0D9AFA135EA6985F976A770B2613183E2AA0101D9AA0F55A0977882AD427618EA117CAF6E24773B1026E53E2700ADA5A1961E7B53B7FA027FD7C337E3801080818D194FE0B7CC1E28F7B0D96BAED52DC3499D7D8E207AFFC83F00703D3243E18345122D2134989478D9AA8CC4959D447BC3CB943CC70448C6718D2AE741A6667BBA2030E9FECD2784EBE6B1ACA473CC1E8FD573BACE952BE54326DC72E419F9872F167160F9EDCA7A5EAEC9A4E36052620F7F7AC242EBEC6E7DB5898A4C673FB489334522144FFFCEC94C0A2B13A352D819672ECEF0C322A8FDDFD44220B3B2F3F9DFA03D21C15474F253D6472D301326BDF2FCD6EBCCC519109A5B424F644CF44B6611E7B9C70C0CCFDBA6F806BDC2275FA4B915652C60DEE9242255BD1DD26DF159D45C291E30E72D8F3860EDD31467D901C1052F8763291E67916C4D11C82046FC61F30D1FBCE4744B6090A236D570422CC1F011CBC055C427391B755848FF5F8B8CC975D34DF3546BBC7336E65C1EA89455E04D9965FD093B50287862E3E562F54B0FBB156025E9A29CF13343A6002987E6D2E86331E2A273E6C0CE292AC067630DB516715E146F45AB2D8D679E91849F768571F58233E2594747314180758C626A50C4C433C440A5FD6DA28246072EEEDF05D4845D3BFFD9D6B445509E71FF4CAC4FF66360BB61FFA0C6D7F9F1770AF8E7A3680129B15117E5E7EB6C0FA7A16E223F9FB60A79C5EC60FBDCBA137BA70689158A06ED1B309D3B9D30EA58A90456EBDF550872BE699F30C4EC2C32F08AEBDFC7E85EFA06700653A4C24D1749BF86EEC9C2A464F49368945F828B240CD8B86274EA57F2FD04E09B266DD56DD3D1CB693550EF1852E76AD21B4F9355E64927AACEC31C0DD3824366192AD09E72636F9945E1E0290A247E576B8C38169D8B6A54982F8C7CF958E7364305FB328F2C90B08D0461CF80EF8EA501B8D13C4FB5150C120C3C808C1DC430072B70FB3B3BCFD9CB47A3054A143CB154F4B07021340610067E55E42E767844E16CD2BEFFE7F4B65F060225801533FC96702016B8DBE208F5953CF281A8F5DDE96553DDB798316C01ED929700F1BFABABF336C859CFC6F78FADA94DC1BACA1BDB1353735AB609804FBBC8C9AF6B4DF2DDB06543B378695299281111B58577B7854744353B1DB4868E57465AF1A3A44E29BA25E2A5BE6808C6C8C3433827BA4B78925752DD77750C922AC1960197AE69FCE8B7E265C3F082EEBB73B7C5DDFB11EF1B45FBDBCEA9CDCA91021D633F52A976326D638AC06AFB45A7BDA09DF0F051C81D8D0EC07DE99F3289072ED2BD362191D921BC93BE30F44EEC15BD4EF8E879E7DE331CD2BA54AA6E8BA29C1377F2DBFE05C8228733C152083B9149A347DD0EEFED8A67A495577BB0043BB6D21A2E838CF18A73ACED6E72B4290FA3974E6C5F2B2876E9AF2A393CCFDD6094499027A910E061DD012783C0C33D264FE0793D020BEC6EE8452C291EF51350A6BC03D14D39F859CE88DFD6793179380610CDD9F59011B4D7E8F98A595A1C2DA4D86C196257B5F707B059A6AC9D68FB27A42ADCA23B0474B65BE862FAAF0B136259F049AAD7EB7E435FCE45D672CD2CE9BD255C5BC2BF634807B949A15A9F4EA1D47A70DC6E98C95CF74D49D8A73F4F550946813EE16825F12B3EF7C72C6BD501599A6399B60573ECBD9C0204E4BECC675D31031FBB4510DE7318A714AE60B5B67DBB2338D53F1600F78740BC70933D9CA79A19F97779CF4DCA4DA0E255DFCBBD90CDA52A5E17D3C64804DFBAE61D12979C479C20A9C0DB18A5E22B4D594300ACAFBB8AB9473AE17E2F59BC0534F73597773DE021C2558A306AA4D52BABDA419FCB19952551707F6FB76796E9A3727887CCE5CDAC88004A61C2D2860F087E2B1DE225C8DF06D9A104FDEB81EABC5EF1A68786FFFCAD391DC6E175F584B3EA79606B48BFC673979E6E73B411DCA35C58A625DB485740A21F1C2B62690BE0A7535C60CFB5C2FAAD184E604F115BB8C15BDF90BB1BF672423E547EB042D3243B561F94251476DC7030C557B6E41A9484C3F54706820F096F5FA60A3C50B10804E5A44C8D2E48F0443572F5E56F0CF19AE65CCB4121C3CC40AA9D4FB6F4C27AA0CF15C74F7E711B8 | |||
| (PID) Process: | (2984) hidaihfa.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) hidaihfa.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
424
Text files
322
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | hidaihfa.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.wbapkdeugc | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\WBAPKDEUGC-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2984 | hidaihfa.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\WBAPKDEUGC-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report