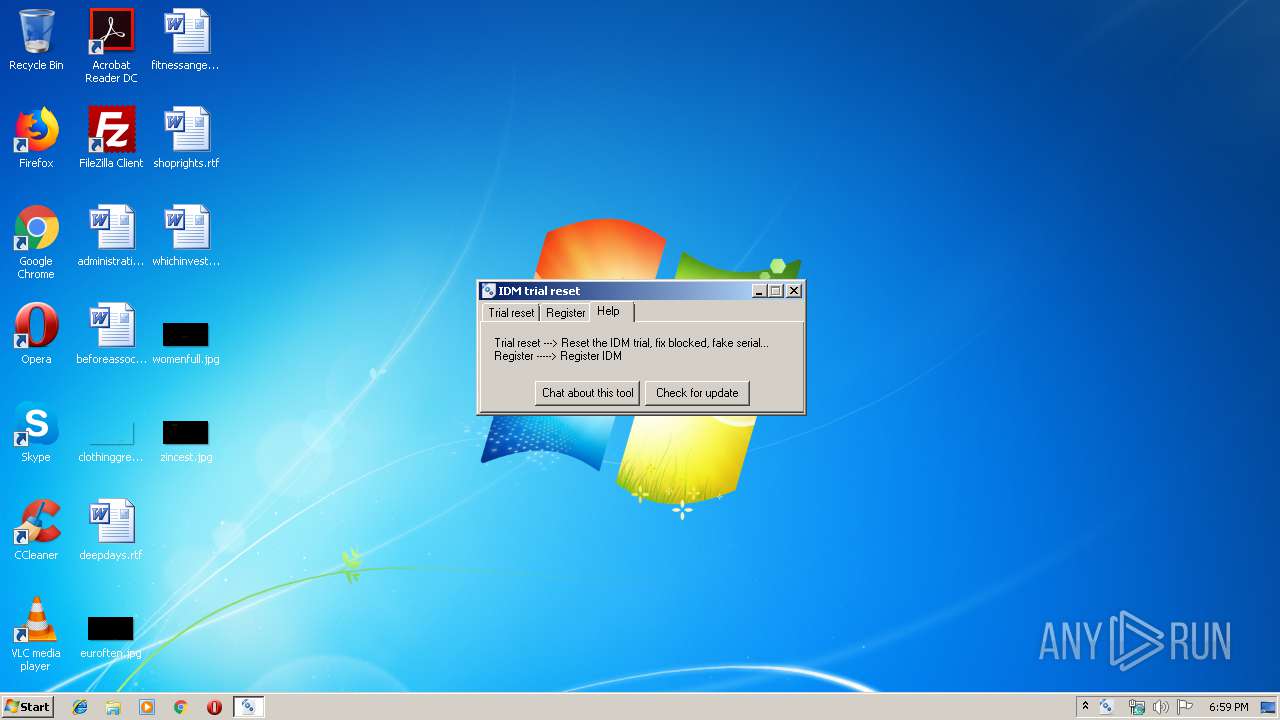
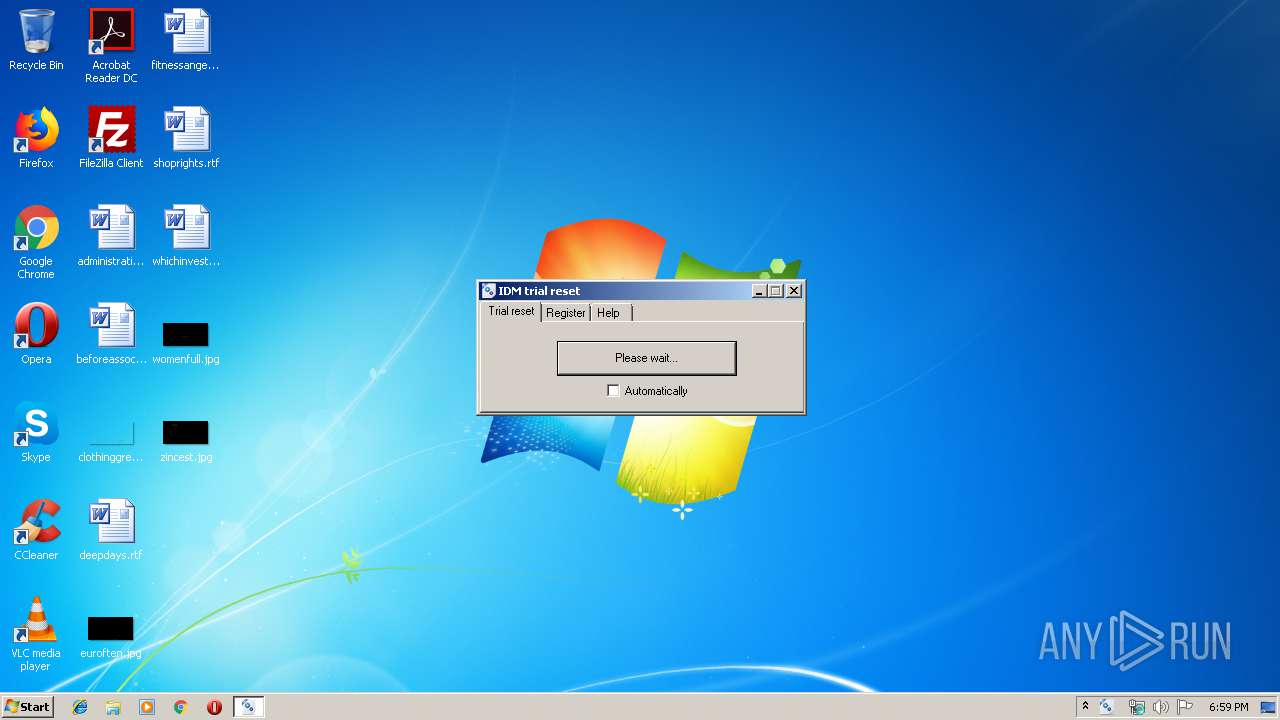
| File name: | idm_trial_reset.exe |
| Full analysis: | https://app.any.run/tasks/50ee28f3-2f7f-46d8-9bfb-8305f82c415f |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 18:59:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 072760D80286205652AF3041D68D7033 |
| SHA1: | 94EB839FD537DBFB93CB51C53B2EB15F70480EDC |
| SHA256: | 56FF6937AC04352EEB83B3AE75B9A1D2EFB3177F7B460C148864A3236B22EFB2 |
| SSDEEP: | 24576:7q5TfcdHj4fmbrPevqKoyWdMIZJ0HyFaoVuy8jadVhZIV7Um5ibp:7UTsamnmvqKoyWdMIZJ0hm38juS |
MALICIOUS
Application was dropped or rewritten from another process
- SetACLx32.exe (PID: 3928)
- SetACLx32.exe (PID: 2336)
- SetACLx32.exe (PID: 2256)
- SetACLx32.exe (PID: 2772)
- SetACLx32.exe (PID: 3628)
- SetACLx32.exe (PID: 3460)
- SetACLx32.exe (PID: 2068)
- SetACLx32.exe (PID: 4036)
- SetACLx32.exe (PID: 920)
- SetACLx32.exe (PID: 2924)
- SetACLx32.exe (PID: 820)
- SetACLx32.exe (PID: 2516)
- SetACLx32.exe (PID: 2564)
- SetACLx32.exe (PID: 892)
- SetACLx32.exe (PID: 3196)
- SetACLx32.exe (PID: 2668)
- SetACLx32.exe (PID: 1928)
- SetACLx32.exe (PID: 1704)
- SetACLx32.exe (PID: 3400)
- SetACLx32.exe (PID: 2528)
- SetACLx32.exe (PID: 532)
- SetACLx32.exe (PID: 1880)
- SetACLx32.exe (PID: 3140)
- SetACLx32.exe (PID: 2788)
- SetACLx32.exe (PID: 3916)
- SetACLx32.exe (PID: 2172)
- SetACLx32.exe (PID: 2336)
- SetACLx32.exe (PID: 2200)
- SetACLx32.exe (PID: 3804)
- SetACLx32.exe (PID: 2620)
- SetACLx32.exe (PID: 2532)
- SetACLx32.exe (PID: 3408)
- SetACLx32.exe (PID: 2372)
- SetACLx32.exe (PID: 1916)
- SetACLx32.exe (PID: 1908)
- SetACLx32.exe (PID: 1216)
- SetACLx32.exe (PID: 2112)
- SetACLx32.exe (PID: 1484)
- SetACLx32.exe (PID: 3932)
- SetACLx32.exe (PID: 584)
- SetACLx32.exe (PID: 2280)
- SetACLx32.exe (PID: 3180)
- SetACLx32.exe (PID: 1764)
- SetACLx32.exe (PID: 1728)
- SetACLx32.exe (PID: 616)
- SetACLx32.exe (PID: 1992)
- SetACLx32.exe (PID: 4040)
- SetACLx32.exe (PID: 1732)
- SetACLx32.exe (PID: 2752)
- SetACLx32.exe (PID: 2840)
- SetACLx32.exe (PID: 592)
- SetACLx32.exe (PID: 3768)
- SetACLx32.exe (PID: 2240)
- SetACLx32.exe (PID: 2740)
- SetACLx32.exe (PID: 3940)
- SetACLx32.exe (PID: 2800)
- SetACLx32.exe (PID: 4000)
- SetACLx32.exe (PID: 3908)
- SetACLx32.exe (PID: 3632)
- SetACLx32.exe (PID: 3832)
- SetACLx32.exe (PID: 4068)
- SetACLx32.exe (PID: 1044)
- SetACLx32.exe (PID: 2552)
- SetACLx32.exe (PID: 1524)
- SetACLx32.exe (PID: 932)
- SetACLx32.exe (PID: 952)
- SetACLx32.exe (PID: 1724)
- SetACLx32.exe (PID: 3940)
- SetACLx32.exe (PID: 2196)
- SetACLx32.exe (PID: 2128)
- SetACLx32.exe (PID: 2236)
- SetACLx32.exe (PID: 1524)
- SetACLx32.exe (PID: 3632)
- SetACLx32.exe (PID: 2148)
- SetACLx32.exe (PID: 3836)
- SetACLx32.exe (PID: 3960)
- SetACLx32.exe (PID: 1152)
- SetACLx32.exe (PID: 3868)
- SetACLx32.exe (PID: 2732)
- SetACLx32.exe (PID: 1816)
SUSPICIOUS
Starts CMD.EXE for commands execution
- idm_trial_reset.exe (PID: 3944)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2824)
- idm_trial_reset.exe (PID: 3944)
Executable content was dropped or overwritten
- idm_trial_reset.exe (PID: 3944)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:04:11 17:52:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 348160 |
| InitializedDataSize: | 835584 |
| UninitializedDataSize: | 1368064 |
| EntryPoint: | 0x1a30d0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Apr-2015 15:52:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 11-Apr-2015 15:52:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0014E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0014F000 | 0x00055000 | 0x00054400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93642 |
.rsrc | 0x001A4000 | 0x000CC000 | 0x000CB600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.70824 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37445 | 955 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 5.45321 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 5.36111 | 2216 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 4.73803 | 1736 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 7.87876 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 7.87365 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 7.84709 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 7.87763 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
212
Monitored processes
91
Malicious processes
1
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKLM\Software\Classes\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC} -ot reg -actn ace -ace "n:everyone;p:full" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 584 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKCU\Software\Classes\Wow6432Node\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn ace -ace "n:everyone;p:read" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 592 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKCU\Software\Classes\Wow6432Node\CLSID\{07999AC3-058B-40BF-984F-69EB1E554CA7} -ot reg -actn ace -ace "n:everyone;p:read" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 616 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKCU\Software\Classes\CLSID\{6DDF00DB-1234-46EC-8356-27E7B2051192} -ot reg -actn ace -ace "n:everyone;p:read" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKCU\Software\Classes\CLSID\{07999AC3-058B-40BF-984F-69EB1E554CA7} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 892 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKLM\Software\Classes\Wow6432Node\CLSID\{07999AC3-058B-40BF-984F-69EB1E554CA7} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKCU\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 932 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKLM\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Temp\SetACLx32.exe" -on HKLM\Software\Classes\Wow6432Node\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
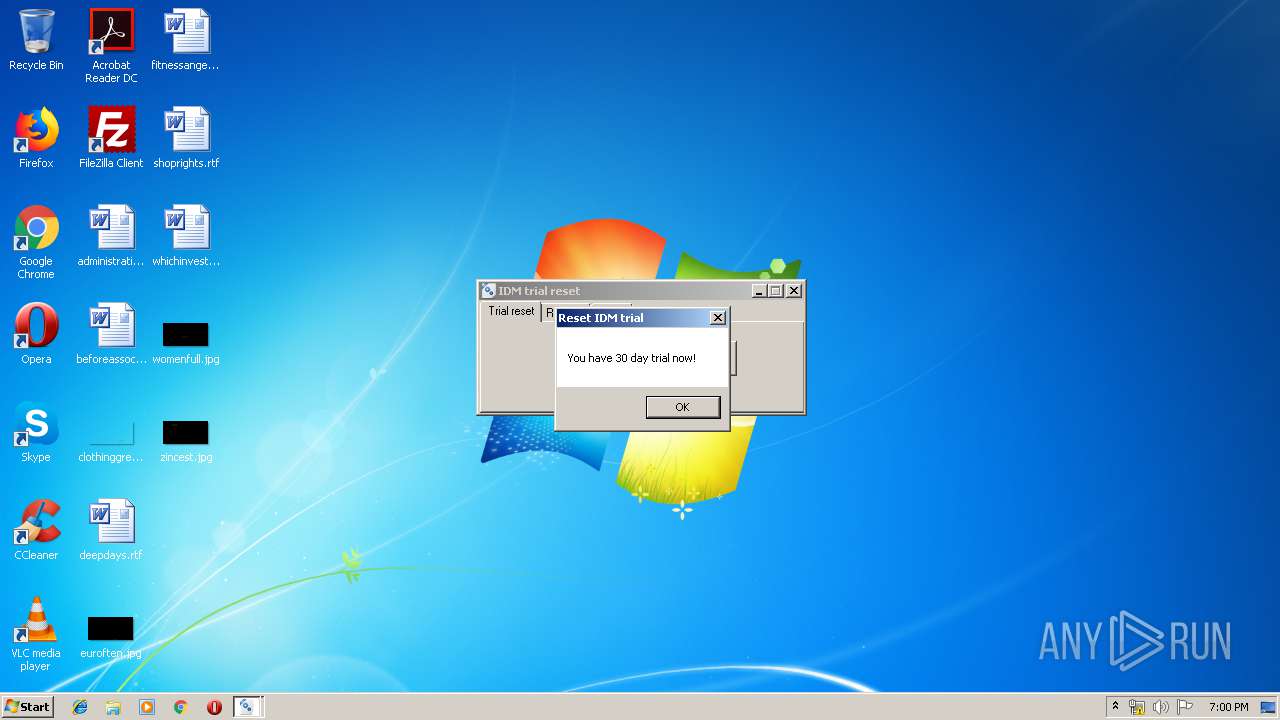
| 992 | reg import "C:\Users\admin\AppData\Local\Temp\idm_trial.reg" | C:\Windows\system32\reg.exe | — | idm_trial_reset.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 859
Read events
18 853
Write events
6
Delete events
0
Modification events
| (PID) Process: | (992) reg.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | Serial |
Value: | |||
| (PID) Process: | (992) reg.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C} |
| Operation: | write | Name: | scansk |
Value: 911DACD6905C42EABA1AAC081A182F162AA80AAA24BF0CFC4E7B3B76F77093585C03037E04ABB07E00000000000000000000 | |||
| (PID) Process: | (992) reg.exe | Key: | HKEY_CLASSES_ROOT\Wow6432Node\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C} |
| Operation: | write | Name: | scansk |
Value: 911DACD6905C42EABA1AAC081A182F162AA80AAA24BF0CFC4E7B3B76F77093585C03037E04ABB07E00000000000000000000 | |||
| (PID) Process: | (992) reg.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | scansk |
Value: 911DACD6905C42EABA1AAC081A182F162AA80AAA24BF0CFC4E7B3B76F77093585C03037E04ABB07E00000000000000000000 | |||
| (PID) Process: | (992) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C} |
| Operation: | write | Name: | scansk |
Value: 911DACD6905C42EABA1AAC081A182F162AA80AAA24BF0CFC4E7B3B76F77093585C03037E04ABB07E00000000000000000000 | |||
| (PID) Process: | (992) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Wow6432Node\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C} |
| Operation: | write | Name: | scansk |
Value: 911DACD6905C42EABA1AAC081A182F162AA80AAA24BF0CFC4E7B3B76F77093585C03037E04ABB07E00000000000000000000 | |||
Executable files
2
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\autAB6D.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\autAB6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\autAB6F.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\autAB70.tmp | — | |
MD5:— | SHA256:— | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\autAB90.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | cmd.exe | C:\Users\admin\AppData\Local\Temp\reg_query.tmp | text | |
MD5:— | SHA256:— | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\idm_reset.reg | text | |
MD5:17EBF21FCCAC9756EAB46EB64BA6C029 | SHA256:290A3F67BBBDBD5C1101E90921475C2B95E97DC69A3141412FBAC79FCADD3EE8 | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\idm_reg.reg | text | |
MD5:3DEDFE7770A57CA2BCB76D01D1756EE6 | SHA256:832134EB65B2A91BE5B6584B48AB69B4B7CE9B6228EA4738F6D1B7A8A0E1915E | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\idm_trial.reg | text | |
MD5:237962E36948F3D0C9EC42EFA289AC52 | SHA256:40AD93CF424EEE41A0877B11ACB92F7F12D58AB3AA6FA6D64D92CFBBE11695A2 | |||
| 3944 | idm_trial_reset.exe | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | executable | |
MD5:3E350EB5DF15C06DEC400A39DD1C6F29 | SHA256:427FF43693CB3CA2812C4754F607F107A6B2D3F5A8B313ADDEE57D89982DF419 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report