| File name: | netscanold.exe |
| Full analysis: | https://app.any.run/tasks/528462bd-1214-4675-80ae-32b7feac6b08 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2022, 12:53:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | BB7C575E798FF5243B5014777253635D |
| SHA1: | 2146F04728FE93C393A74331B76799EA8FE0269F |
| SHA256: | 572D88C419C6AE75AEB784CEAB327D040CB589903D6285BBFFA77338111AF14B |
| SSDEEP: | 24576:D+c6hlrwmBYO0ToPjesrqayUByzNu+pzghCwDUkJDFellgCgHqTXhFZ+eQnbzOa8:DnUlcYYvTobdYNXFghlDHnewCThkjbFK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4060)
Reads the computer name
- netscanold.exe (PID: 2944)
Checks supported languages
- netscanold.exe (PID: 2944)
Starts Internet Explorer
- netscanold.exe (PID: 2944)
INFO
Reads the date of Windows installation
- iexplore.exe (PID: 2492)
Checks Windows Trust Settings
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 2492)
- netscanold.exe (PID: 2944)
Changes settings of System certificates
- iexplore.exe (PID: 2492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2492)
Reads settings of System Certificates
- iexplore.exe (PID: 4060)
- netscanold.exe (PID: 2944)
- iexplore.exe (PID: 2492)
Checks supported languages
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 2492)
Reads the computer name
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 2492)
Changes internet zones settings
- iexplore.exe (PID: 2492)
Application launched itself
- iexplore.exe (PID: 2492)
Reads internet explorer settings
- iexplore.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
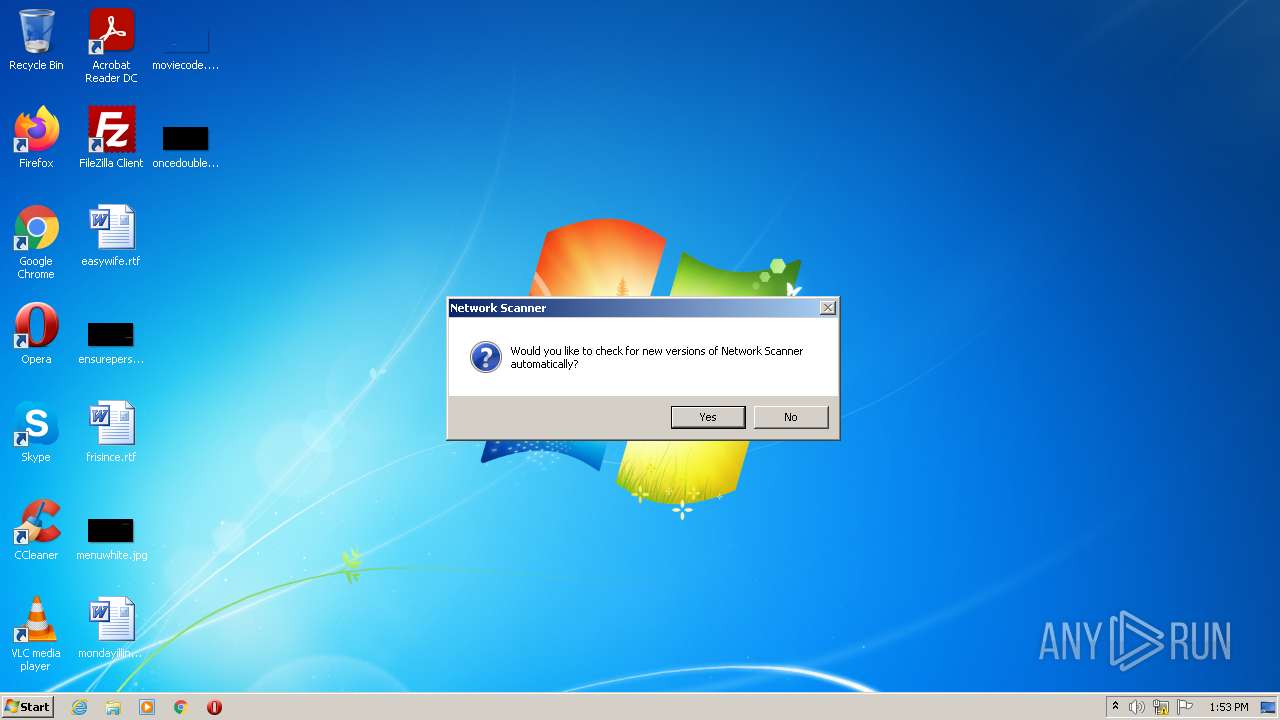
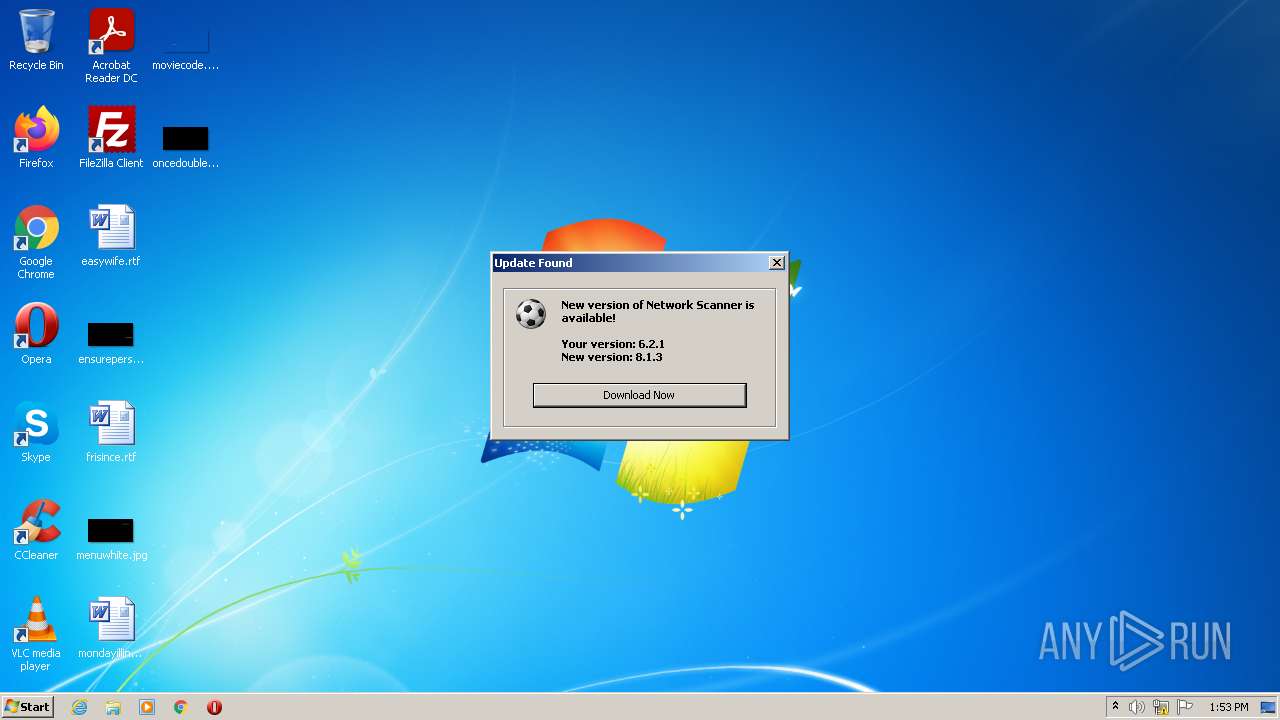
| ProductVersion: | 6.2.1.0 |
|---|---|
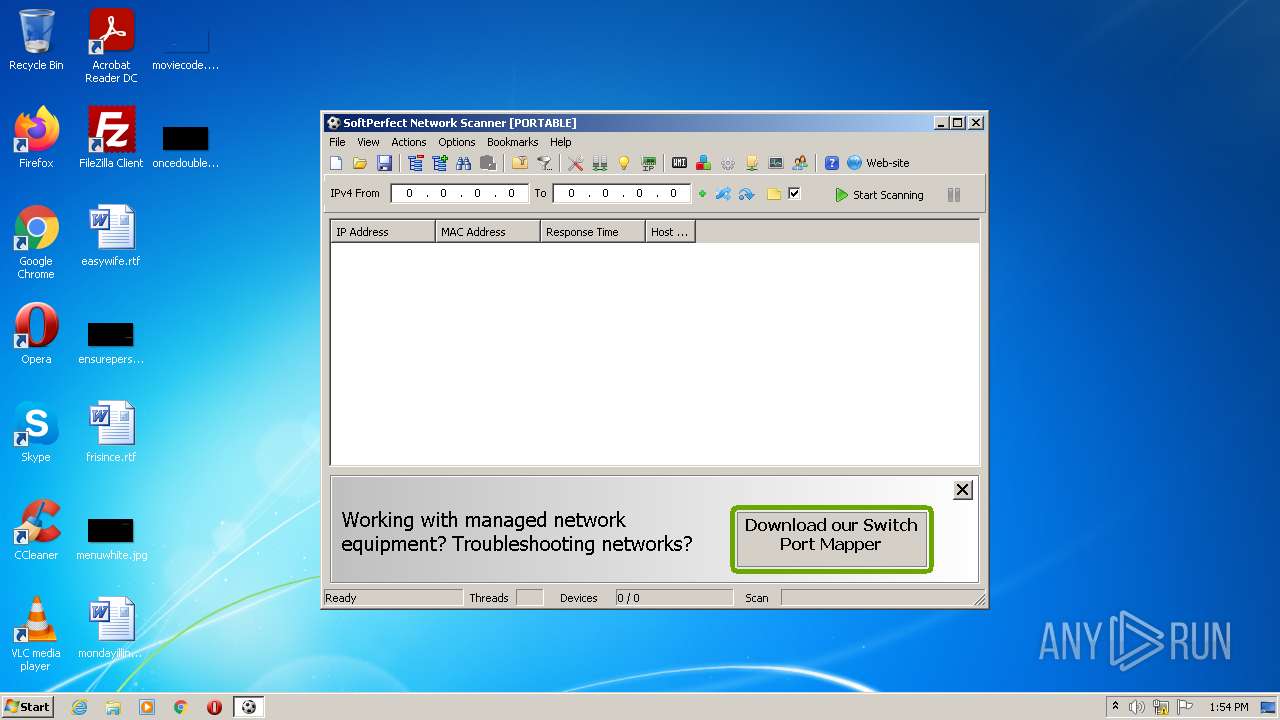
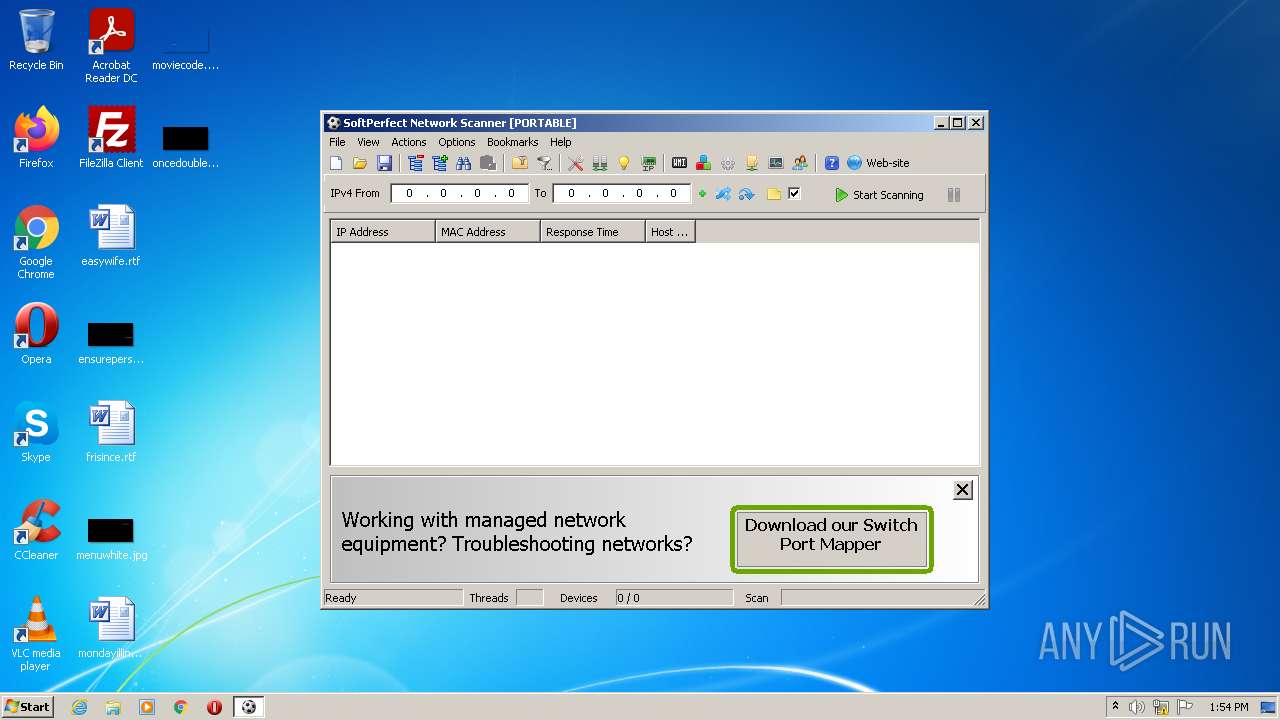
| ProductName: | SoftPerfect Network Scanner |
| LegalCopyright: | 2003-2016 SoftPerfect |
| FileVersion: | 6.2.1.0 |
| FileDescription: | Multipurpose IPv4/IPv6 network scanner |
| CompanyName: | SoftPerfect |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (Australian) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.2.1.0 |
| FileVersionNumber: | 6.2.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x57d862 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 777216 |
| CodeSize: | 4925440 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2016:10:18 08:11:22+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Oct-2016 06:11:22 |
| Detected languages: |
|
| CompanyName: | SoftPerfect |
| FileDescription: | Multipurpose IPv4/IPv6 network scanner |
| FileVersion: | 6.2.1.0 |
| LegalCopyright: | 2003-2016 SoftPerfect |
| ProductName: | SoftPerfect Network Scanner |
| ProductVersion: | 6.2.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 18-Oct-2016 06:11:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.MPRESS1 | 0x00001000 | 0x0057C000 | 0x0015A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99987 |
.MPRESS2@\x14 | 0x0057D000 | 0x00001440 | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15 |
.rsrc | 0x0057F000 | 0x000256C4 | 0x00025800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.14248 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99747 | 952 | UNKNOWN | English - Australia | RT_MANIFEST |
2 | 6.19294 | 2216 | UNKNOWN | English - Australia | RT_ICON |
3 | 5.69944 | 1736 | UNKNOWN | English - Australia | RT_ICON |
4 | 3.88244 | 1384 | UNKNOWN | English - Australia | RT_ICON |
5 | 7.93807 | 27063 | UNKNOWN | English - Australia | RT_ICON |
6 | 5.48696 | 67624 | UNKNOWN | English - Australia | RT_ICON |
7 | 5.61953 | 16936 | UNKNOWN | English - Australia | RT_ICON |
8 | 5.38803 | 9640 | UNKNOWN | English - Australia | RT_ICON |
9 | 5.59426 | 4264 | UNKNOWN | English - Australia | RT_ICON |
10 | 5.54625 | 2440 | UNKNOWN | English - Australia | RT_ICON |
Imports
KERNEL32.DLL |
SHFolder.dll |
URLMON.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
dnsapi.dll |
gdi32.dll |
iphlpapi.dll |
mgmtapi.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x00062A1C |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.softperfect.com/products/networkscanner/?from=auto | C:\Program Files\Internet Explorer\iexplore.exe | netscanold.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\AppData\Local\Temp\netscanold.exe" | C:\Users\admin\AppData\Local\Temp\netscanold.exe | Explorer.EXE | ||||||||||||
User: admin Company: SoftPerfect Integrity Level: MEDIUM Description: Multipurpose IPv4/IPv6 network scanner Exit code: 0 Version: 6.2.1.0 Modules
| |||||||||||||||
| 4060 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 700
Read events
15 563
Write events
133
Delete events
4
Modification events
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2944) netscanold.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
14
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | netscanold.exe | C:\Users\admin\AppData\Local\Temp\CabAF42.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 4060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\css[1].css | text | |
MD5:— | SHA256:— | |||
| 4060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\css-dk[1].css | text | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8CDE76B69A3854E3862D3A31D1197AF9 | binary | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\Local\Temp\TarAF43.tmp | cat | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2944 | netscanold.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 4060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\logo[1].svg | image | |
MD5:BB1C6CA739E0DEA73FD68D045EBEADBF | SHA256:E2395A59754E5E96975E9E2EE7A6EE608A7FA43CE03F18CFB683D2278F958FE4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | netscanold.exe | GET | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPBtQGfb0mZzVlbWDCo3nzrQA%3D%3D | US | der | 503 b | shared |
2492 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2944 | netscanold.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
2944 | netscanold.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?950f7c31d4c5a531 | DE | compressed | 4.70 Kb | whitelisted |
2944 | netscanold.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8203a0e989c95329 | DE | compressed | 59.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | netscanold.exe | 198.211.116.136:443 | www.softperfect.com | Digital Ocean, Inc. | US | suspicious |
2944 | netscanold.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
4060 | iexplore.exe | 198.211.116.136:443 | www.softperfect.com | Digital Ocean, Inc. | US | suspicious |
2944 | netscanold.exe | 184.24.77.67:80 | r3.o.lencr.org | Time Warner Cable Internet LLC | US | unknown |
2492 | iexplore.exe | 198.211.116.136:443 | www.softperfect.com | Digital Ocean, Inc. | US | suspicious |
2492 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2492 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2944 | netscanold.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.softperfect.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |