| File name: | PsExec.exe |
| Full analysis: | https://app.any.run/tasks/da2a5982-cc14-472c-9a83-b59b8027d874 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 14:22:55 |
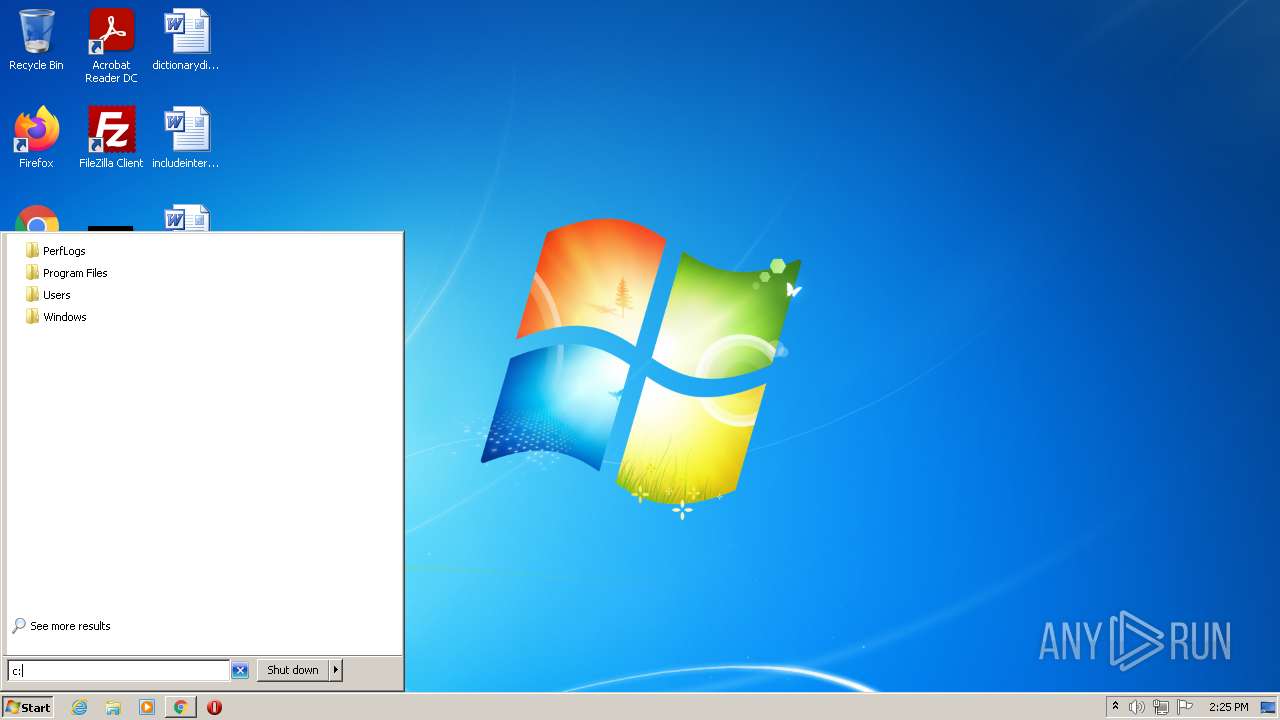
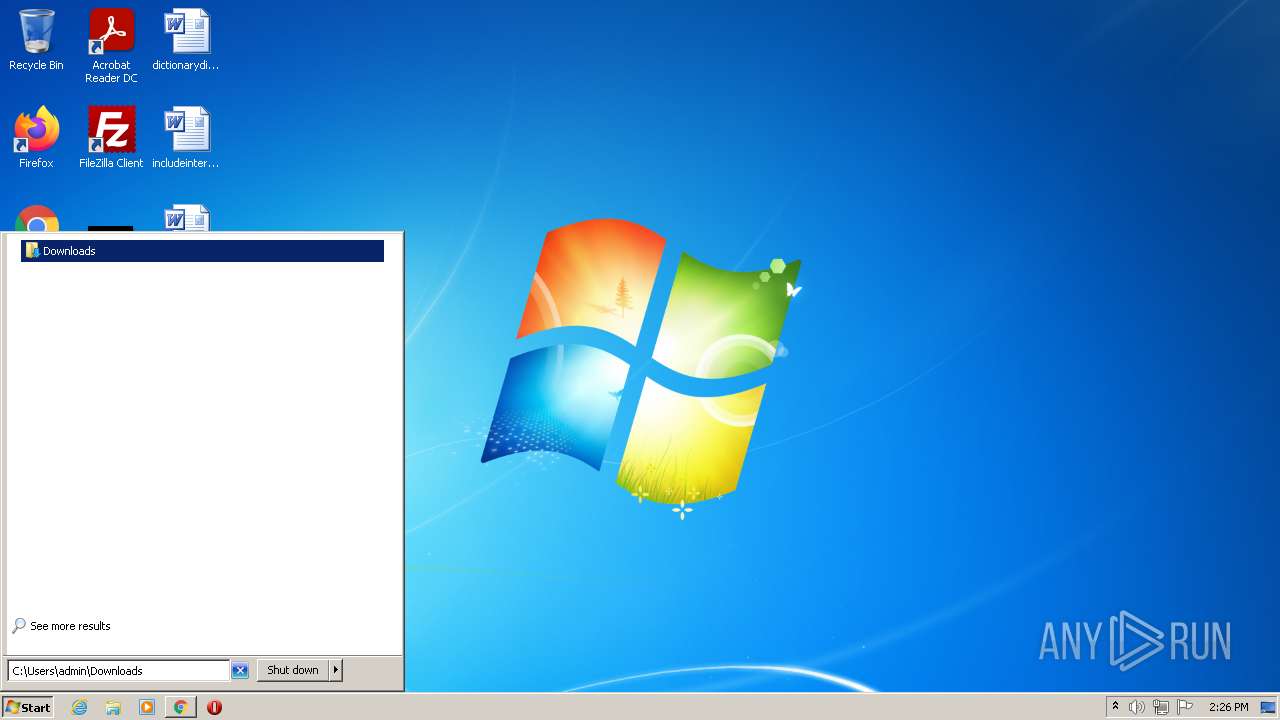
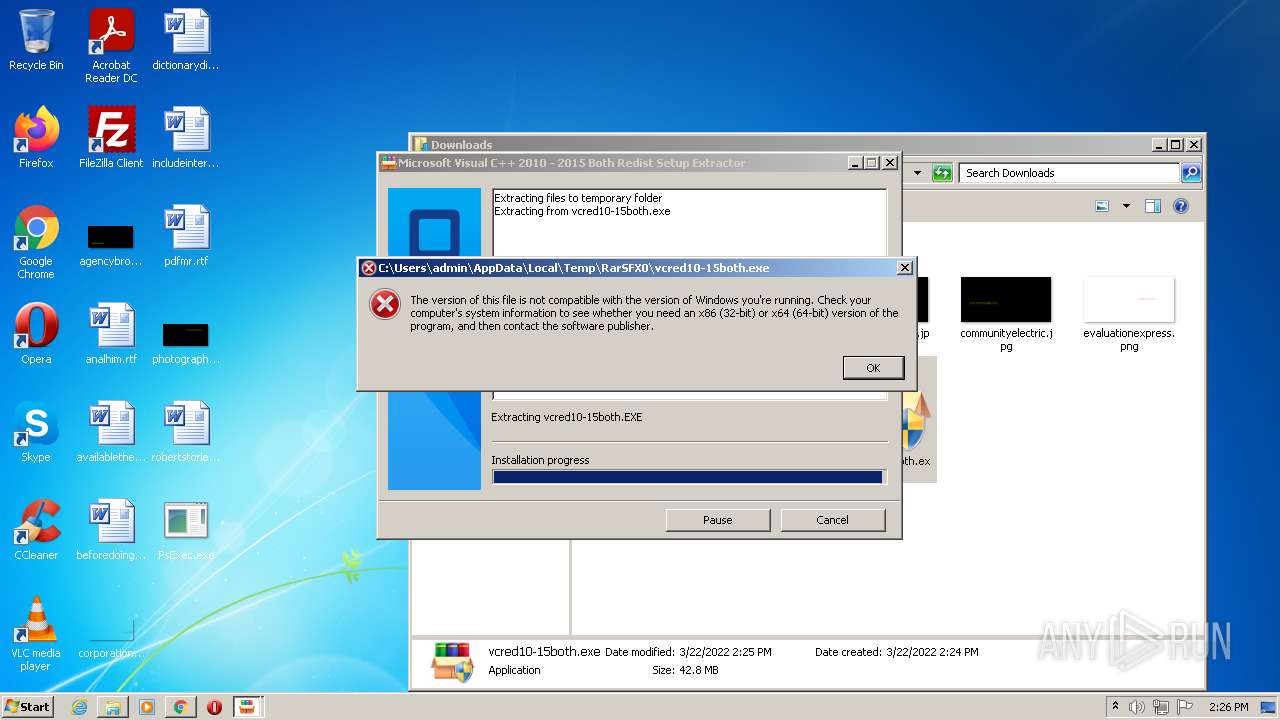
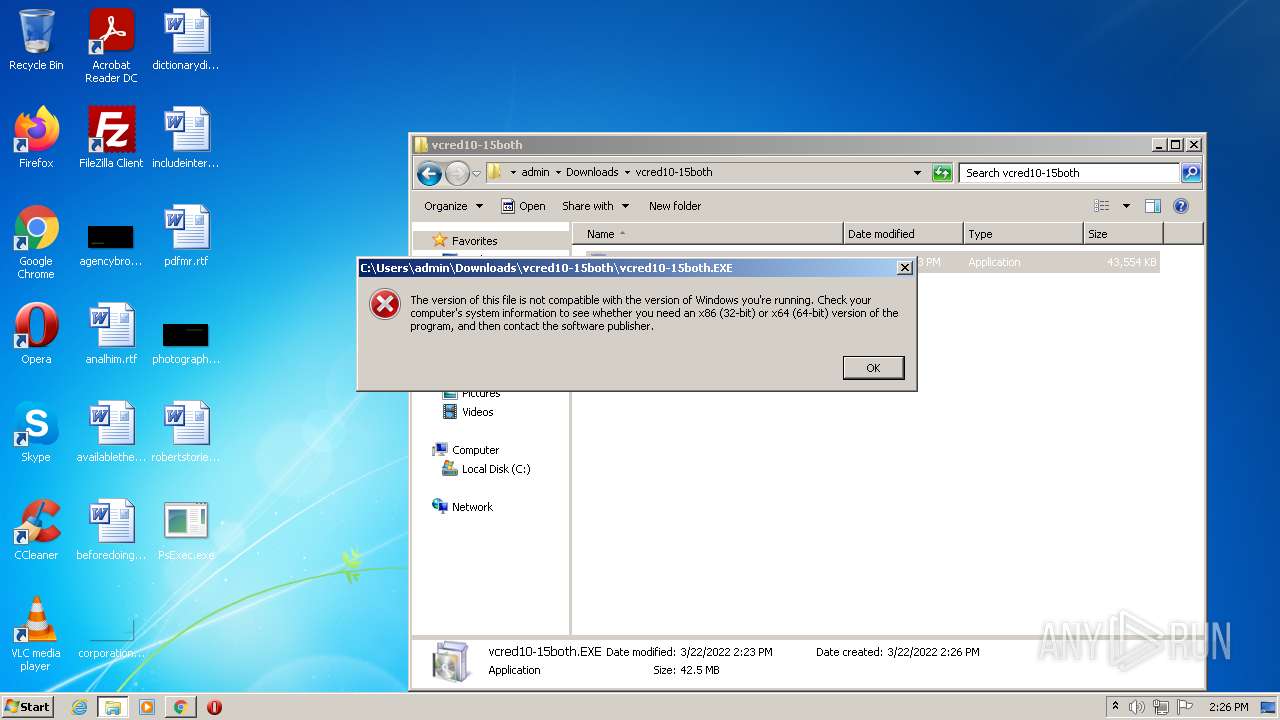
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | C590A84B8C72CF18F35AE166F815C9DF |
| SHA1: | B97761358338E640A31EEF5E5C5773B633890914 |
| SHA256: | 57492D33B7C0755BB411B22D2DFDFDF088CBBFCD010E30DD8D425D5FE66ADFF4 |
| SSDEEP: | 12288:RkNmqjrUz5KzNeXAUEcgX8DsWTbiMktn/TtYsEzWd0ShE+SrOQRUvjbxks4:RkxeDgMDsWTbijtLhE+SrRRUvjbxA |
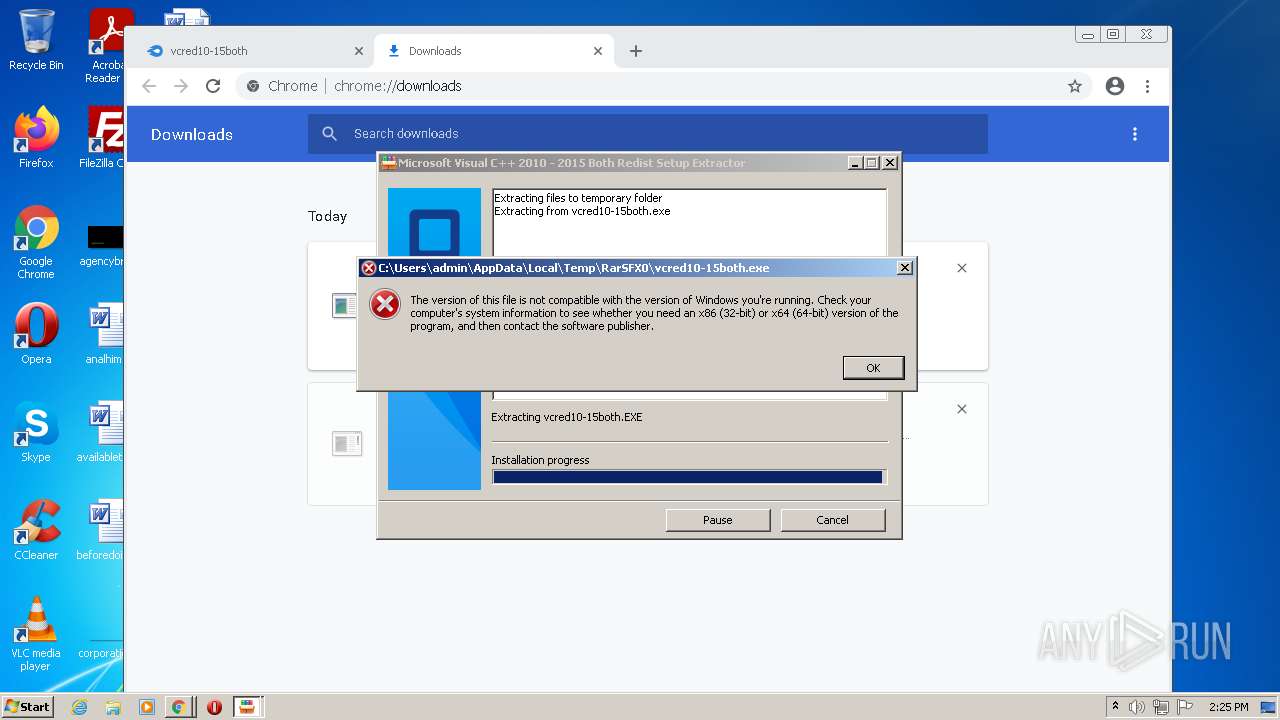
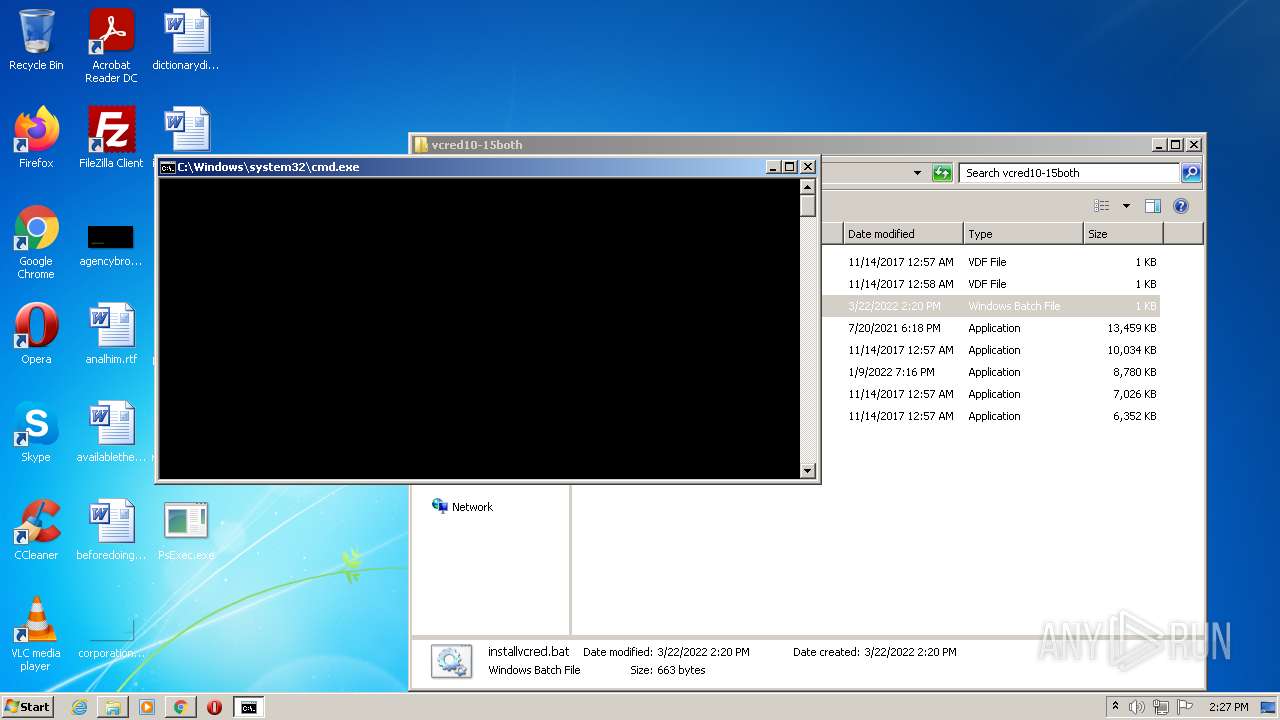
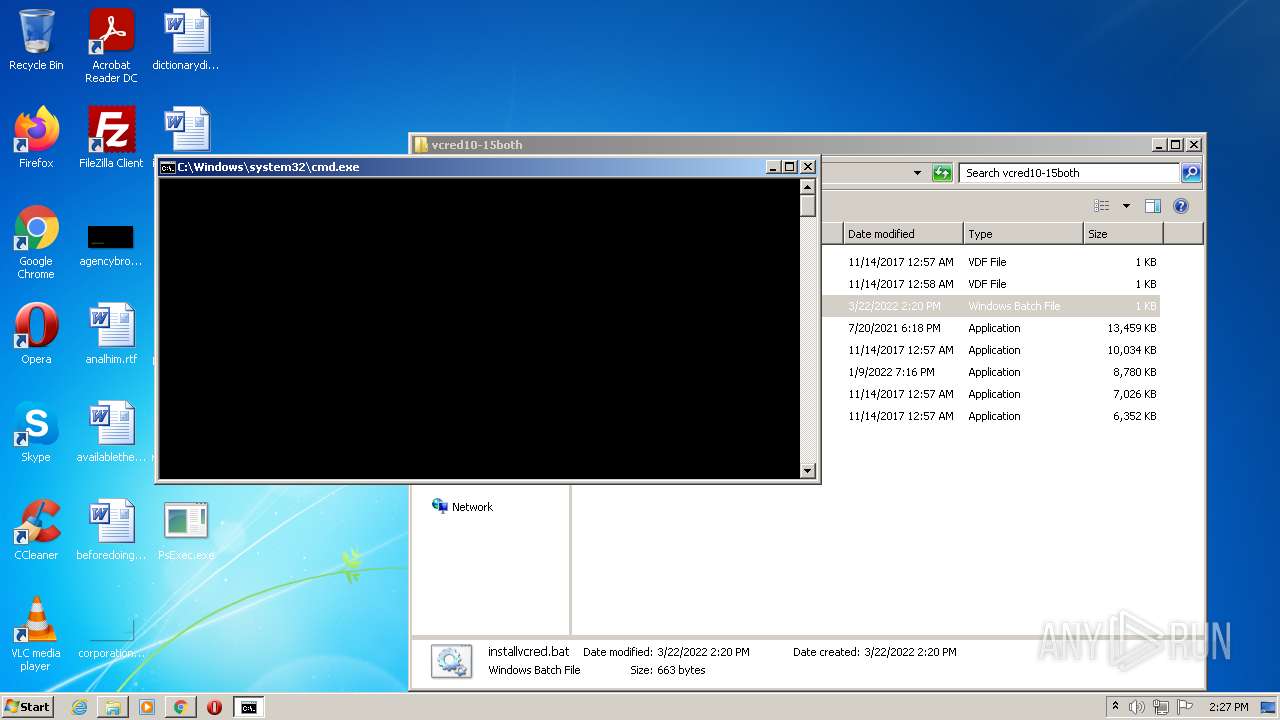
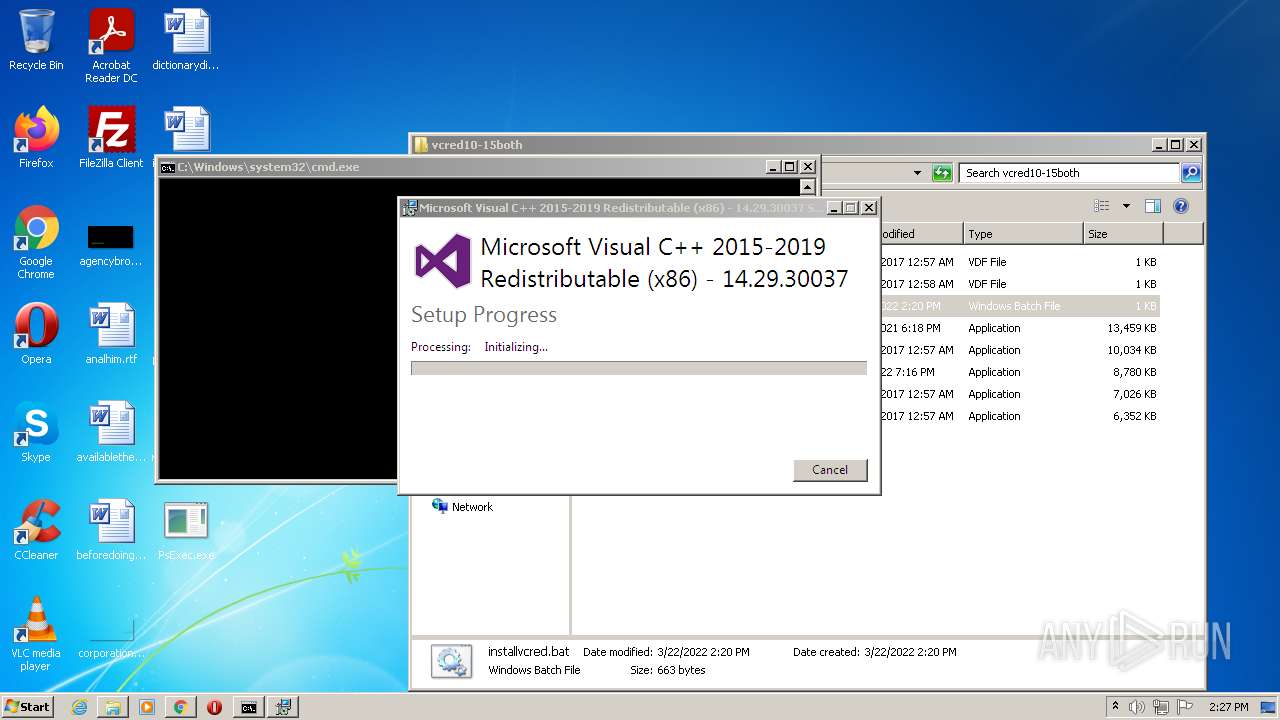
MALICIOUS
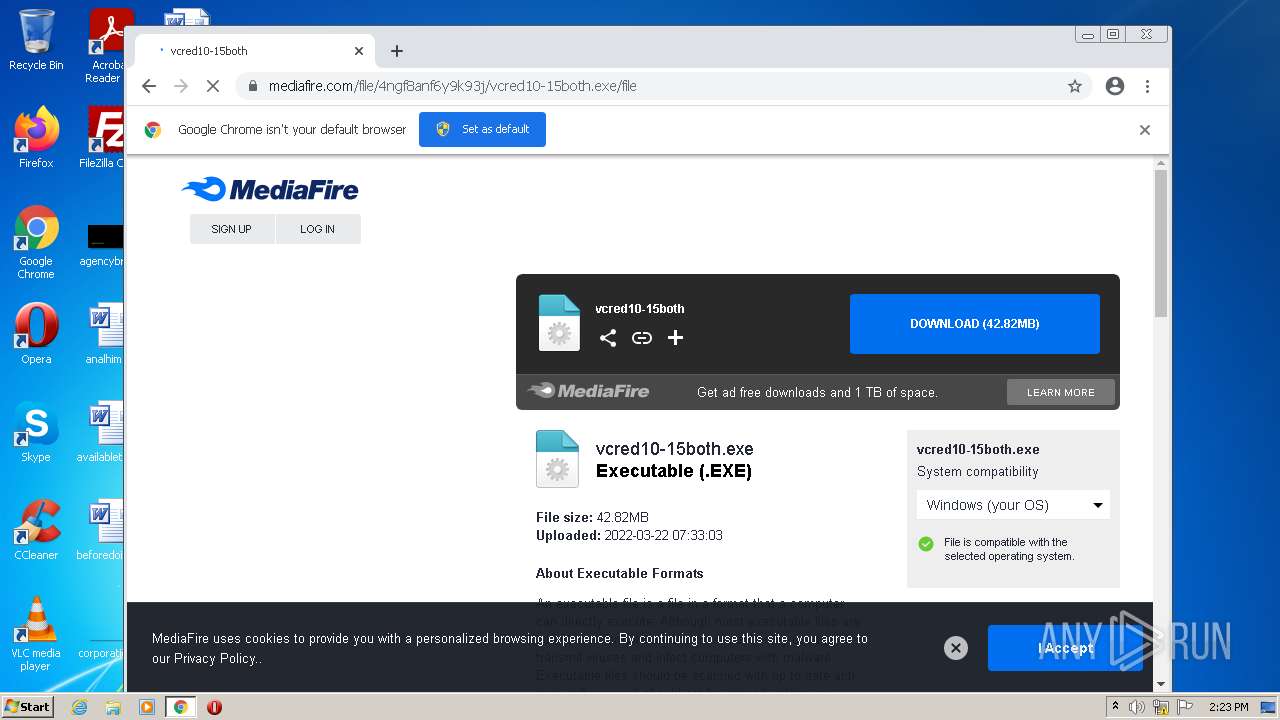
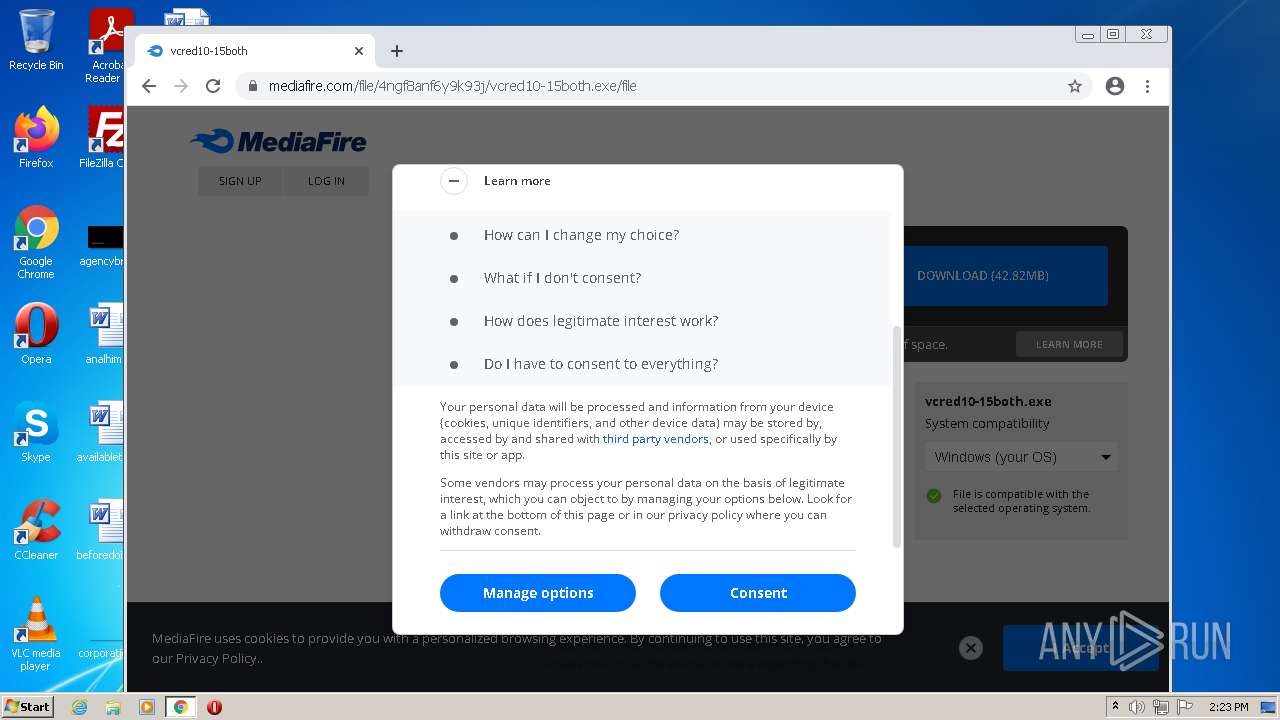
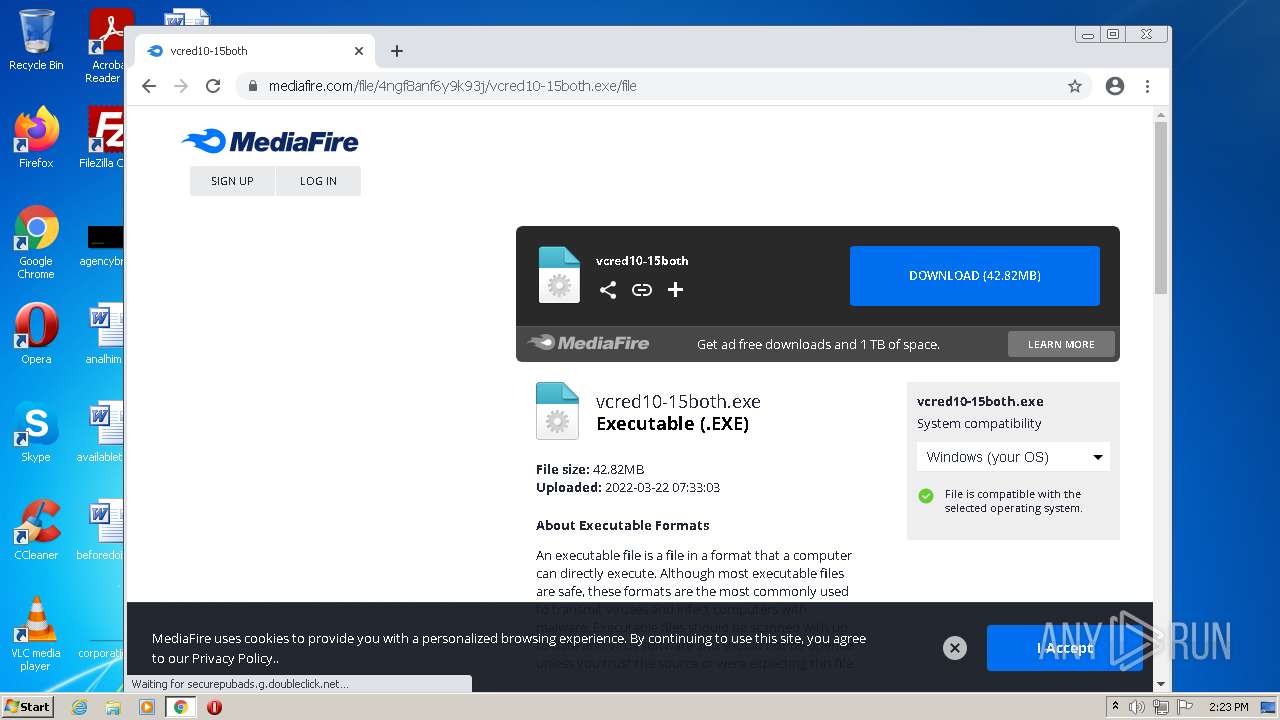
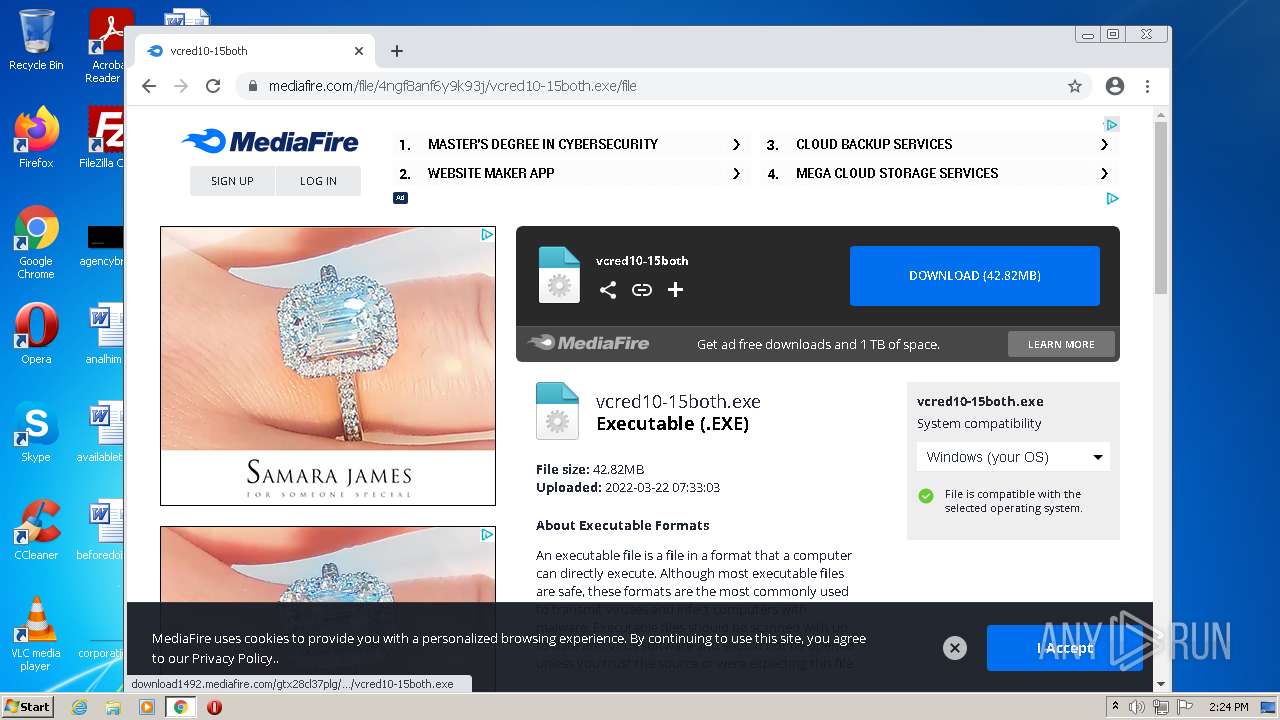
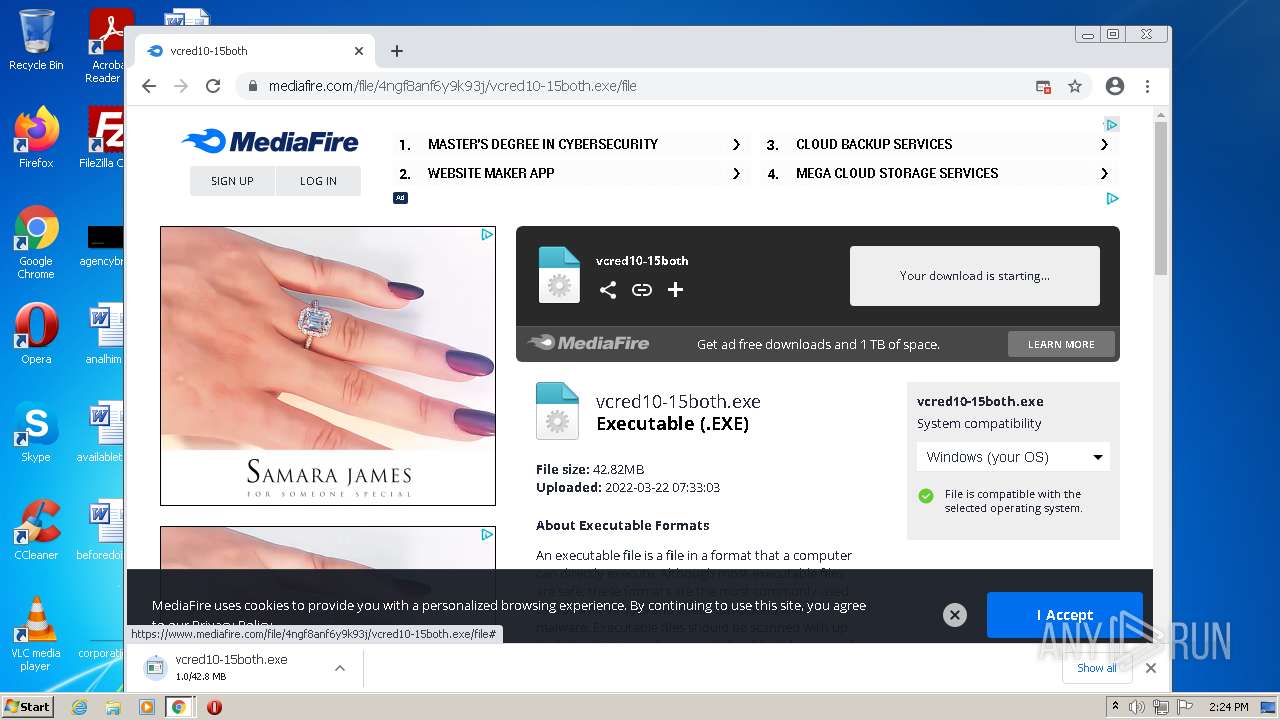
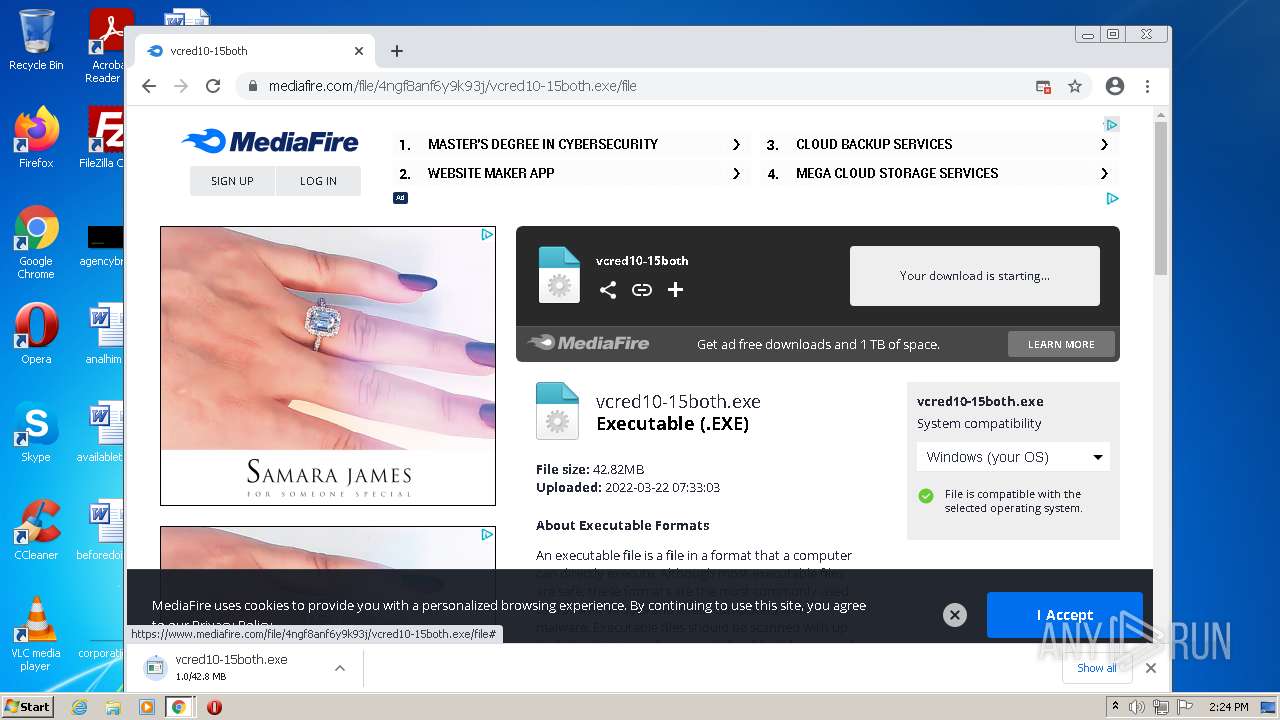
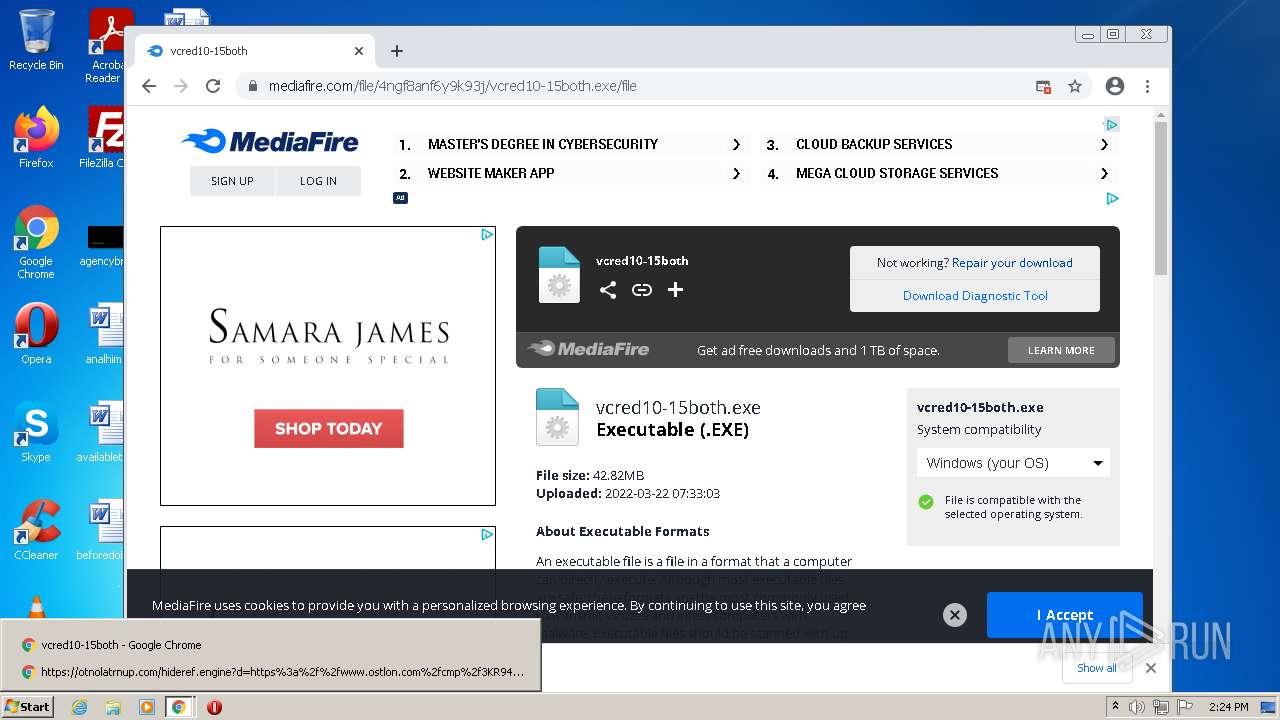
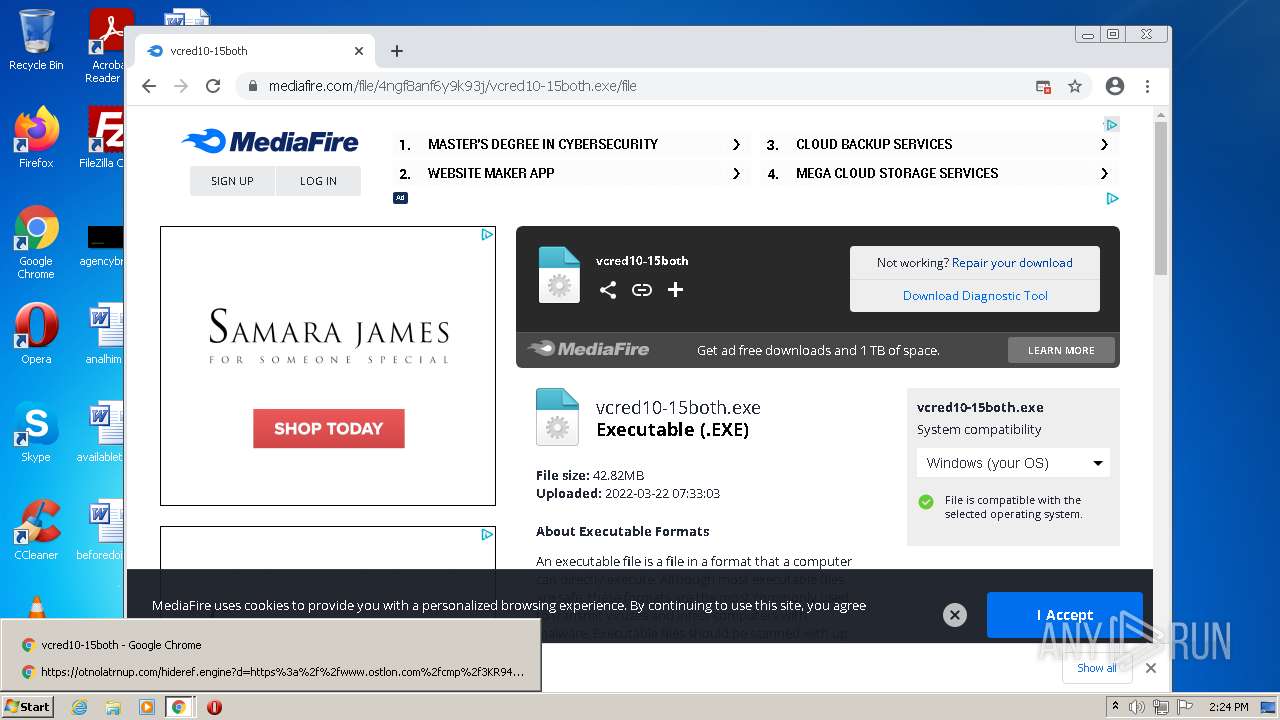
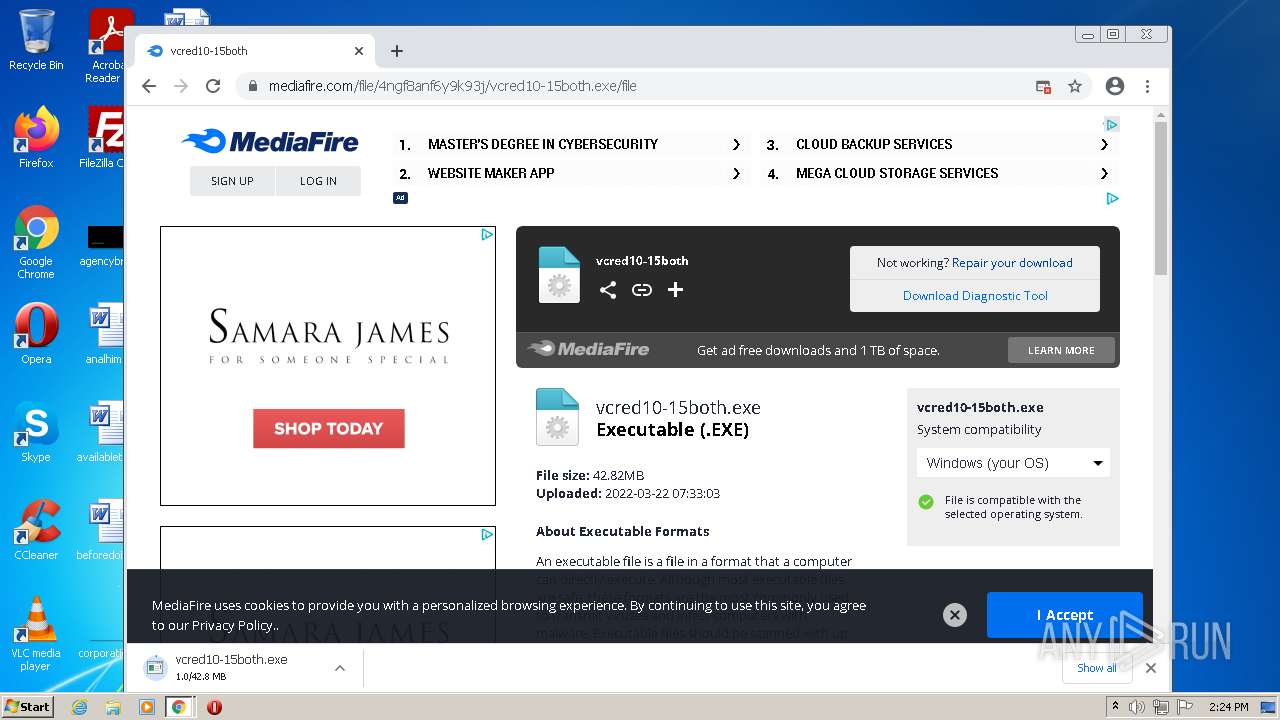
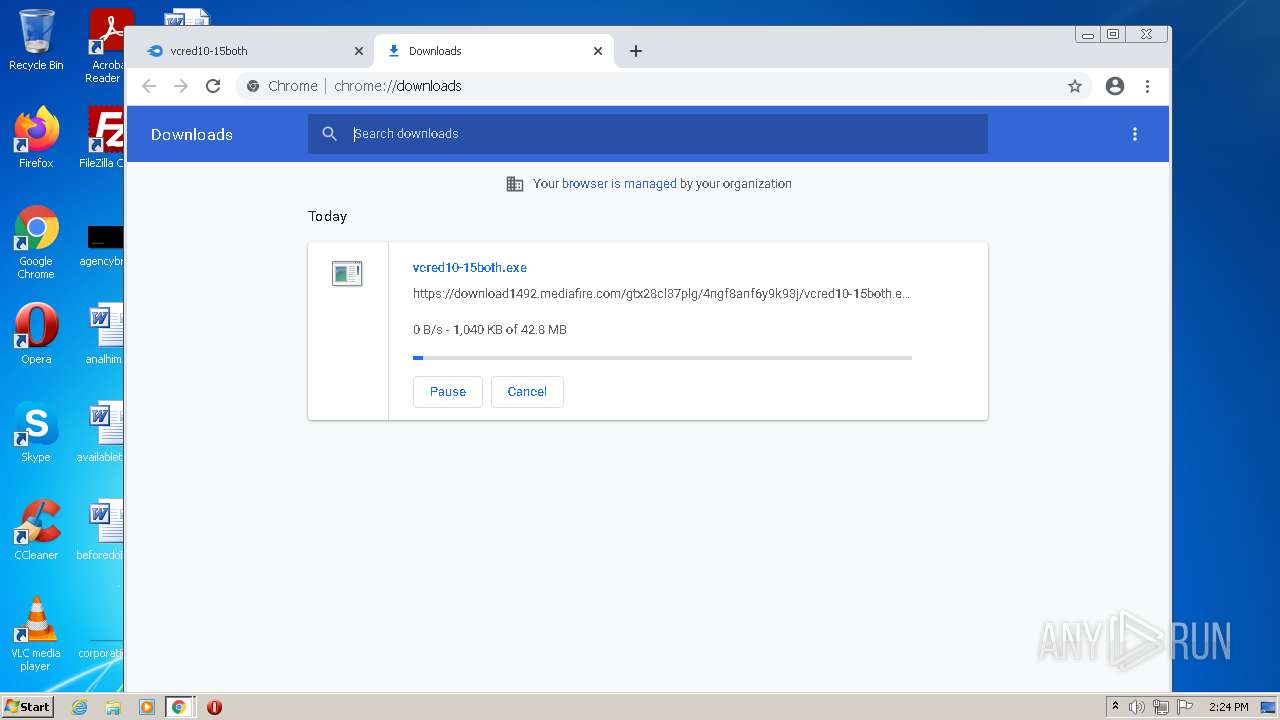
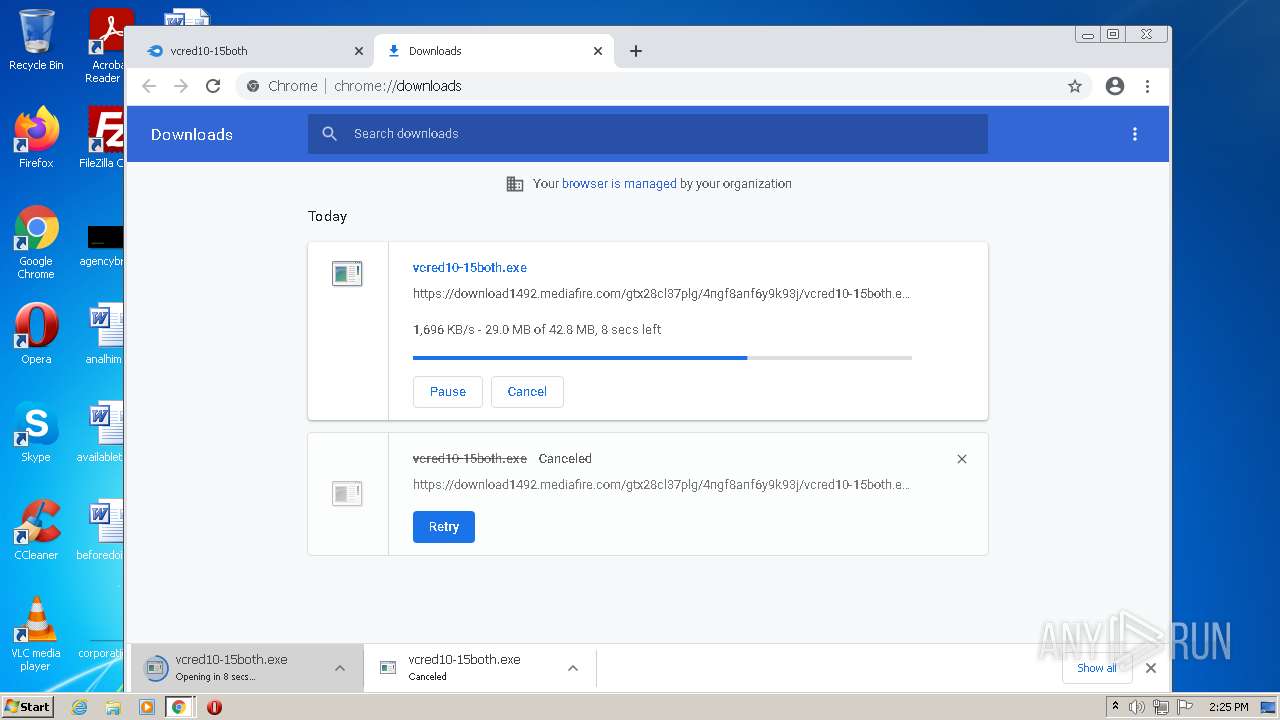
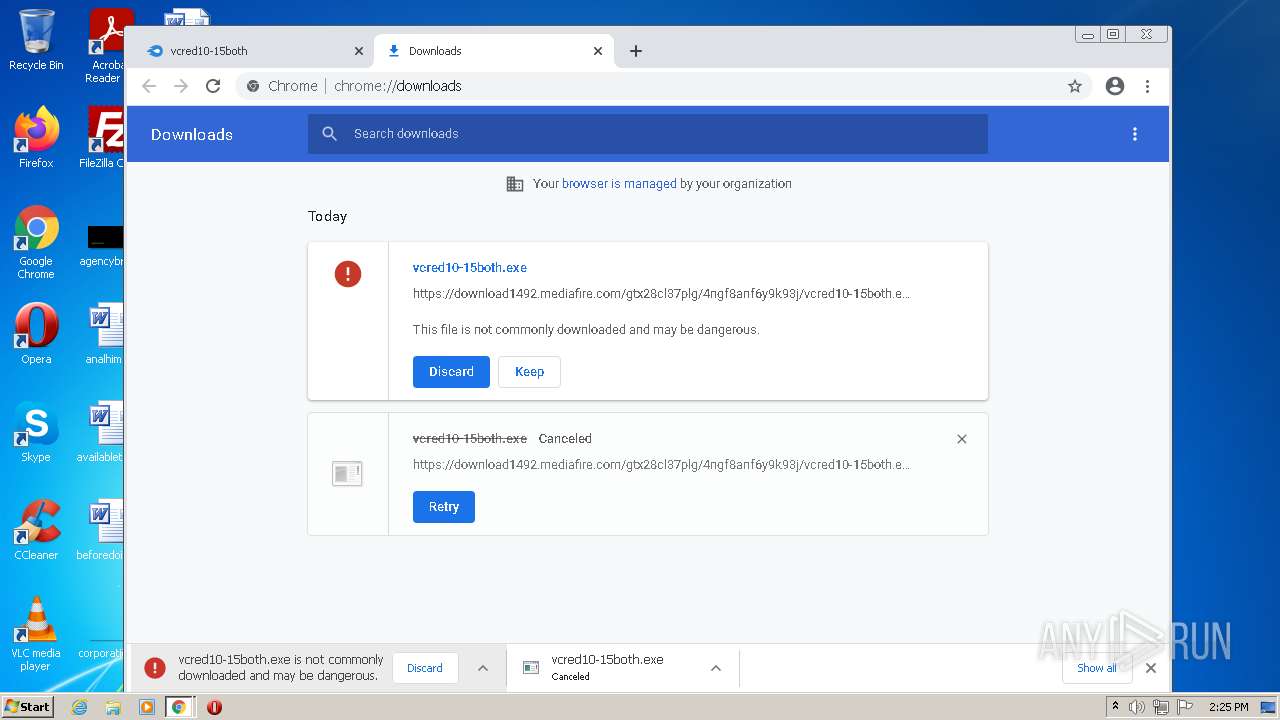
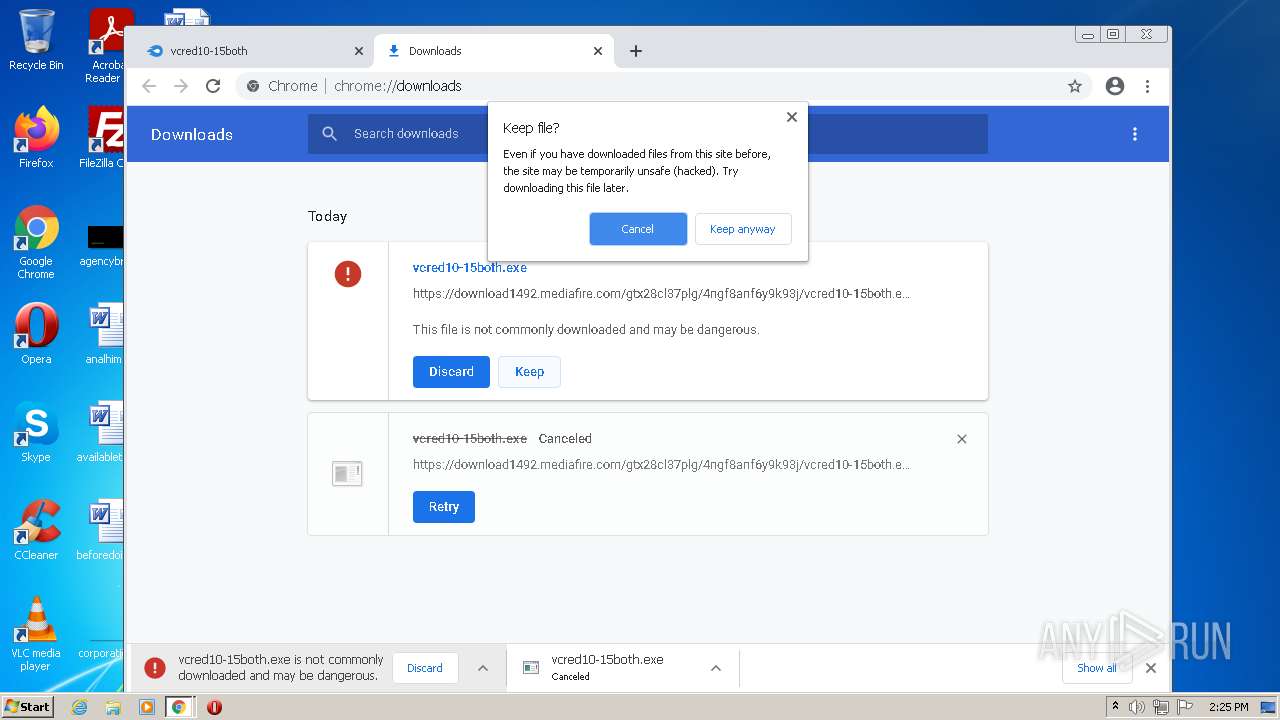
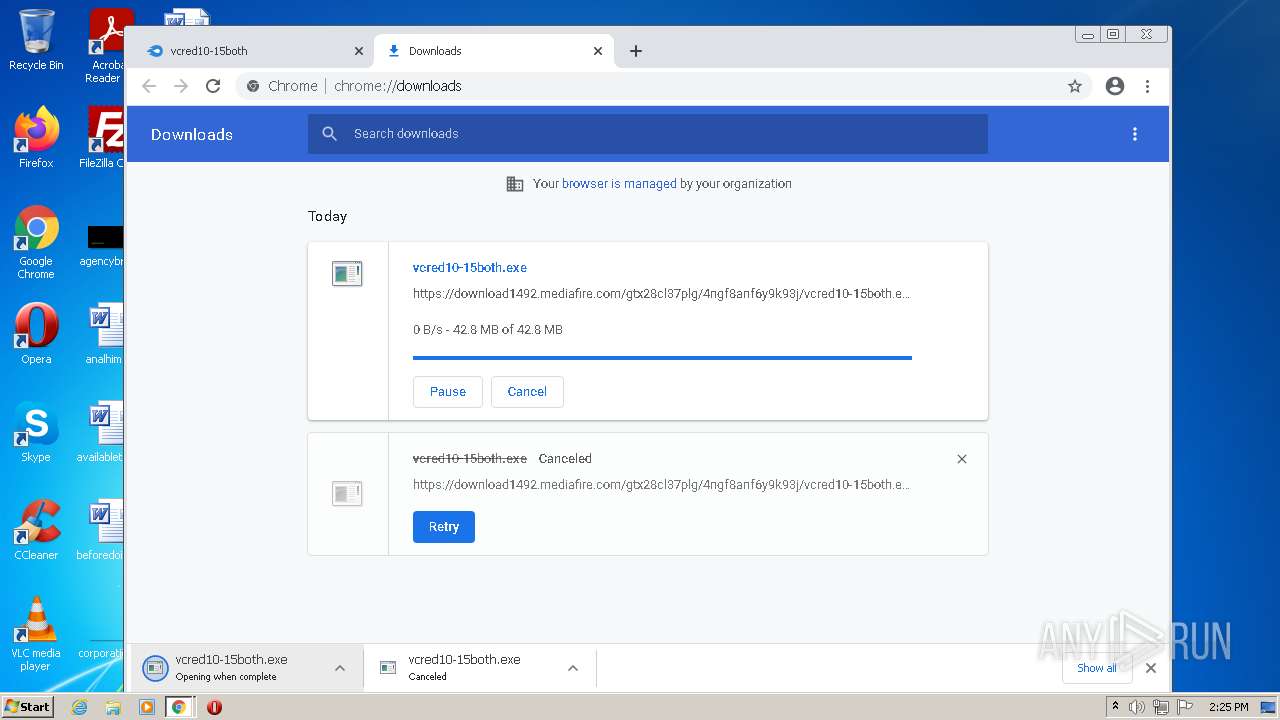
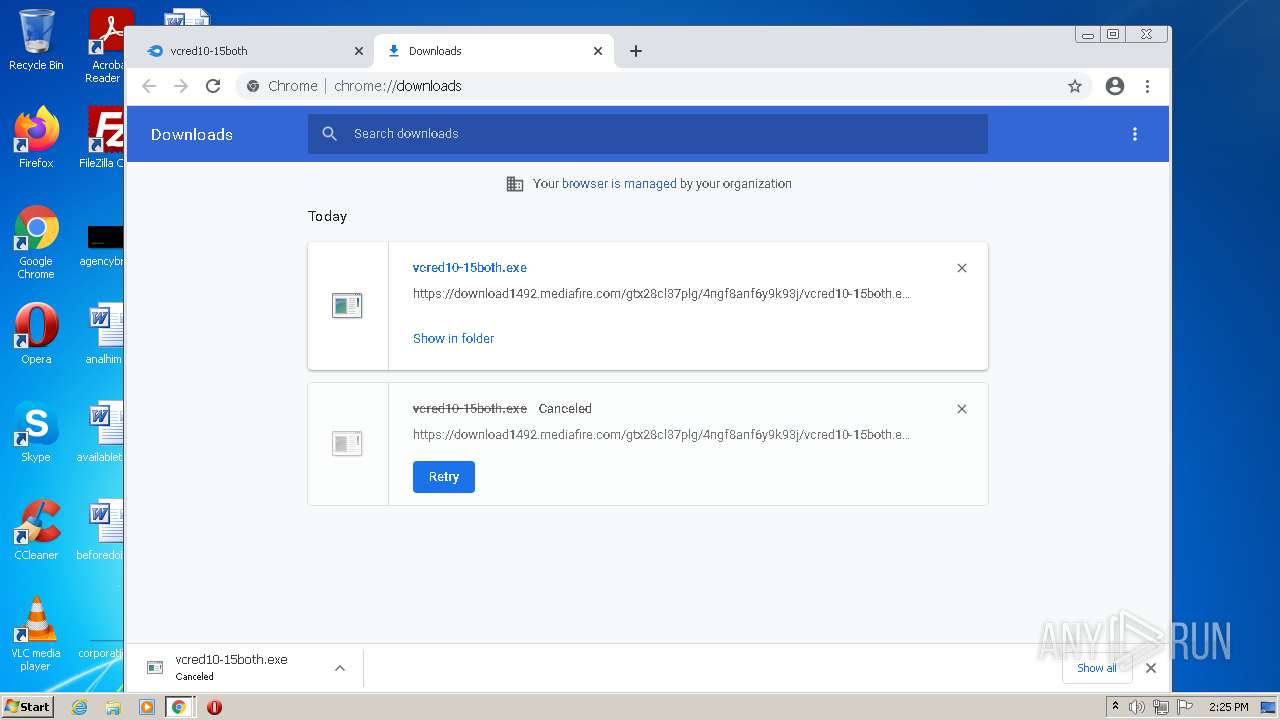
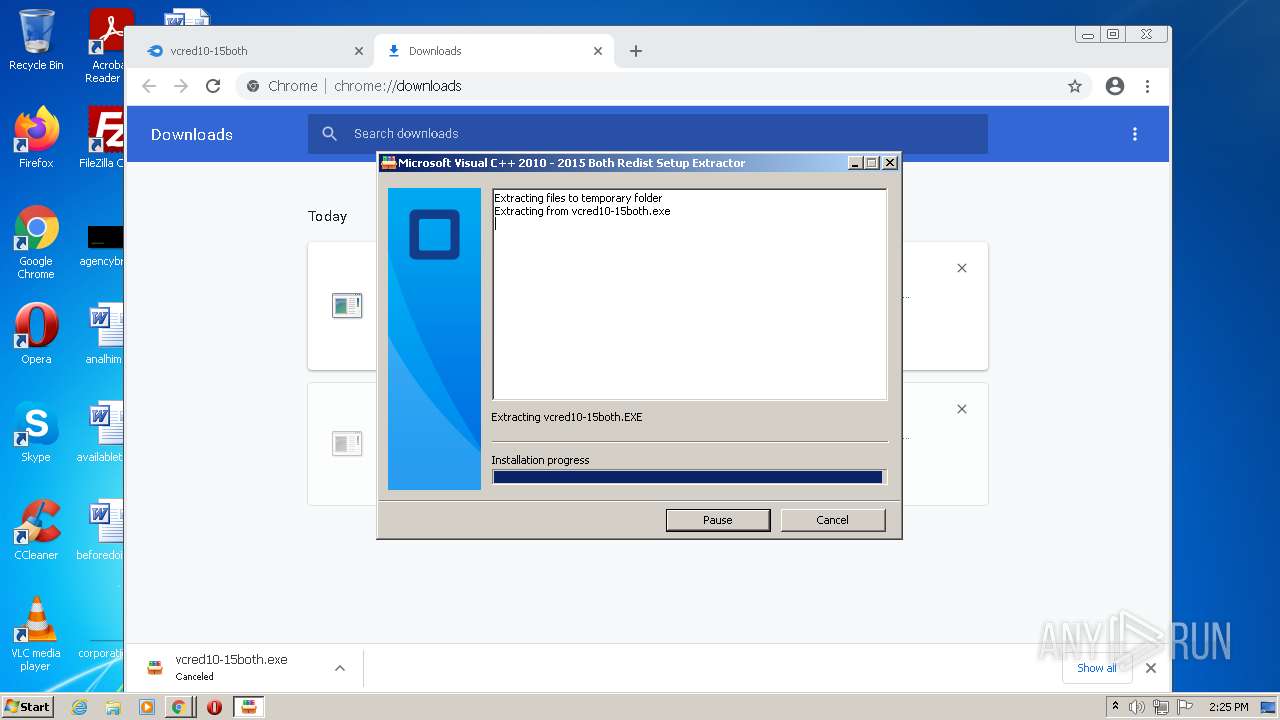
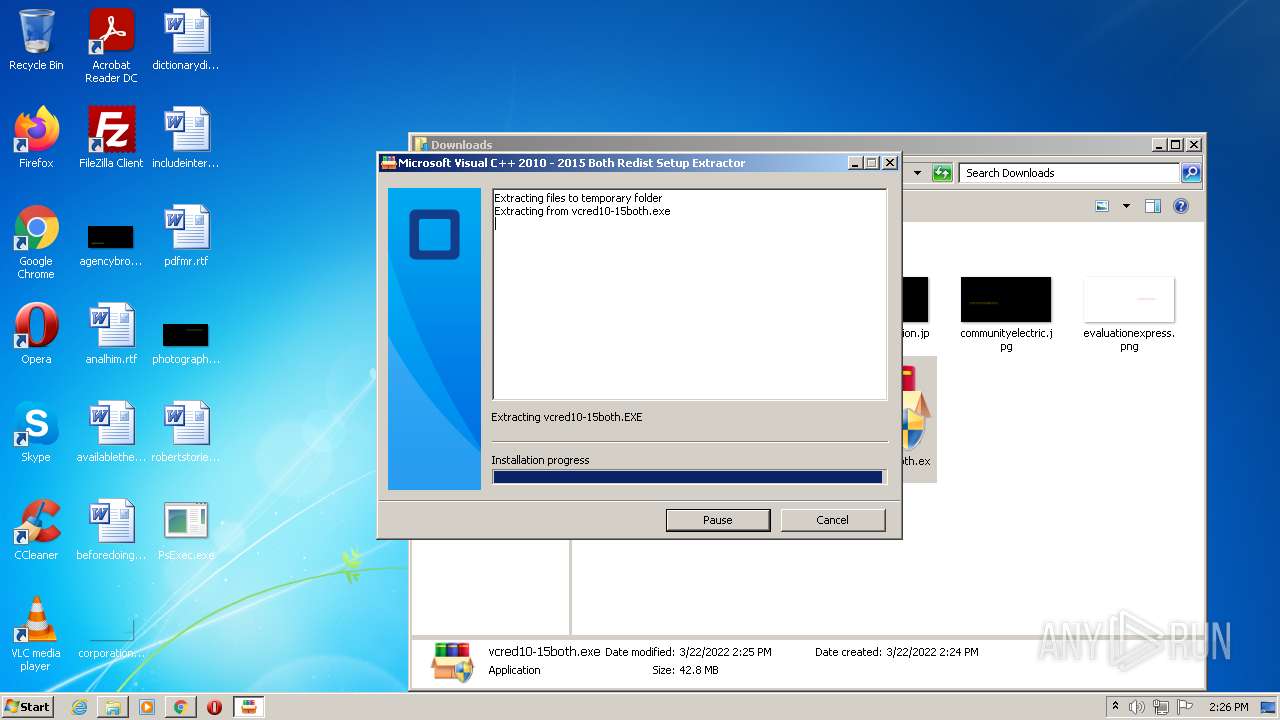
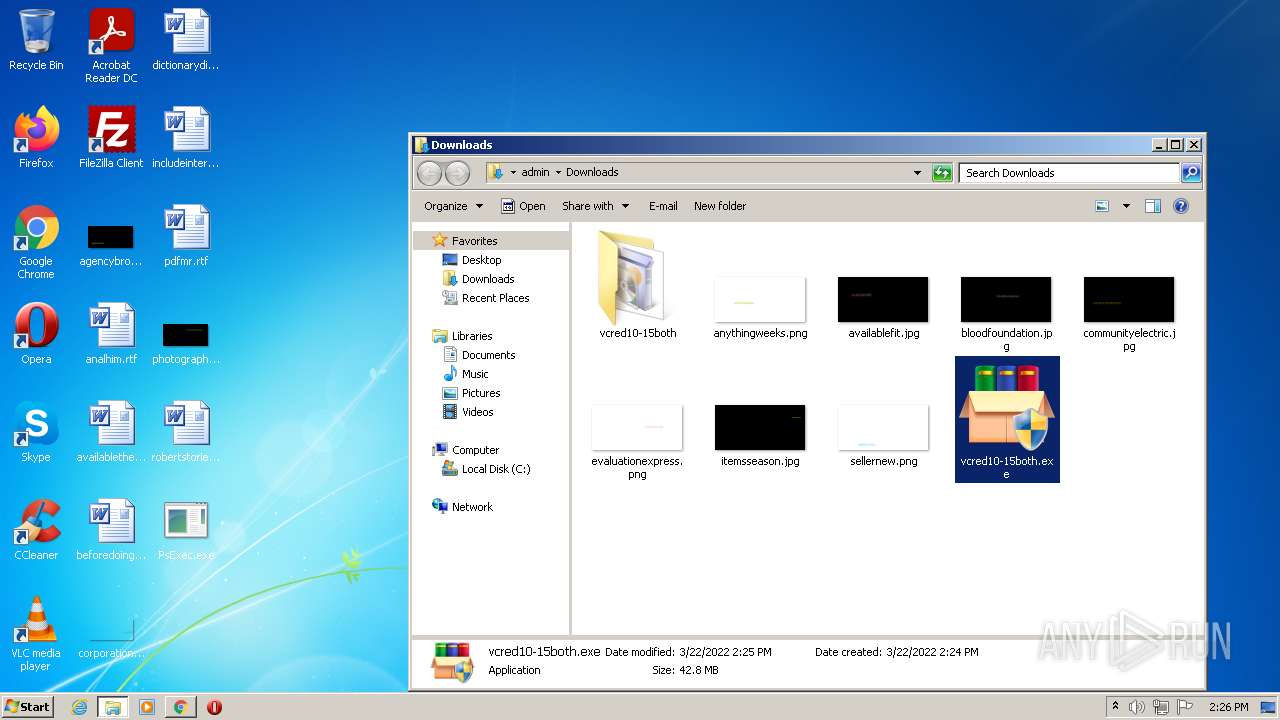
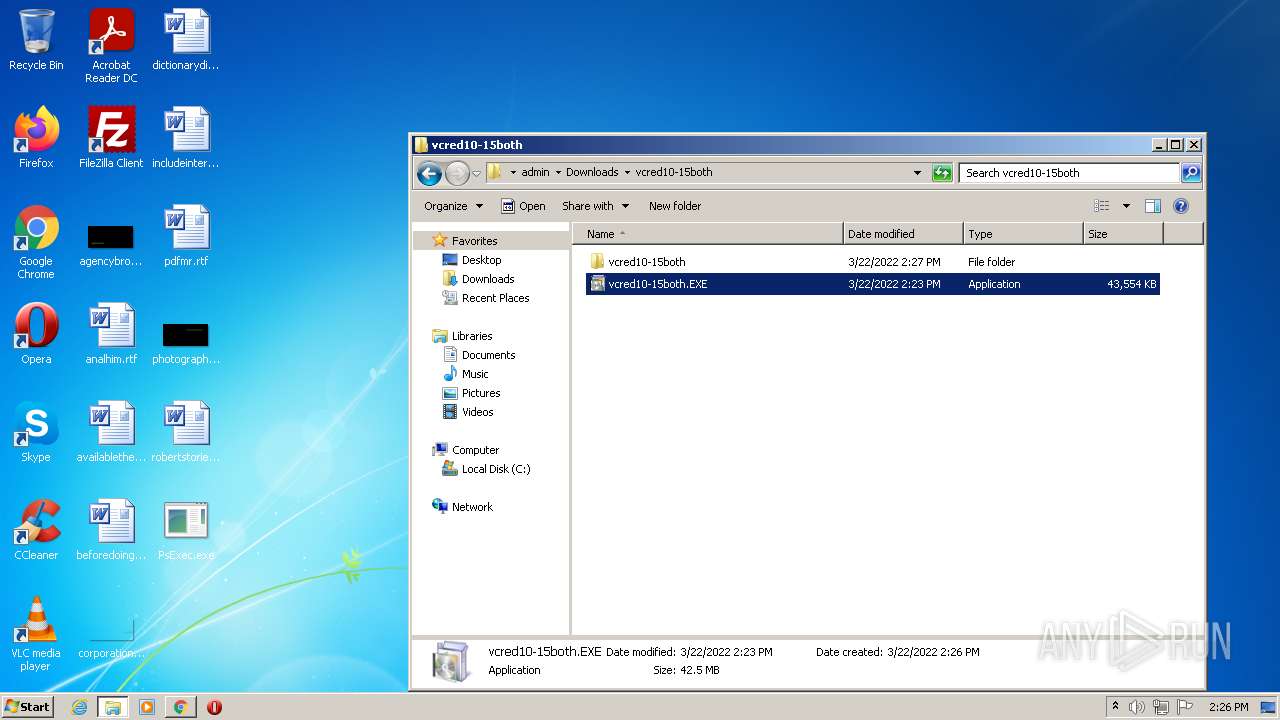
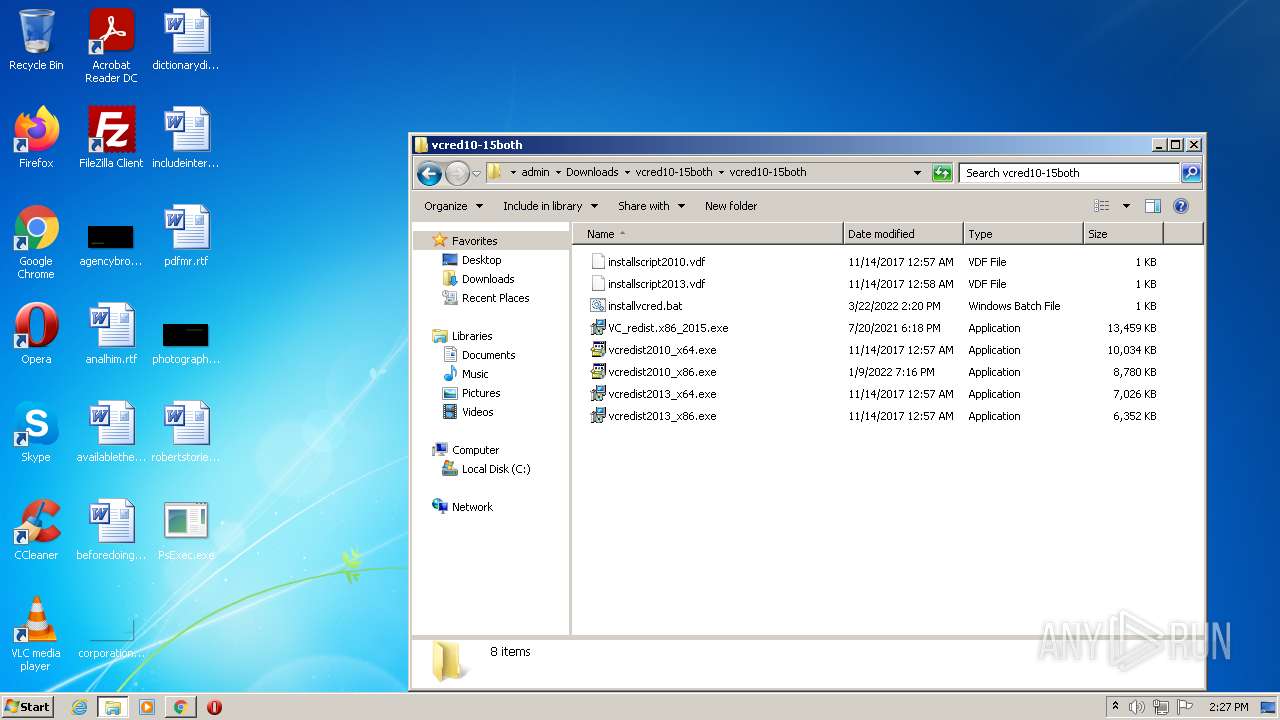
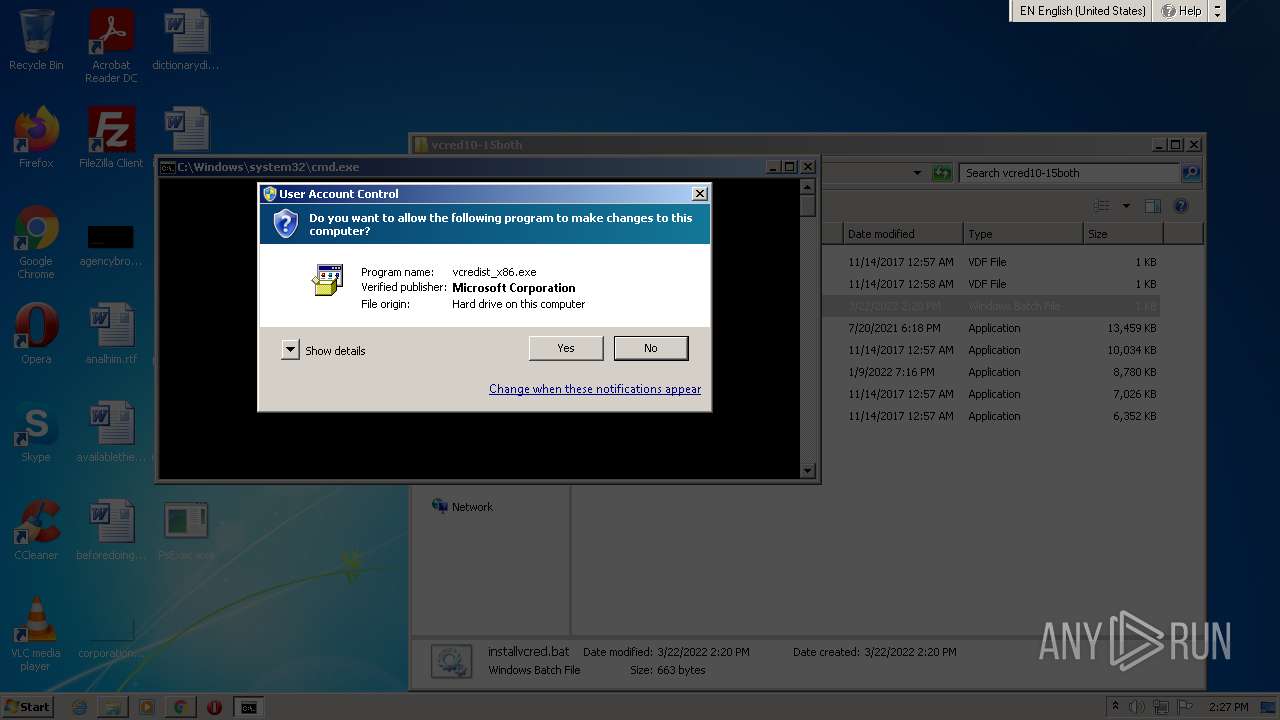
Application was dropped or rewritten from another process
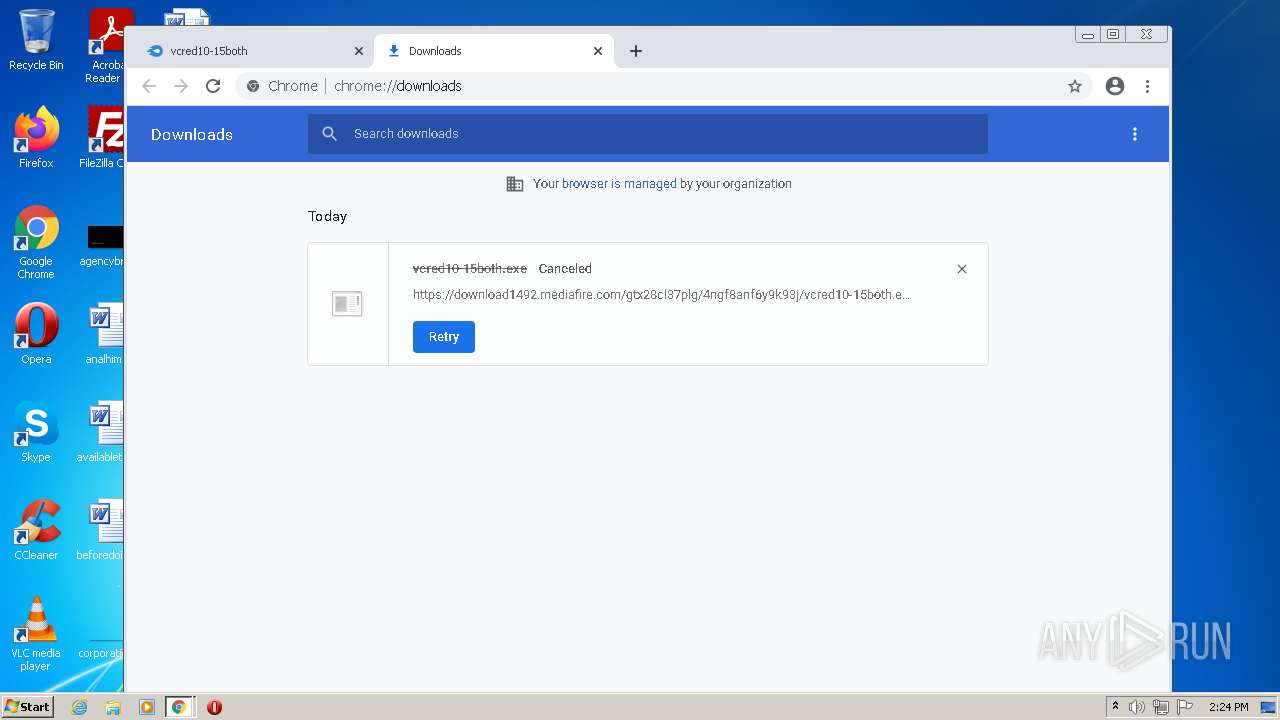
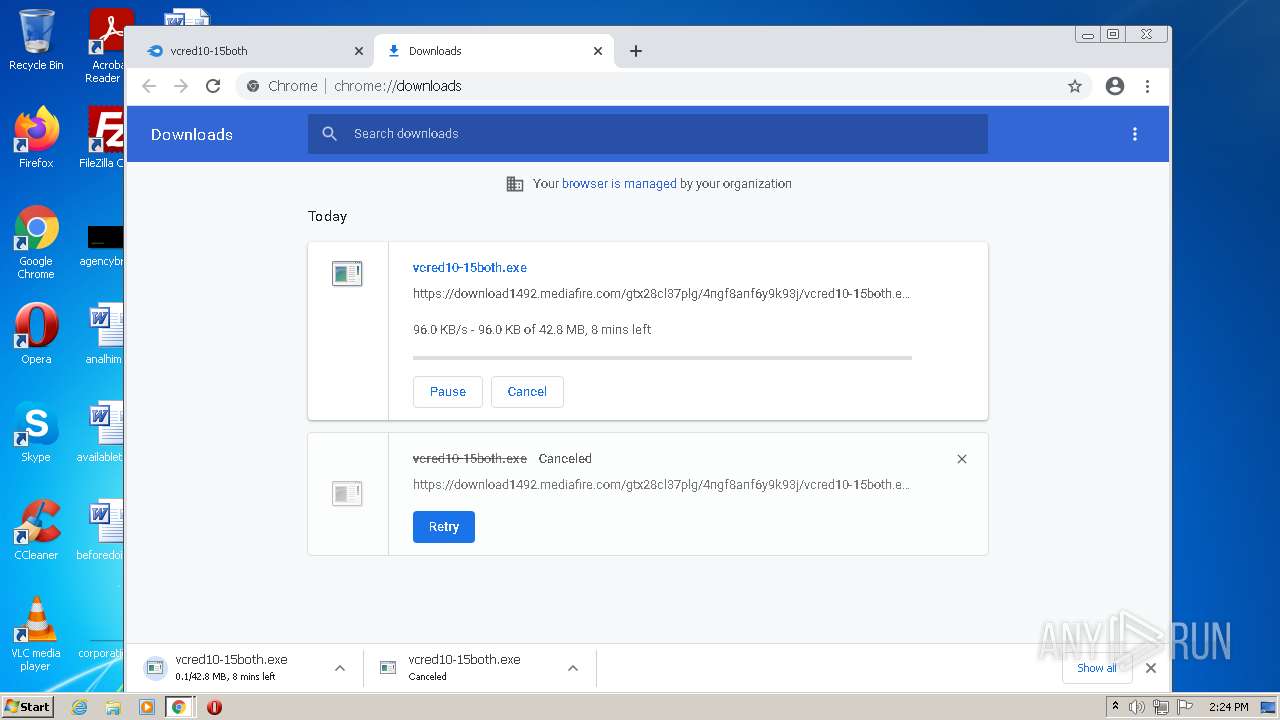
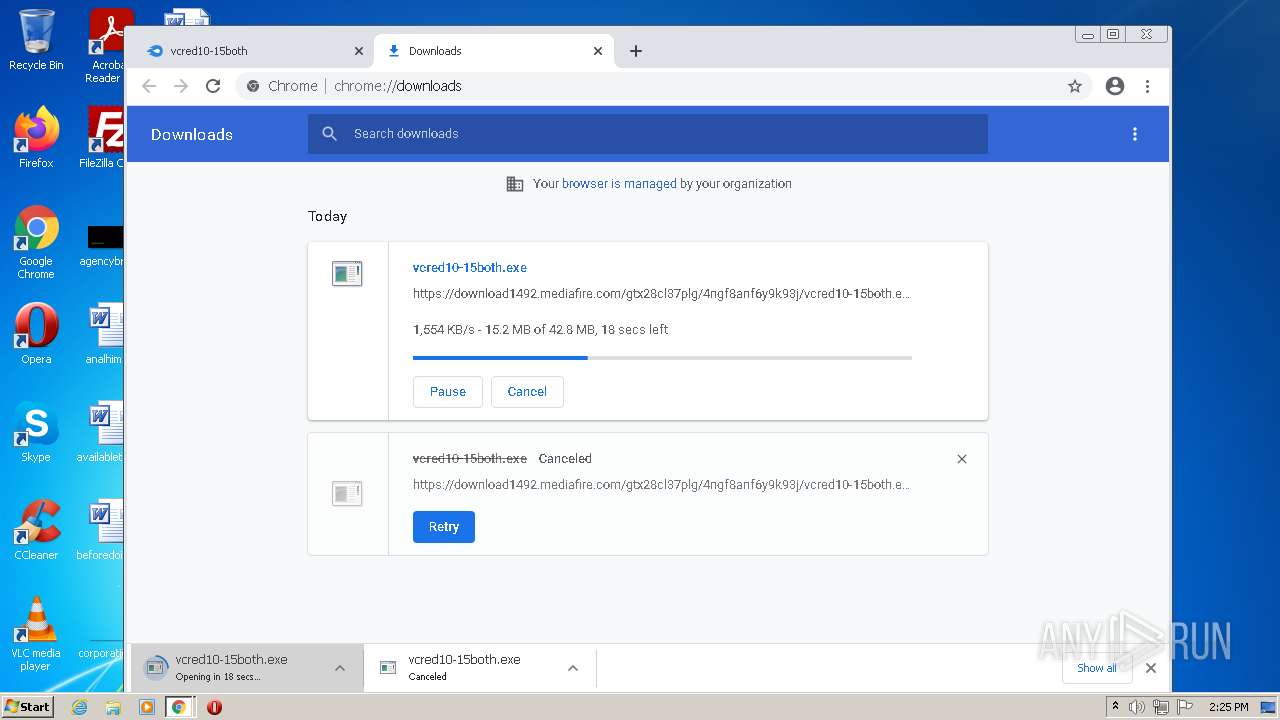
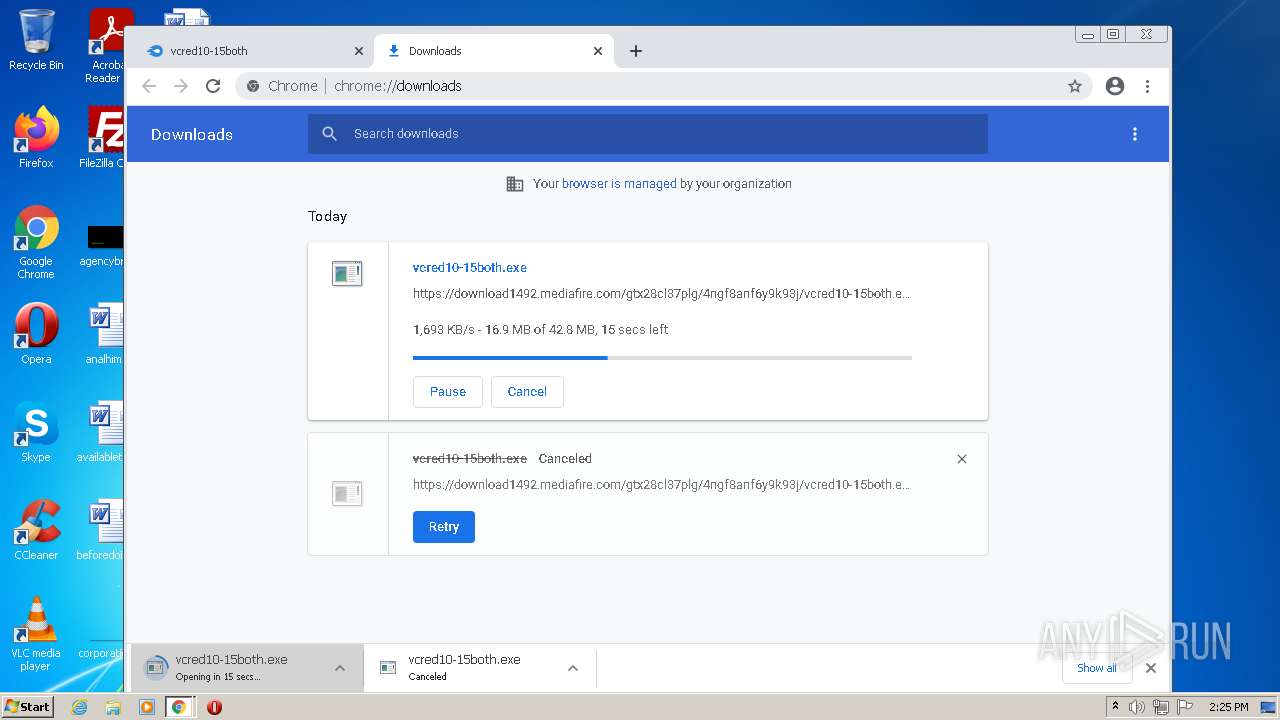
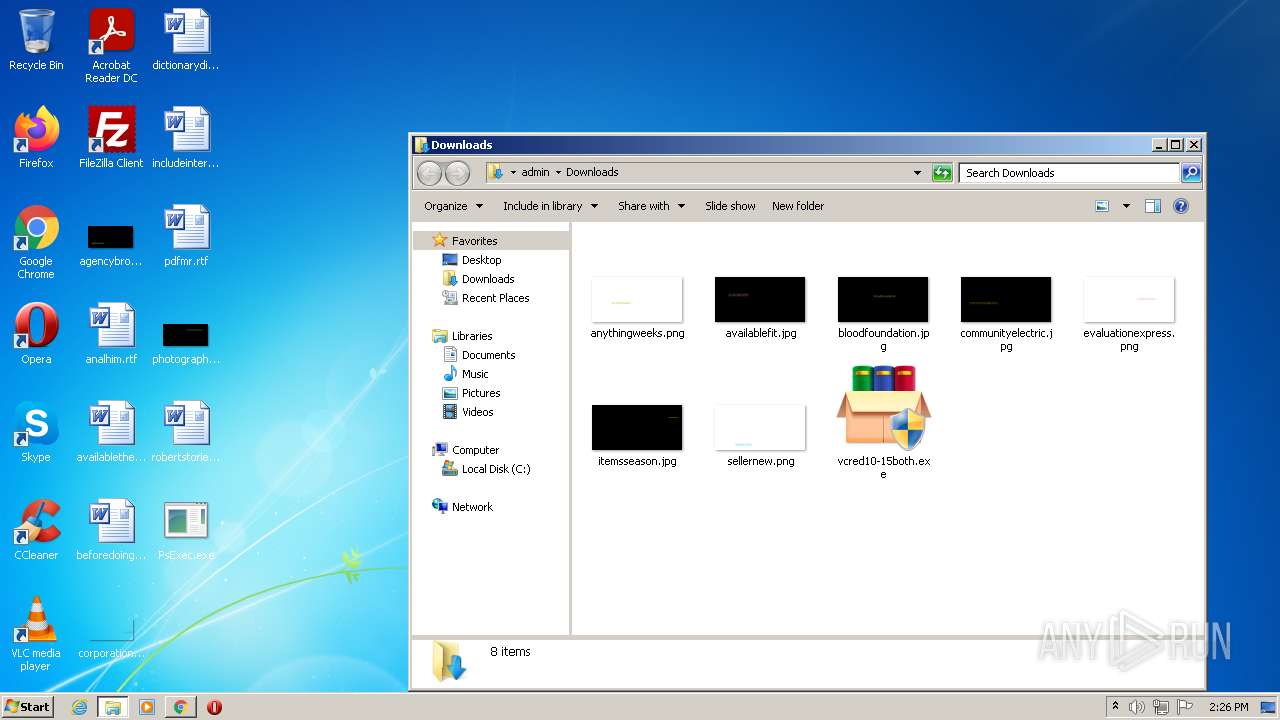
- vcred10-15both.exe (PID: 6048)
- vcred10-15both.exe (PID: 5372)
- vcred10-15both.exe (PID: 5168)
- vcredist2010_x64.exe (PID: 4936)
- vcredist2010_x64.exe (PID: 2124)
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 5280)
- vcredist2010_x86.exe (PID: 1768)
- Setup.exe (PID: 4172)
- vcredist2010_x86.exe (PID: 3036)
- vcred10-15both.exe (PID: 1532)
- Setup.exe (PID: 1708)
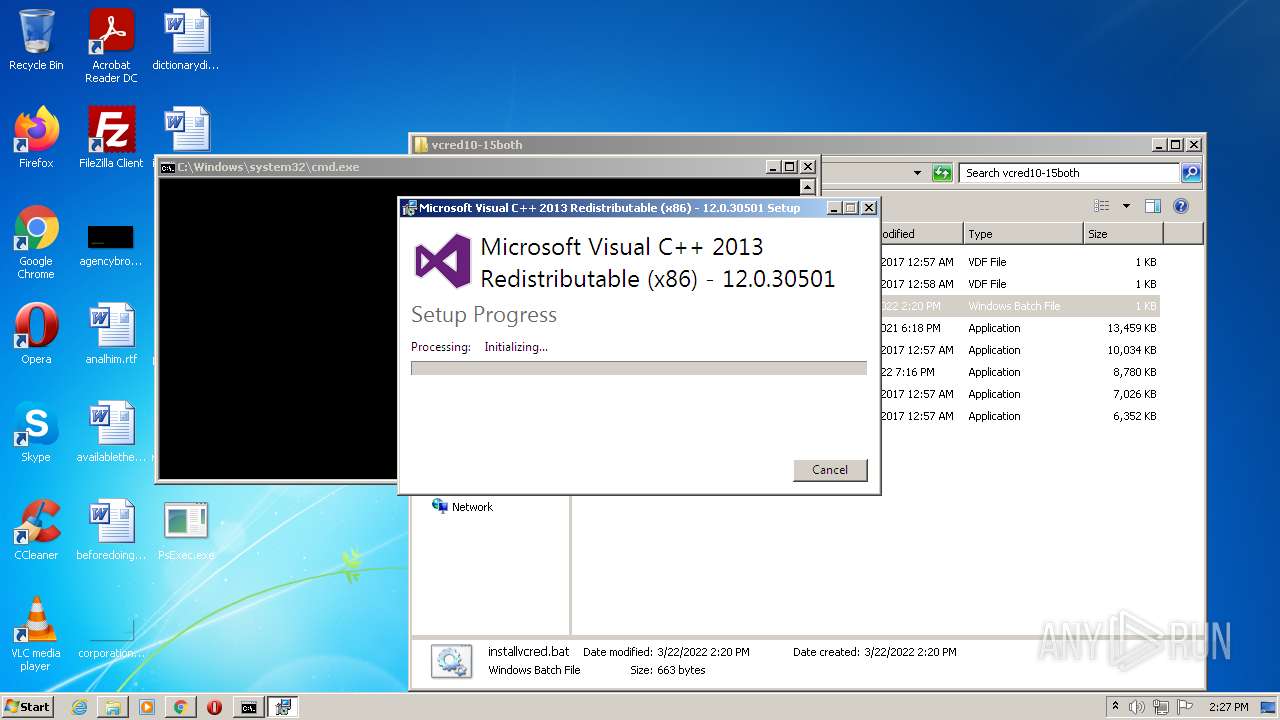
- vcredist2013_x64.exe (PID: 4384)
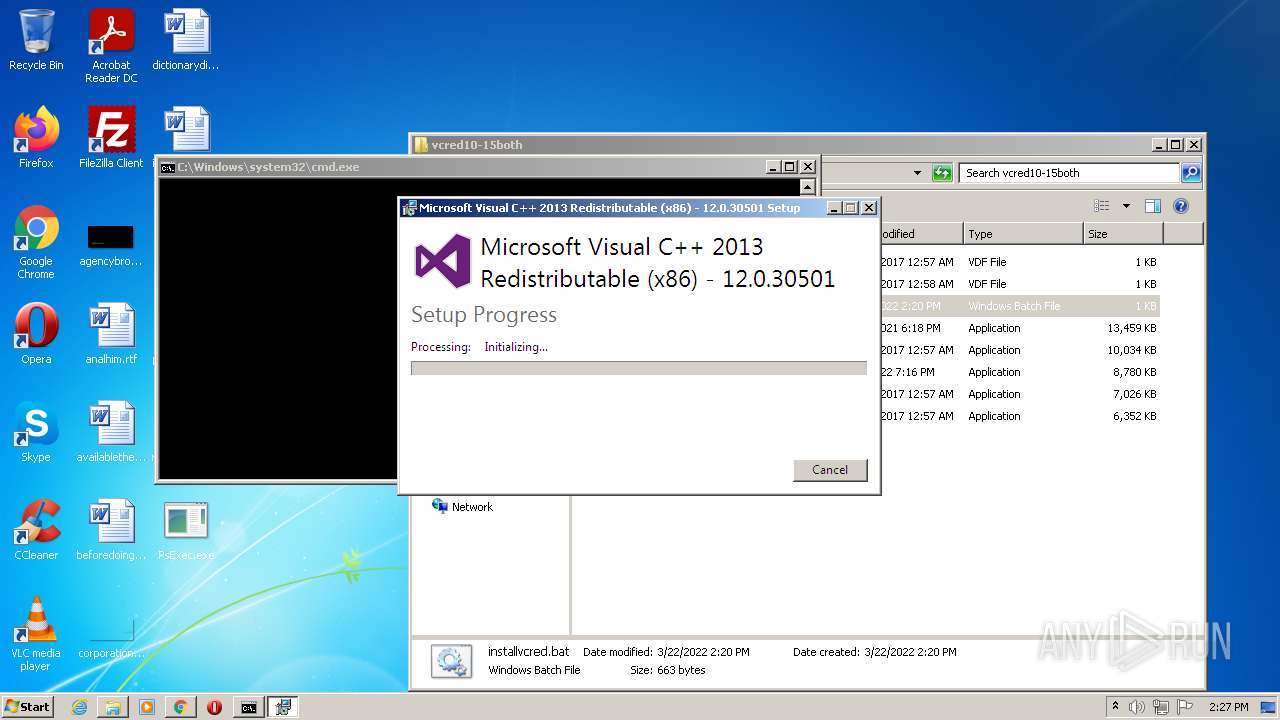
- vcredist2013_x86.exe (PID: 4612)
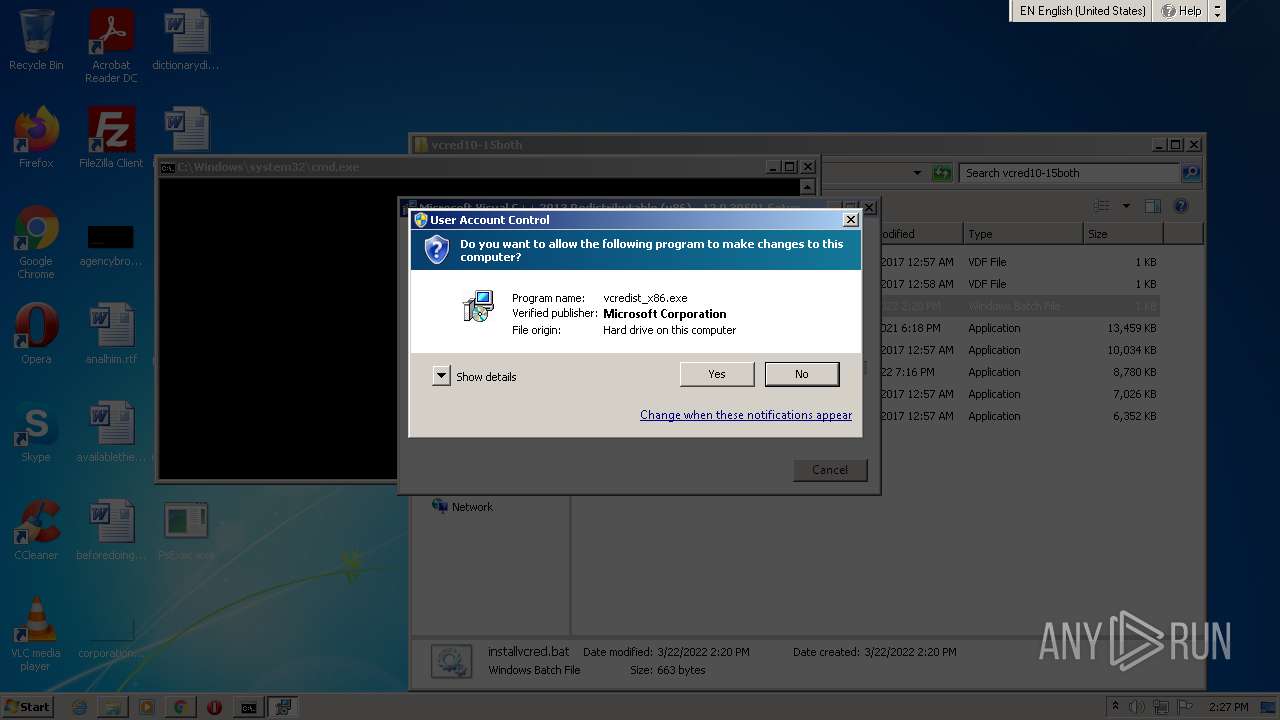
- vcredist_x86.exe (PID: 3760)
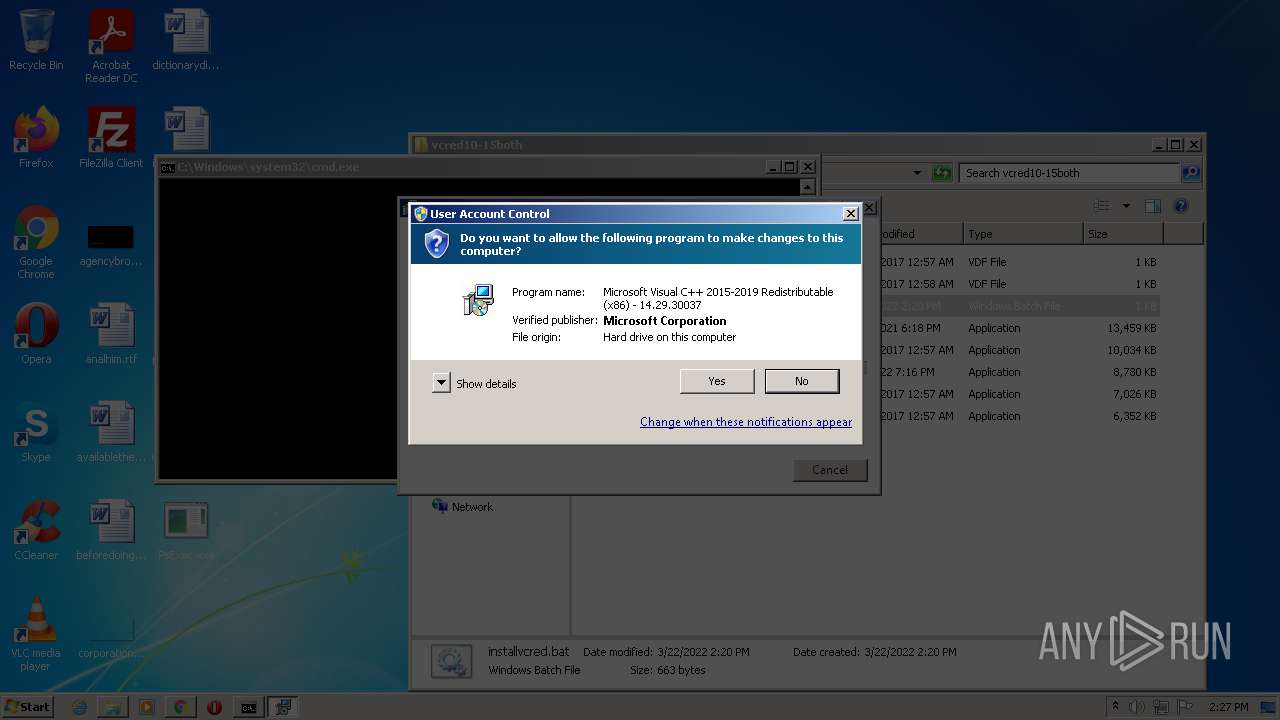
- VC_redist.x86_2015.exe (PID: 4148)
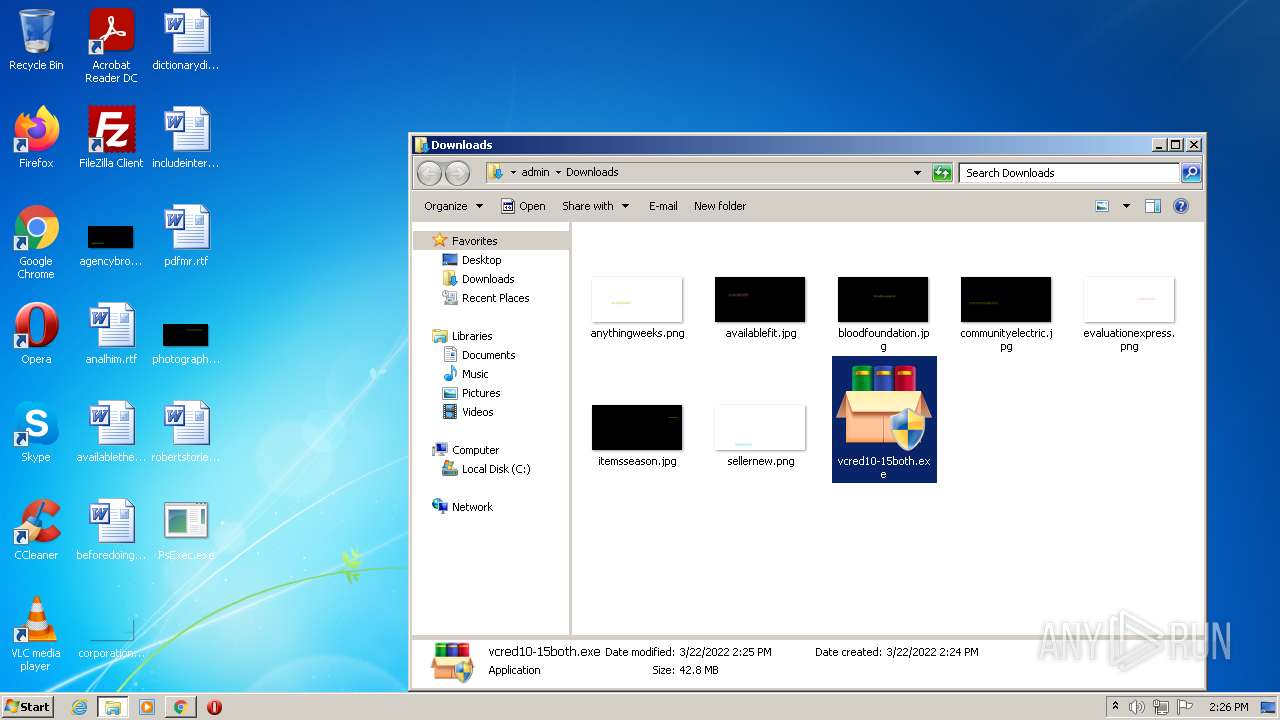
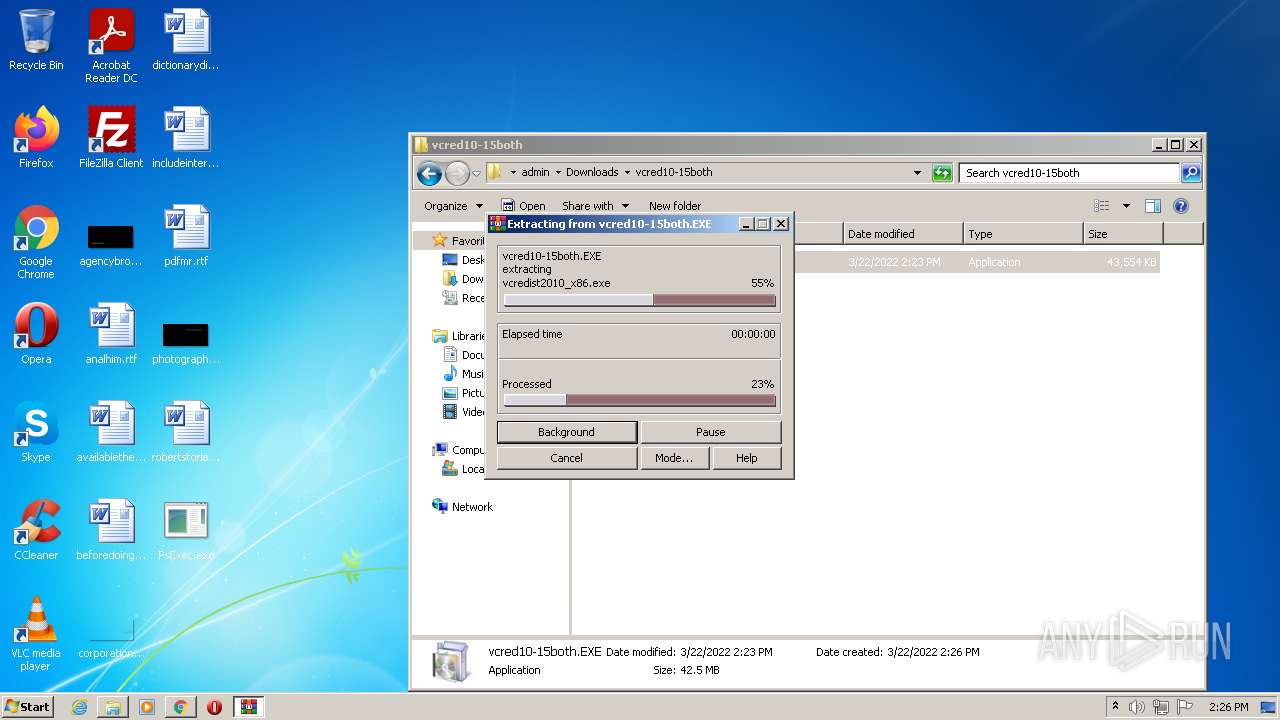
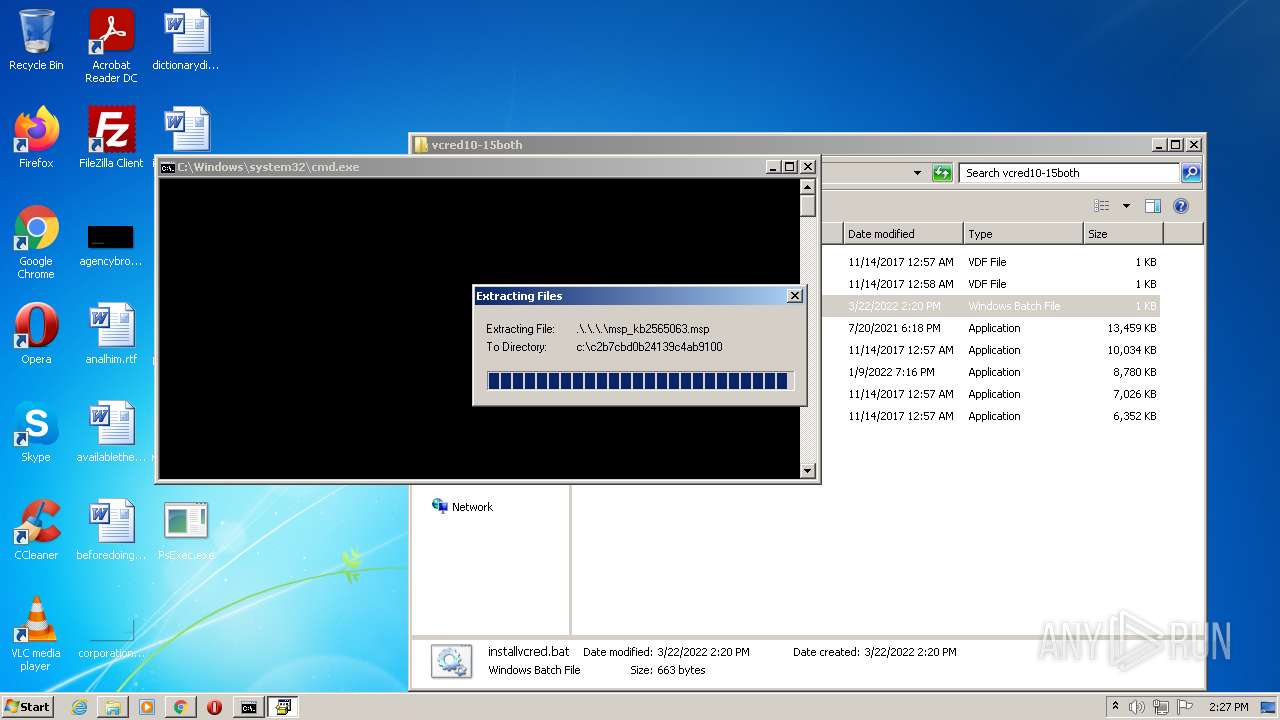
Drops executable file immediately after starts
- chrome.exe (PID: 6016)
- WinRAR.exe (PID: 4392)
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 3036)
- vcredist2013_x64.exe (PID: 4384)
- vcredist2013_x86.exe (PID: 4612)
Actions looks like stealing of personal data
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 3036)
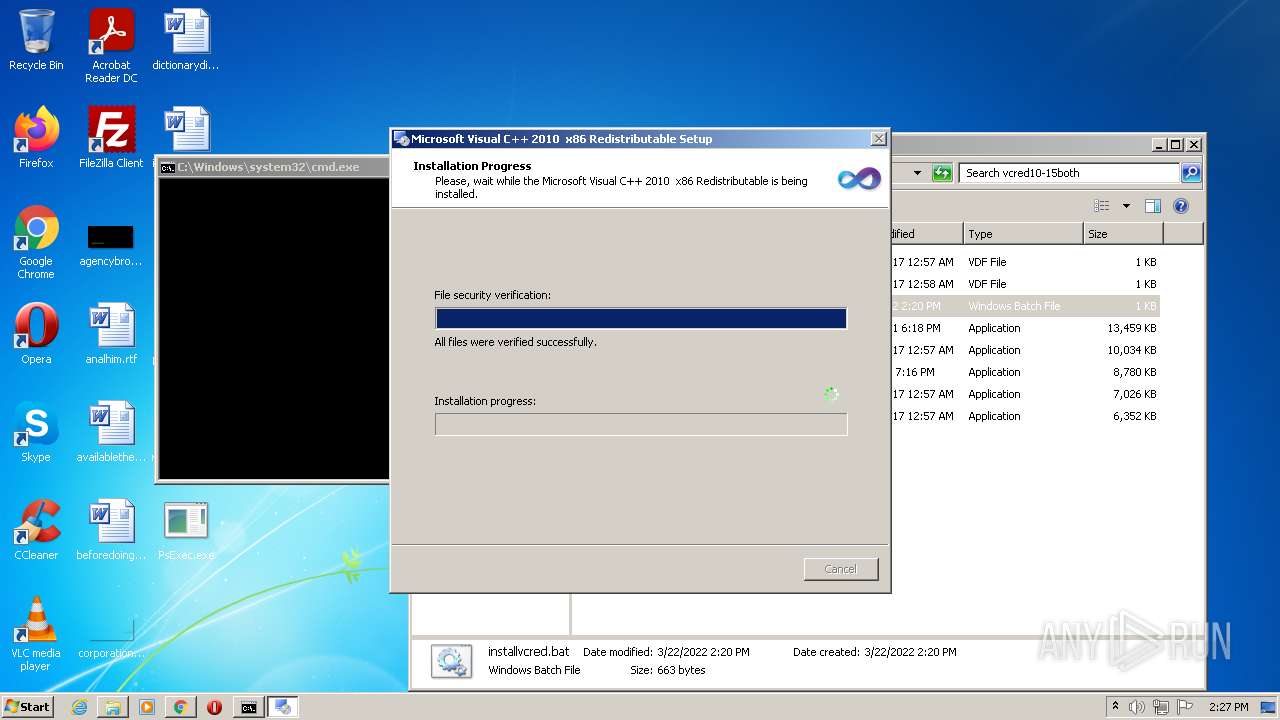
Loads dropped or rewritten executable
- Setup.exe (PID: 4172)
- Setup.exe (PID: 1708)
- vcredist2013_x64.exe (PID: 4384)
- vcredist2013_x86.exe (PID: 4612)
SUSPICIOUS
Reads the computer name
- PsExec.exe (PID: 3972)
- cmd.exe (PID: 1548)
- vcred10-15both.exe (PID: 5372)
- mshta.exe (PID: 5332)
- vcred10-15both.exe (PID: 5168)
- mshta.exe (PID: 5600)
- WinRAR.exe (PID: 4392)
- WinRAR.exe (PID: 2440)
- cmd.exe (PID: 4884)
- vcredist2010_x64.exe (PID: 5960)
- Setup.exe (PID: 4172)
- vcredist2010_x86.exe (PID: 3036)
- vcredist2013_x64.exe (PID: 4384)
- vcredist2013_x86.exe (PID: 4612)
- vcredist_x86.exe (PID: 3760)
- Setup.exe (PID: 1708)
Checks supported languages
- cmd.exe (PID: 1548)
- PsExec.exe (PID: 3972)
- vcred10-15both.exe (PID: 5372)
- mshta.exe (PID: 5332)
- vcred10-15both.exe (PID: 5168)
- mshta.exe (PID: 5600)
- WinRAR.exe (PID: 4392)
- cmd.exe (PID: 4884)
- vcredist2010_x64.exe (PID: 5960)
- Setup.exe (PID: 4172)
- vcredist2010_x86.exe (PID: 3036)
- Setup.exe (PID: 1708)
- vcredist2013_x86.exe (PID: 4612)
- vcredist_x86.exe (PID: 3760)
- vcredist2013_x64.exe (PID: 4384)
- WinRAR.exe (PID: 2440)
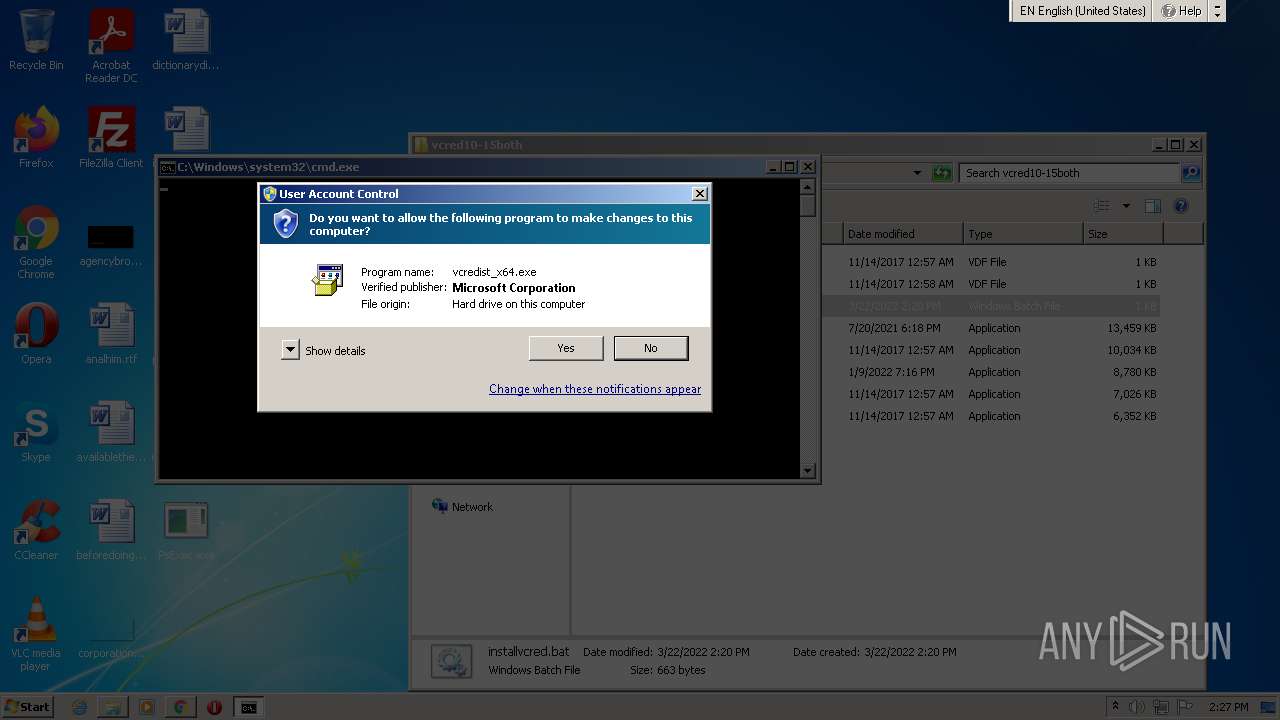
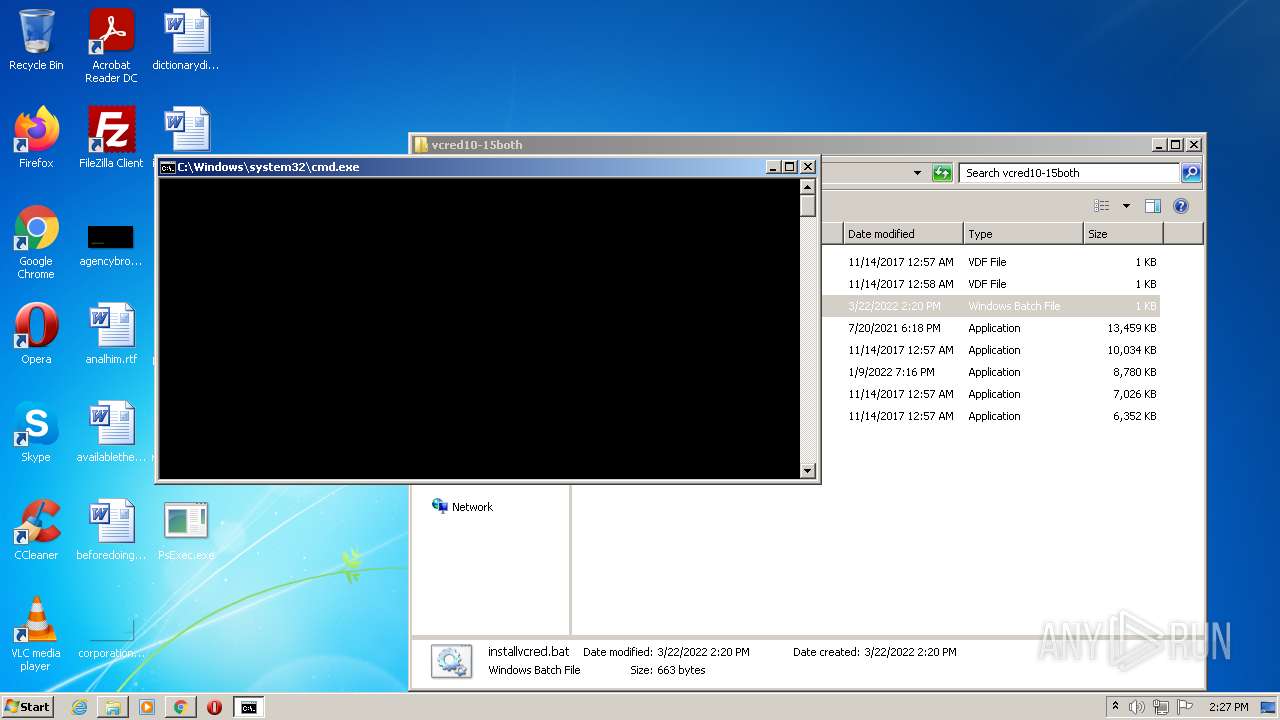
Starts CMD.EXE for commands execution
- PsExec.exe (PID: 3972)
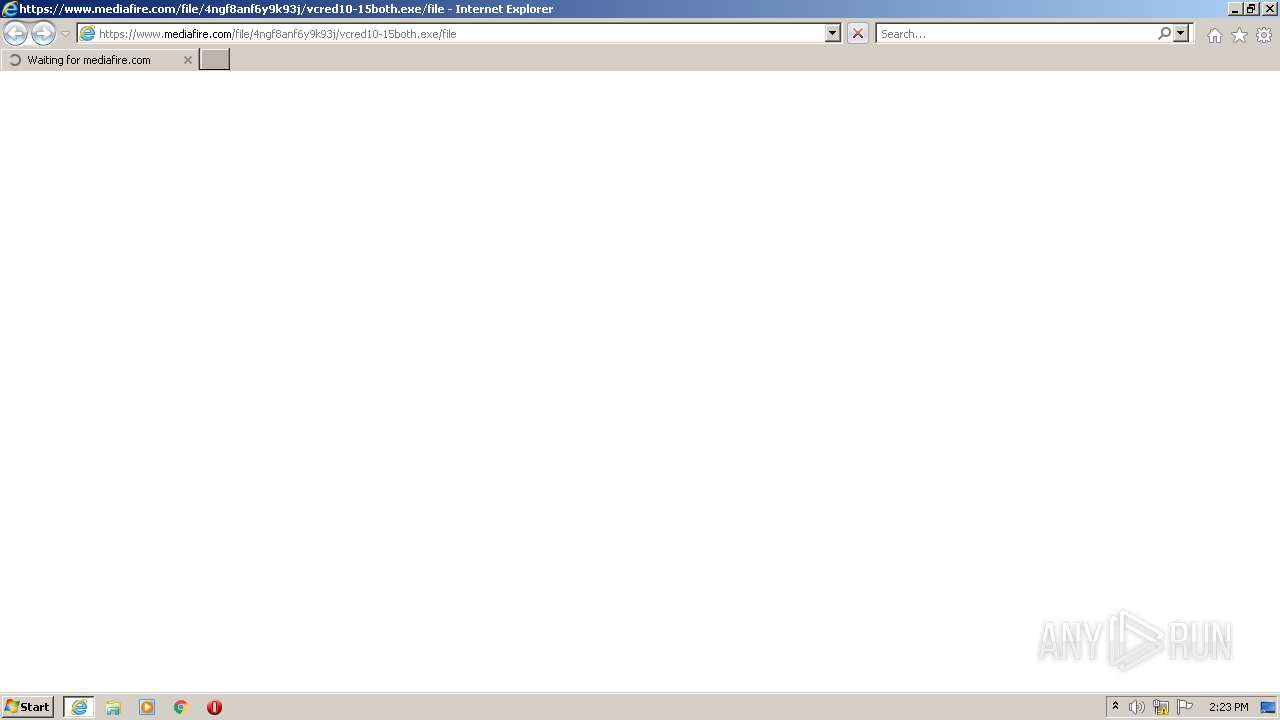
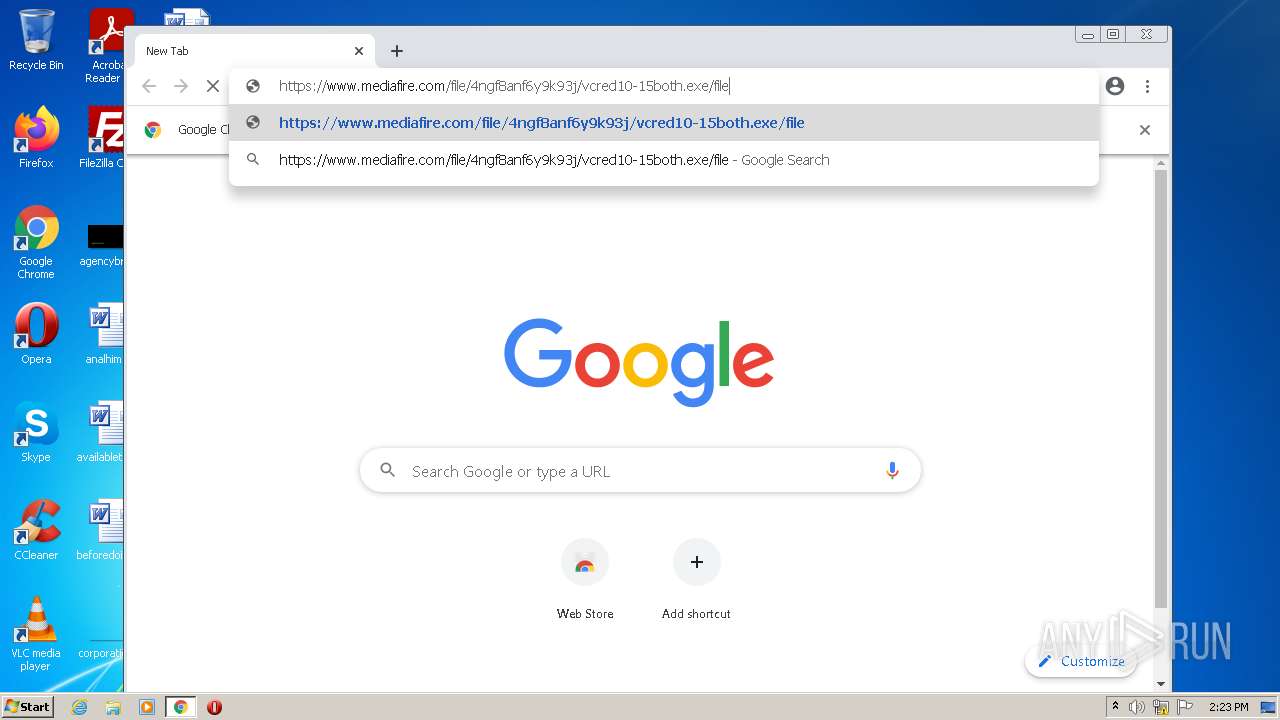
Starts Internet Explorer
- cmd.exe (PID: 1548)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2600)
- mshta.exe (PID: 5332)
- mshta.exe (PID: 5600)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3252)
Starts MSHTA.EXE for opening HTA or HTMLS files
- vcred10-15both.exe (PID: 5372)
- vcred10-15both.exe (PID: 5168)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 6016)
- WinRAR.exe (PID: 4392)
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 3036)
- msiexec.exe (PID: 5164)
- vcredist2013_x86.exe (PID: 4612)
- vcredist2013_x64.exe (PID: 4384)
Executable content was dropped or overwritten
- chrome.exe (PID: 6016)
- WinRAR.exe (PID: 4392)
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 3036)
- msiexec.exe (PID: 5164)
- vcredist2013_x64.exe (PID: 4384)
- vcredist2013_x86.exe (PID: 4612)
Drops a file with too old compile date
- WinRAR.exe (PID: 4392)
- vcredist2010_x64.exe (PID: 5960)
- vcredist2010_x86.exe (PID: 3036)
Reads Environment values
- vcredist2010_x64.exe (PID: 5960)
- vssvc.exe (PID: 5184)
- vcredist2010_x86.exe (PID: 3036)
Reads CPU info
- Setup.exe (PID: 4172)
- Setup.exe (PID: 1708)
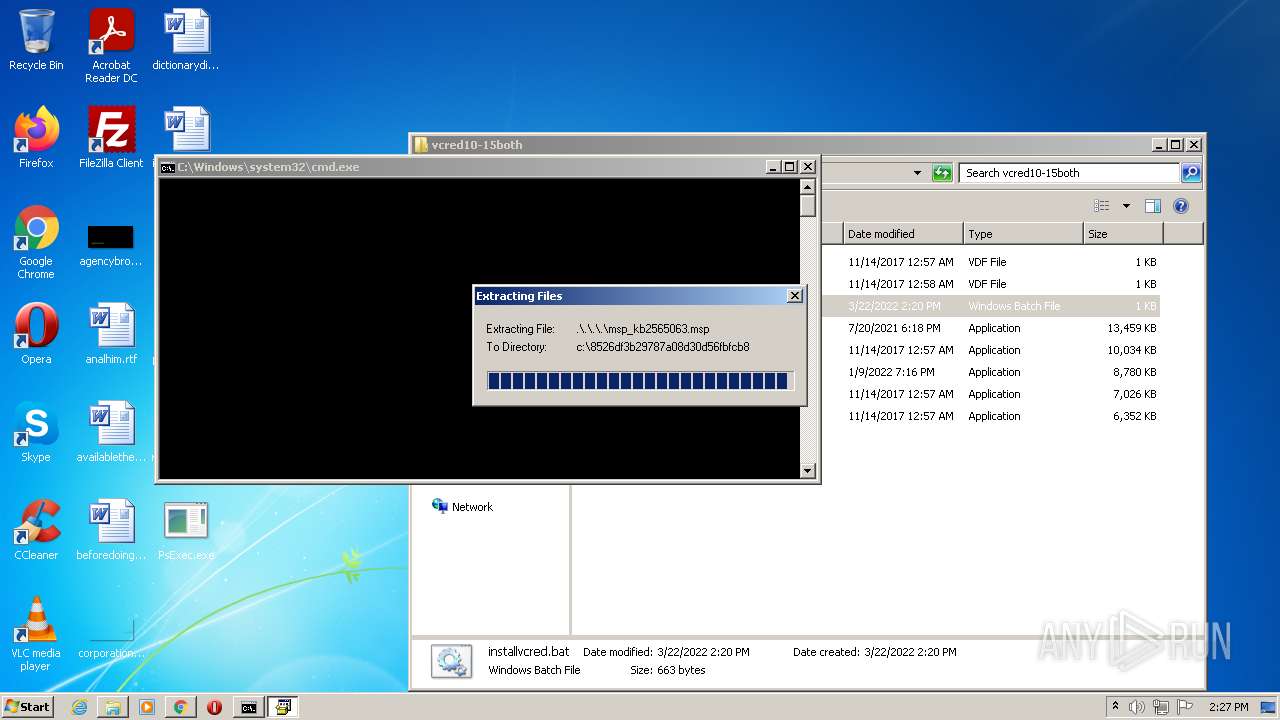
Executed as Windows Service
- msiexec.exe (PID: 5164)
- vssvc.exe (PID: 5184)
Reads the Windows organization settings
- msiexec.exe (PID: 5164)
Reads Windows owner or organization settings
- msiexec.exe (PID: 5164)
Creates files in the Windows directory
- msiexec.exe (PID: 5164)
Creates a software uninstall entry
- msiexec.exe (PID: 5164)
Searches for installed software
- msiexec.exe (PID: 5164)
- vcredist2013_x64.exe (PID: 4384)
- vcredist2013_x86.exe (PID: 4612)
- vcredist_x86.exe (PID: 3760)
Removes files from Windows directory
- msiexec.exe (PID: 5164)
INFO
Checks supported languages
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2600)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 964)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 1464)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 520)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 1032)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 1700)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 4484)
- chrome.exe (PID: 4292)
- chrome.exe (PID: 4792)
- chrome.exe (PID: 5520)
- chrome.exe (PID: 4208)
- chrome.exe (PID: 5000)
- chrome.exe (PID: 5760)
- chrome.exe (PID: 5728)
- chrome.exe (PID: 5776)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 6016)
- verclsid.exe (PID: 5712)
- chrome.exe (PID: 4652)
- chrome.exe (PID: 5188)
- chrome.exe (PID: 5756)
- msiexec.exe (PID: 5164)
- chrome.exe (PID: 3164)
- vssvc.exe (PID: 5184)
Reads the computer name
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2600)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 4484)
- chrome.exe (PID: 5760)
- chrome.exe (PID: 5000)
- msiexec.exe (PID: 5164)
- vssvc.exe (PID: 5184)
Reads settings of System Certificates
- iexplore.exe (PID: 2600)
- iexplore.exe (PID: 3496)
- chrome.exe (PID: 4012)
- Setup.exe (PID: 1708)
- msiexec.exe (PID: 5164)
Checks Windows Trust Settings
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2600)
- chrome.exe (PID: 3252)
- Setup.exe (PID: 1708)
- msiexec.exe (PID: 5164)
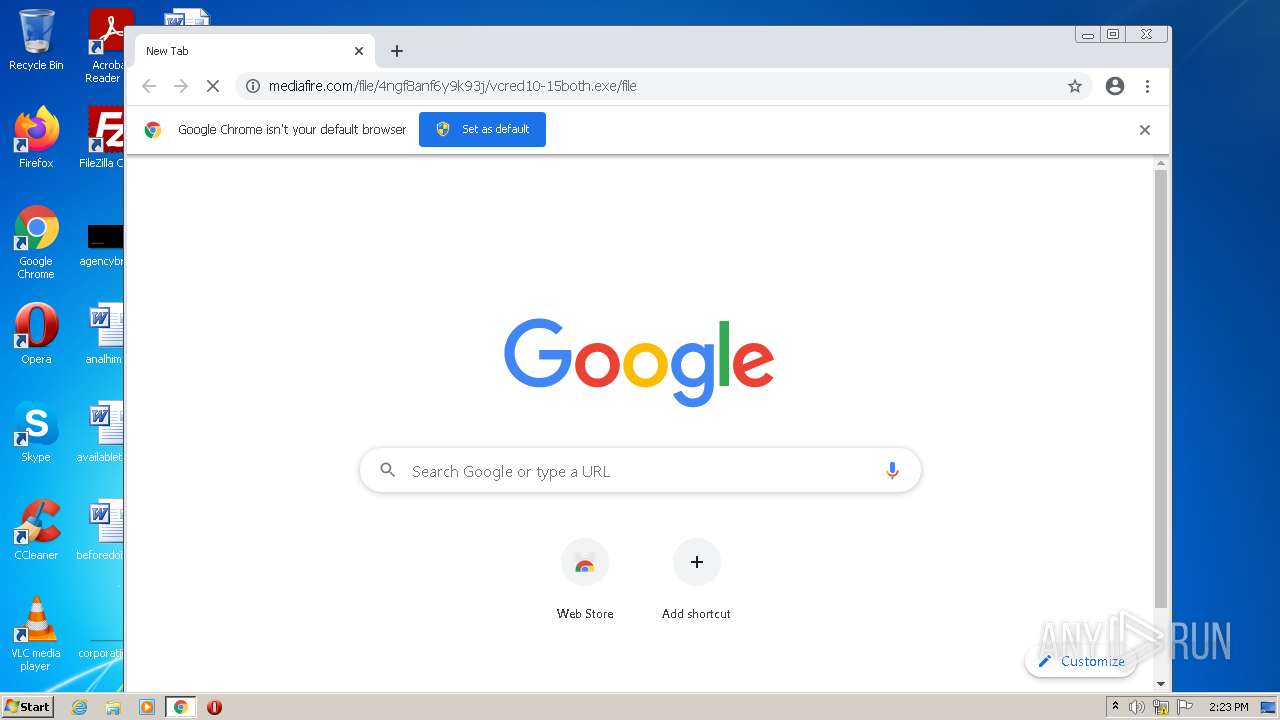
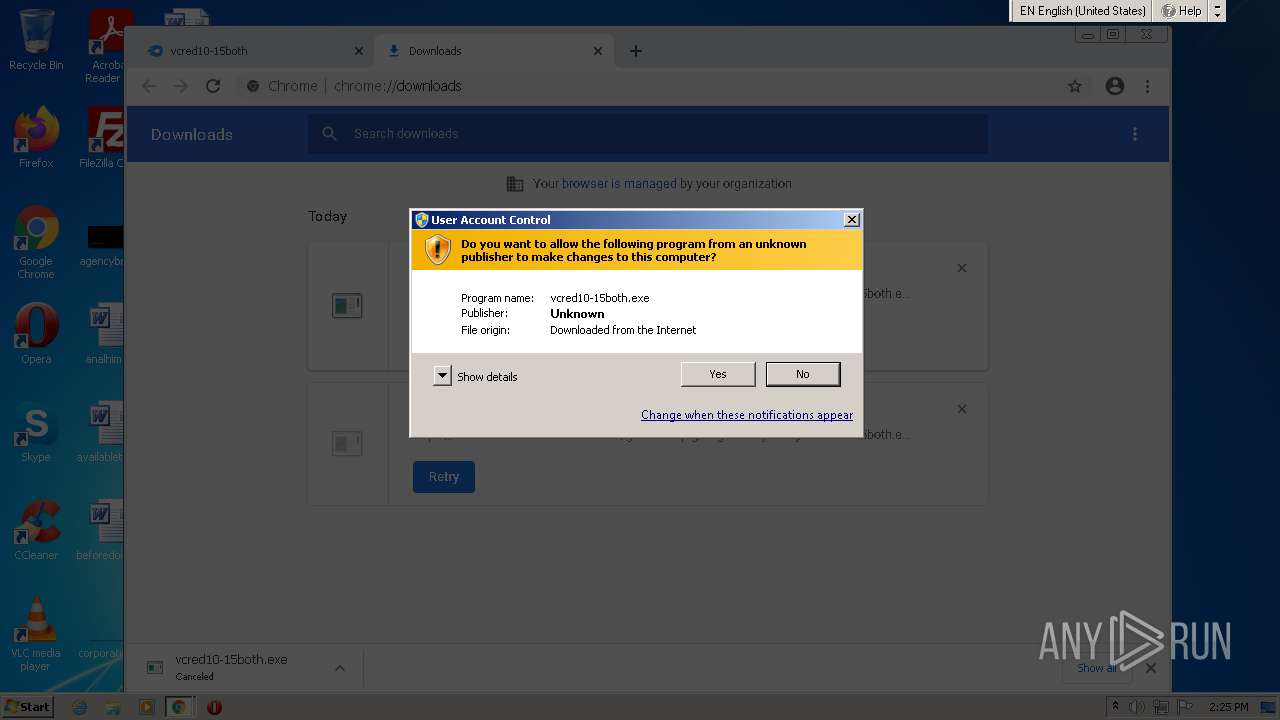
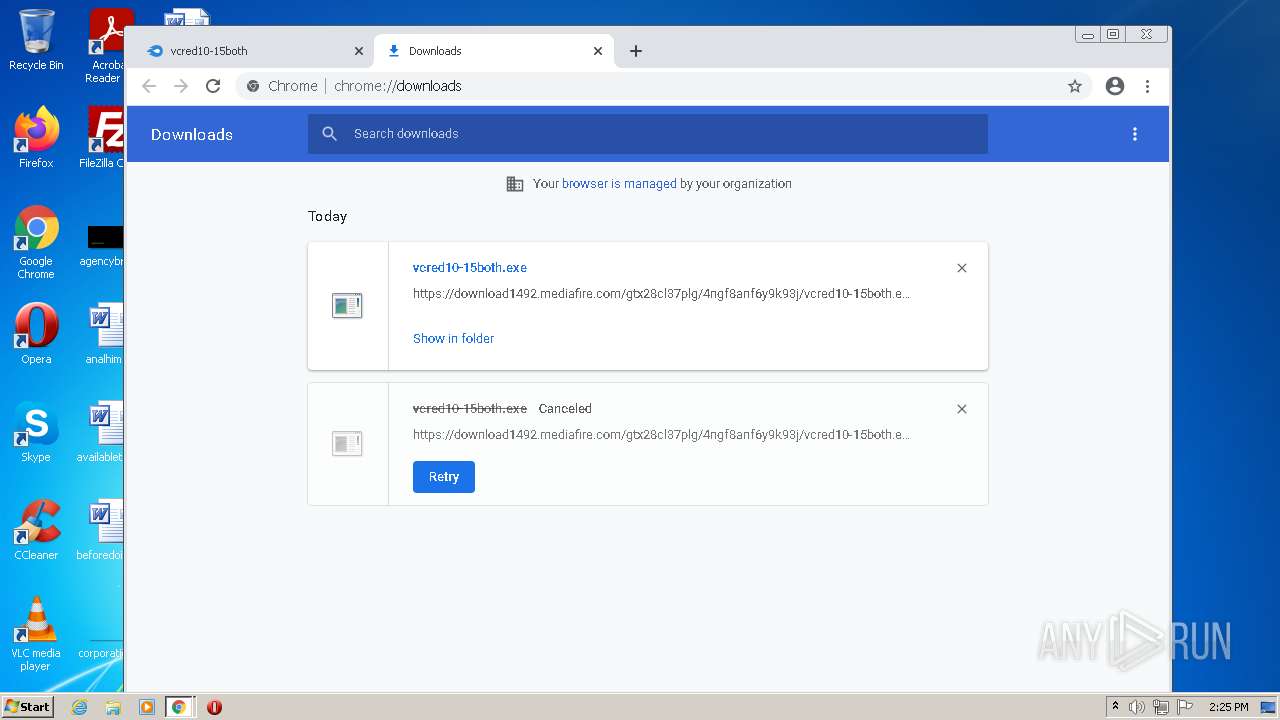
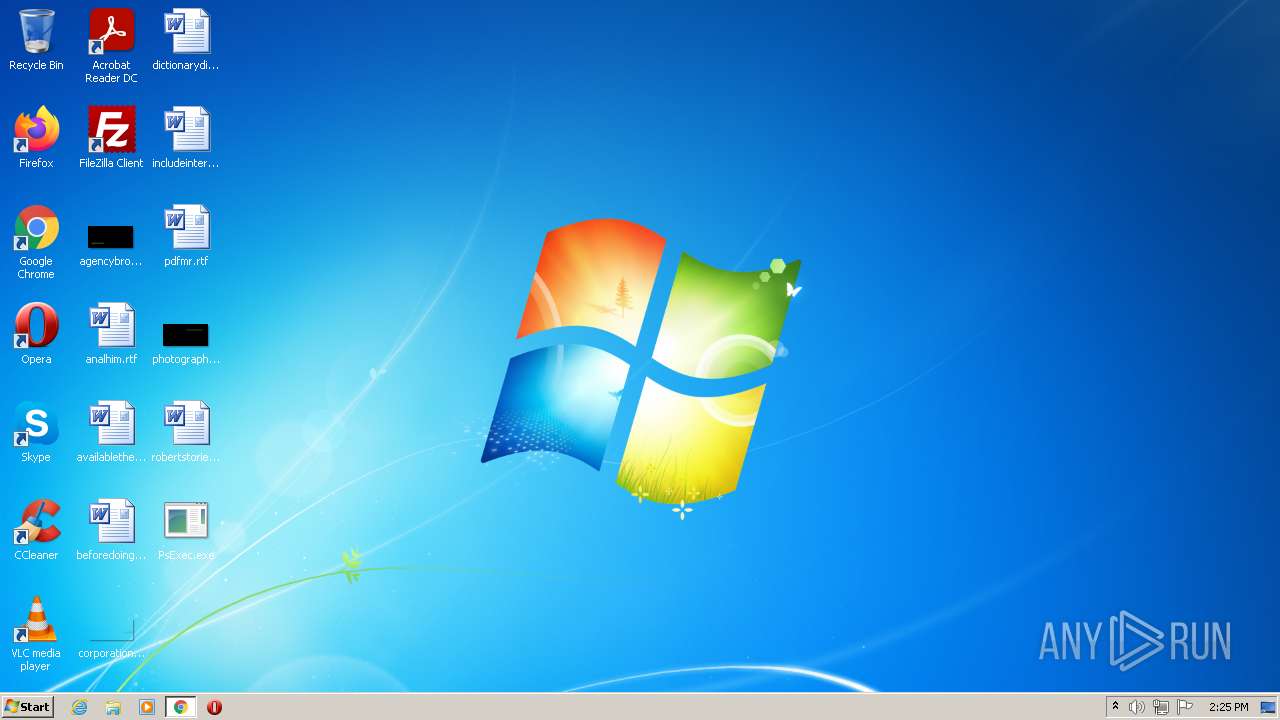
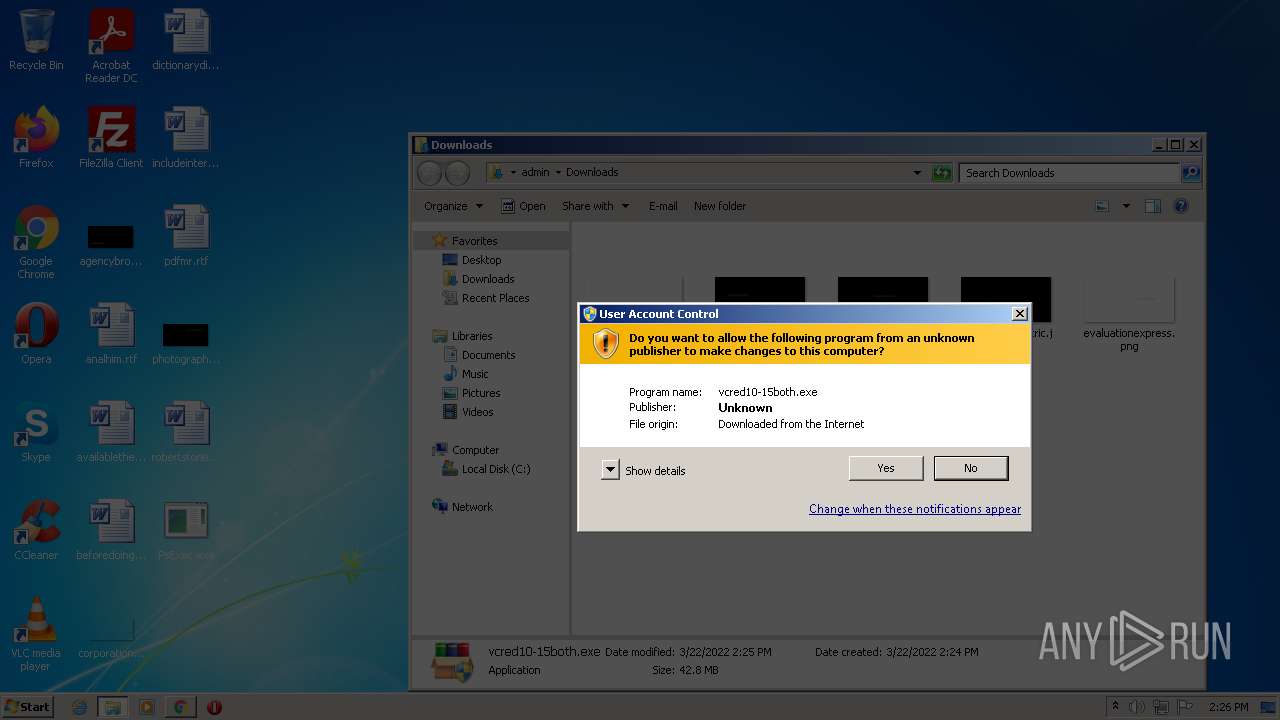
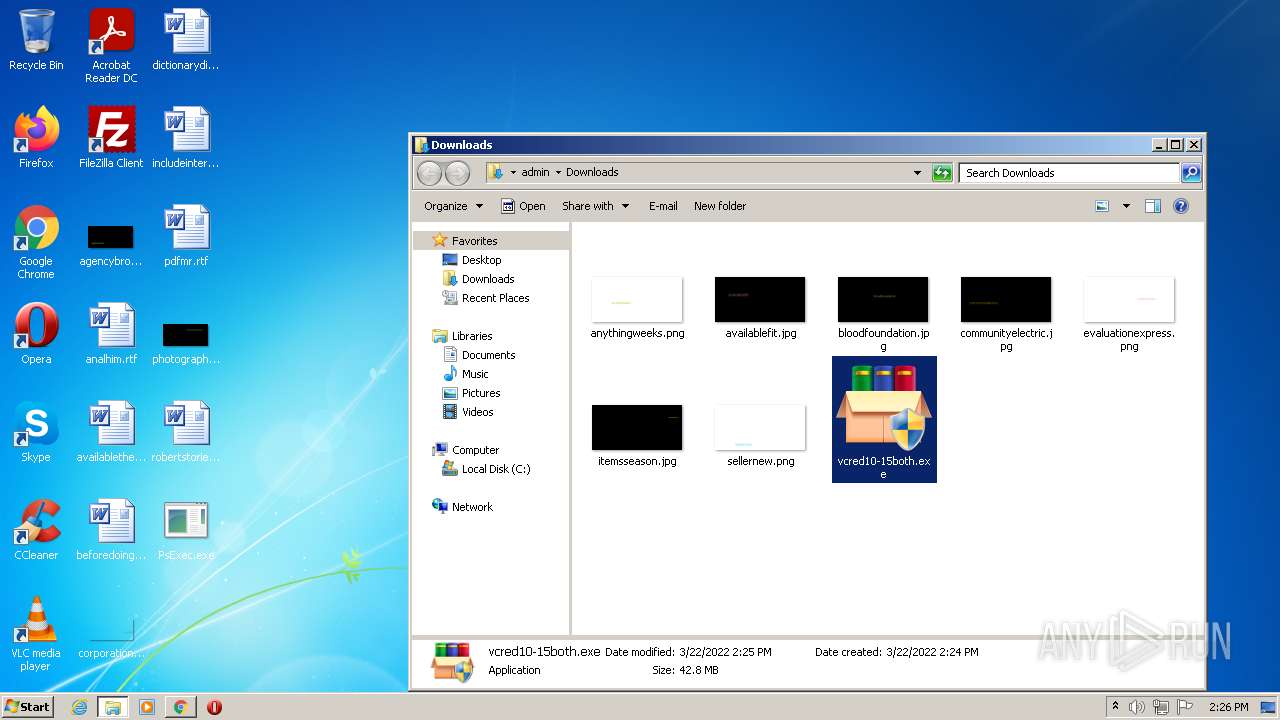
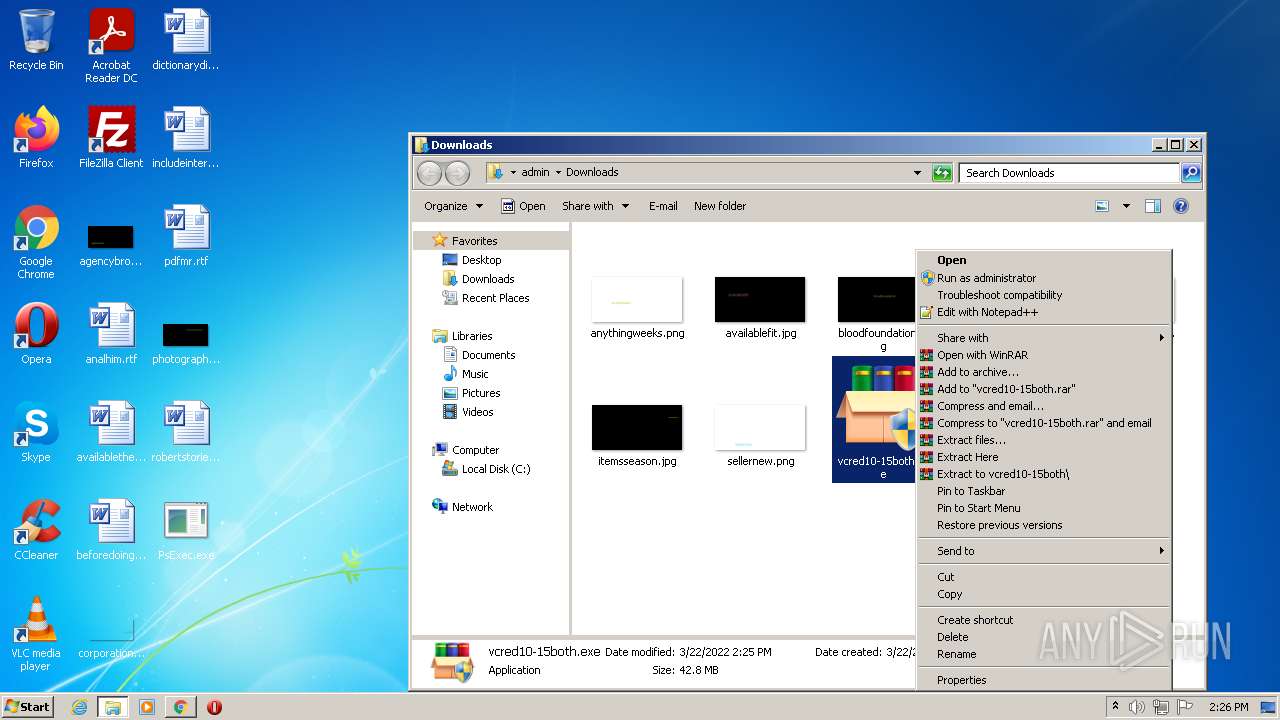
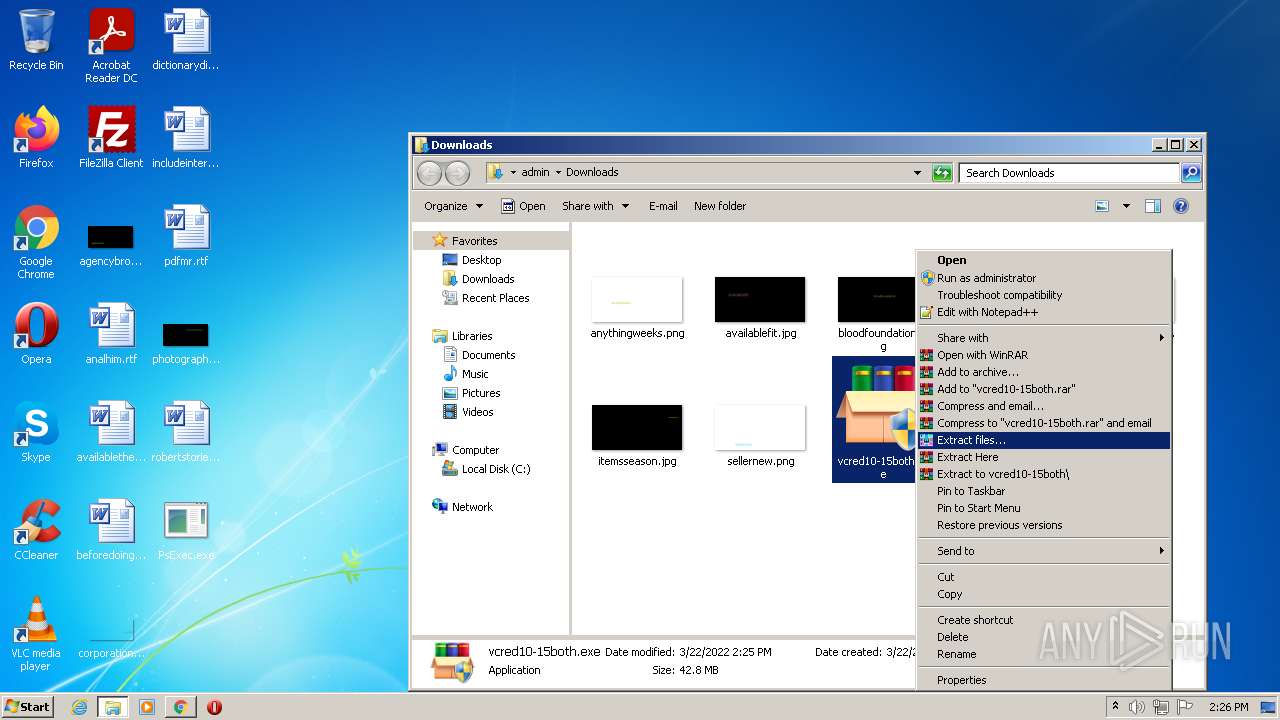
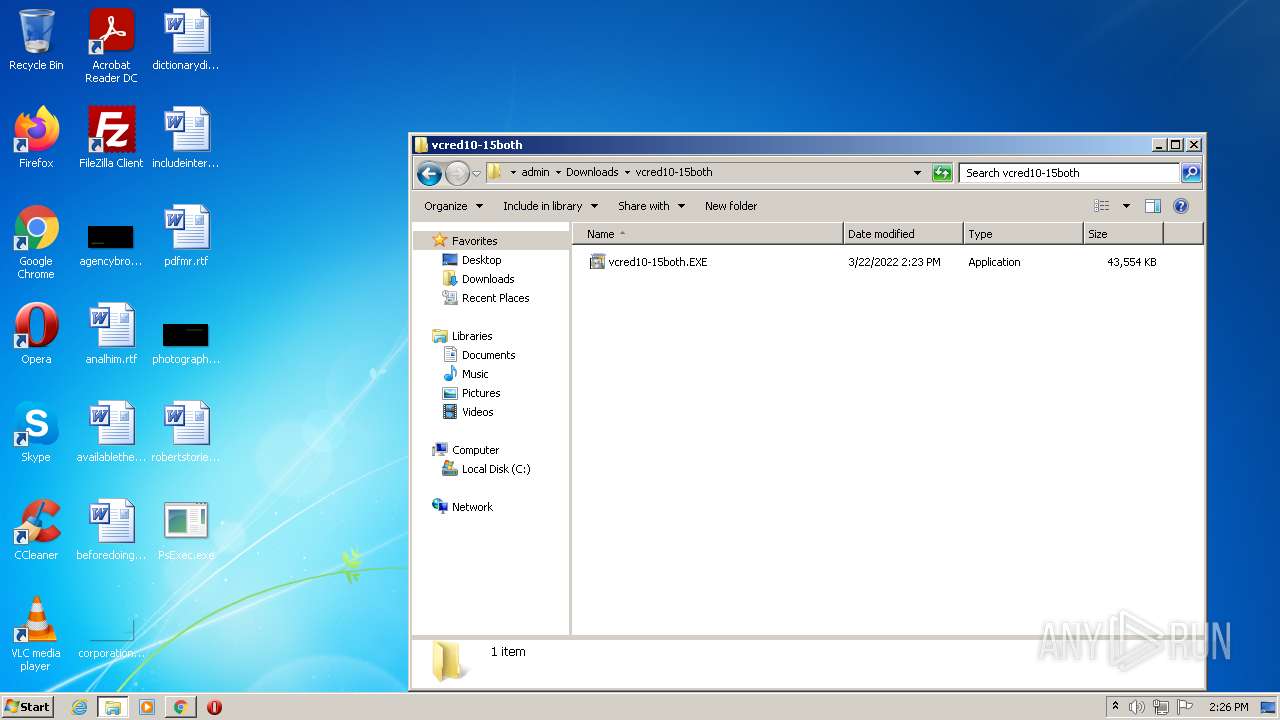
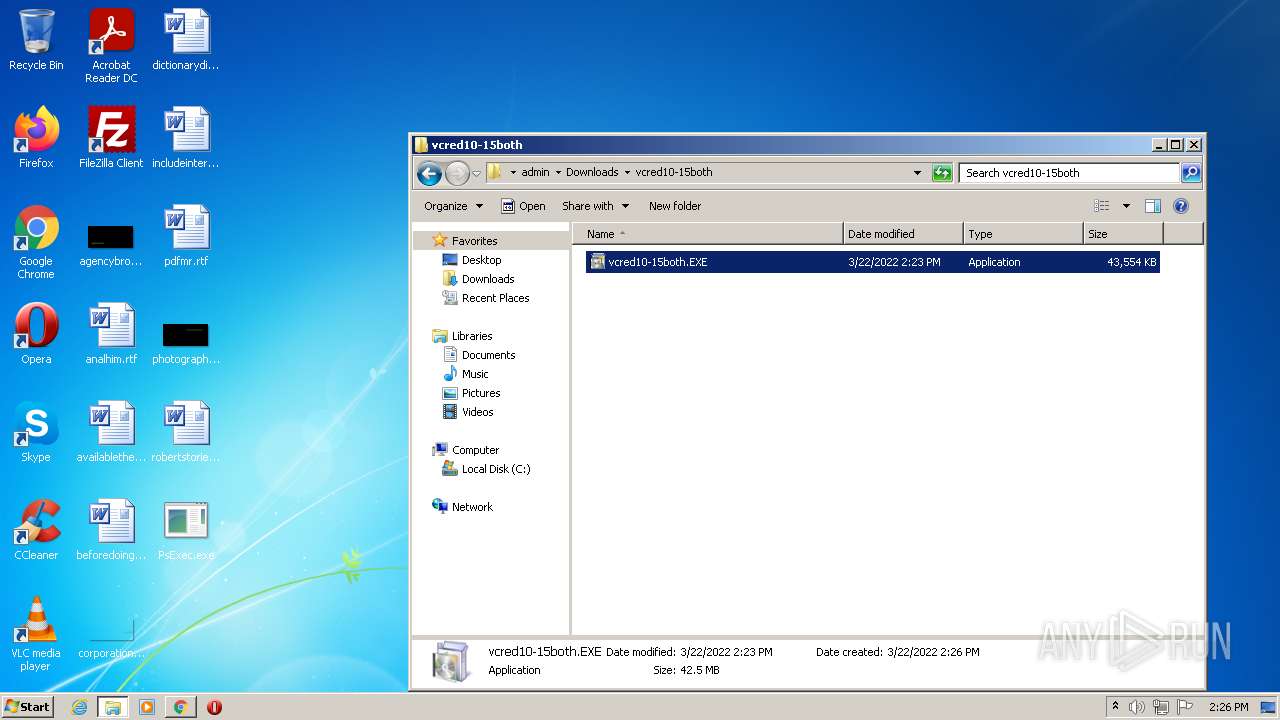
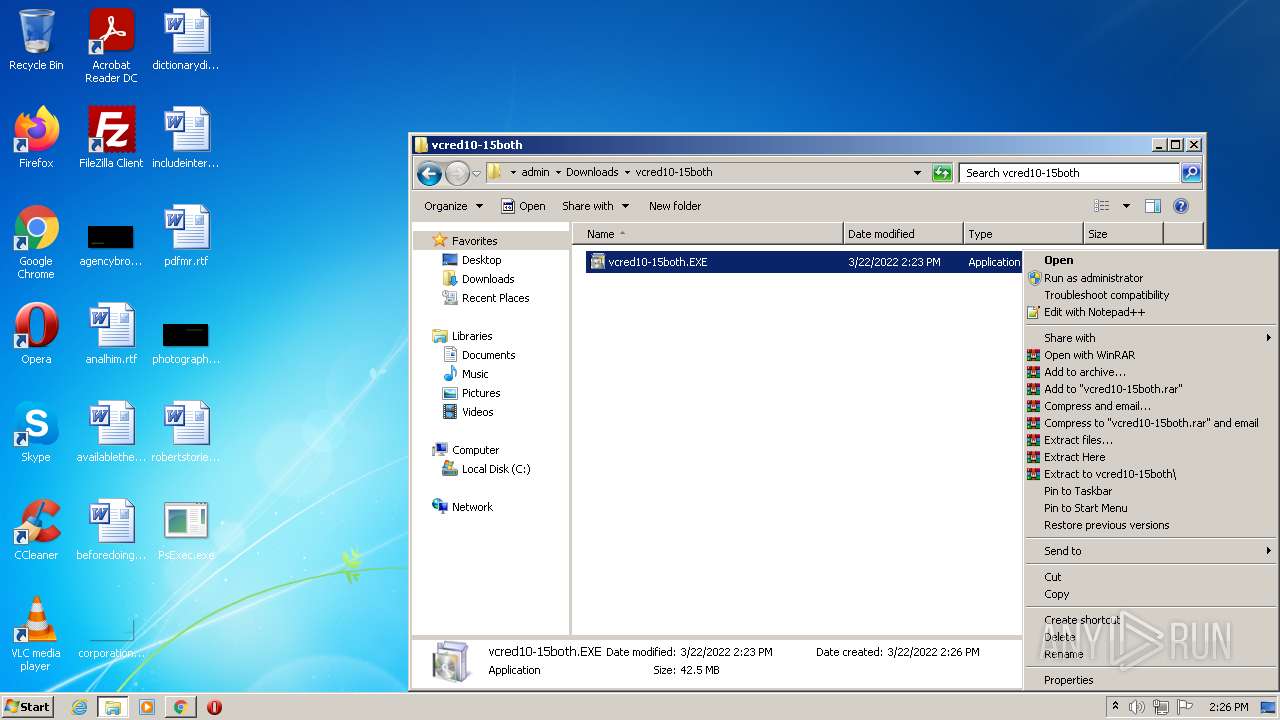
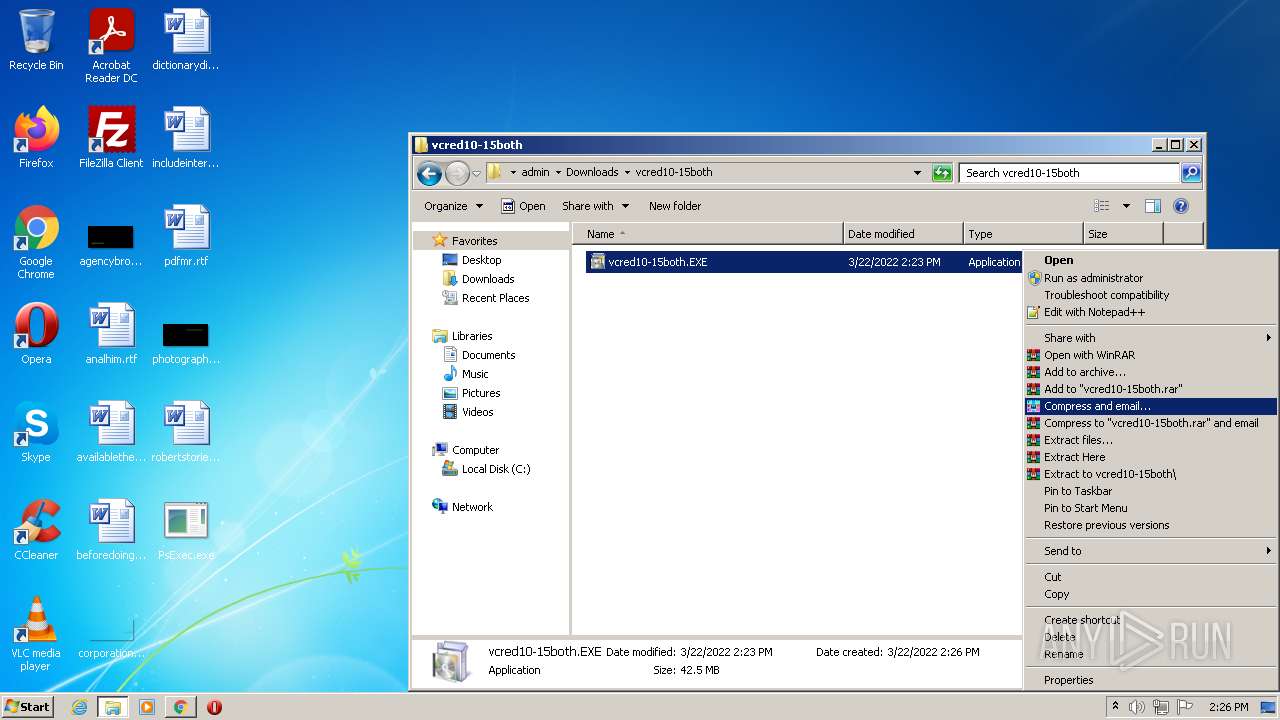
Manual execution by user
- chrome.exe (PID: 3252)
- verclsid.exe (PID: 5712)
- vcred10-15both.exe (PID: 1532)
- vcred10-15both.exe (PID: 5168)
- WinRAR.exe (PID: 2440)
- WinRAR.exe (PID: 4392)
- cmd.exe (PID: 4884)
Application launched itself
- iexplore.exe (PID: 3496)
- chrome.exe (PID: 3252)
Changes internet zones settings
- iexplore.exe (PID: 3496)
Reads the date of Windows installation
- iexplore.exe (PID: 3496)
- chrome.exe (PID: 2560)
Reads internet explorer settings
- iexplore.exe (PID: 2600)
- mshta.exe (PID: 5332)
- mshta.exe (PID: 5600)
Reads the hosts file
- chrome.exe (PID: 3252)
- chrome.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 2.34 |
|---|---|
| ProductName: | Sysinternals PsExec |
| OriginalFileName: | psexec.c |
| LegalCopyright: | Copyright (C) 2001-2021 Mark Russinovich |
| InternalName: | PsExec |
| FileVersion: | 2.34 |
| FileDescription: | Execute processes remotely |
| CompanyName: | Sysinternals - www.sysinternals.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.34.0.0 |
| FileVersionNumber: | 2.34.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x99fa |
| UninitializedDataSize: | - |
| InitializedDataSize: | 658944 |
| CodeSize: | 341504 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:12 15:14:52+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-May-2021 13:14:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Execute processes remotely |
| FileVersion: | 2.34 |
| InternalName: | PsExec |
| LegalCopyright: | Copyright (C) 2001-2021 Mark Russinovich |
| OriginalFilename: | psexec.c |
| ProductName: | Sysinternals PsExec |
| ProductVersion: | 2.34 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-May-2021 13:14:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00053489 | 0x00053600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60376 |
.rdata | 0x00055000 | 0x00013086 | 0x00013200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.90523 |
.data | 0x00069000 | 0x0002C8CC | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.46914 |
.rsrc | 0x00096000 | 0x0005E200 | 0x0005E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.59768 |
.reloc | 0x000F5000 | 0x00002EF8 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67913 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 2.38755 | 122 | UNKNOWN | English - United States | RT_STRING |
PSEXESVC | 6.60317 | 383872 | UNKNOWN | English - United States | BINRES |
Imports
ADVAPI32.dll |
COMDLG32.dll |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
USER32.dll (delay-loaded) |
VERSION.dll |
WS2_32.dll |
Total processes
178
Monitored processes
113
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=65 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,8347611779367053144,9474918116449462944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
57 890
Read events
56 870
Write events
976
Delete events
44
Modification events
| (PID) Process: | (3972) PsExec.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\PsExec |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30948856 | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30948856 | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3496) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
87
Suspicious files
266
Text files
349
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{935E4933-A9EB-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3496 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA4D74B72871A3F18.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6239DBD9-CB4.pma | — | |
MD5:— | SHA256:— | |||
| 3496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{9CDBC56F-A9EB-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{9CDBC56E-A9EB-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3496 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2BD52B326E23CCBD.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\572BF21E454637C9F000BE1AF9B1E1A9 | der | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\572BF21E454637C9F000BE1AF9B1E1A9 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
288
DNS requests
200
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
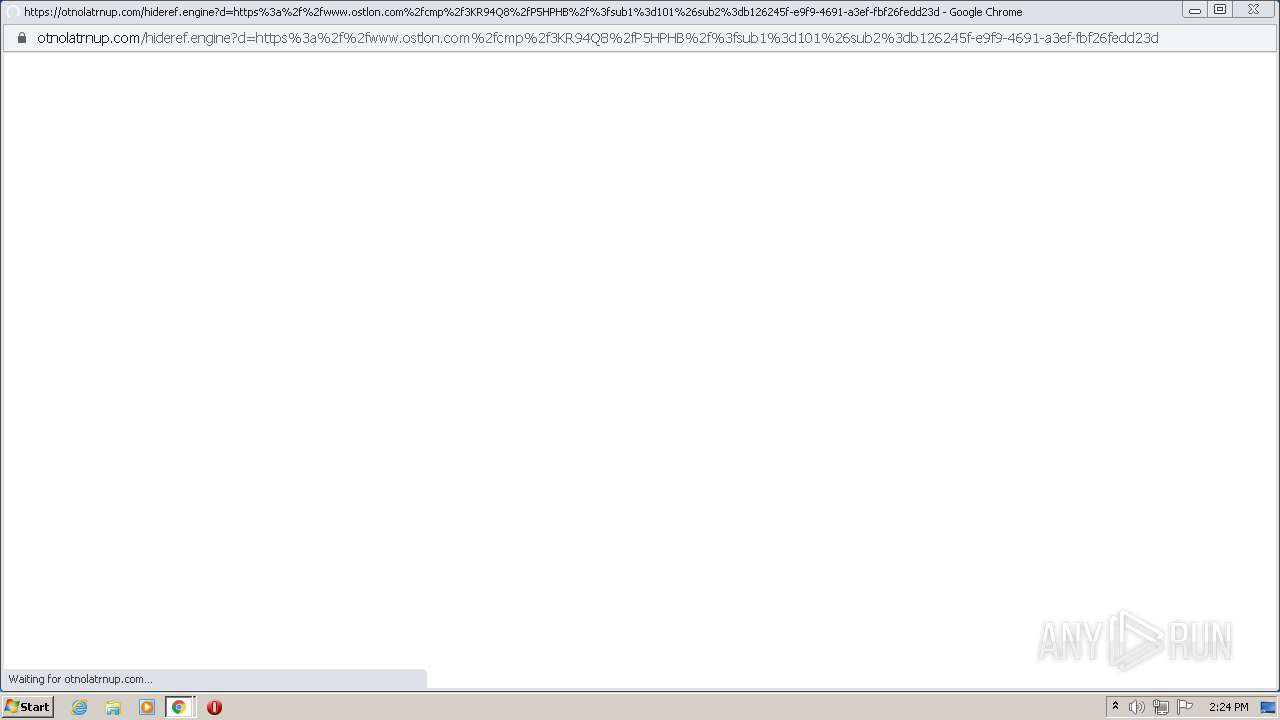
4012 | chrome.exe | GET | 302 | 104.19.214.37:80 | http://otnolatrnup.com/hideref.engine?d=https%3a%2f%2fwww.ostlon.com%2fcmp%2f3KR94Q8%2fP5HPHB%2f%3fsub1%3d101%26sub2%3db126245f-e9f9-4691-a3ef-fbf26fedd23d | US | — | — | whitelisted |
2600 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.73 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 43.4 Kb | whitelisted |
4012 | chrome.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d6940fc531cfaf23 | US | compressed | 59.5 Kb | whitelisted |
3496 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 88.5 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 178 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2600 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2600 | iexplore.exe | 104.16.203.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
3496 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2600 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3496 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4012 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2600 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
4012 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
4012 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | A StopBlock was hit or a System Requirement was not met. |
Setup.exe | The operation completed successfully.
|