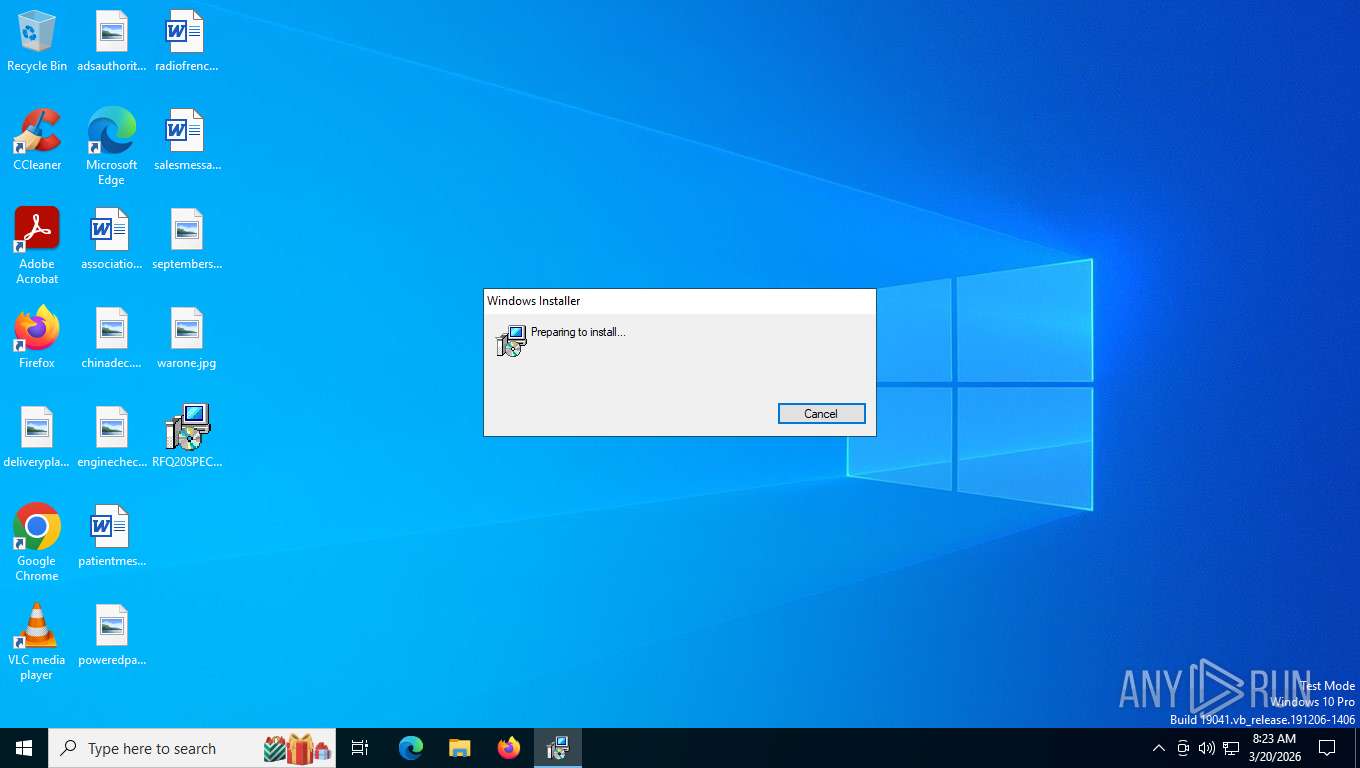
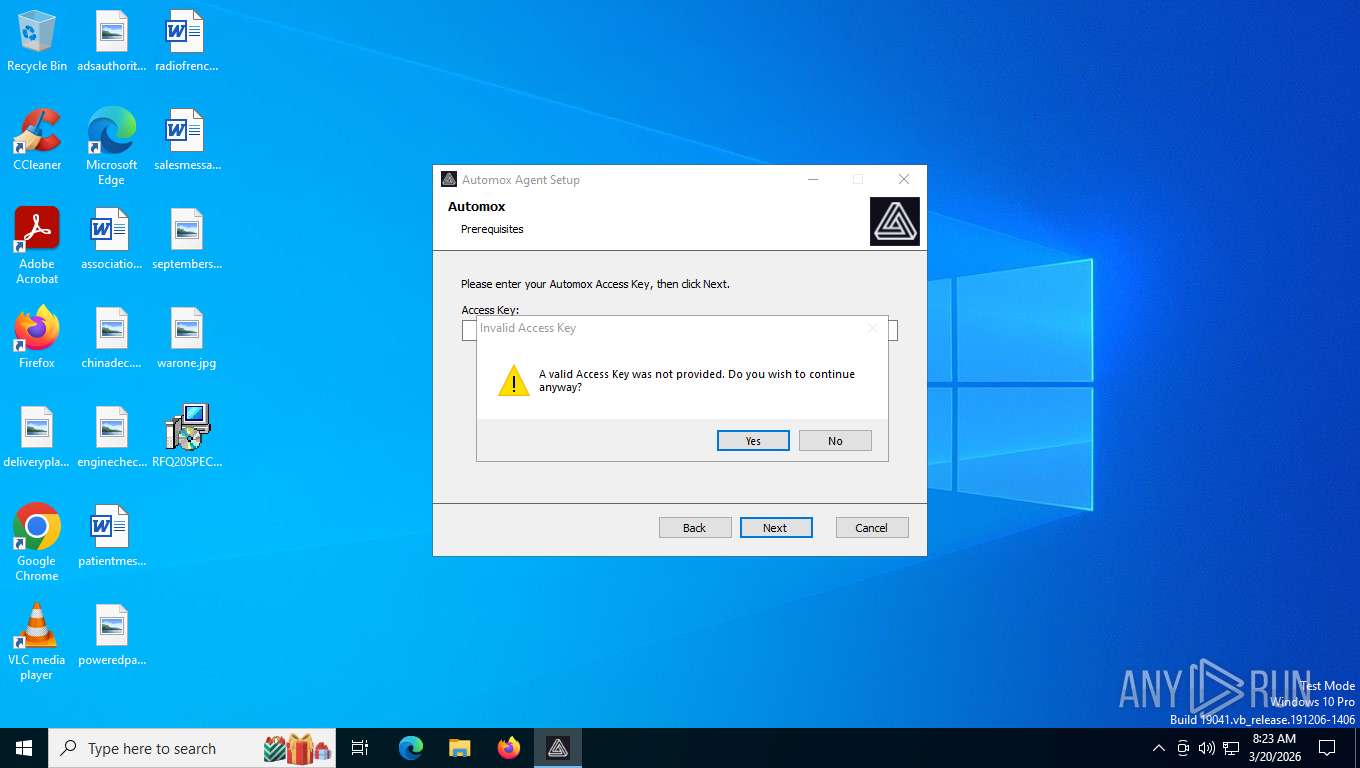
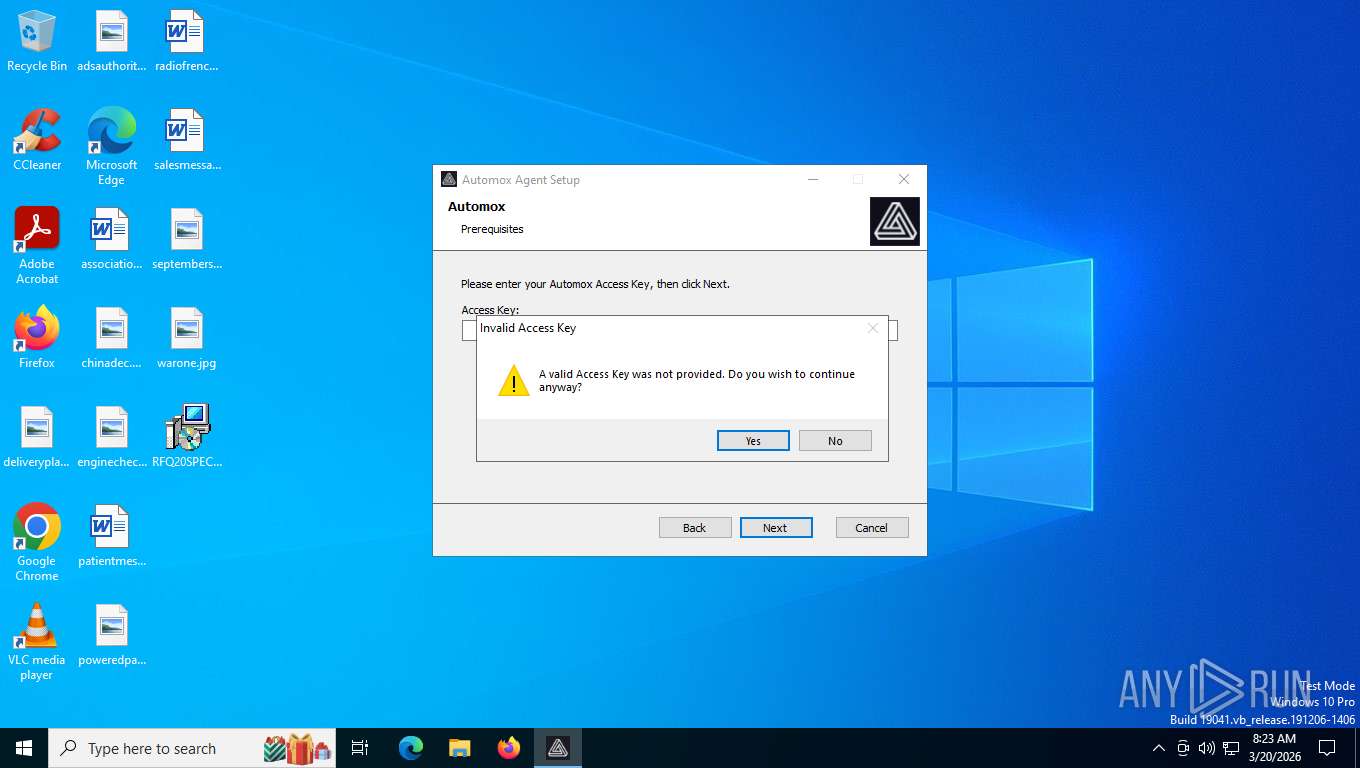
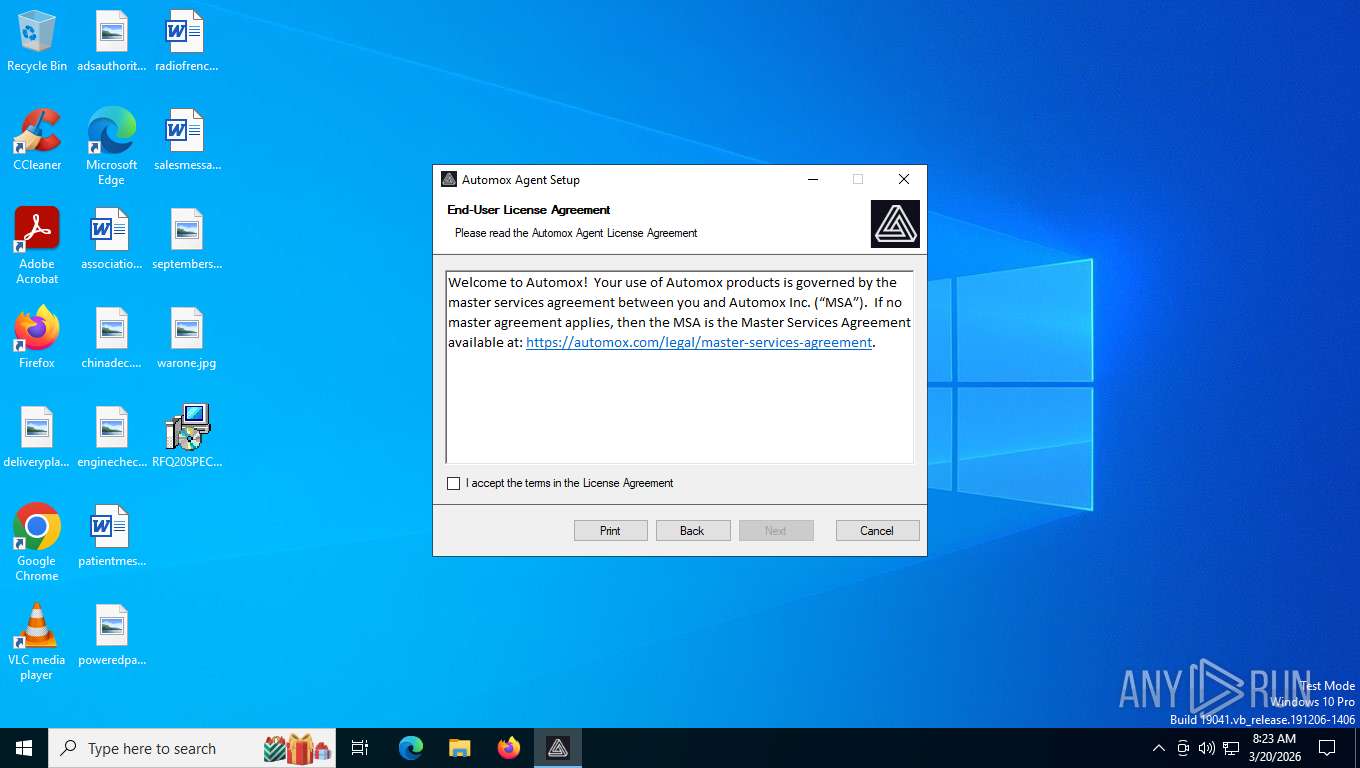
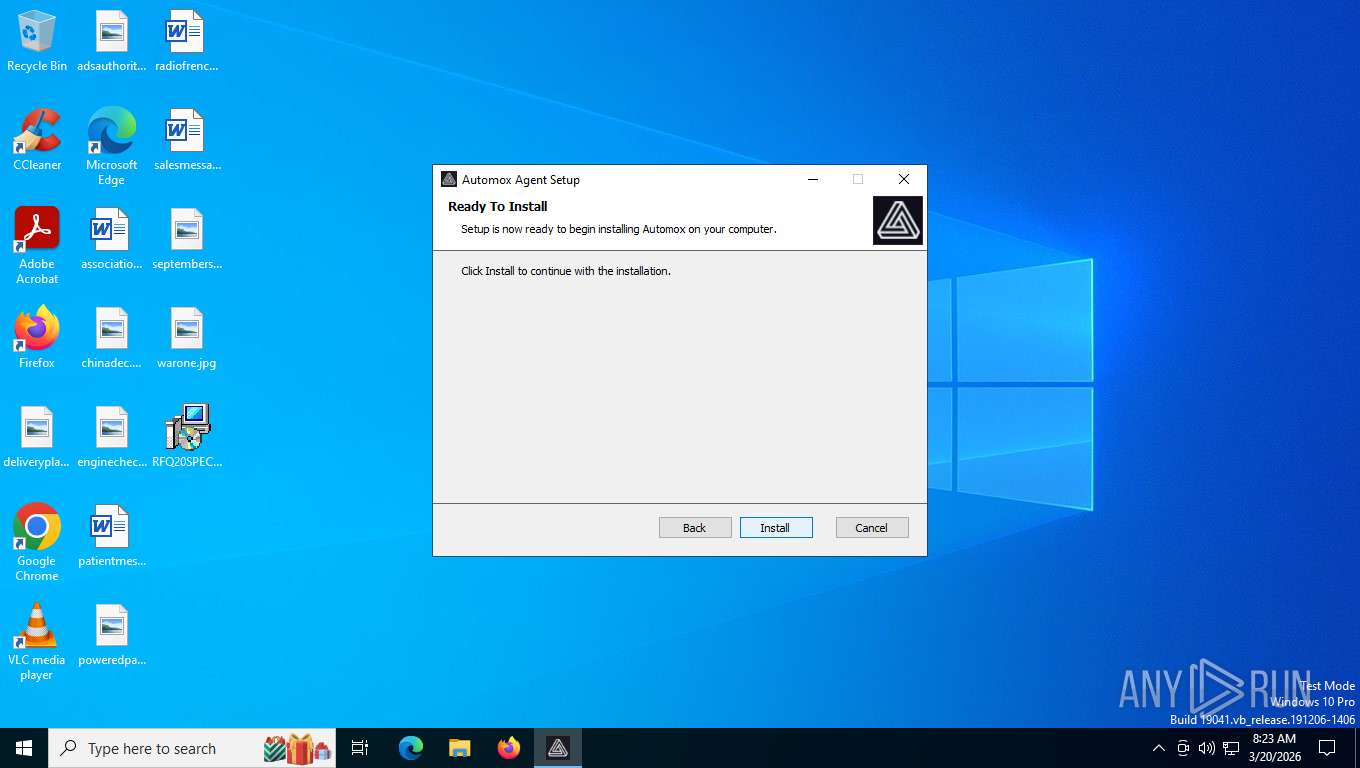
| File name: | RFQ20SPECIFICATION.msi |
| Full analysis: | https://app.any.run/tasks/84e3c03b-54cd-40f3-aecc-2fbd9c2d2d57 |
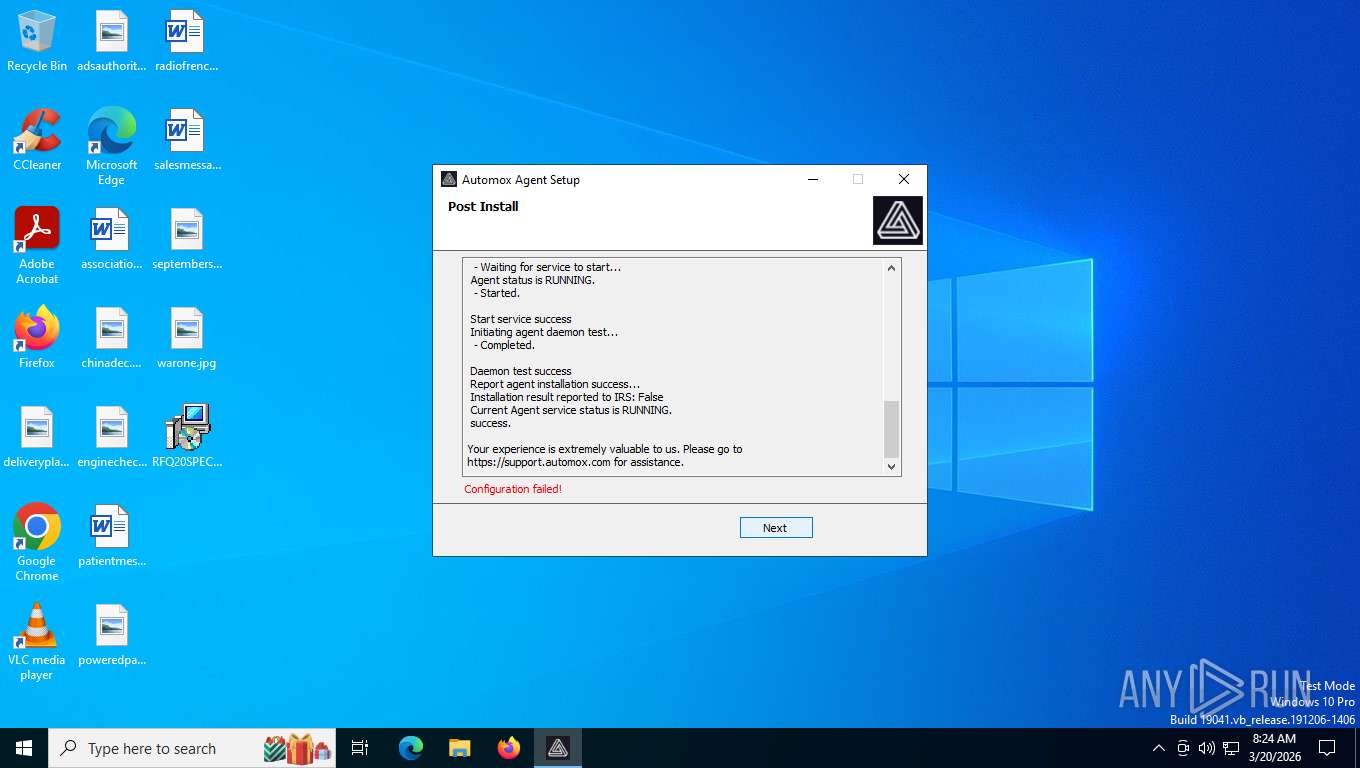
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2026, 12:23:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
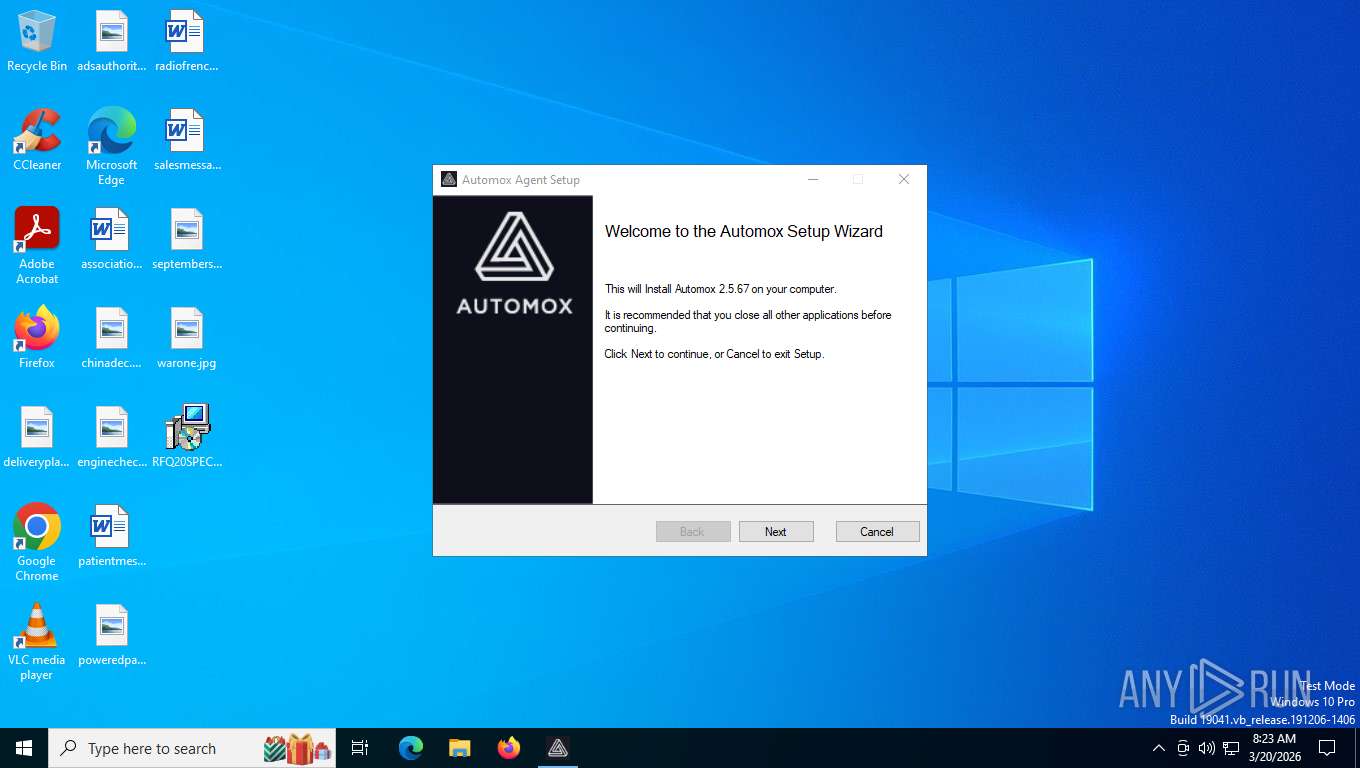
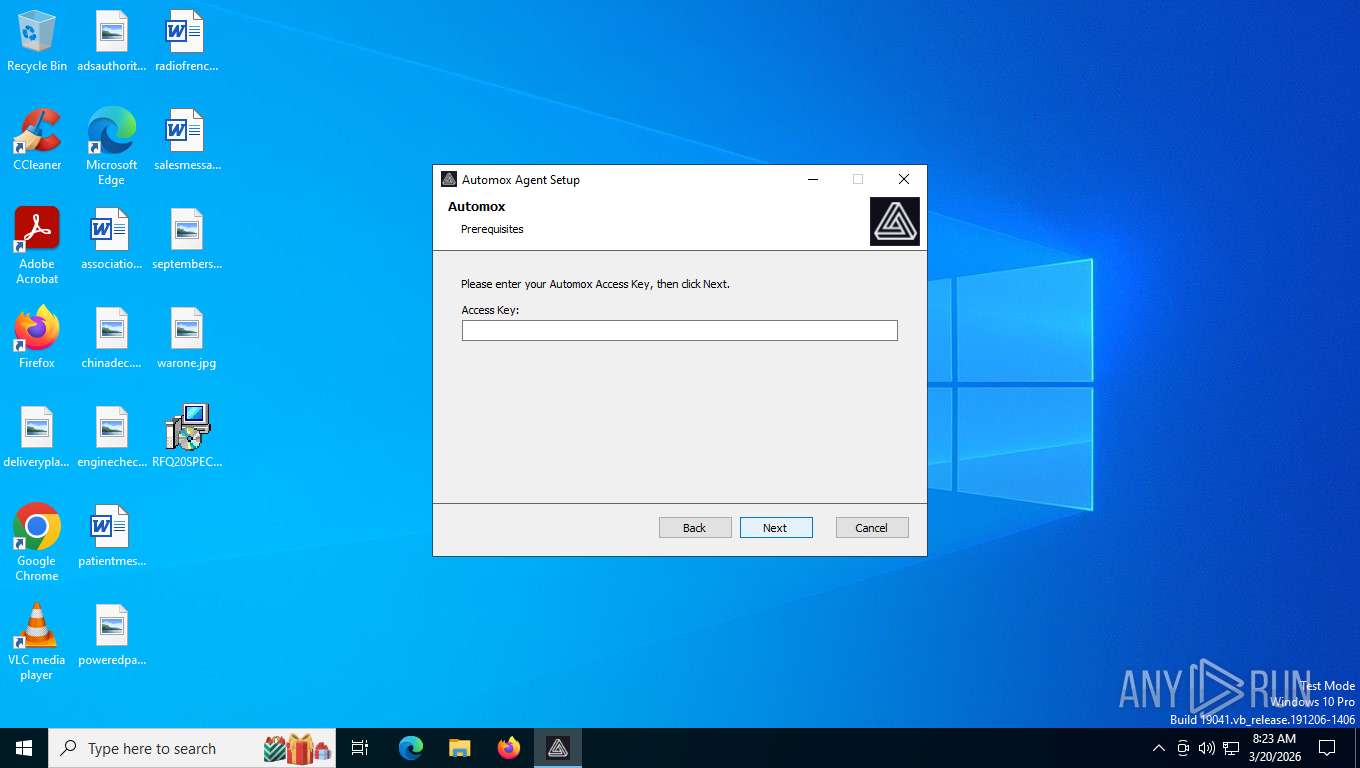
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Automox Agent, Author: Automox, Keywords: Installer, Comments: This installer database contains the logic and data required to install Automox Agent., Template: Intel;1033, Revision Number: {9A3726AC-448E-4F39-808C-686C590FAE26}, Create Time/Date: Wed Mar 4 22:22:54 2026, Last Saved Time/Date: Wed Mar 4 22:22:54 2026, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.1.2318), Security: 2 |
| MD5: | 09181F9B021BFCEDC5E9332FD77AD2D8 |
| SHA1: | FC4C6DE05BB3857B0E98B436E65228B3AC9BA24D |
| SHA256: | 5763CFEAAB30486E6E4AB024F76CAC6E26BCC527330874666AF4C7BD8C63F93E |
| SSDEEP: | 3:uKNaNaQT6VR:FAjaR |
MALICIOUS
No malicious indicators.SUSPICIOUS
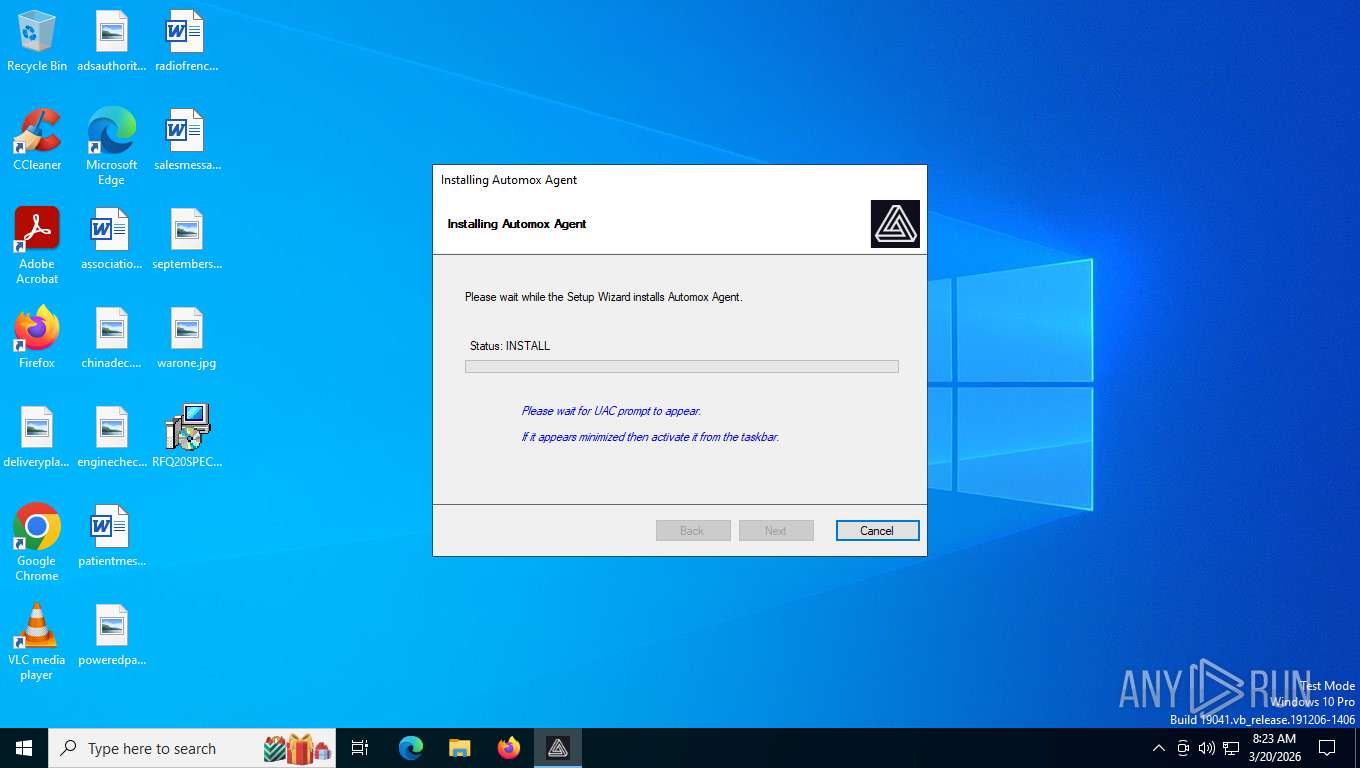
Executes as Windows Service
- VSSVC.exe (PID: 468)
- amagent-watchdog.exe (PID: 3004)
- amagent.exe (PID: 7712)
- MicrosoftEdgeUpdate.exe (PID: 5164)
Uses RUNDLL32.EXE to run a file without a DLL extension
- rundll32.exe (PID: 5784)
- rundll32.exe (PID: 9168)
- rundll32.exe (PID: 1080)
- rundll32.exe (PID: 5796)
- rundll32.exe (PID: 8708)
- rundll32.exe (PID: 132)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5784)
- rundll32.exe (PID: 9168)
- rundll32.exe (PID: 1080)
- rundll32.exe (PID: 5796)
- rundll32.exe (PID: 8708)
- rundll32.exe (PID: 132)
- MicrosoftEdgeWebview2Setup-746804179.exe (PID: 7776)
Windows service management via SC.EXE
- sc.exe (PID: 4644)
- sc.exe (PID: 8396)
- sc.exe (PID: 6108)
- sc.exe (PID: 1388)
- sc.exe (PID: 5048)
Searches for installed software
- rundll32.exe (PID: 8708)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup-746804179.exe (PID: 7776)
- MicrosoftEdgeUpdate.exe (PID: 1464)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 1464)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 1464)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8788)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5992)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1956)
- MicrosoftEdgeUpdate.exe (PID: 7548)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 5164)
Reads Internet Explorer settings
- msiexec.exe (PID: 4624)
INFO
An automatically generated document
- msiexec.exe (PID: 1848)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1848)
- MicrosoftEdgeUpdate.exe (PID: 1464)
Reads the computer name
- msiexec.exe (PID: 4624)
- msiexec.exe (PID: 2864)
- msiexec.exe (PID: 8240)
- msiexec.exe (PID: 7416)
- amagent.exe (PID: 7932)
- amagent.exe (PID: 848)
- amagent.exe (PID: 7712)
- amagent-watchdog.exe (PID: 3004)
- amagent.exe (PID: 8692)
- amagent.exe (PID: 8552)
- MicrosoftEdgeUpdate.exe (PID: 1464)
- MicrosoftEdgeUpdate.exe (PID: 7548)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8788)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5992)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1956)
- MicrosoftEdgeUpdate.exe (PID: 5604)
- MicrosoftEdgeUpdate.exe (PID: 7680)
- MicrosoftEdgeUpdate.exe (PID: 9200)
- MicrosoftEdgeUpdate.exe (PID: 5164)
- MicrosoftEdgeUpdate.exe (PID: 7472)
Creates files or folders in the user directory
- msiexec.exe (PID: 1848)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4624)
- msiexec.exe (PID: 1848)
- msiexec.exe (PID: 2864)
Checks supported languages
- msiexec.exe (PID: 2864)
- msiexec.exe (PID: 4624)
- msiexec.exe (PID: 8240)
- msiexec.exe (PID: 7416)
- amagent.exe (PID: 7932)
- agent-db-migration_windows_386.exe (PID: 6896)
- agent-db-migration_windows_386.exe (PID: 3664)
- amagent.exe (PID: 848)
- amagent.exe (PID: 7712)
- amagent.exe (PID: 8552)
- amagent-watchdog.exe (PID: 3004)
- amagent.exe (PID: 8692)
- MicrosoftEdgeWebview2Setup-746804179.exe (PID: 7776)
- MicrosoftEdgeUpdate.exe (PID: 1464)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5992)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8788)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1956)
- MicrosoftEdgeUpdate.exe (PID: 5604)
- MicrosoftEdgeUpdate.exe (PID: 9200)
- MicrosoftEdgeUpdate.exe (PID: 7680)
- MicrosoftEdgeUpdate.exe (PID: 7548)
- MicrosoftEdgeUpdate.exe (PID: 5164)
- MicrosoftEdgeUpdate.exe (PID: 7472)
Create files in a temporary directory
- msiexec.exe (PID: 4624)
- msiexec.exe (PID: 1848)
- rundll32.exe (PID: 5784)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4624)
- amagent.exe (PID: 848)
- amagent-watchdog.exe (PID: 3004)
- amagent.exe (PID: 7712)
Manages system restore points
- SrTasks.exe (PID: 4992)
The sample compiled with english language support
- msiexec.exe (PID: 2864)
- MicrosoftEdgeWebview2Setup-746804179.exe (PID: 7776)
- MicrosoftEdgeUpdate.exe (PID: 1464)
Reads Environment values
- amagent.exe (PID: 848)
- amagent.exe (PID: 8692)
- amagent-watchdog.exe (PID: 3004)
- amagent.exe (PID: 7712)
- MicrosoftEdgeUpdate.exe (PID: 5604)
- MicrosoftEdgeUpdate.exe (PID: 7472)
Creates files in the program directory
- amagent.exe (PID: 7932)
- MicrosoftEdgeWebview2Setup-746804179.exe (PID: 7776)
Drops encrypted JS script (Microsoft Script Encoder)
- amagent.exe (PID: 7712)
Reads product name
- amagent.exe (PID: 848)
- amagent.exe (PID: 8692)
- amagent.exe (PID: 7712)
Creates a software uninstall entry
- rundll32.exe (PID: 8708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Automox Agent |
| Author: | Automox |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Automox Agent. |
| Template: | Intel;1033 |
| RevisionNumber: | {9A3726AC-448E-4F39-808C-686C590FAE26} |
| CreateDate: | 2026:03:04 22:22:54 |
| ModifyDate: | 2026:03:04 22:22:54 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.1.2318) |
| Security: | Read-only recommended |
Total processes
195
Monitored processes
50
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | rundll32.exe "C:\WINDOWS\Installer\MSI50.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_2031718 83 WixSharp!WixSharp.ManagedProjectActions.CancelRequestHandler | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 468 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Automox\amagent.exe" selftest | C:\Program Files (x86)\Automox\amagent.exe | rundll32.exe | ||||||||||||
User: SYSTEM Company: Automox Inc. Integrity Level: SYSTEM Description: Automox Agent Exit code: 0 Version: 2.5.67 Modules
| |||||||||||||||
| 1080 | rundll32.exe "C:\WINDOWS\Installer\MSID6F9.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_2021125 21 WixSharpSetup!AutomoxInstaller.CustomActions.cleanOldInstall | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\WINDOWS\System32\sc.exe" query amagent | C:\Windows\SysWOW64\sc.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | amagent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1464 | "C:\Program Files (x86)\Microsoft\Temp\EU596.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EU596.tmp\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeWebview2Setup-746804179.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Version: 1.3.225.7 Modules
| |||||||||||||||
| 1520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | amagent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1848 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\RFQ20SPECIFICATION.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 414
Read events
35 035
Write events
3 270
Delete events
109
Modification events
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\TempPackages |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\MSI15309 |
Value: 2 | |||
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000042F4226864B8DC01300B0000DC0B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000042F4226864B8DC01300B0000DC0B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000AFC8786864B8DC01300B0000DC0B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000AFC8786864B8DC01300B0000DC0B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000008DC8976864B8DC01300B00007C100000E8030000010000000000000000000000A4BB1940BDCF4F42BF4D06B2D7B7C40300000000000000000000000000000000 | |||
| (PID) Process: | (468) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003515A66864B8DC01D4010000A41E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (468) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003515A66864B8DC01D4010000D80B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (468) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003515A66864B8DC01D401000020000000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (468) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003515A66864B8DC01D4010000481D0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
249
Suspicious files
35
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2864 | msiexec.exe | C:\Windows\Installer\1ecca4.msi | — | |
MD5:— | SHA256:— | |||
| 1848 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:8A2CE352473B120E3416D5AC90066FE6 | SHA256:8305B0B64D90AF9E6A822A6C96D61BACAB03964708F2623846B65784AC74AA44 | |||
| 5784 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSID32C.tmp-\WixSharp.dll | executable | |
MD5:618725C35F774689928E9F4B565817F9 | SHA256:5AC869ED452489D0F2FE7BC05B9EC1B590632B1A158741B795667399AA519DE4 | |||
| 1848 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:9E1461EF180DF26DA7B3D6CFC20016C9 | SHA256:AAD5220BE350DED69D657B31F929D5D0C383F7AE03AC7681E3BF8822DA2078A5 | |||
| 1848 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI15309\WixSharp.UI.CA.dll | executable | |
MD5:D795B0019B22E90564A655D7CE7B0D53 | SHA256:5DB558F78037741F2AB12887288529777DA76B423040DC8AA4DE4144E18BD8B4 | |||
| 1848 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_921D712AE33DF9593FDB983A68C378B1 | binary | |
MD5:0EC74C2BA5B6E44D52FC613EE6C6A6E9 | SHA256:827B66E52F0BF610D8EF49C81768D4BFEE6ECEC086F6E4F71AAD9ECD453E94C1 | |||
| 4624 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI15309\EmbeddedUI.config | xml | |
MD5:C9C40AF1656F8531EAA647CACEB1E436 | SHA256:1A67F60962CA1CBF19873B62A8518EFE8C701A09CD609AF4C50ECC7F0B468BB8 | |||
| 1848 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:97470A1AC071EB561155D037C2FAAC63 | SHA256:FC126F85AB4F5FAC191DAD82DFBD4EE04BD31C3A23DBFBD75A11CED5A49C9601 | |||
| 4624 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\tmp73A7.tmp | xml | |
MD5:9348B23324772FCC40D9687FC2B3A8CA | SHA256:CFFD70A9E9A9844315252FC48B52AEC7AA65FA925A9D83CF92A3862CE257E06F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
76
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1848 | msiexec.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAyqwRmNut24tKviyUK5Lj8%3D | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | binary | 203 b | whitelisted |
6200 | svchost.exe | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6200 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | unknown | text | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.65:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.86.251.28:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6200 | svchost.exe | 23.216.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6200 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5444 | svchost.exe | Misc activity | ET INFO Packed Executable Download |