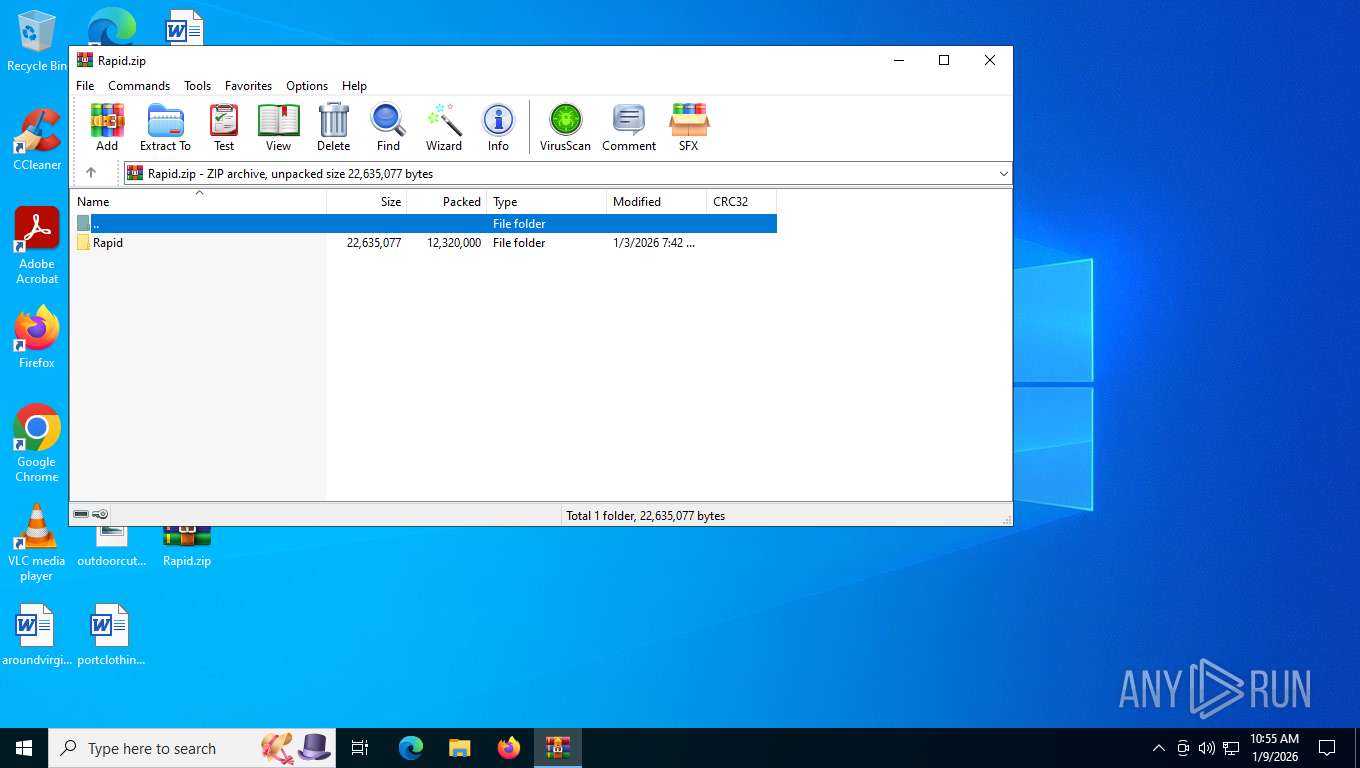
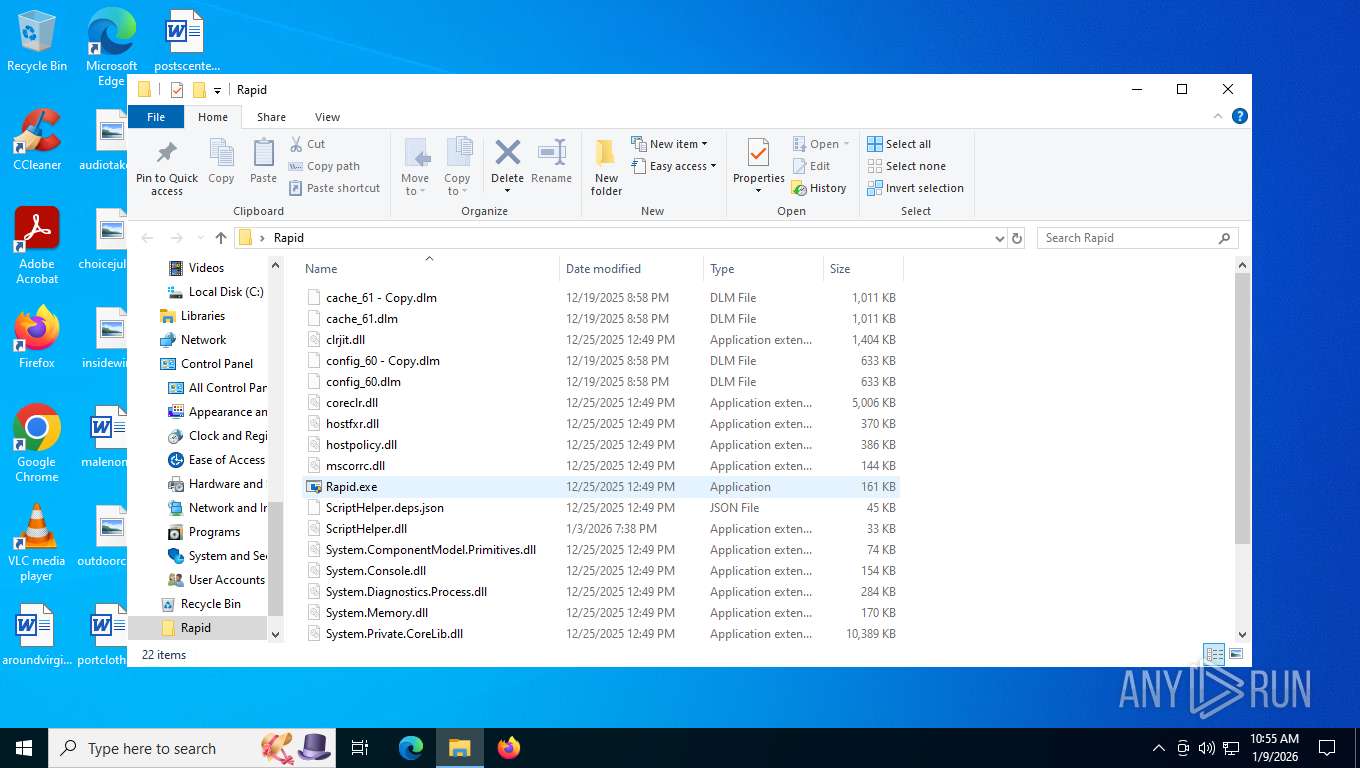
| File name: | Rapid.zip |
| Full analysis: | https://app.any.run/tasks/ecd6c03a-4b12-45b3-a78d-21fff5e4c278 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2026, 15:54:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 9D3D834480CDC4AE28B5686D09DAA2A9 |
| SHA1: | 6FF378CDD03C18EA5FEB42D52A5B307087745436 |
| SHA256: | 5789B5D74F1578F7BE74E6DDE1ECAF636C3A4F012906A071F120A0B9136008E7 |
| SSDEEP: | 98304:Yh5hwPj6AqBsR/3C7MPcHItedcVlkKw9qbubUNeLJP8Q4ldqD/Yocf/QfR+j48QW:VcYkfK1p1XSvSuPWfJgdaQod/P |
MALICIOUS
Adds path to the Windows Defender exclusion list
- Rapid.exe (PID: 8068)
Changes Windows Defender settings
- Rapid.exe (PID: 8068)
Run PowerShell with an invisible window
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8172)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 8172)
SUSPICIOUS
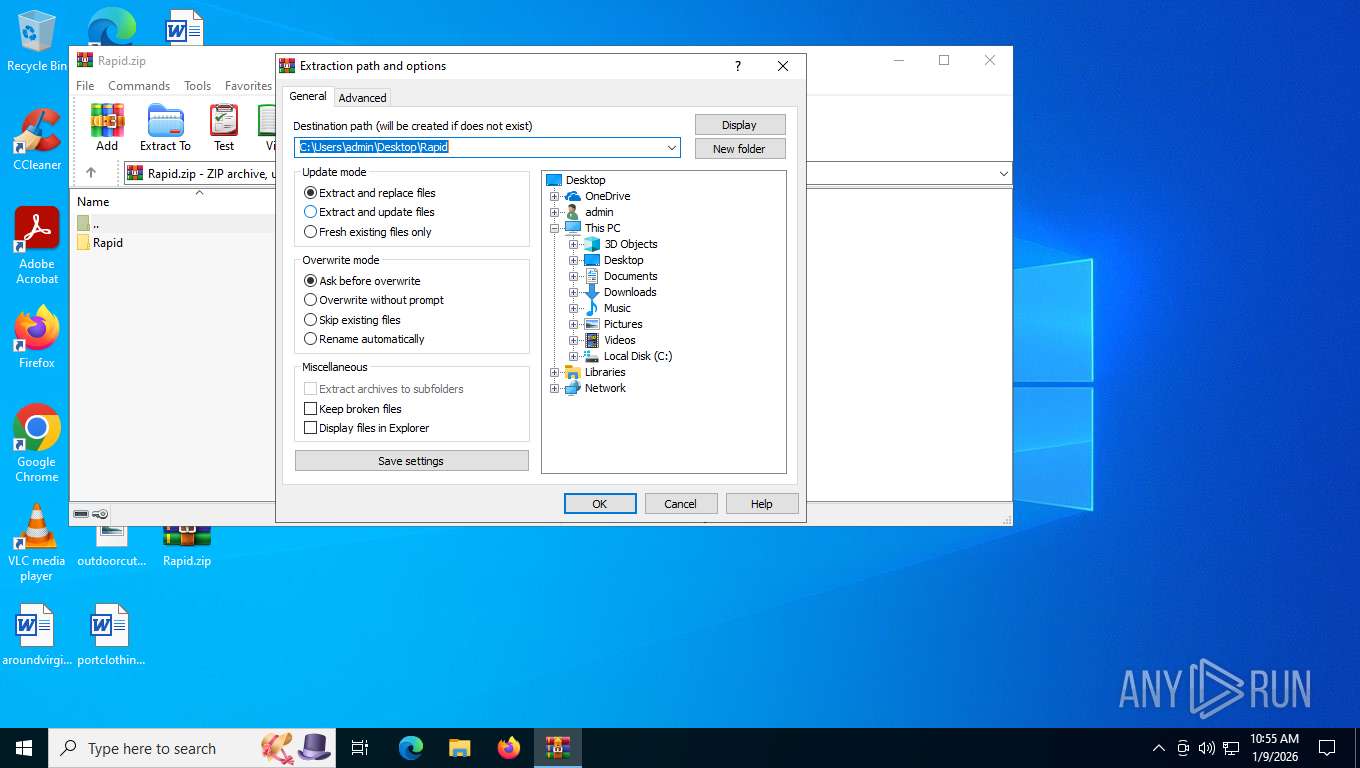
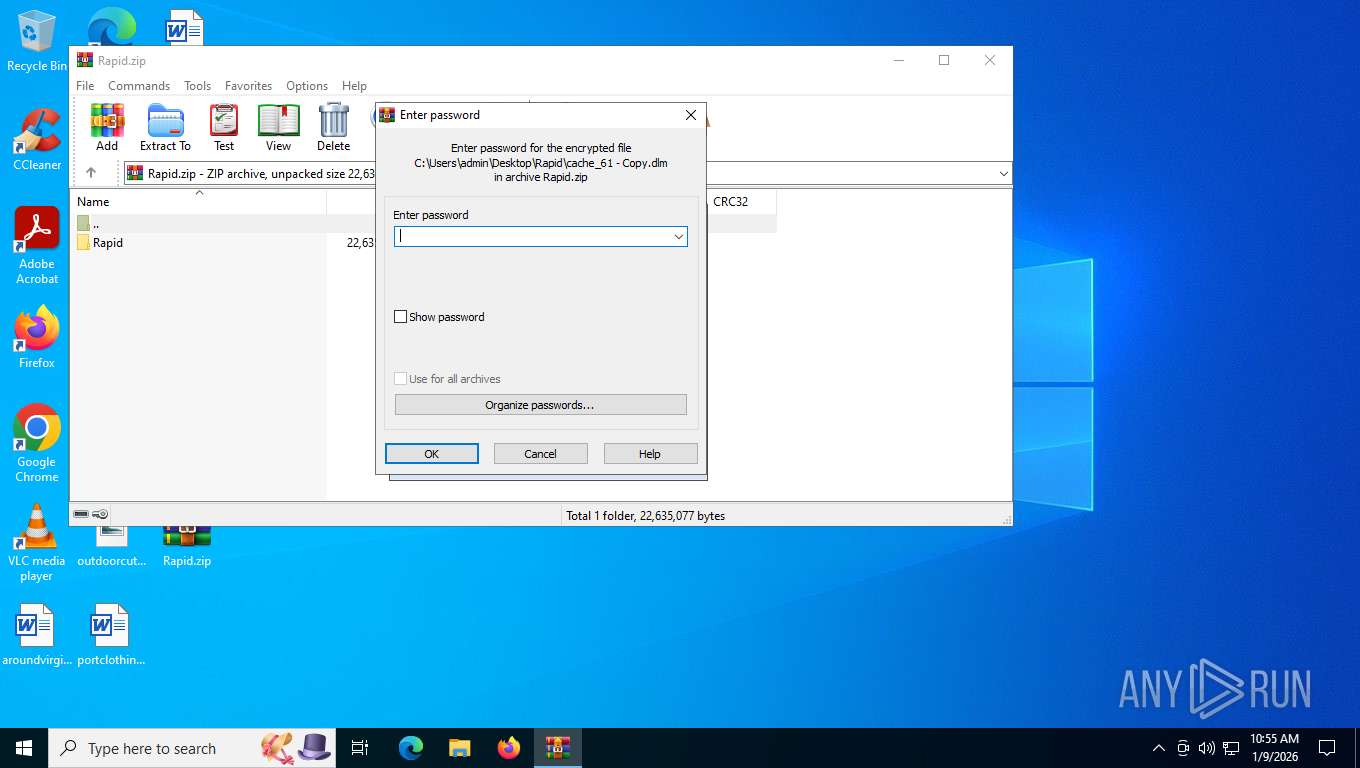
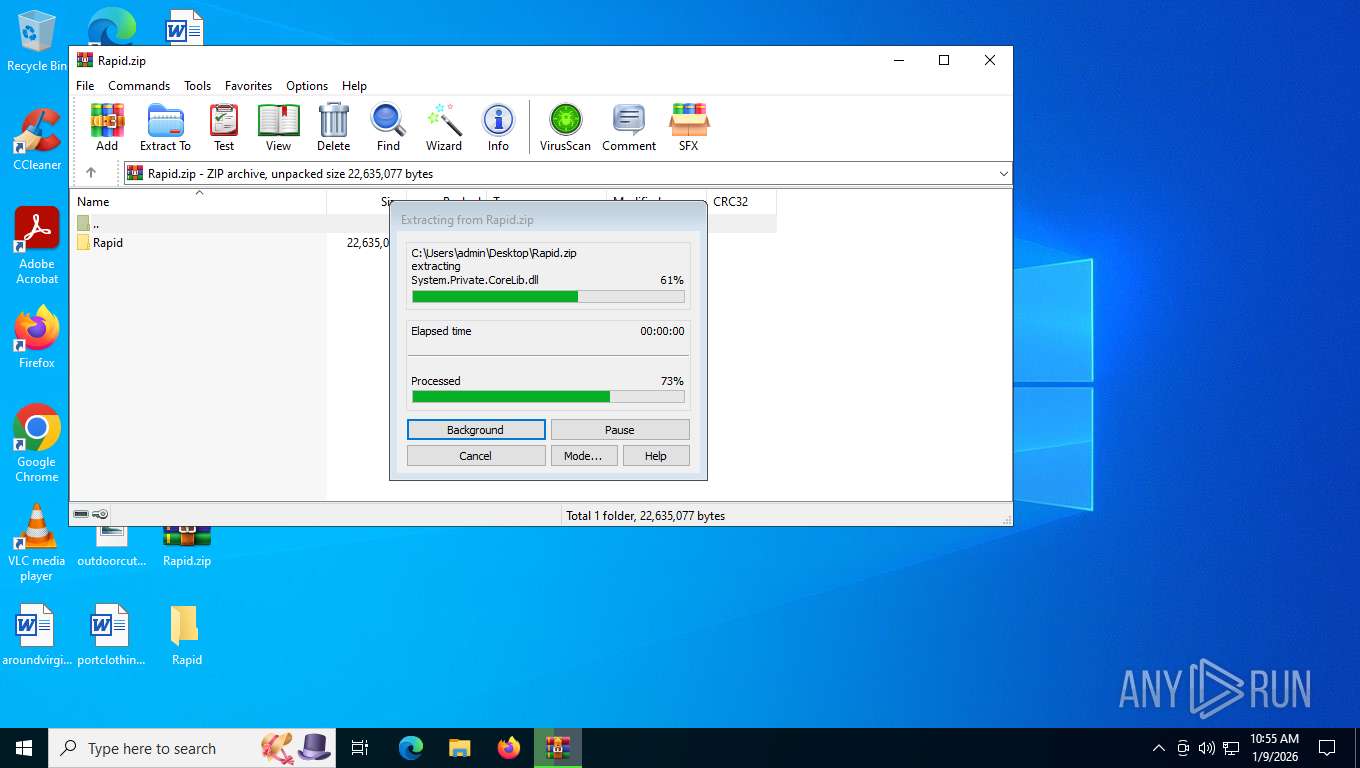
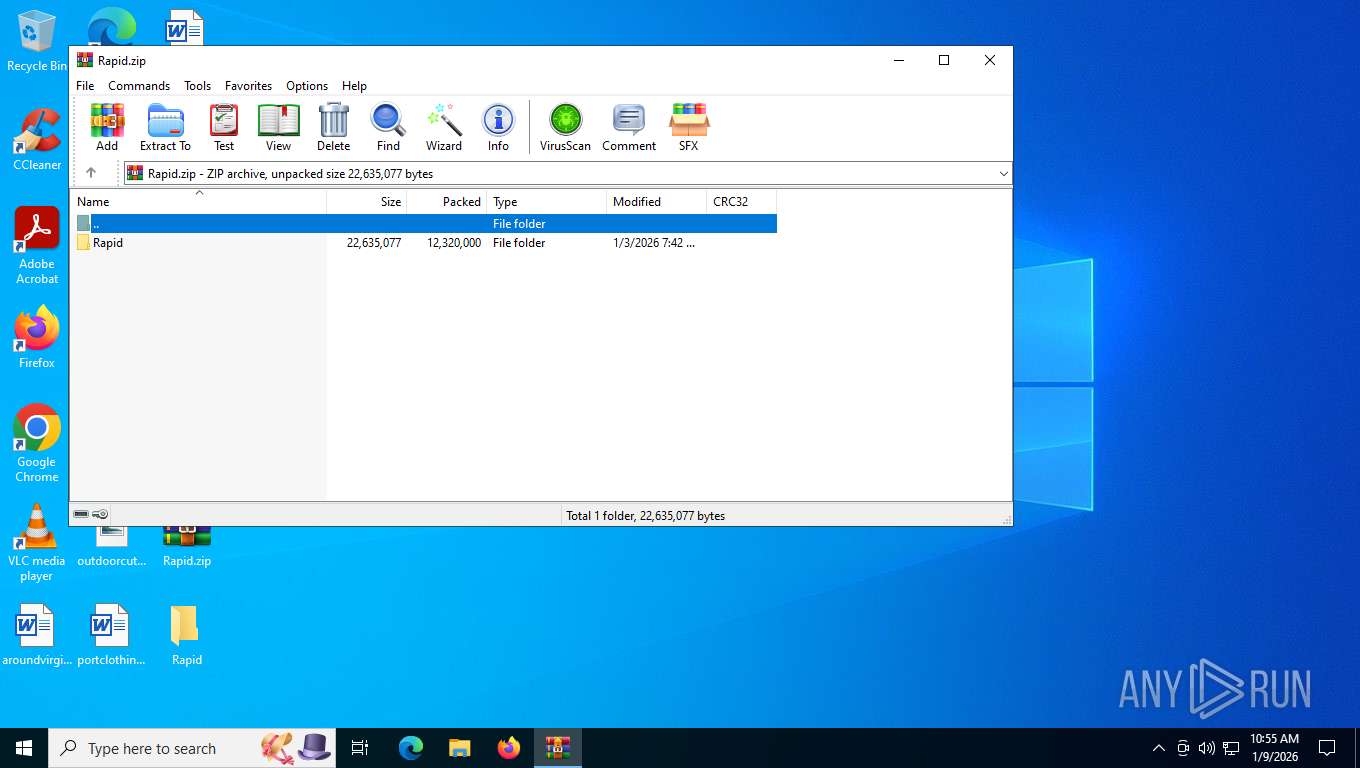
Process drops legitimate windows executable
- WinRAR.exe (PID: 7632)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7632)
The process bypasses the loading of PowerShell profile settings
- Rapid.exe (PID: 8068)
Script adds exclusion path to Windows Defender
- Rapid.exe (PID: 8068)
Starts POWERSHELL.EXE for commands execution
- Rapid.exe (PID: 8068)
Possibly malicious use of IEX has been detected
- Rapid.exe (PID: 8068)
Reads security settings of Internet Explorer
- Rapid.exe (PID: 8068)
Found IP address in command line
- powershell.exe (PID: 8172)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 8172)
Write to the desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 7632)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7632)
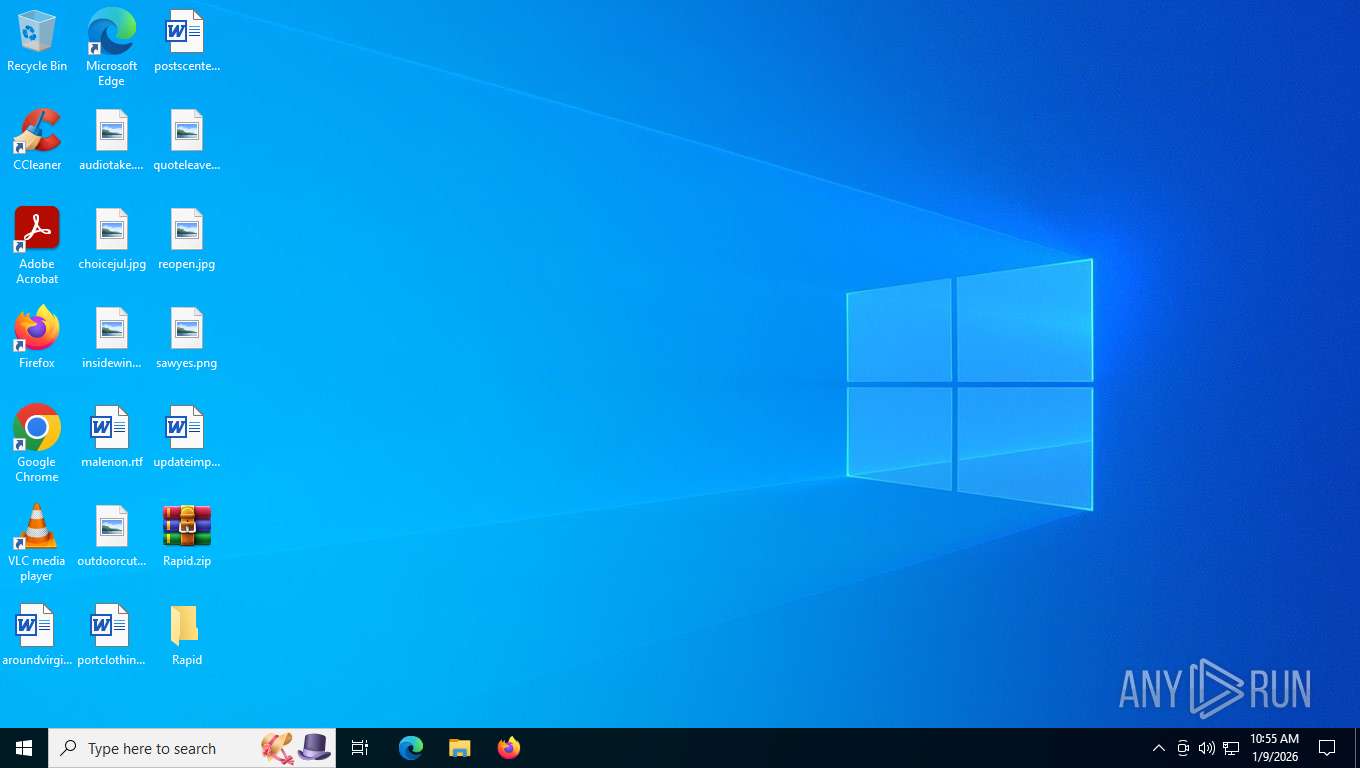
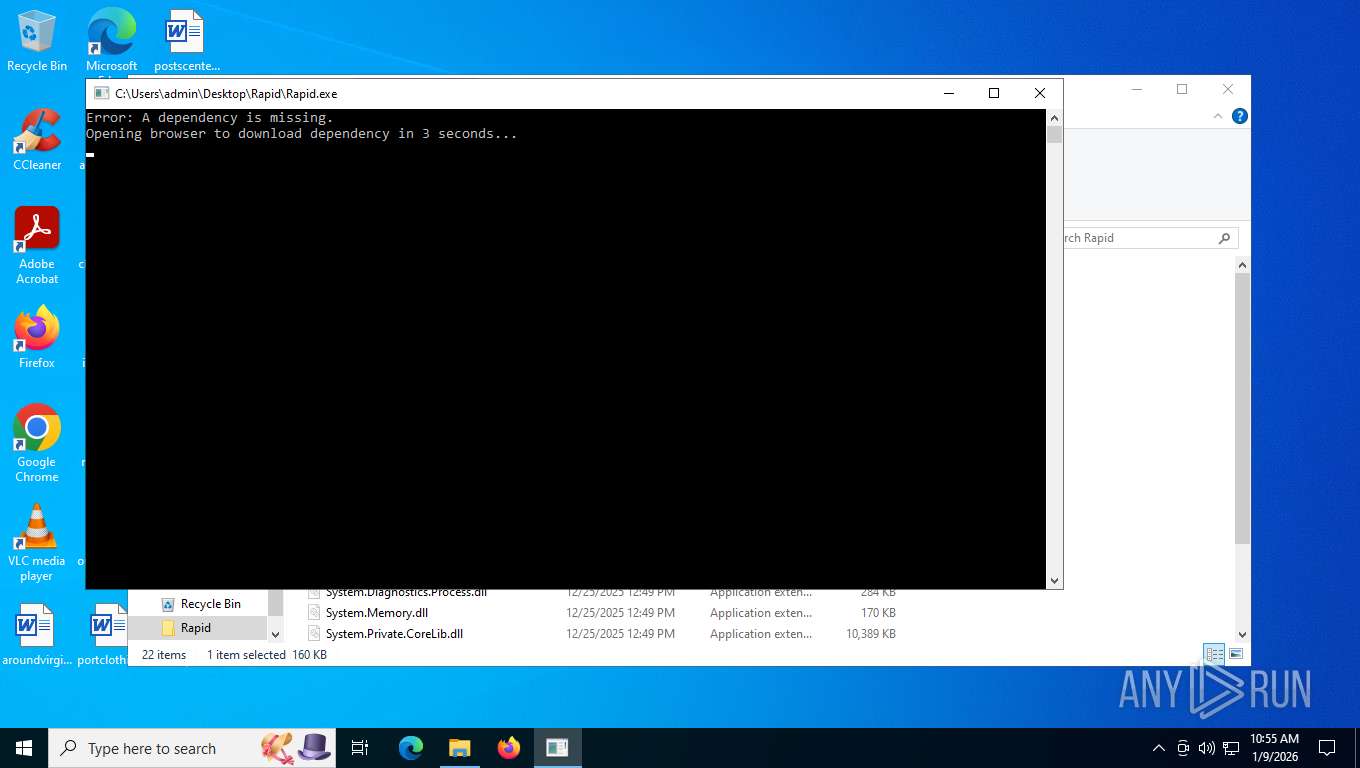
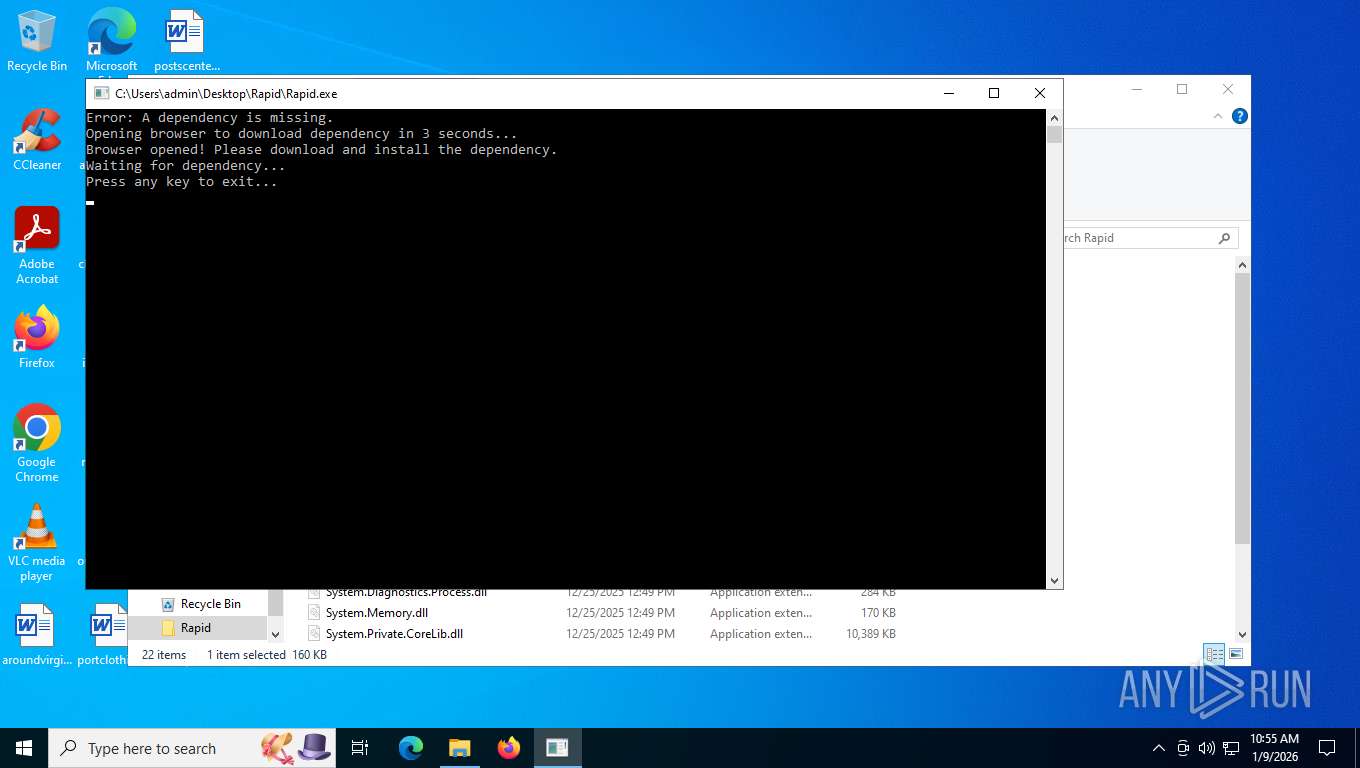
Manual execution by a user
- Rapid.exe (PID: 8068)
- Rapid.exe (PID: 8016)
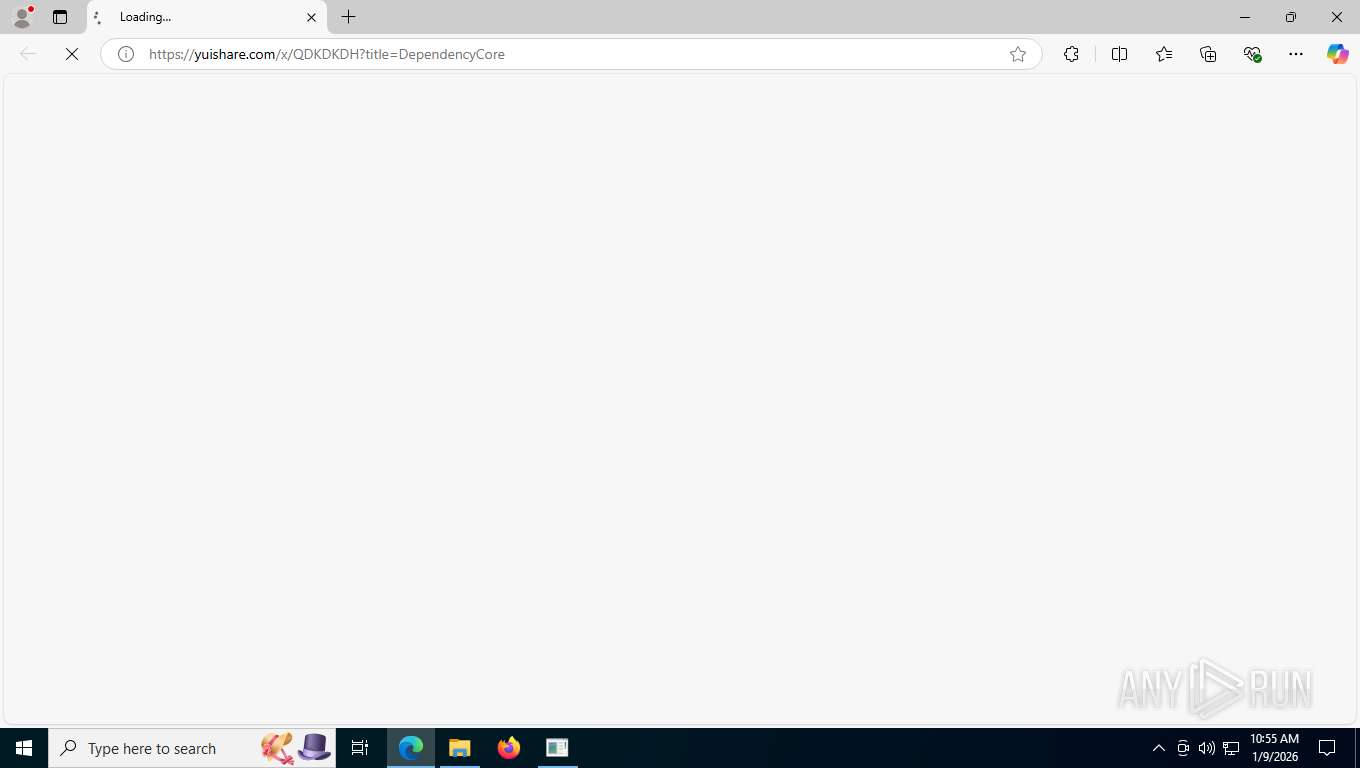
- msedge.exe (PID: 2308)
Checks supported languages
- Rapid.exe (PID: 8068)
Creates files in the program directory
- Rapid.exe (PID: 8068)
Disables trace logs
- powershell.exe (PID: 8172)
Checks proxy server information
- powershell.exe (PID: 8172)
- slui.exe (PID: 7336)
Reads the computer name
- Rapid.exe (PID: 8068)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 8172)
Application launched itself
- msedge.exe (PID: 7280)
- msedge.exe (PID: 2308)
- msedge.exe (PID: 7180)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8172)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8156)
The sample compiled with english language support
- WinRAR.exe (PID: 7632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2026:01:03 19:42:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Rapid/ |
Total processes
171
Monitored processes
24
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1784 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2128,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=2632 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1924,i,5036821694949307682,8127392468487329196,262144 --variations-seed-version --mojo-platform-channel-handle=2428 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument https://yuishare.com/x/QDKDKDH?title=DependencyCore | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2572,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=2568 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=3616,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=5212 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2752 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2312,i,5036821694949307682,8127392468487329196,262144 --variations-seed-version --mojo-platform-channel-handle=2292 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2648,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4224,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=4272 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3592,i,7202526468706888285,1401590896556885036,262144 --variations-seed-version --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
17 376
Read events
17 337
Write events
26
Delete events
13
Modification events
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Rapid.zip | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7632) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
19
Suspicious files
43
Text files
69
Unknown types
0
Dropped files
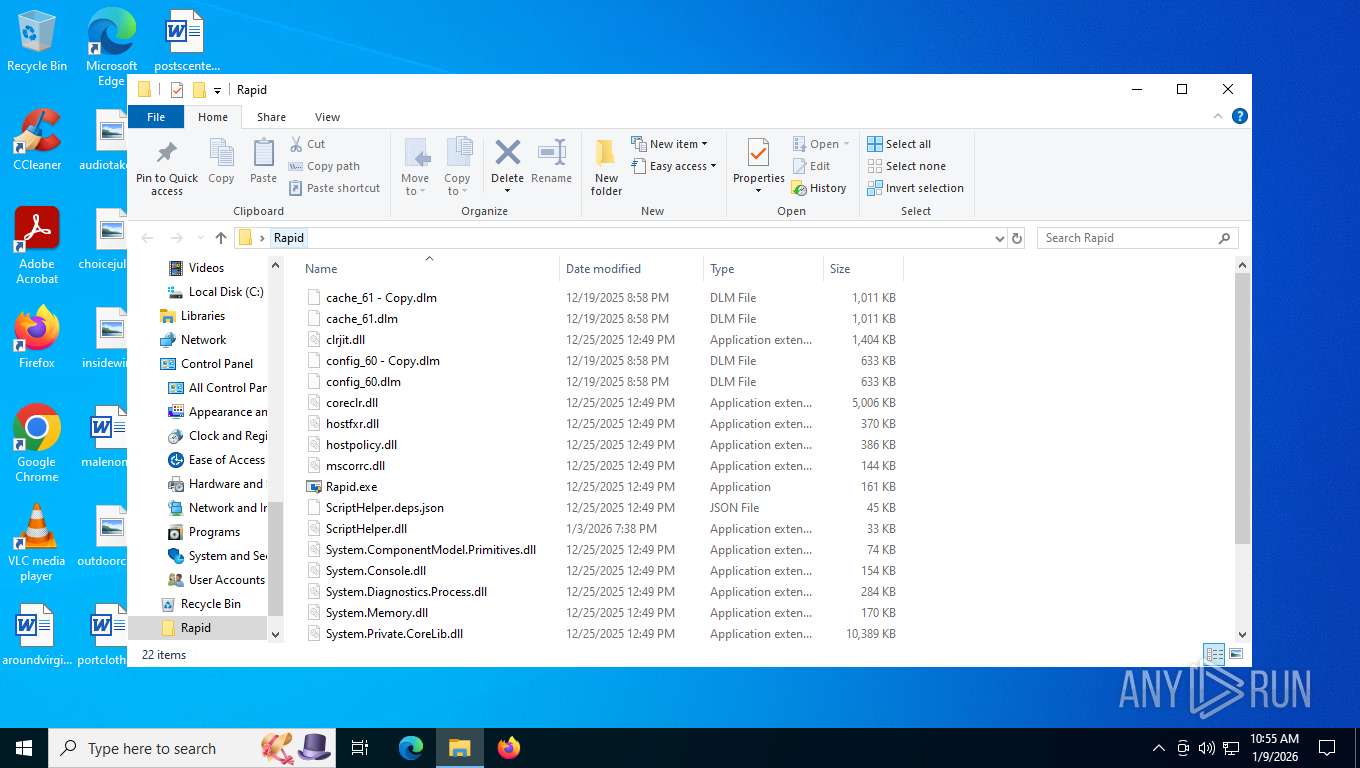
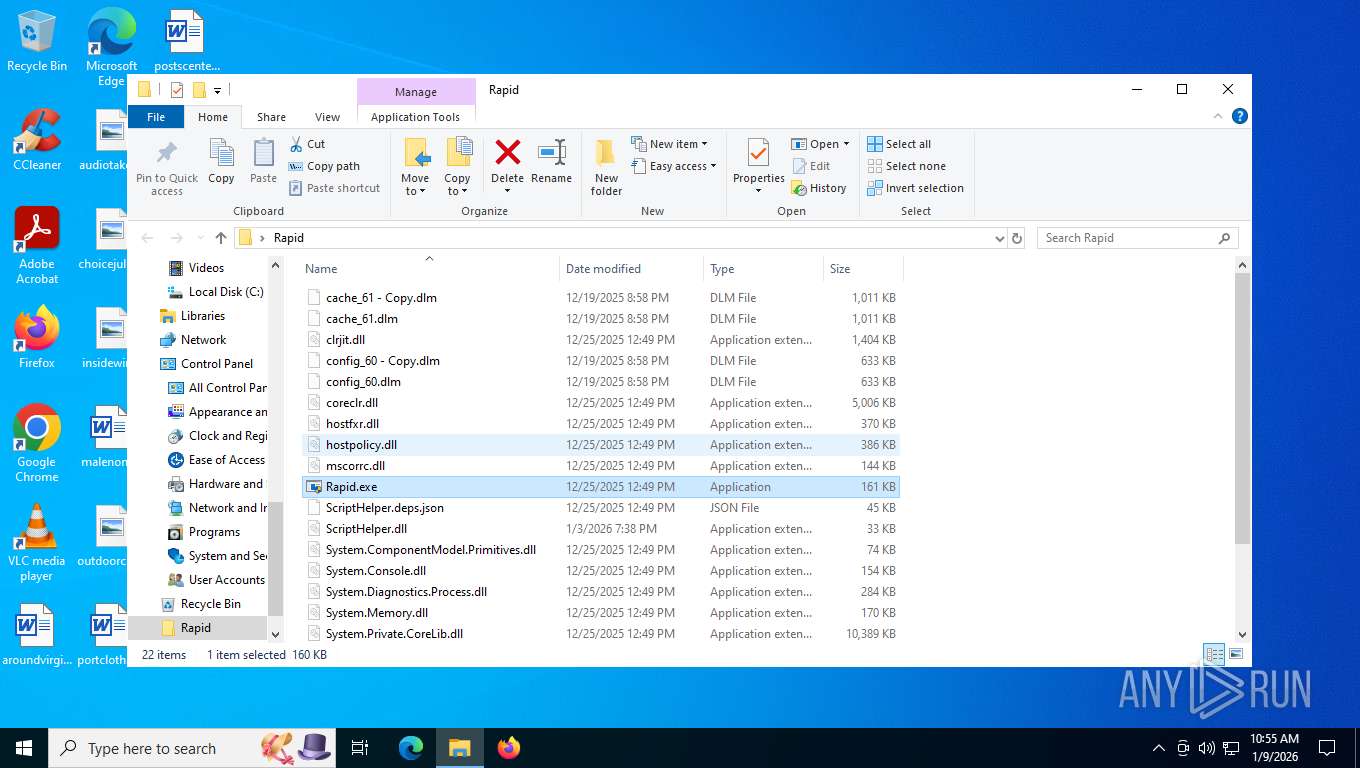
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\clrjit.dll | executable | |
MD5:C83270C072E51D37928AB8D4D42BE464 | SHA256:CC9C853642C185B17D18F189C5E80928963BF485B0EEEF7714E94339C5858E88 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\coreclr.dll | executable | |
MD5:6F84D00E152BC64261AC7A0F6D4DC3F5 | SHA256:58D91F3C88293AC3B9761362C53AF32520CA42F8BE14244C0BD7A8E6D1C95564 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\config_60 - Copy.dlm | binary | |
MD5:9D28E8BA0538565BE1E966C65DF16B05 | SHA256:55EE80F78E0D60DD6D625534F971DA2671CA9B6F1CC91B162860E41A5728B6D2 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\cache_61.dlm | binary | |
MD5:6A2492D361BB6AE4FF2162ABB12EF119 | SHA256:B9AD41F738E55EB73F0F2898B920BB62B2F66625899EFD9C11B57D2A853167BC | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\ScriptHelper.deps.json | text | |
MD5:39F226BF8E421C0EF3F80AA896ED2A52 | SHA256:6CED04AFD565960CC447F48149D4B07761109997995E5B377A5D8D052A783A8D | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\desktop.ini | text | |
MD5:9A12C8D20625FD6FE7F972AE54A6C094 | SHA256:580820459AC9464C1865F007658F1F7DE32C1D9414391597F74469E7FC92A1BD | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\hostfxr.dll | executable | |
MD5:155E4D45F02A4F7A2A228B44FA4791EF | SHA256:E2486FC6DD58DB5A55DB18547459C0B160BA1B2E824193AE0DEE0E9A0673D8D7 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\ScriptHelper.dll | executable | |
MD5:47520C7C435E5799488D7EB3CE1B97E9 | SHA256:8CC0DDE7D151A7634B62C2B0BDB06BBD71011D9BD2F8F21D6D1BEBC2972E2D31 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\System.ComponentModel.Primitives.dll | executable | |
MD5:C735BD356E654447D20B566D06E9EB40 | SHA256:96789FBDE342BE57152E83B20E833BCC33F12CF30A7B5C9C0790990CF5886D48 | |||
| 7632 | WinRAR.exe | C:\Users\admin\Desktop\Rapid\mscorrc.dll | executable | |
MD5:5F50C1CF588DD6F882FF5A329390FCD4 | SHA256:A231D44280D7044FDA539B85288FBBADABA4830DA421F0F28FD0444A05C2F107 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
44
DNS requests
40
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
32 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
32 | svchost.exe | POST | 200 | 20.190.159.130:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
32 | svchost.exe | POST | 200 | 20.190.159.130:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
4476 | svchost.exe | GET | 200 | 23.212.193.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4476 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
32 | svchost.exe | POST | 200 | 20.190.159.130:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
8172 | powershell.exe | GET | 200 | 46.151.182.233:80 | http://46.151.182.233/update | unknown | — | — | unknown |
4476 | svchost.exe | GET | 200 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 5.48 Kb | whitelisted |
1784 | msedge.exe | GET | — | 188.114.96.3:443 | https://installxcheck.com/templates/file/theme3.php?id=0&title=dependencycore&instructions=To%20continue%20the%20download%20of%20the%20dependencycore%20-%20complete%20the%20offer%20below&button_start_text=Start%20Download&button_end_text=&option_int1=&conversions_required=1&auto_unlock_timer=0&custom= | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4476 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1784 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
32 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
32 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4476 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4476 | svchost.exe | 23.212.193.218:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
yuishare.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8172 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 7 |
8172 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1784 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
8172 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
Process | Message |
|---|---|
Rapid.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 8068. Message ID: [0x2509].
|