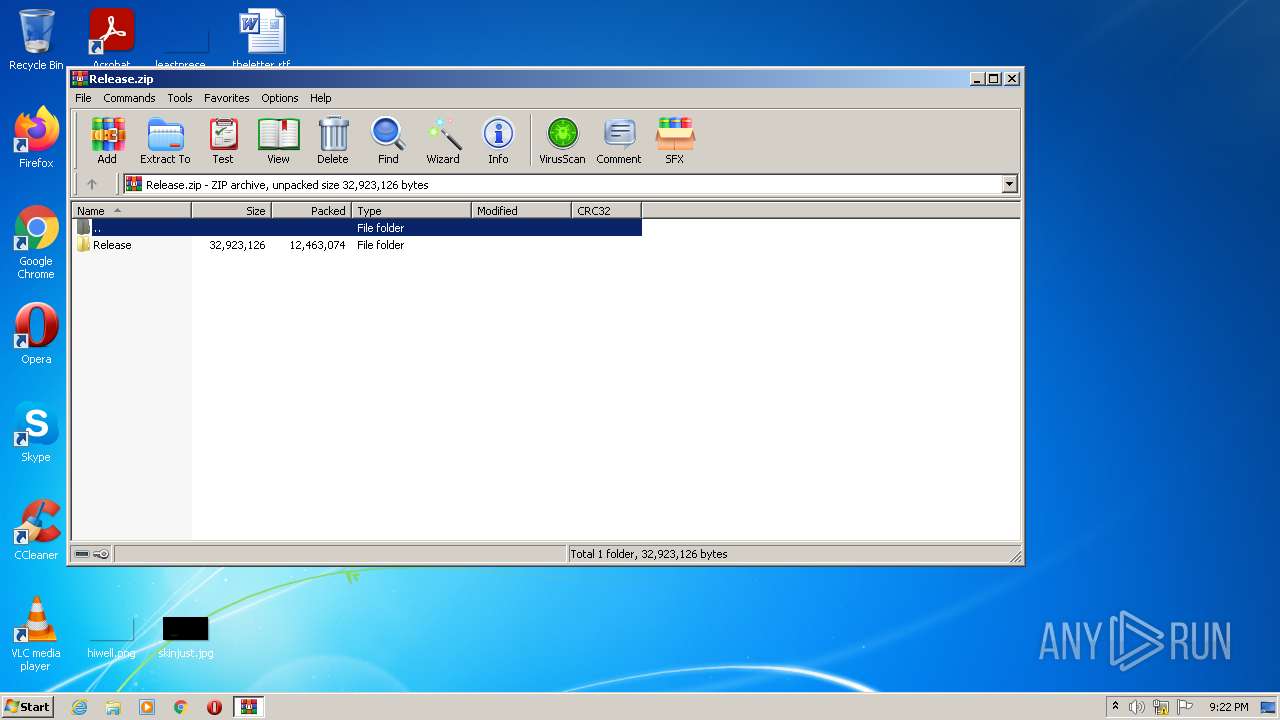
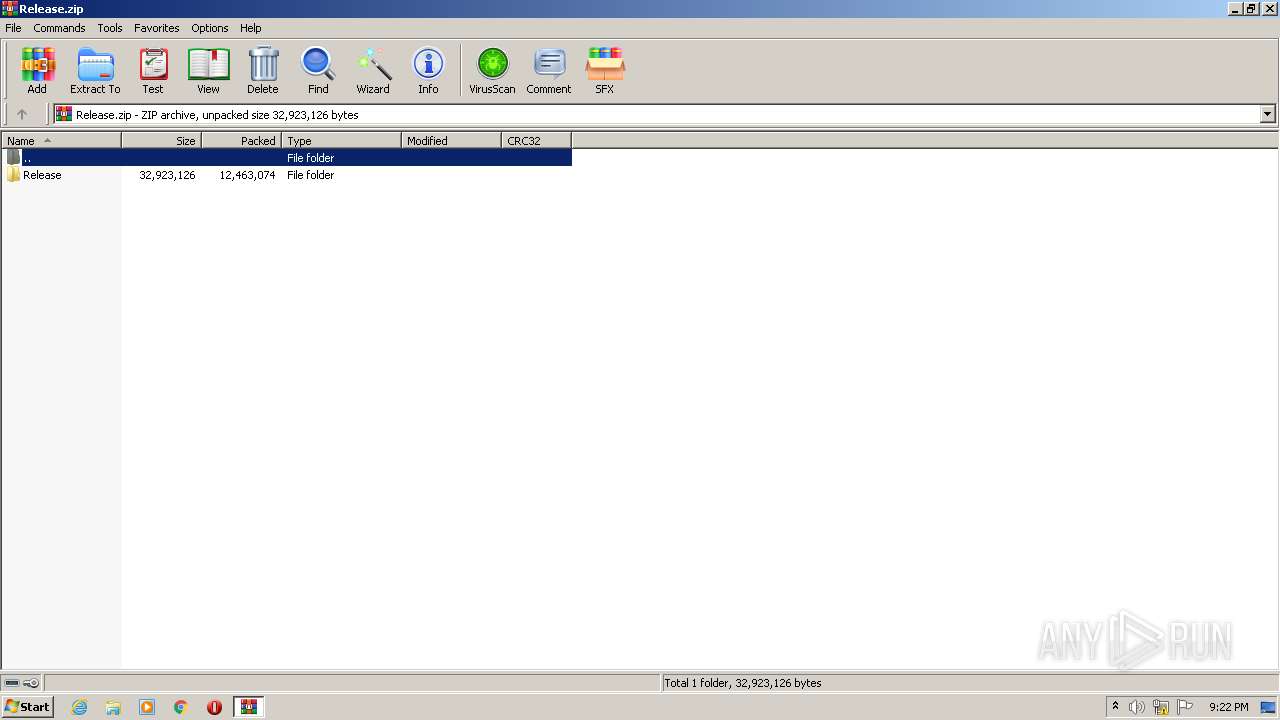
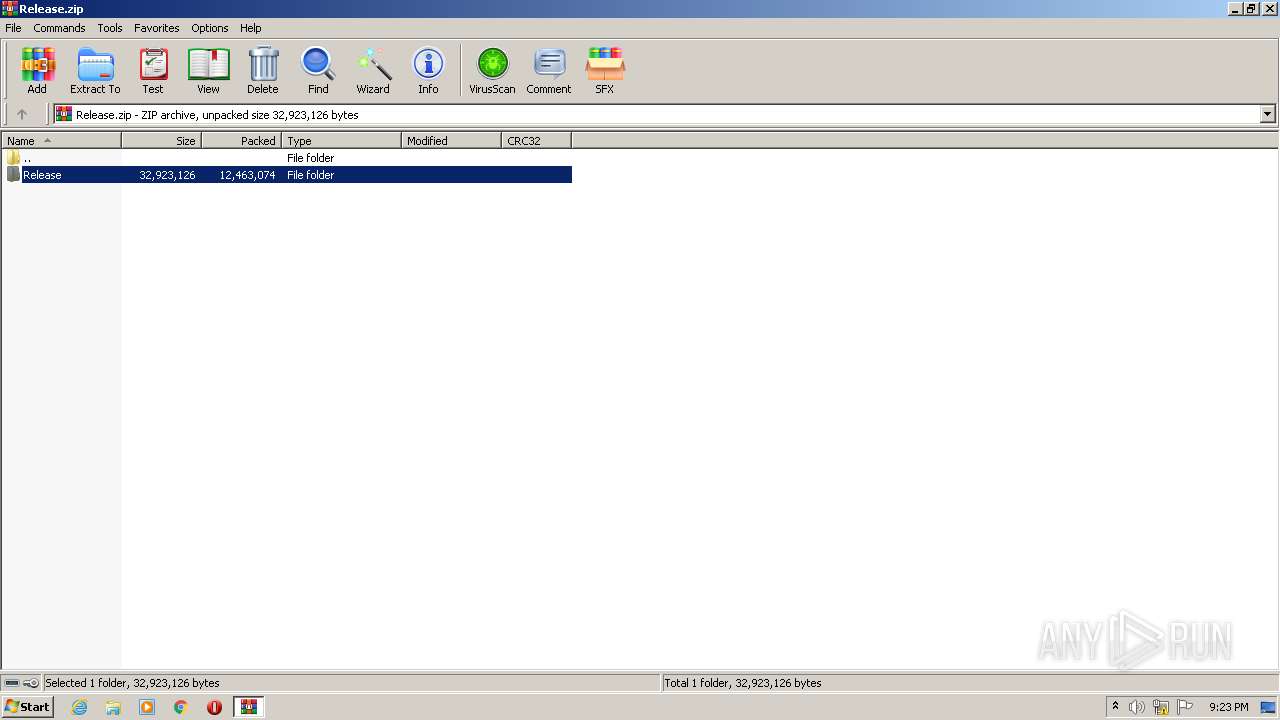
| File name: | Release.zip |
| Full analysis: | https://app.any.run/tasks/3fec42a8-be00-44d8-95ca-e358a7e05762 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 21:22:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0B77799FBBFEFF4CC608830AA4C543E8 |
| SHA1: | 10CF3C68218E9FEF2A370CDE0C0C249D078809C5 |
| SHA256: | 57289250571863ECF91CCF60CA6386DB00410E4401914AA5FF06728F8443DBAC |
| SSDEEP: | 196608:0XpwF21zF2cJ4IKKORJwfZ6o1NhH0hxrlaboAwlTwF215cEV2cuKfKKORJwFZ6mH:apwQ1B4IKBiR6otH0nrlaEAw5wQ13SKj |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3536)
- Etiff.exe (PID: 2984)
Application was dropped or rewritten from another process
- Etiff.exe (PID: 2984)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3624)
- Etiff.exe (PID: 2984)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3624)
Checks supported languages
- WinRAR.exe (PID: 3624)
- Etiff.exe (PID: 2984)
Drops a file with too old compile date
- WinRAR.exe (PID: 3624)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3624)
Reads Environment values
- Etiff.exe (PID: 2984)
Reads default file associations for system extensions
- Etiff.exe (PID: 2984)
INFO
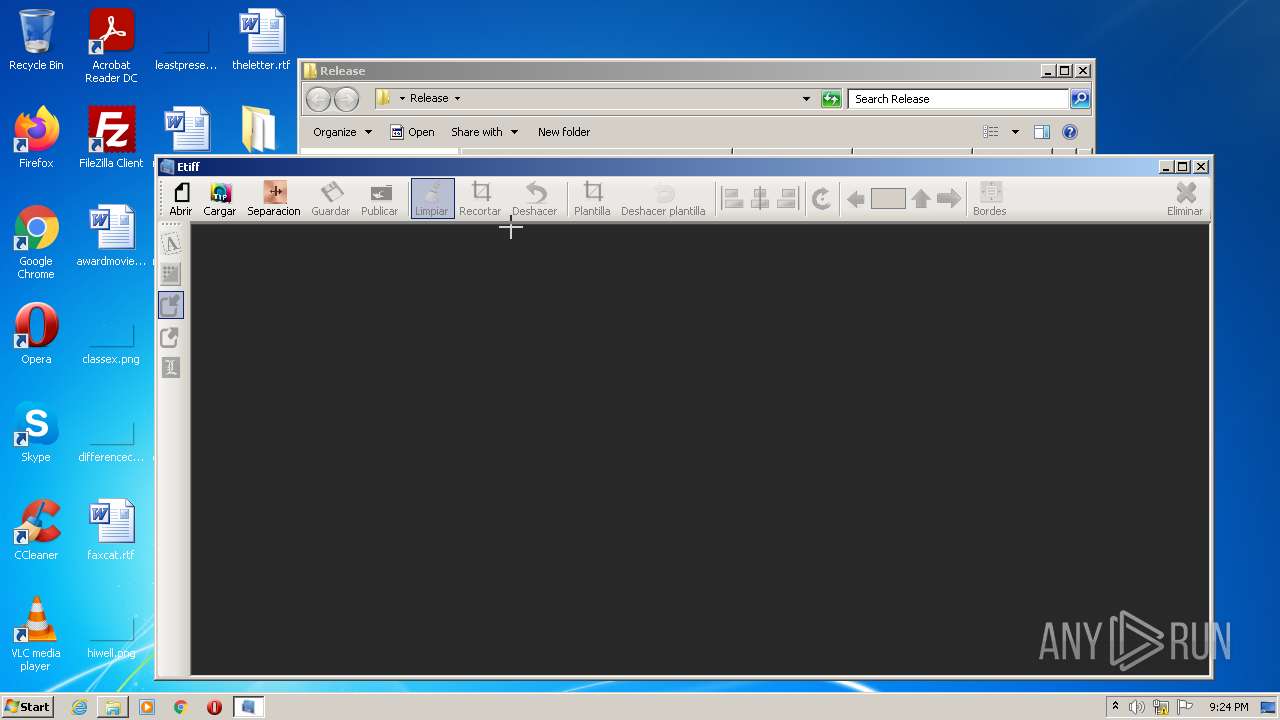
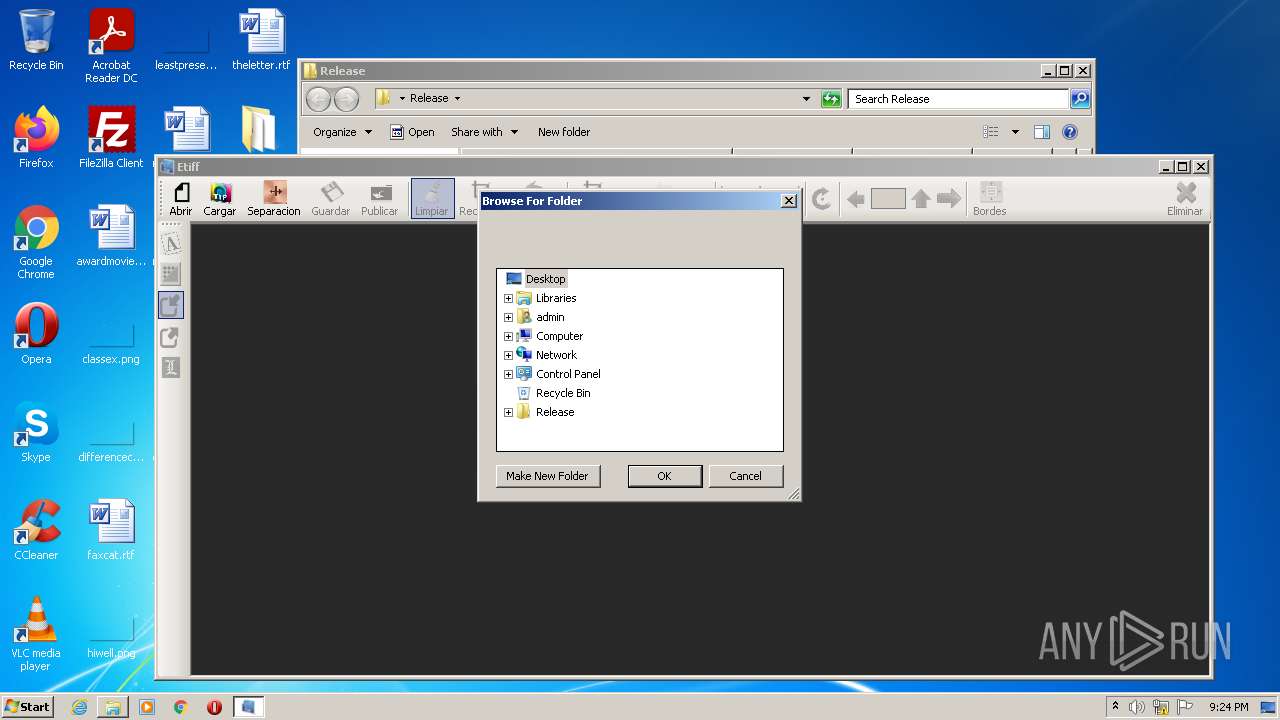
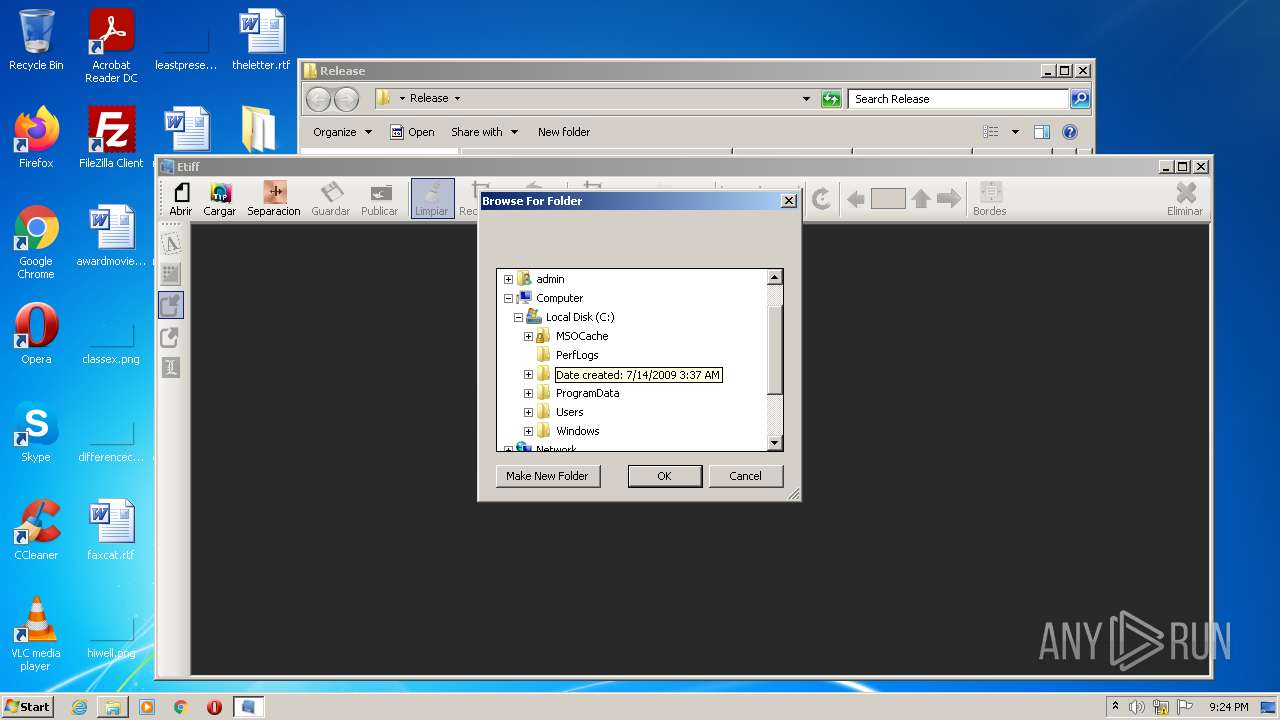
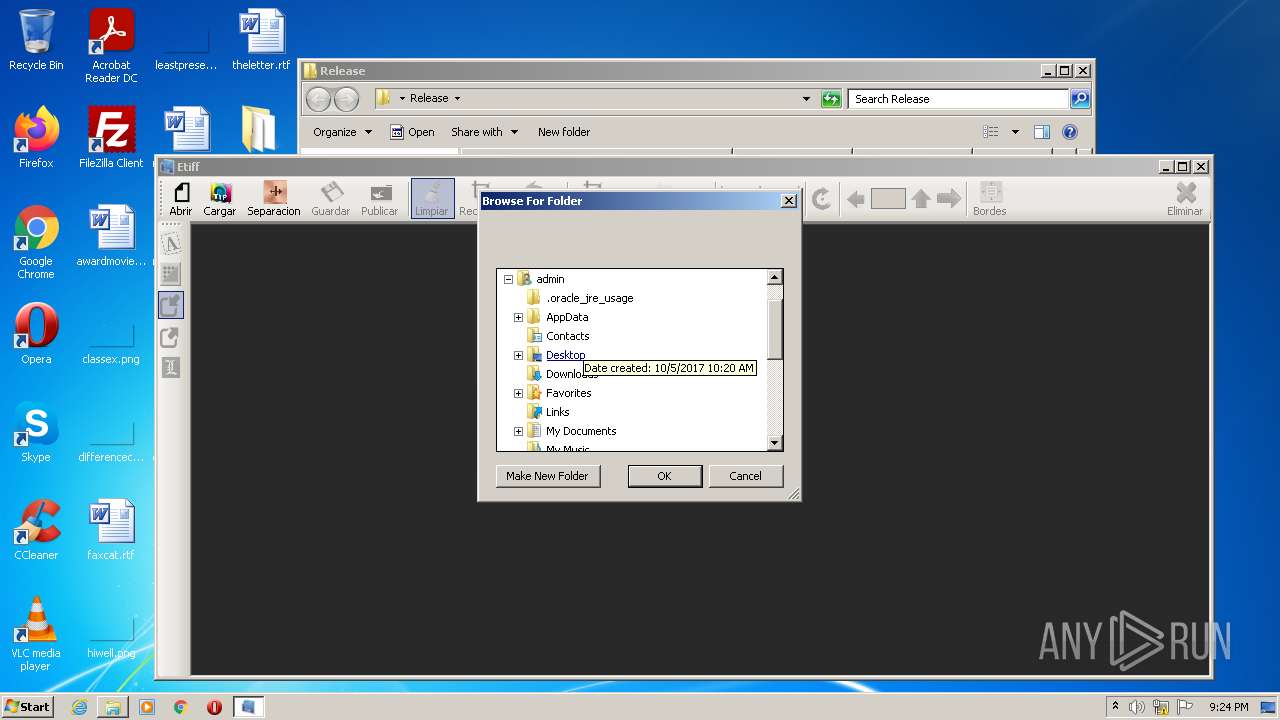
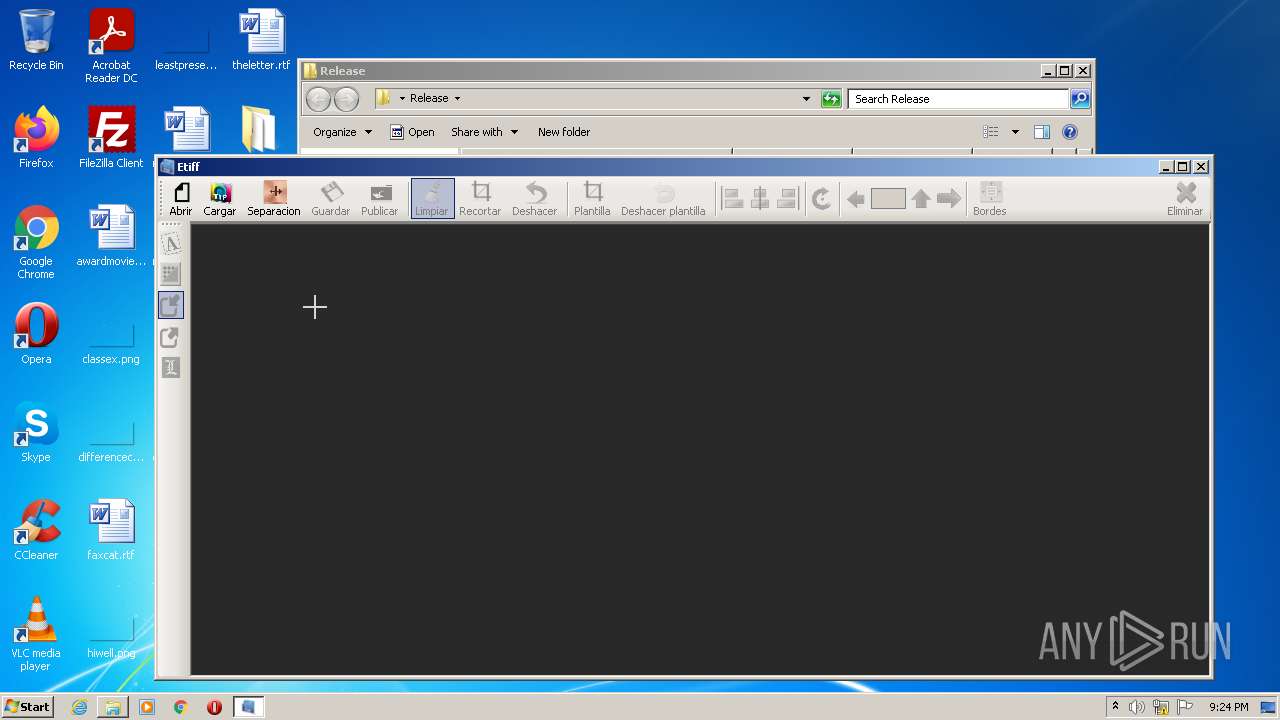
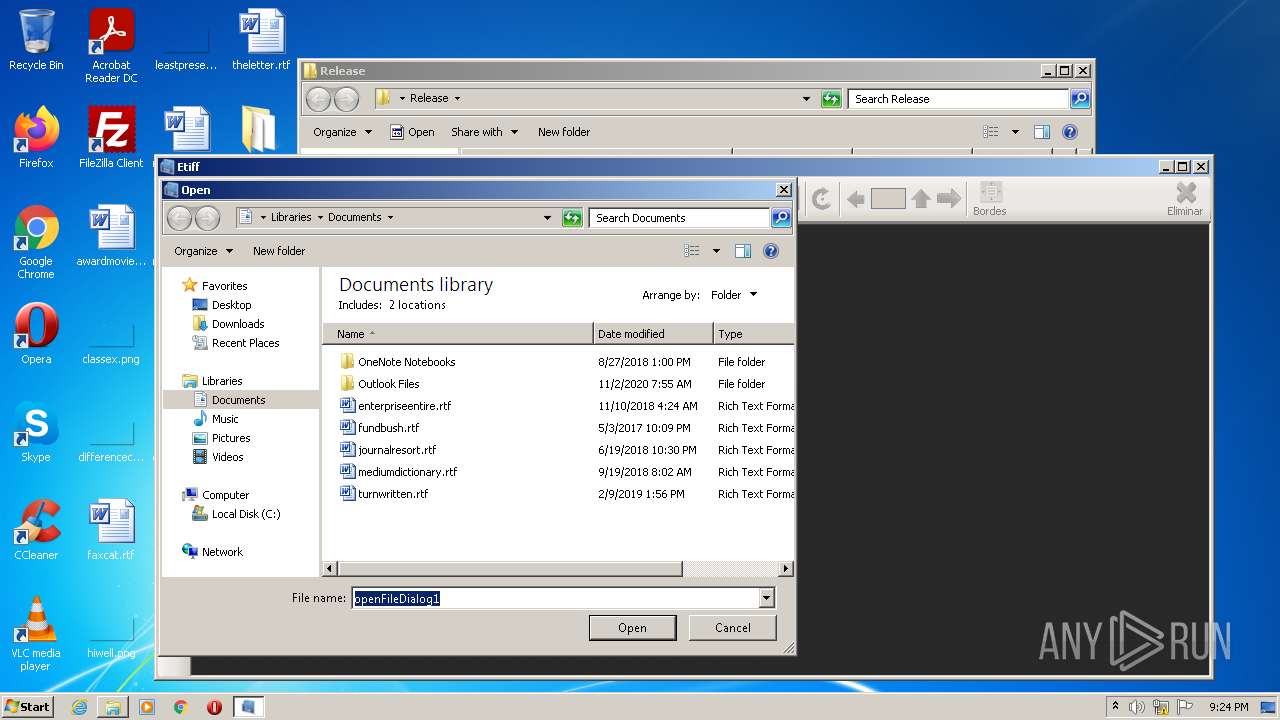
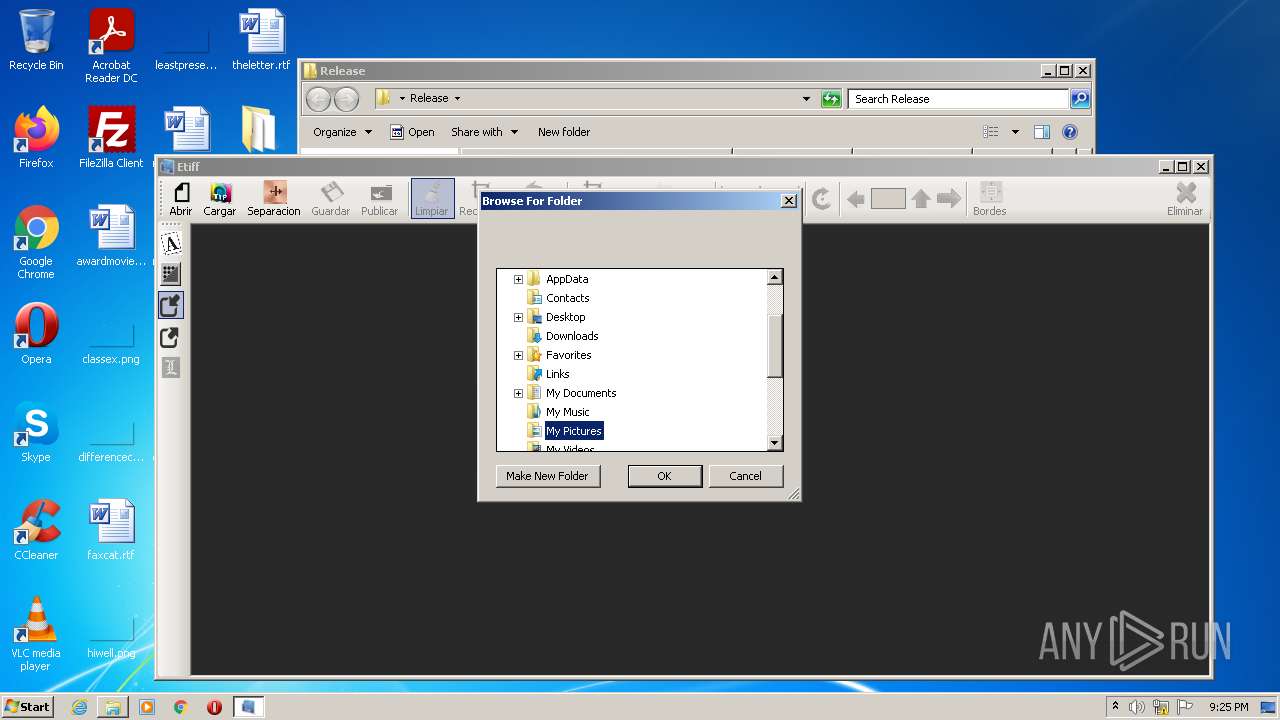
Manual execution by user
- Etiff.exe (PID: 2984)
Reads settings of System Certificates
- Etiff.exe (PID: 2984)
Checks Windows Trust Settings
- Etiff.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Release/mysql.data.dll |
|---|---|
| ZipUncompressedSize: | 315392 |
| ZipCompressedSize: | 123983 |
| ZipCRC: | 0x0f3da4f2 |
| ZipModifyDate: | 2022:01:14 14:53:13 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0008 |
| ZipRequiredVersion: | 20 |
Total processes
39
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
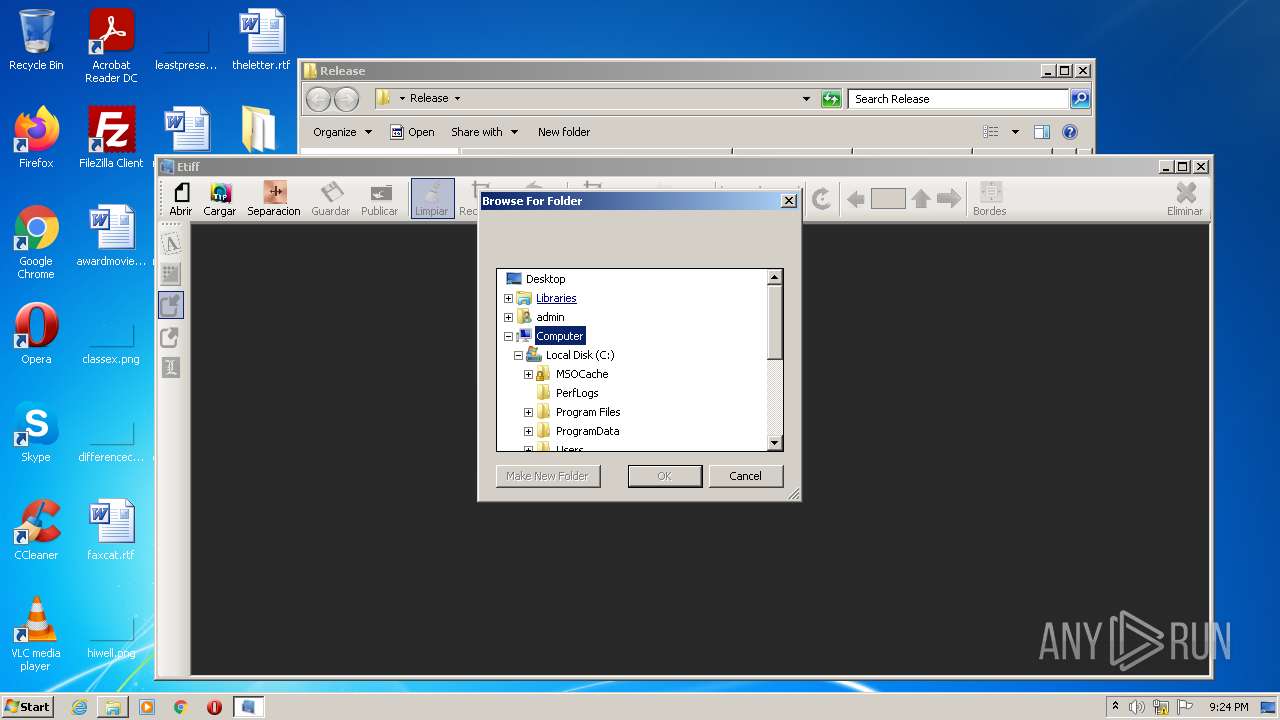
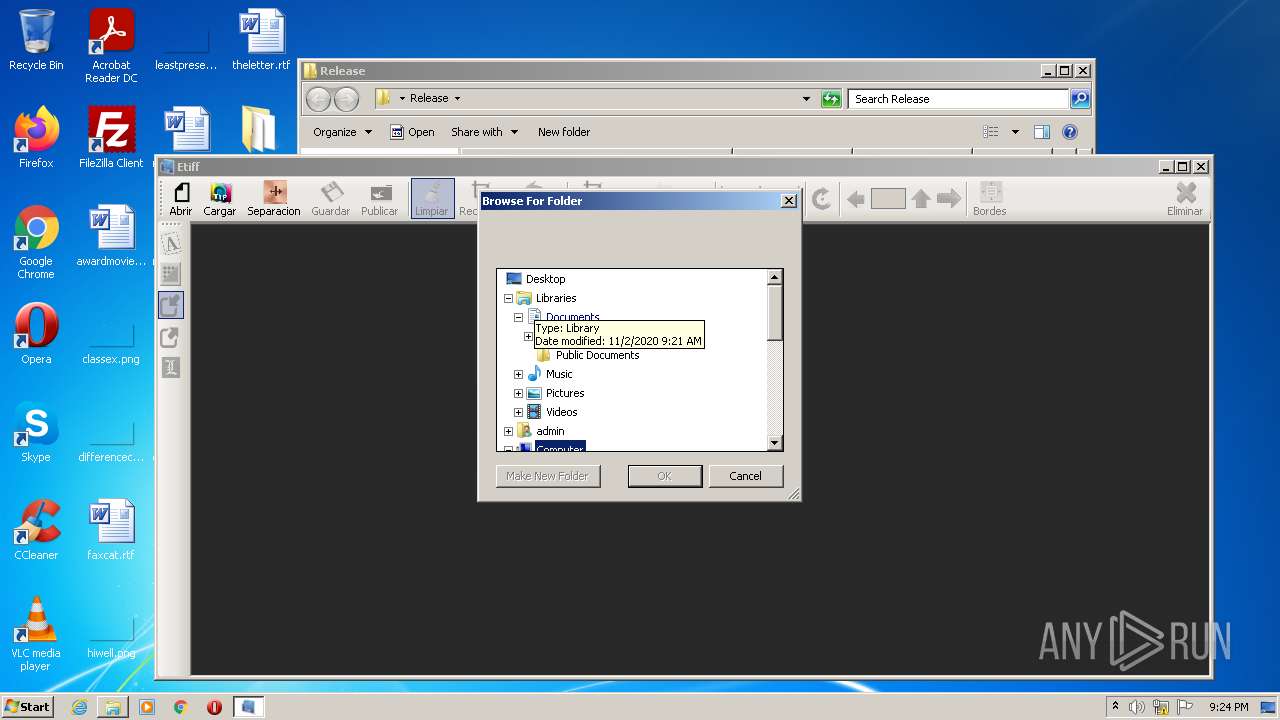
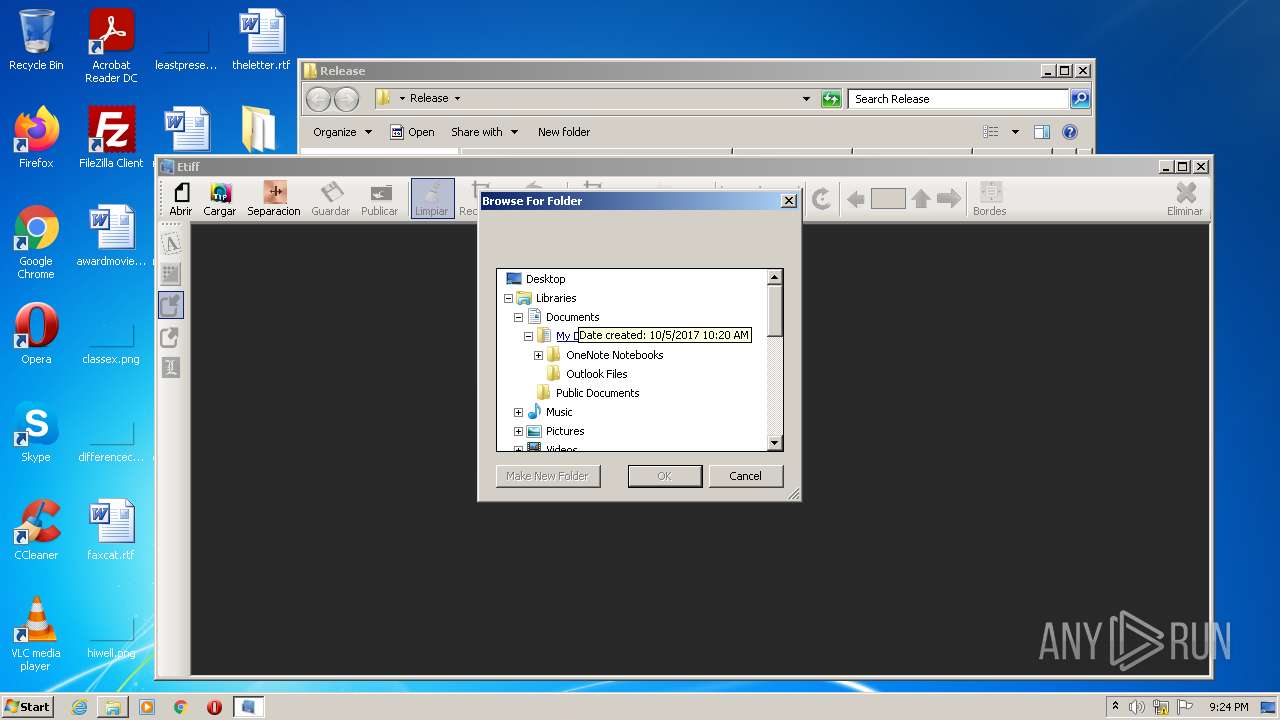
| 2984 | "C:\Users\admin\Desktop\Release\Etiff.exe" | C:\Users\admin\Desktop\Release\Etiff.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Etiff Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3536 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
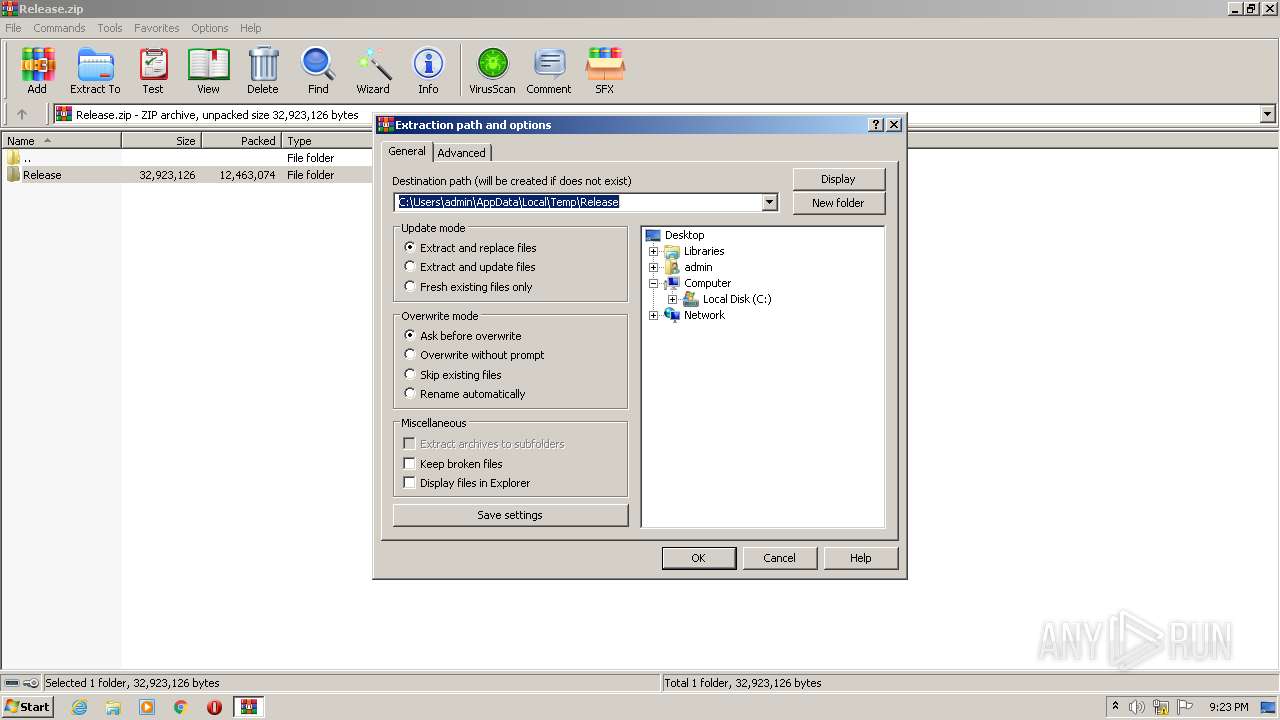
| 3624 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Release.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
11 492
Read events
11 247
Write events
241
Delete events
4
Modification events
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Release.zip | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
35
Suspicious files
0
Text files
13
Unknown types
1
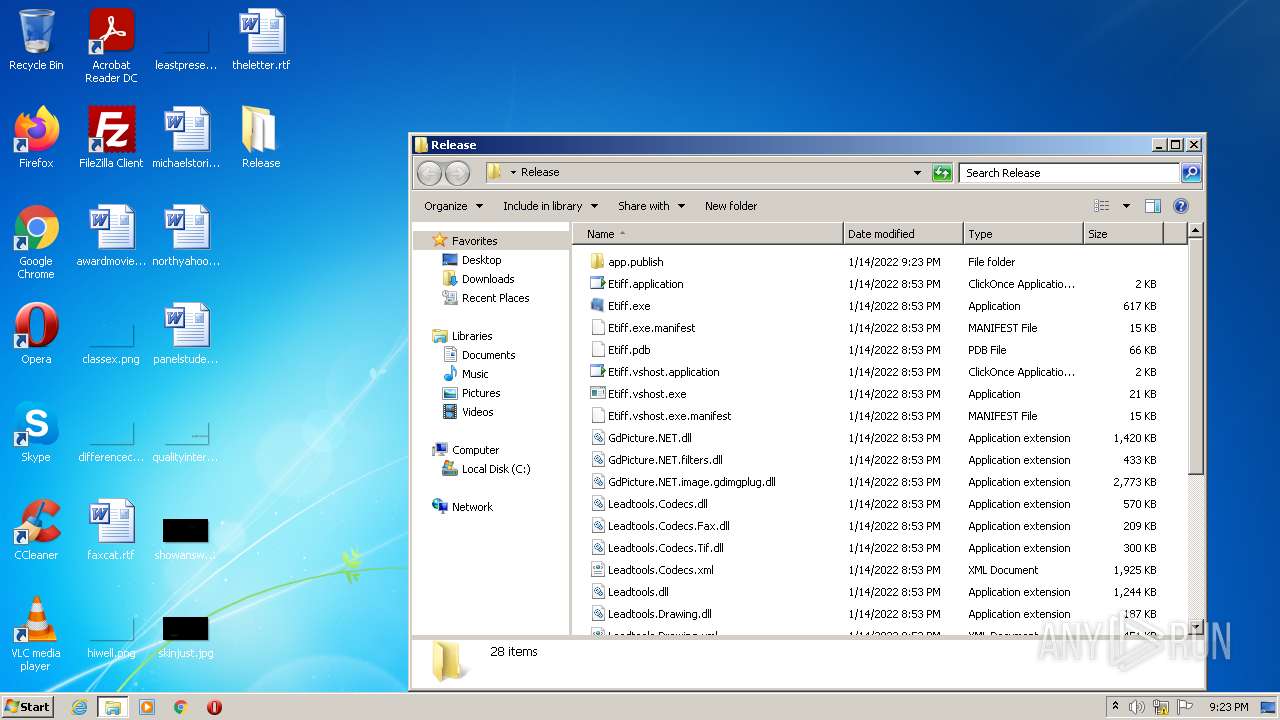
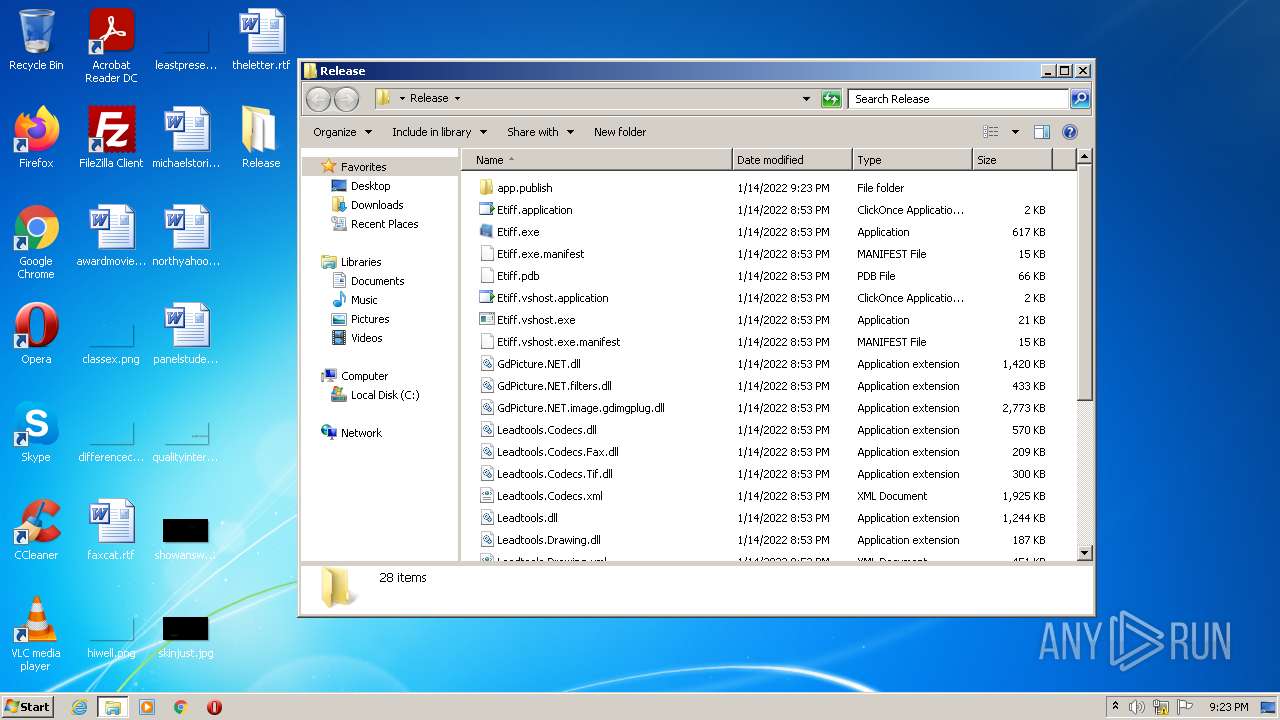
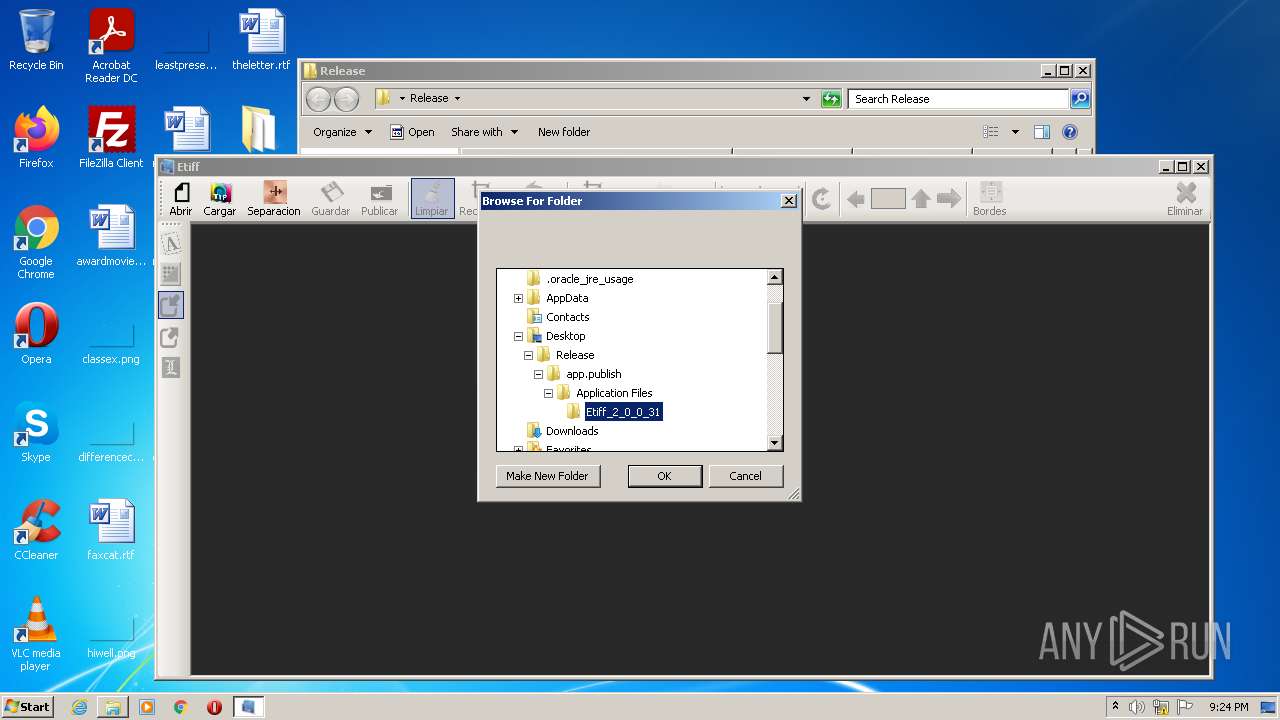
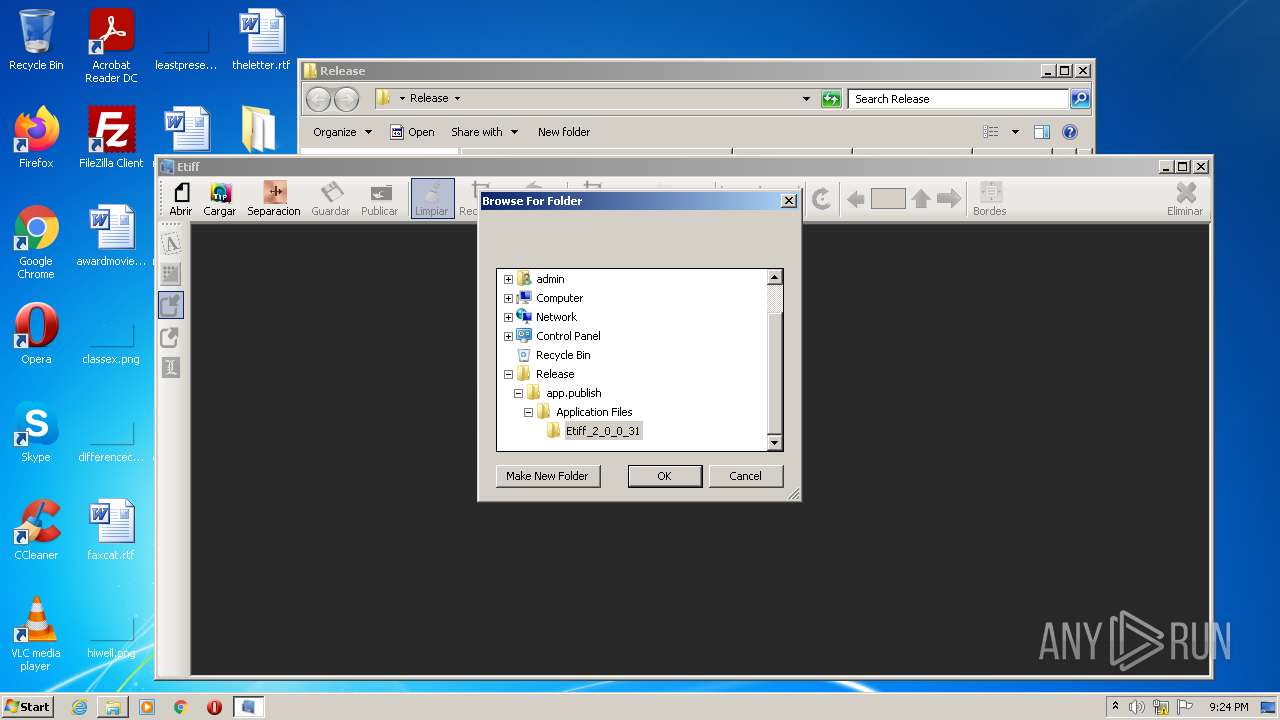
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Etiff.application | xml | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\TiffCrop.exe.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\Leadtools.Codecs.Tif.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\Leadtools.ImageProcessing.Core.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\Leadtools.Codecs.Fax.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\GdPicture.NET.image.gdimgplug.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\GdPicture.NET.wia.gateway.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\GdPicture.NET.dll.deploy | executable | |
MD5:— | SHA256:— | |||
| 3624 | WinRAR.exe | C:\Users\admin\Desktop\Release\app.publish\Application Files\Etiff_2_0_0_31\GdPicture.NET.barcode.1d.writer.dll.deploy | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.67:62825 | — | — | — | malicious |
— | — | 192.168.100.67:63050 | — | — | — | malicious |
— | — | 192.168.100.67:63341 | — | — | — | malicious |
— | — | 192.168.100.67:63342 | — | — | — | malicious |
— | — | 192.168.100.67:63602 | — | — | — | malicious |
— | — | 192.168.100.67:64400 | — | — | — | malicious |
— | — | 192.168.100.67:63051 | — | — | — | malicious |
— | — | 192.168.100.67:63603 | — | — | — | malicious |
— | — | 192.168.100.67:64401 | — | — | — | malicious |
DNS requests
Threats
Process | Message |
|---|---|
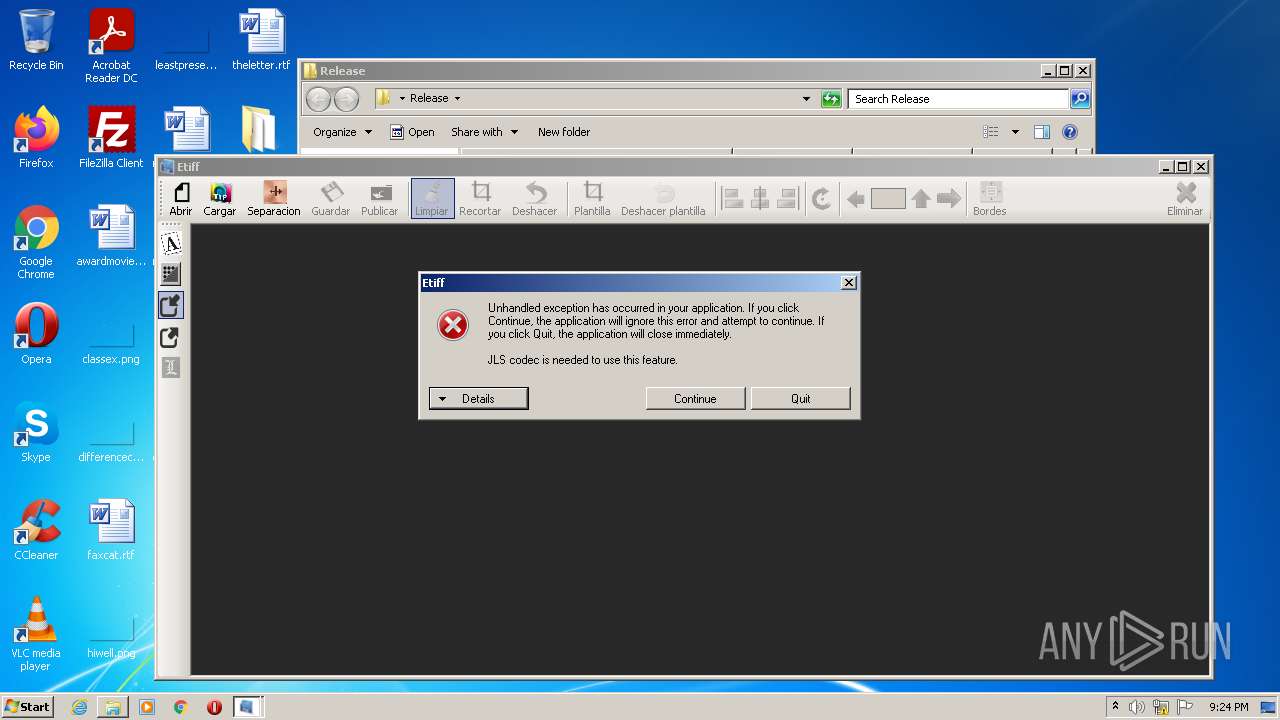
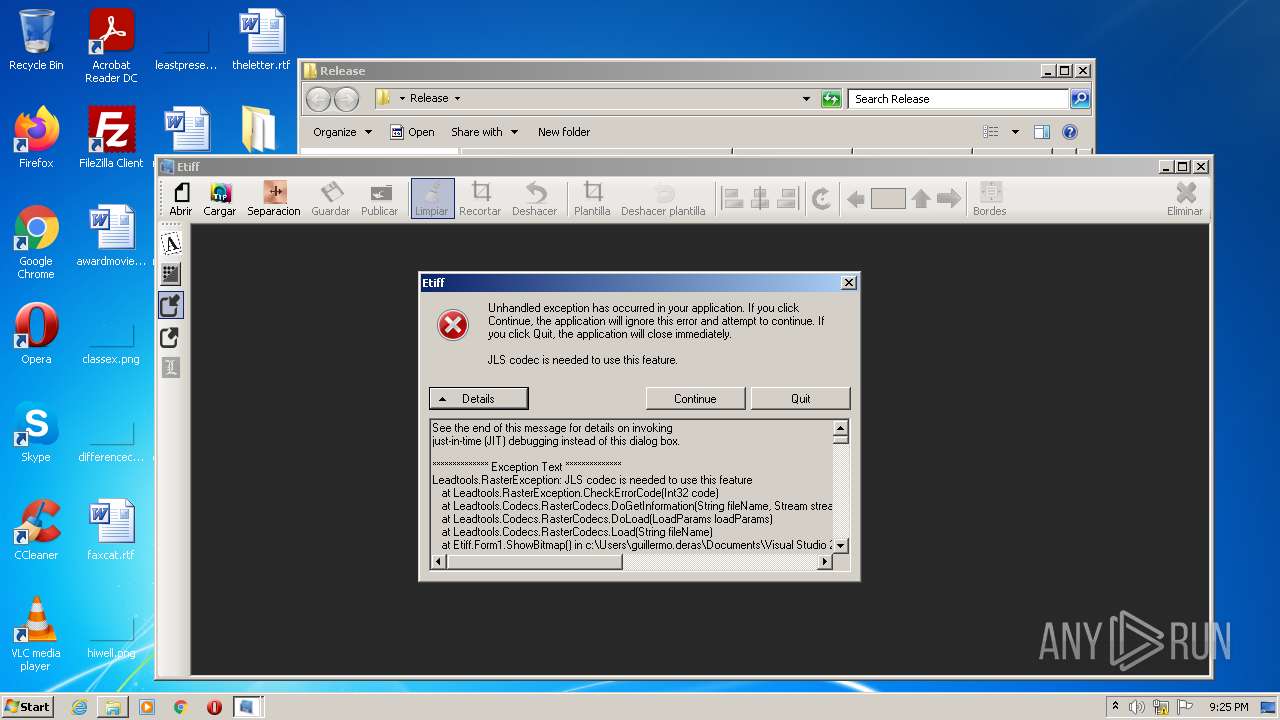
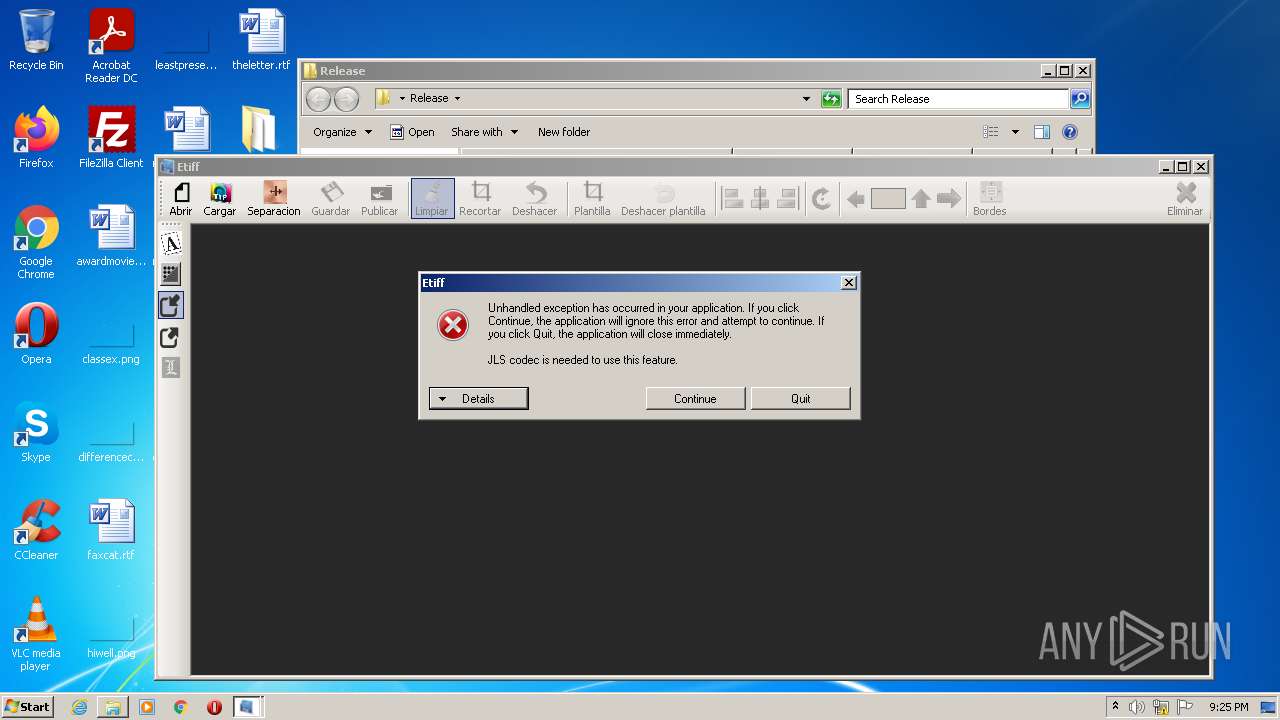
Etiff.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Etiff.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Etiff.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Etiff.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Etiff.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Etiff.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Etiff.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Etiff.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Etiff.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Etiff.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|