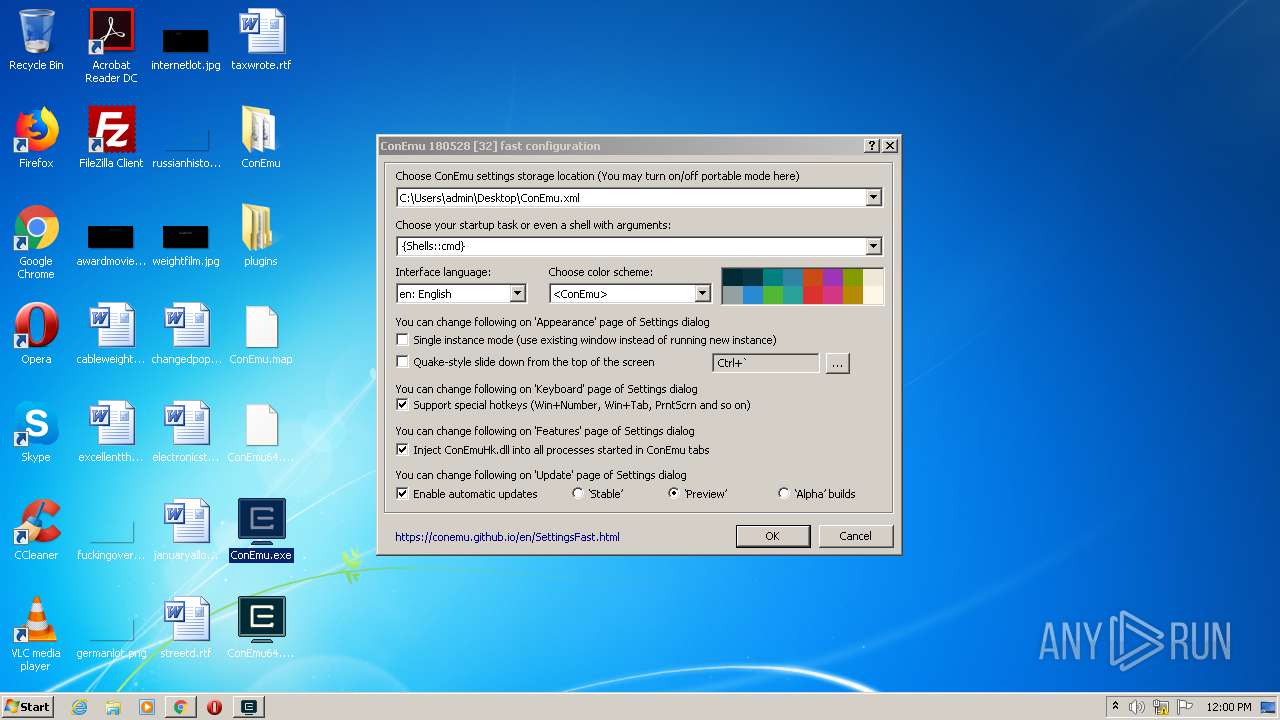
| File name: | ConEmu.exe |
| Full analysis: | https://app.any.run/tasks/cda873fb-196a-498c-93fc-0a59093eb3cd |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2020, 10:58:03 |
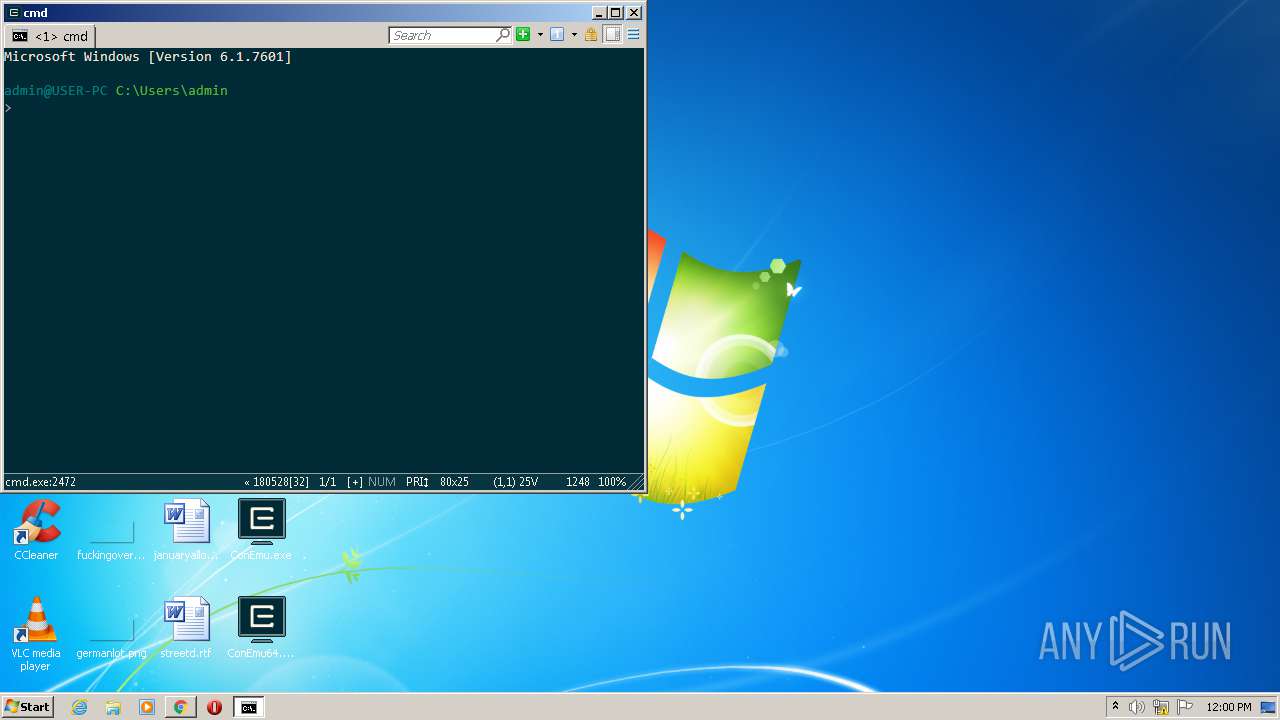
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4C6C1EFF11215FEF112FDC03FB46947E |
| SHA1: | D5628D312881E7175A53C678F372F1CA2C0999E8 |
| SHA256: | 570D2059BF33EED8FAB77A4CA6CD67E996EF3E2C2D70E0E269C53DC961C4802F |
| SSDEEP: | 49152:5Jfe3owTB0iXJ9aF7VnGFm6S/KEqzS3vv3jirr3jjWiTaOvifviOrGbpa:5Ne3owTB0iXJgFtGFm6S/+zS3vv3jirW |
MALICIOUS
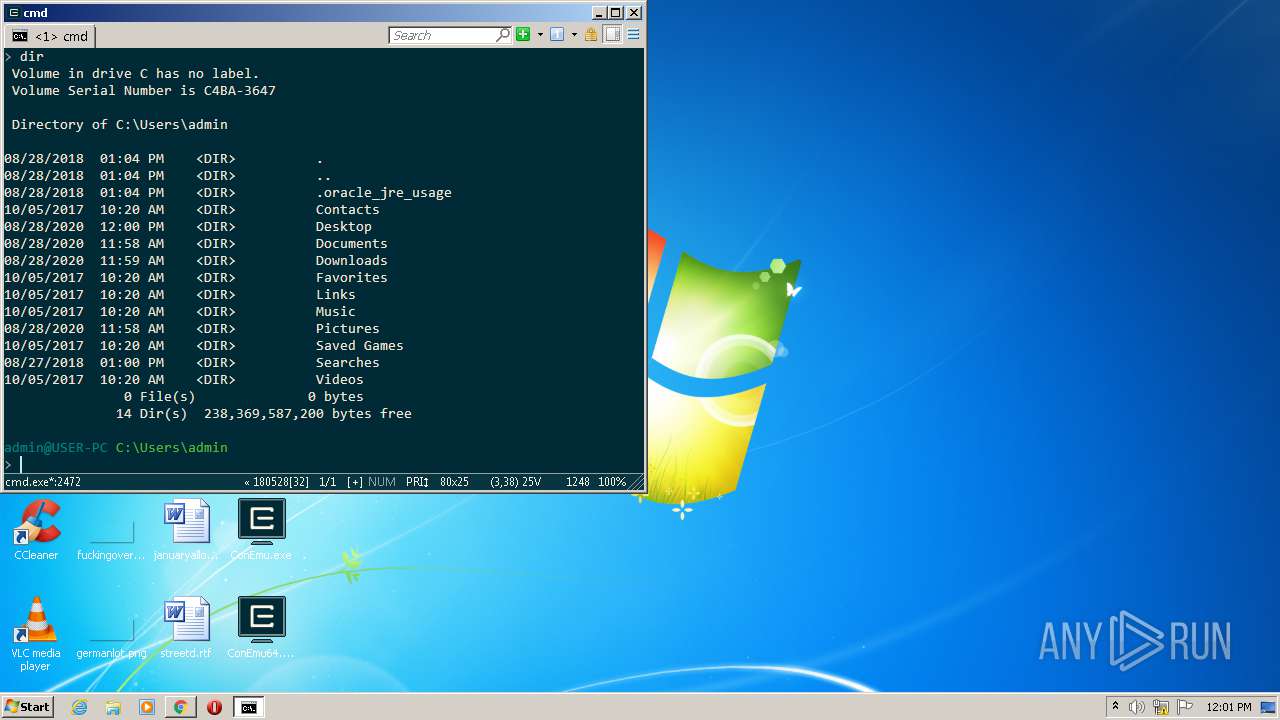
Loads dropped or rewritten executable
- ConEmu.exe (PID: 1328)
- cmd.exe (PID: 2472)
- ConEmuC.exe (PID: 1248)
- SearchProtocolHost.exe (PID: 3536)
- cmd.exe (PID: 2800)
- find.exe (PID: 660)
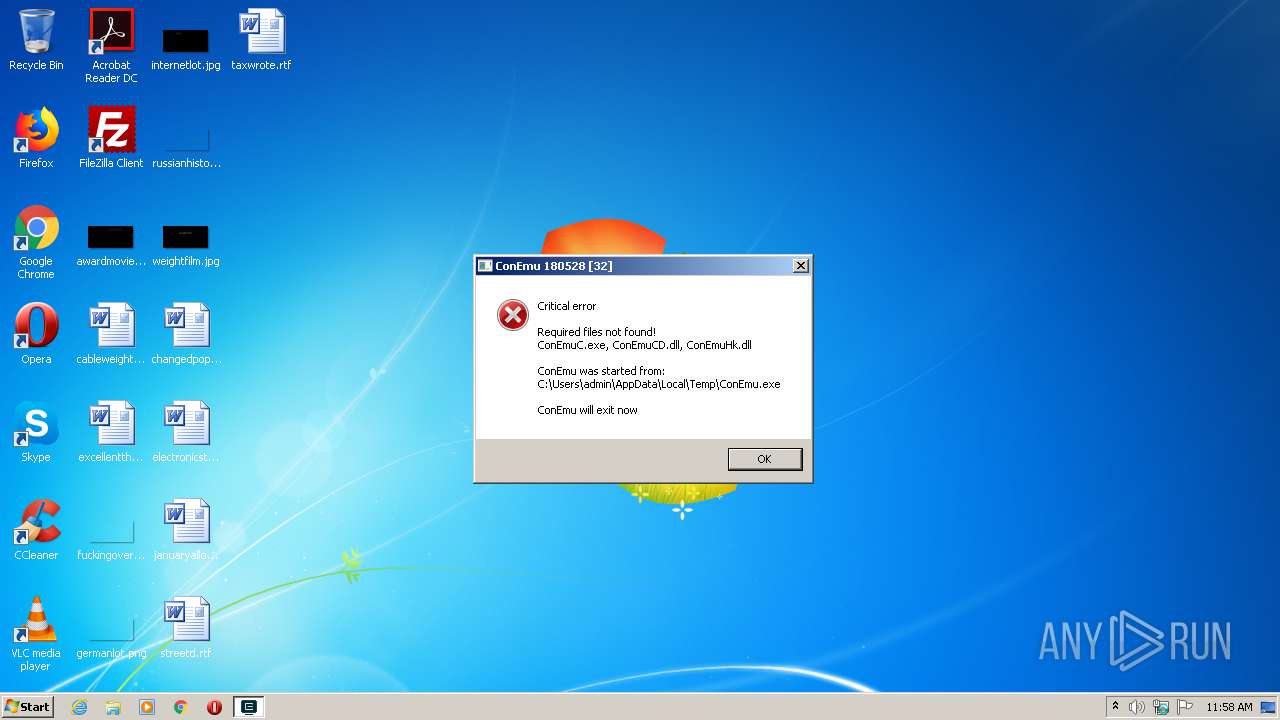
Application was dropped or rewritten from another process
- ConEmuC.exe (PID: 2756)
- ConEmuC.exe (PID: 1248)
Detects Cygwin installation
- WinRAR.exe (PID: 3208)
SUSPICIOUS
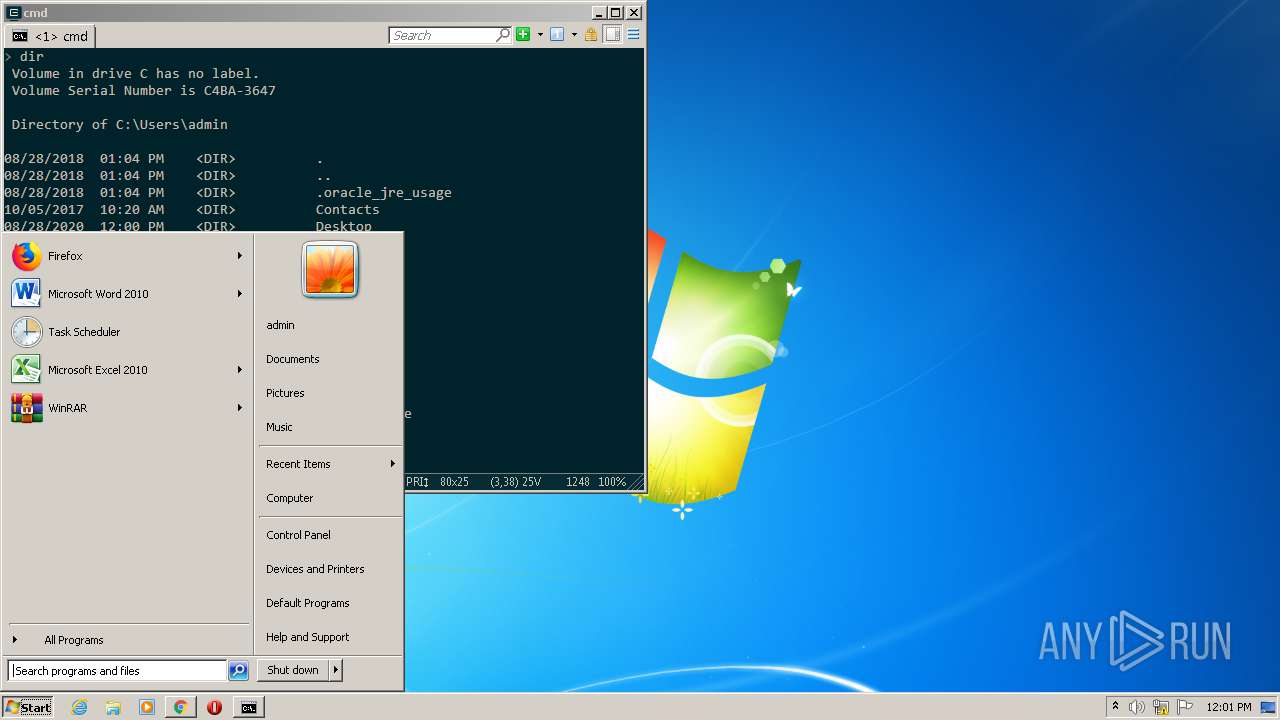
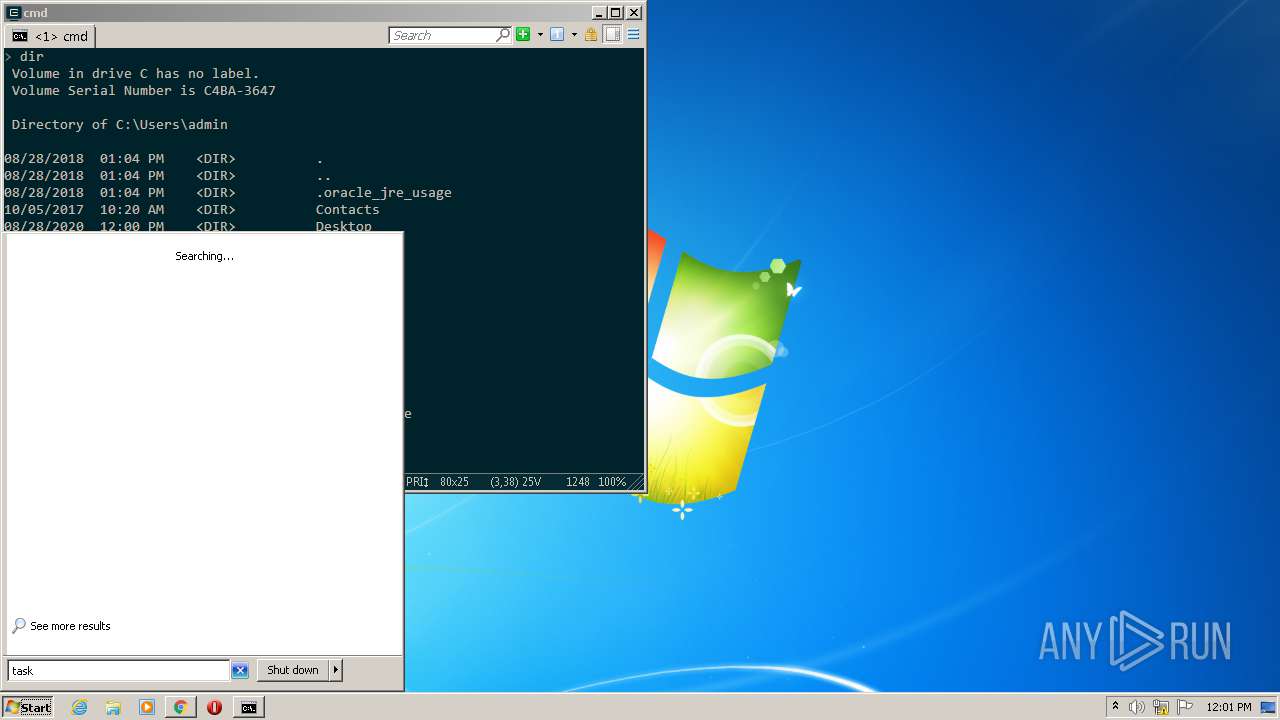
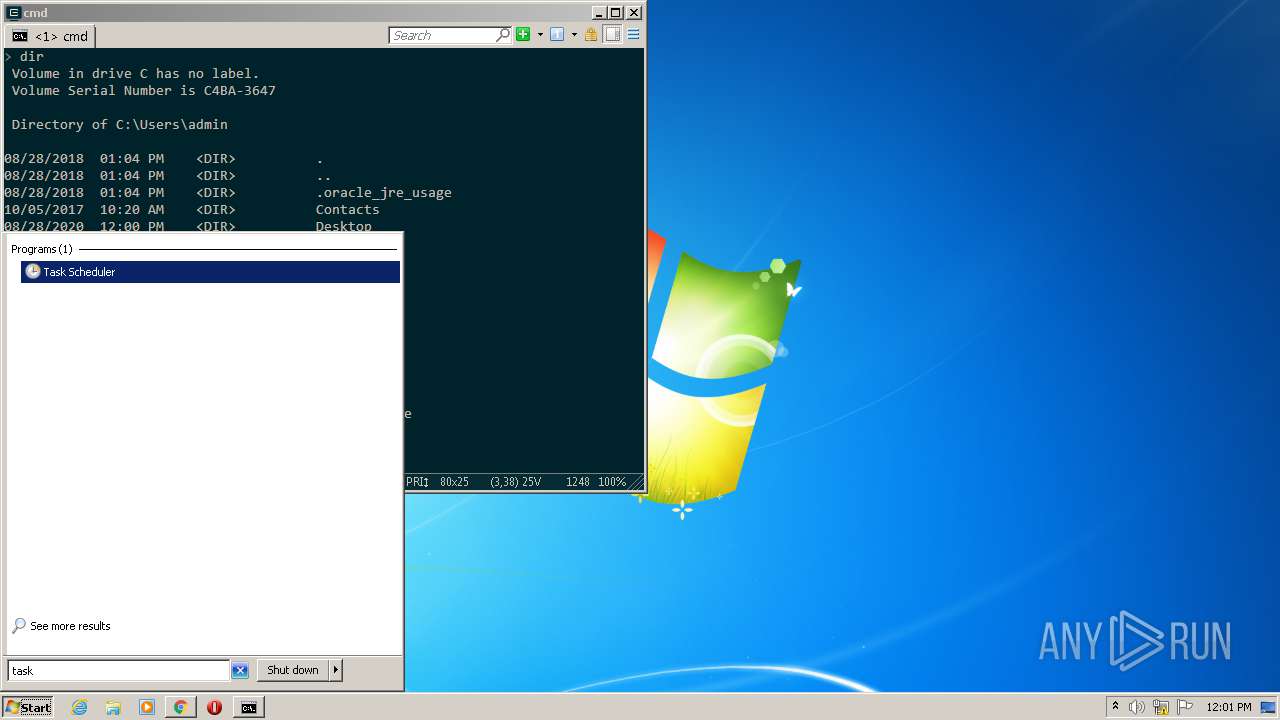
Searches for installed software
- ConEmu.exe (PID: 1328)
- ConEmu.exe (PID: 1448)
Reads Internet Cache Settings
- ConEmuC.exe (PID: 2756)
Starts CMD.EXE for commands execution
- ConEmuC.exe (PID: 1248)
- cmd.exe (PID: 2472)
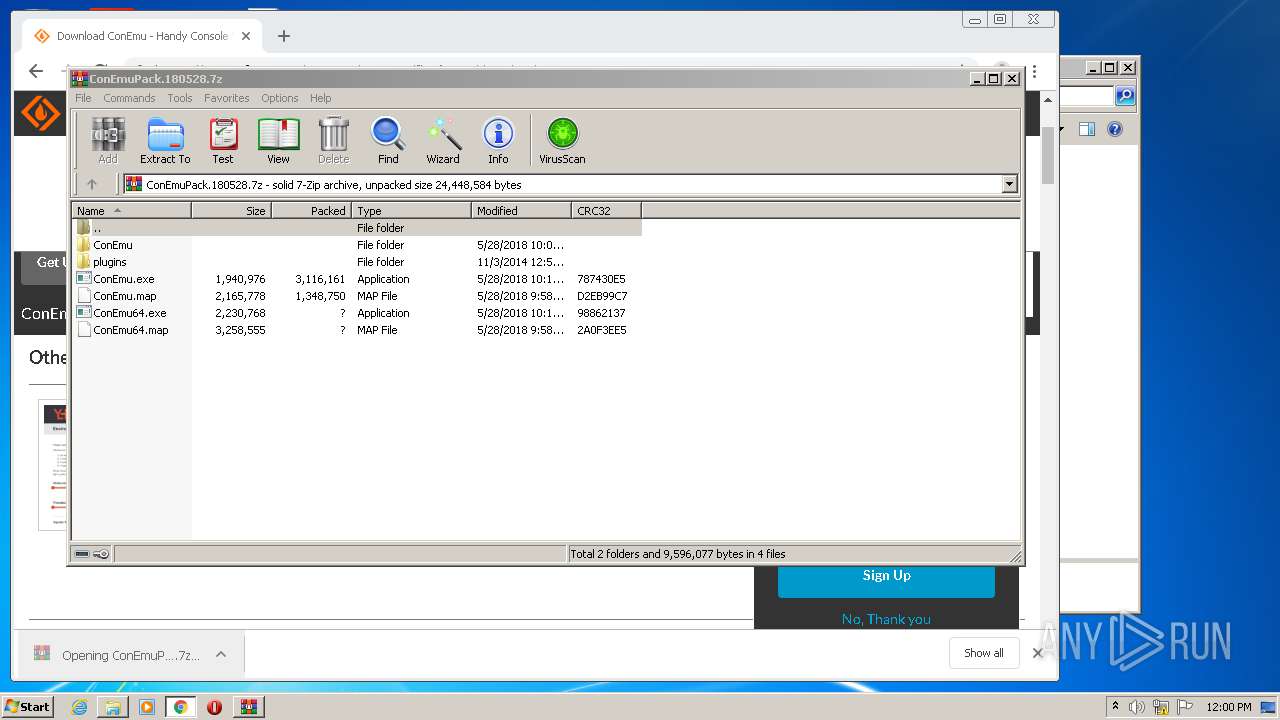
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3208)
Application launched itself
- cmd.exe (PID: 2472)
INFO
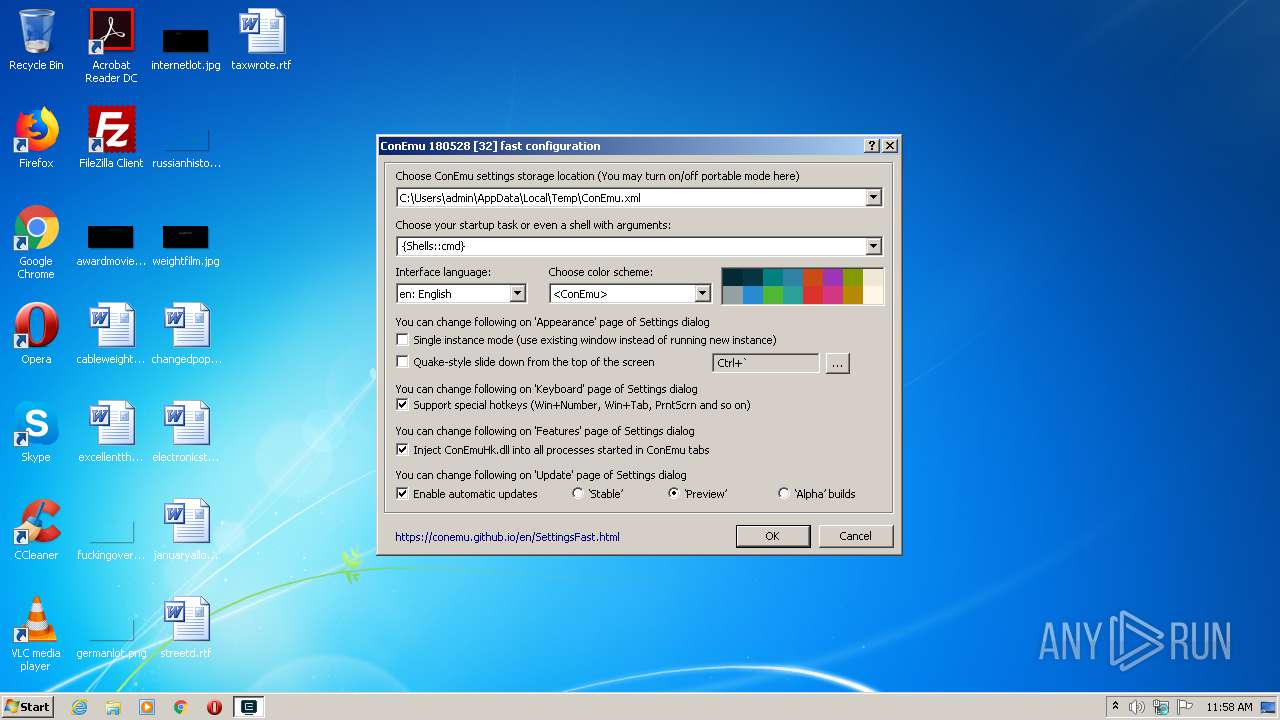
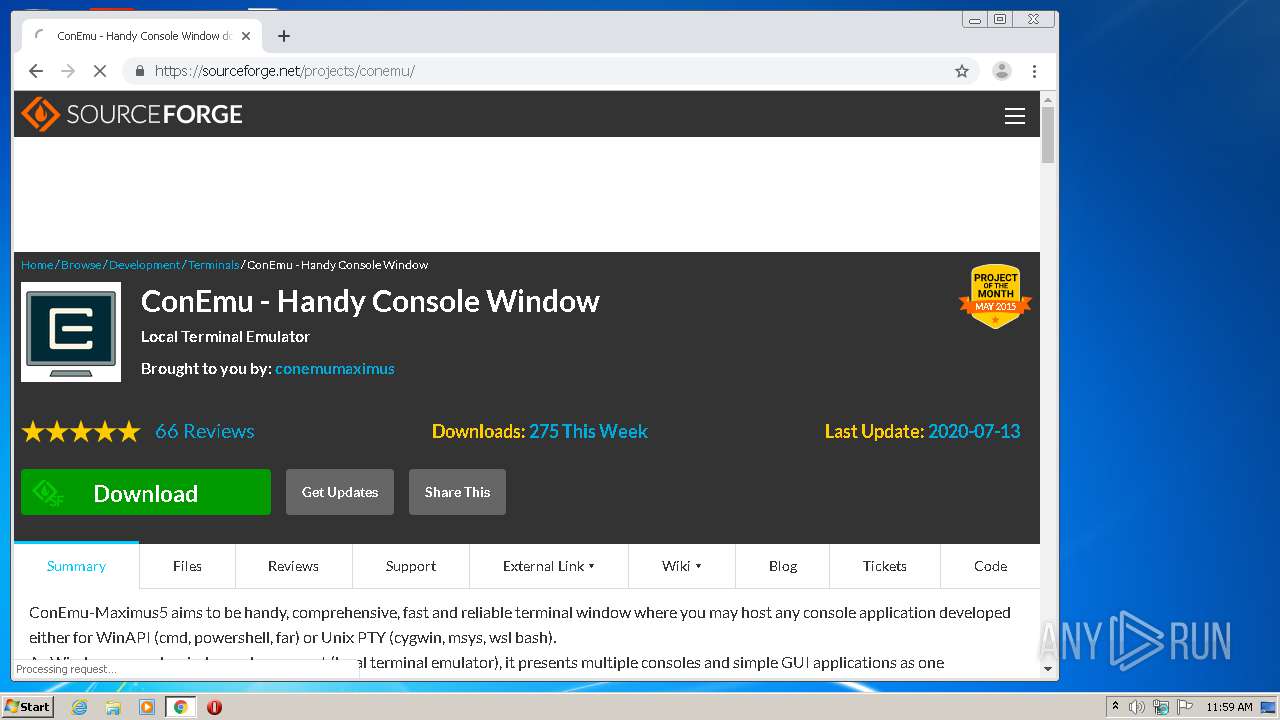
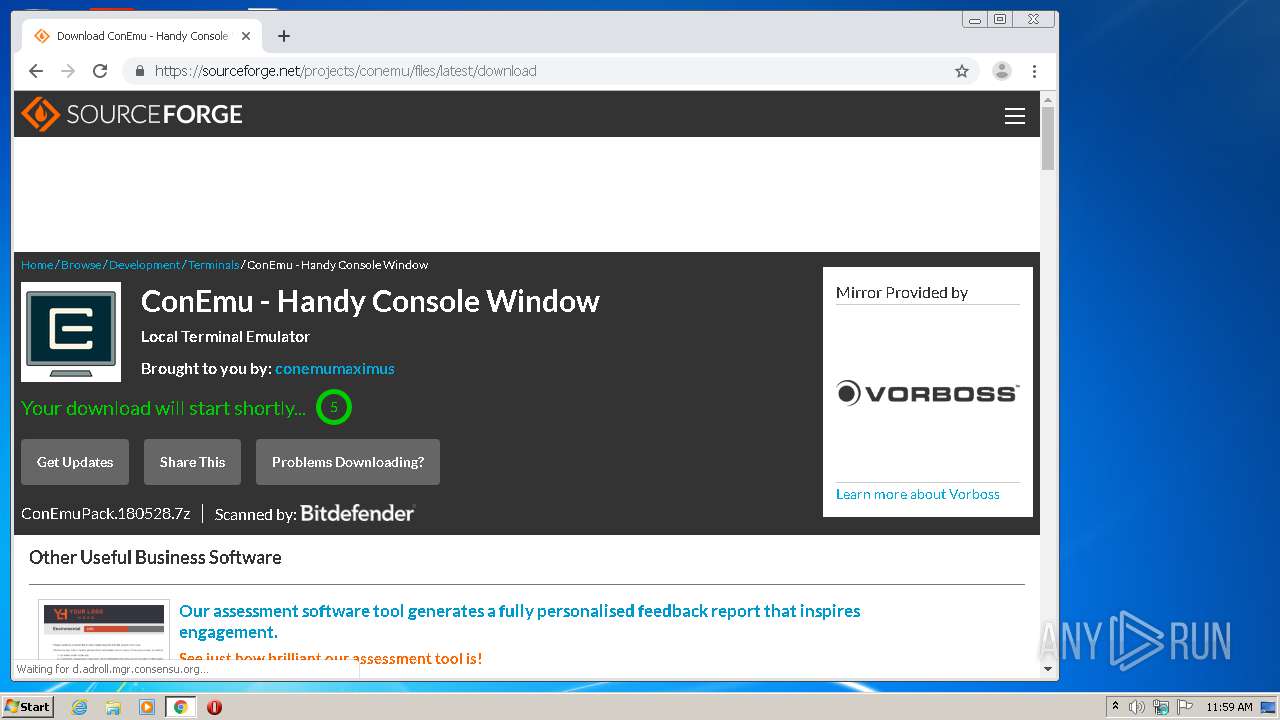
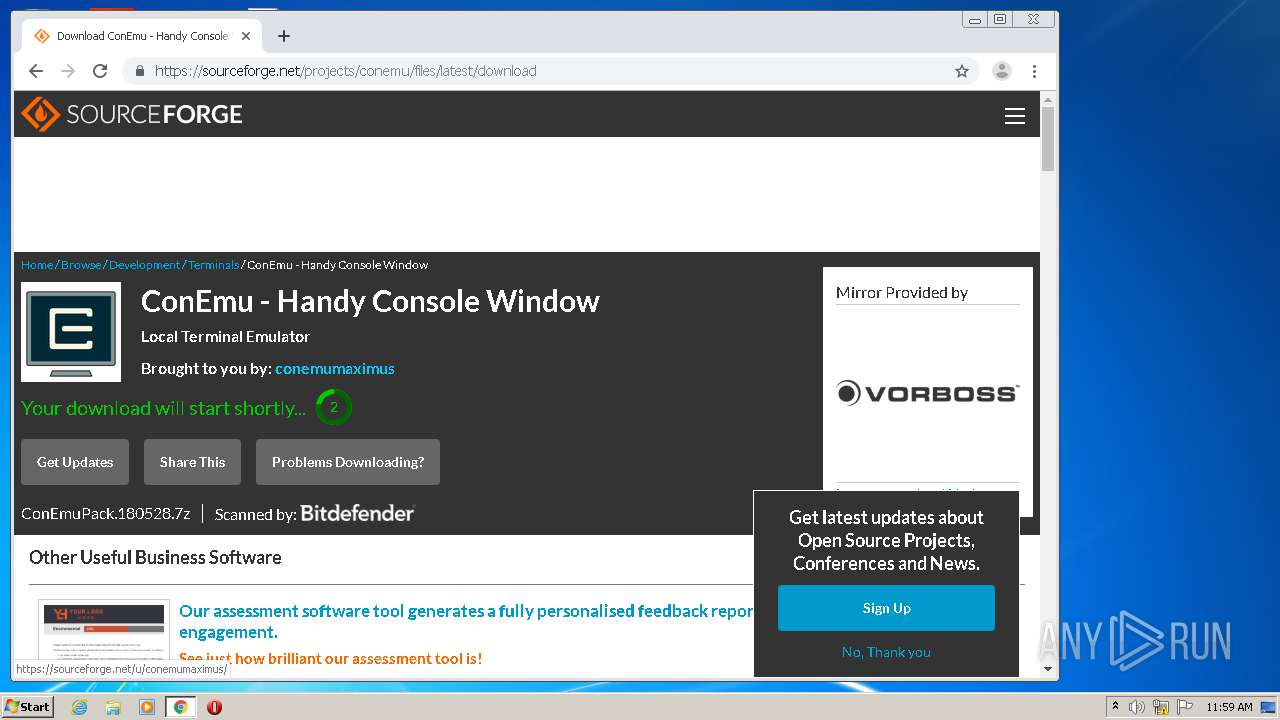
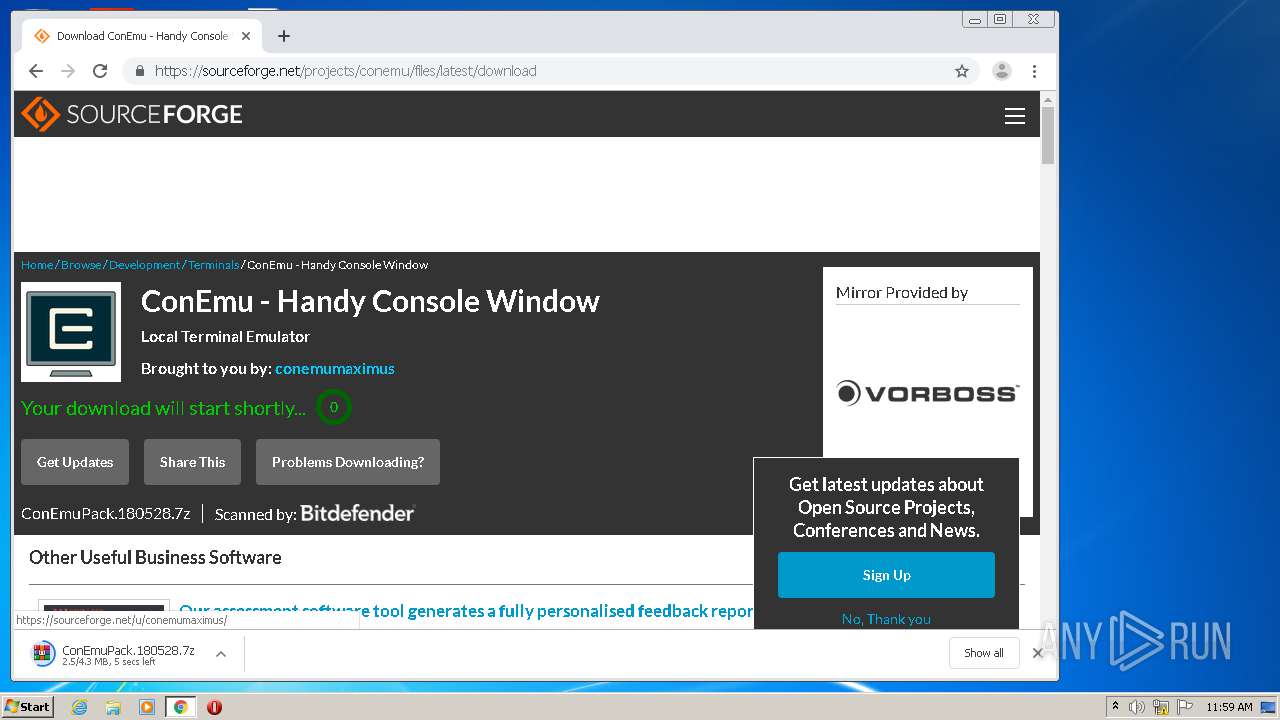
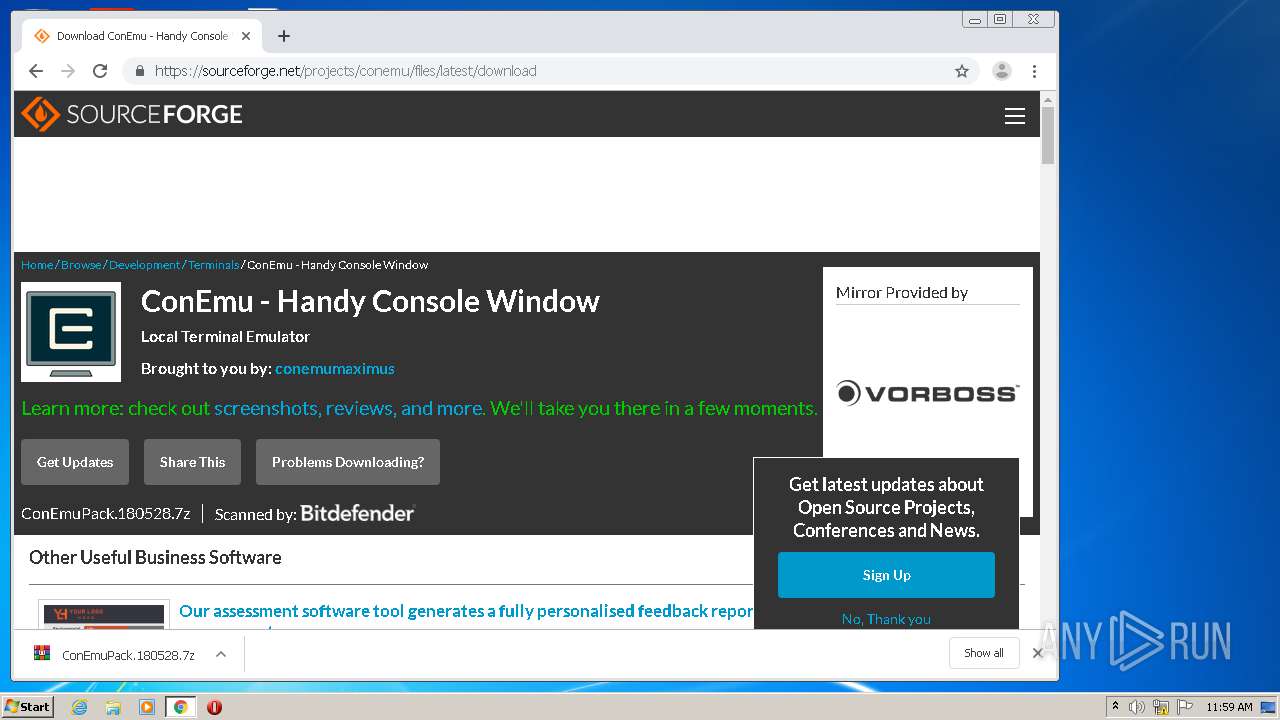
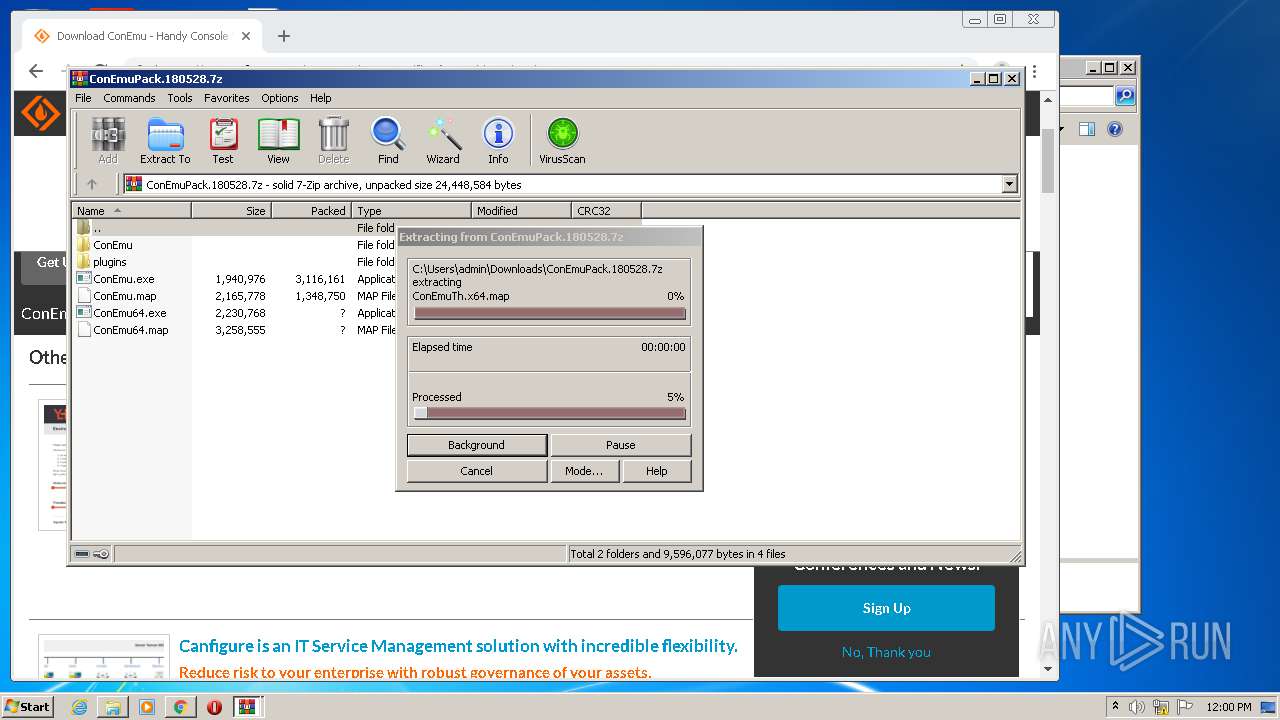
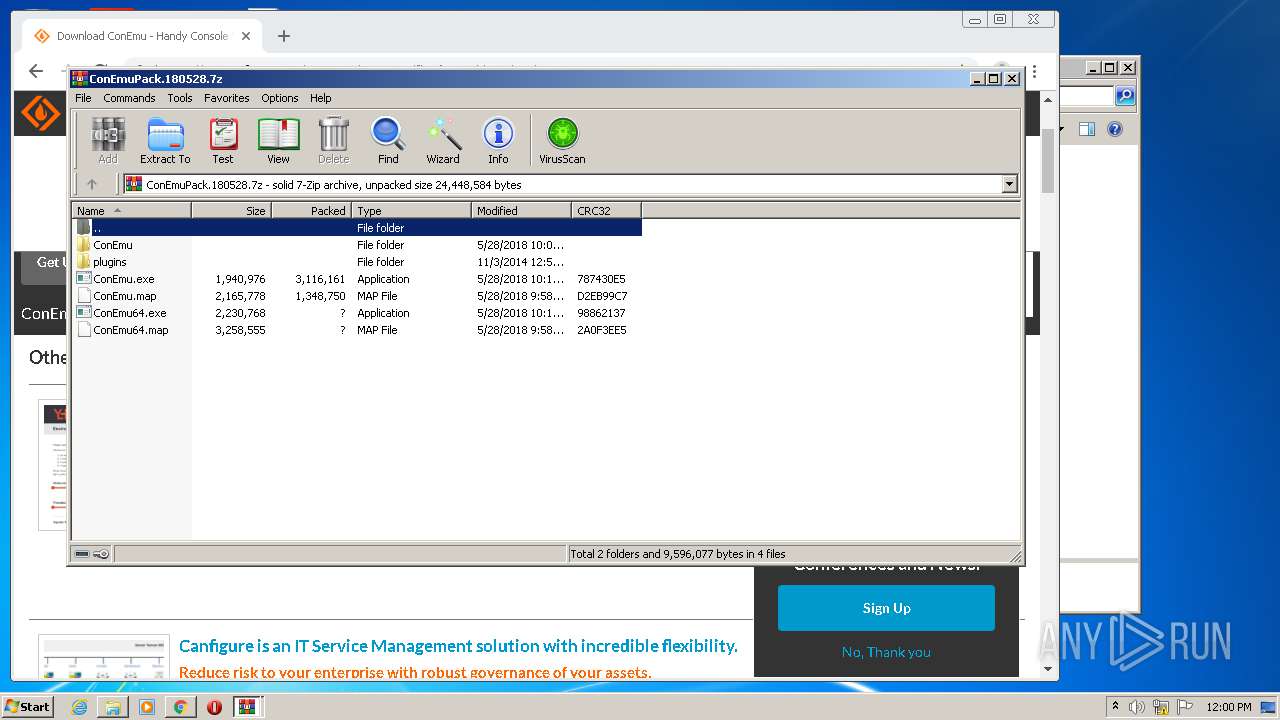
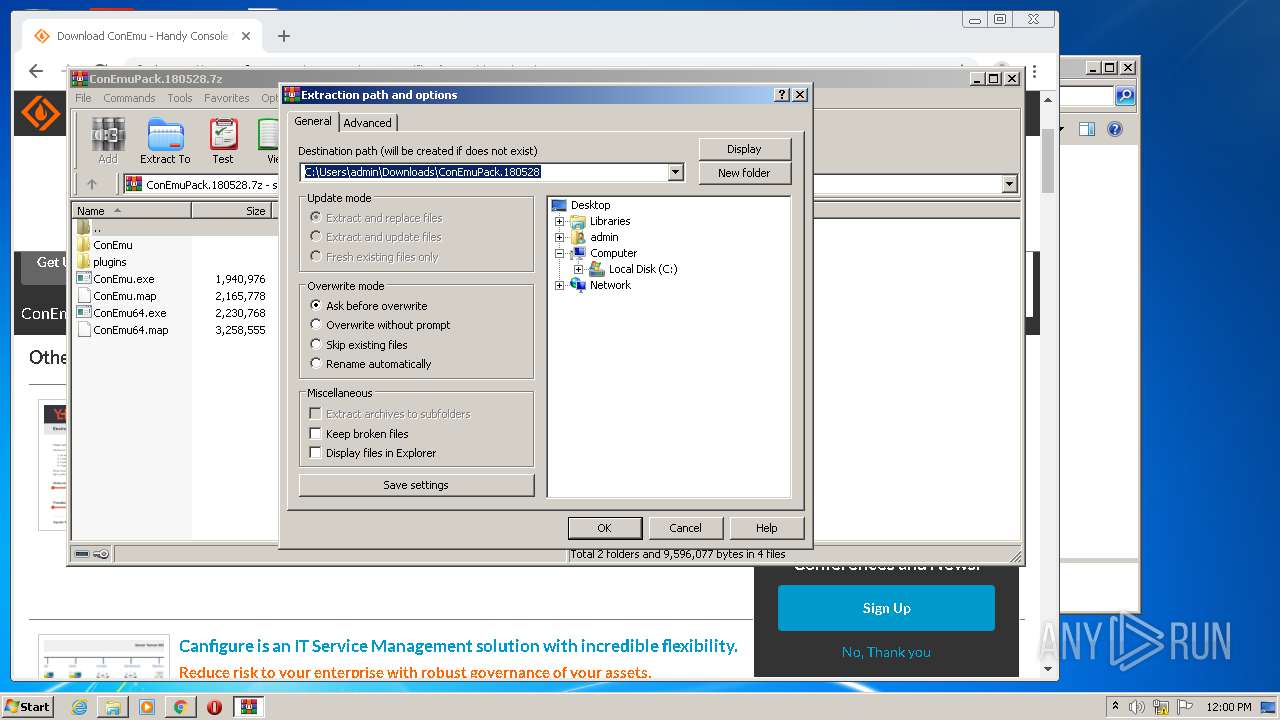
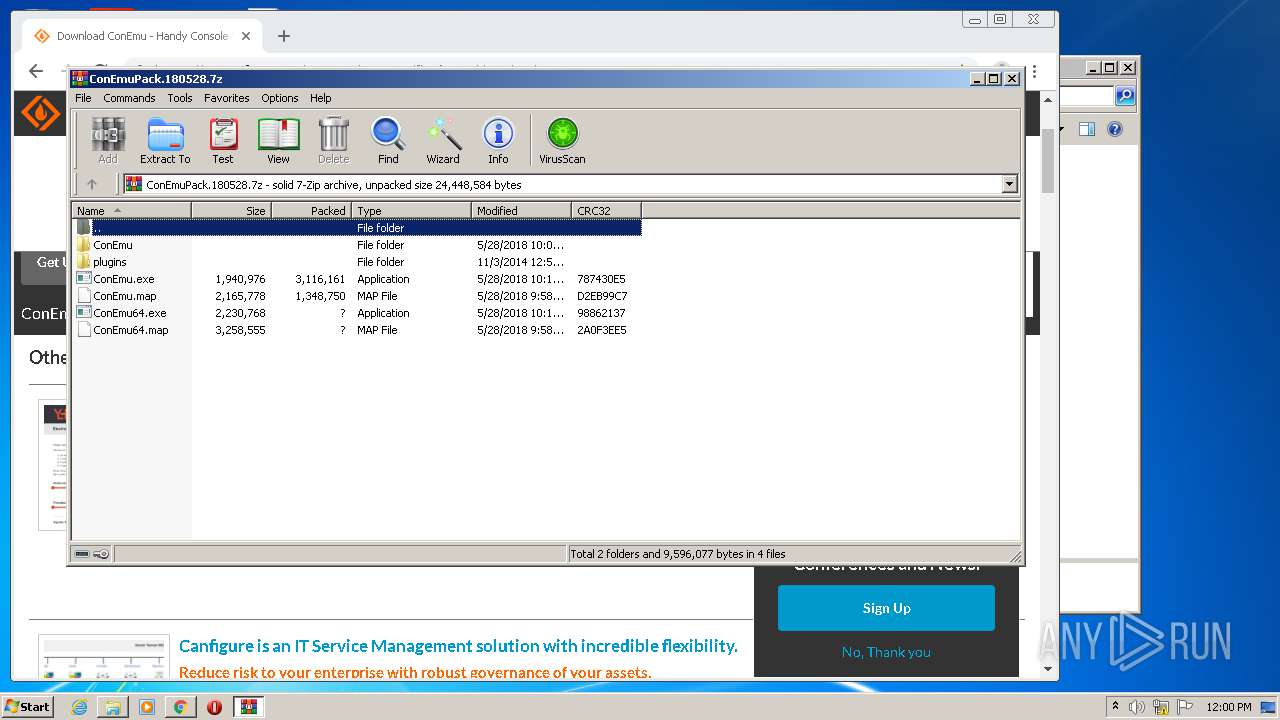
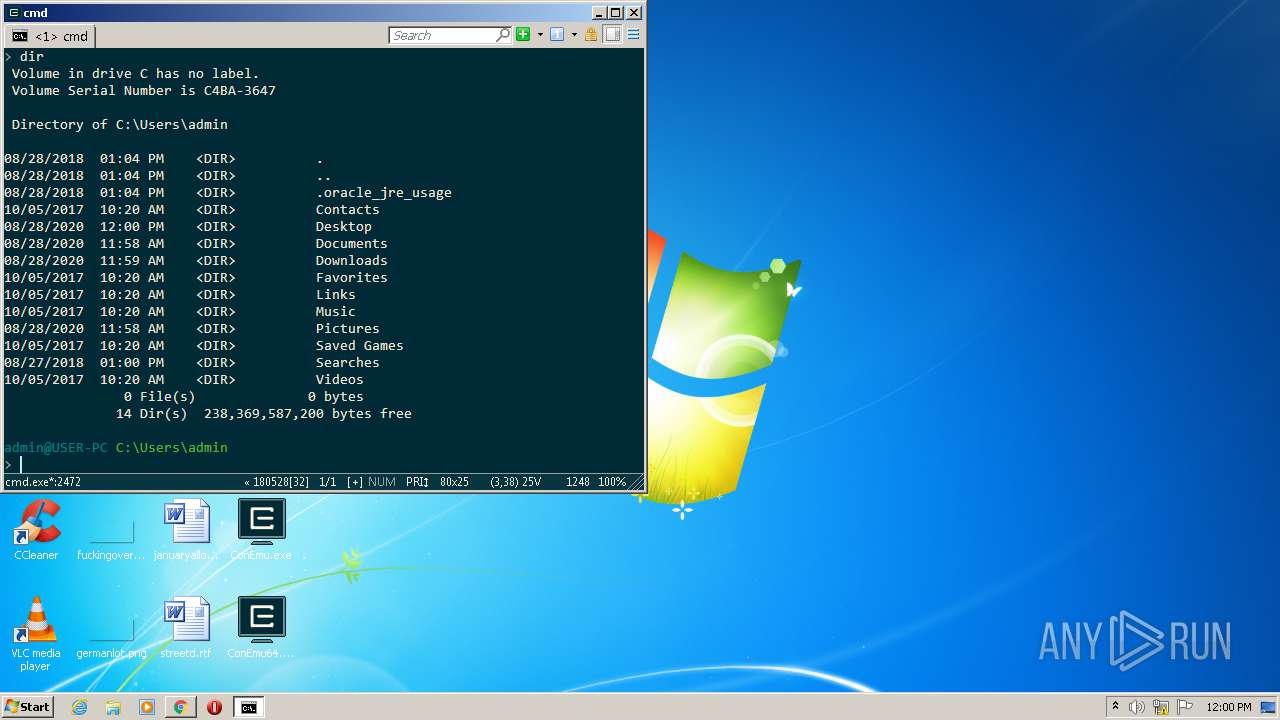
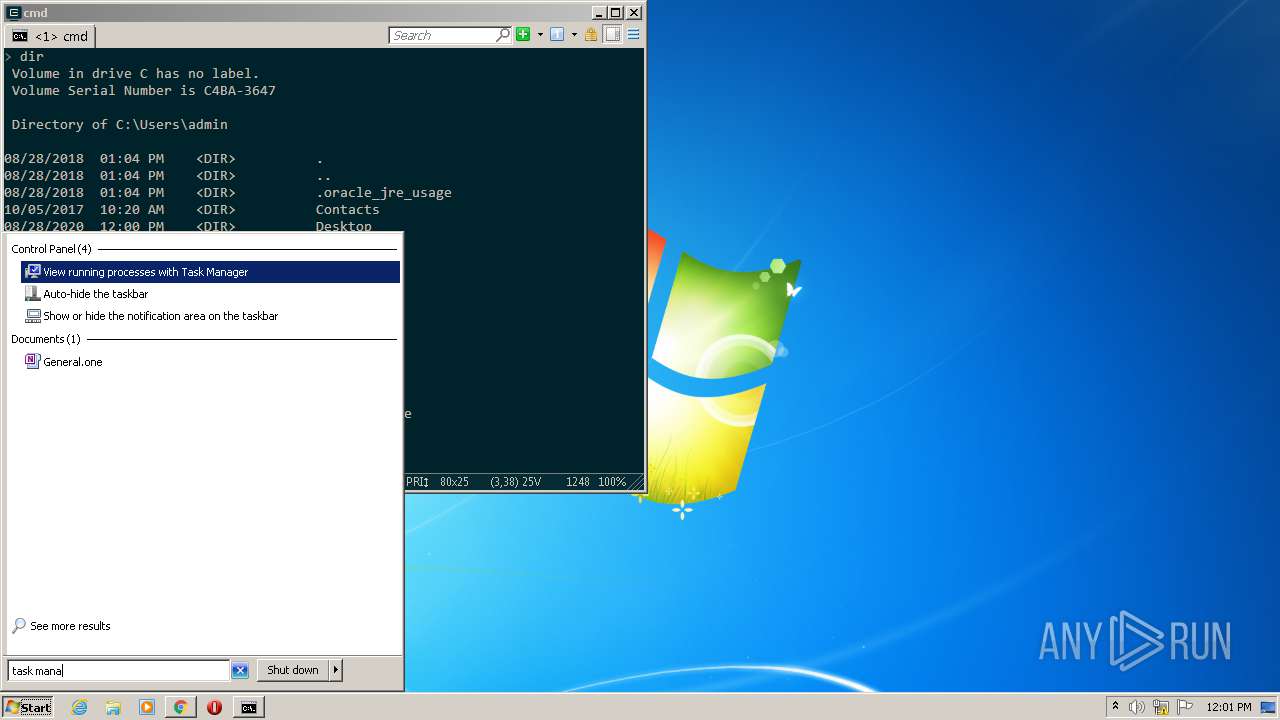
Manual execution by user
- ConEmu.exe (PID: 1328)
- chrome.exe (PID: 2068)
- explorer.exe (PID: 2884)
Reads the hosts file
- chrome.exe (PID: 2068)
- chrome.exe (PID: 3908)
Reads Internet Cache Settings
- chrome.exe (PID: 2068)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3208)
Application launched itself
- chrome.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:28 22:58:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 1123328 |
| InitializedDataSize: | 1001472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf415c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 18.5.28.0 |
| ProductVersionNumber: | 18.5.28.0 |
| FileFlagsMask: | 0x0037 |
| FileFlags: | Special build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | ConEmu-Maximus5 |
| LegalCopyright: | © ConEmu.Maximus5@gmail.com |
| FileDescription: | Console Emulator (x86) |
| FileVersion: | 180528 |
| OriginalFileName: | ConEmu.exe |
| ProductName: | ConEmu |
| ProductVersion: | 180528 |
| SpecialBuild: | Preview |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-May-2018 20:58:34 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ConEmu-Maximus5 |
| LegalCopyright: | © ConEmu.Maximus5@gmail.com |
| FileDescription: | Console Emulator (x86) |
| FileVersion: | 180528 |
| OriginalFilename: | ConEmu.exe |
| ProductName: | ConEmu |
| ProductVersion: | 180528 |
| SpecialBuild: | Preview |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-May-2018 20:58:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00112342 | 0x00112400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6092 |
.rdata | 0x00114000 | 0x0006C42C | 0x0006C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27488 |
.data | 0x00181000 | 0x000324E0 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.39785 |
.rsrc | 0x001B4000 | 0x000469B8 | 0x00046A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07231 |
.reloc | 0x001FB000 | 0x0000F1AC | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78293 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18848 | 2153 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.60889 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 1.9815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
4 | 3.23434 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 3.31347 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.67785 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 7.37706 | 3113 | UNKNOWN | English - United States | RT_ICON |
8 | 3.57076 | 5144 | UNKNOWN | English - United States | RT_ICON |
9 | 3.93685 | 3752 | UNKNOWN | English - United States | RT_ICON |
10 | 4.13501 | 2984 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
75
Monitored processes
32
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,9734394757075413605,16984889943699888390,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8014055097959035243 --mojo-platform-channel-handle=1140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Windows\system32\find.exe" "Windows" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,9734394757075413605,16984889943699888390,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=198506202879027466 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,9734394757075413605,16984889943699888390,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=516493911686209770 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\Desktop\ConEmu\ConEmuC.exe" /CINMODE=600020 /AID=1000 /GID=1328 /GHWND=000C0138 /BW=80 /BH=25 /BZ=32766 "/FN=Lucida Console" /FW=3 /FH=5 /TA=10100007 /HIDE /ROOT cmd.exe /k "%ConEmuBaseDir%\CmdInit.cmd" | C:\Users\admin\Desktop\ConEmu\ConEmuC.exe | — | ConEmu.exe | |||||||||||
User: admin Company: ConEmu-Maximus5 Integrity Level: MEDIUM Description: ConEmu console extender (x86) Exit code: 0 Version: 180528 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,9734394757075413605,16984889943699888390,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14919788747254841104 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,9734394757075413605,16984889943699888390,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17667923773422214139 --mojo-platform-channel-handle=896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Desktop\ConEmu.exe" | C:\Users\admin\Desktop\ConEmu.exe | — | explorer.exe | |||||||||||
User: admin Company: ConEmu-Maximus5 Integrity Level: MEDIUM Description: Console Emulator (x86) Exit code: 0 Version: 180528 Modules
| |||||||||||||||
| 1448 | "C:\Users\admin\AppData\Local\Temp\ConEmu.exe" | C:\Users\admin\AppData\Local\Temp\ConEmu.exe | — | explorer.exe | |||||||||||
User: admin Company: ConEmu-Maximus5 Integrity Level: MEDIUM Description: Console Emulator (x86) Exit code: 100 Version: 180528 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4076 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 691
Read events
2 525
Write events
162
Delete events
4
Modification events
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2068-13243085929539875 |
Value: 259 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2068) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
31
Suspicious files
108
Text files
252
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\53273f8e-5668-4749-bd9d-eb196ae254fd.tmp | — | |
MD5:— | SHA256:— | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 1448 | ConEmu.exe | C:\Users\admin\AppData\Local\Temp\ConEmu.xml | xml | |
MD5:65D4AB1367585465B95F042C73D7FB4D | SHA256:59DE5AE7CC05EF5E711A4709BFF0450979F1FACAFF86242560E58DD943EE7E72 | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFed51e.TMP | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:0CE1FA0314D44178816BA5E7133E07DD | SHA256:8D81EC8C4EFED885A0FF9267B0B388FB53316938EEDCDFABDC697E3610883714 | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed695.TMP | — | |
MD5:— | SHA256:— | |||
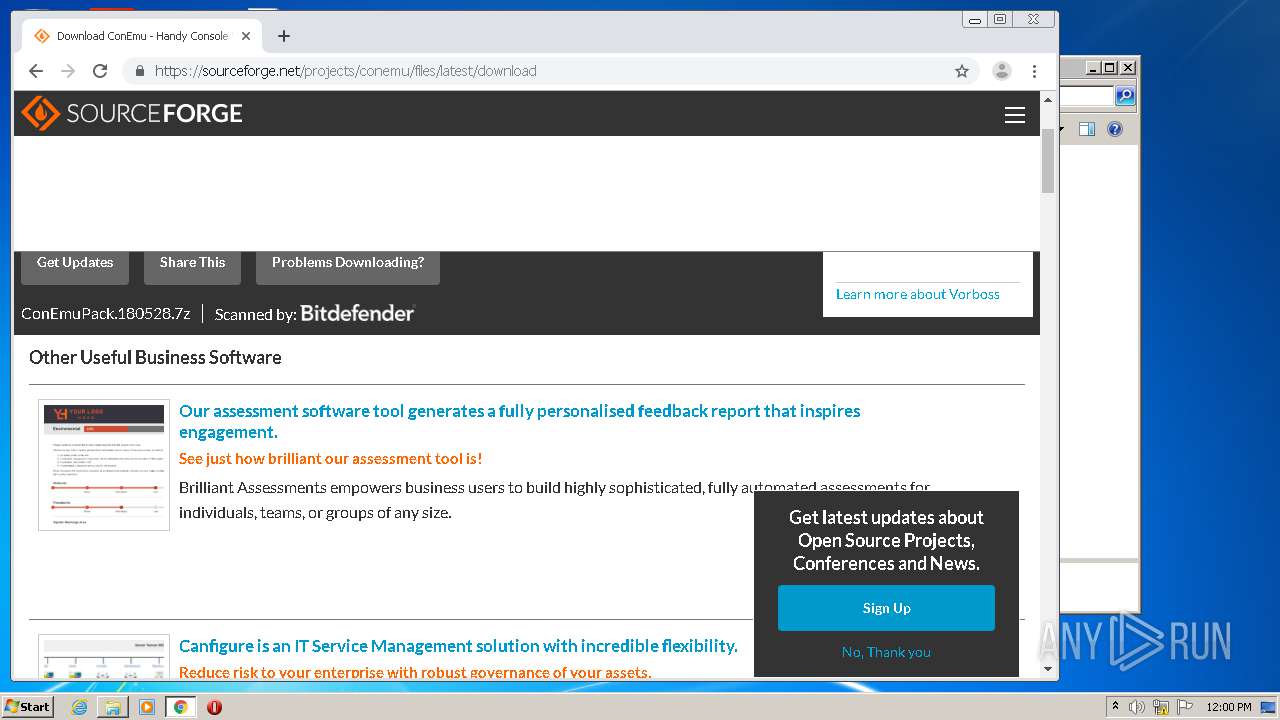
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
88
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2756 | ConEmuC.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3908 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3908 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 216.58.210.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 216.58.208.46:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3908 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 216.58.205.238:443 | consent.google.com | Google Inc. | US | whitelisted |
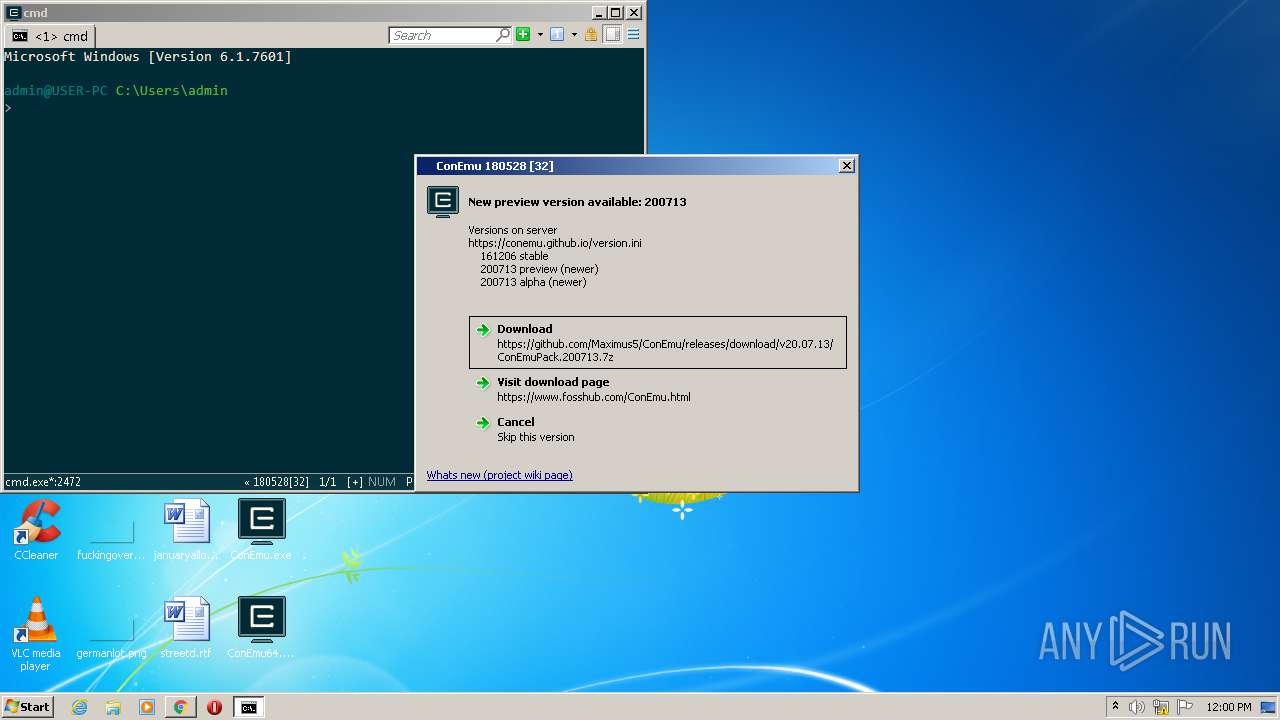
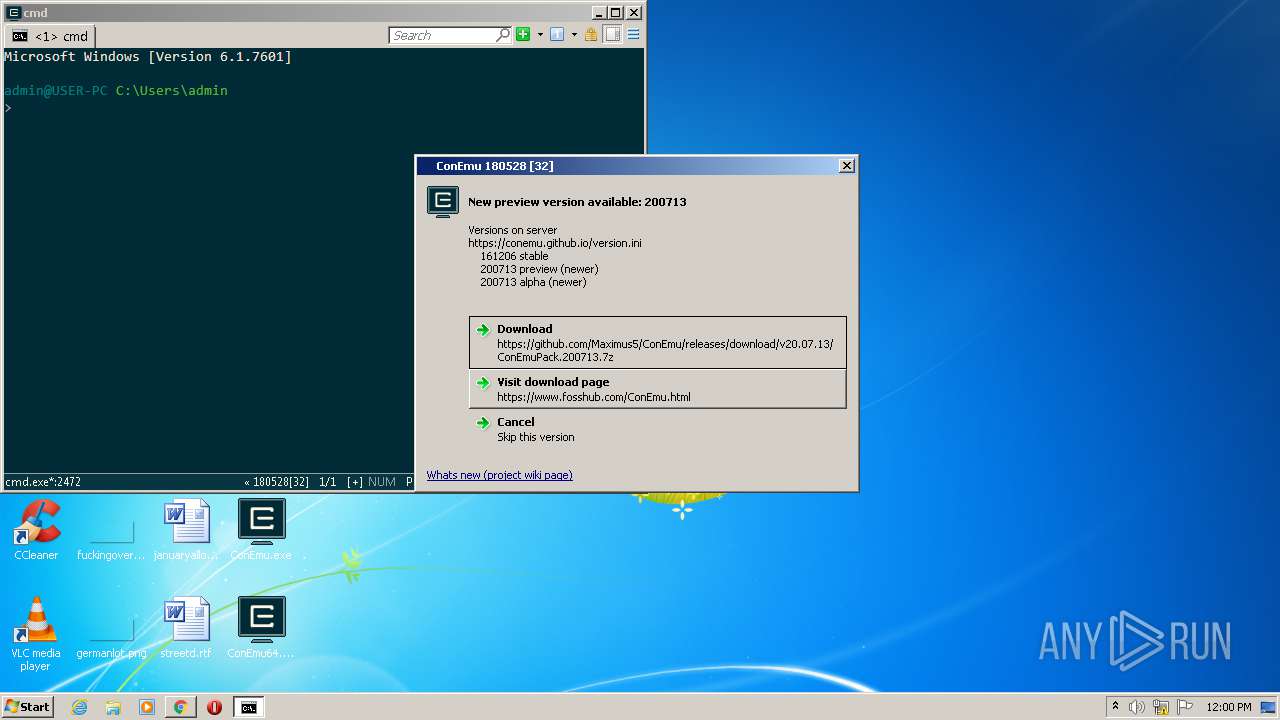
— | — | 185.199.110.153:443 | conemu.github.io | GitHub, Inc. | NL | shared |
3908 | chrome.exe | 185.199.110.153:443 | conemu.github.io | GitHub, Inc. | NL | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
consent.google.com |
| shared |