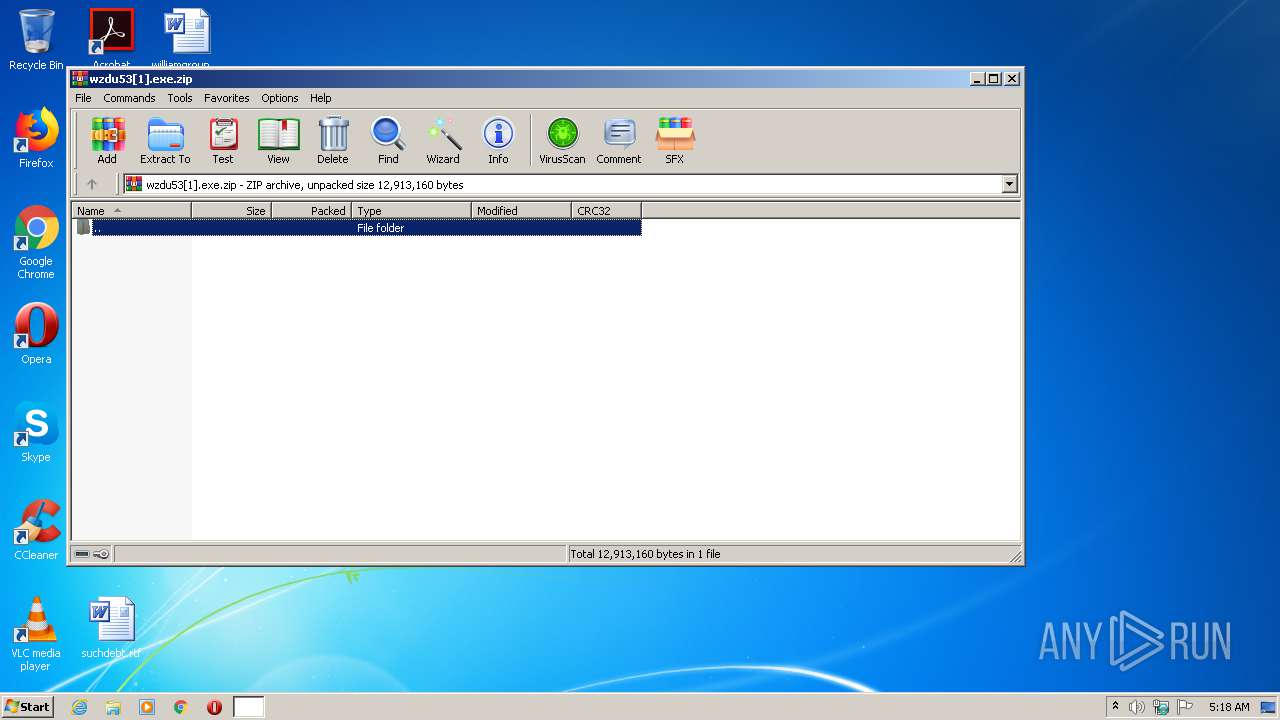
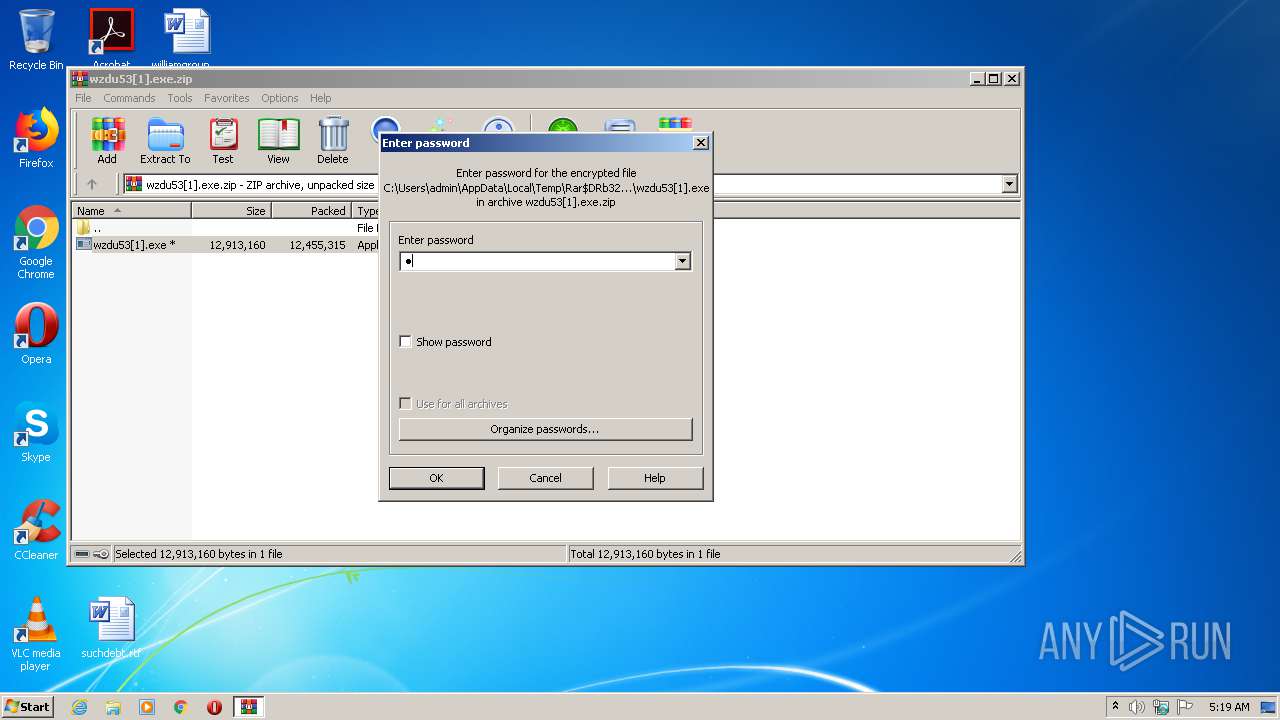
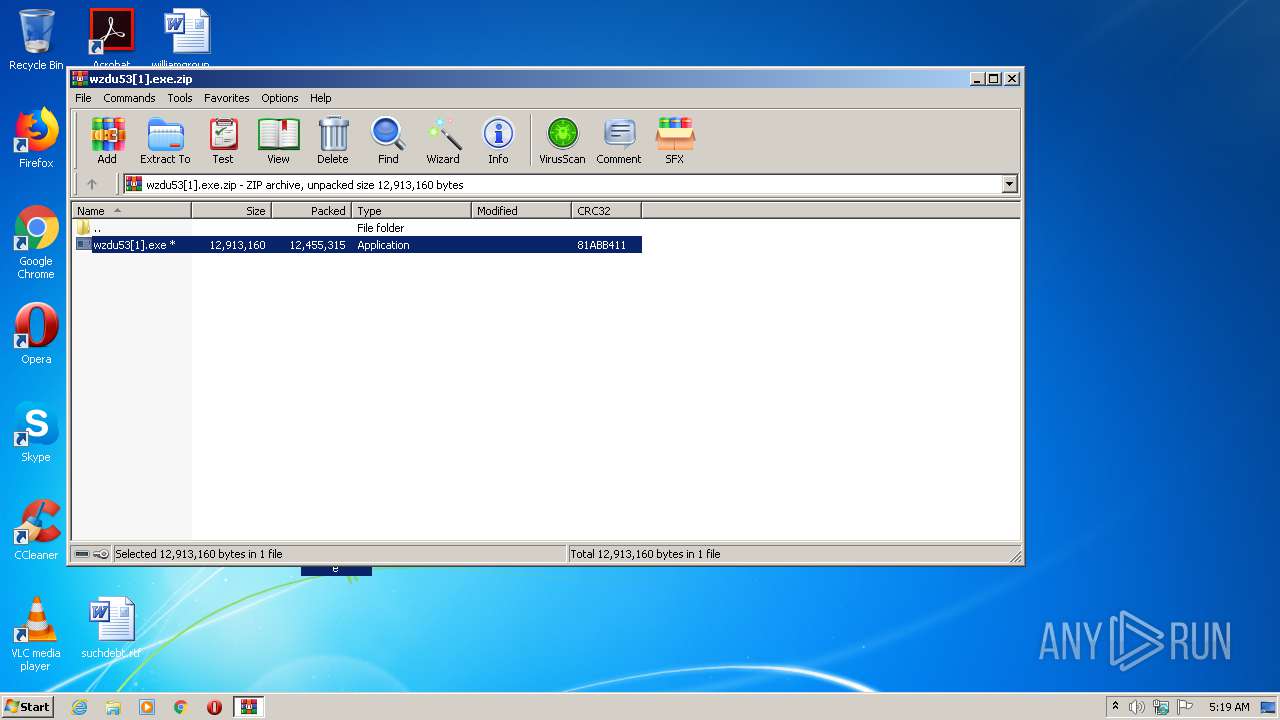
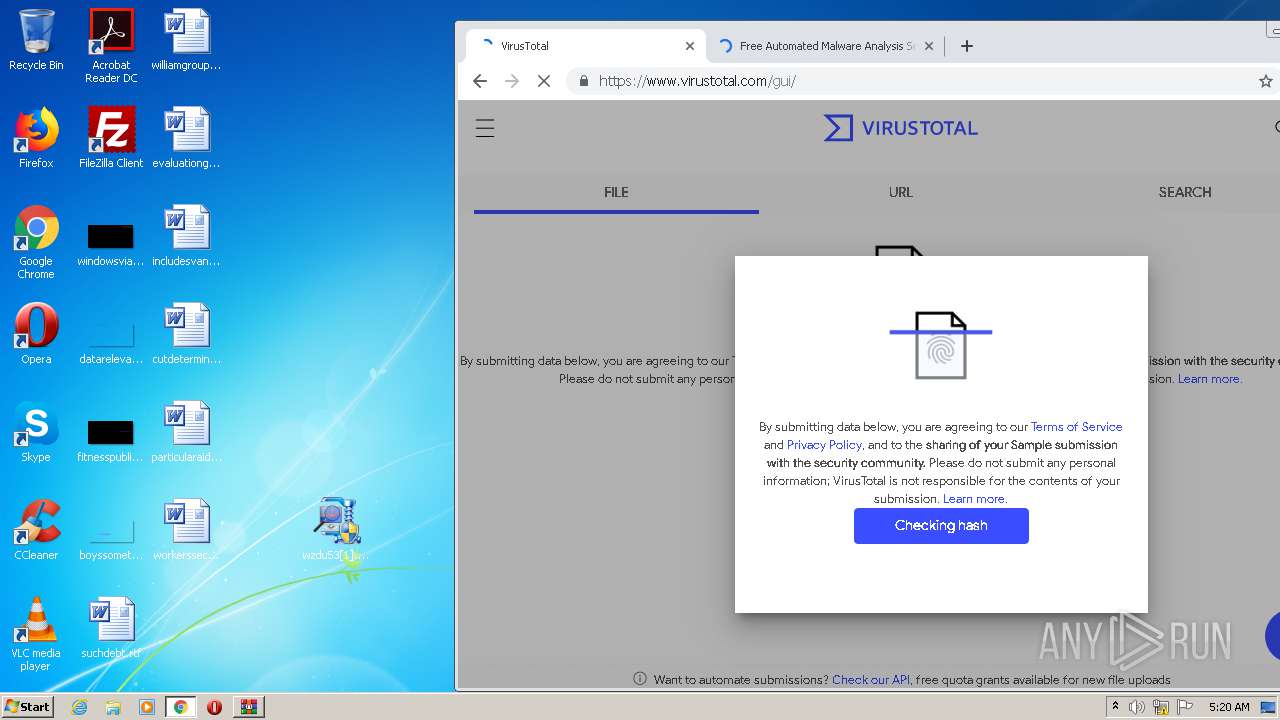
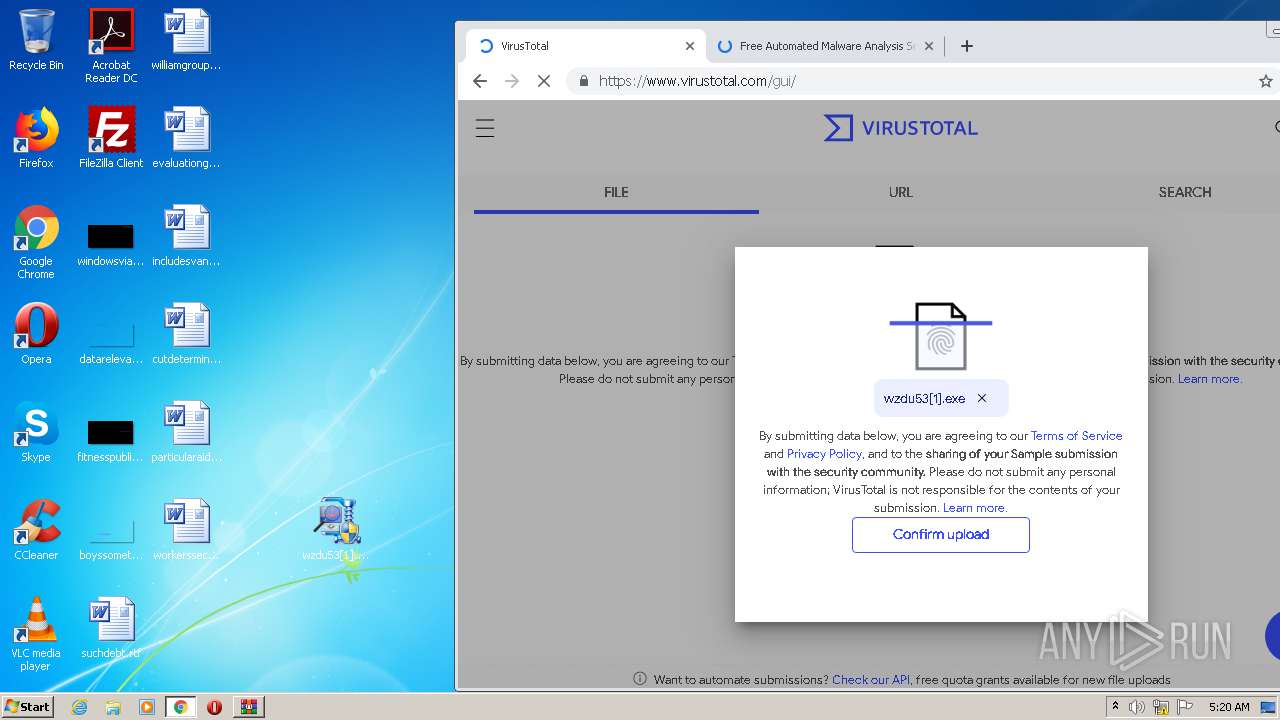
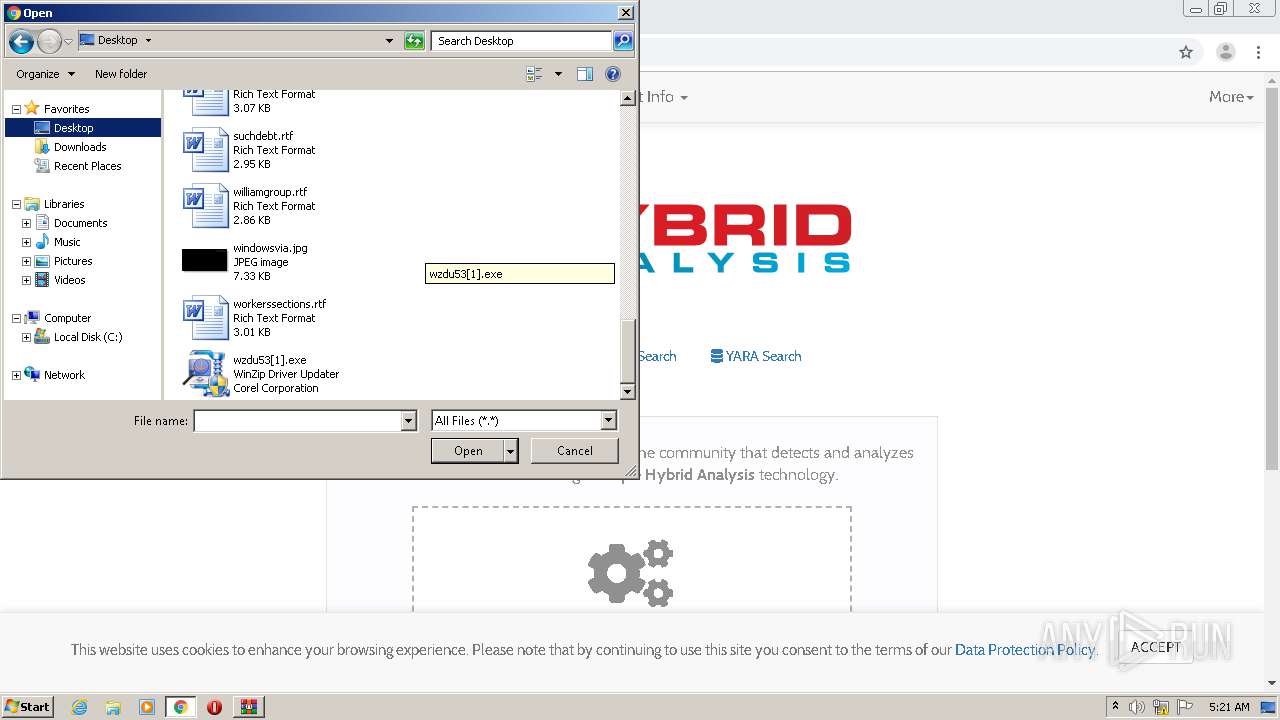
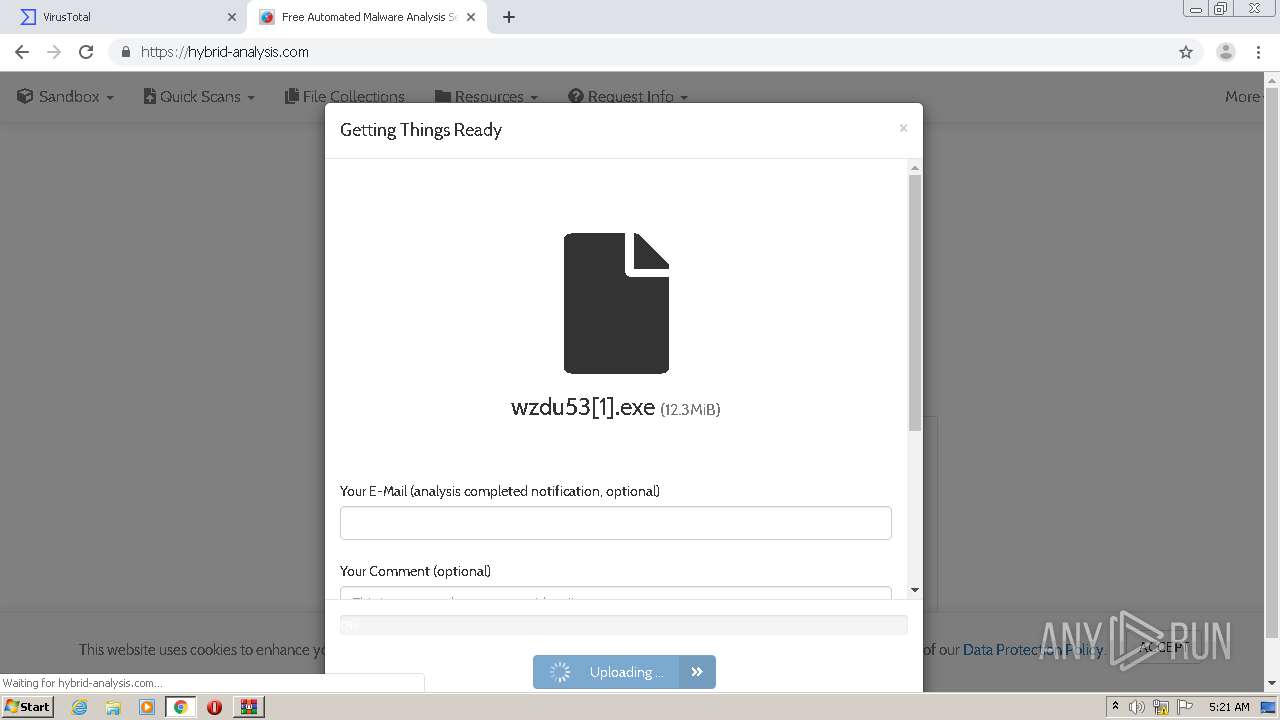
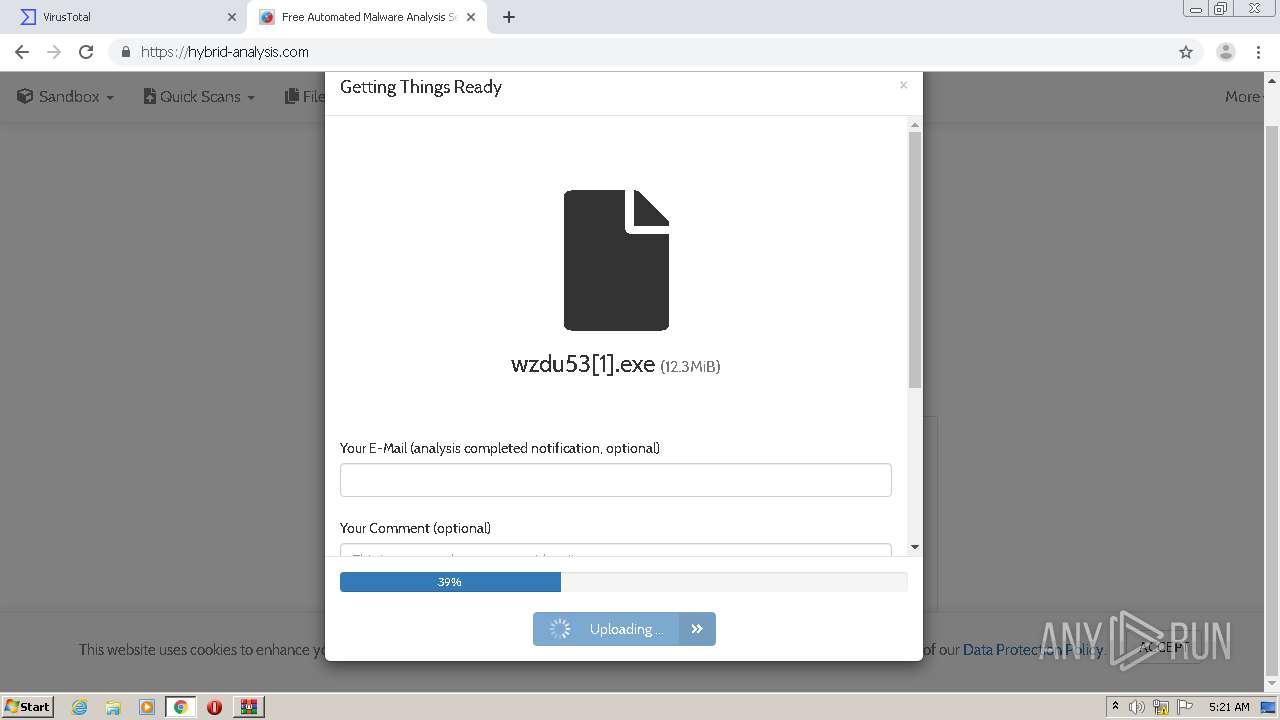
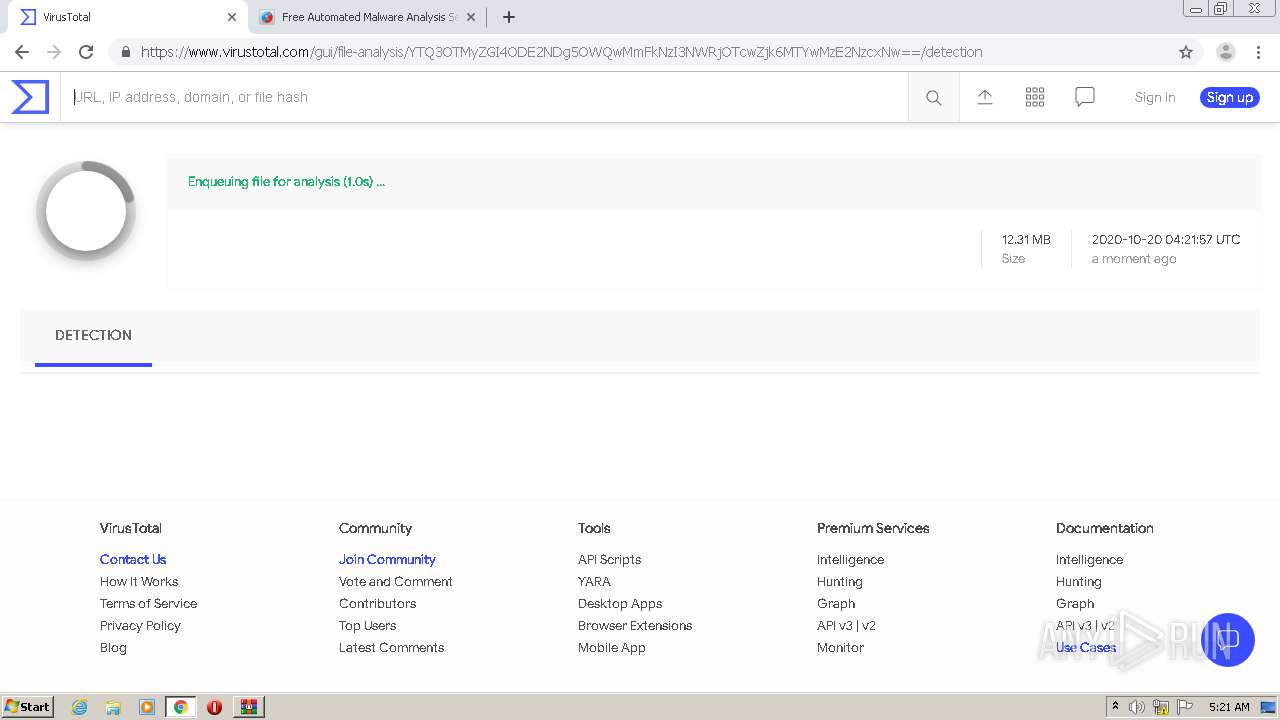
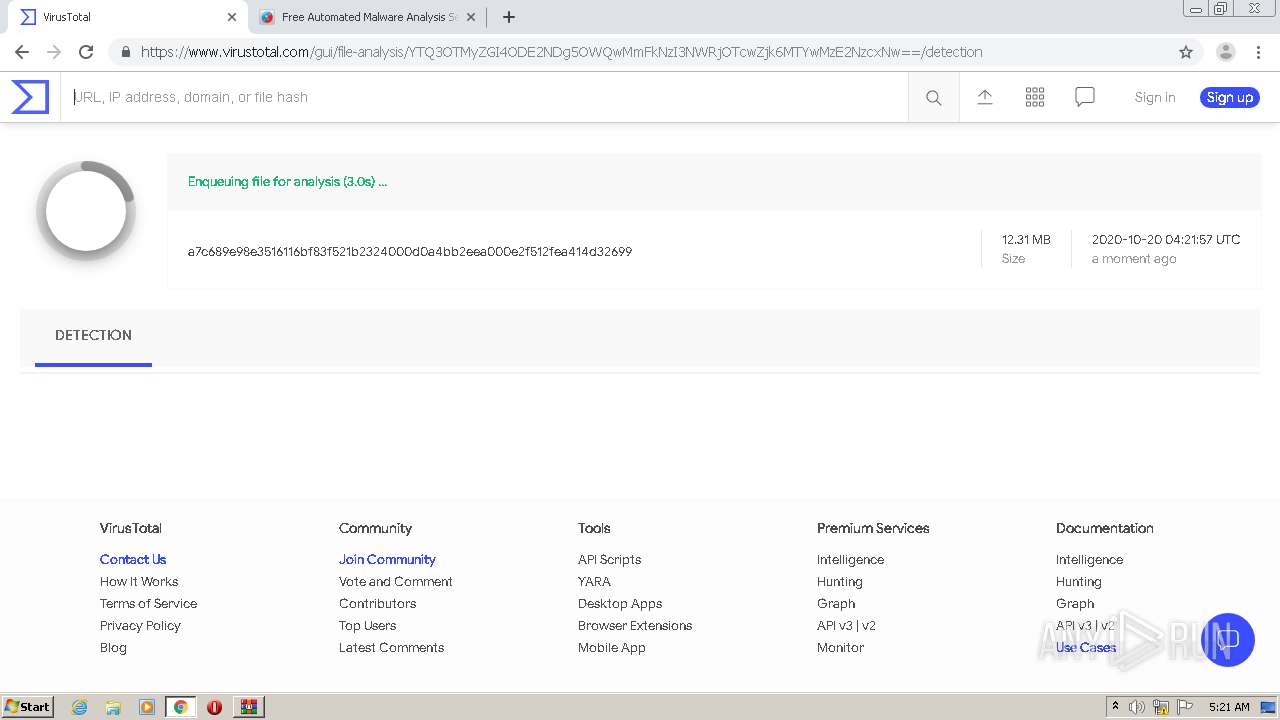
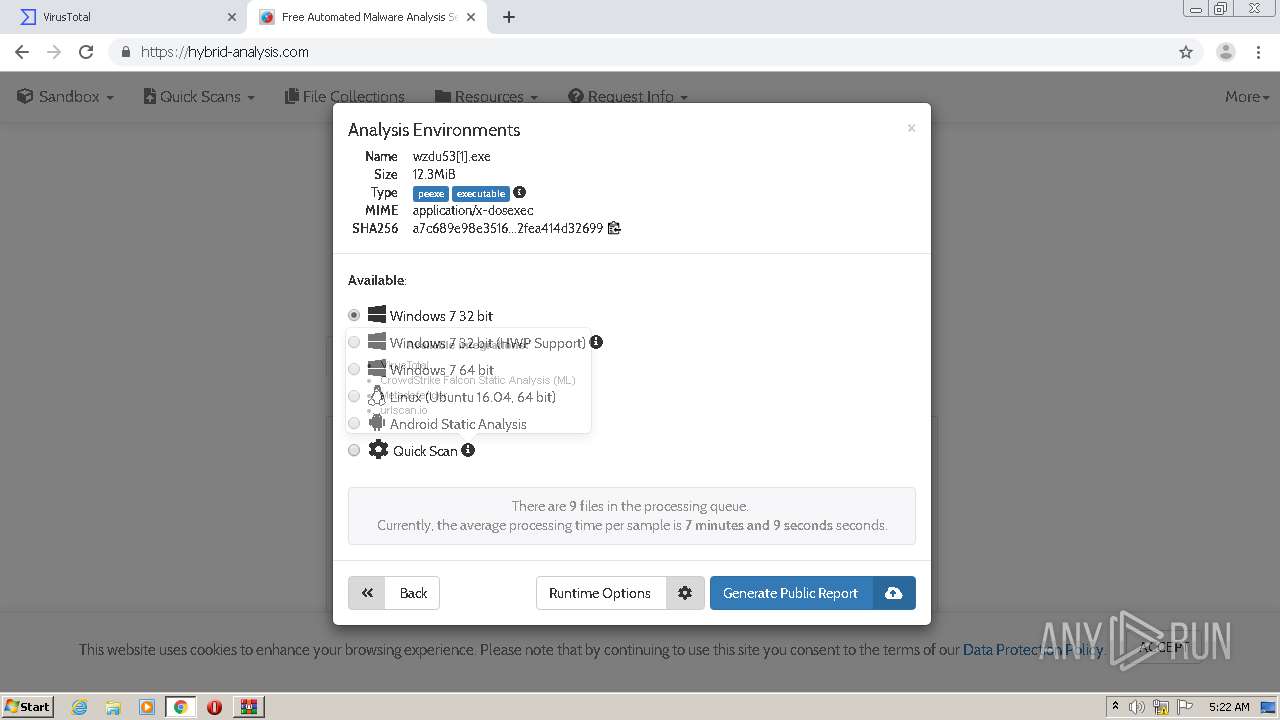
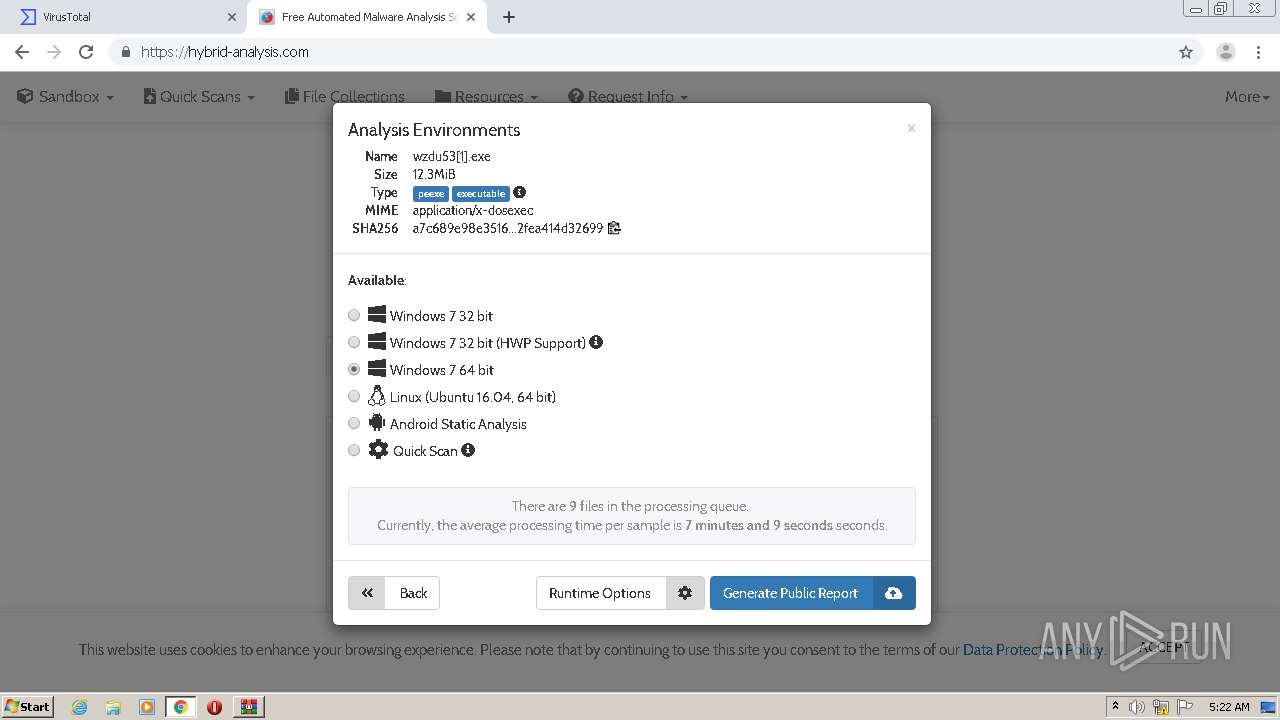
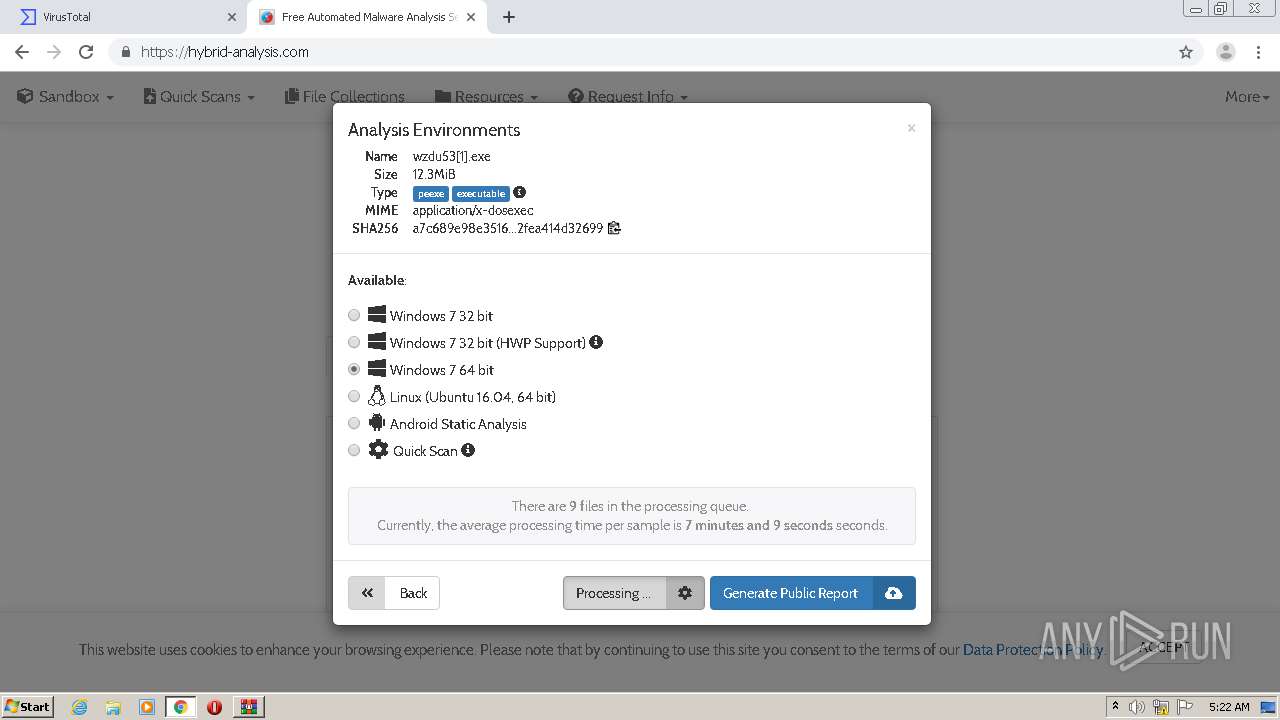
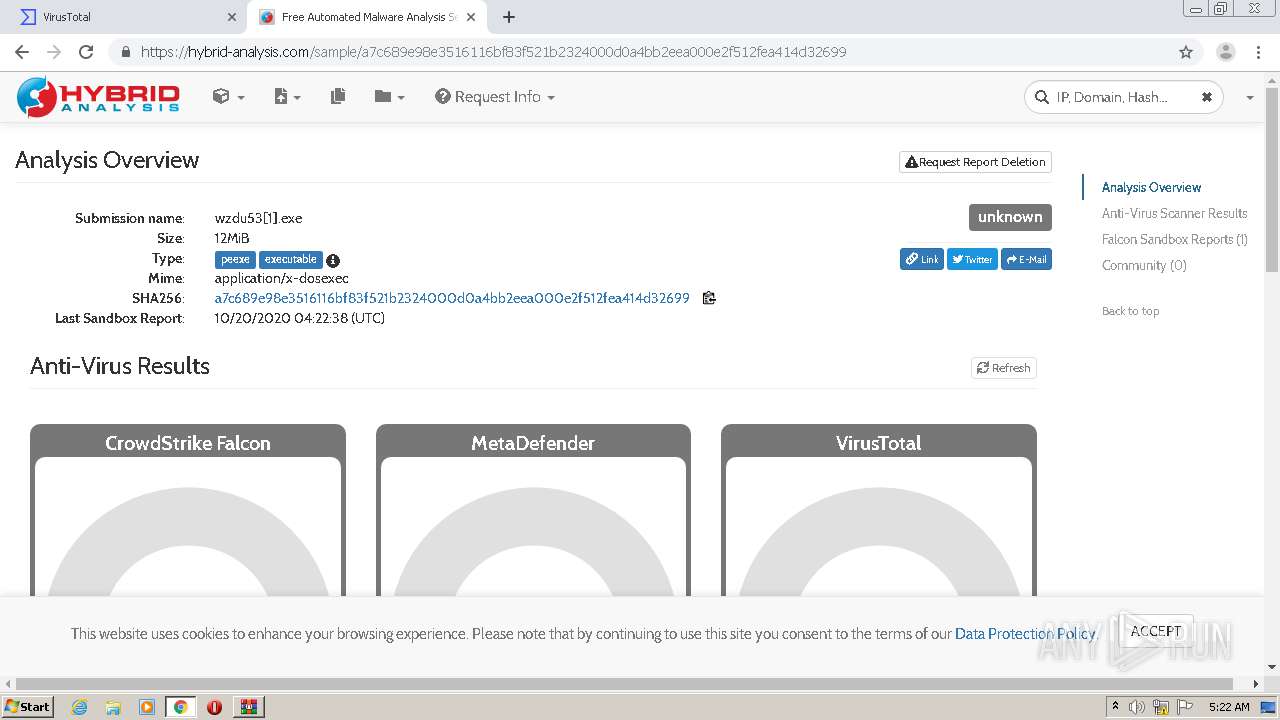
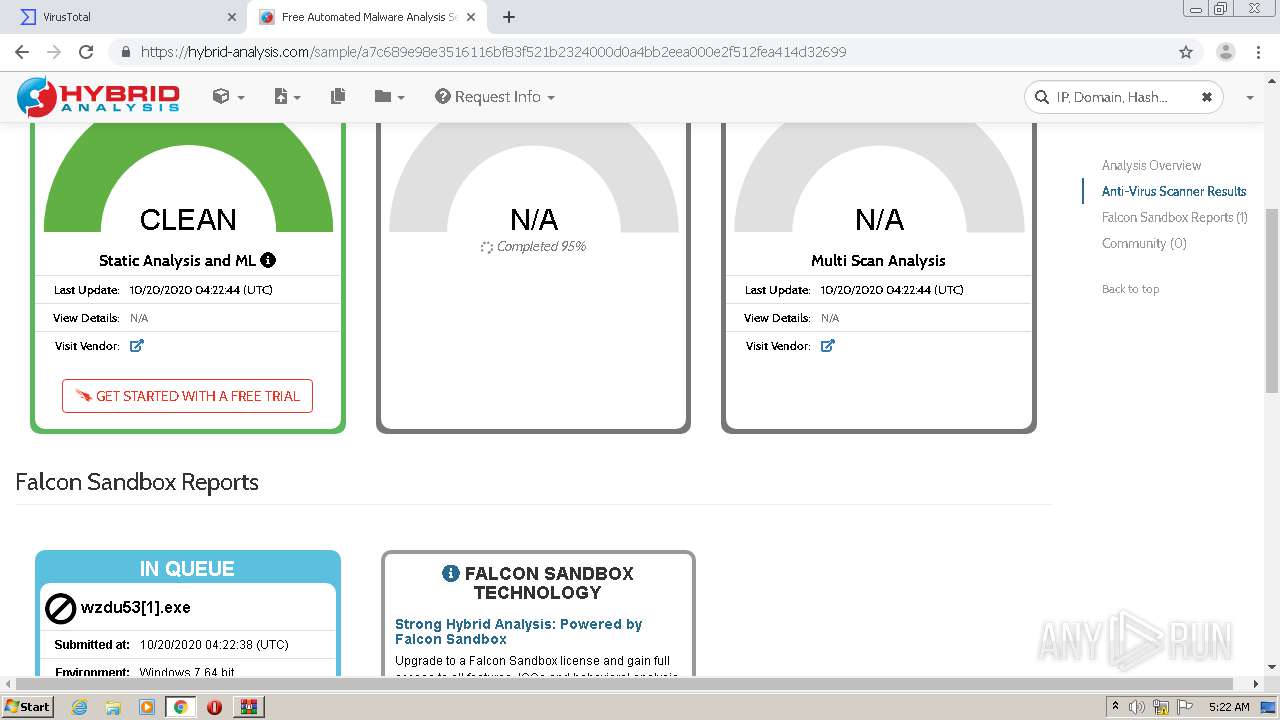
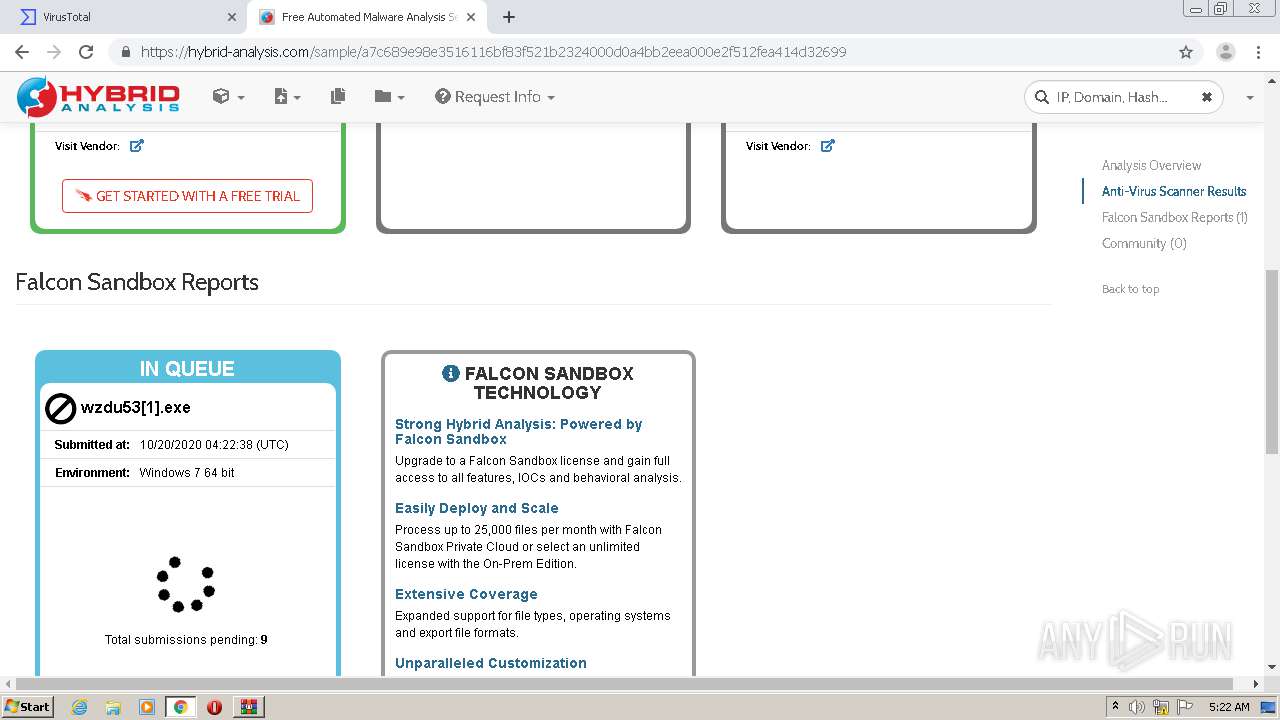
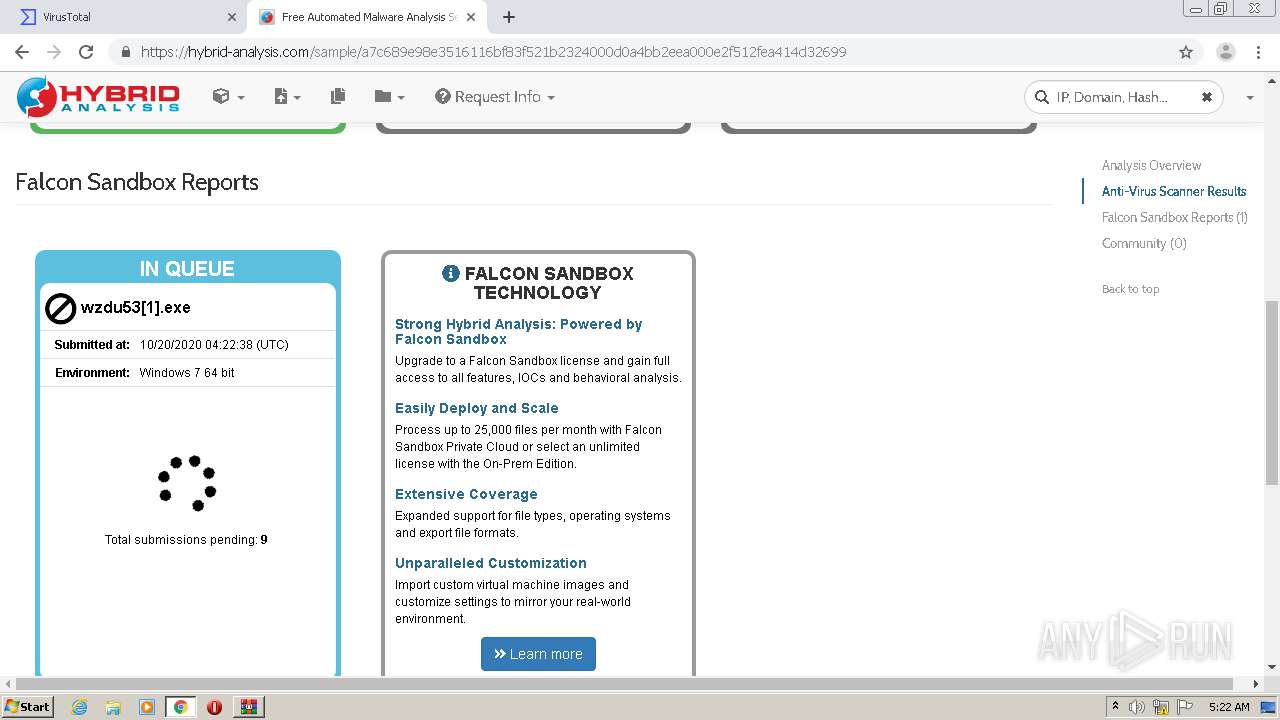
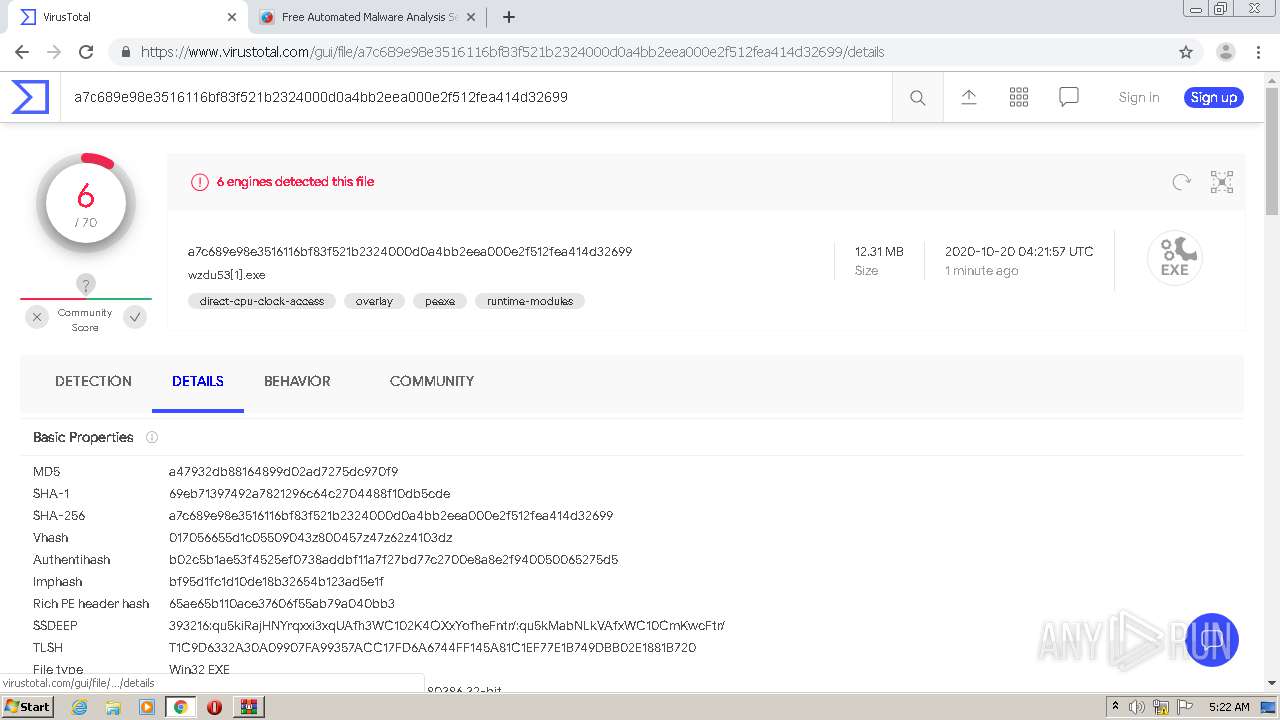
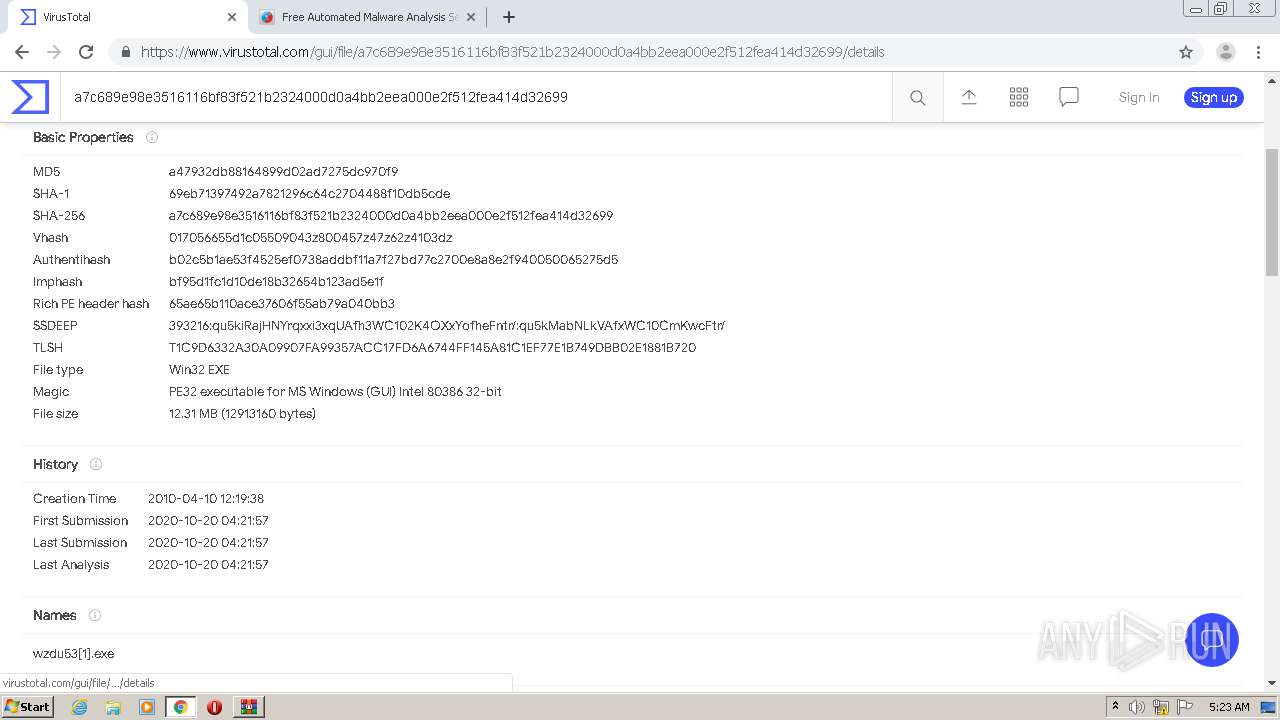
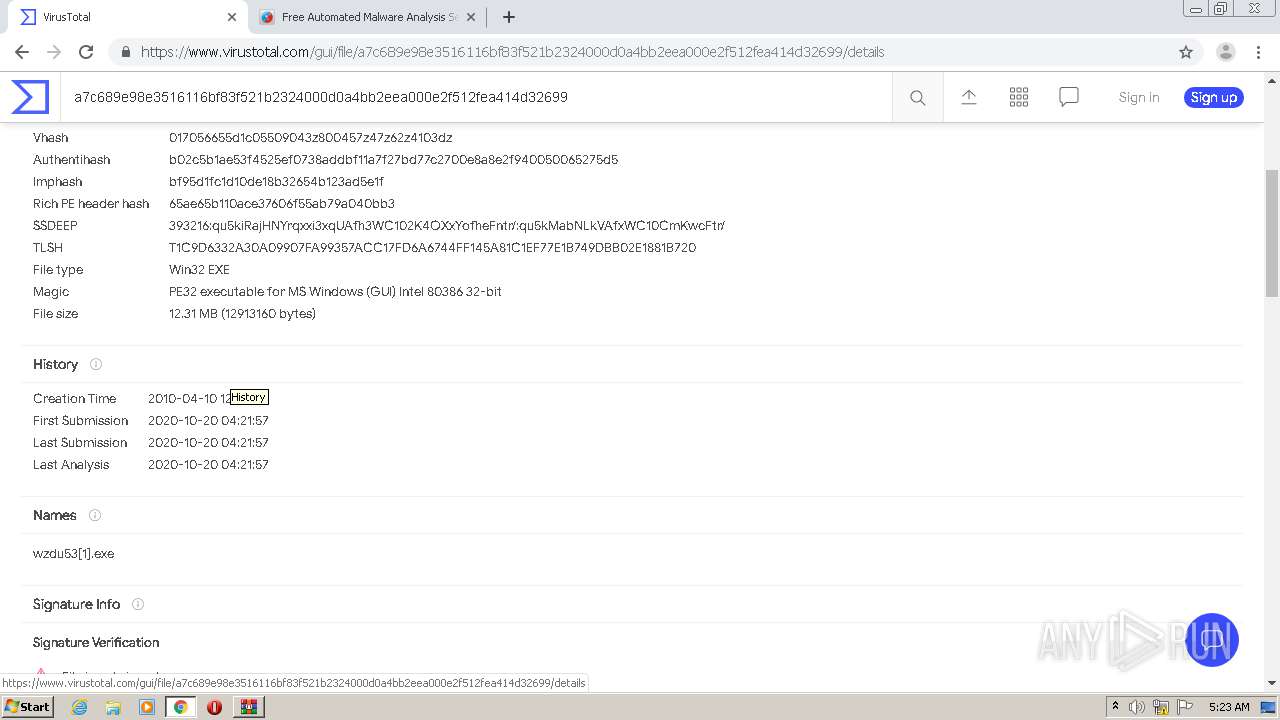
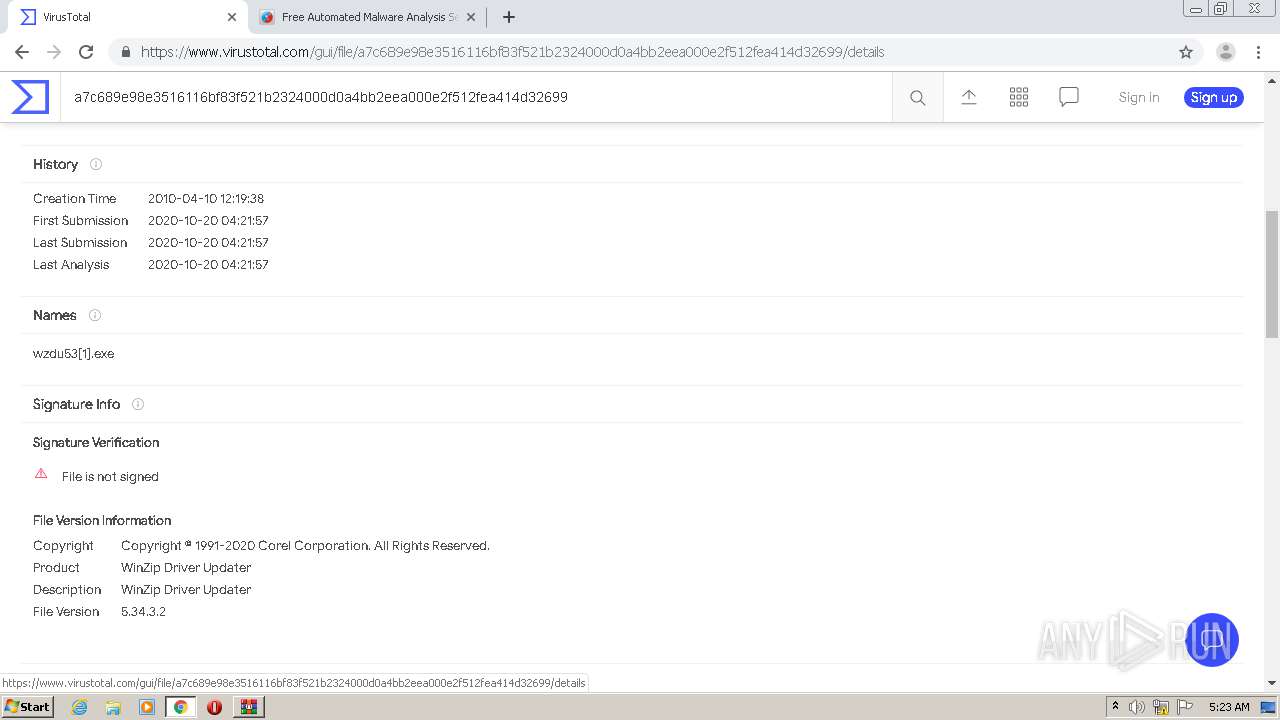
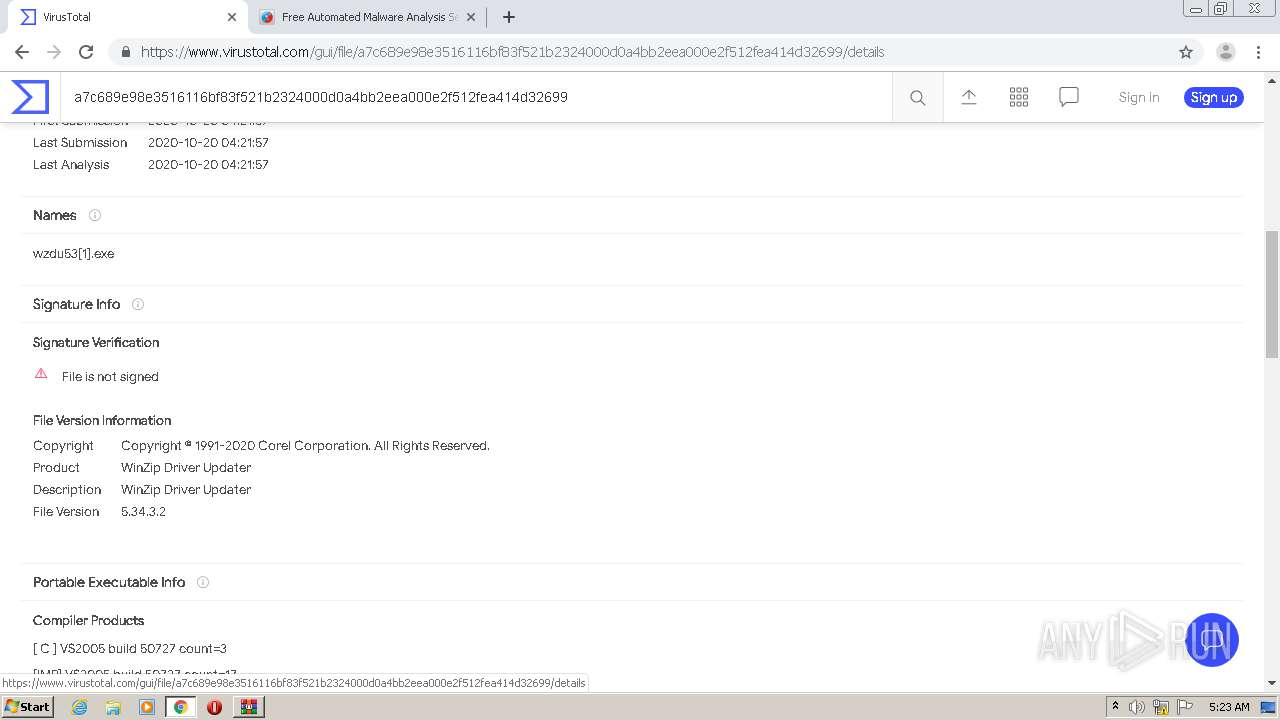
| File name: | wzdu53[1].exe.zip |
| Full analysis: | https://app.any.run/tasks/2db5fdef-e484-486f-ac42-de78ddce931c |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 04:18:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FE0DD96AEEA566F6680882D6677EDE04 |
| SHA1: | F3F7AAF36846F7089881BB8F7F525D75A7ABD38F |
| SHA256: | 5724C49DD981F11F6C2F1CB19EDAEBB7F8A1F34C002A3B63CAB941E0CC517C02 |
| SSDEEP: | 196608:KONxAtFJILecbMI0PDXN6sl4NyNGo8YbIArEM9wTQhYSobgKxhyPPcrVK:KONxAt8L/b/GXNfKNy8oZbIArunhp0PR |
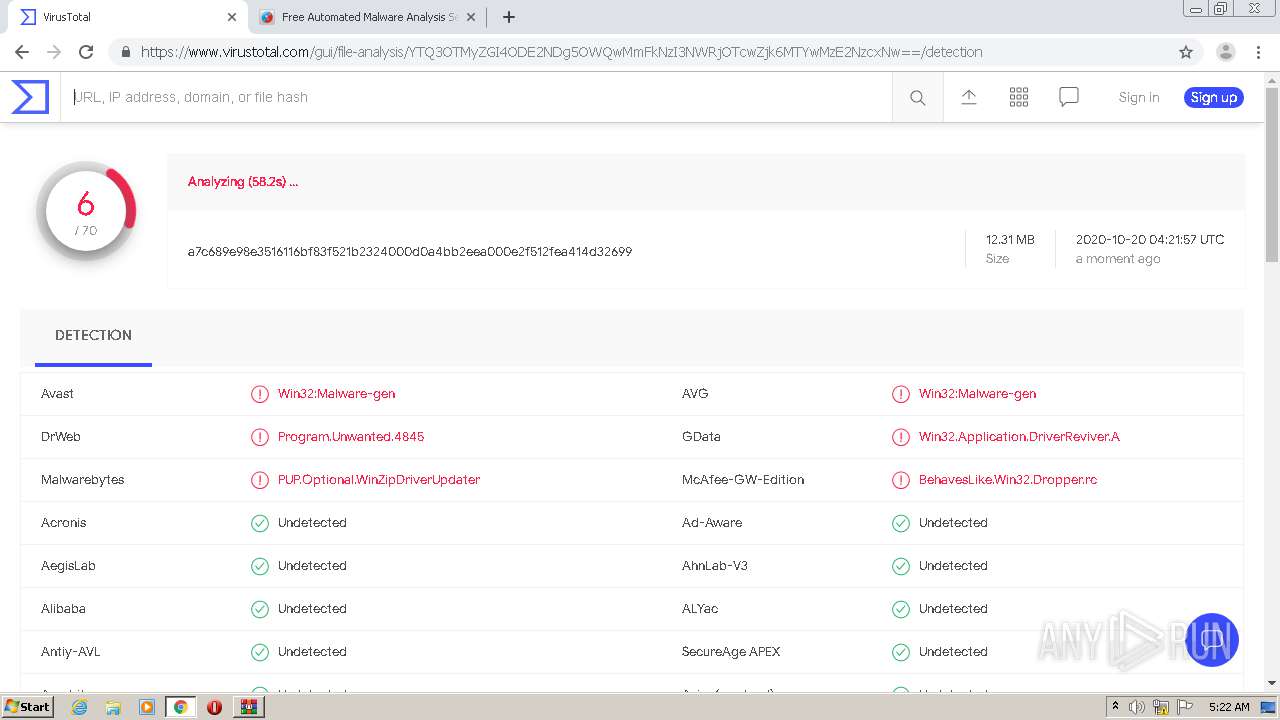
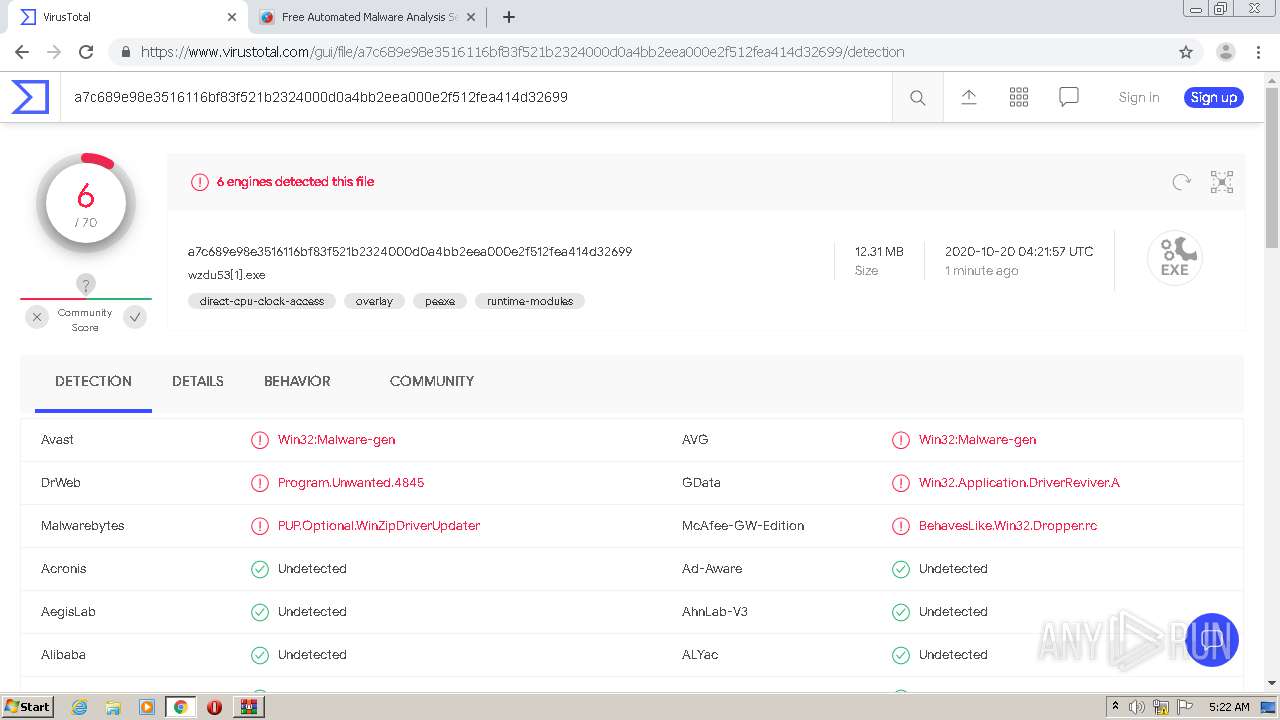
MALICIOUS
Application was dropped or rewritten from another process
- wzdu53[1].exe (PID: 2212)
- wzdu53[1].exe (PID: 2308)
- wzdu53[1].exe (PID: 2596)
- wzdu53[1].exe (PID: 3704)
- wzdu53[1].exe (PID: 2340)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3224)
INFO
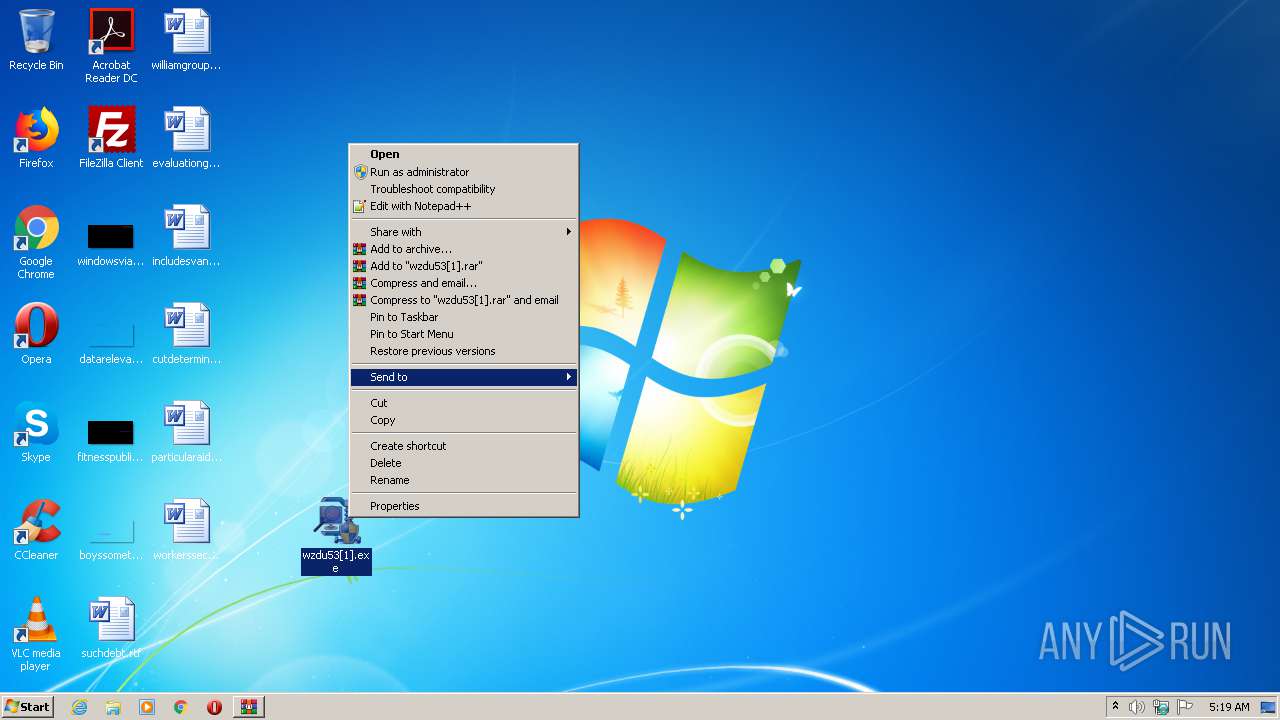
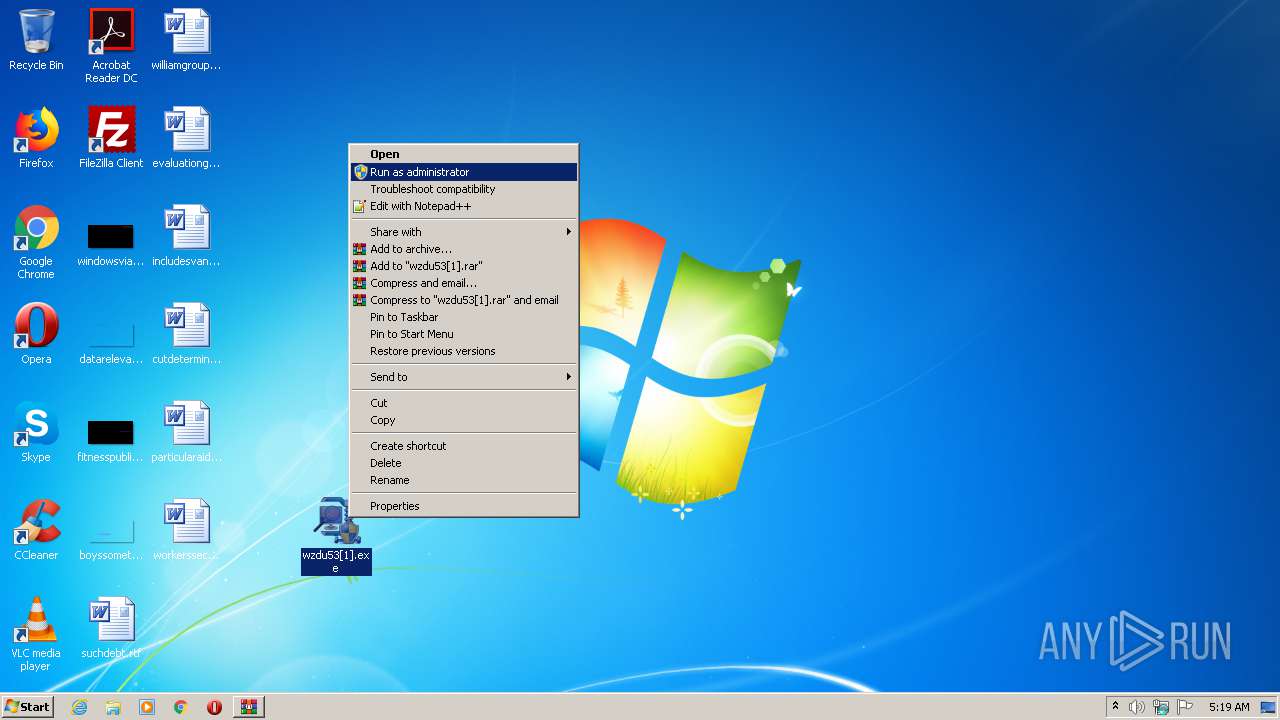
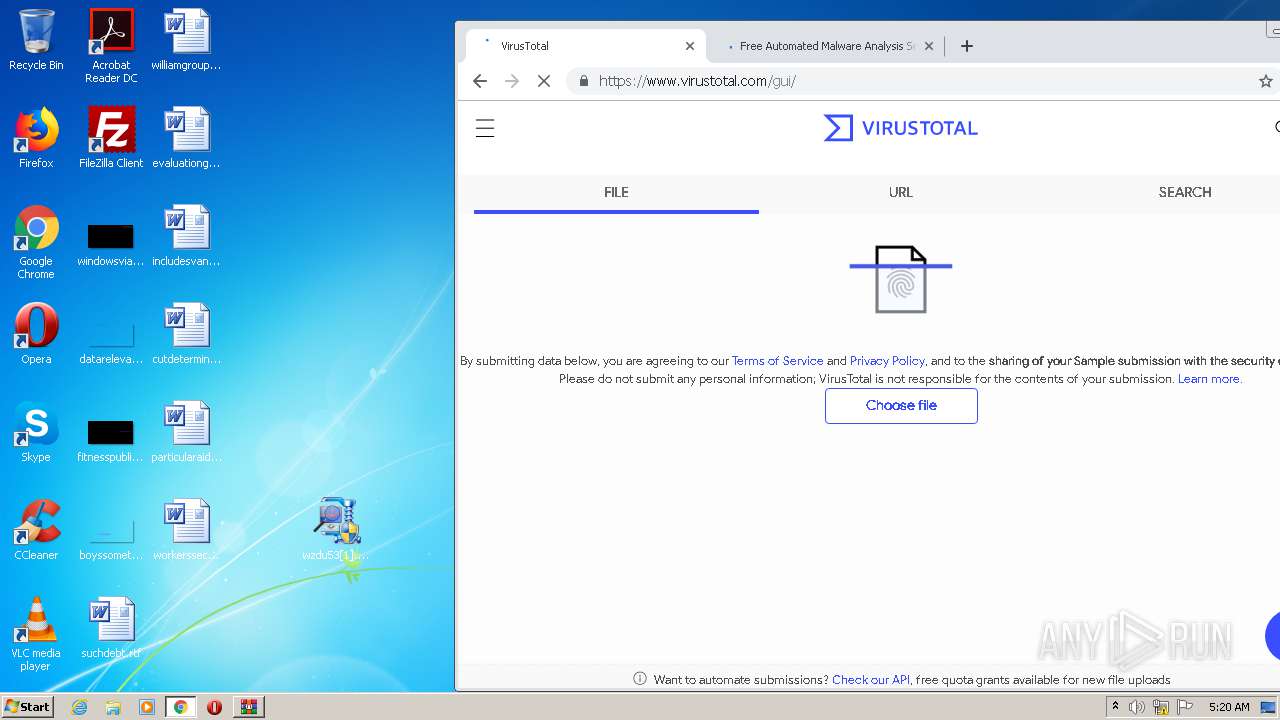
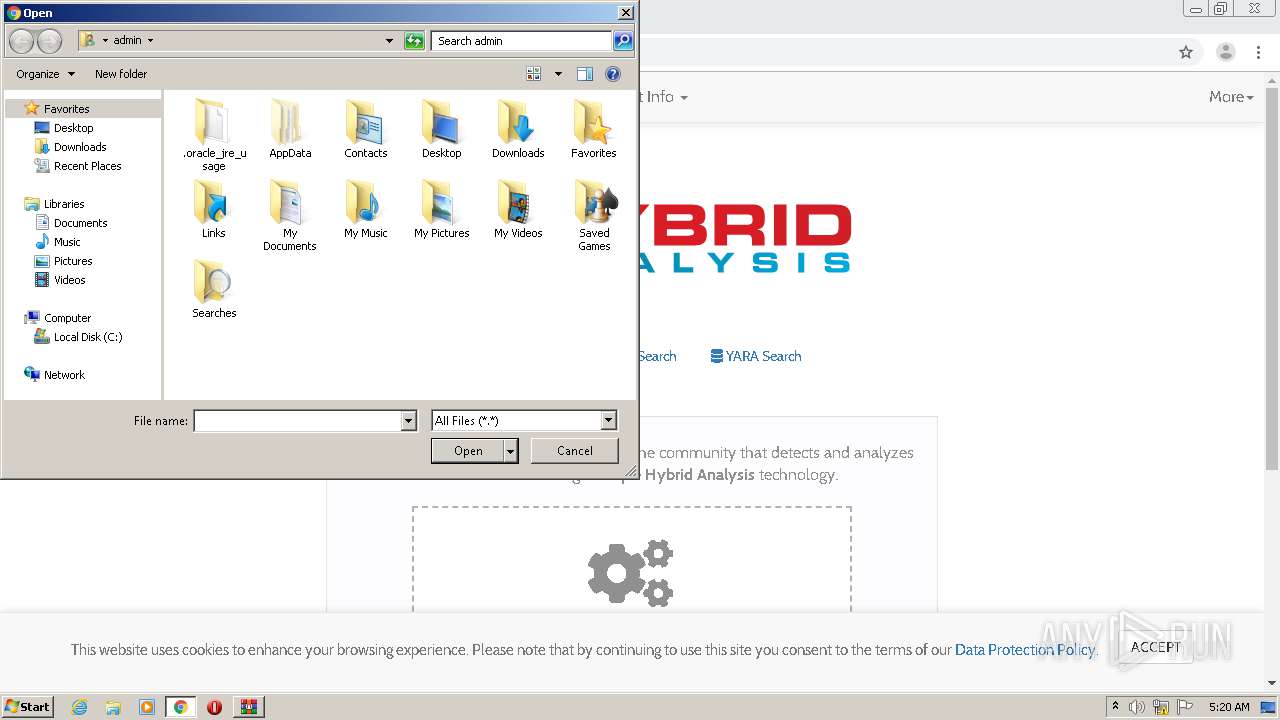
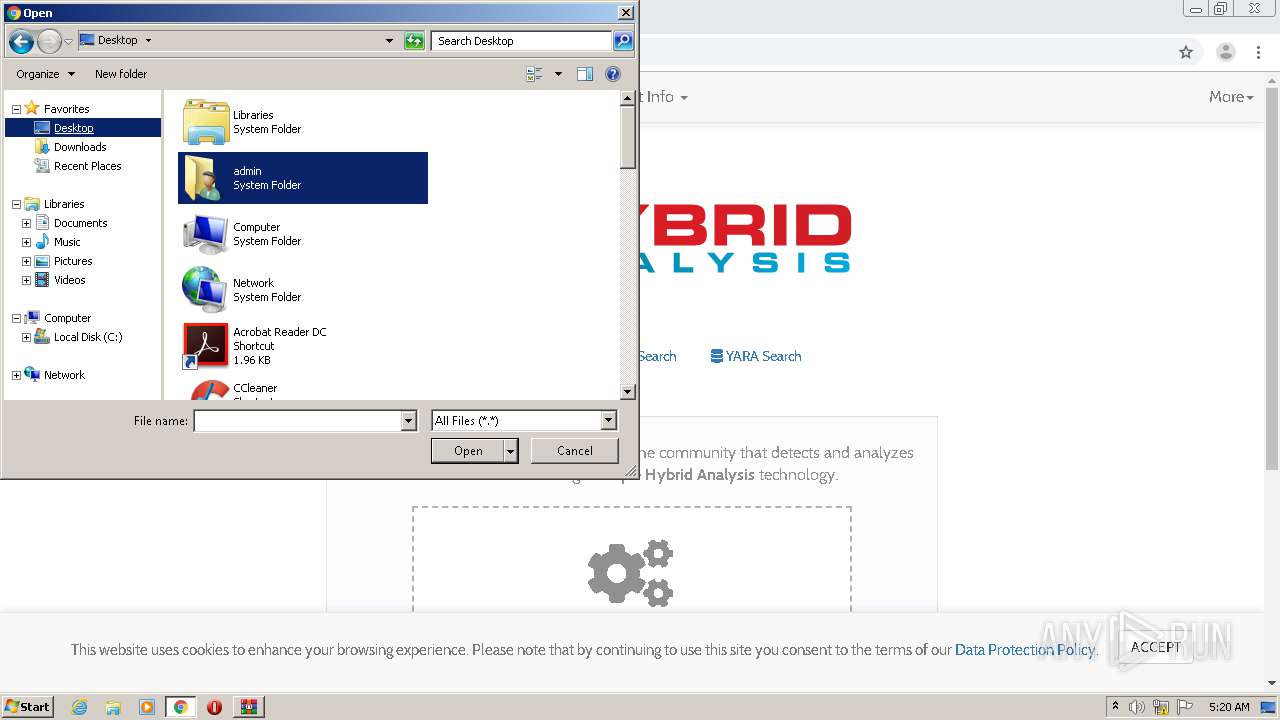
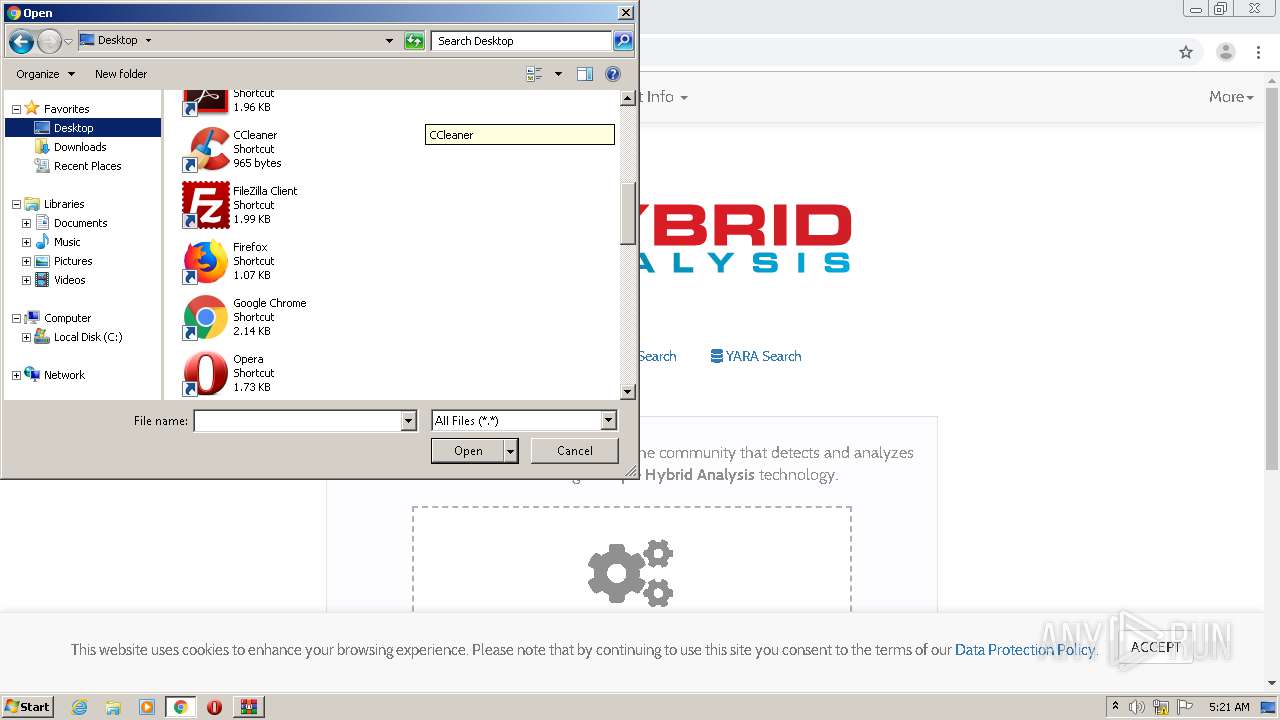
Manual execution by user
- wzdu53[1].exe (PID: 2596)
- wzdu53[1].exe (PID: 2340)
- wzdu53[1].exe (PID: 2308)
- chrome.exe (PID: 2864)
Reads the hosts file
- chrome.exe (PID: 2864)
- chrome.exe (PID: 4088)
Reads settings of System Certificates
- chrome.exe (PID: 4088)
Application launched itself
- chrome.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
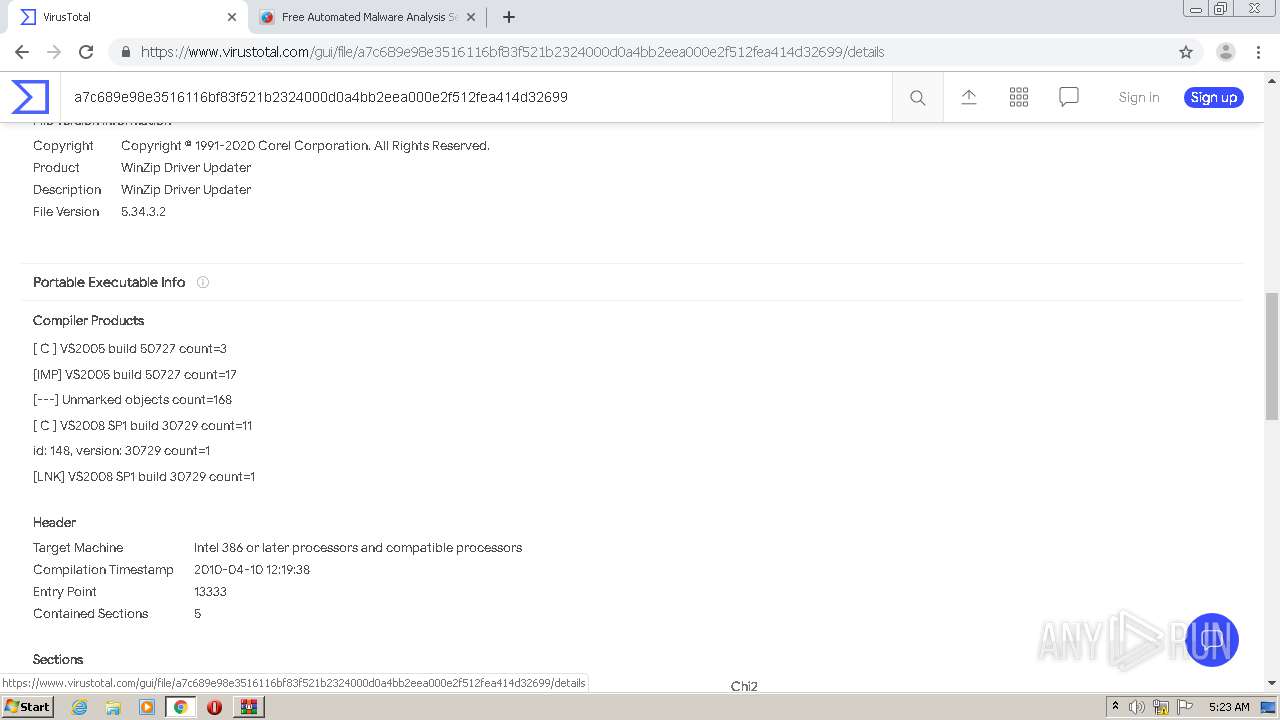
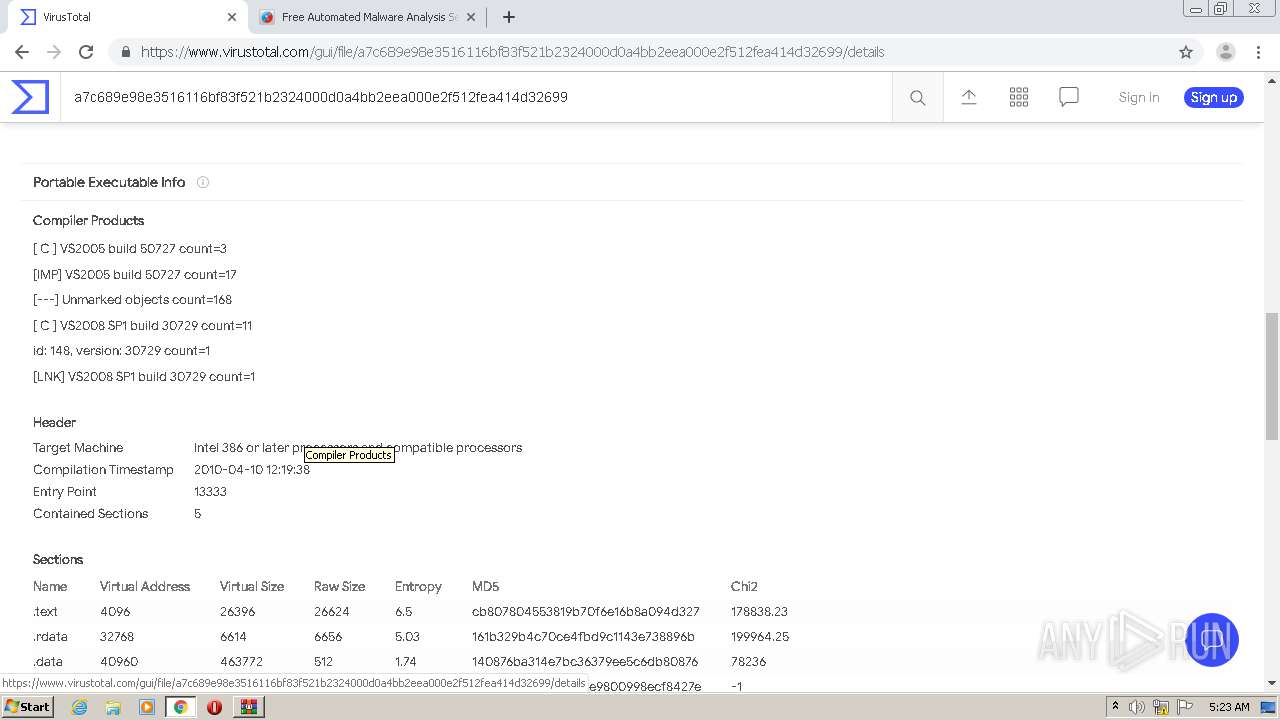
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
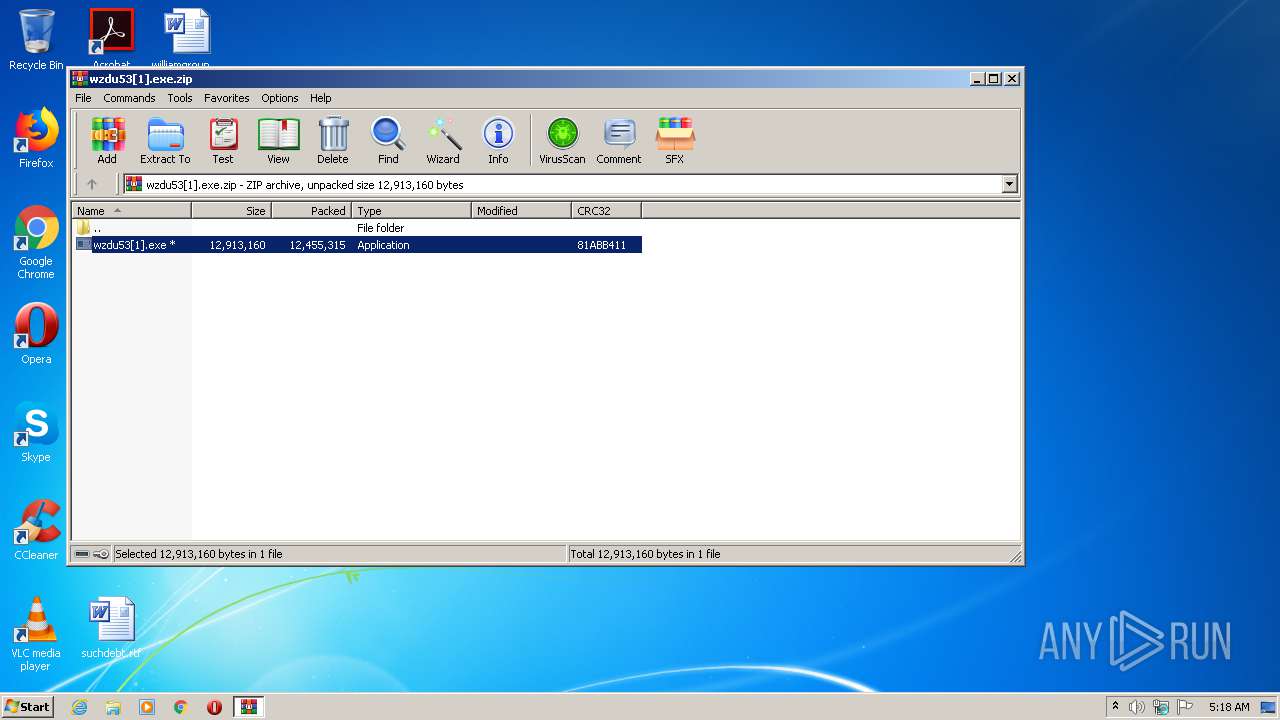
| ZipCRC: | 0x81abb411 |
| ZipCompressedSize: | 12455315 |
| ZipUncompressedSize: | 12913160 |
| ZipFileName: | wzdu53[1].exe |
Total processes
78
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17192854876456653847 --mojo-platform-channel-handle=2492 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14336907073827670035 --mojo-platform-channel-handle=1196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4289379285095801492 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f0da9d0,0x6f0da9e0,0x6f0da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
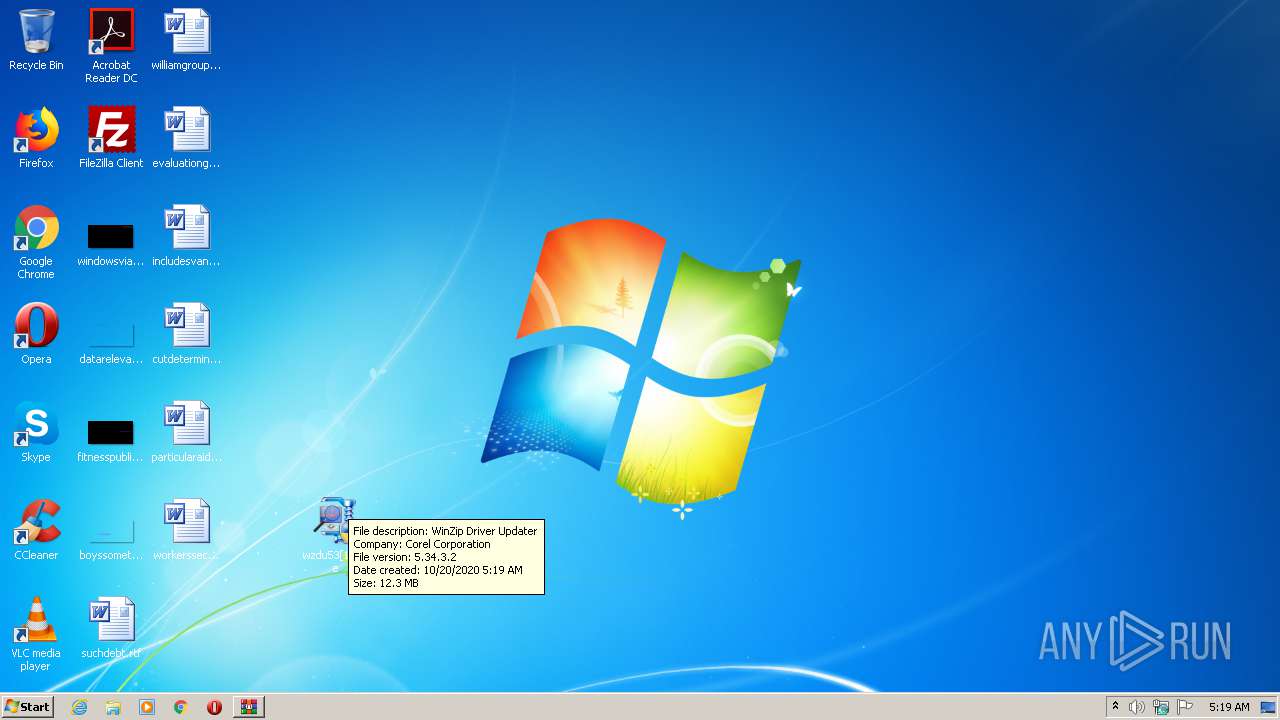
| 2212 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3224.34988\wzdu53[1].exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3224.34988\wzdu53[1].exe | WinRAR.exe | ||||||||||||
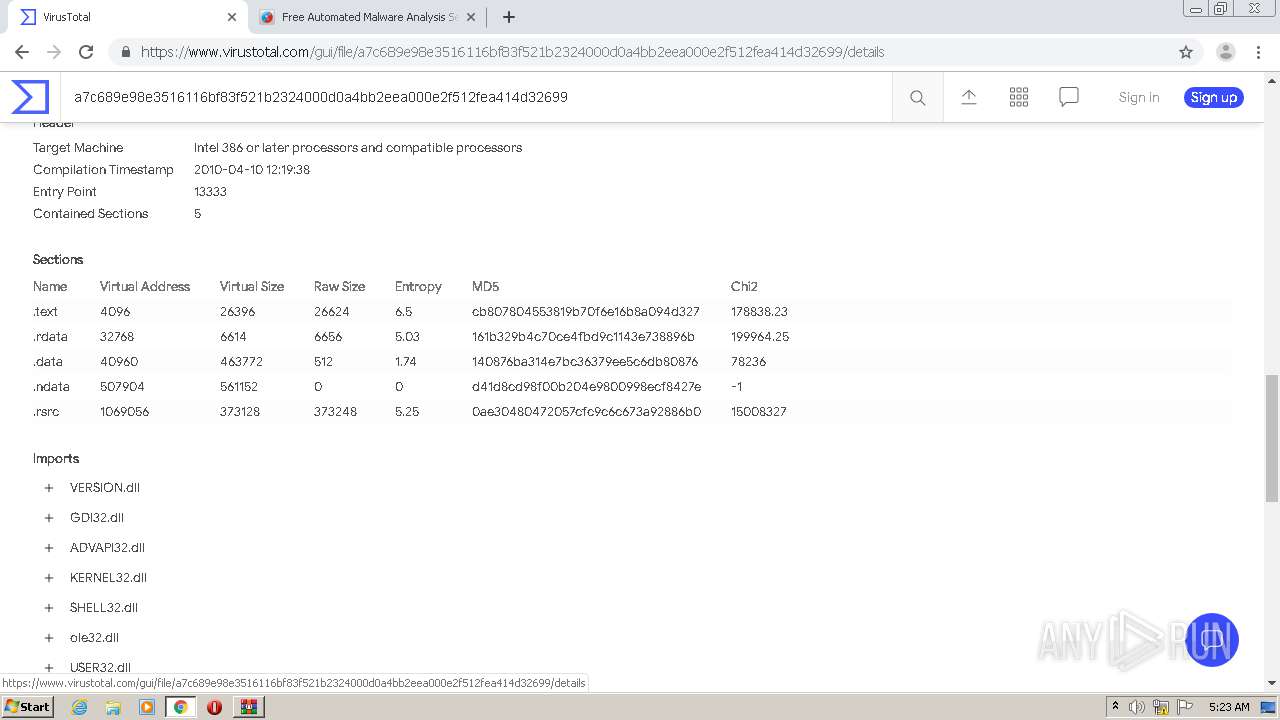
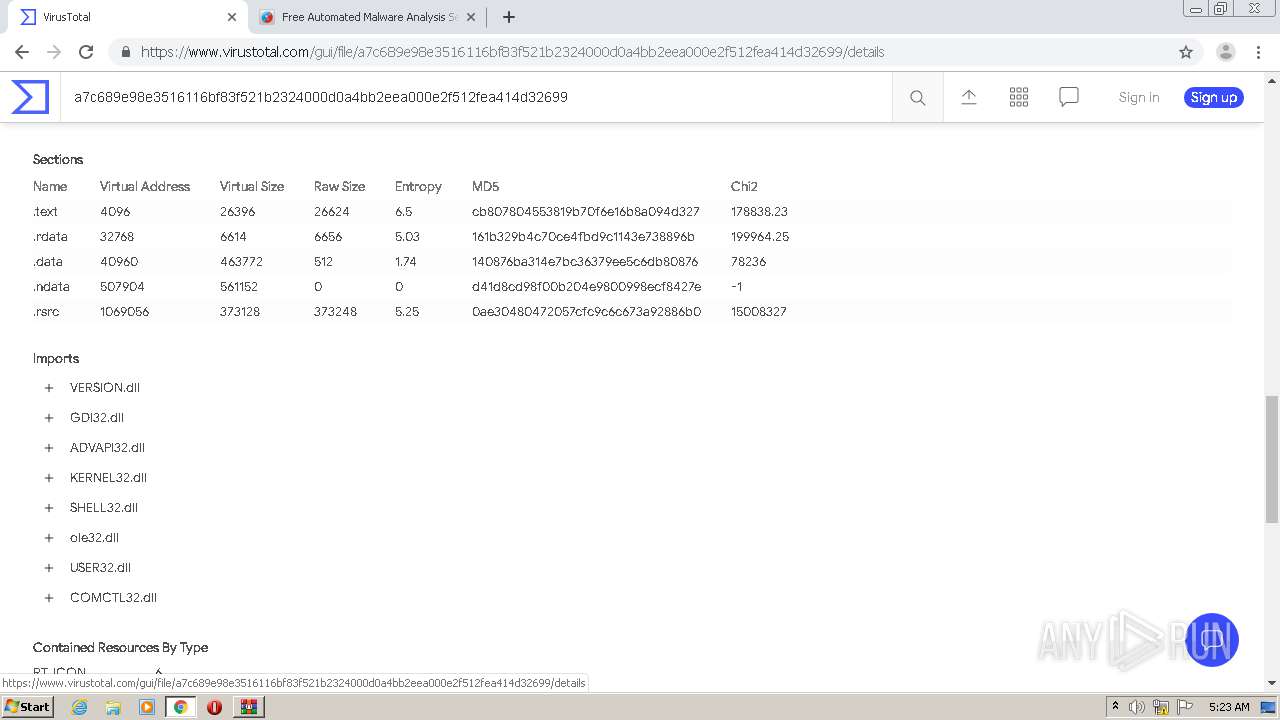
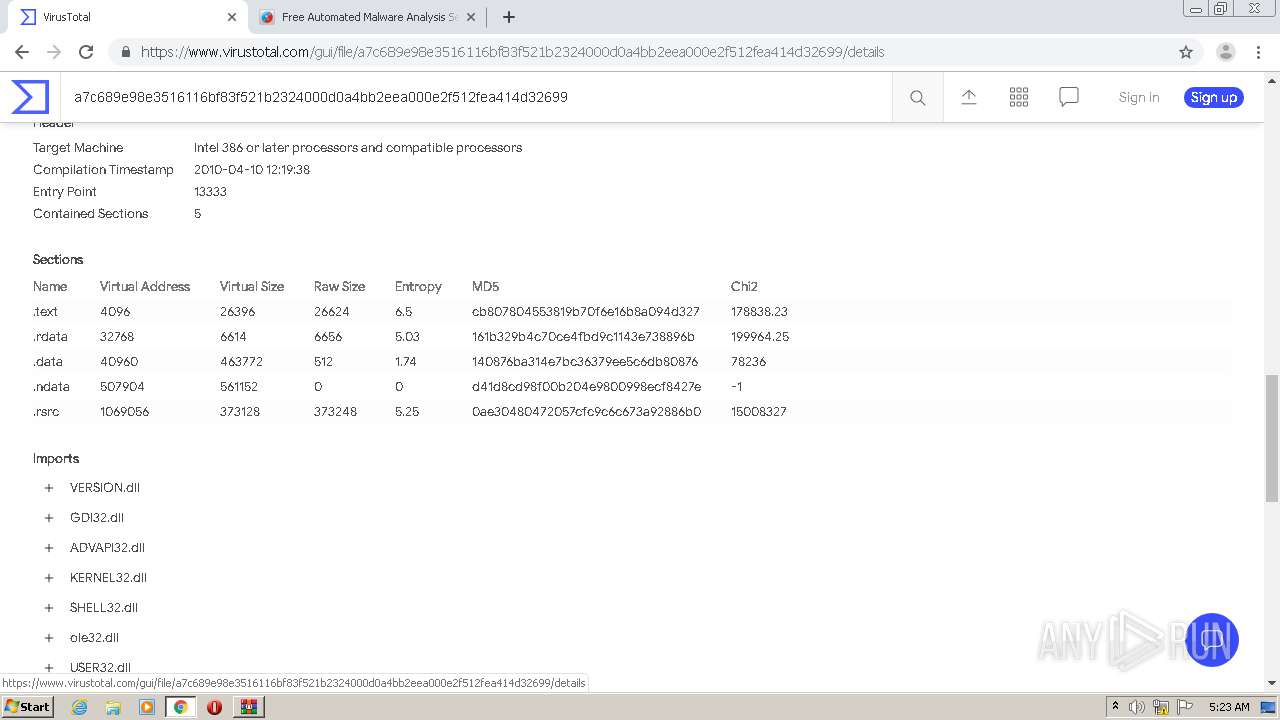
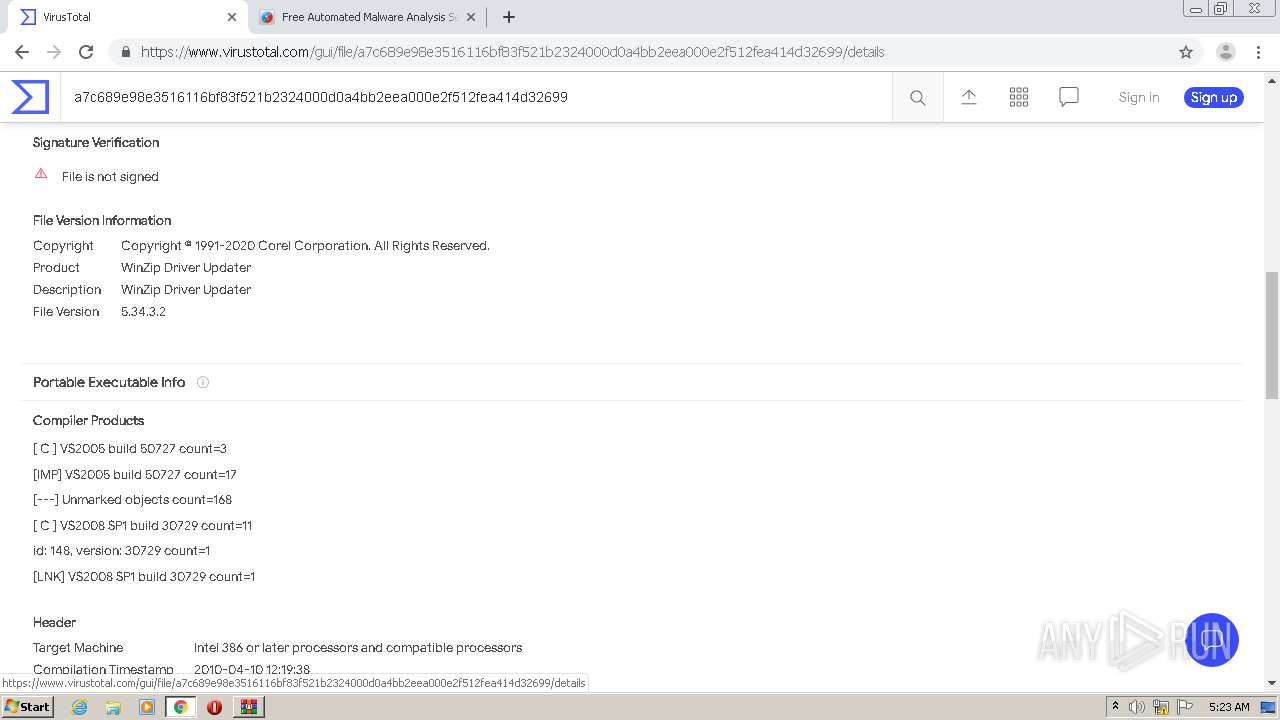
User: admin Company: Corel Corporation Integrity Level: HIGH Description: WinZip Driver Updater Exit code: 2 Version: 5.34.3.2 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\Desktop\wzdu53[1].exe" | C:\Users\admin\Desktop\wzdu53[1].exe | — | explorer.exe | |||||||||||
User: admin Company: Corel Corporation Integrity Level: MEDIUM Description: WinZip Driver Updater Exit code: 3221226540 Version: 5.34.3.2 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Desktop\wzdu53[1].exe" | C:\Users\admin\Desktop\wzdu53[1].exe | explorer.exe | ||||||||||||
User: admin Company: Corel Corporation Integrity Level: HIGH Description: WinZip Driver Updater Exit code: 2 Version: 5.34.3.2 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5741387575694148251 --mojo-platform-channel-handle=3308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8475274131166745546 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17796536266907450035,13614275397822180212,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3899860157611388336 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 115
Read events
1 953
Write events
157
Delete events
5
Modification events
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\wzdu53[1].exe.zip | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
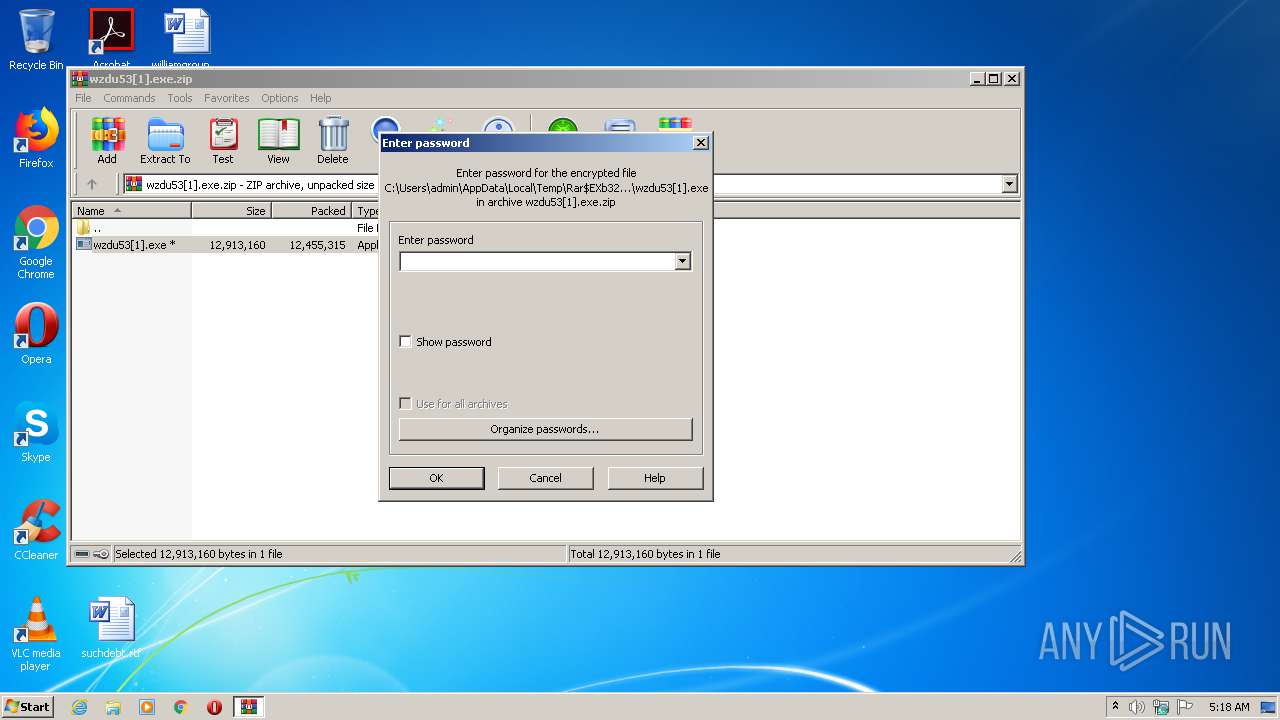
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
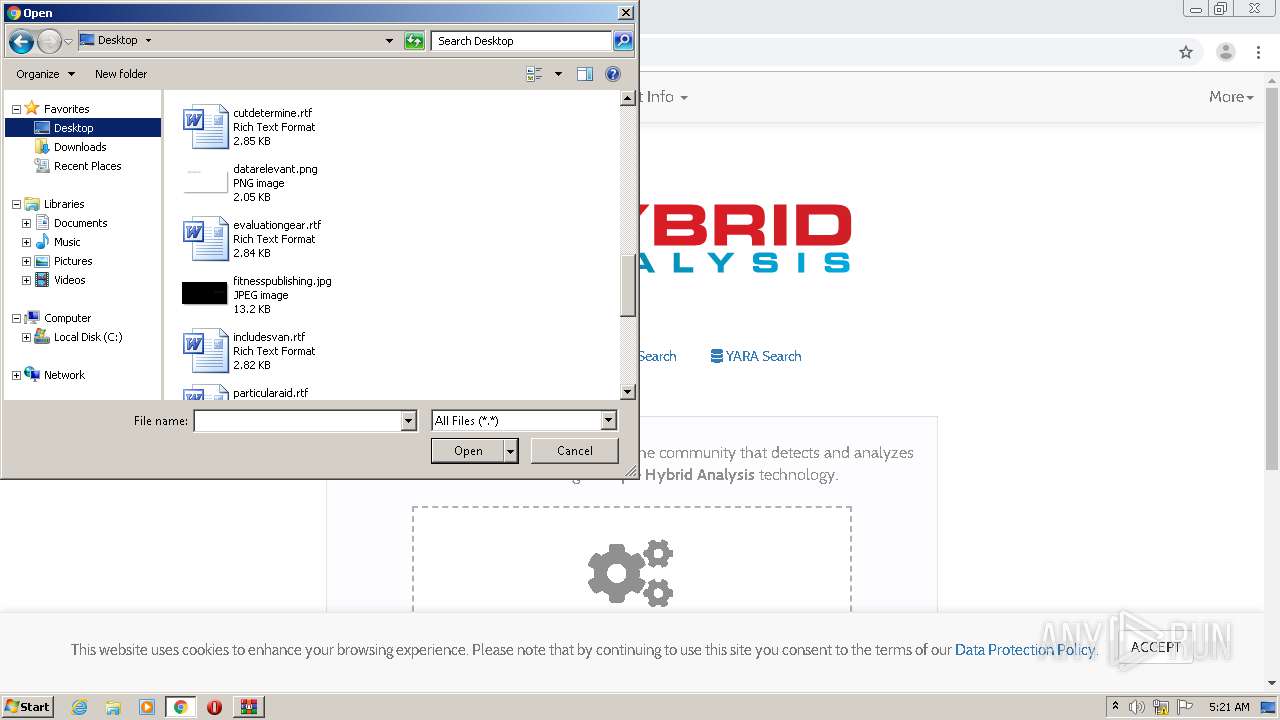
Executable files
1
Suspicious files
75
Text files
121
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3224.37191\wzdu53[1].exe | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E655F-B30.pma | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7d94f593-ca49-4fe6-9420-7219afd693fb.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3224 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3224.34988\wzdu53[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF178211.TMP | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF17823f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
28
DNS requests
20
Threats
0
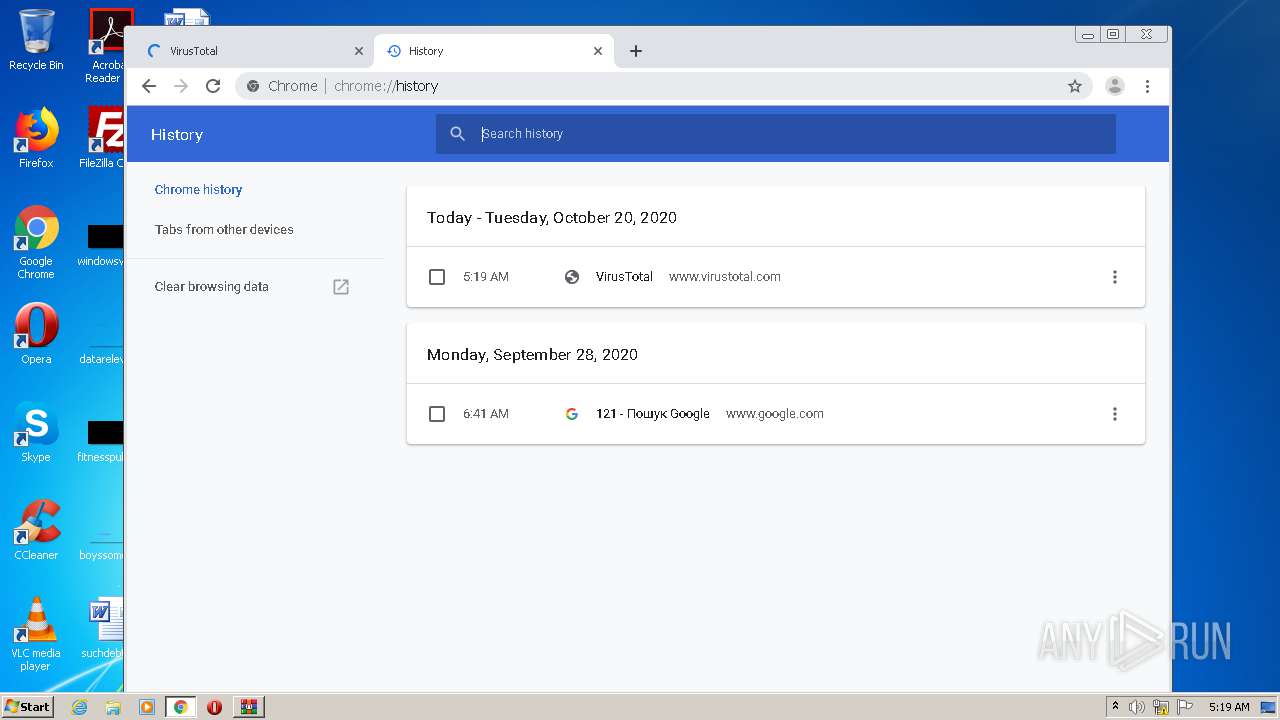
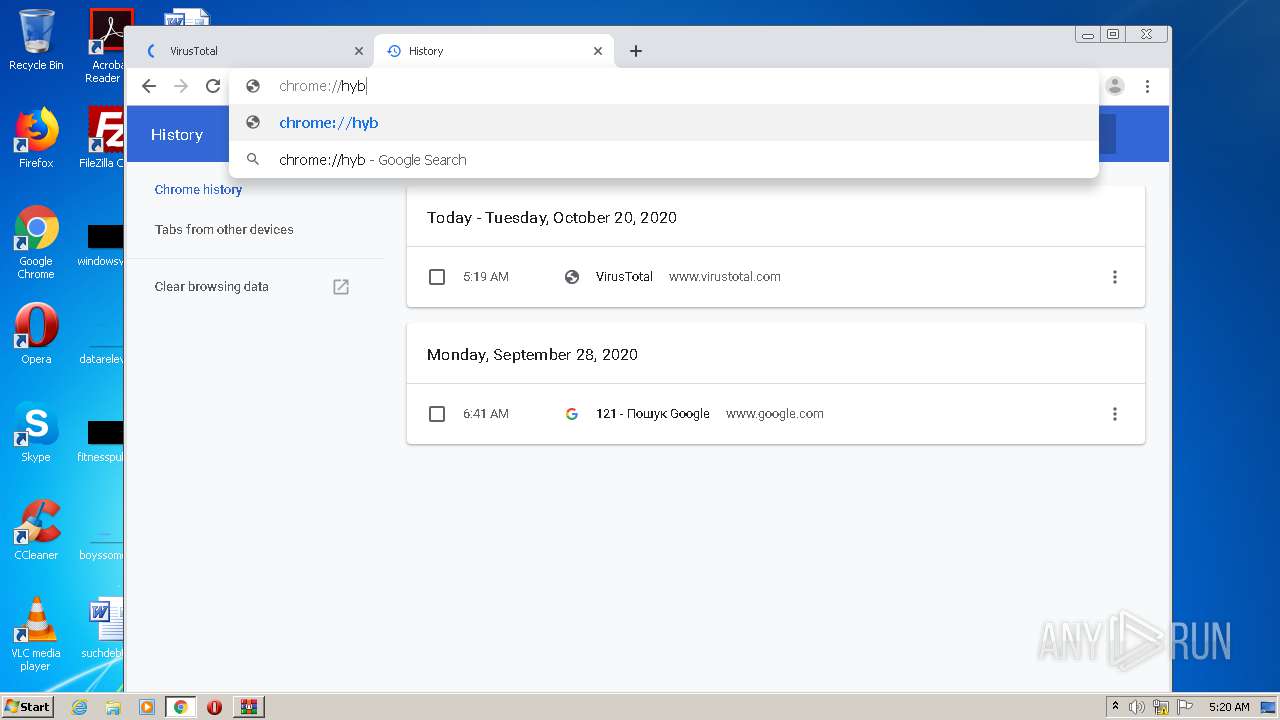
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
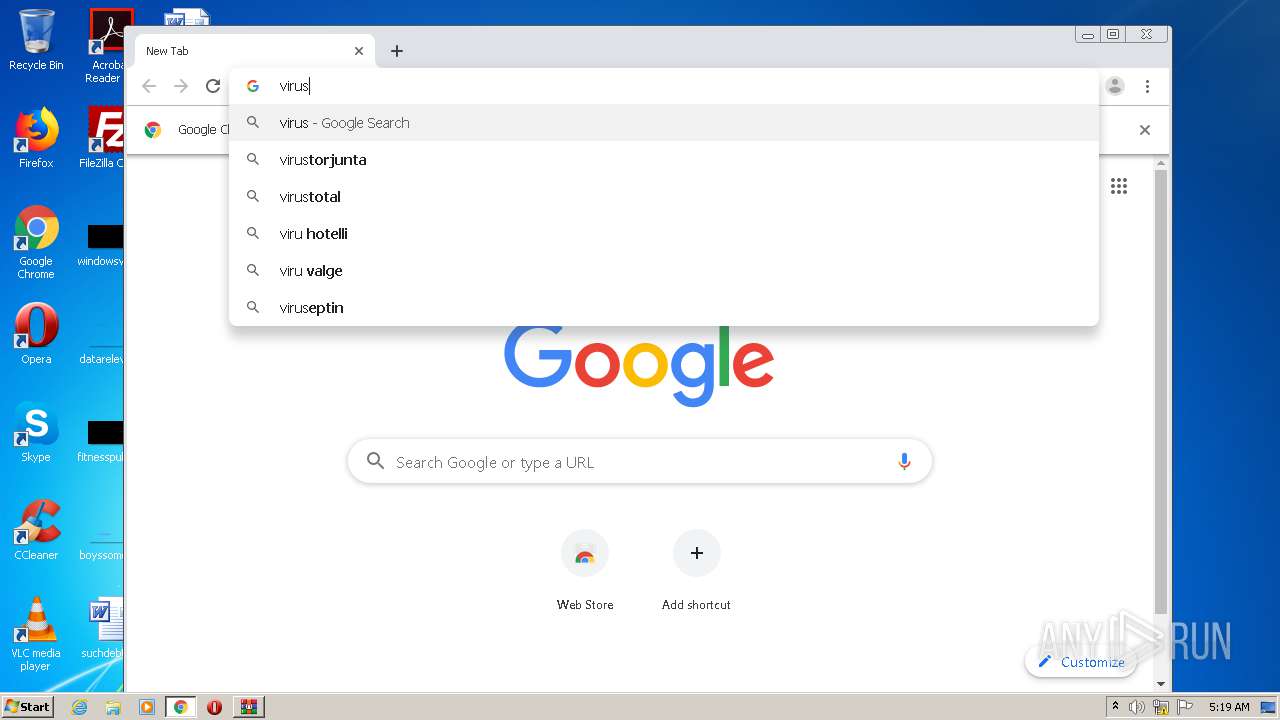
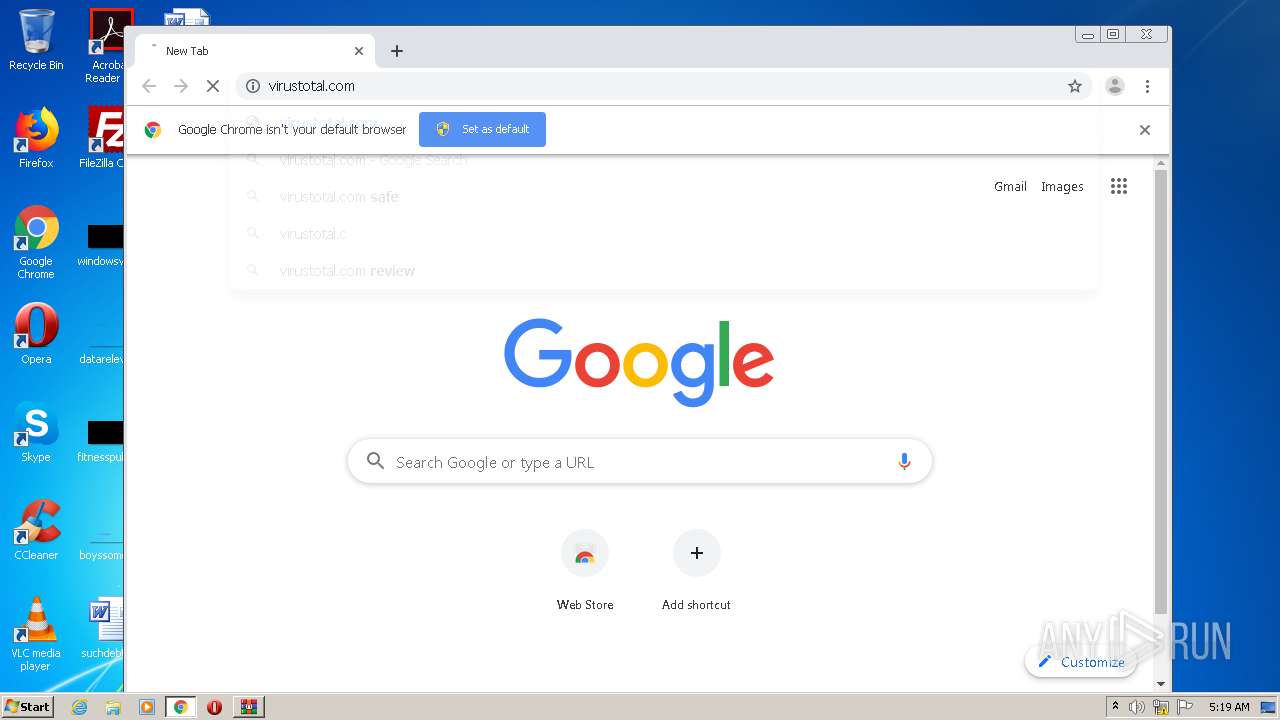
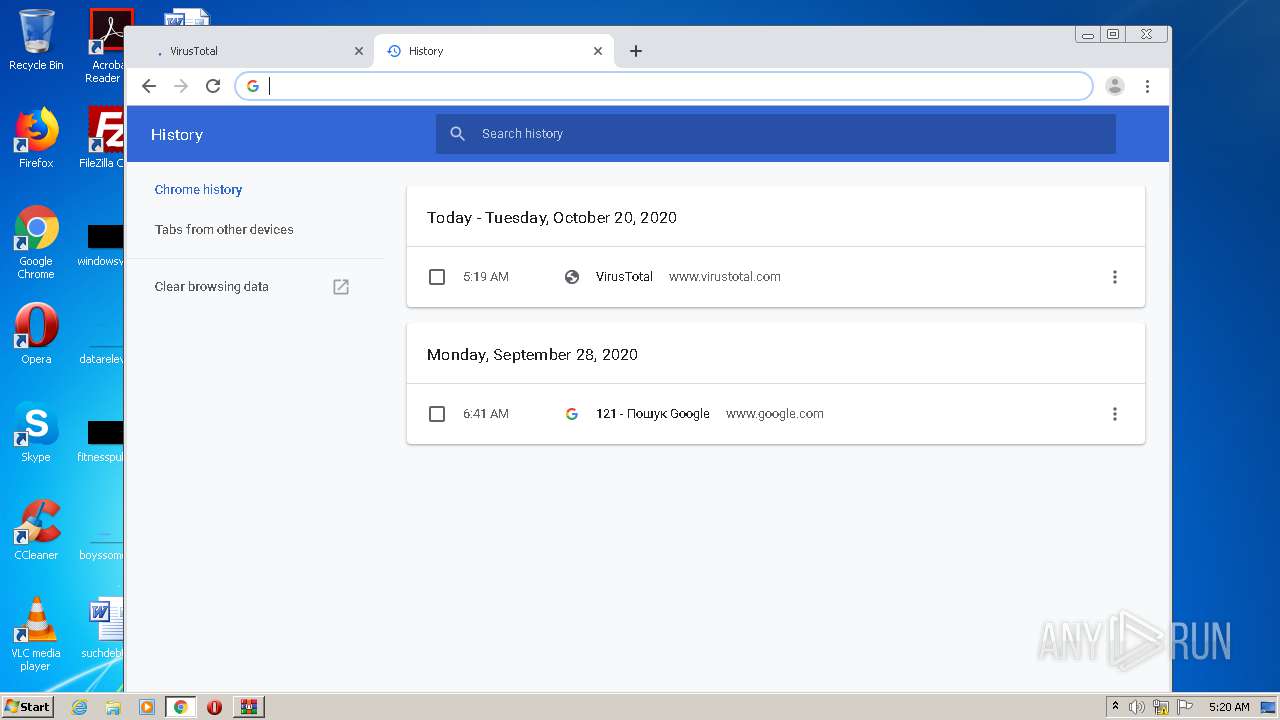
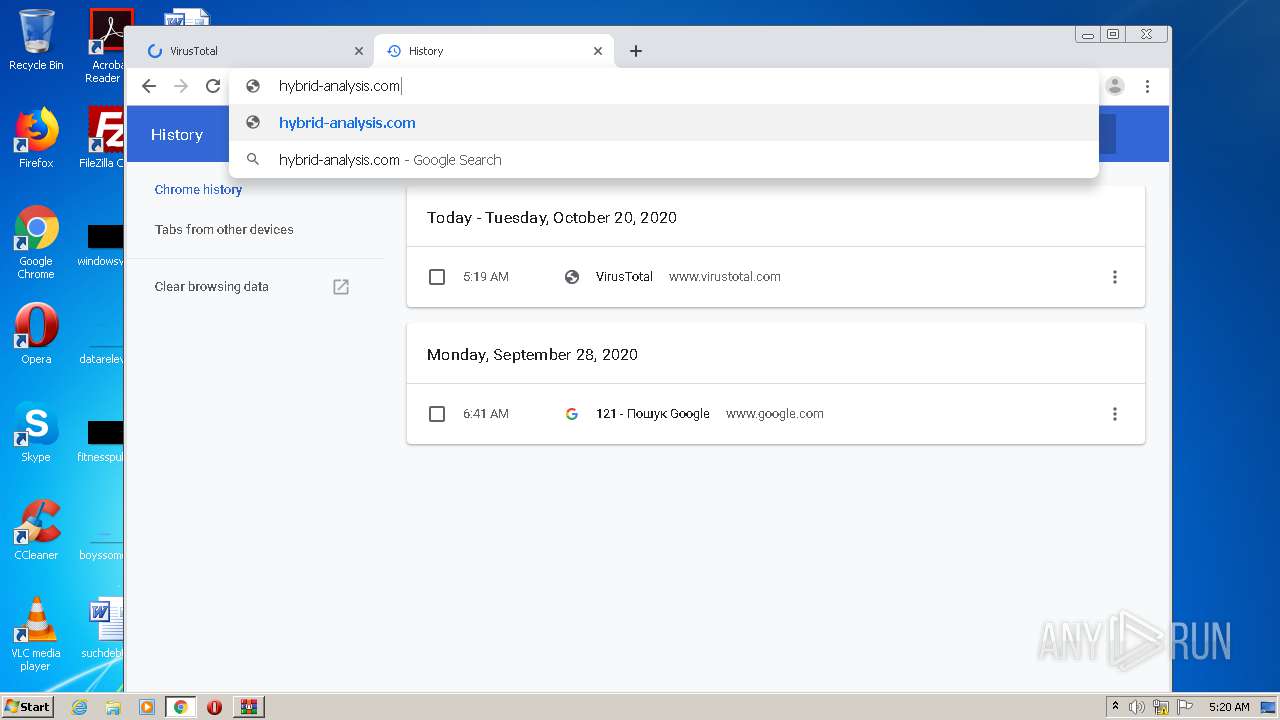
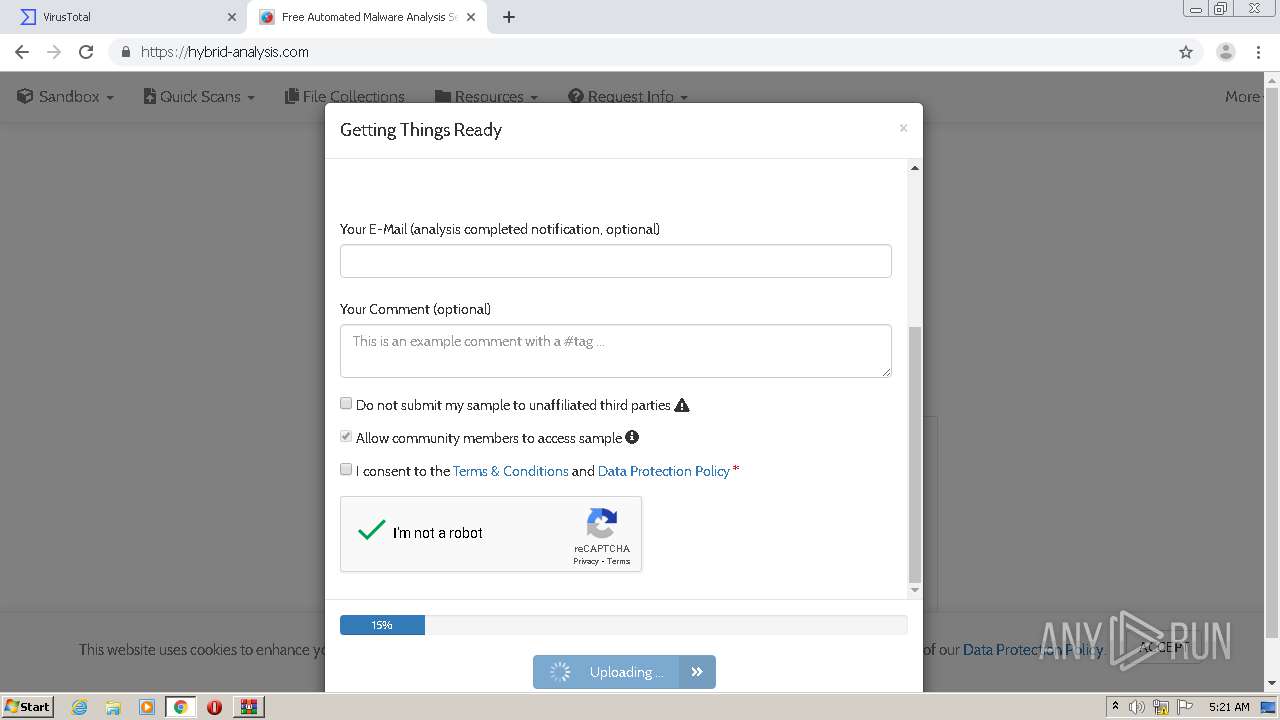
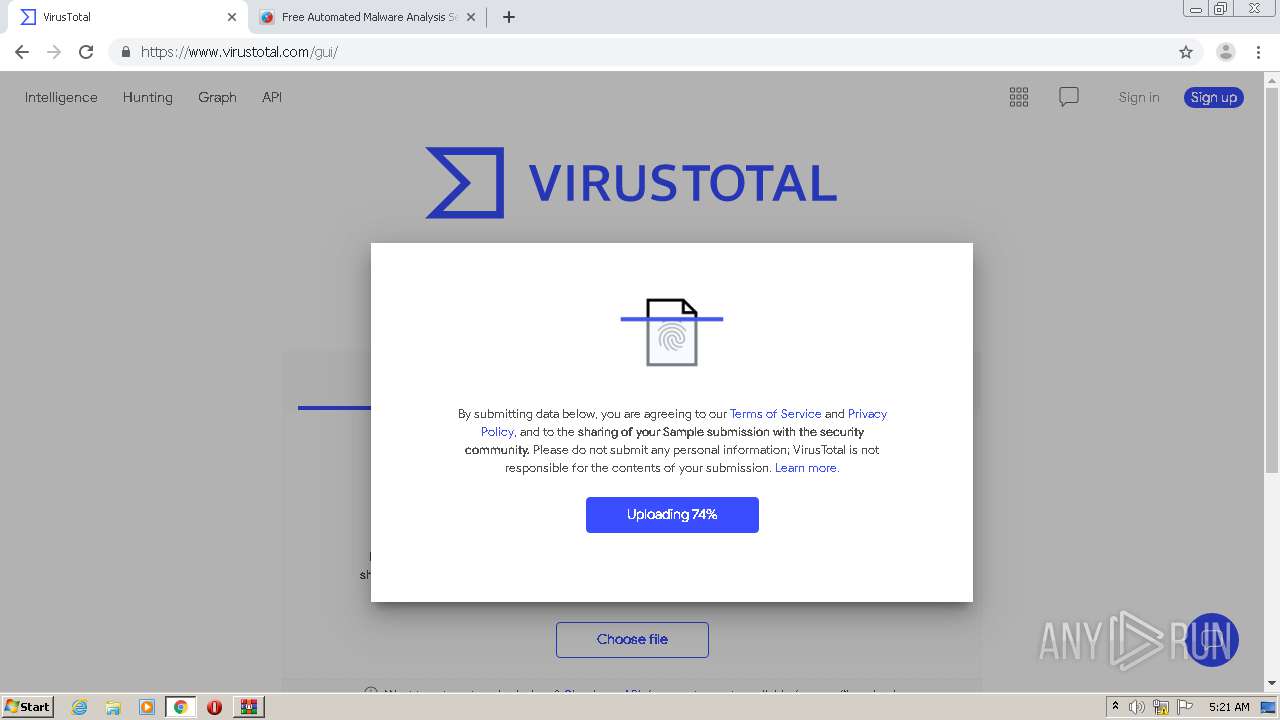
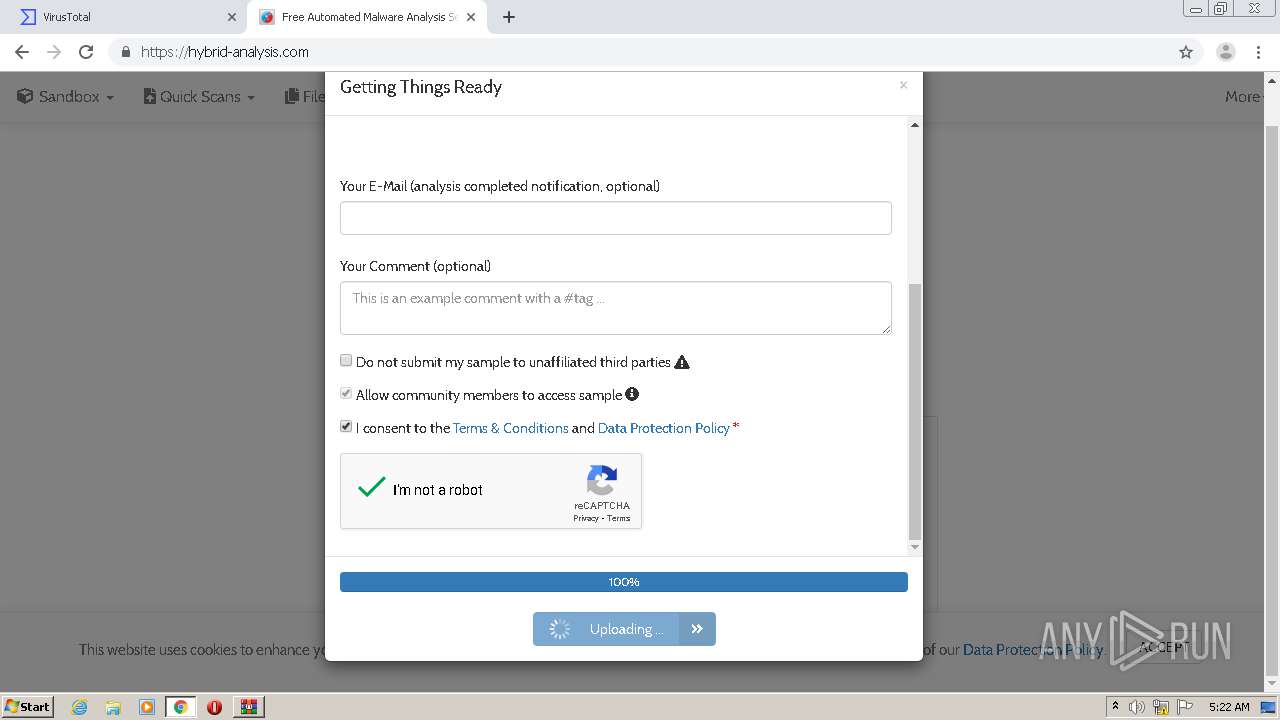
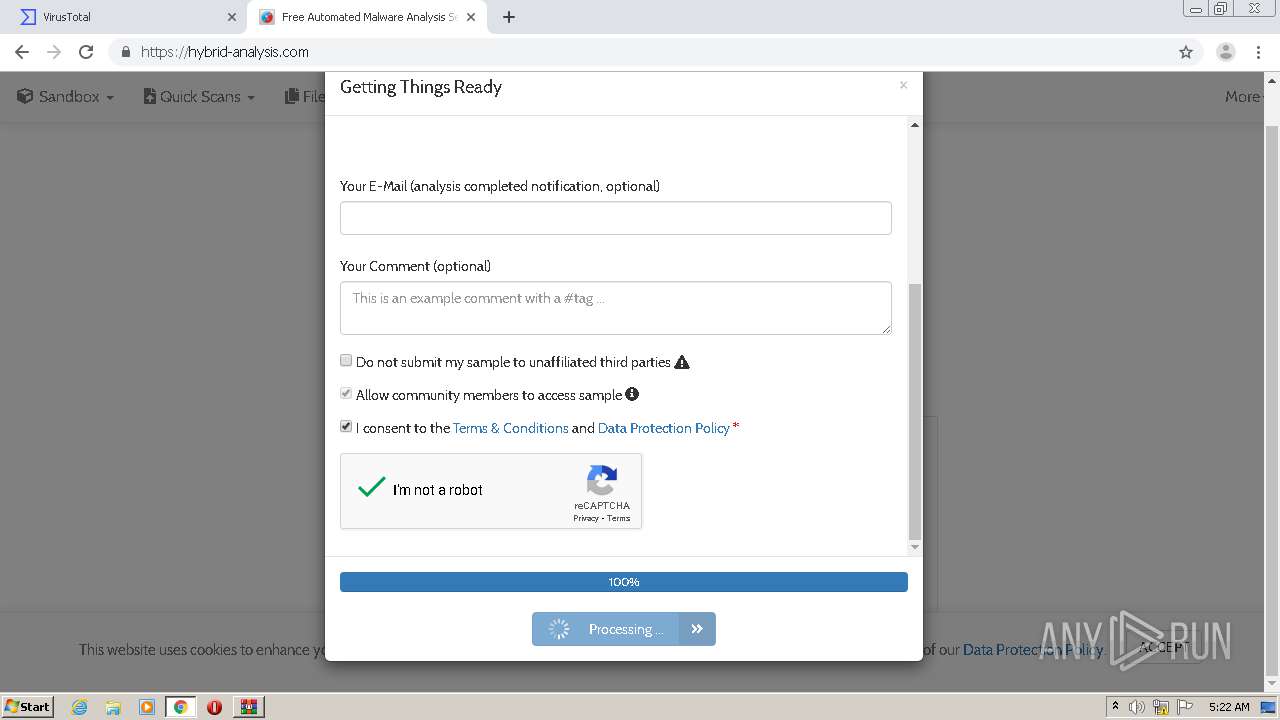
4088 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
4088 | chrome.exe | GET | 301 | 104.22.13.77:80 | http://hybrid-analysis.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 216.239.32.21:80 | virustotal.com | Google Inc. | US | whitelisted |
— | — | 216.239.32.21:80 | virustotal.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 216.239.32.21:443 | virustotal.com | Google Inc. | US | whitelisted |
4088 | chrome.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
virustotal.com |
| whitelisted |