| URL: | http://getfileslic.site/download?id=qUwFk4WxAx8&s=C0B24C23 |
| Full analysis: | https://app.any.run/tasks/db71831c-a14e-4513-bd47-fc602f9554f6 |
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2020, 19:56:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5271697BE9DF538188757975F3E6064A |
| SHA1: | B1CD13B8BE39F974E50ADC01C6F5CF896E6BF2D7 |
| SHA256: | 571E1D0B0D0FBF4B20D762DC7040698902F7E47CDE36BF4781E910B099F54FEC |
| SSDEEP: | 3:N1KZARcAjcLRZKSS2nxvY+RgW:C+7M2STRYugW |
MALICIOUS
Uses Task Scheduler to run other applications
- sihost.exe (PID: 2756)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2976)
- schtasks.exe (PID: 672)
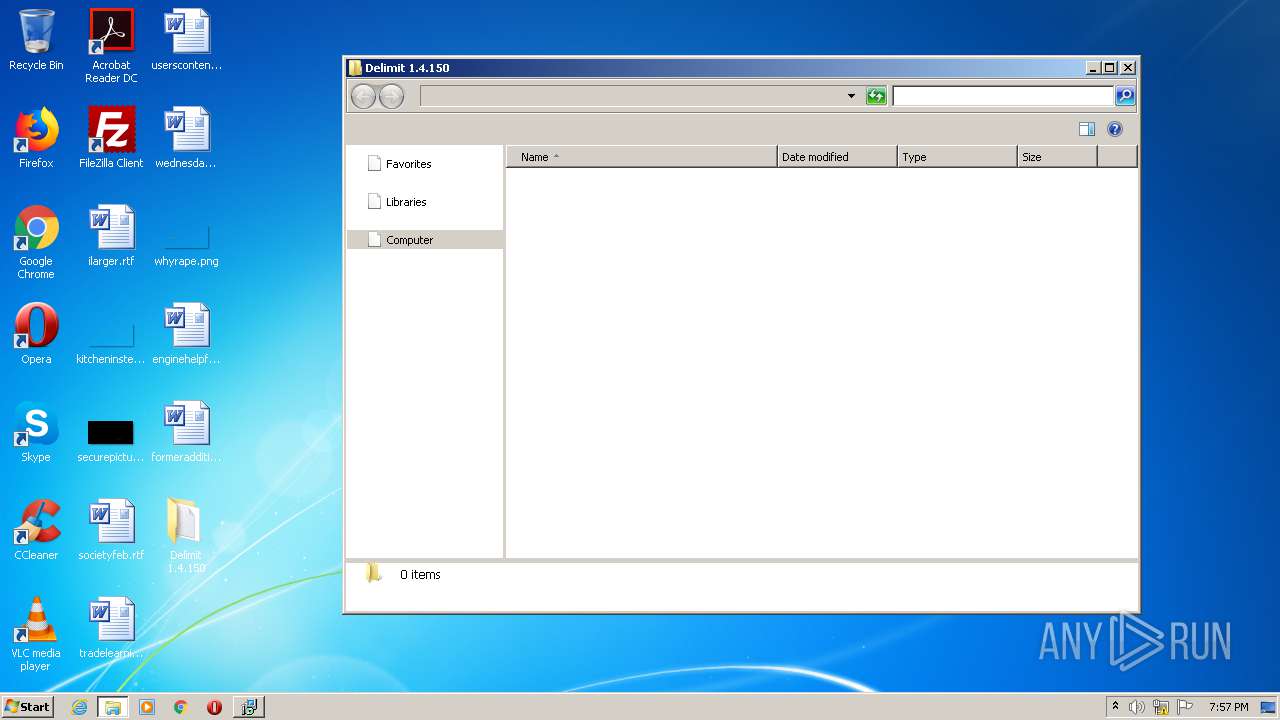
Application was dropped or rewritten from another process
- sihost.exe (PID: 2756)
- Delimit 1.4.150.exe (PID: 1408)
- Delimit 1.4.150.exe (PID: 1768)
SUSPICIOUS
Reads the Windows organization settings
- Delimit 1.4.150.tmp (PID: 1000)
Executable content was dropped or overwritten
- Delimit 1.4.150.exe (PID: 1408)
- Delimit 1.4.150.tmp (PID: 1000)
- 7za.exe (PID: 2132)
- Delimit 1.4.150.exe (PID: 1768)
Reads Windows owner or organization settings
- Delimit 1.4.150.tmp (PID: 1000)
Creates files in the user directory
- Delimit 1.4.150.tmp (PID: 1000)
- sihost.exe (PID: 2756)
Executed via COM
- explorer.exe (PID: 1912)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 2608)
Changes internet zones settings
- iexplore.exe (PID: 2608)
Application launched itself
- iexplore.exe (PID: 2608)
Creates files in the user directory
- iexplore.exe (PID: 2480)
Application was dropped or rewritten from another process
- Delimit 1.4.150.tmp (PID: 1000)
- 7za.exe (PID: 2132)
- 7za.exe (PID: 2936)
- 7za.exe (PID: 960)
- Delimit 1.4.150.tmp (PID: 2596)
Reads settings of System Certificates
- iexplore.exe (PID: 2608)
Changes settings of System certificates
- iexplore.exe (PID: 2608)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2608)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2608)
Manual execution by user
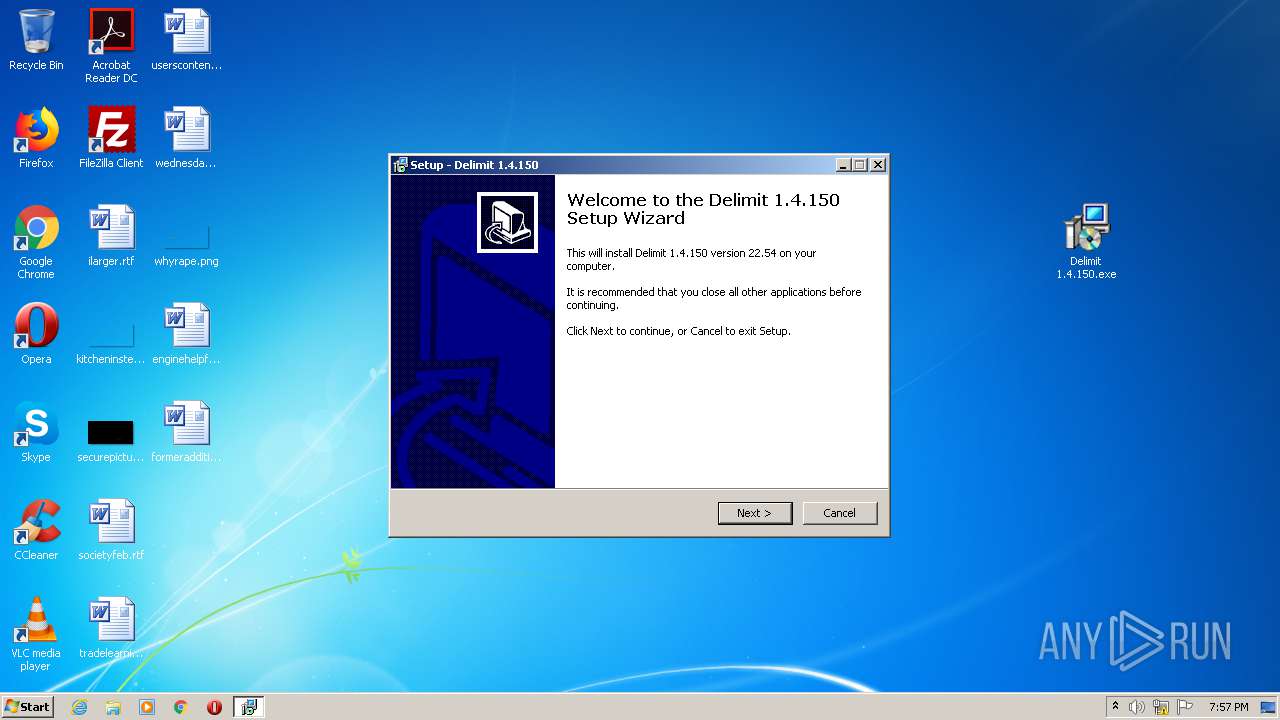
- Delimit 1.4.150.exe (PID: 1768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
16
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Windows\system32\schtasks.exe" /Create /f /XML "C:\Users\admin\AppData\Roaming\ToolSysHost\data.xml" /tn "Microsoft\Windows\Windows Error Reporting\SysInfo" | C:\Windows\system32\schtasks.exe | — | sihost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
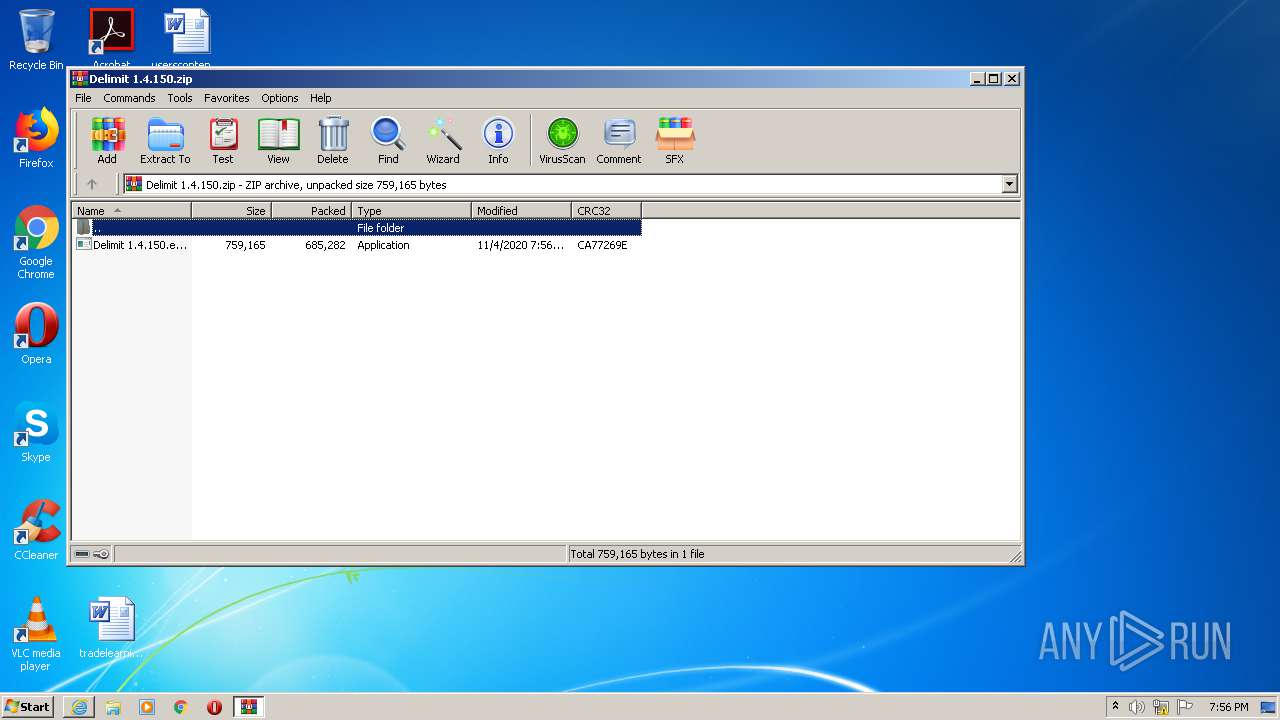
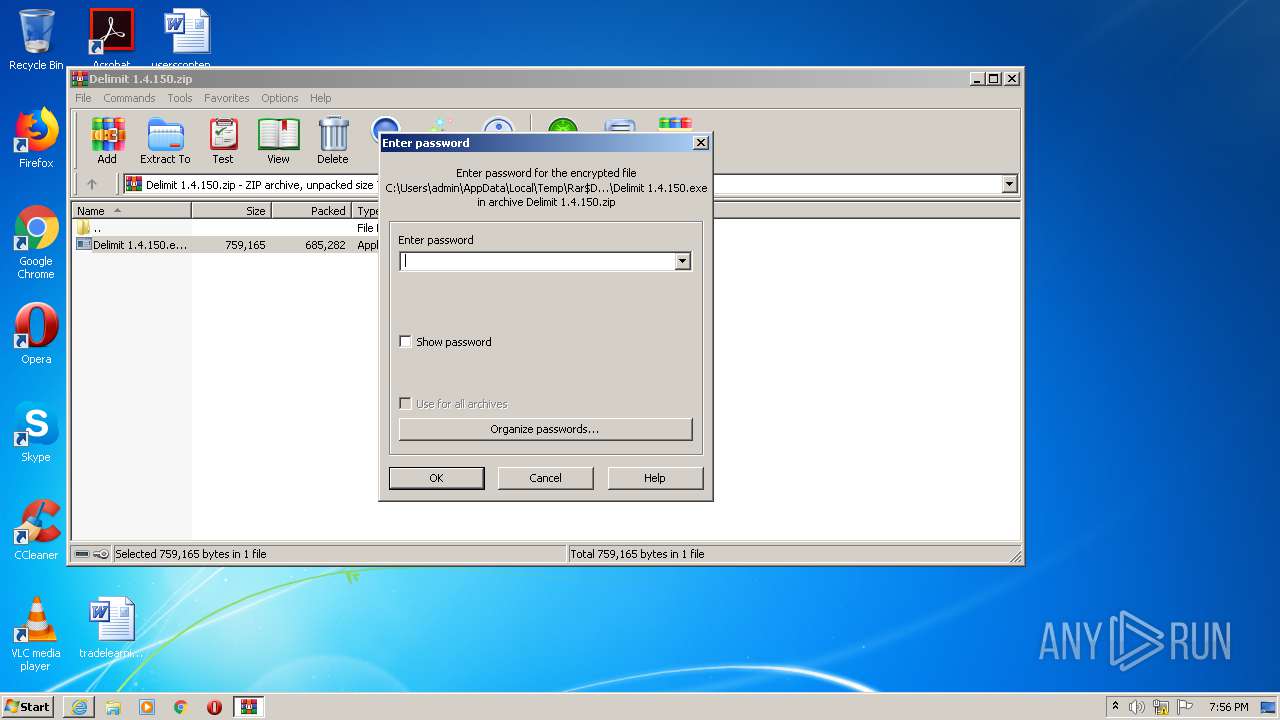
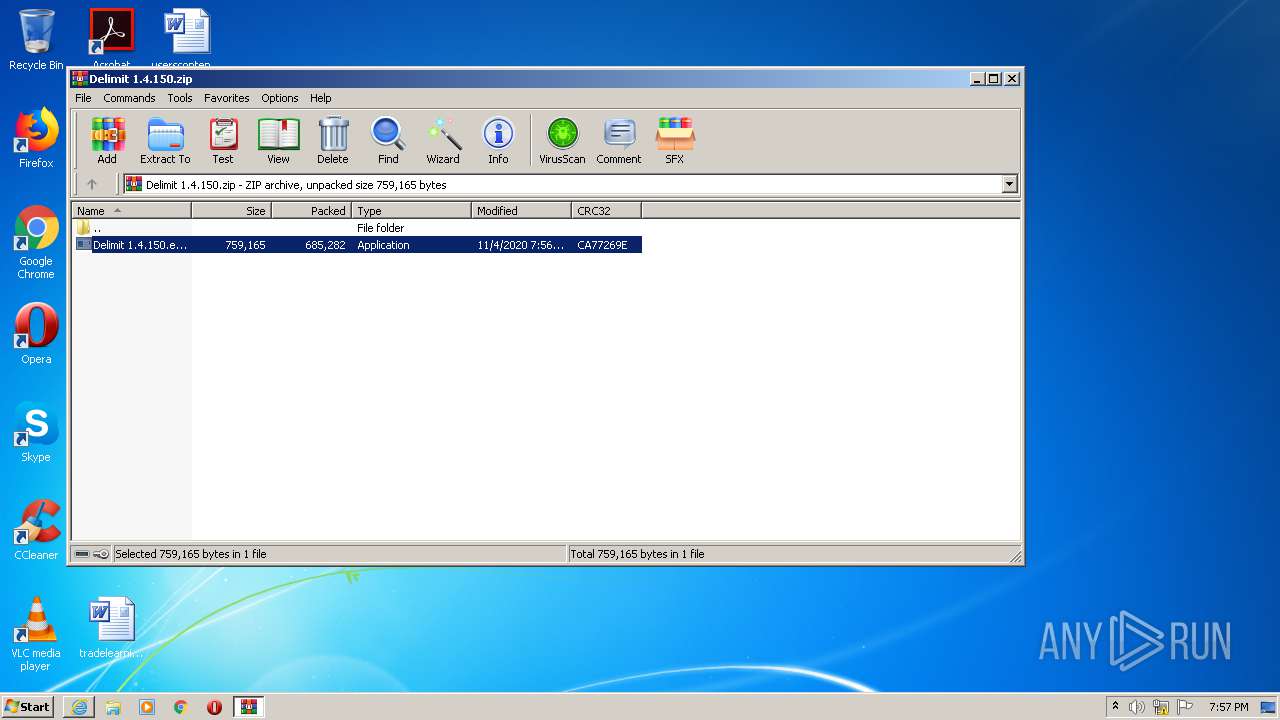
| 676 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Delimit 1.4.150.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\misc.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\7za.exe | — | Delimit 1.4.150.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\AppData\Local\Temp\is-7575T.tmp\Delimit 1.4.150.tmp" /SL5="$4018C,368825,121344,C:\Users\admin\Desktop\Delimit 1.4.150.exe" /SPAWNWND=$4014E /NOTIFYWND=$70138 | C:\Users\admin\AppData\Local\Temp\is-7575T.tmp\Delimit 1.4.150.tmp | Delimit 1.4.150.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1408 | "C:\Users\admin\Desktop\Delimit 1.4.150.exe" /SPAWNWND=$4014E /NOTIFYWND=$70138 | C:\Users\admin\Desktop\Delimit 1.4.150.exe | Delimit 1.4.150.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: 22.54 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\Desktop\Delimit 1.4.150.exe" | C:\Users\admin\Desktop\Delimit 1.4.150.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: 22.54 Modules
| |||||||||||||||
| 1912 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\form.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-A5JUL.tmp\7za.exe | Delimit 1.4.150.tmp | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2608 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\is-24HSK.tmp\Delimit 1.4.150.tmp" /SL5="$70138,368825,121344,C:\Users\admin\Desktop\Delimit 1.4.150.exe" | C:\Users\admin\AppData\Local\Temp\is-24HSK.tmp\Delimit 1.4.150.tmp | — | Delimit 1.4.150.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
2 439
Read events
2 263
Write events
173
Delete events
3
Modification events
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2925015314 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847716 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
12
Text files
9
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8537.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8538.tmp | — | |
MD5:— | SHA256:— | |||
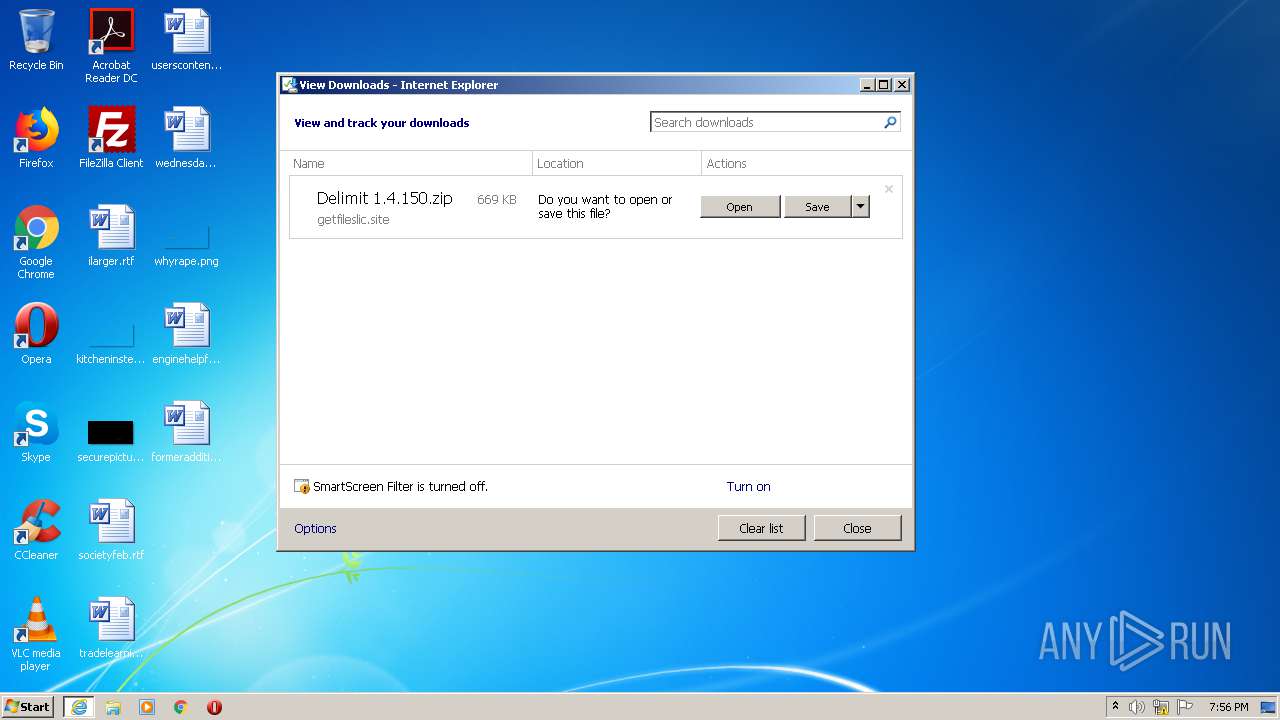
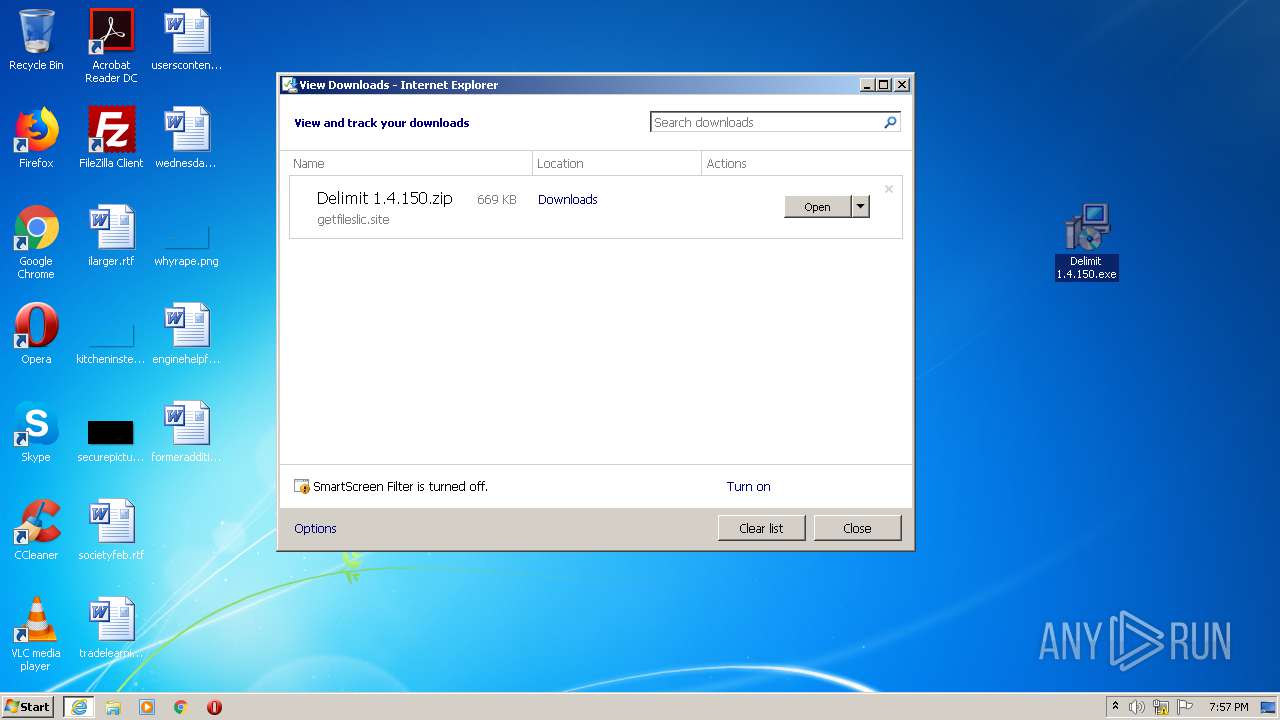
| 2480 | iexplore.exe | C:\Users\admin\Downloads\Delimit 1.4.150.zip.o4nm3ou.partial | — | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA17DC006260A9923.TMP | — | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\Downloads\Delimit 1.4.150.zip.o4nm3ou.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb676.14713\Delimit 1.4.150.exe | — | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE2BCF86149A24188.TMP | — | |
MD5:— | SHA256:— | |||
| 2608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DA14CBD1-1ED7-11EB-9CF6-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 1000 | Delimit 1.4.150.tmp | C:\Users\admin\AppData\Local\Temp\{01FD3C10-7094-4682-AA5E-4A8C9372297F}\is-UF88I.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | Delimit 1.4.150.tmp | C:\Users\admin\AppData\Local\Temp\{01FD3C10-7094-4682-AA5E-4A8C9372297F}\license.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
13
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | iexplore.exe | GET | 301 | 104.18.50.174:80 | http://getfileslic.site/download?id=qUwFk4WxAx8&s=C0B24C23 | US | — | — | suspicious |
2608 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2608 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1000 | Delimit 1.4.150.tmp | GET | 200 | 104.18.57.107:80 | http://worldofbooks.org/getchannel | US | binary | 1 b | malicious |
1000 | Delimit 1.4.150.tmp | POST | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
1000 | Delimit 1.4.150.tmp | POST | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2608 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2480 | iexplore.exe | 104.18.50.174:80 | getfileslic.site | Cloudflare Inc | US | shared |
2480 | iexplore.exe | 104.18.50.174:443 | getfileslic.site | Cloudflare Inc | US | shared |
2480 | iexplore.exe | 104.18.51.174:80 | getfileslic.site | Cloudflare Inc | US | shared |
2480 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1000 | Delimit 1.4.150.tmp | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2608 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2608 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1000 | Delimit 1.4.150.tmp | 104.18.57.107:80 | worldofbooks.org | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getfileslic.site |
| suspicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
worldofbooks.org |
| malicious |