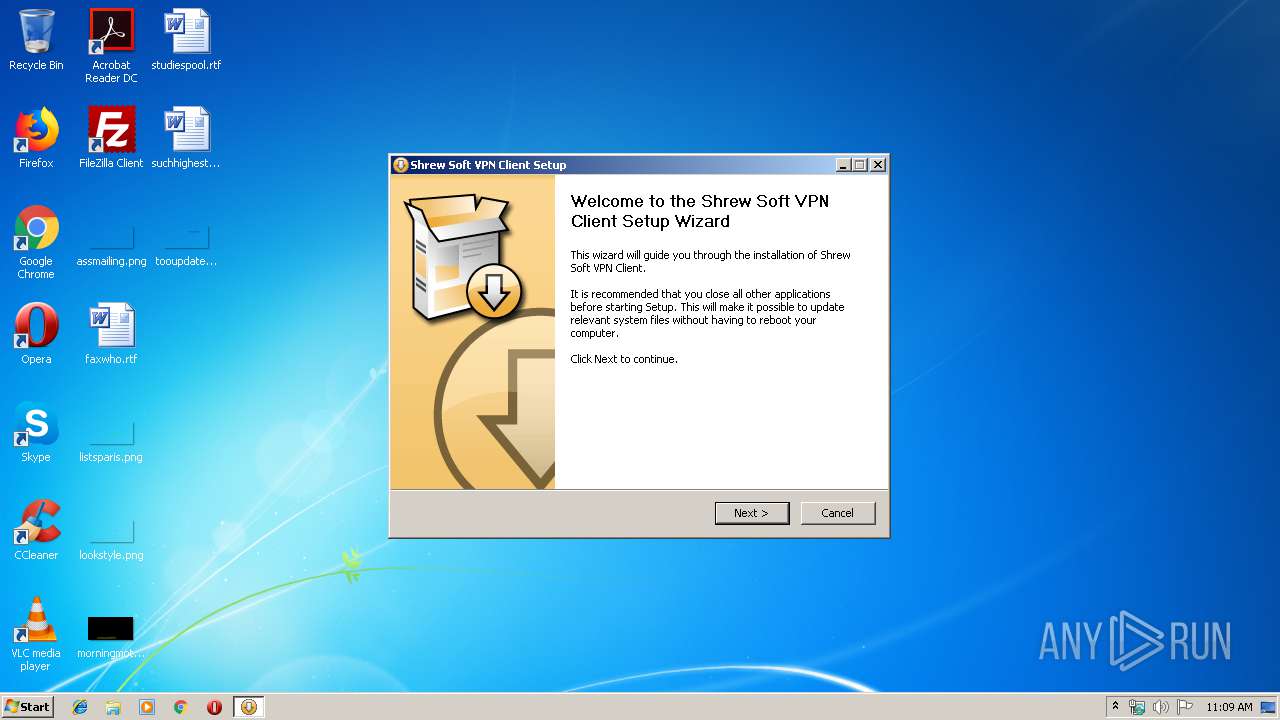
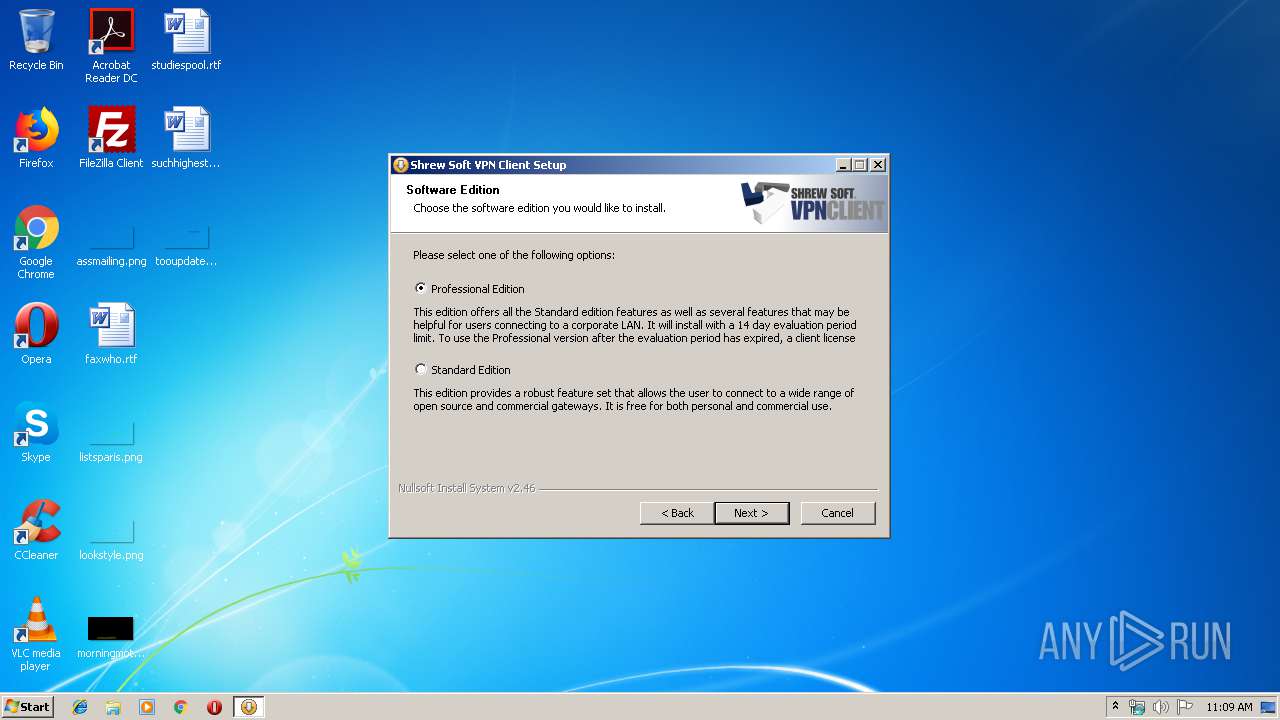
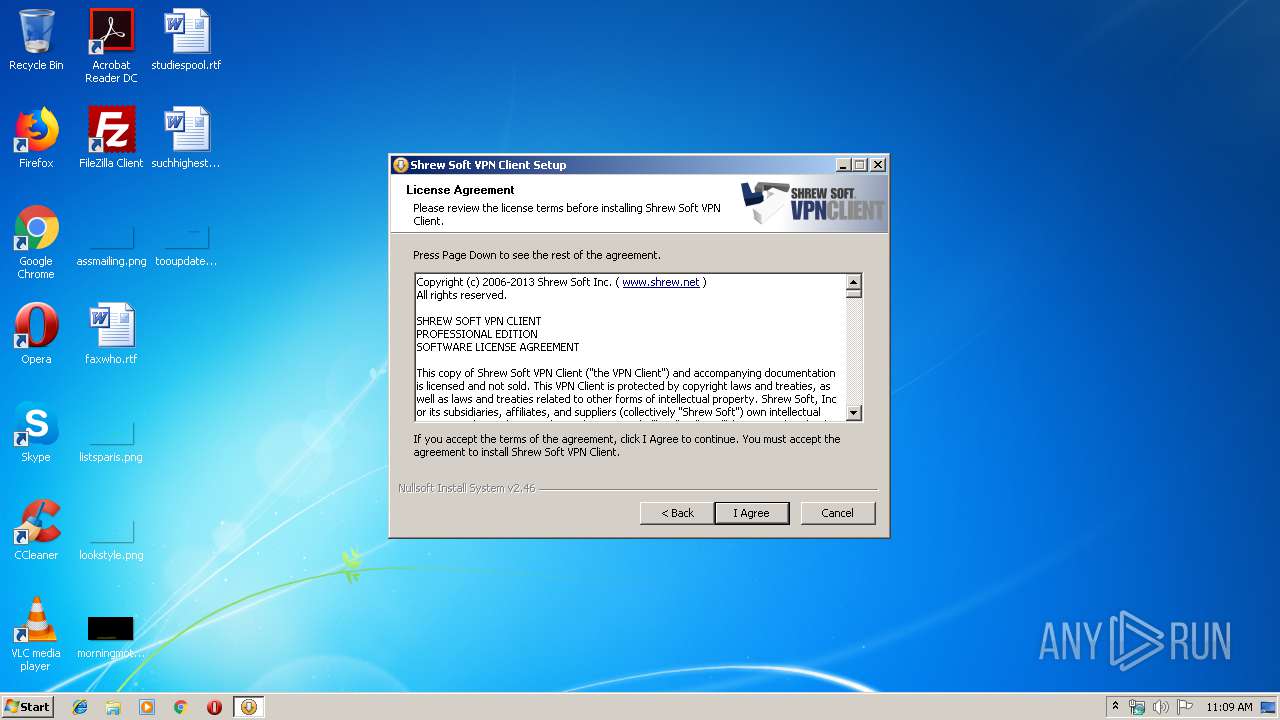
| File name: | vpn-client-2.2.2-release.exe |
| Full analysis: | https://app.any.run/tasks/ea1f61ff-31d3-4947-b549-c5c53fc0c99b |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 11:09:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
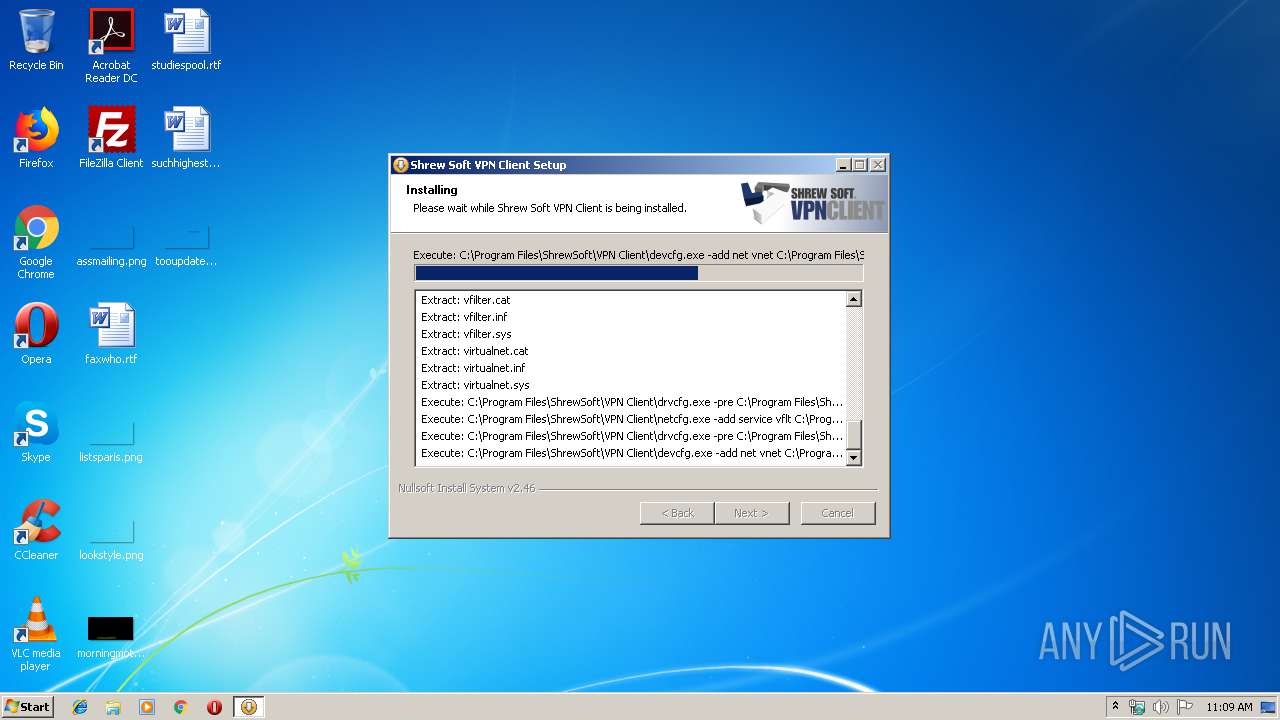
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 43E3EF7766E4352583129CF0EEC72AB7 |
| SHA1: | 182577786892E619A4B85270FA8D915C71E63C4C |
| SHA256: | 573B26315D49AB55E10EC39AA092F43FF0A061F3472AD99D3F5F106DADD18C3D |
| SSDEEP: | 98304:4+5LpcUagH964P5CoiS4Ipk8u2bakpomFBH:4+5tBBH84P8S3ijsa9mf |
MALICIOUS
Loads dropped or rewritten executable
- vpn-client-2.2.2-release.exe (PID: 1016)
- ipseca.exe (PID: 1932)
- drvcfg.exe (PID: 1820)
- drvcfg.exe (PID: 3096)
- devcfg.exe (PID: 3364)
- ipsecd.exe (PID: 2516)
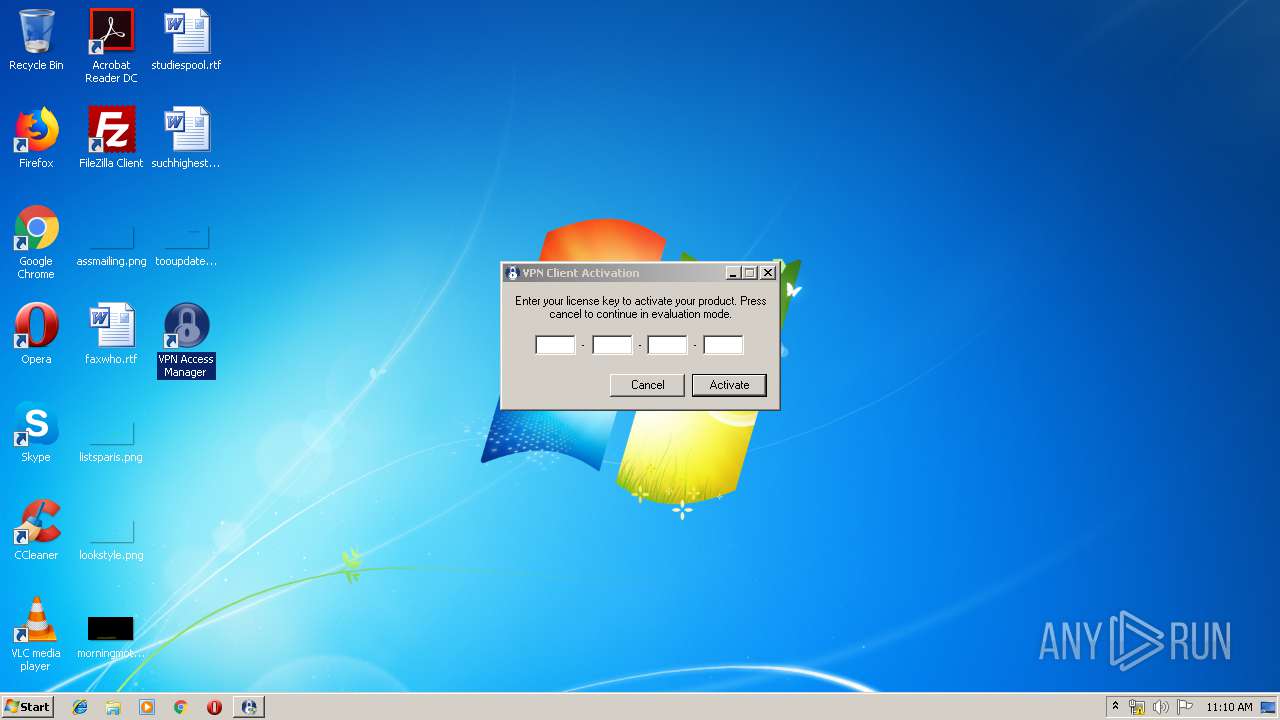
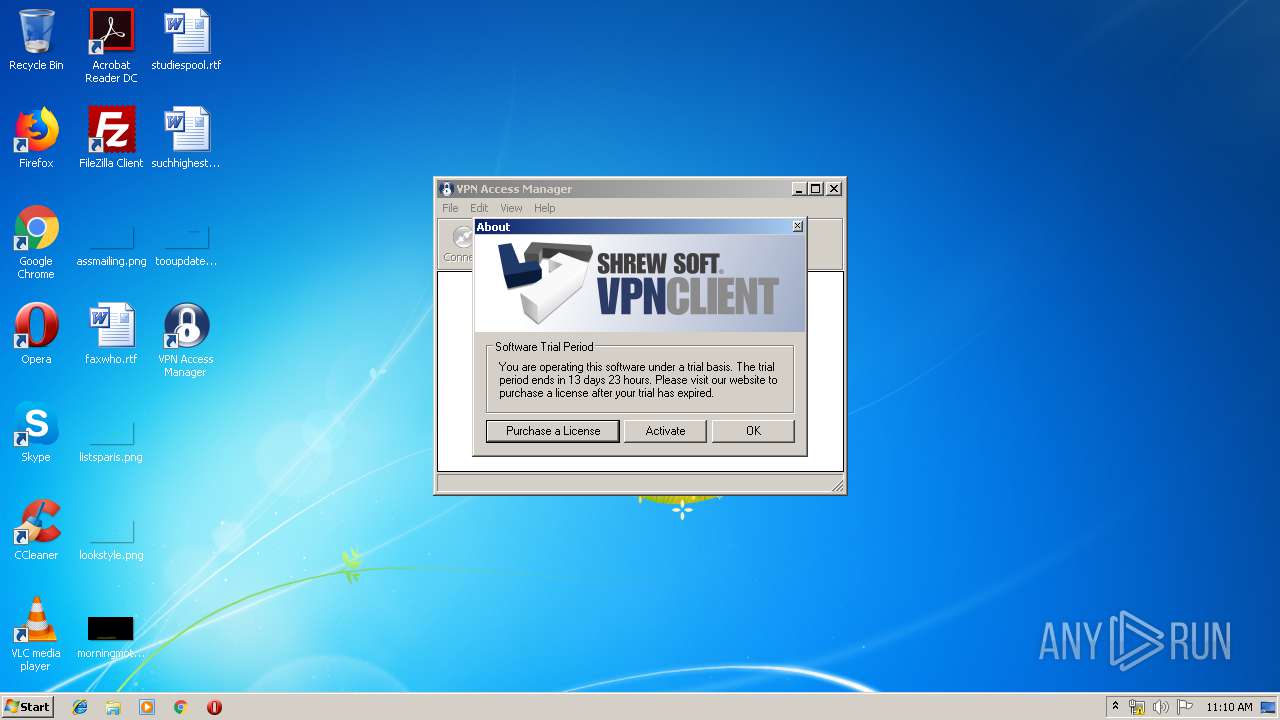
- activate.exe (PID: 2700)
- dtpd.exe (PID: 320)
- ipseca.exe (PID: 3916)
- iked.exe (PID: 1948)
- ipseca.exe (PID: 2500)
- ipseca.exe (PID: 4012)
Application was dropped or rewritten from another process
- ipseca.exe (PID: 1932)
- netcfg.exe (PID: 3392)
- drvcfg.exe (PID: 1820)
- drvcfg.exe (PID: 3096)
- devcfg.exe (PID: 3364)
- ipsecd.exe (PID: 2516)
- dtpd.exe (PID: 320)
- ipseca.exe (PID: 3916)
- activate.exe (PID: 436)
- ipseca.exe (PID: 2500)
- iked.exe (PID: 1948)
- activate.exe (PID: 2700)
- ipseca.exe (PID: 4012)
Writes to a start menu file
- vpn-client-2.2.2-release.exe (PID: 1016)
SUSPICIOUS
Creates files in the program directory
- ipseca.exe (PID: 1932)
- vpn-client-2.2.2-release.exe (PID: 1016)
- iked.exe (PID: 1948)
- dtpd.exe (PID: 320)
- ipsecd.exe (PID: 2516)
Creates files in the Windows directory
- vpn-client-2.2.2-release.exe (PID: 1016)
- DrvInst.exe (PID: 3316)
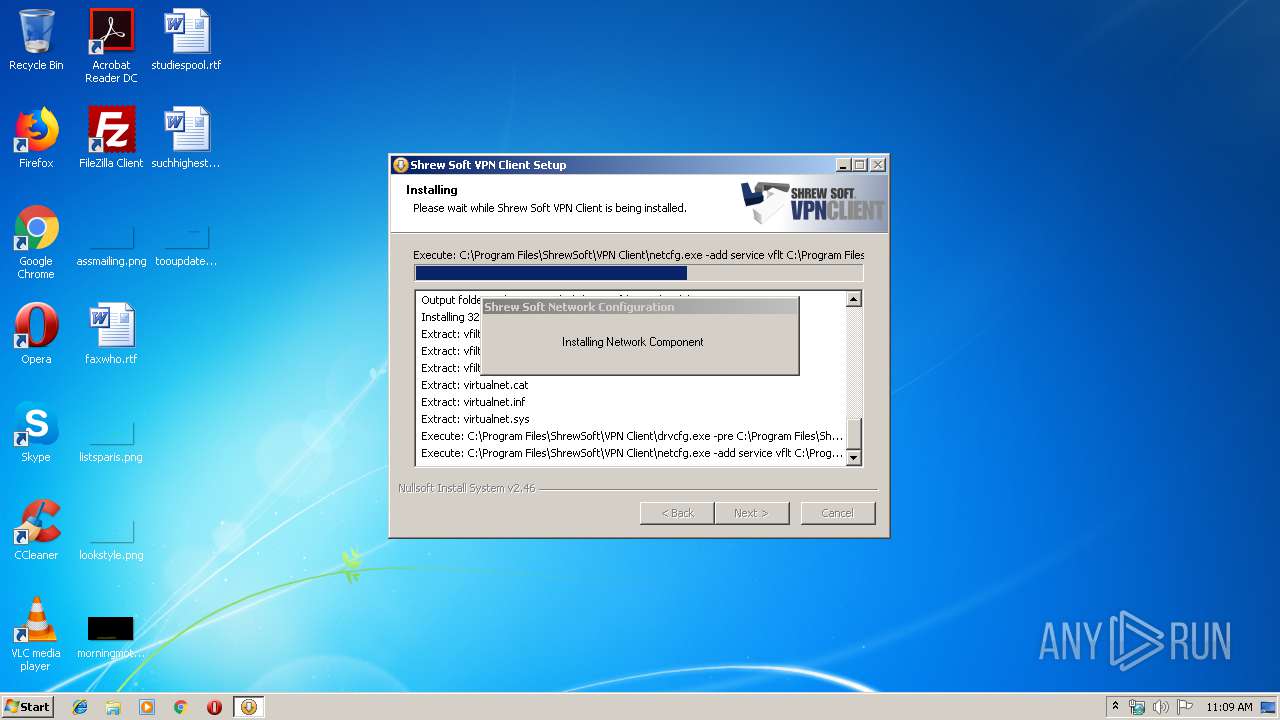
- netcfg.exe (PID: 3392)
- DrvInst.exe (PID: 1936)
- DrvInst.exe (PID: 2696)
Executable content was dropped or overwritten
- vpn-client-2.2.2-release.exe (PID: 1016)
- netcfg.exe (PID: 3392)
- drvcfg.exe (PID: 3096)
- DrvInst.exe (PID: 2696)
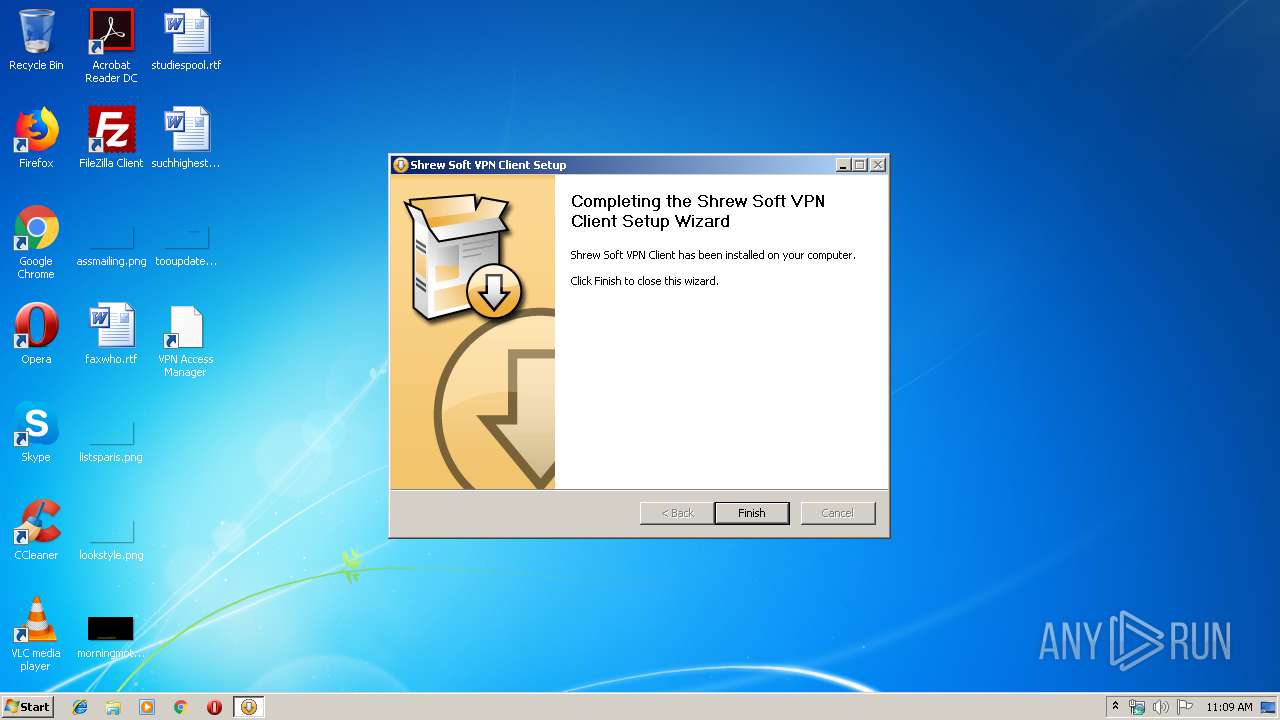
Creates a software uninstall entry
- vpn-client-2.2.2-release.exe (PID: 1016)
Executed via COM
- DrvInst.exe (PID: 3316)
- DrvInst.exe (PID: 1936)
- DrvInst.exe (PID: 2696)
- rundll32.exe (PID: 408)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1708)
Removes files from Windows directory
- DrvInst.exe (PID: 3316)
- netcfg.exe (PID: 3392)
- DrvInst.exe (PID: 1936)
- DrvInst.exe (PID: 2696)
Creates files in the driver directory
- DrvInst.exe (PID: 3316)
- netcfg.exe (PID: 3392)
- DrvInst.exe (PID: 1936)
- DrvInst.exe (PID: 2696)
Executed as Windows Service
- ipsecd.exe (PID: 2516)
- dtpd.exe (PID: 320)
- iked.exe (PID: 1948)
Creates COM task schedule object
- vpn-client-2.2.2-release.exe (PID: 1016)
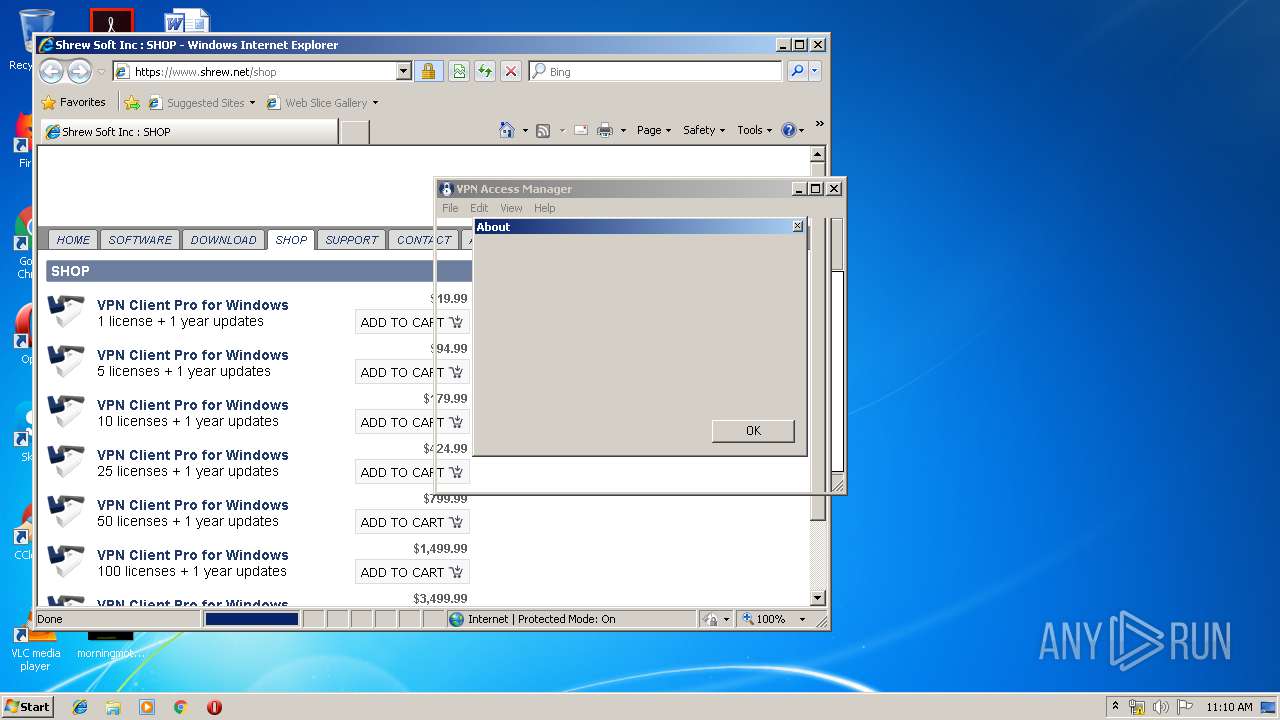
Starts Internet Explorer
- ipseca.exe (PID: 2500)
INFO
Dropped object may contain Bitcoin addresses
- vpn-client-2.2.2-release.exe (PID: 1016)
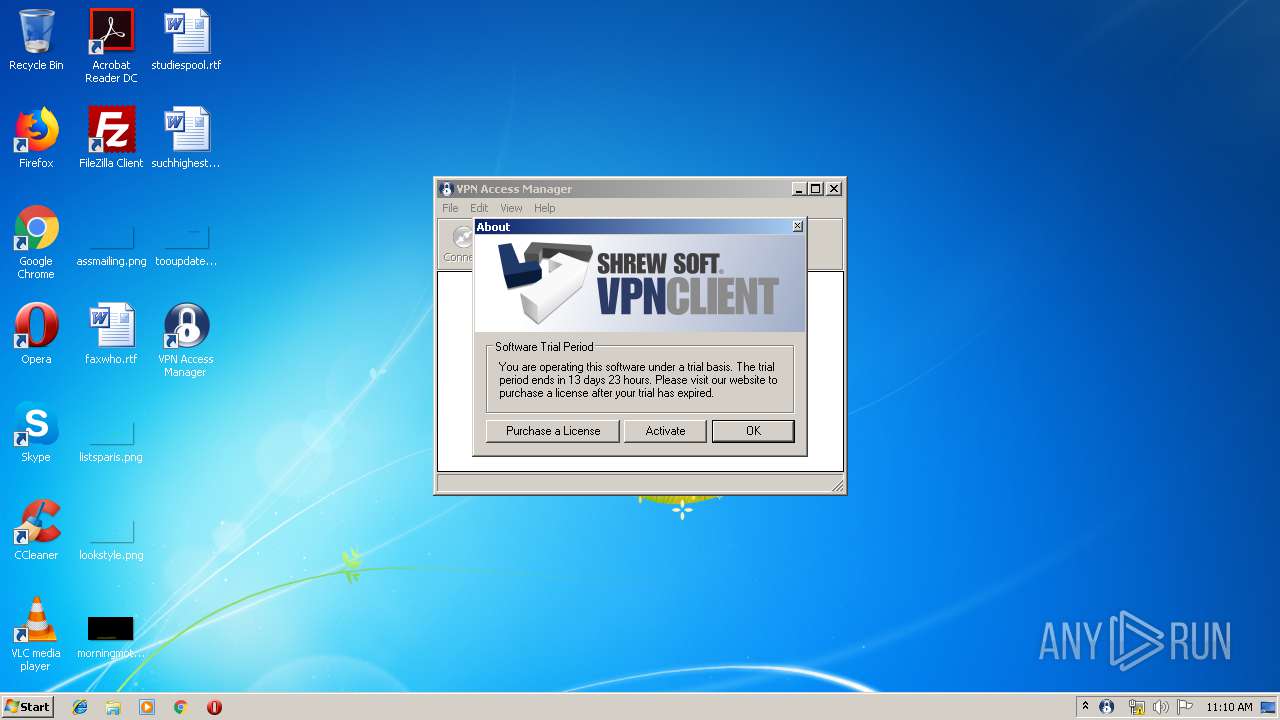
Manual execution by user
- ipseca.exe (PID: 3916)
- ipseca.exe (PID: 2500)
- ipseca.exe (PID: 4012)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1708)
- iexplore.exe (PID: 3340)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
Changes internet zones settings
- iexplore.exe (PID: 3028)
Reads Internet Cache Settings
- iexplore.exe (PID: 3340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:53:18+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 124928 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x36a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:53:18 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:53:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061A4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44297 |
.rdata | 0x00008000 | 0x000011E0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.3067 |
.data | 0x0000A000 | 0x0001C3F8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1303 |
.ndata | 0x00027000 | 0x0000D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00034000 | 0x000065E8 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06092 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.89539 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.3403 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.86327 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.97538 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.63025 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
62
Monitored processes
22
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\ShrewSoft\VPN Client\dtpd.exe" -service | C:\Program Files\ShrewSoft\VPN Client\dtpd.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 408 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | "C:\Program Files\ShrewSoft\VPN Client\activate.exe" | C:\Program Files\ShrewSoft\VPN Client\activate.exe | — | ipseca.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Temp\vpn-client-2.2.2-release.exe" | C:\Users\admin\AppData\Local\Temp\vpn-client-2.2.2-release.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1708 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
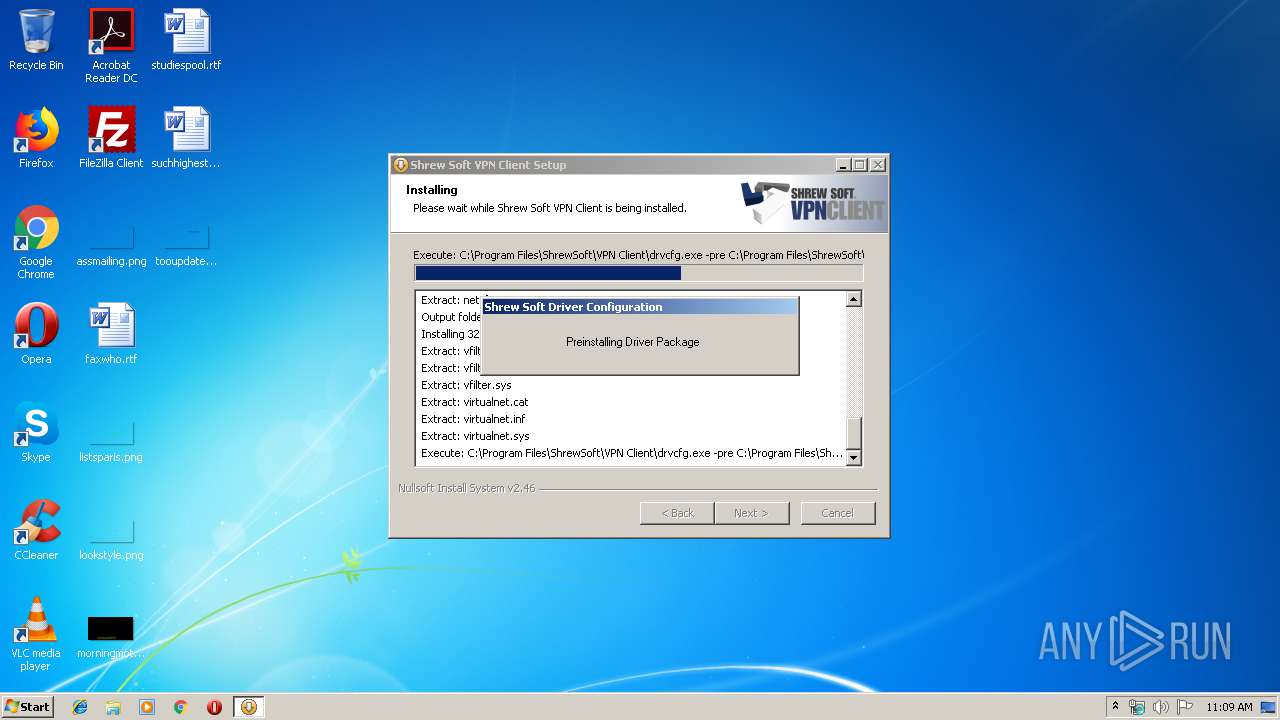
| 1820 | "C:\Program Files\ShrewSoft\VPN Client\drvcfg.exe" -pre C:\Program Files\ShrewSoft\VPN Client\drivers\vfilter.inf | C:\Program Files\ShrewSoft\VPN Client\drvcfg.exe | — | vpn-client-2.2.2-release.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225547 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\ShrewSoft\VPN Client\ipseca.exe" -import C:\Users\admin\AppData\Local\Temp | C:\Program Files\ShrewSoft\VPN Client\ipseca.exe | — | vpn-client-2.2.2-release.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1936 | DrvInst.exe "4" "20" "C:\Users\admin\AppData\Local\Temp\{2c6545fc-d0dd-4b29-c25e-f206e674221d}\virtualnet.inf" "0" "6df63bb27" "0000055C" "WinSta0\Default" "00000060" "208" "C:\Program Files\ShrewSoft\VPN Client\drivers" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\ShrewSoft\VPN Client\iked.exe" -service | C:\Program Files\ShrewSoft\VPN Client\iked.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\ShrewSoft\VPN Client\ipseca.exe" | C:\Program Files\ShrewSoft\VPN Client\ipseca.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 618
Read events
1 099
Write events
474
Delete events
45
Modification events
| (PID) Process: | (1932) ipseca.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | bindat |
Value: 68FCB480FB2763E586106977B1A35763E9C66D9428C91AA0777EF1BD9CE8366A | |||
| (PID) Process: | (3316) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1820) drvcfg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (1820) drvcfg.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | path |
Value: C:\Program Files\ShrewSoft\VPN Client | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | logfile-iked |
Value: C:\Program Files\ShrewSoft\VPN Client\debug\iked.log | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | logfile-dtpd |
Value: C:\Program Files\ShrewSoft\VPN Client\debug\dtpd.log | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | logfile-ipsecd |
Value: C:\Program Files\ShrewSoft\VPN Client\debug\ipsec.log | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ShrewSoft\vpn |
| Operation: | write | Name: | loglevel |
Value: 0 | |||
| (PID) Process: | (1016) vpn-client-2.2.2-release.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Shrew Soft VPN Client |
| Operation: | write | Name: | DisplayName |
Value: Shrew Soft VPN Client | |||
Executable files
33
Suspicious files
24
Text files
169
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1016 | vpn-client-2.2.2-release.exe | C:\Users\admin\AppData\Local\Temp\nsbB13B.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Users\admin\AppData\Local\Temp\nsbB13B.tmp\modern-wizard.bmp | image | |
MD5:9E4CD80A60DB6947642677BF31A10906 | SHA256:A7B2F12E01CBEA88D4F645F797F2CA6107D76AE13CD1BE6DC532B759BFE0D925 | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Users\admin\AppData\Local\Temp\nsbB13B.tmp\nsDialogs.dll | executable | |
MD5:AB73C0C2A23F913EABDC4CB24B75CBAD | SHA256:3D0060C5C9400A487DBEFE4AC132DD96B07D3A4BA3BADAB46A7410A667C93457 | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Users\admin\AppData\Local\Temp\nsbB13B.tmp\modern-header.bmp | image | |
MD5:9A5E2514F5EAB0C7D00C2957C39F59A3 | SHA256:5806BF48146DFD3DC2E6715CC8DFEFDD5244EF325352A1EE2A3BAA15BC2159CA | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Program Files\ShrewSoft\VPN Client\libdtp.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Users\admin\AppData\Local\Temp\nsbB13B.tmp\nsProcess.dll | executable | |
MD5:05450FACE243B3A7472407B999B03A72 | SHA256:95FE9D92512FF2318CC2520311EF9145B2CEE01209AB0E1B6E45C7CE1D4D0E89 | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Program Files\ShrewSoft\VPN Client\readme.txt | text | |
MD5:1A50B68A24F23037D847684034E35CBF | SHA256:FABB2D8E94C8F72A3A0AFA085A075B6B3CBDCF30C982B7EB6960864013A79BF5 | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Program Files\ShrewSoft\VPN Client\license.txt | text | |
MD5:FAA316092E6B239C2EDC86F25D1B1034 | SHA256:F7F42641B524BC55BAC1E3CF33017B7A2AC74DB7696CC9D55D883E7926AF5307 | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Program Files\ShrewSoft\VPN Client\ipsecc.exe | executable | |
MD5:— | SHA256:— | |||
| 1016 | vpn-client-2.2.2-release.exe | C:\Program Files\ShrewSoft\VPN Client\ipsecd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | ipseca.exe | 38.97.5.129:443 | update.shrew.net | Cogent Communications | US | unknown |
2500 | ipseca.exe | 38.97.5.129:443 | update.shrew.net | Cogent Communications | US | unknown |
3028 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3340 | iexplore.exe | 38.97.5.129:443 | update.shrew.net | Cogent Communications | US | unknown |
3028 | iexplore.exe | 38.97.5.129:443 | update.shrew.net | Cogent Communications | US | unknown |
3340 | iexplore.exe | 172.217.22.72:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.shrew.net |
| unknown |
www.bing.com |
| whitelisted |
www.shrew.net |
| unknown |
ssl.google-analytics.com |
| whitelisted |