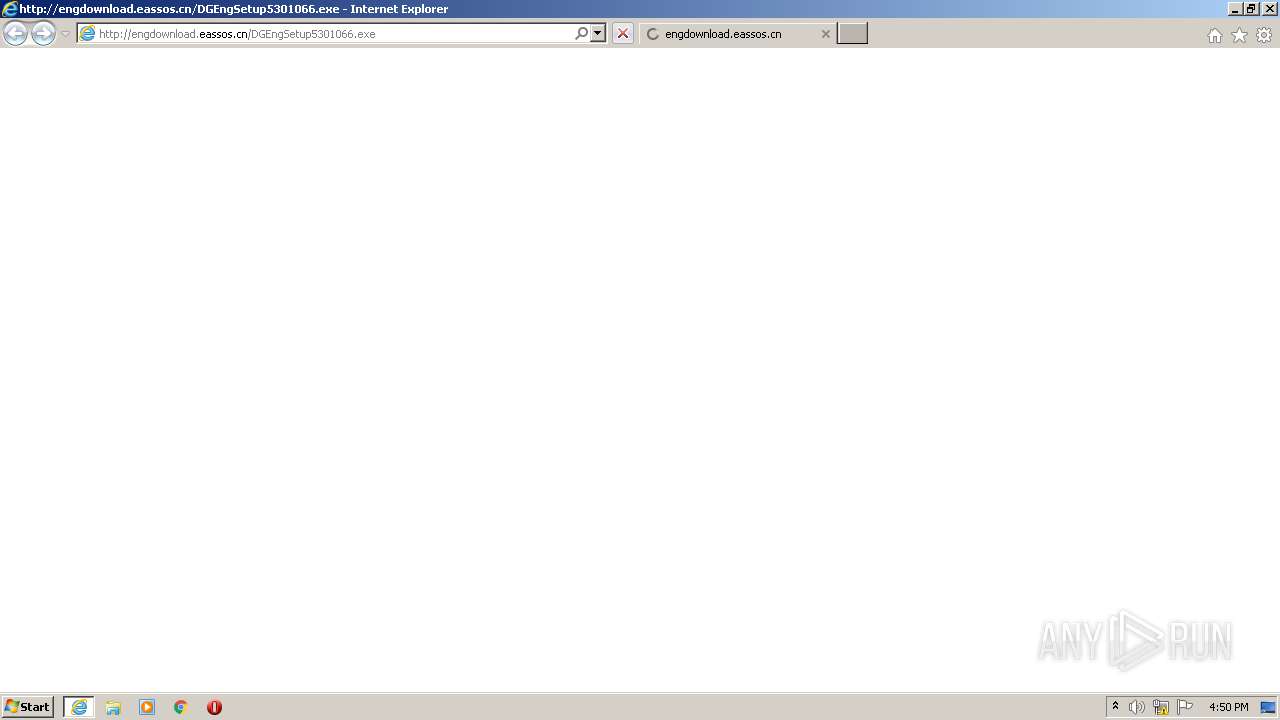
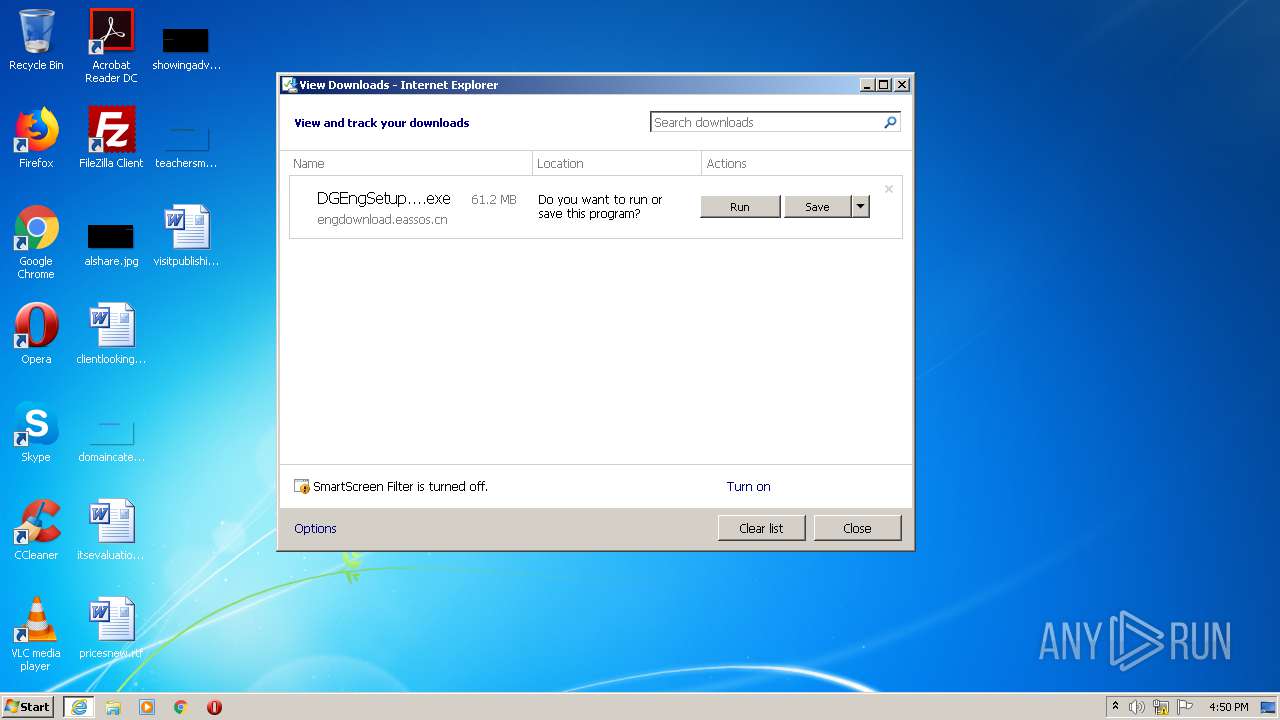
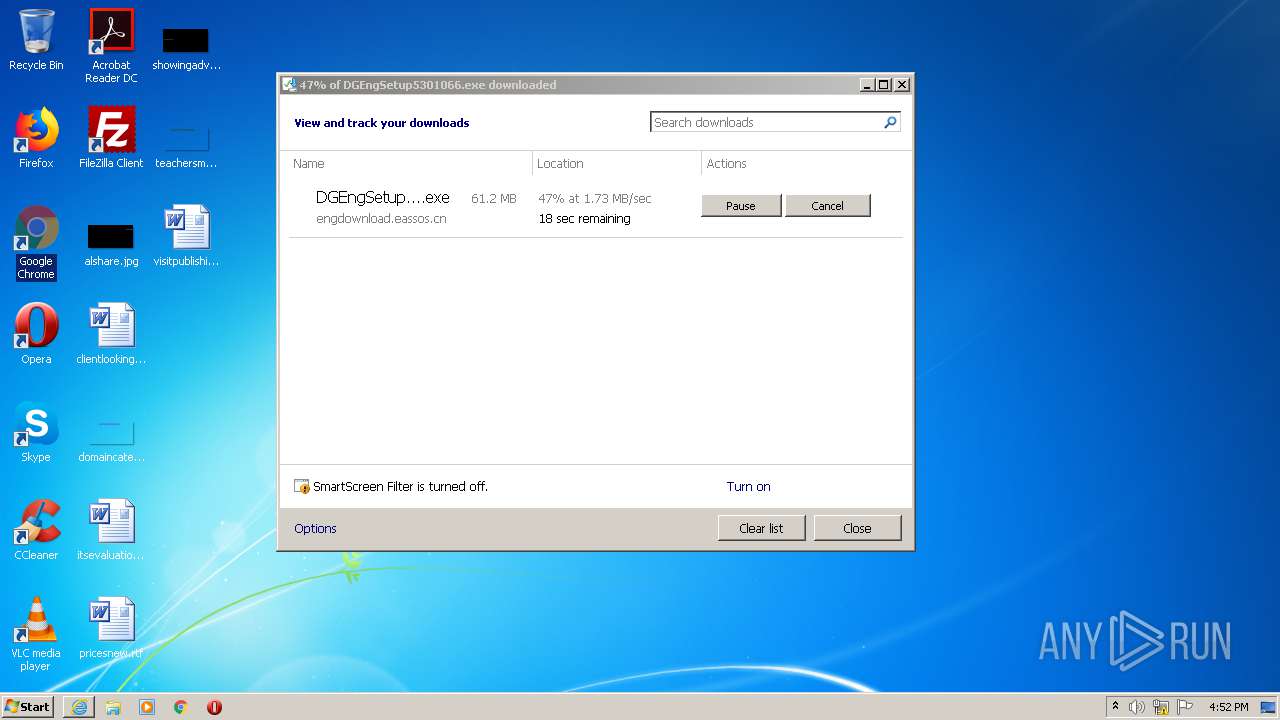
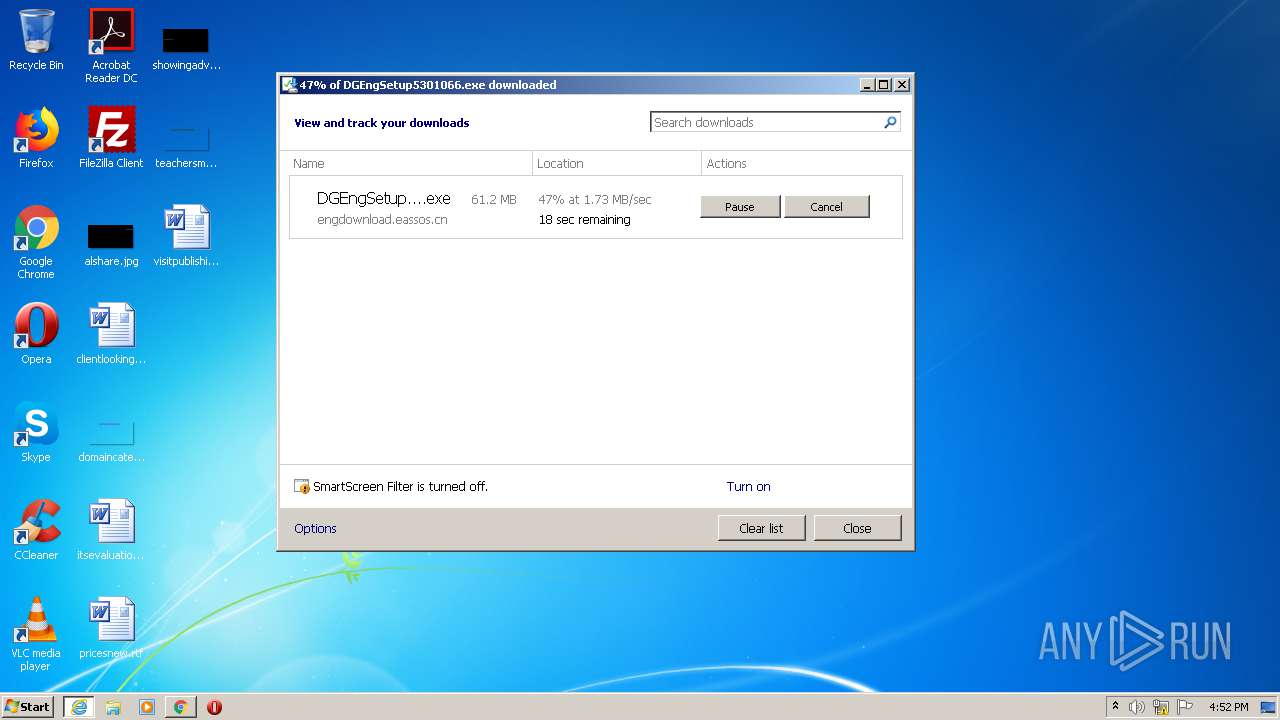
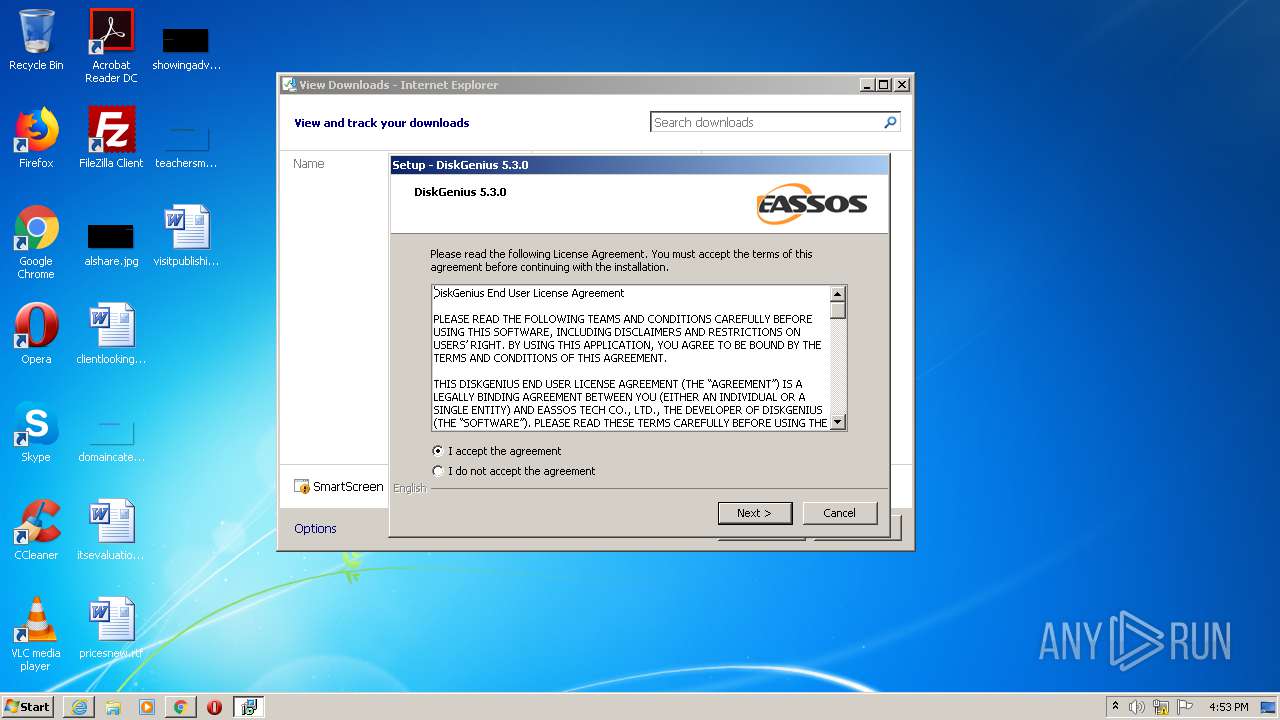
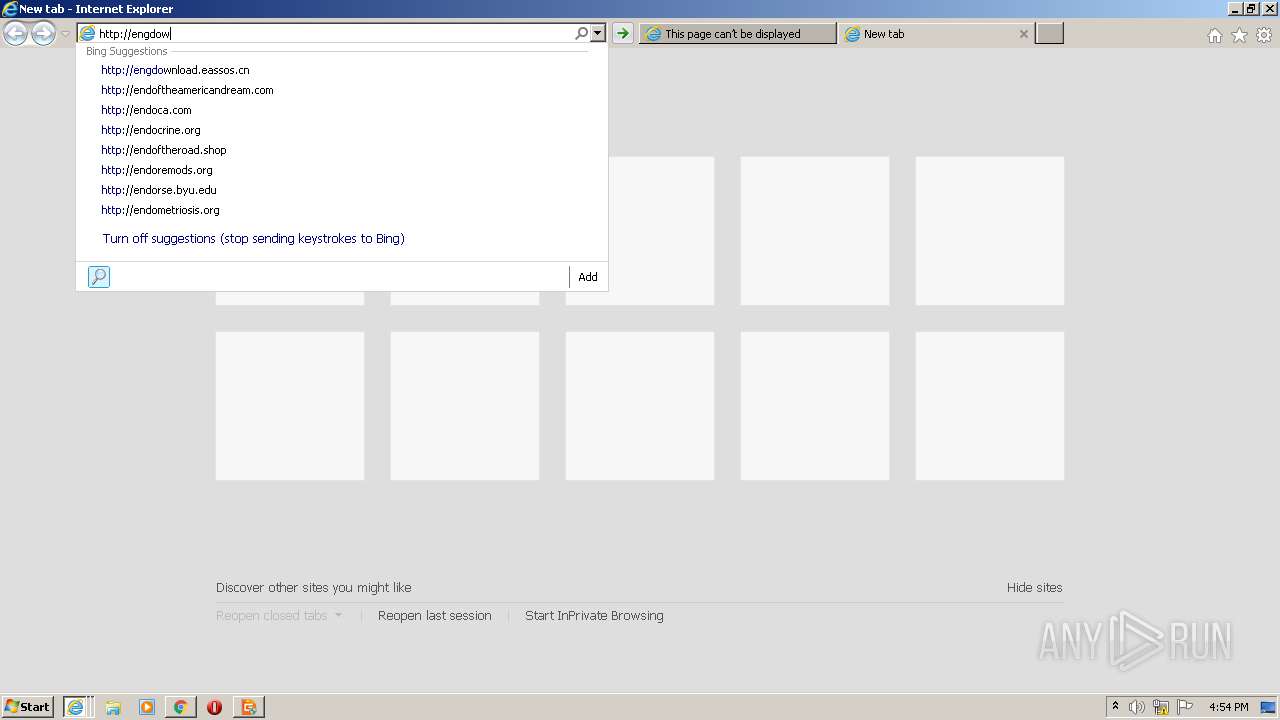
| URL: | http://engdownload.eassos.cn/DGEngSetup5301066.exe |
| Full analysis: | https://app.any.run/tasks/f1647410-c87e-45a6-a202-266a09c18b96 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 15:50:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 21762C33CDE0191CD2FEA3258D937932 |
| SHA1: | 6CCA8518EAC66032A671E9047291D266349DF6CD |
| SHA256: | 579FE79BBCA7CCDB2FB92C6CE24CE1E235B21D70A4C81BD308564853214DD22A |
| SSDEEP: | 3:N1Kb+nmWyeS20AJST0Cn:CynmHeS20AJStn |
MALICIOUS
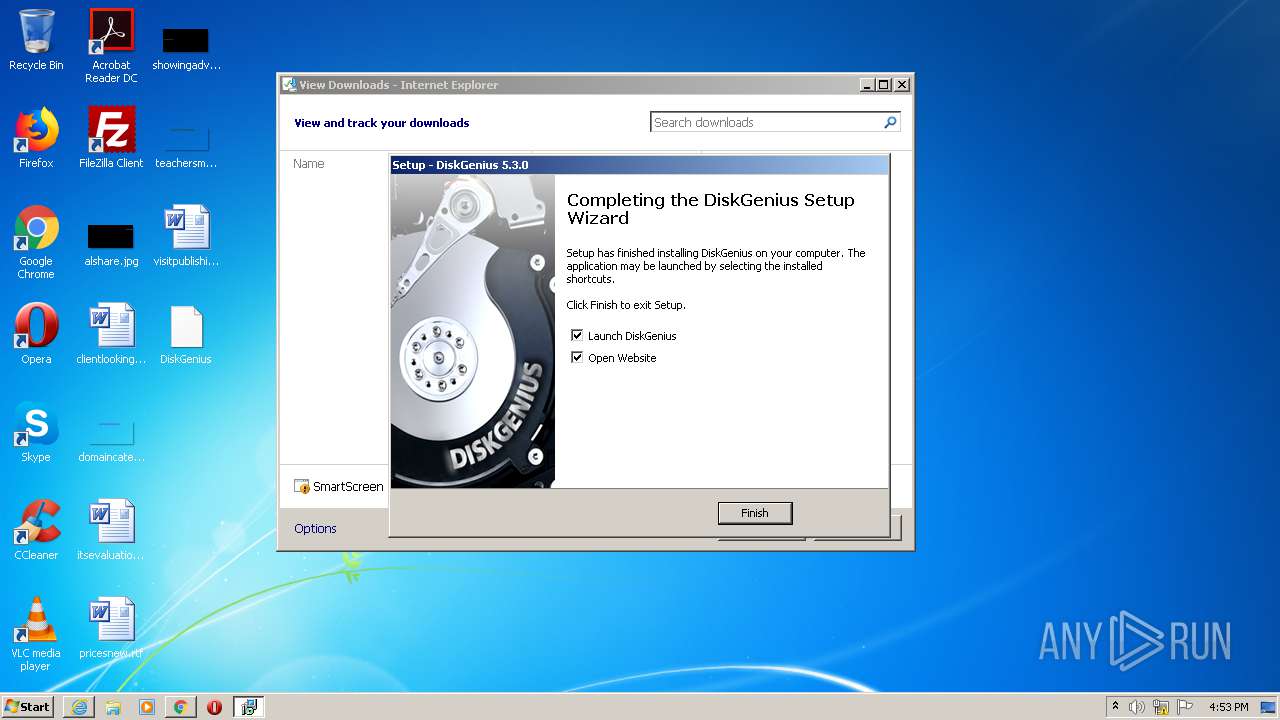
Application was dropped or rewritten from another process
- DGEngSetup5301066.exe (PID: 3924)
- DGEngSetup5301066.exe (PID: 1628)
- DiskGenius.exe (PID: 2604)
Changes settings of System certificates
- DiskGenius.exe (PID: 2604)
SUSPICIOUS
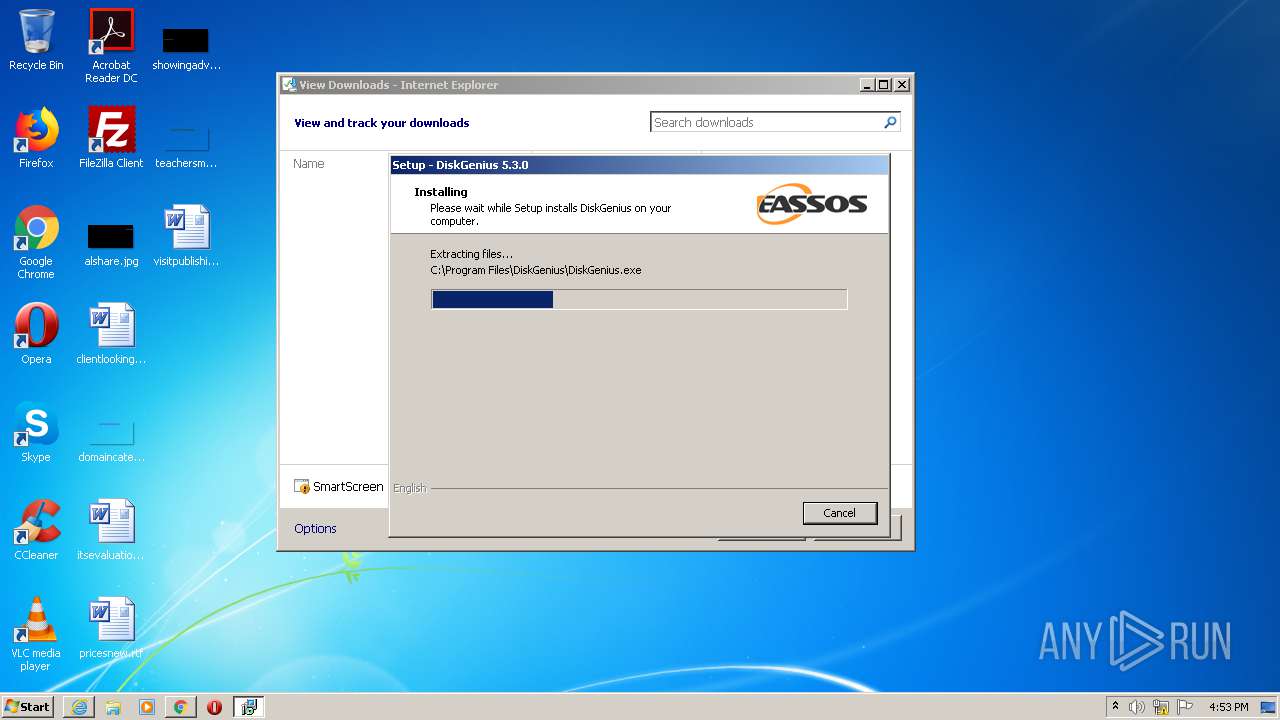
Executable content was dropped or overwritten
- DGEngSetup5301066.exe (PID: 3924)
- iexplore.exe (PID: 2732)
- DGEngSetup5301066.exe (PID: 1628)
- DGEngSetup5301066.tmp (PID: 3620)
Reads the Windows organization settings
- DGEngSetup5301066.tmp (PID: 3620)
Reads Windows owner or organization settings
- DGEngSetup5301066.tmp (PID: 3620)
Reads Internet Cache Settings
- DiskGenius.exe (PID: 2604)
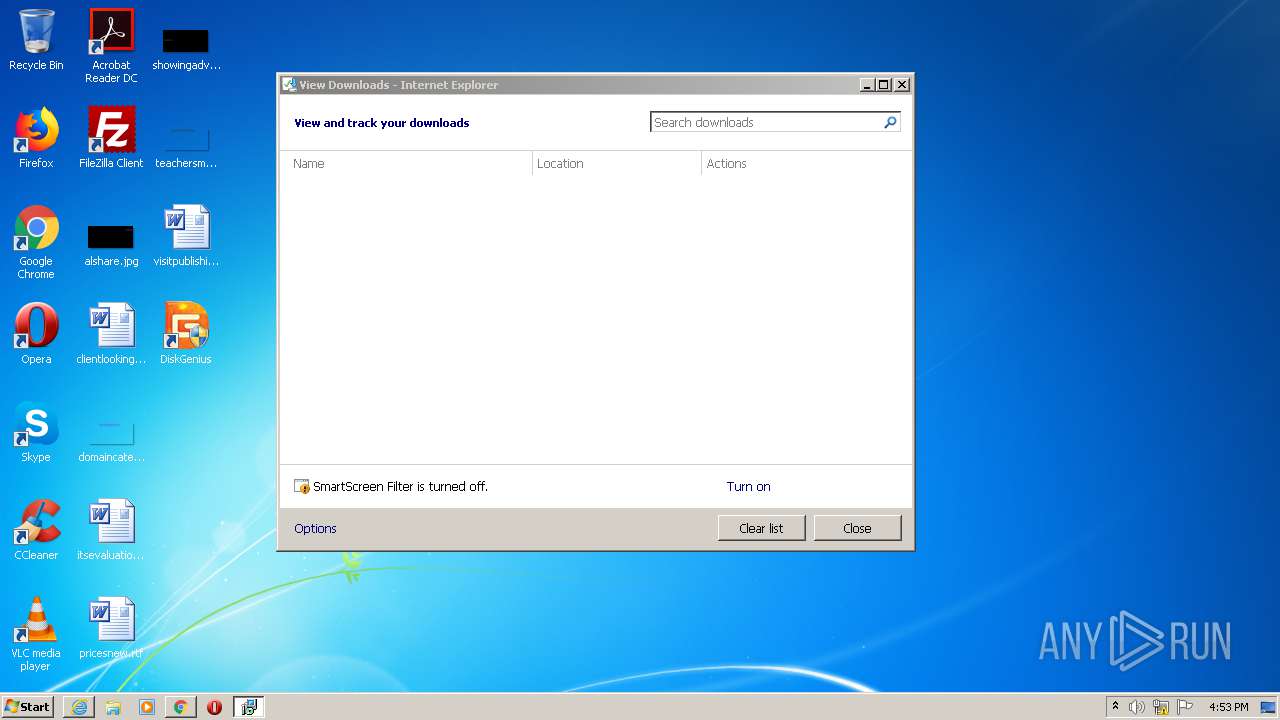
Starts Internet Explorer
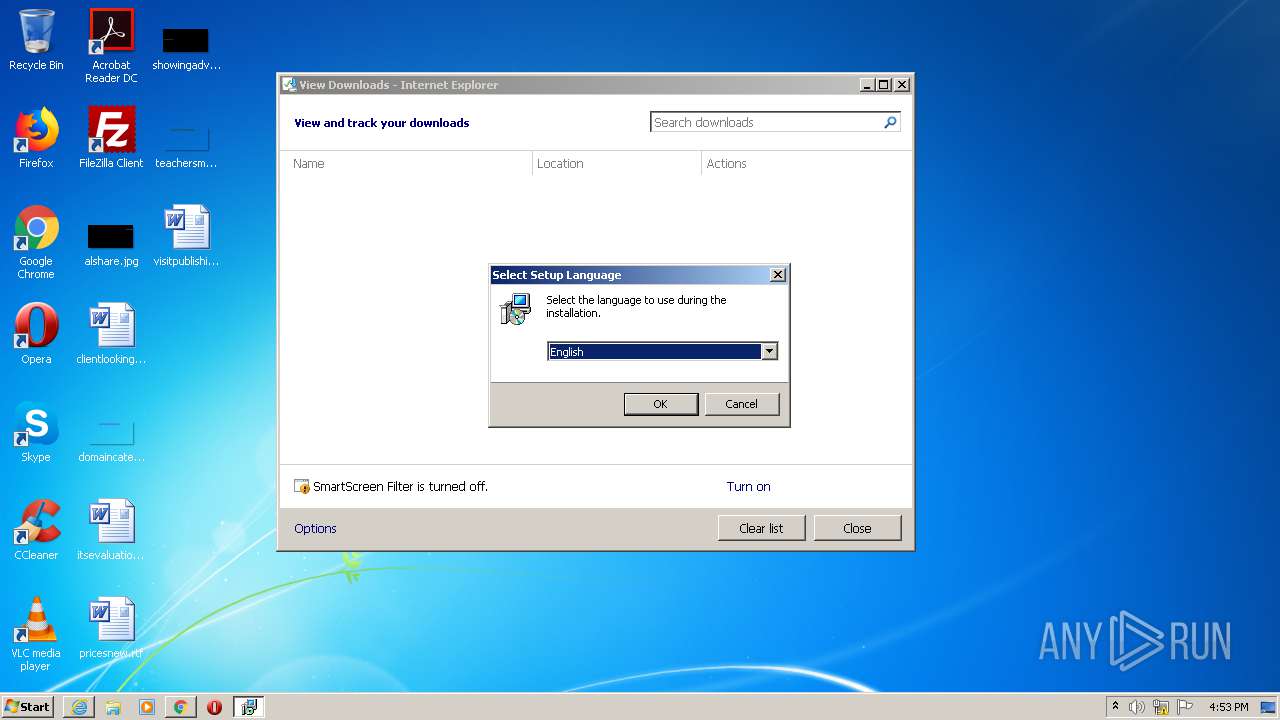
- DGEngSetup5301066.tmp (PID: 2420)
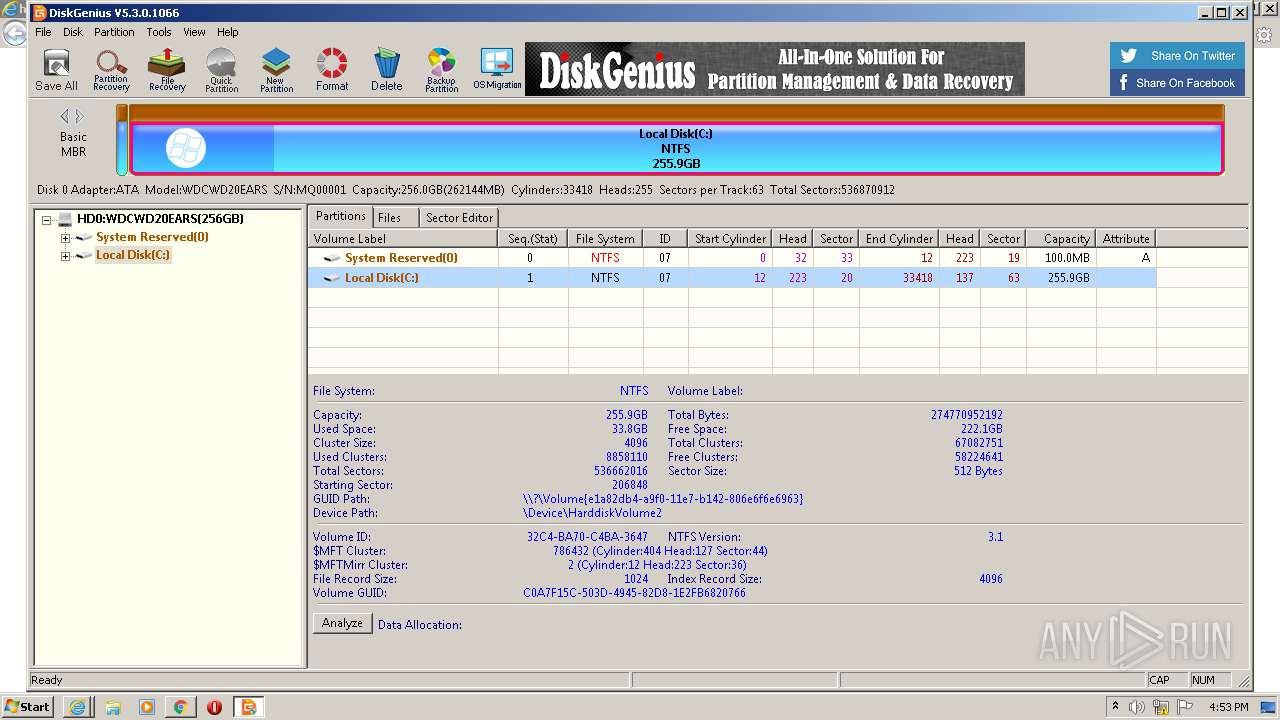
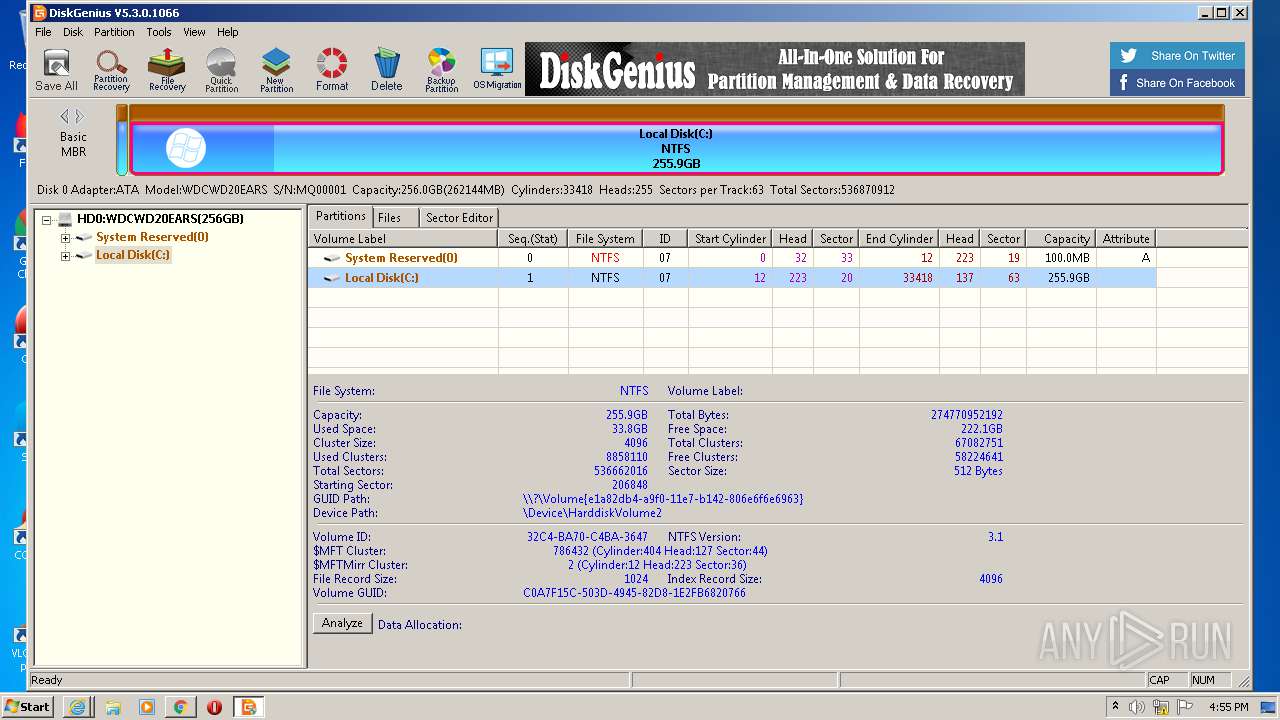
Low-level read access rights to disk partition
- DiskGenius.exe (PID: 2604)
Adds / modifies Windows certificates
- DiskGenius.exe (PID: 2604)
INFO
Application launched itself
- iexplore.exe (PID: 1876)
- chrome.exe (PID: 3028)
Reads Internet Cache Settings
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 3048)
Changes internet zones settings
- iexplore.exe (PID: 1876)
Creates files in the user directory
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 3048)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1876)
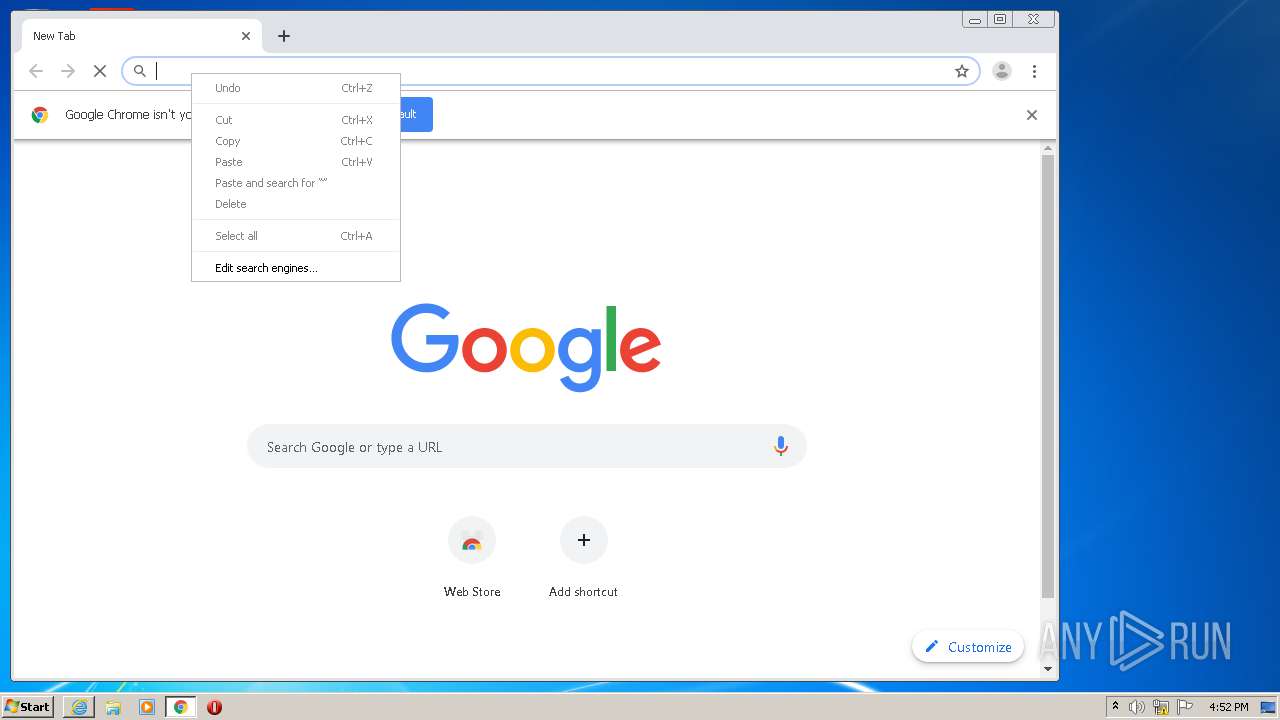
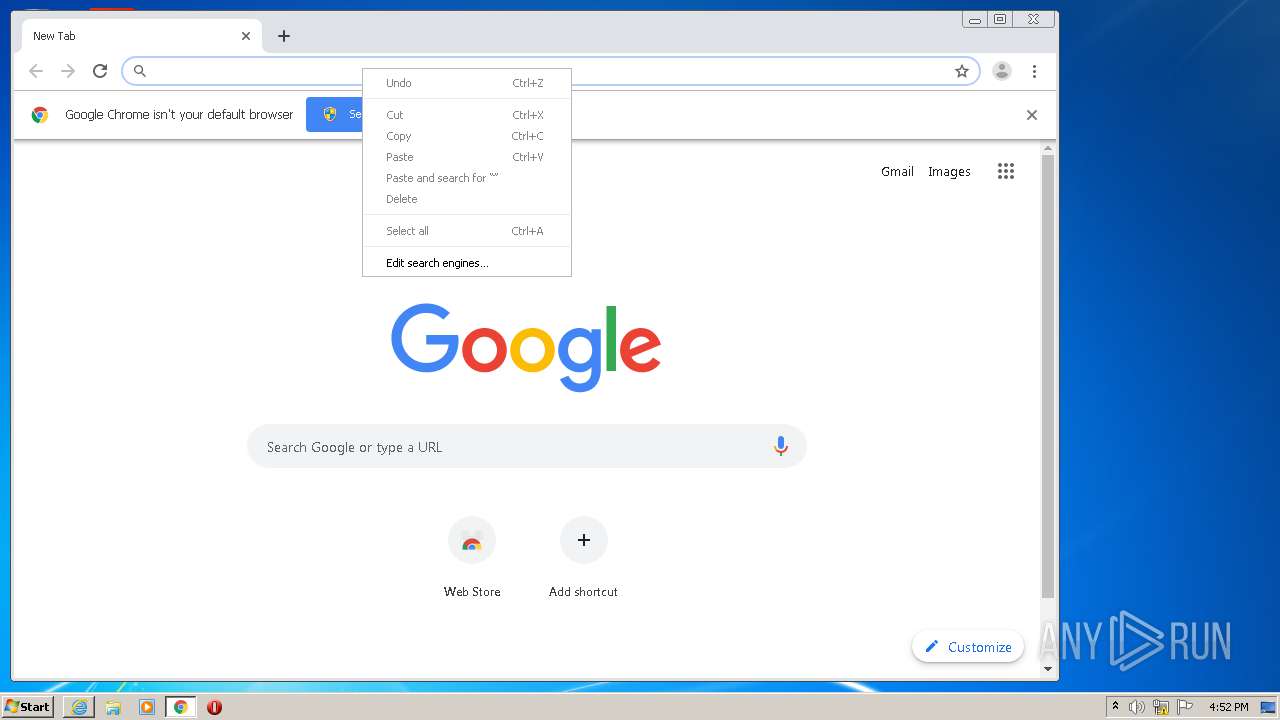
Manual execution by user
- chrome.exe (PID: 3028)
Changes settings of System certificates
- iexplore.exe (PID: 1876)
Reads the hosts file
- chrome.exe (PID: 3028)
- chrome.exe (PID: 4020)
Reads settings of System Certificates
- iexplore.exe (PID: 1876)
- chrome.exe (PID: 4020)
- DiskGenius.exe (PID: 2604)
- iexplore.exe (PID: 2732)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1876)
Application was dropped or rewritten from another process
- DGEngSetup5301066.tmp (PID: 2420)
- DGEngSetup5301066.tmp (PID: 3620)
Reads internet explorer settings
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 3048)
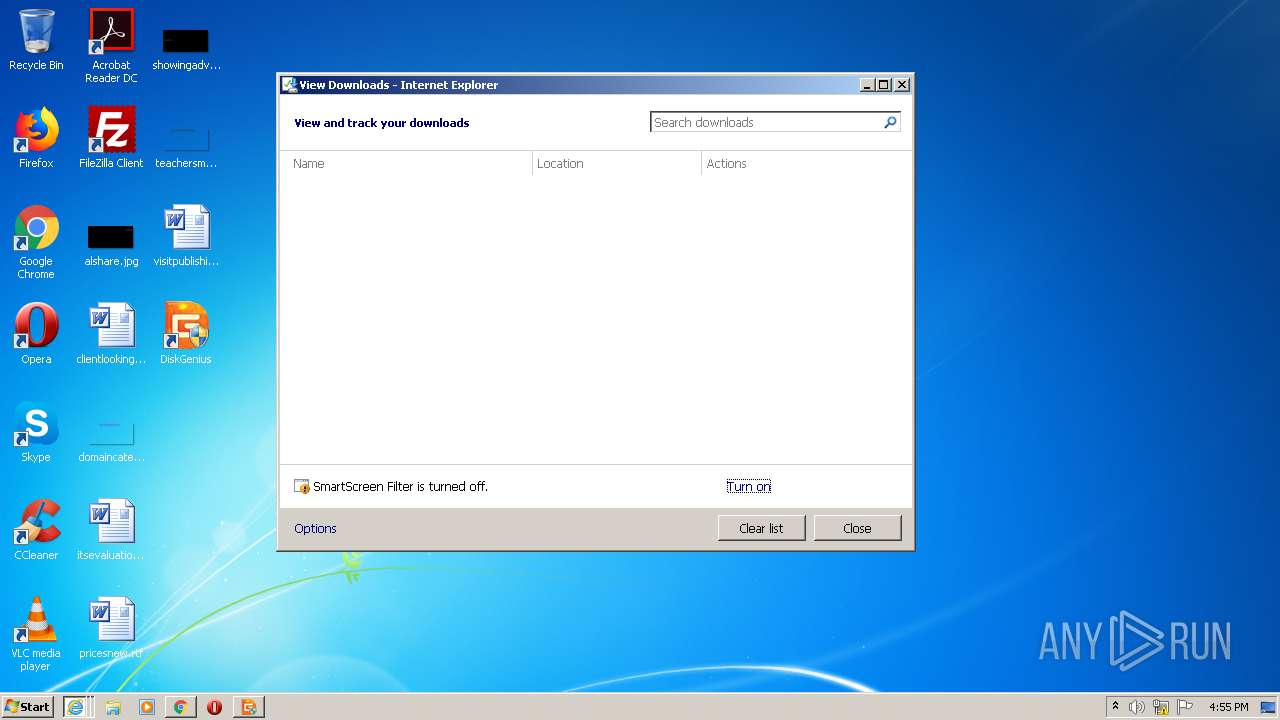
Creates a software uninstall entry
- DGEngSetup5301066.tmp (PID: 3620)
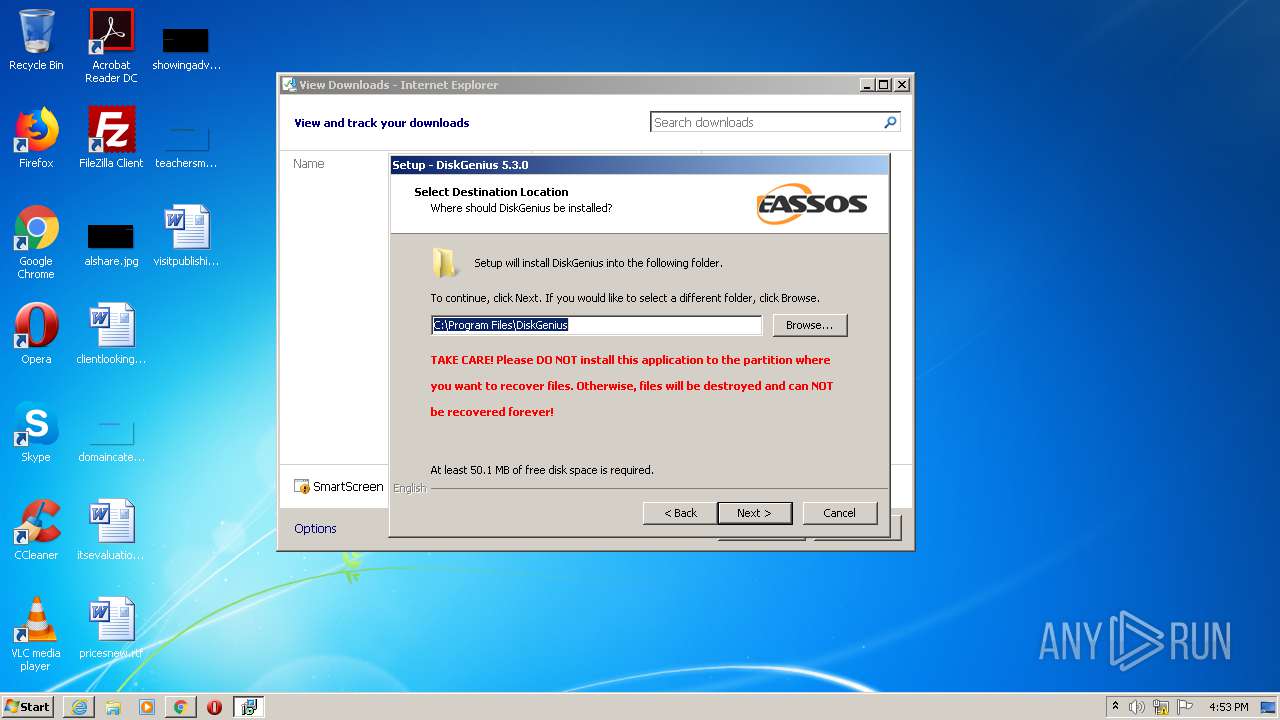
Creates files in the program directory
- DGEngSetup5301066.tmp (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
25
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11671398288873248257,1336973575872455861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7786441056793505696 --mojo-platform-channel-handle=3656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,11671398288873248257,1336973575872455861,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13019186730027441789 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ea5a9d0,0x6ea5a9e0,0x6ea5a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DGEngSetup5301066.exe" /SPAWNWND=$2019E /NOTIFYWND=$3019C | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DGEngSetup5301066.exe | DGEngSetup5301066.tmp | ||||||||||||
User: admin Company: Eassos Co., Ltd. Integrity Level: HIGH Description: DiskGenius Setup Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11671398288873248257,1336973575872455861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4514501544233699130 --mojo-platform-channel-handle=3048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
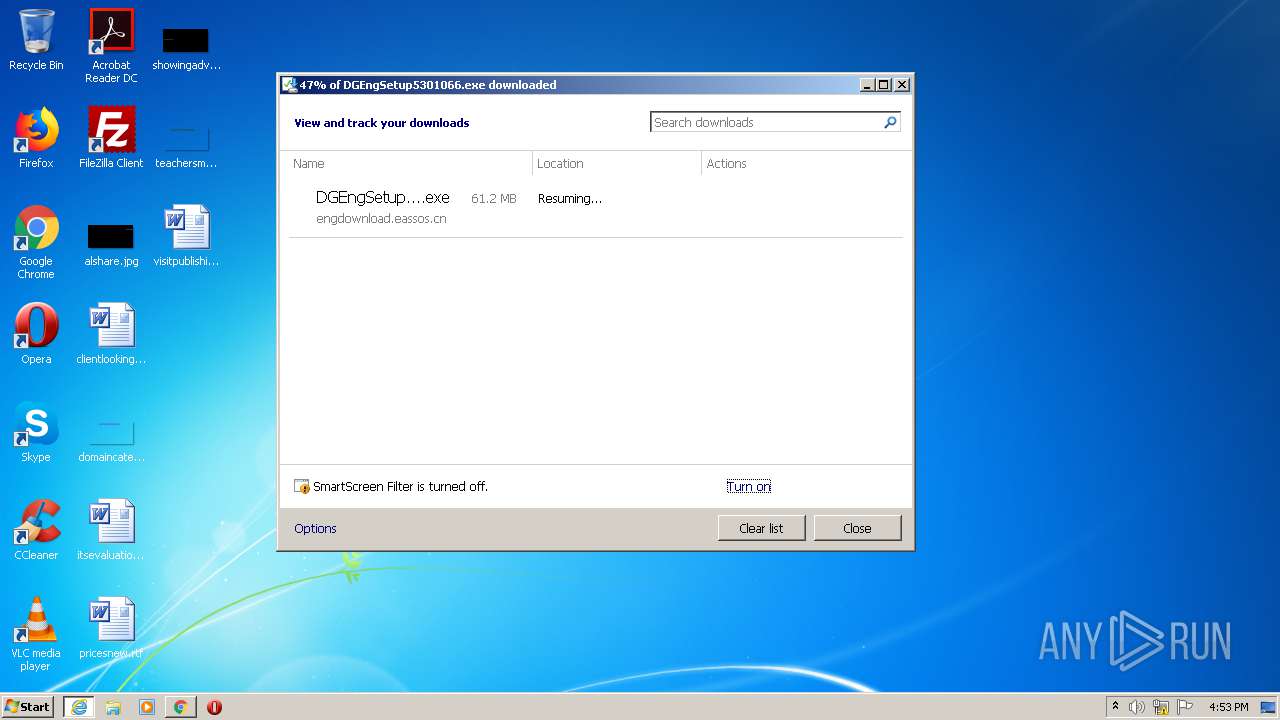
| 1876 | "C:\Program Files\Internet Explorer\iexplore.exe" http://engdownload.eassos.cn/DGEngSetup5301066.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11671398288873248257,1336973575872455861,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9610930589699470898 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\is-2FG28.tmp\DGEngSetup5301066.tmp" /SL5="$3019C,63392047,780800,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DGEngSetup5301066.exe" | C:\Users\admin\AppData\Local\Temp\is-2FG28.tmp\DGEngSetup5301066.tmp | — | DGEngSetup5301066.exe | |||||||||||
User: admin Company: Eassos Co., Ltd. Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
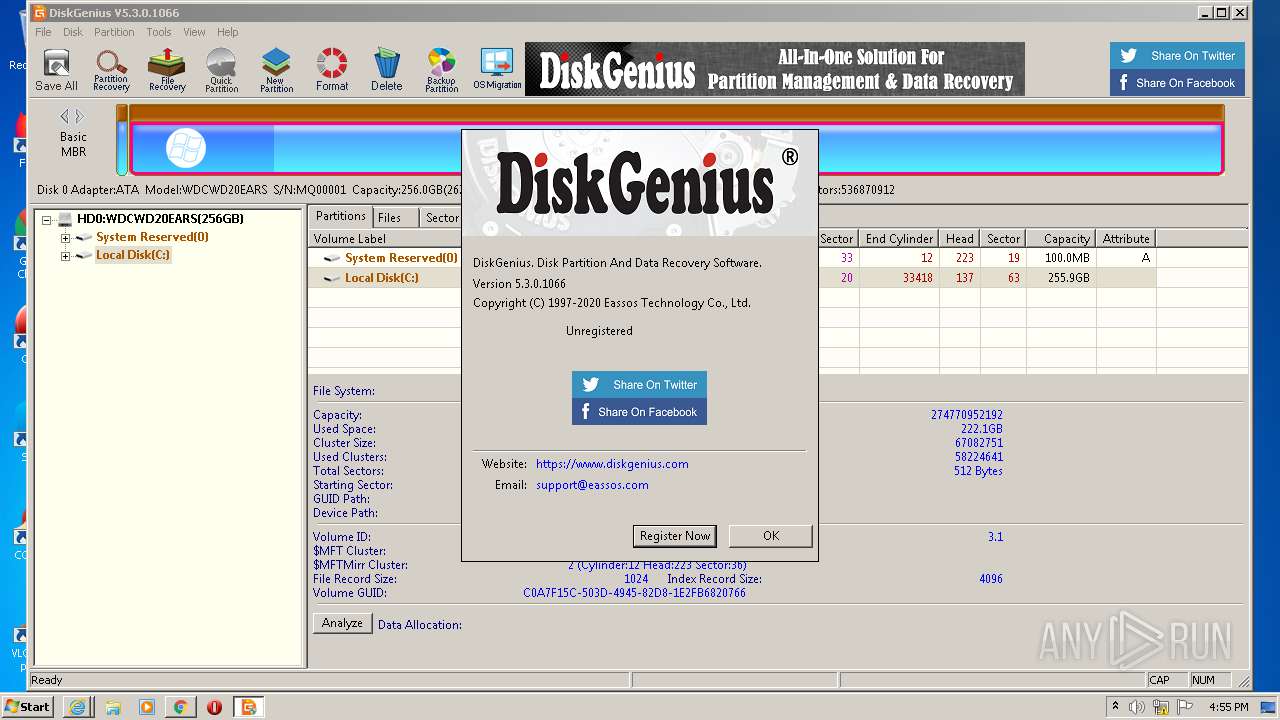
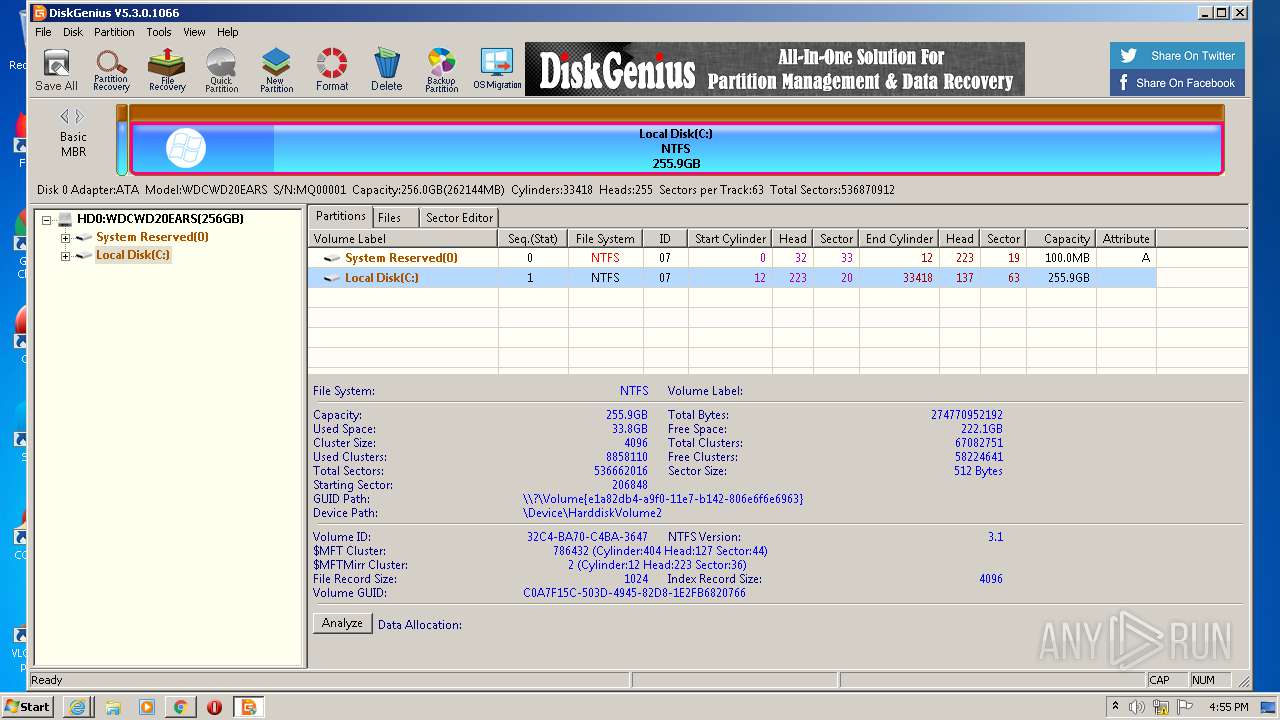
| 2604 | "C:\Program Files\DiskGenius\DiskGenius.exe" | C:\Program Files\DiskGenius\DiskGenius.exe | DGEngSetup5301066.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: DiskGenius Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 938
Read events
2 666
Write events
258
Delete events
14
Modification events
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3166148194 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30831186 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
29
Suspicious files
55
Text files
98
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
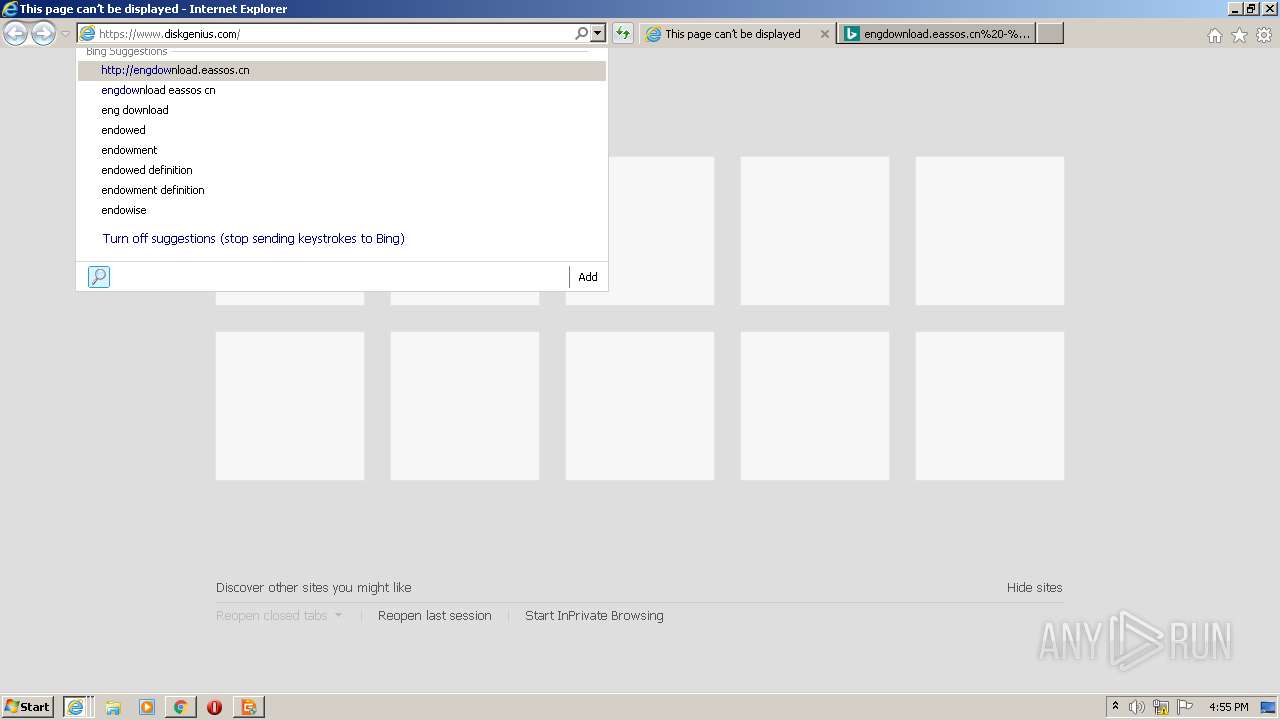
| 2732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\DGEngSetup5301066[1].exe | — | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD599.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD59A.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verD5CA.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0EN74OK5.txt | — | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ZL14I607.txt | — | |
MD5:— | SHA256:— | |||
| 2732 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BSROS03Q.txt | text | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 1876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | der | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
58
DNS requests
38
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
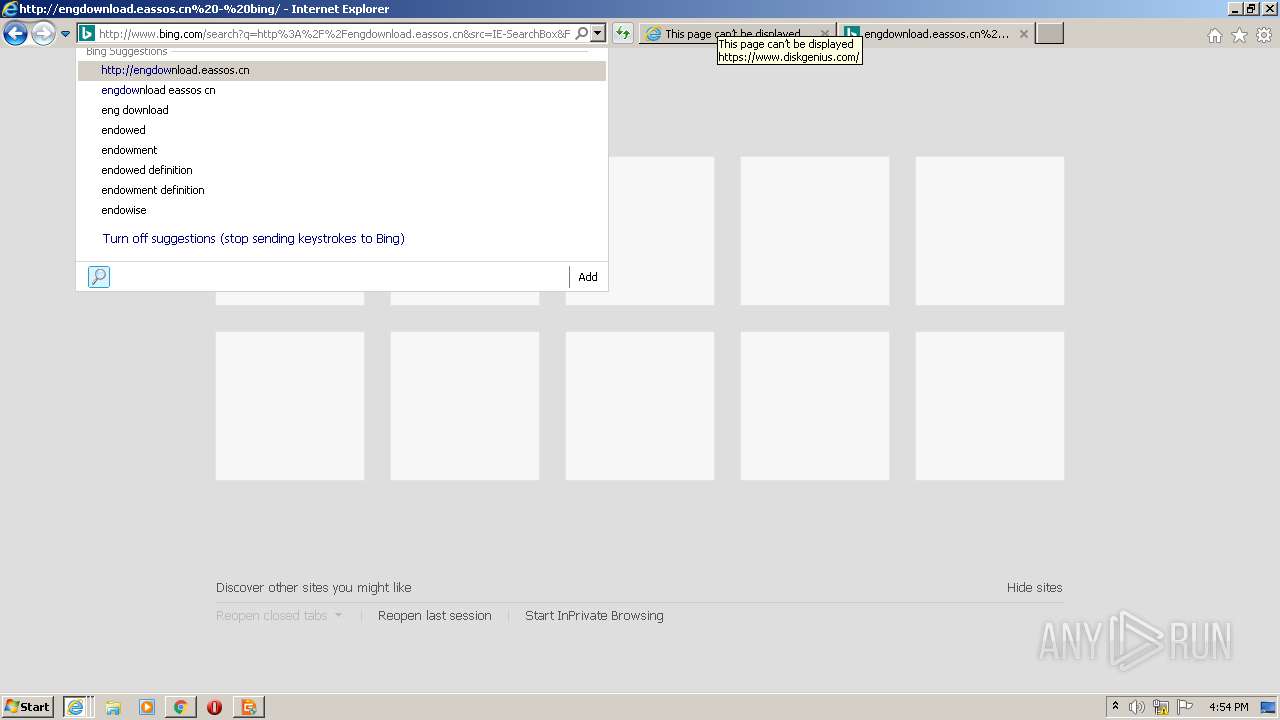
2732 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2732 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=htt&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.42 Kb | whitelisted |
1876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.42 Kb | whitelisted |
2604 | DiskGenius.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSXi0cW5bD2WLrmnasWibg2OuPDpgQUVXRPsnJP9WC6UNHX5lFcmgGHGtcCEAZ%2FKbrbi6QaIUlSniK2x%2BI%3D | US | der | 471 b | whitelisted |
2604 | DiskGenius.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSXi0cW5bD2WLrmnasWibg2OuPDpgQUVXRPsnJP9WC6UNHX5lFcmgGHGtcCEAaEI4YpBn9FGyG7EL50P%2B4%3D | US | der | 471 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2732 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | US | der | 471 b | whitelisted |
2732 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 251 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1876 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1876 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1876 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4020 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.21.238:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
4020 | chrome.exe | 216.58.212.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2732 | iexplore.exe | 162.159.237.122:80 | engdownload.eassos.cn | Cloudflare Inc | — | suspicious |
4020 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.18.3:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
engdownload.eassos.cn |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2732 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |