| File name: | dq.exe |
| Full analysis: | https://app.any.run/tasks/23c2f180-e2c5-42f1-b1c2-c2dc9adc9a59 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 22:03:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 9058772629F6D76B88E27A2B4AB7350C |
| SHA1: | DCB78B69B05C96B0B621884BE2E64FE093B23A4C |
| SHA256: | 57856F0EC7026F7C9EF854F6778A665EAF812D5D1FBE78D908A7327FA368D62C |
| SSDEEP: | 24576:gbaBr/DduQqmzhFfvRUKd/k6Ub1G8hzKP//GA3V3:TBrZkYZoRG8VKP//z3V3 |
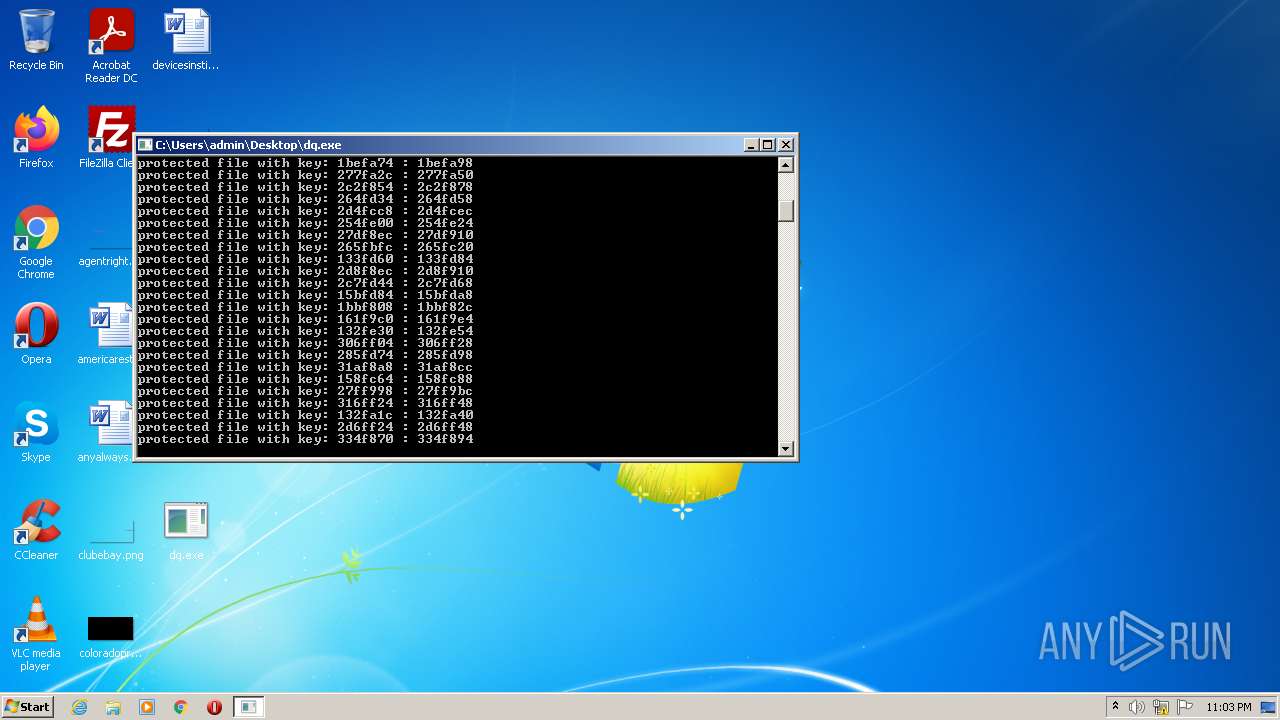
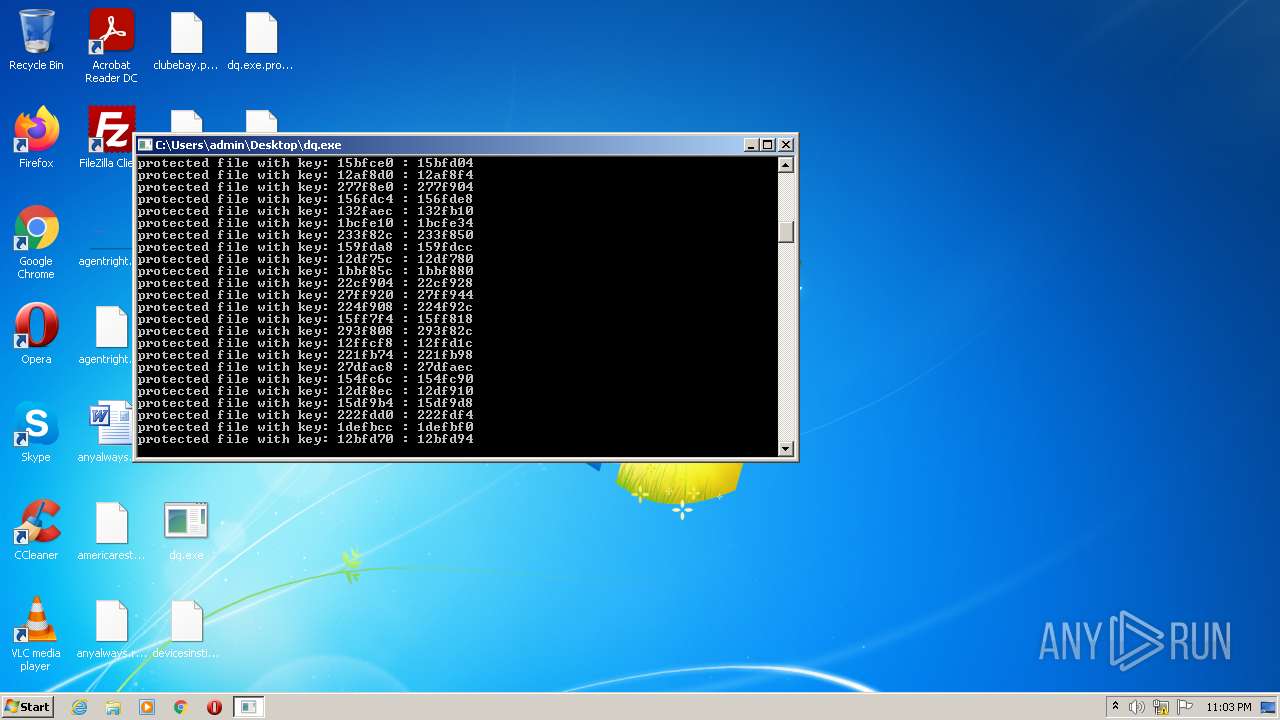
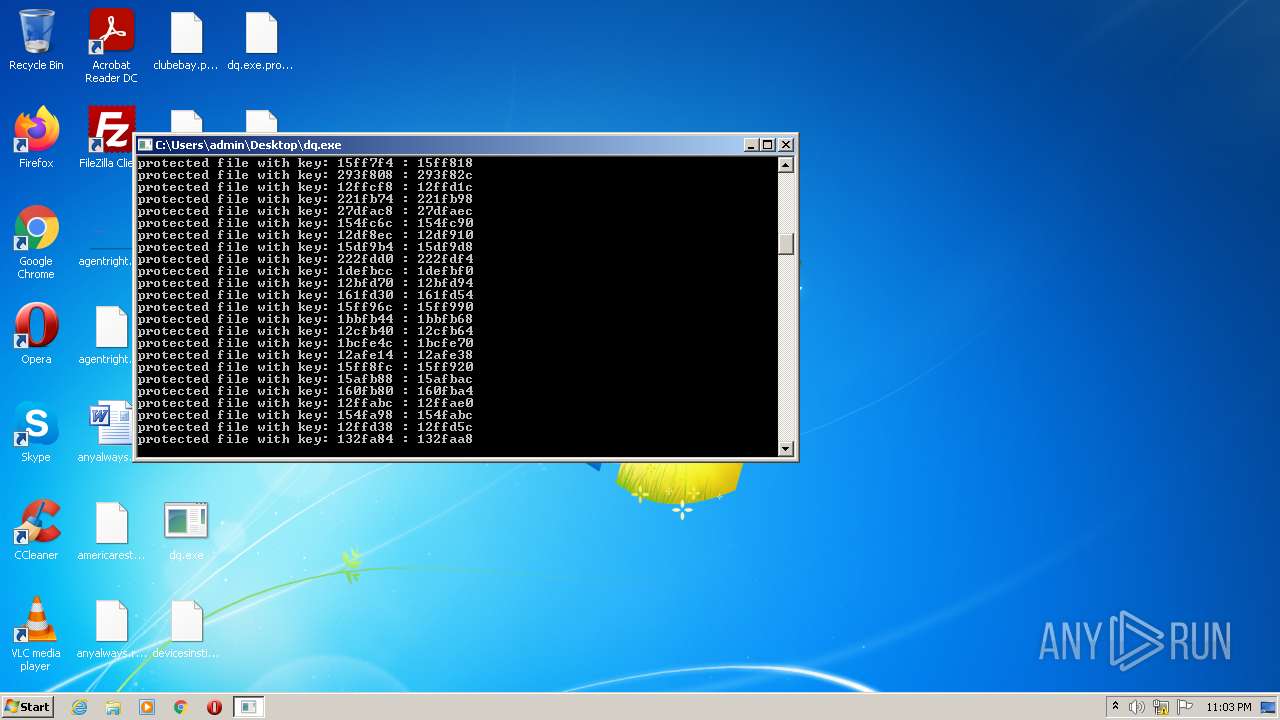
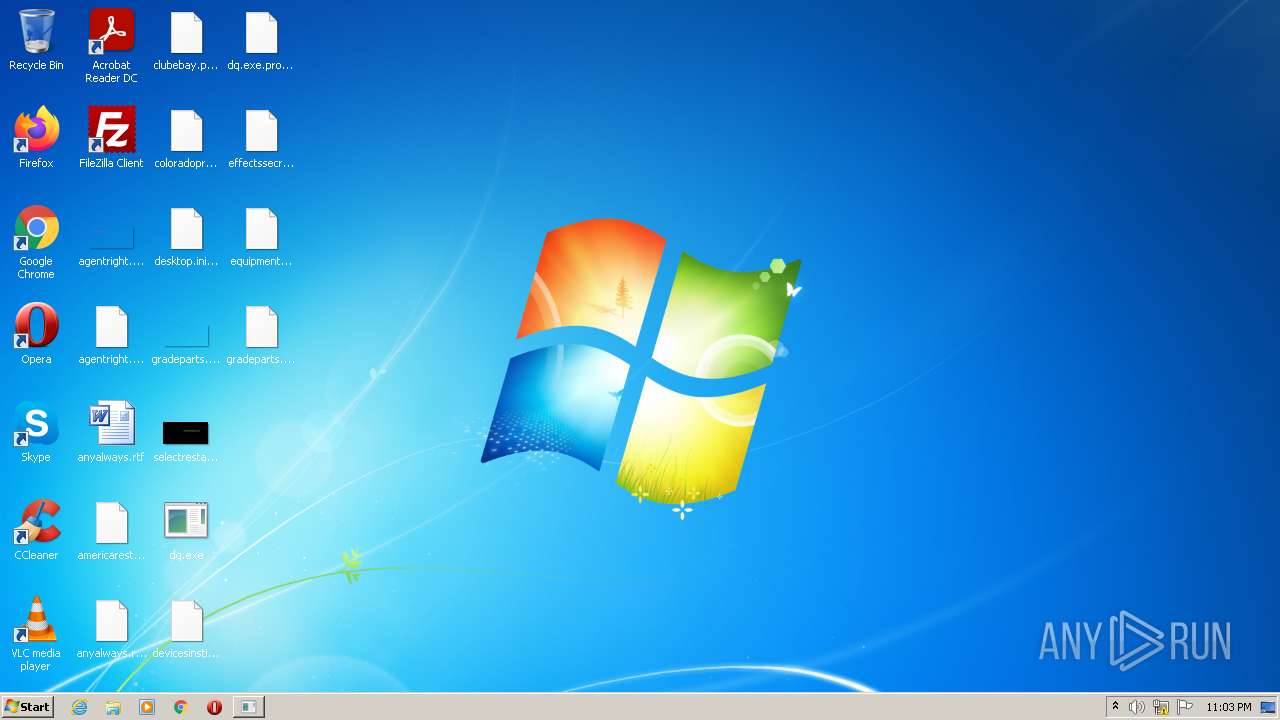
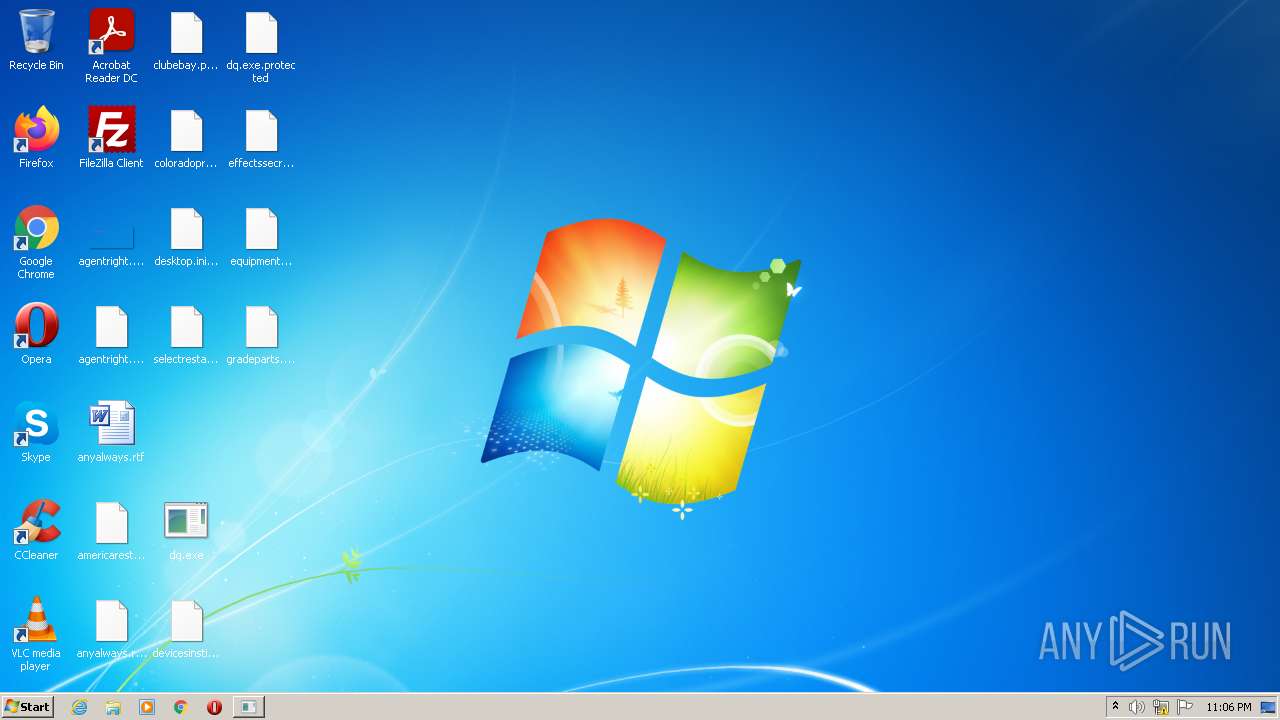
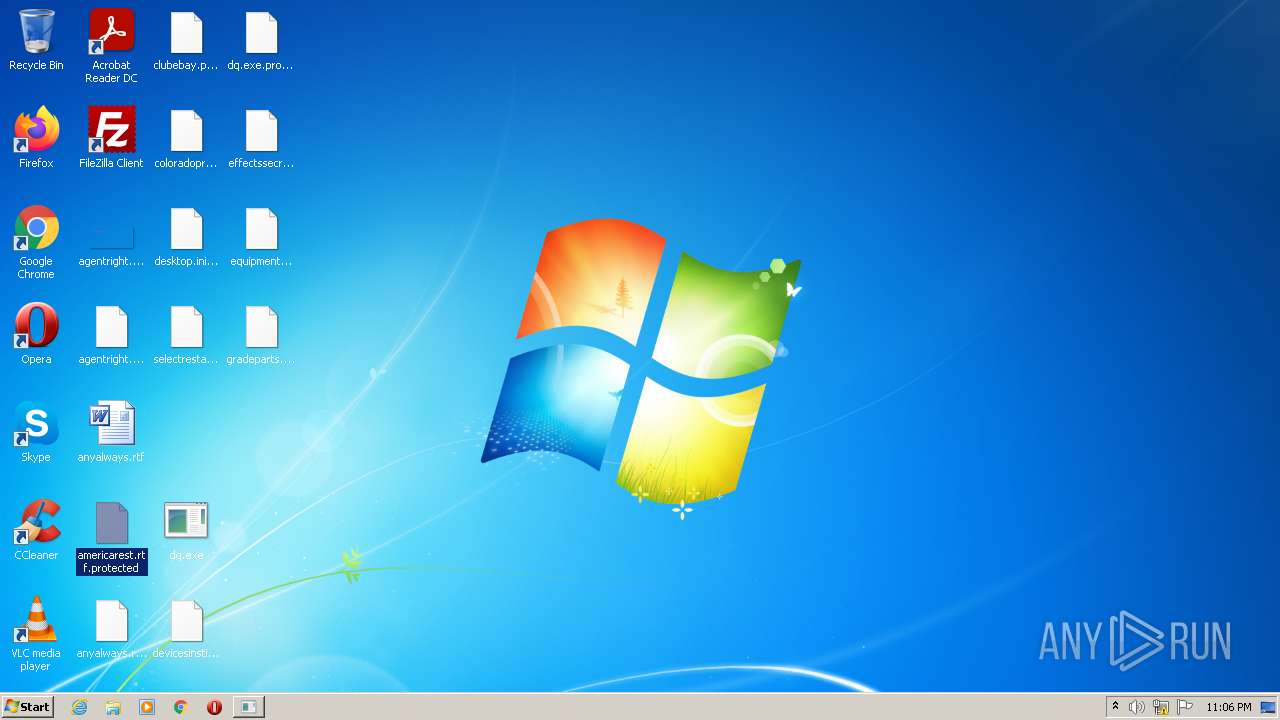
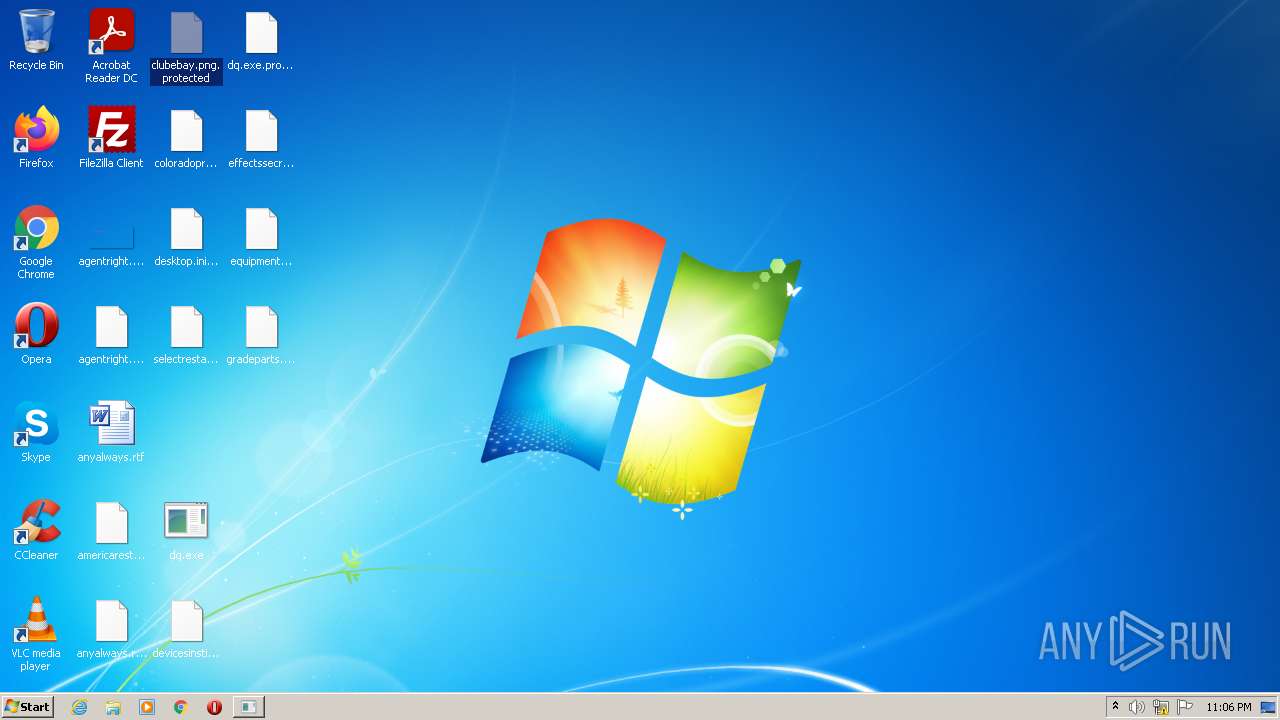
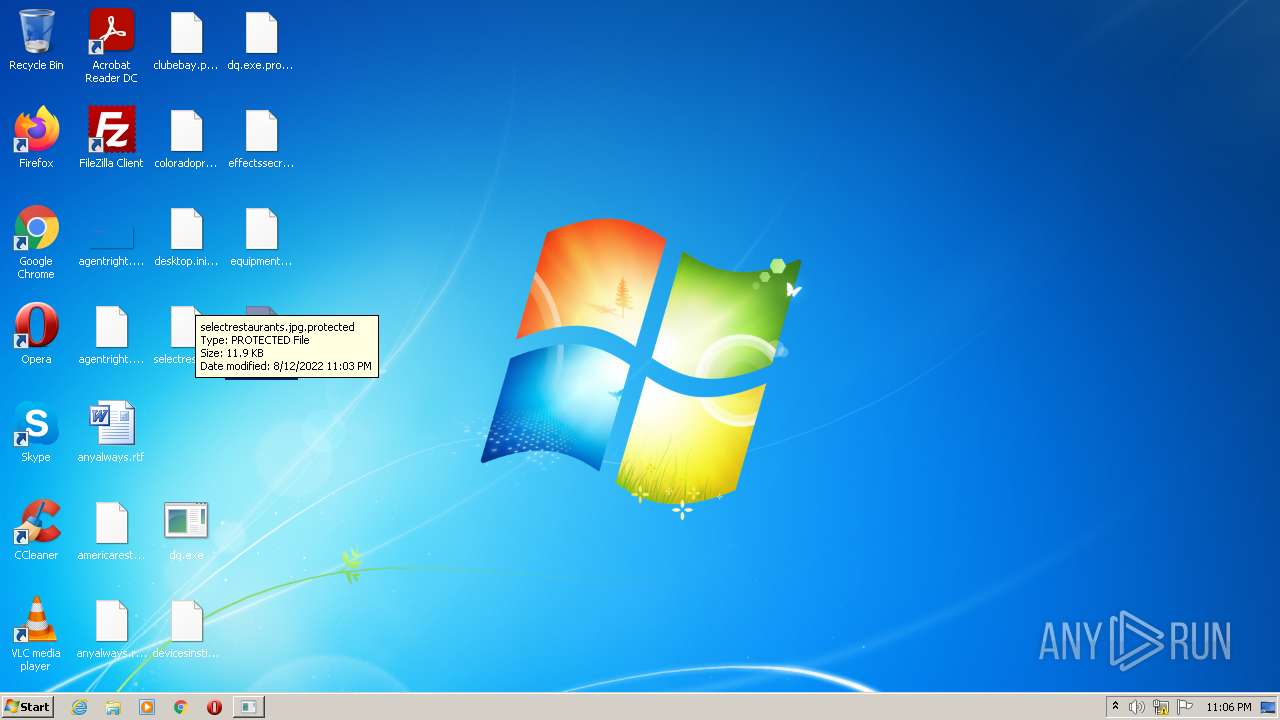
MALICIOUS
Drops executable file immediately after starts
- dq.exe (PID: 3508)
Writes to a start menu file
- dq.exe (PID: 3508)
Steals credentials from Web Browsers
- dq.exe (PID: 3508)
Actions looks like stealing of personal data
- dq.exe (PID: 3508)
Modifies files in Chrome extension folder
- dq.exe (PID: 3508)
SUSPICIOUS
Checks supported languages
- dq.exe (PID: 3508)
Executable content was dropped or overwritten
- dq.exe (PID: 3508)
Drops a file with a compile date too recent
- dq.exe (PID: 3508)
INFO
Checks supported languages
- rundll32.exe (PID: 3252)
- WINWORD.EXE (PID: 4516)
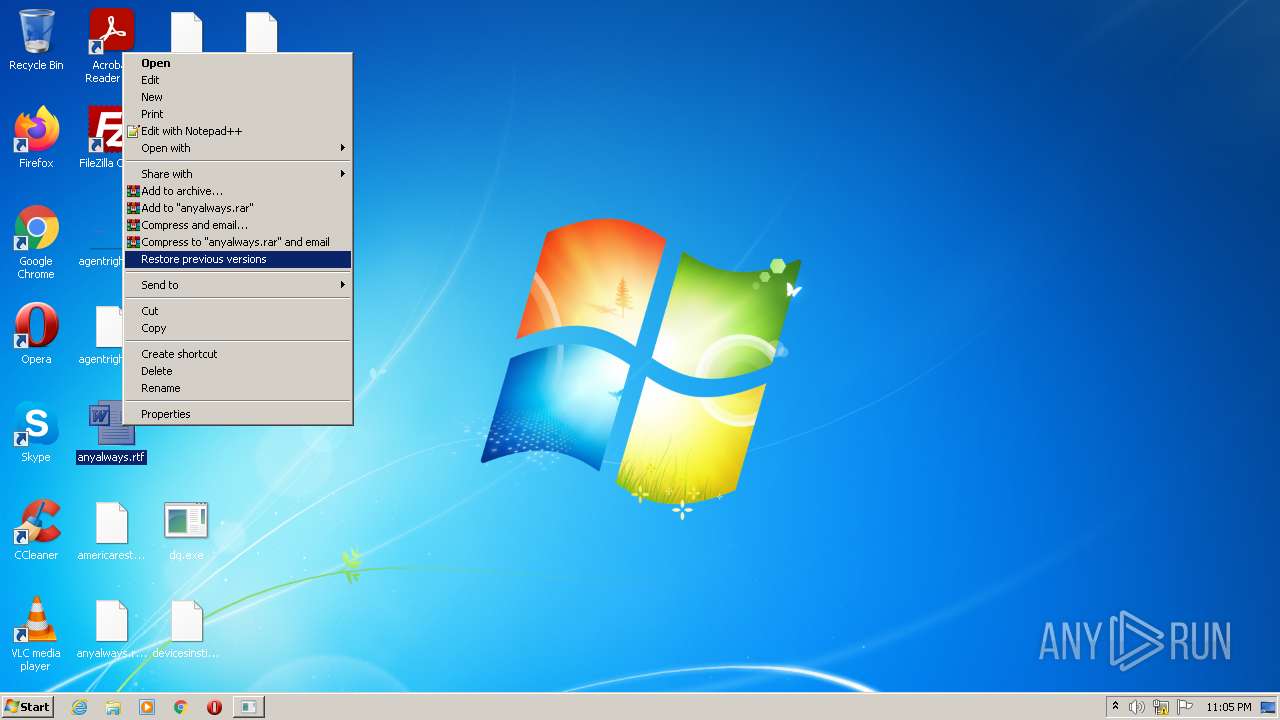
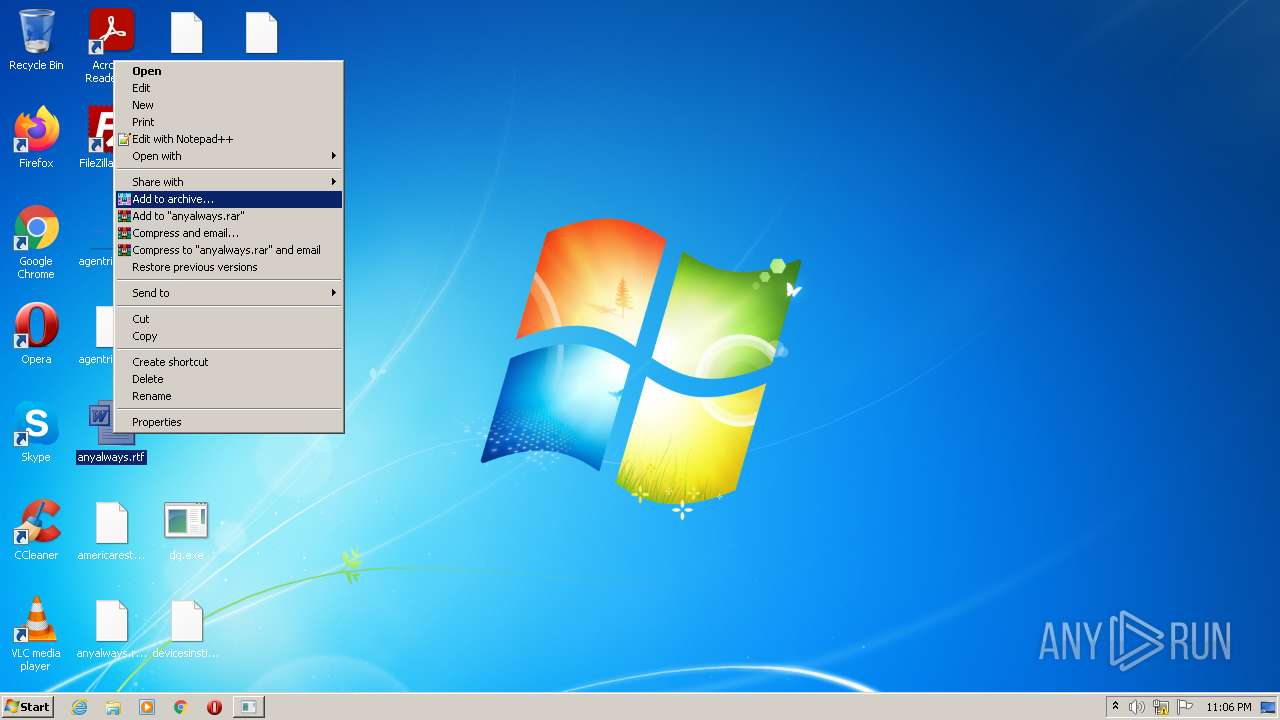
Manual execution by user
- rundll32.exe (PID: 3252)
- WINWORD.EXE (PID: 4516)
Reads the computer name
- WINWORD.EXE (PID: 4516)
Dropped object may contain Bitcoin addresses
- dq.exe (PID: 3508)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x9679a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 380416 |
| CodeSize: | 724480 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:08:13 00:01:03+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-Aug-2022 22:01:03 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Aug-2022 22:01:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B0C04 | 0x000B0E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61438 |
.rdata | 0x000B2000 | 0x0004AD74 | 0x0004AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.20351 |
.data | 0x000FD000 | 0x00007E34 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88496 |
.rsrc | 0x00105000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00106000 | 0x00009C74 | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59707 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
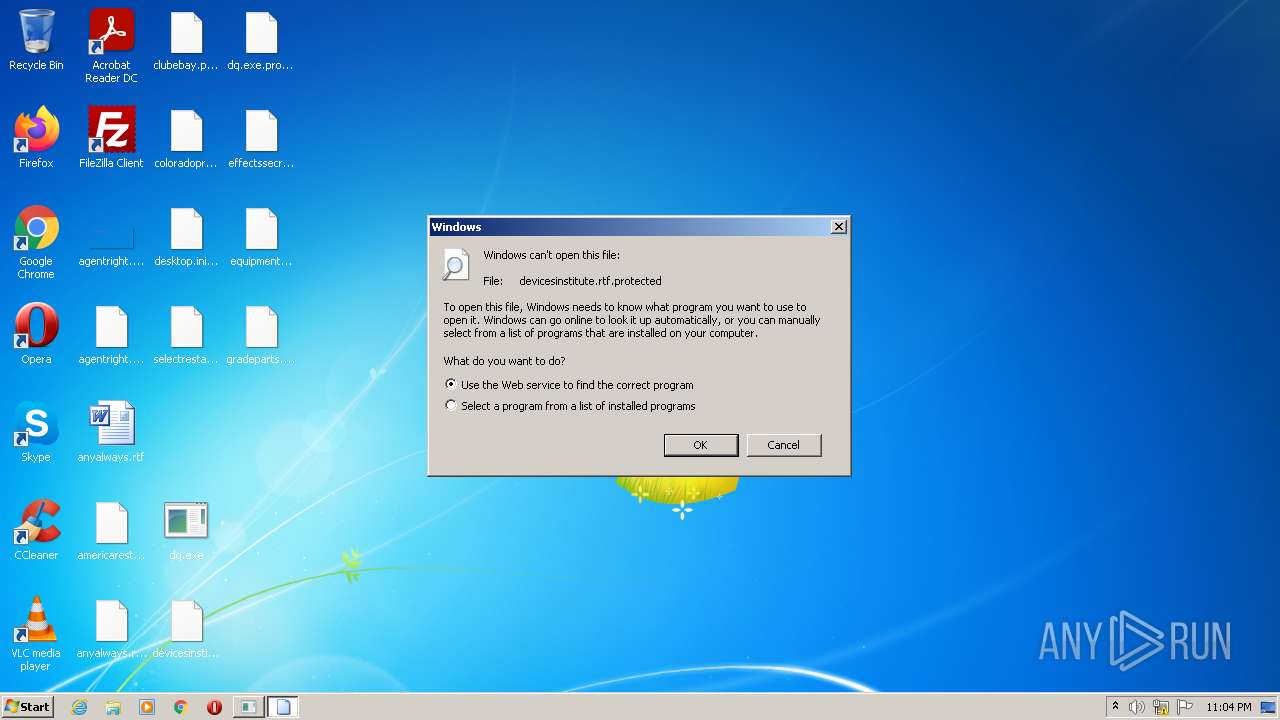
| 3252 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\devicesinstitute.rtf.protected | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\Desktop\dq.exe" | C:\Users\admin\Desktop\dq.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
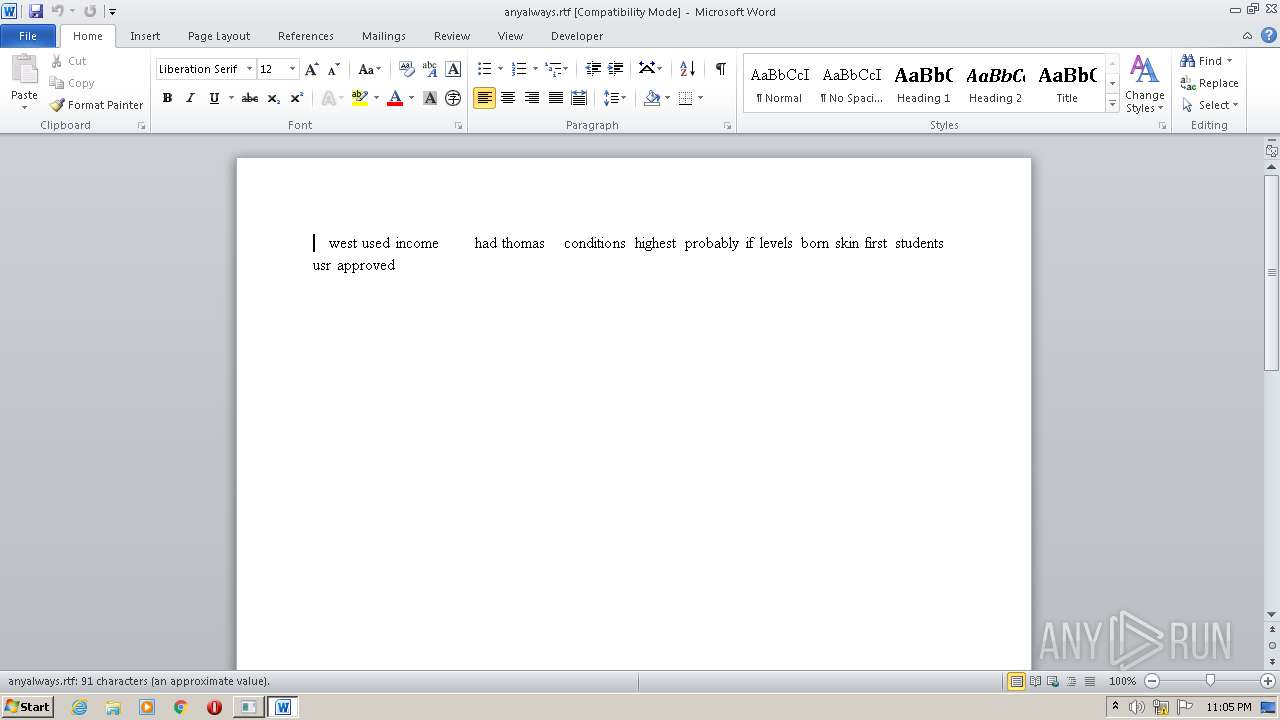
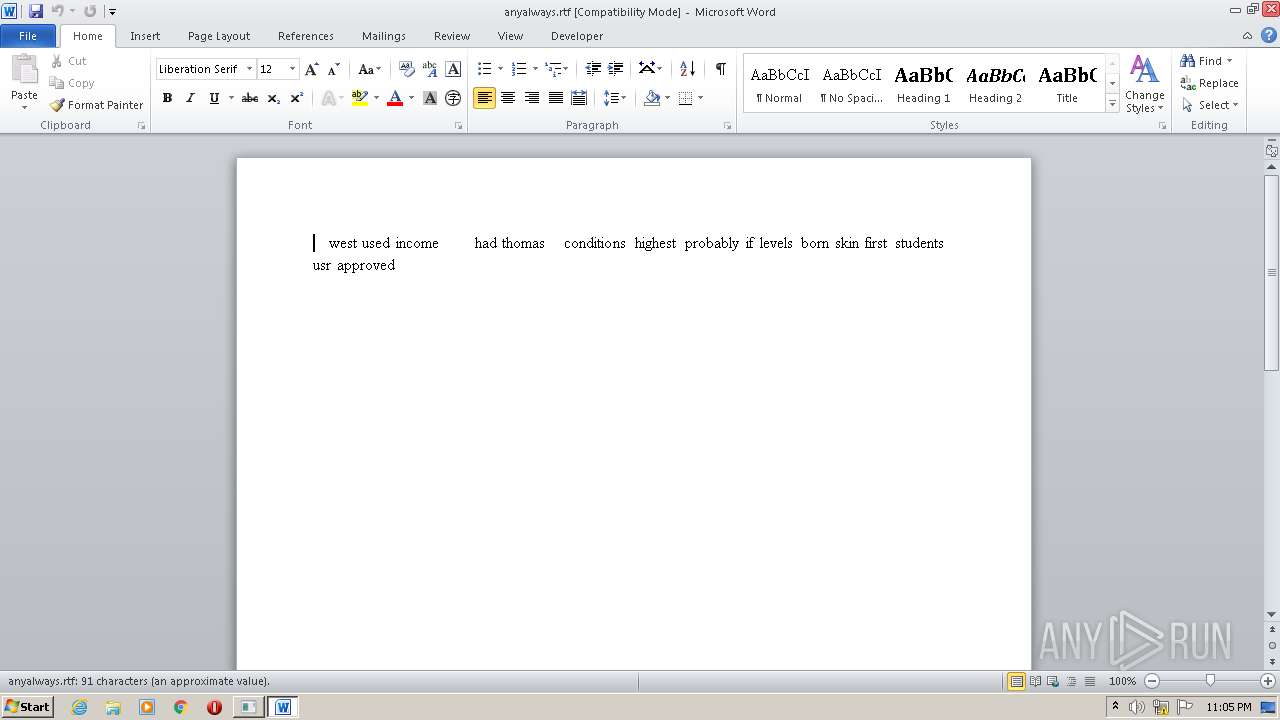
| 4516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /vu "C:\Users\admin\Desktop\anyalways.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 684
Read events
1 423
Write events
122
Delete events
139
Modification events
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j(? |
Value: 6A283F00A4110000010000000000000000000000 | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (4516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
1 794
Text files
33
Unknown types
67
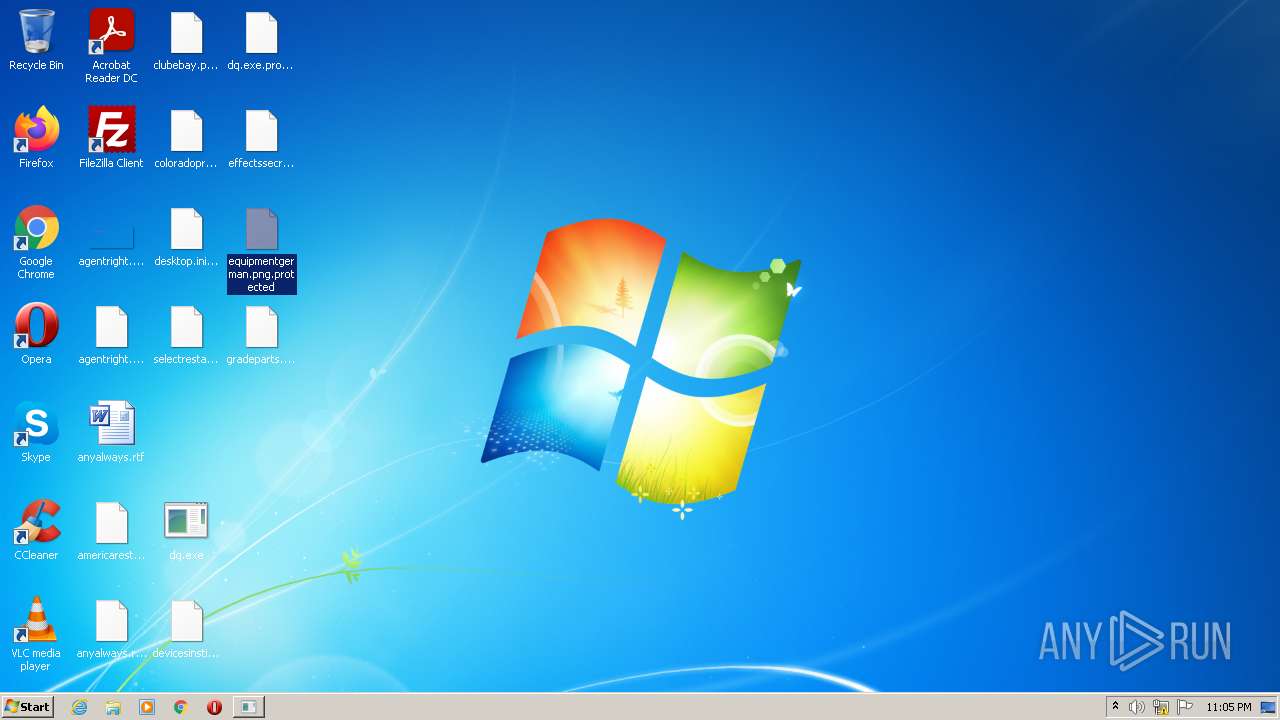
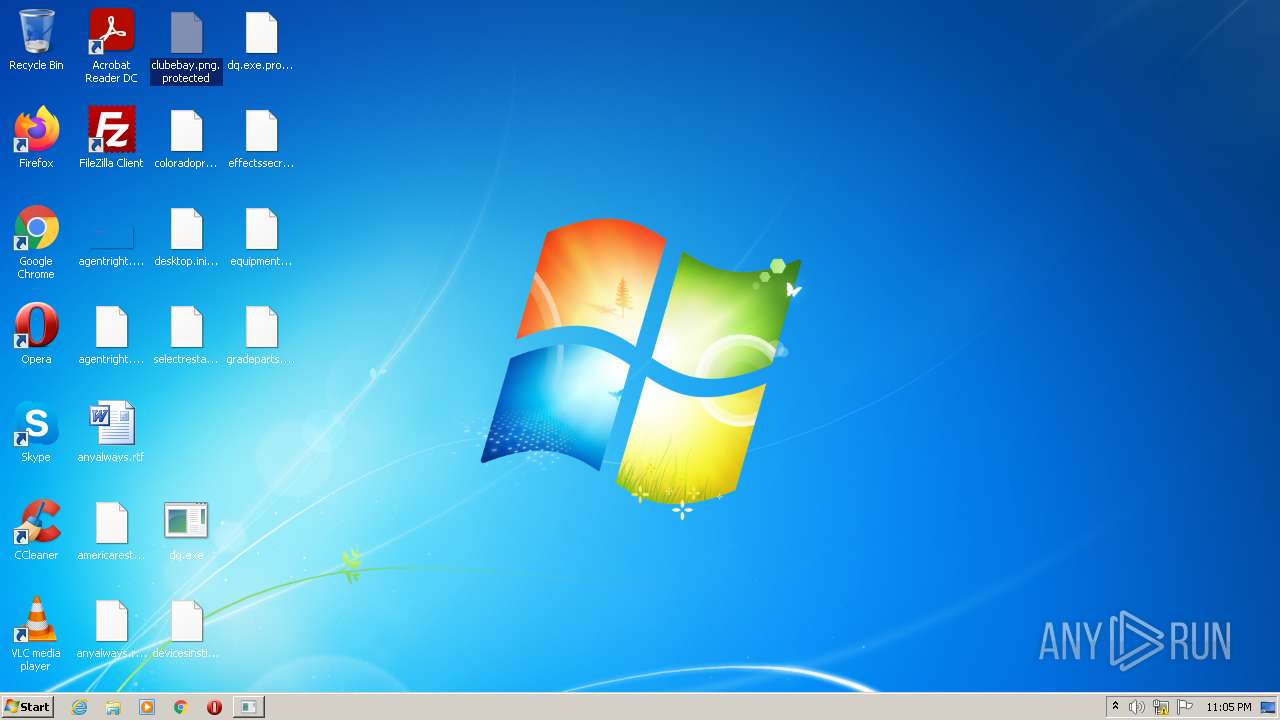
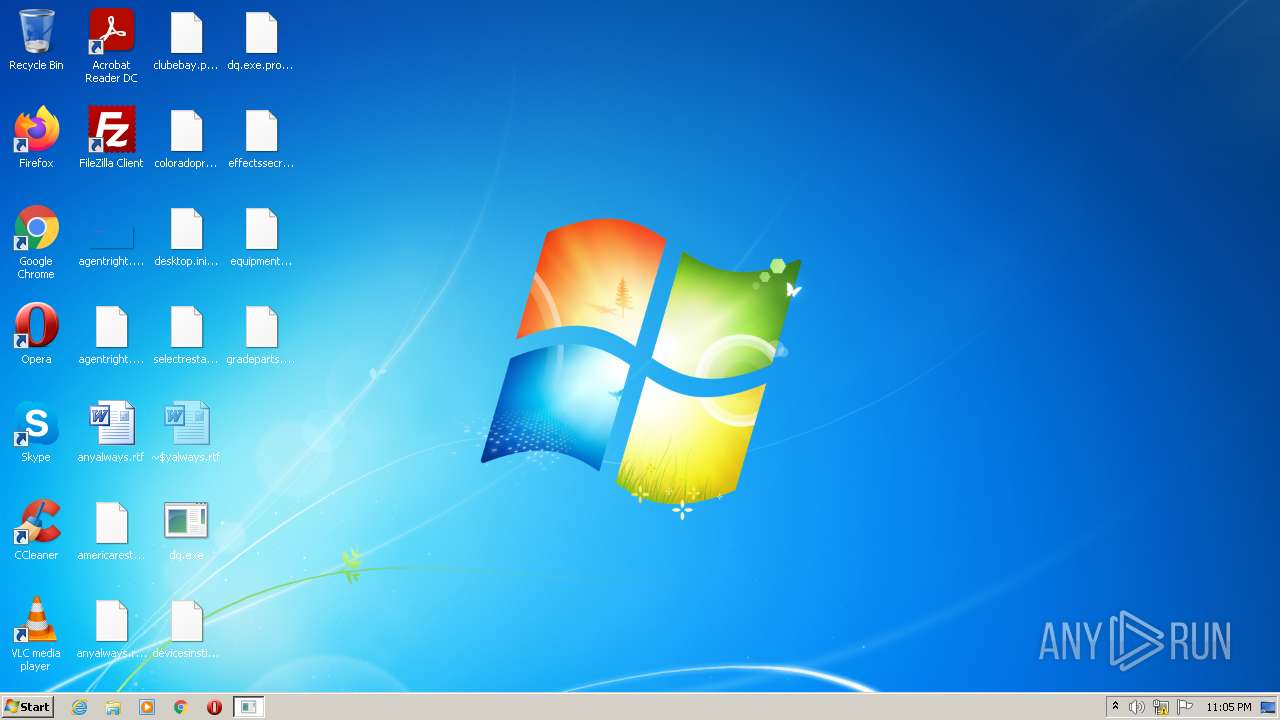
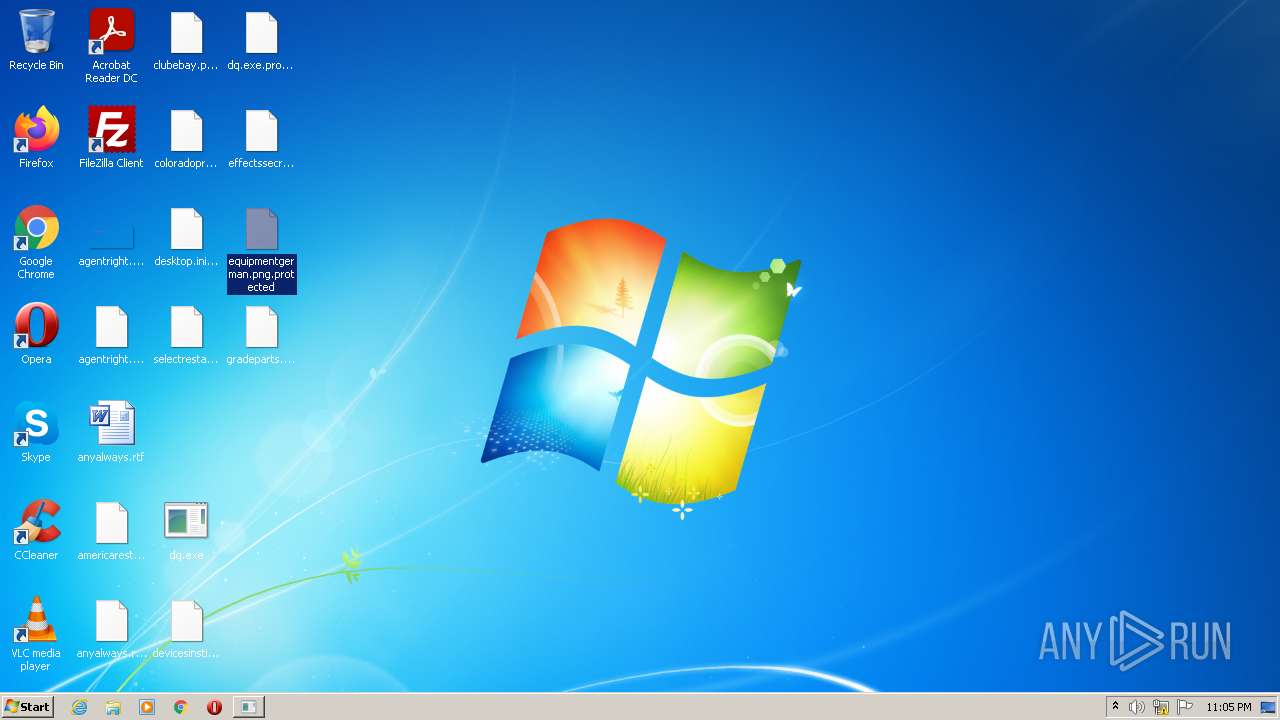
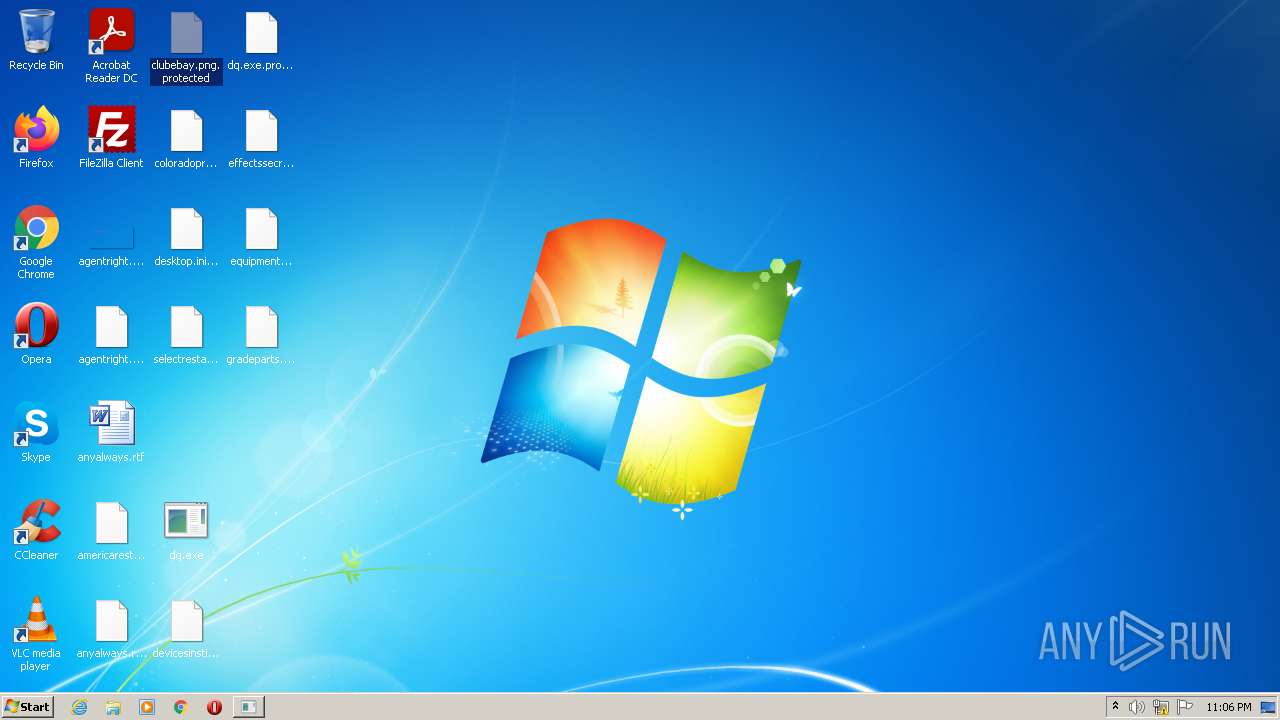
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | dq.exe | C:\Users\admin\ntuser.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Saved Games\desktop.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Searches\desktop.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Music\desktop.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Downloads\desktop.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Contacts\admin.contact.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Pictures\desktop.ini.protected | binary | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Desktop\agentright.png.protected | bs | |
MD5:— | SHA256:— | |||
| 3508 | dq.exe | C:\Users\admin\Documents\bottomsupport.rtf.protected | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report