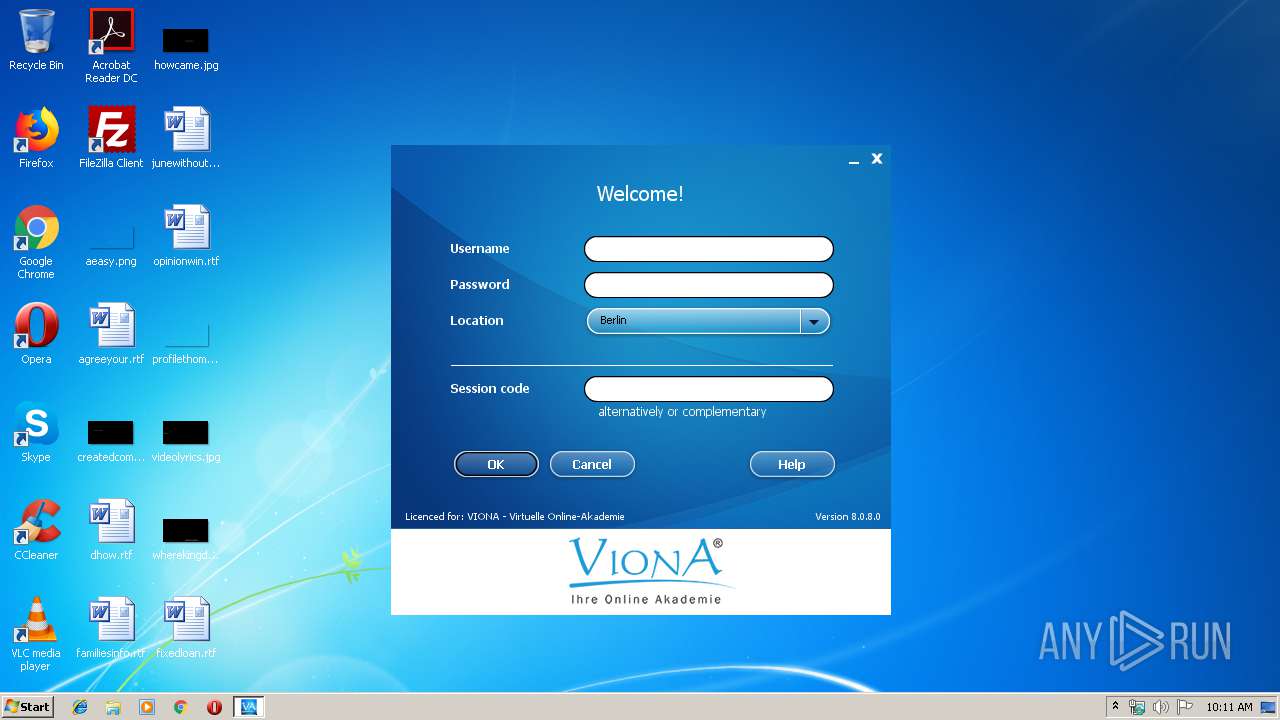
| File name: | viona.exe |
| Full analysis: | https://app.any.run/tasks/49e1f24e-d1eb-4dab-8780-97d6be40da03 |
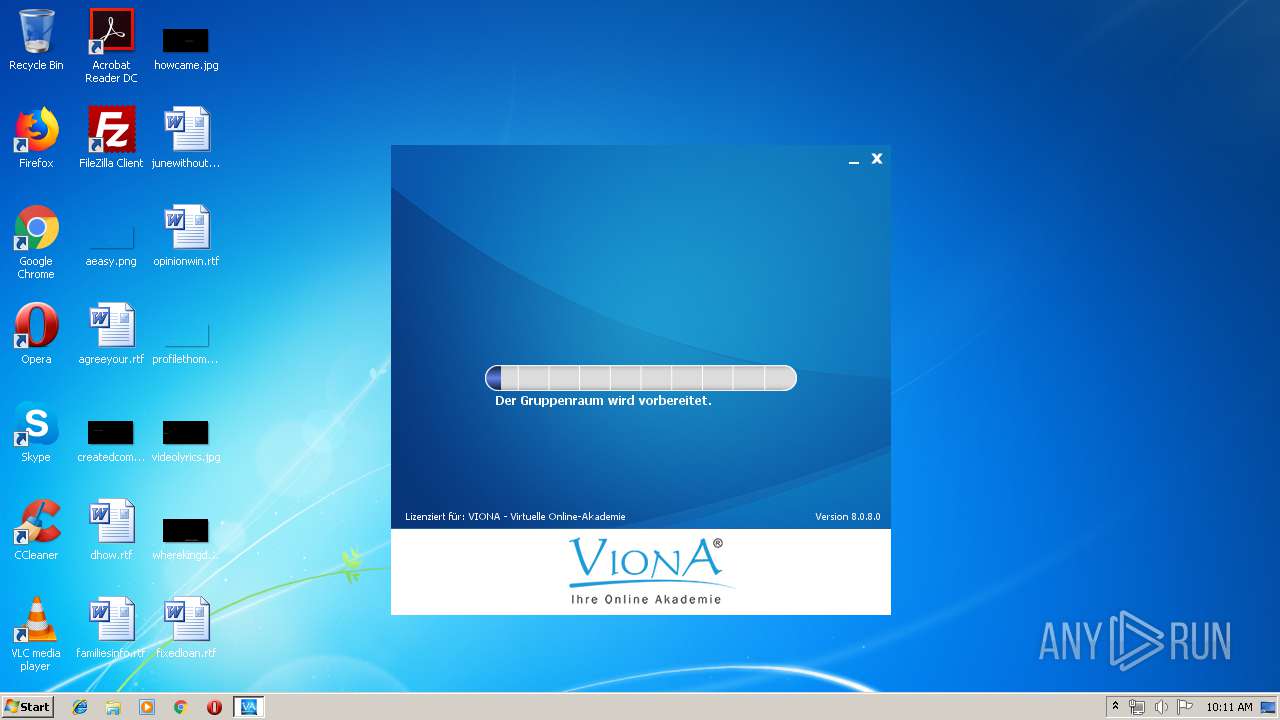
| Verdict: | Suspicious activity |
| Analysis date: | September 26, 2019, 09:10:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | CF668DB91A3ADBE11D00DE540A514F97 |
| SHA1: | 817EAC4C5C9BF3A6EC1E4BE0A63F6CDDF2E40374 |
| SHA256: | 5706EA3291340810F140872D056A3A117F8A8F178E7C8C348B2763C8D6A6ED99 |
| SSDEEP: | 196608:TVMXGas94/R6MIZpxJvkZNbSQLRI1J1Q4uFOnPNbsND5M/yiVSS2YtrkmWsk9L19:TV089GHILfvmsQ1CiYw5UVPW7ZEgd |
MALICIOUS
Application was dropped or rewritten from another process
- viterocontroller.exe (PID: 1196)
- vitero.exe (PID: 2176)
Loads dropped or rewritten executable
- vitero.exe (PID: 2176)
Changes settings of System certificates
- vitero.exe (PID: 2176)
SUSPICIOUS
Adds / modifies Windows certificates
- vitero.exe (PID: 2176)
Executable content was dropped or overwritten
- vitero.exe (PID: 2176)
- viona.exe (PID: 3740)
Creates files in the user directory
- vitero.exe (PID: 2176)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:13 10:37:17+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 13045760 |
| InitializedDataSize: | 299008 |
| UninitializedDataSize: | 11722752 |
| EntryPoint: | 0x179ecb0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Dec-2017 09:37:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Dec-2017 09:37:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00B2E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00B2F000 | 0x00C71000 | 0x00C70A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99999 |
.rsrc | 0x017A0000 | 0x00049000 | 0x00048200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.60203 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.69651 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.21695 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.91502 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.61717 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.70013 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.98959 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.77968 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.58104 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
A | 2.819 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
USER32.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1196 | "C:\Users\admin\AppData\Local\Temp\viterocontroller.exe" "C:\Users\admin\AppData\Local\Temp\viona.exe" | C:\Users\admin\AppData\Local\Temp\viterocontroller.exe | — | viona.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\vitero.exe" | C:\Users\admin\AppData\Local\Temp\vitero.exe | viterocontroller.exe | ||||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: MEDIUM Description: Adobe Projector Exit code: 0 Version: 11.5r593 Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\Temp\viona.exe" | C:\Users\admin\AppData\Local\Temp\viona.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
505
Read events
459
Write events
45
Delete events
1
Modification events
| (PID) Process: | (1196) viterocontroller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\vitero.exe |
Value: HIGHDPIAWARE | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\Adobe\Shockwave 11\uicontrol\sw3dbaddriverlist1 |
| Operation: | write | Name: | |
Value: *2k*savage/ix!^5.12.01.7012$79x=stbnvidiatnt16mb!=4.10.01.9131$o2k=diamondstealthiiis530!=5.12.01.8007-8.30.24$72k=m!=5.00.2180.3711$***=atigraphicsproturbopci(atim64-gx)!^9999.0.0.0$ont=nvidiageforce256!=4.00.1381.0327$****virge!^9999.0.0.0$*9x=ibmthinkpad(cyber9397dvd)!=4.10.01.2173$79x=mach64:ragepro!=4.11.2560$*2k=m!^5.12.01.1200$o9x=intel(r)82810graphicscontroller!=4.12.01.2656$o**=m!^5.12.01.1509$o2k=3dfxvoodooseries!=5.00.2195.0197$ont=3dfxvoodooseries!=4.00.1381.0229$o2k=diamondstealthiiis540!=5.12.01.8007-8.30.24$*9x*permedia2!^4.10.01.2359$****mystique!^9999.0.0.0$*9x*g400!^4.12.1.1710$***=2164w!^9999.0.0.0$*9x=mach64:ragepro!^4.10.1720$ont*3dblasterriva!^4.03.00.2100$ont*nvidia!^4.00.1381.0508$79x*nvidia!^4.12.01.0513$o9x*diamondviperv770!^4.11.01.0402$****g100!^9999.0.0.0$59x*nvidiariva128!=4.10.1713$ont*radeon!^4.3.3109$o2k*voodoobanshee!=5.00.2195.2b$o***permedia3!^4.12.01.2107$o***ragefury!^4.3.139$o***rage128glagp!=4.00$ont*voodoo4!=4.00.1381.0229$o2k*s3inc.savage/mx!^5.12.1.7026$ont*3dfxvoodoo3!^4.00.1381.0391$ont=voodoo55500pci!^4.00.1381.0229$*9x=mach64:ragepro!^4.11.2611$*9x=2064w!^4.10.1682$79x=diamondviperv330!=4.10.01.0014$ont*nvidiarivatnt2!^4.00.1381.0631$*9x*g450!^4.12.1.1709$o***g450!^4.12.01.1799$*9x*xpert@play!^4.10.2237$****trio!^9999.0.0.0$79x*voodooo3!^4.11.01.1204$o9x*voodoo3!^4.11.01.7160$*2k*voodooseries!^5.00.2195.0232$79x*voodoo3!^4.12.01.1225$72k*voodoo3!^5.00.2180.58$o2k=elsagloriasynergy!=5.00.2180.1$72k=elsagloriasynergy!=5.00.2180.1$79x=glintdelta+glintmx!^4.10.0106$79x*rageii!=4.10.2165$59x*rageii!=4.10.2165$*9x=3dlabsoxygengvx1!^4.12.01.2107-0828$59x*cyber9397dvd!^4.11.01.2177$79x=mach64lt!^4.11.2022$79x=mach64gt!^4.11.2474$o9x*atirage128glsdagp!^4.12.6269$o9x*nvidia!=4.12.01.0618$ont*nvidia!=4.00.1381.0618$o2k*nvidia!=5.12.01.0618$***=unknown!=unknown$o9x*nvidia!=4.12.01.0650$59x=mach64gt!^4.03.00.2030$59x=mach64gt!^4.03.00.2030$59x*810chipset!^4.11.01.2506$ | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\Adobe\Shockwave 11\uicontrol\sw3dbaddriverlist2 |
| Operation: | write | Name: | |
Value: *9x*g200!^4.11.01.2519$o9x*g200!=4.12.01.2730$o9x=glintr3.!^4.12.01.2107-0829R$omc=.display_rage128!1.0.1f14/opengl1.1.2$59x=magnum/xpert128/x99/xpert2000(english)!=4.12.6292$59x=magnum/xpert128/x99/xpert2000!=4.13.7078$52k=atiragemobility-pagp(english)!=5.00.2195.4045$52k*ragexl!=5.00.2180.1$****neomagic!^9$o9x*g400!^4.12.01.1799$ont*g400!^9999.0.0.0$o2k*g400!^9999.0.0.0$ont*nvidia!=4.00.1381.0650$ont*rage128gl!=4.3.40$*2k=s3inc.savage4!^5.12.01.8011$79x*trio3d/2x!^4.11.01.5001$72k*savage/ixdisplaydriver!=5.12.01.7028-7.31.06$ont*prosavagepm133!^4.1024.1010.0010$o2k*prosavagepm133!^5.12.01.1002$59x*3dimage9!=4.10.01.2161$79x*3dimage9!=4.10.01.2161$72k=diamondmultimediafiregl1000pro!=5.00.2180.1$72k*s3graphicsprosavage!^5.13.01.1010-11.80.20$ | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\Adobe\Shockwave 11\renderer3dsetting |
| Operation: | write | Name: | |
Value: 0 | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vitero.exe | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vitero.exe | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1237094986 | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vitero.exe | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vitero_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2176) vitero.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vitero_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
44
Suspicious files
8
Text files
139
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\vitero.exe | executable | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\vitero.bmp | image | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\windowelements.cct | cct | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\caloa_lib_loader.x32 | executable | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\audio.dcr | dcr | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\tooltip.dcr | dcr | |
MD5:649B07C525BB1D9F49593CC1202637CE | SHA256:79520B8A6BDAAE690BC8E3B5EFCB9D26B707268EAC7977F6E96954A5EA37357A | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\vitero.ini | text | |
MD5:F0A31B457BBED94429F671F6F85072DF | SHA256:7048B3F25C7B08D3995F1516F23C142396C57FBEEE917C197F6065E5E8FE54A7 | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\AvatarSmile.png | image | |
MD5:3DFE9A959A5C85333F1B9B4892F89C69 | SHA256:B3C4655B92EE18C9F8B535AFFF1E0AEEB595CEEABE56310059739429D0BCBC14 | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\dfc_adapter.swf | swf | |
MD5:— | SHA256:— | |||
| 3740 | viona.exe | C:\Users\admin\AppData\Local\Temp\AvatarNormal.png | image | |
MD5:3DFE9A959A5C85333F1B9B4892F89C69 | SHA256:B3C4655B92EE18C9F8B535AFFF1E0AEEB595CEEABE56310059739429D0BCBC14 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2176 | vitero.exe | 212.162.55.198:1935 | — | Level 3 Communications, Inc. | GB | unknown |
2176 | vitero.exe | 212.162.55.193:443 | class-staging.viona24.com | Level 3 Communications, Inc. | GB | unknown |
2176 | vitero.exe | 212.162.55.196:16501 | — | Level 3 Communications, Inc. | GB | unknown |
2176 | vitero.exe | 212.162.55.202:1935 | — | Level 3 Communications, Inc. | GB | unknown |
2176 | vitero.exe | 212.162.55.194:16501 | — | Level 3 Communications, Inc. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
class-staging.viona24.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2176 | vitero.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2176 | vitero.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |