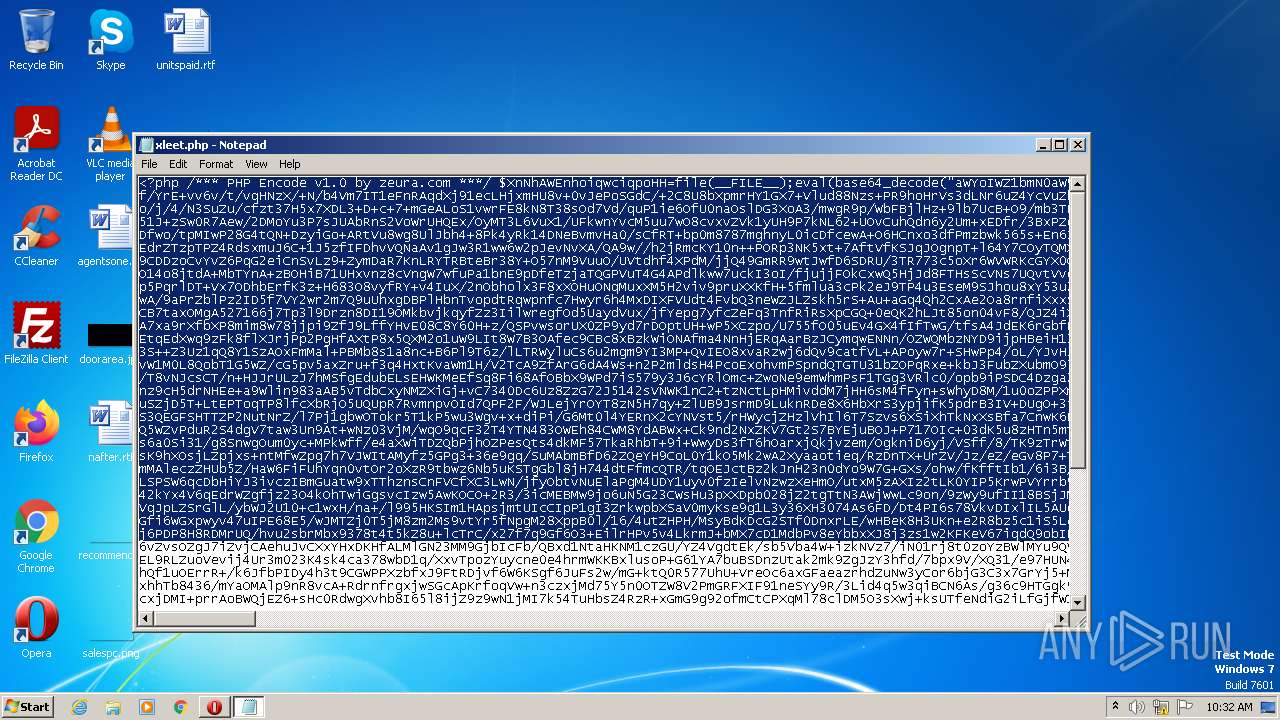
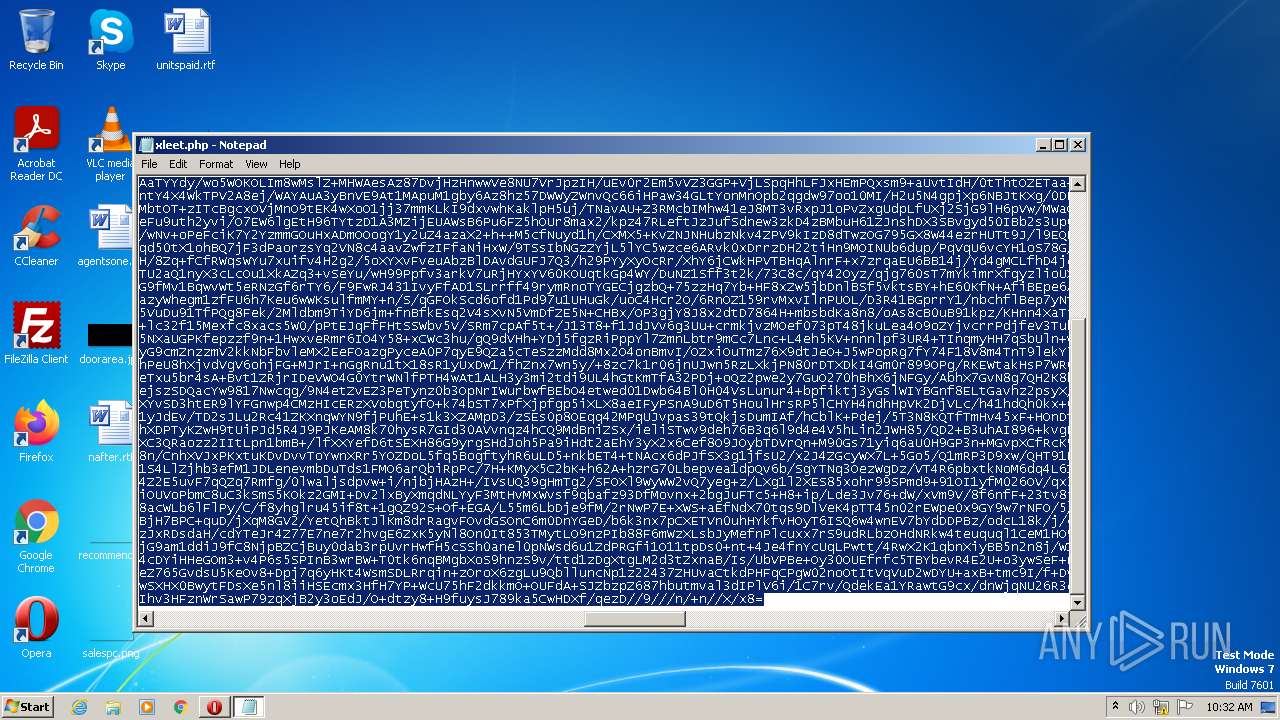
| File name: | xleet.php |
| Full analysis: | https://app.any.run/tasks/2295bac9-5cbe-4060-b520-c99ebb3d1e98 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 09:31:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
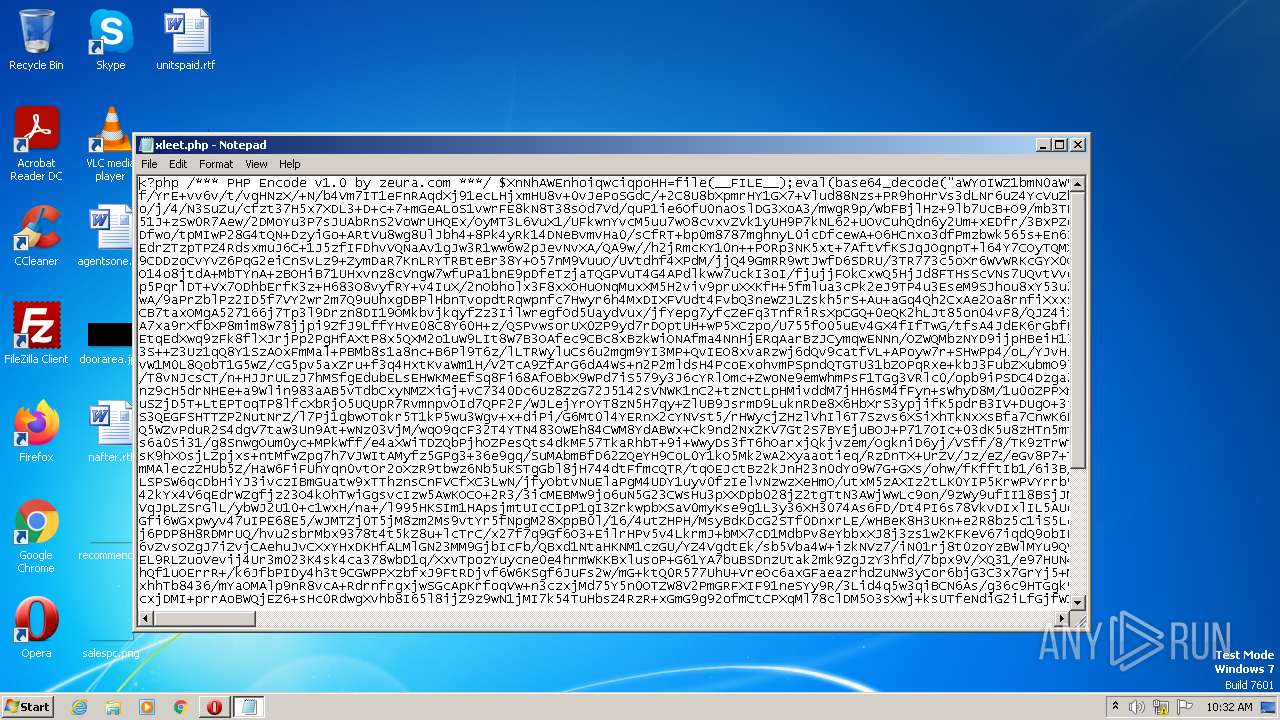
| MIME: | text/x-php |
| File info: | PHP script, ASCII text, with very long lines, with no line terminators |
| MD5: | 7740B928DEED28272391A3ECFA93DC8A |
| SHA1: | 1692688AEA50D20CF65A16D6F0FC13B11A88BACD |
| SHA256: | 56FE2502F2ED1C9C803300CDAA25377C4A151201C0BA07926382E84B76CABEDE |
| SSDEEP: | 768:46Y+DdgStiKL8lO5ZH/12eGaJ44WXL9F8b6YAp5m7DKwh460NTjGteI8dhhrzYQD:zZ3tYo5R/gO44WXxwem7GO4hNkexhSy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 2368)
INFO
The process checks LSA protection
- rundll32.exe (PID: 2368)
Manual execution by a user
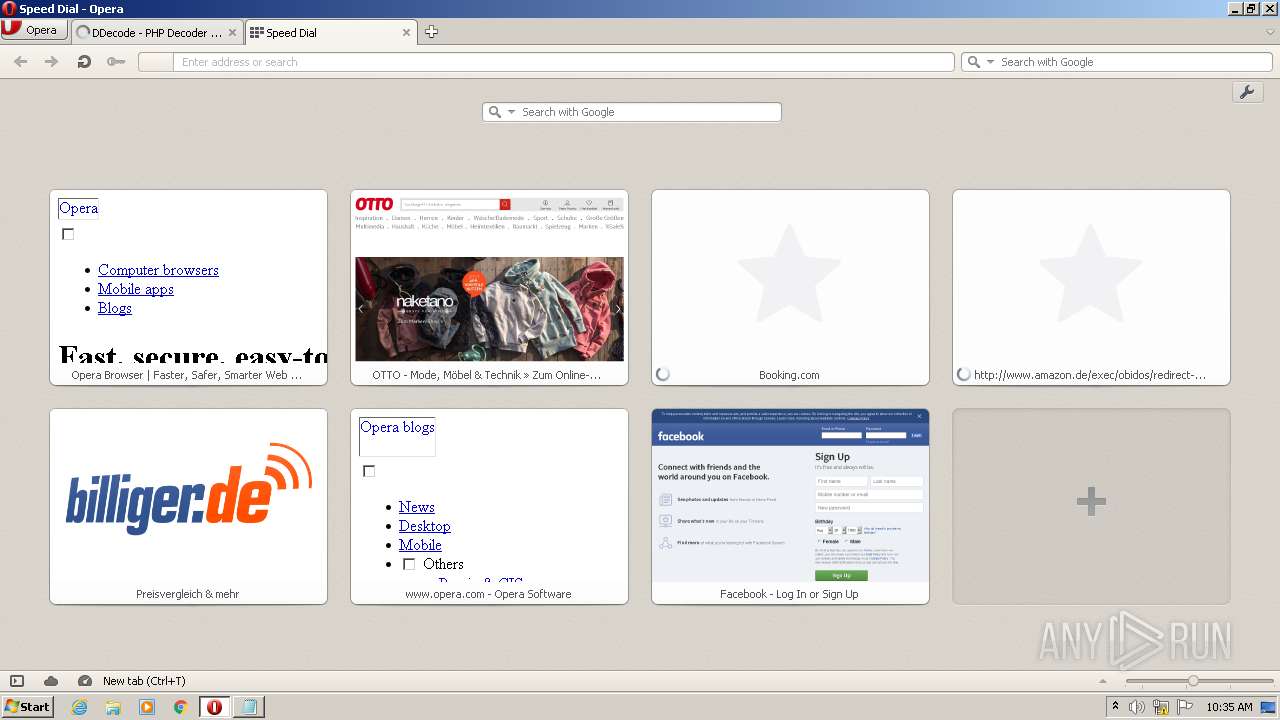
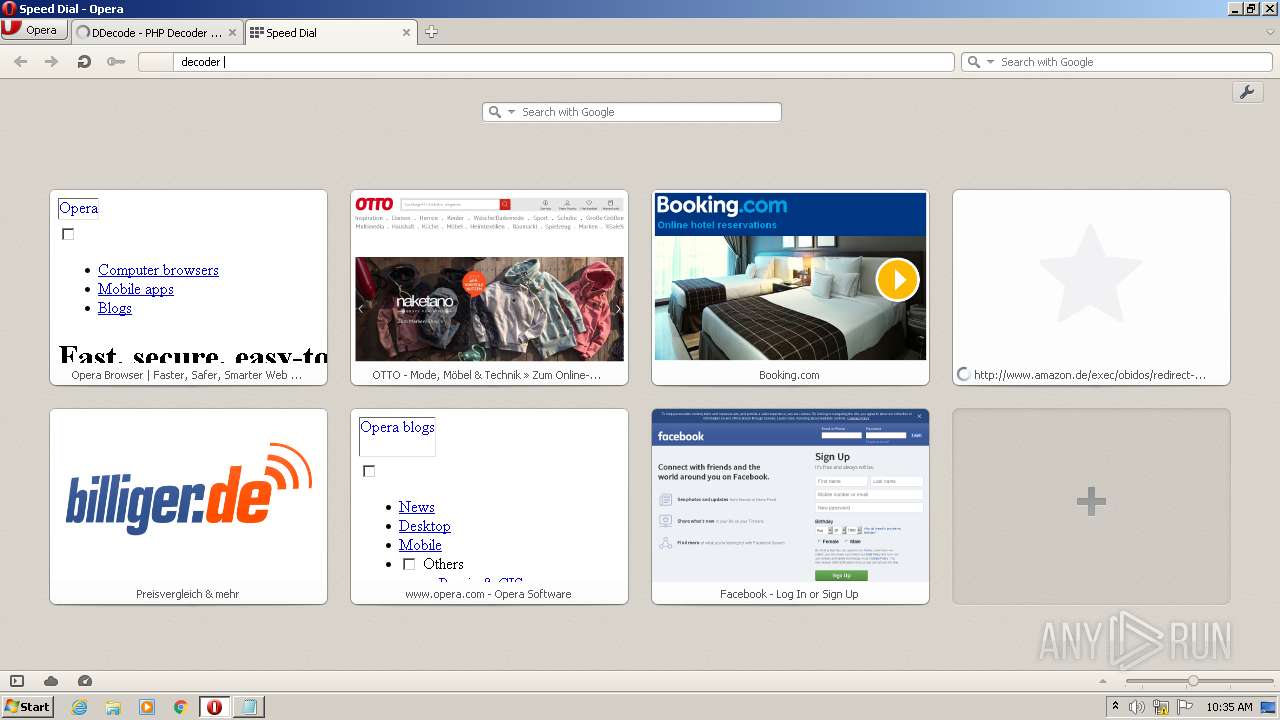
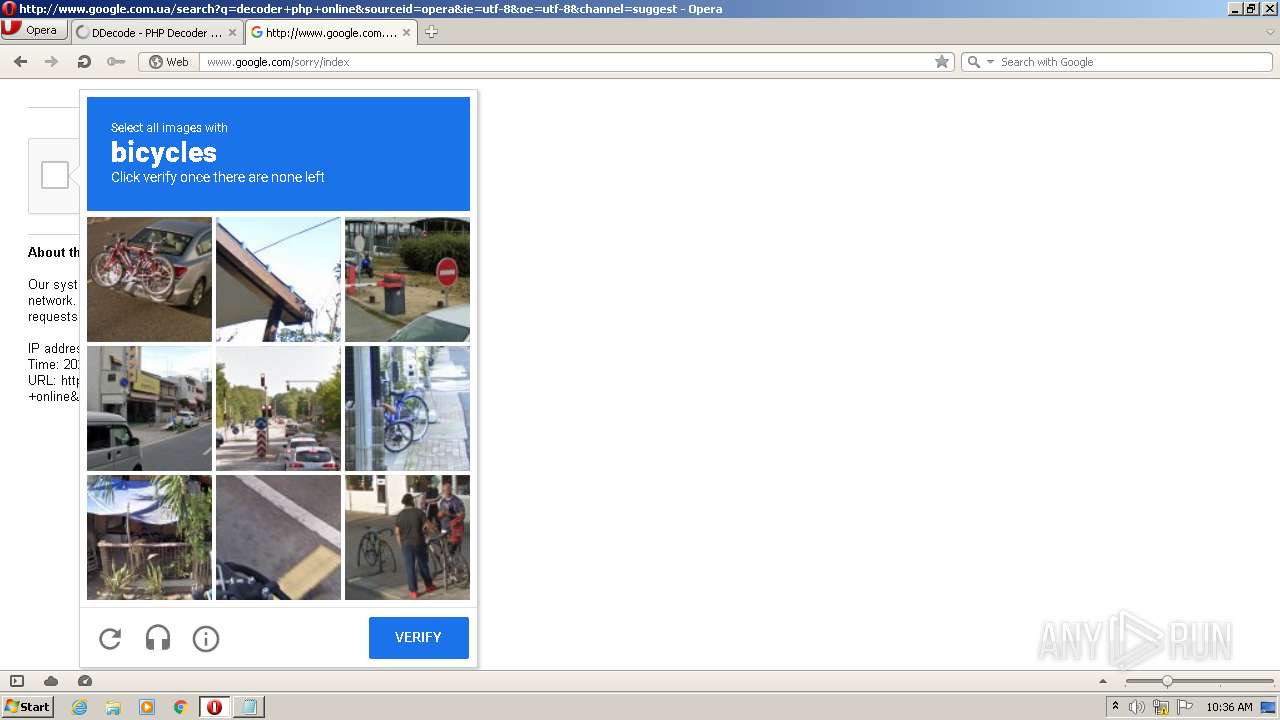
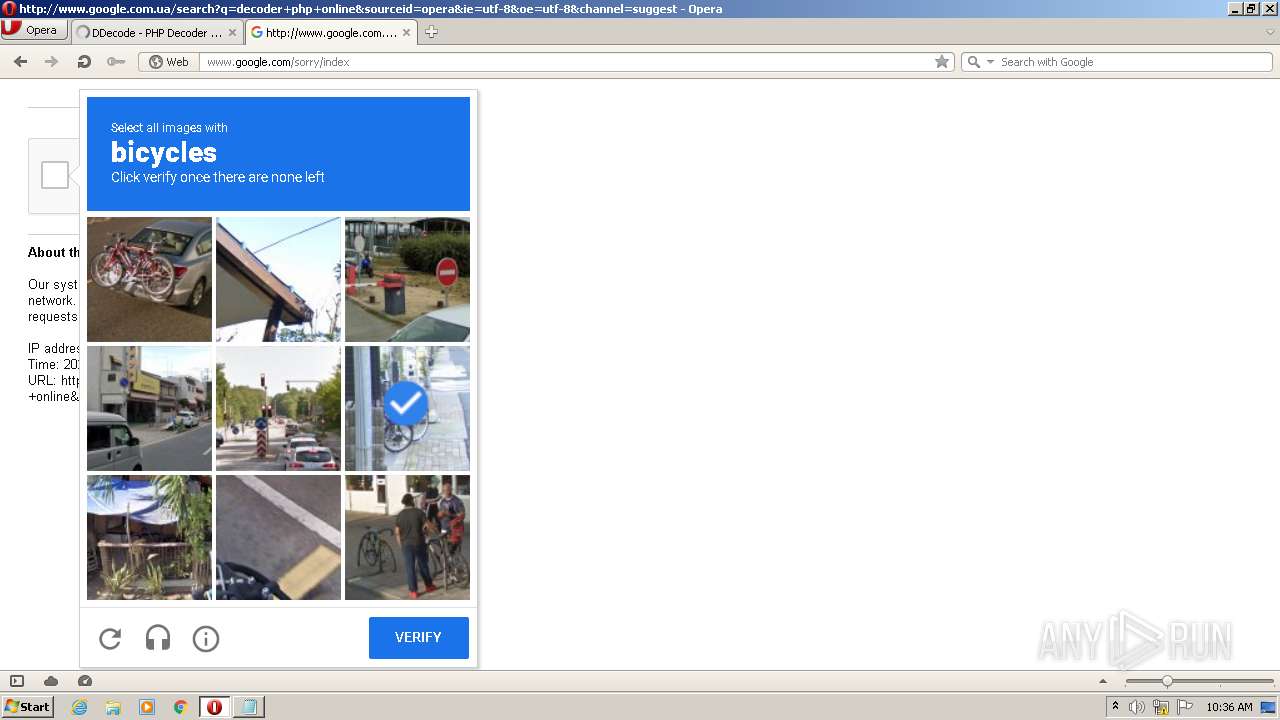
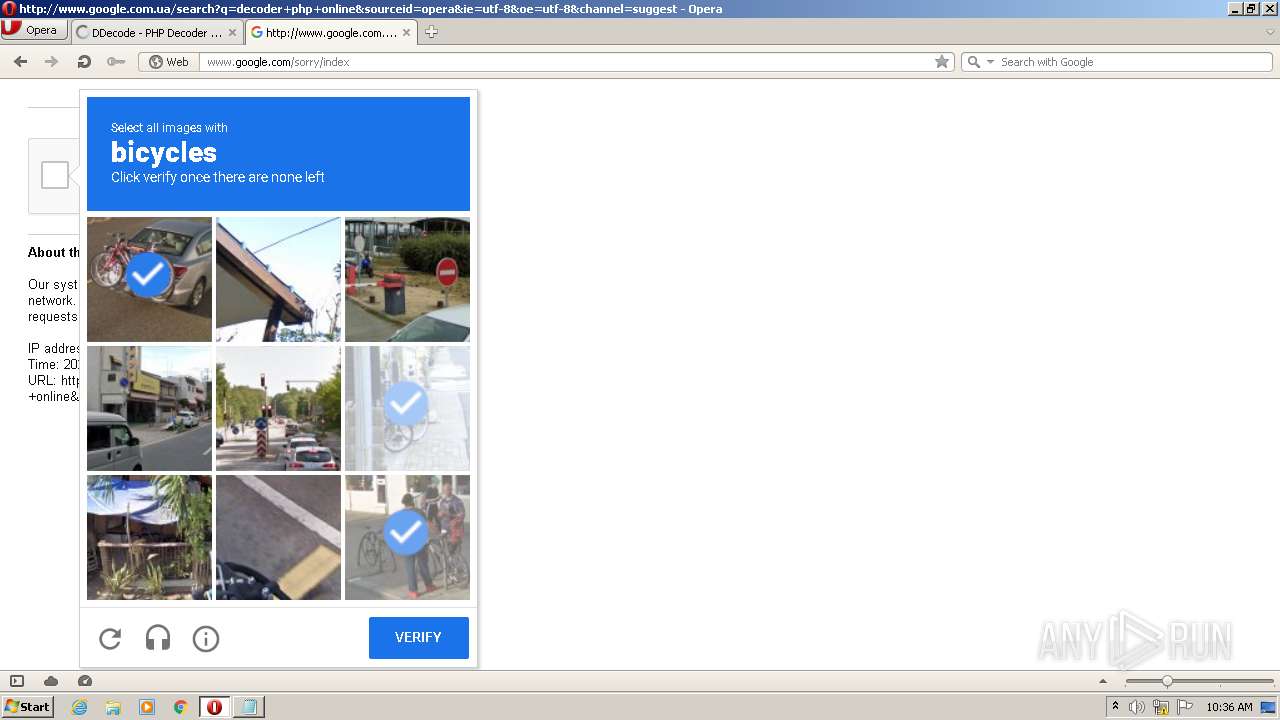
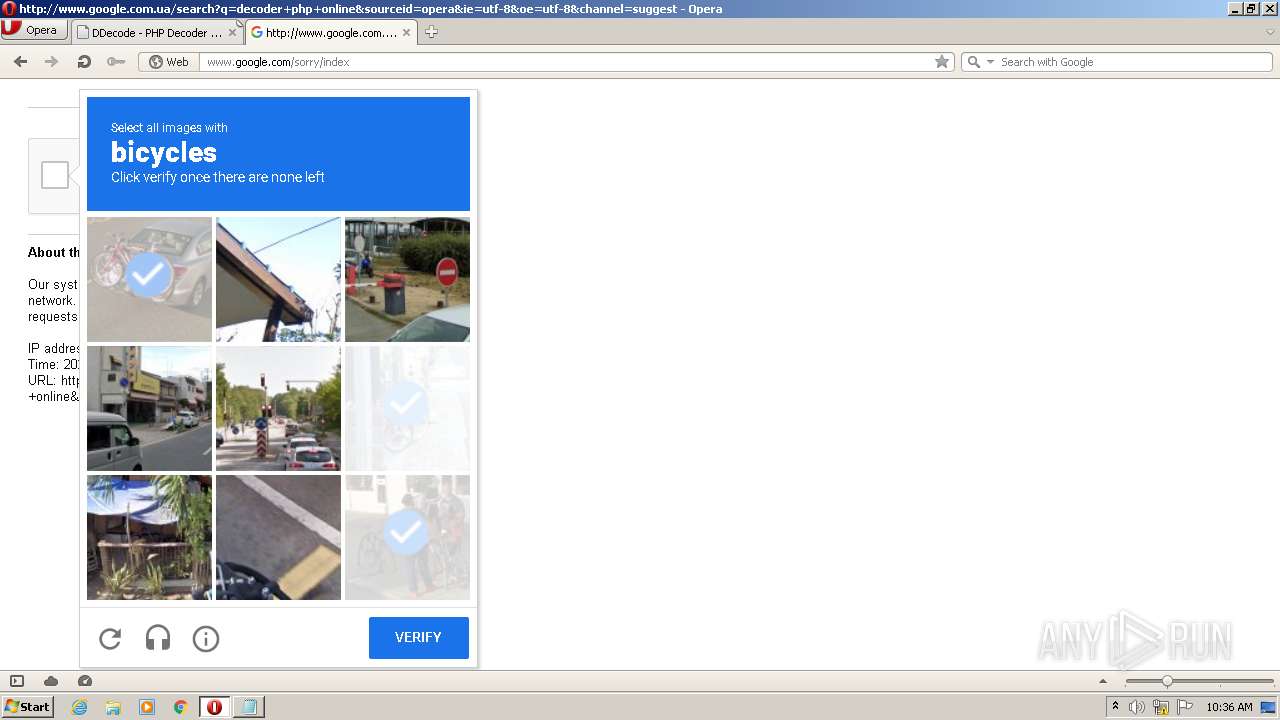
- opera.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .php | | | PHP source (100) |
|---|
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
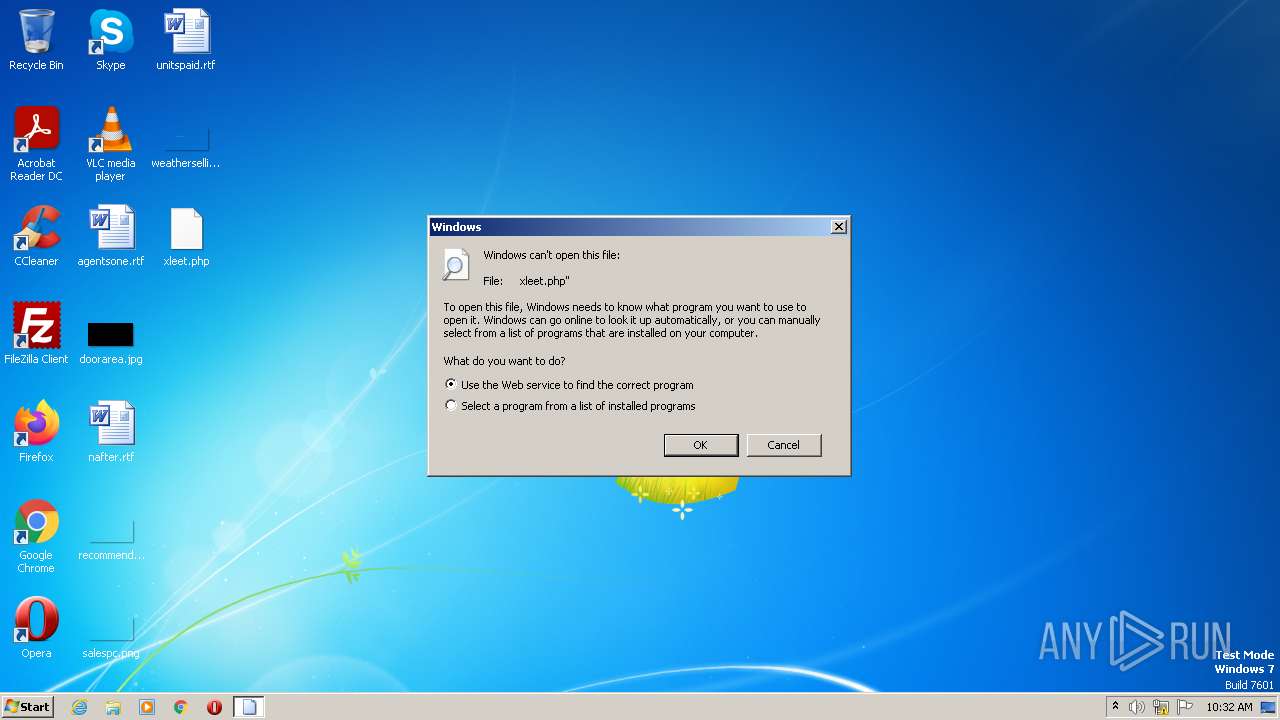
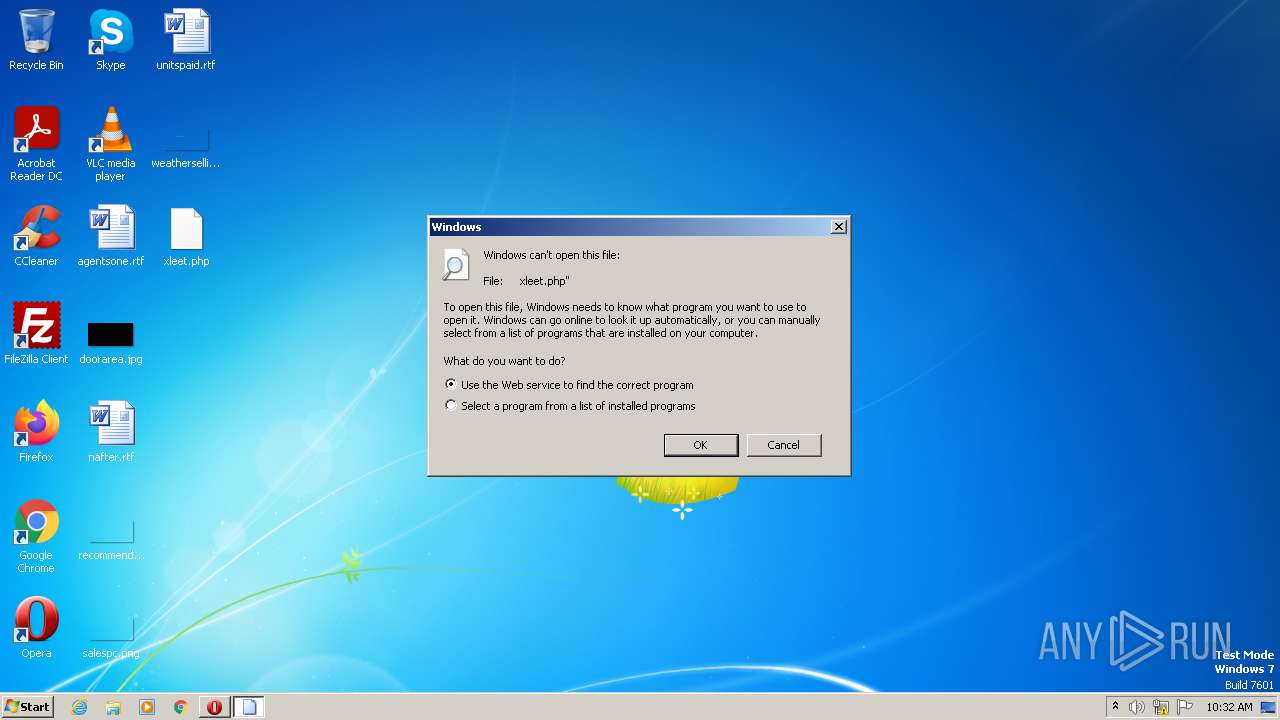
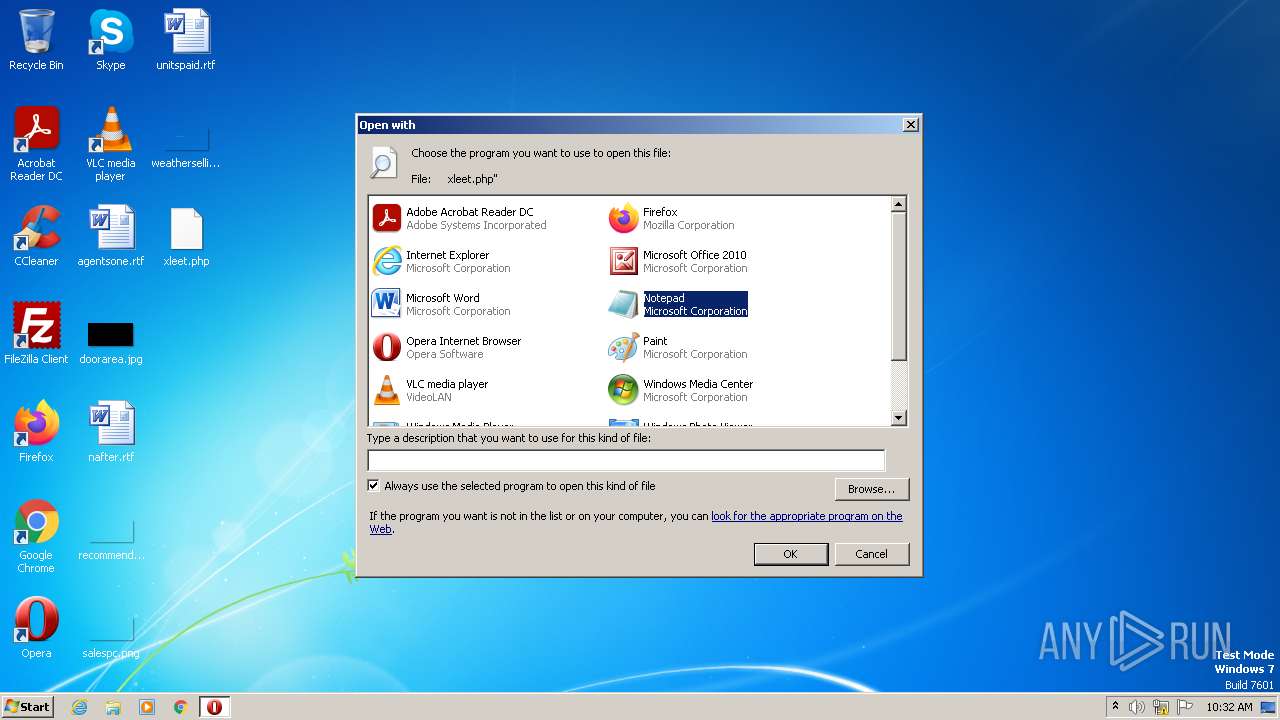
| 2368 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\xleet.php" | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\xleet.php | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
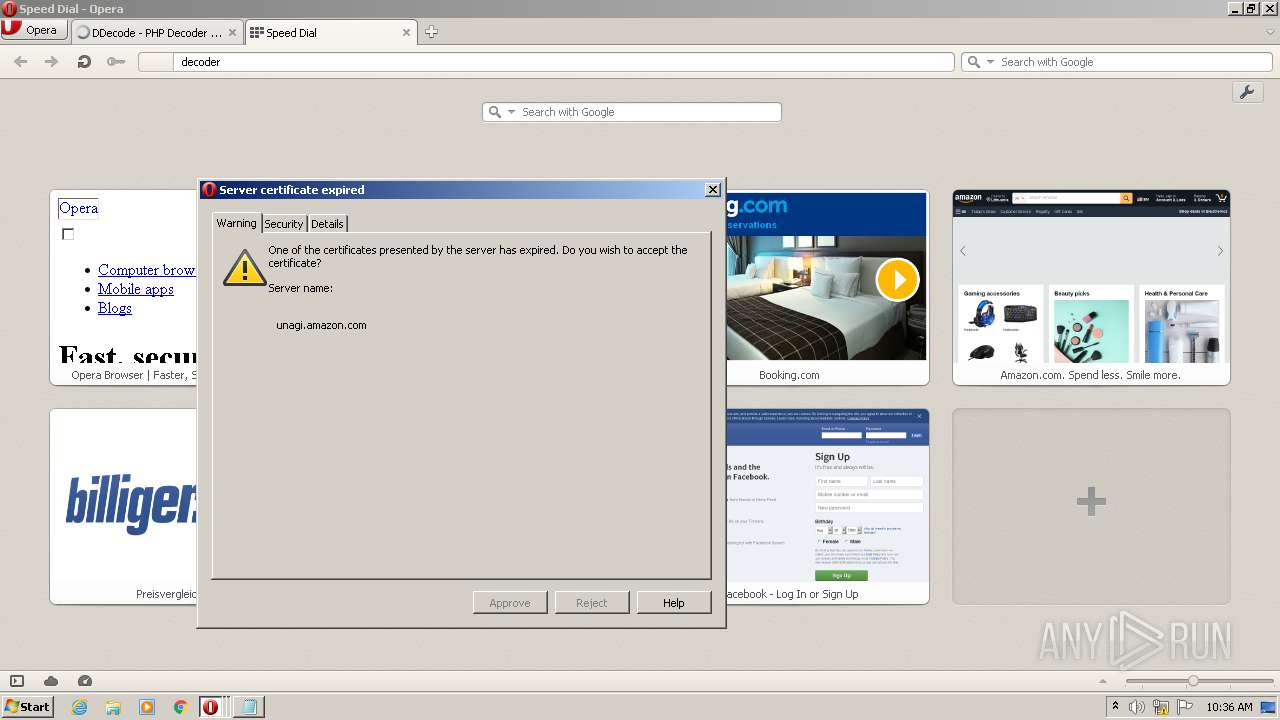
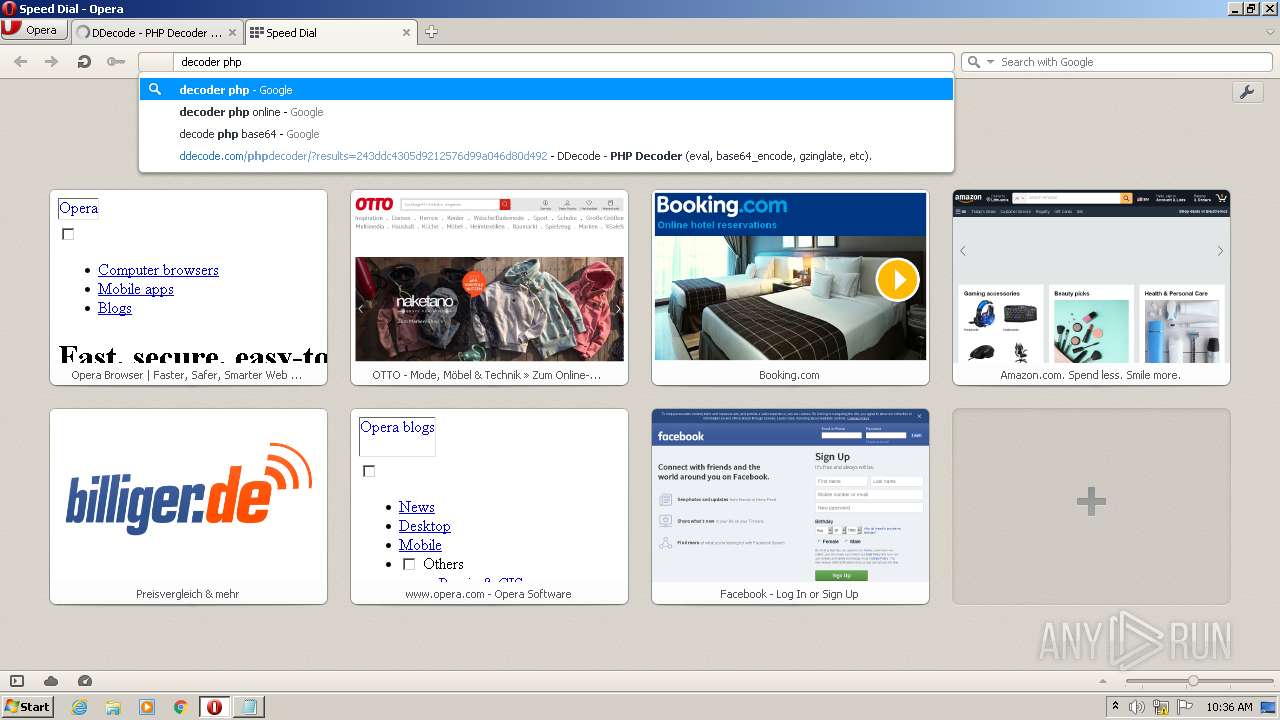
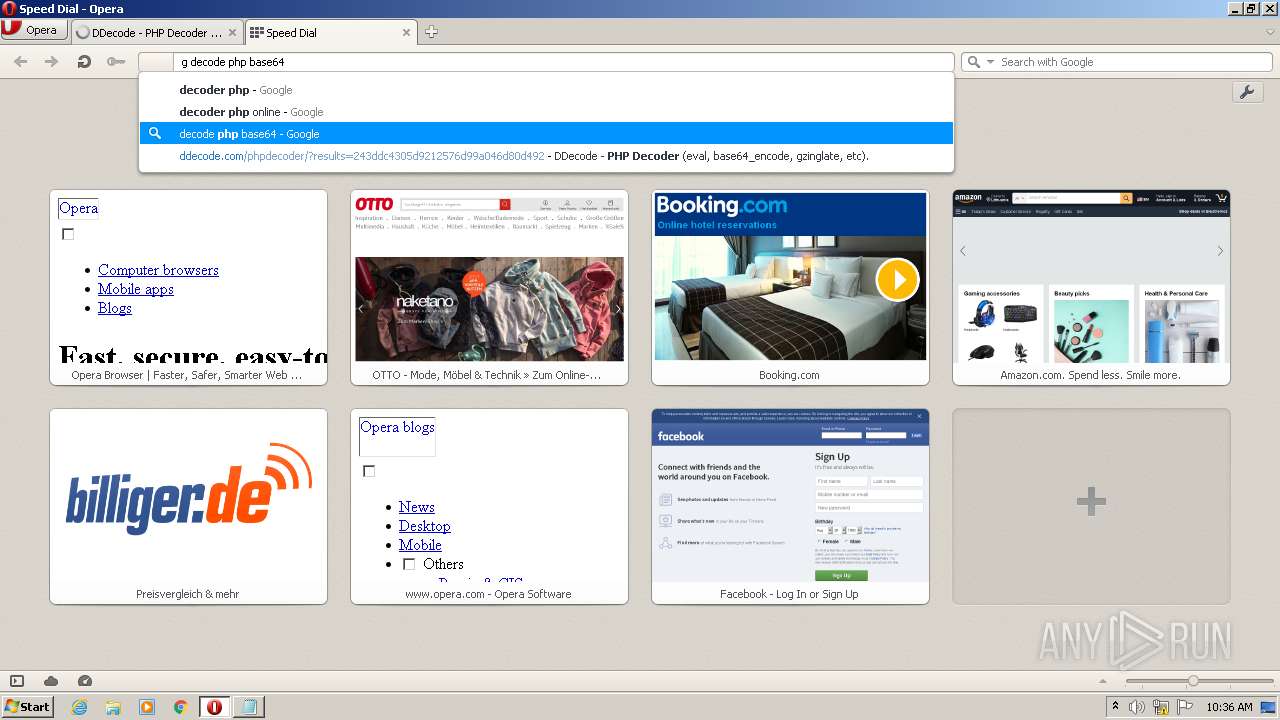
| 3104 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
1 766
Read events
1 650
Write events
116
Delete events
0
Modification events
| (PID) Process: | (3104) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3104) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2368) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
84
Text files
754
Unknown types
66
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3276.tmp | text | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr5A43.tmp | text | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr32B5.tmp | xml | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\assoc002\sesn\opr00003.000 | ttf | |
MD5:— | SHA256:— | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4GCTLMU56XD1HI5D2J2G.temp | binary | |
MD5:FDBCDB294DED05EA01DCAA246B98C2C5 | SHA256:EAEC5A291DBC8E8760BAB0C1BB27CB801F671166CE85310FD173F54111357C4B | |||
| 3104 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:FDBCDB294DED05EA01DCAA246B98C2C5 | SHA256:EAEC5A291DBC8E8760BAB0C1BB27CB801F671166CE85310FD173F54111357C4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
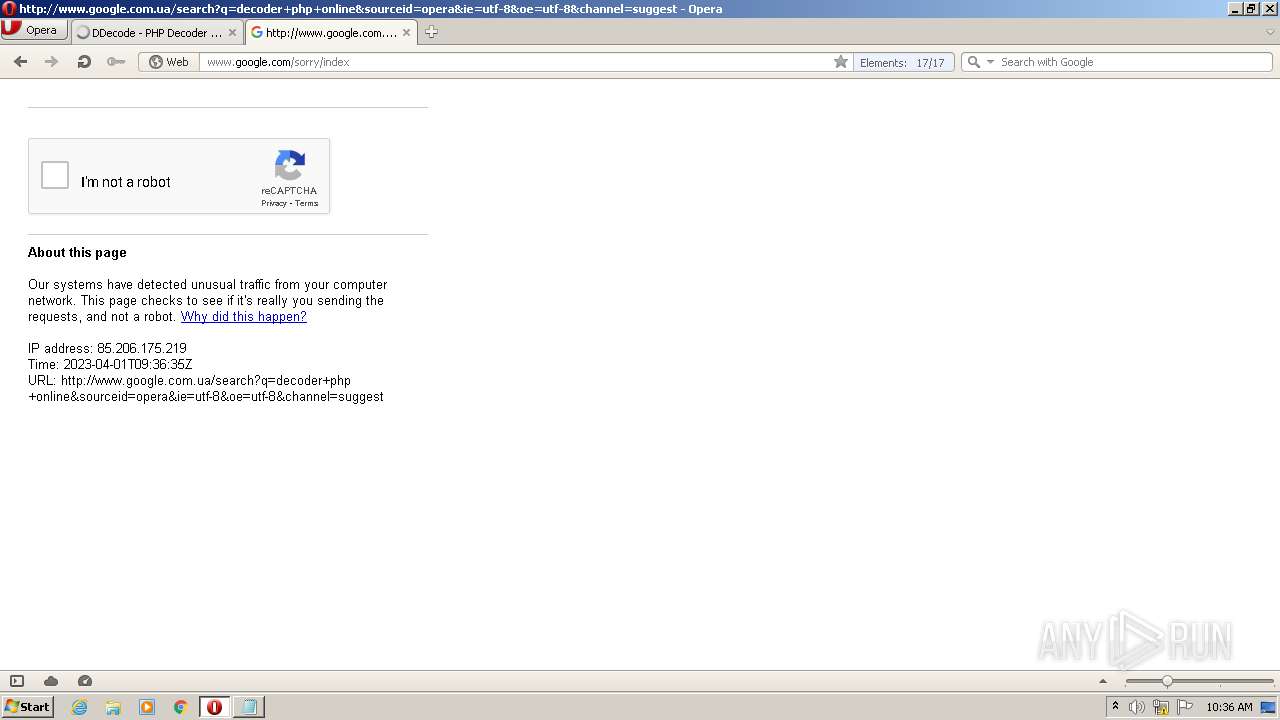
289
DNS requests
75
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | opera.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCg1AAPrImNIAq7YSXkGtvN | US | der | 472 b | whitelisted |
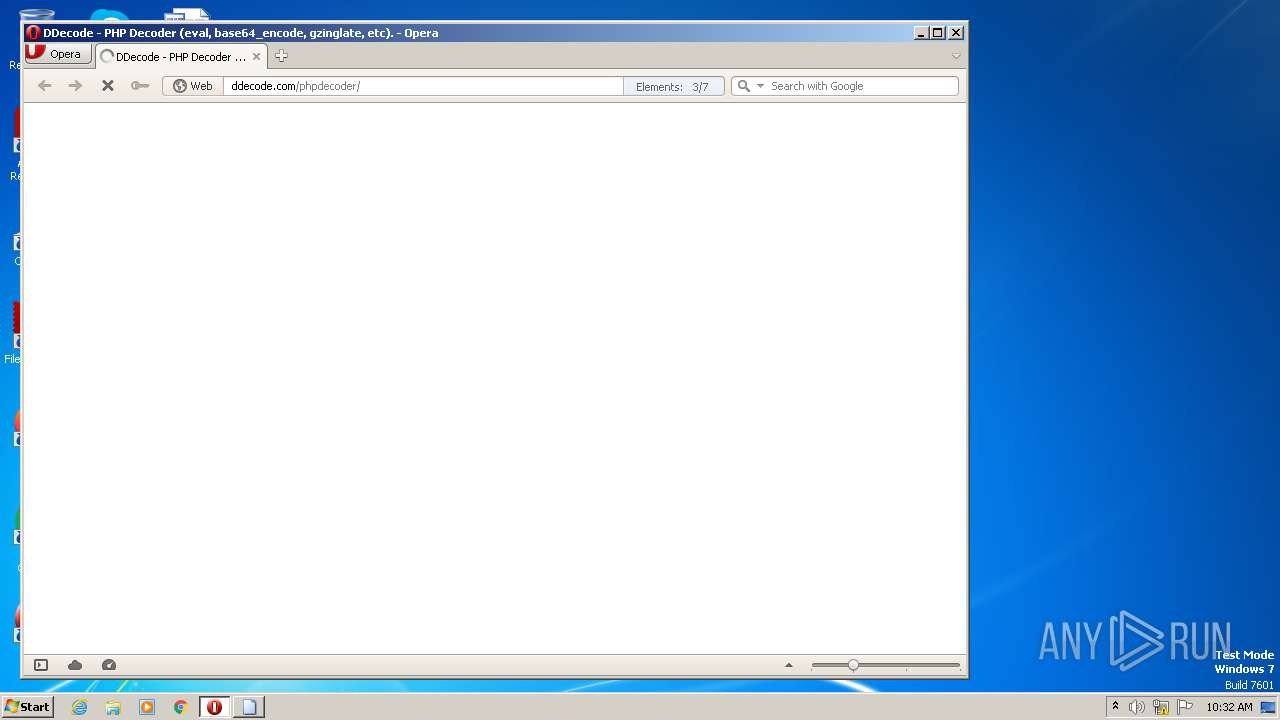
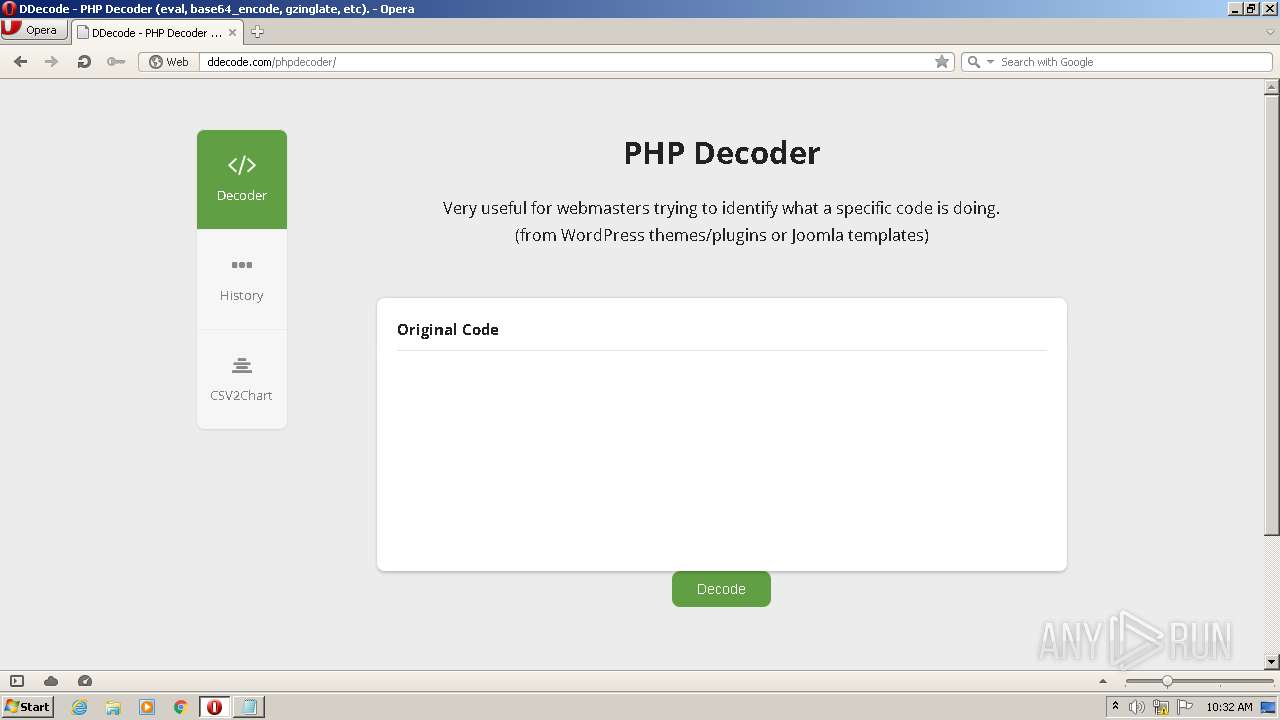
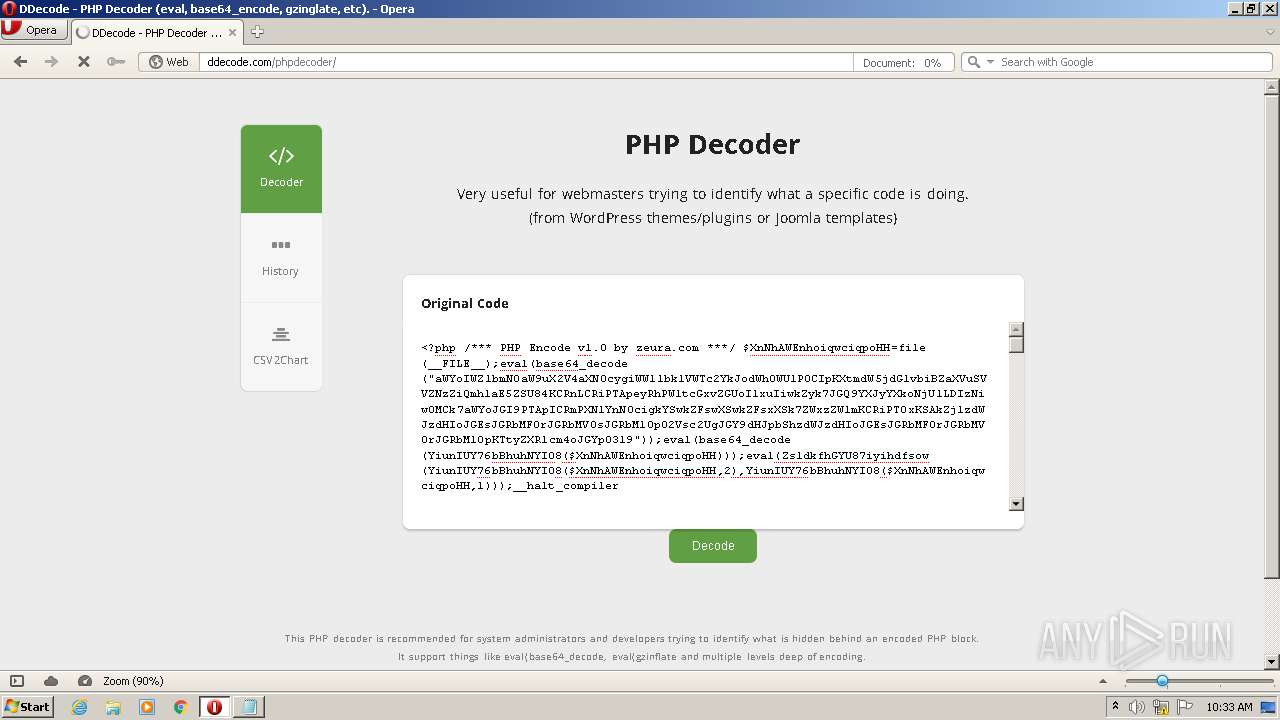
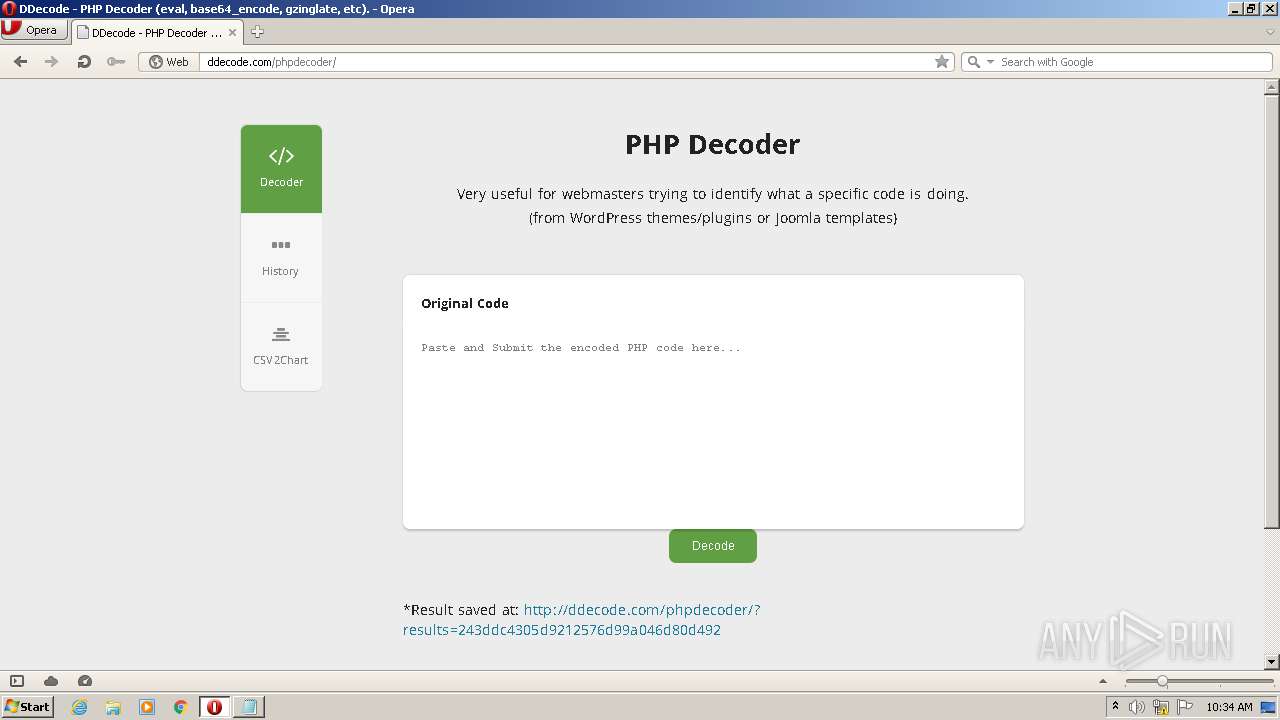
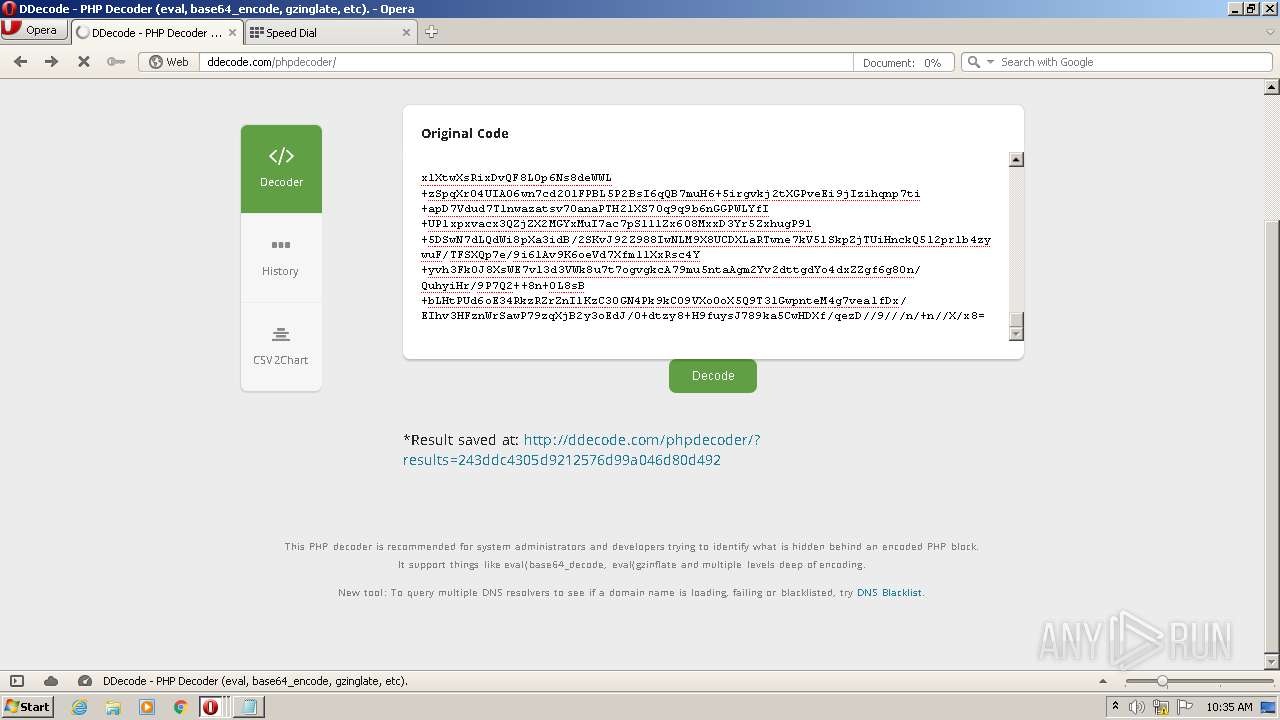
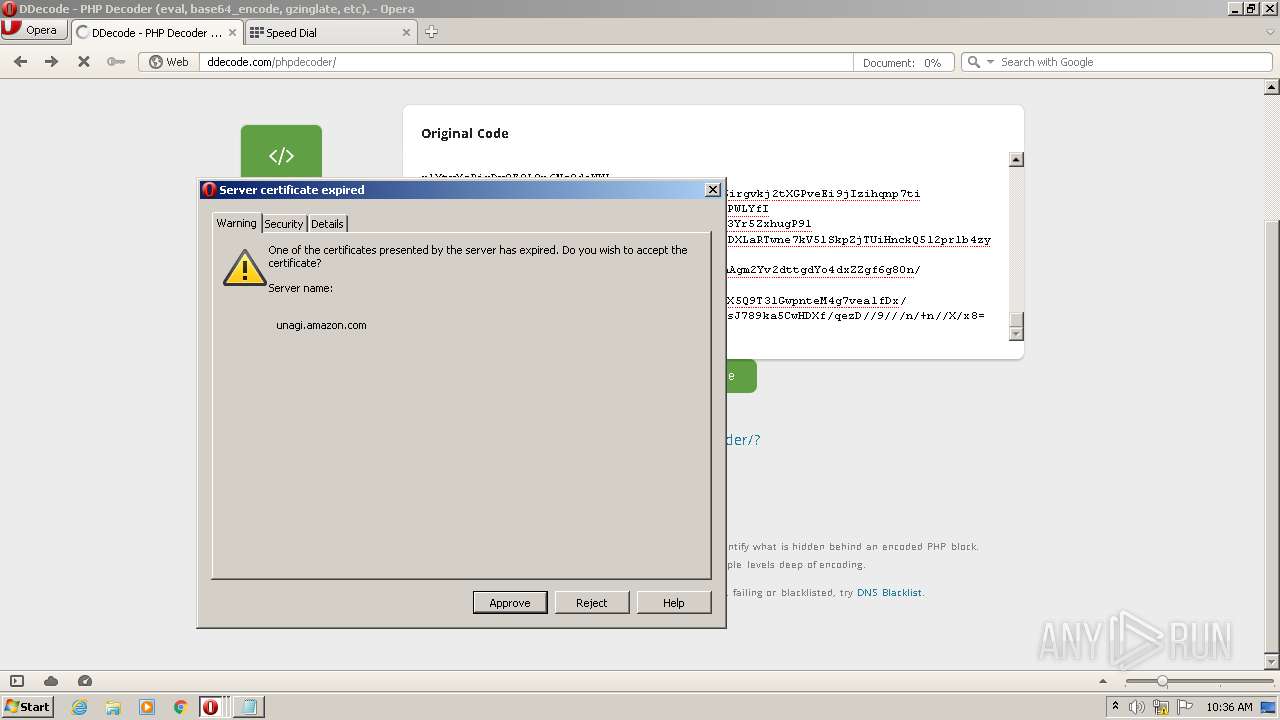
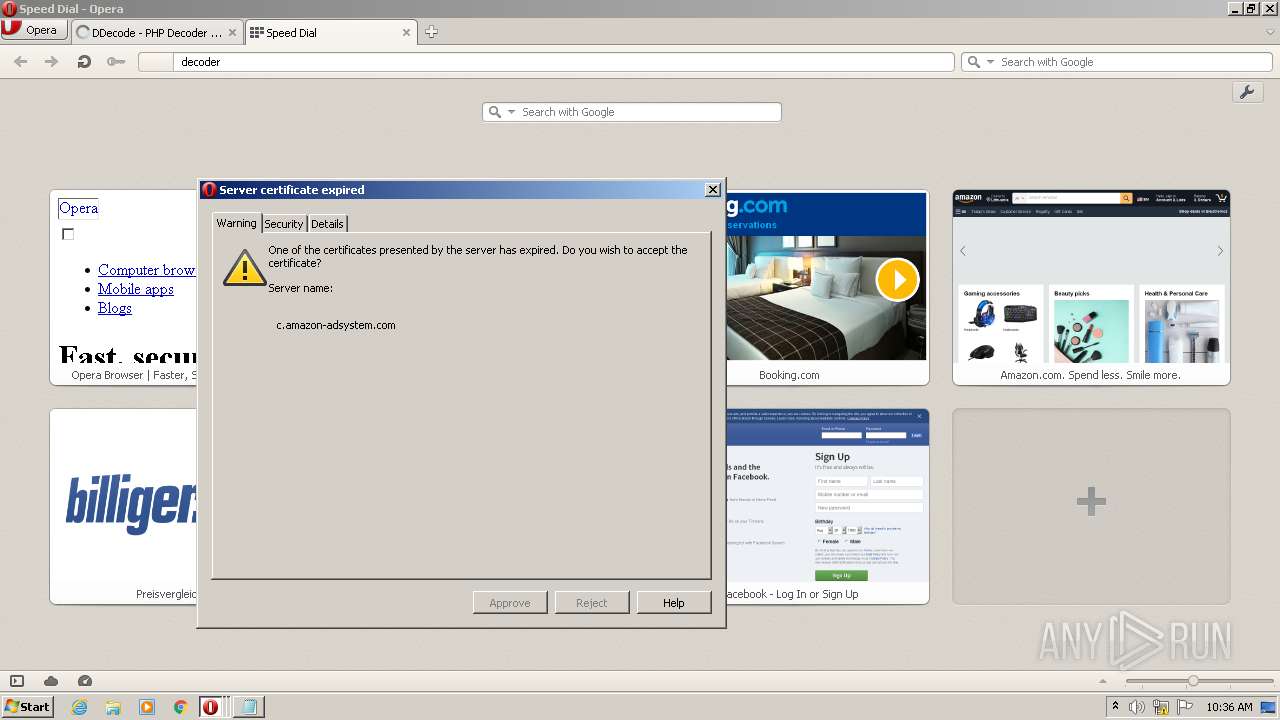
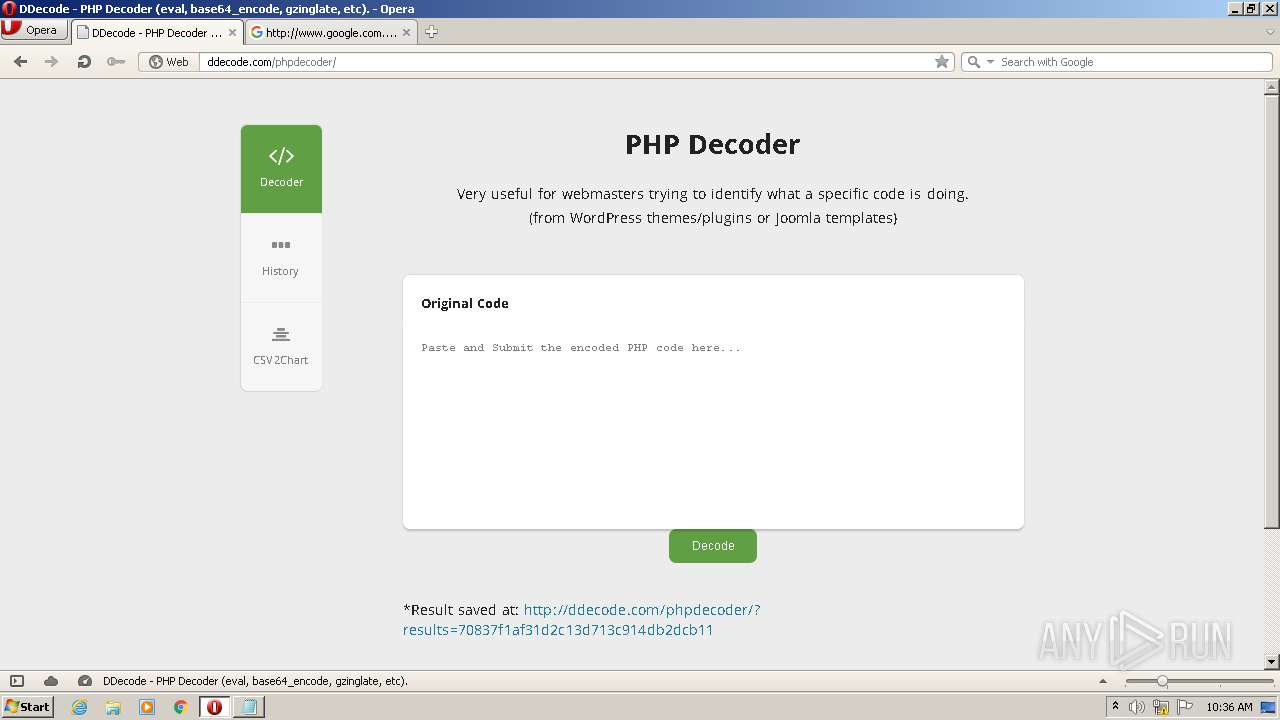
3104 | opera.exe | GET | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/style.css?v1 | US | text | 7.97 Kb | whitelisted |
3104 | opera.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGnf9r%2Flg7ADCgAFoANnbzM%3D | US | der | 471 b | whitelisted |
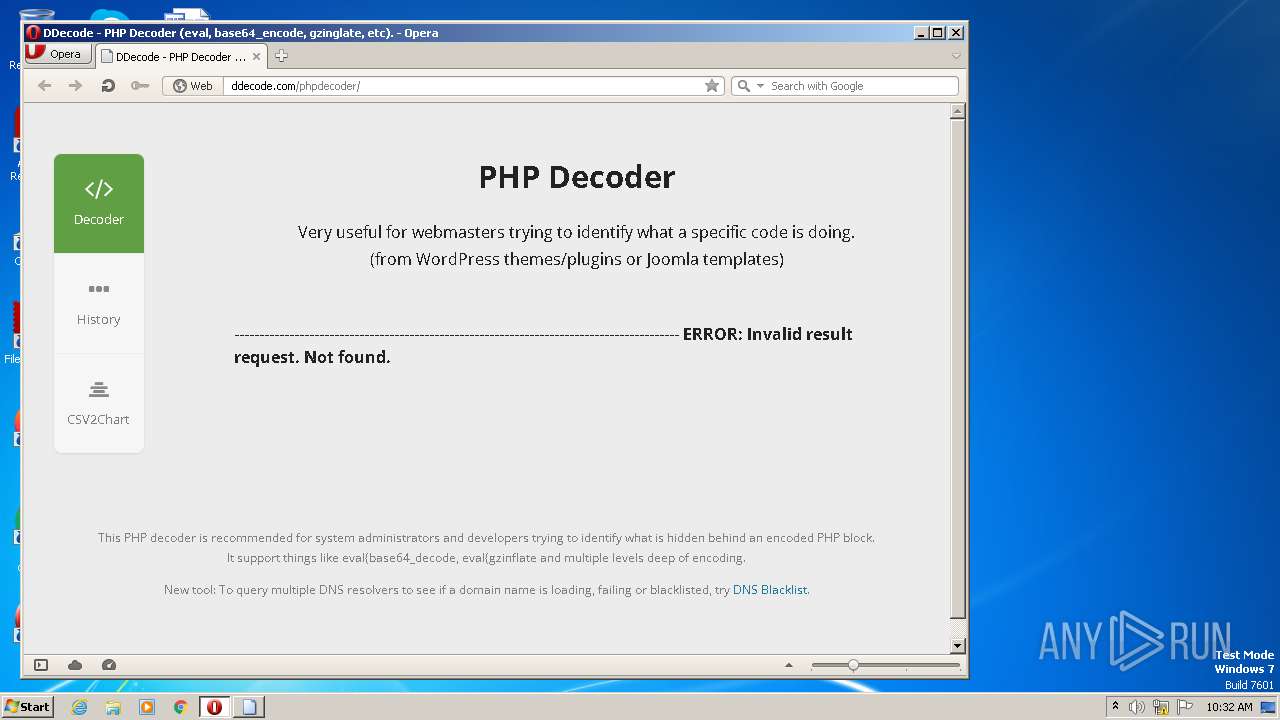
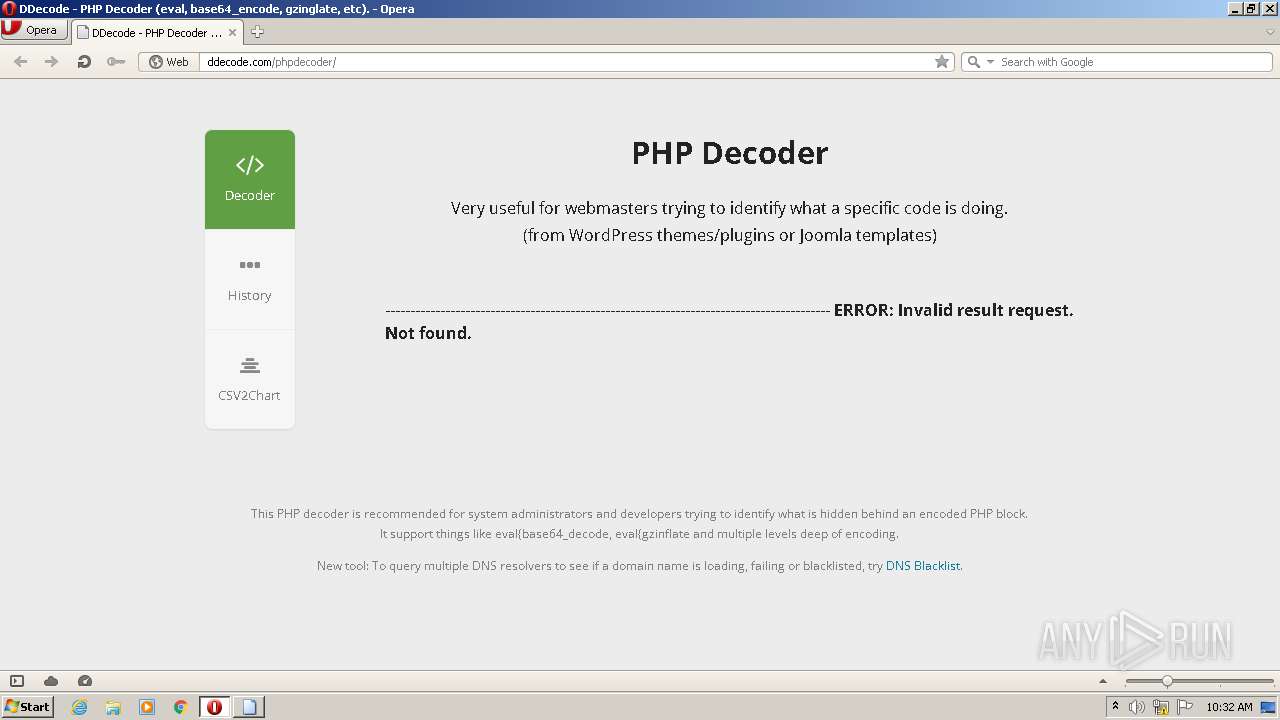
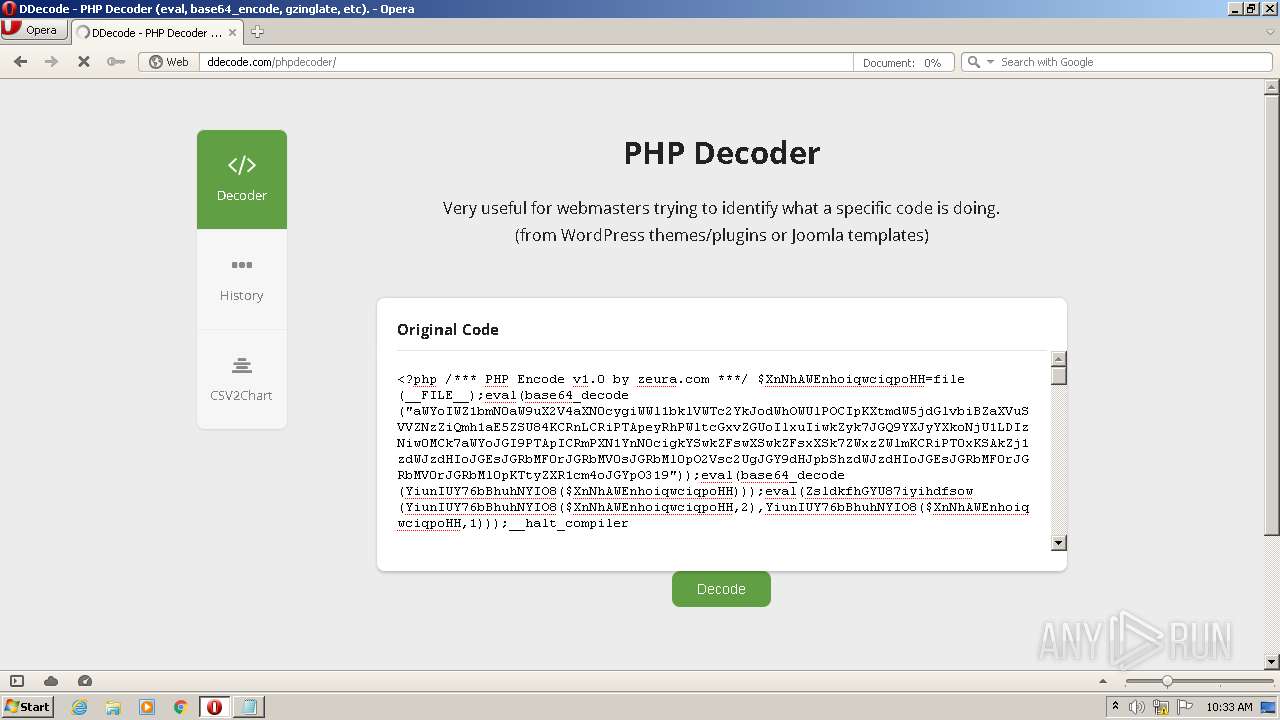
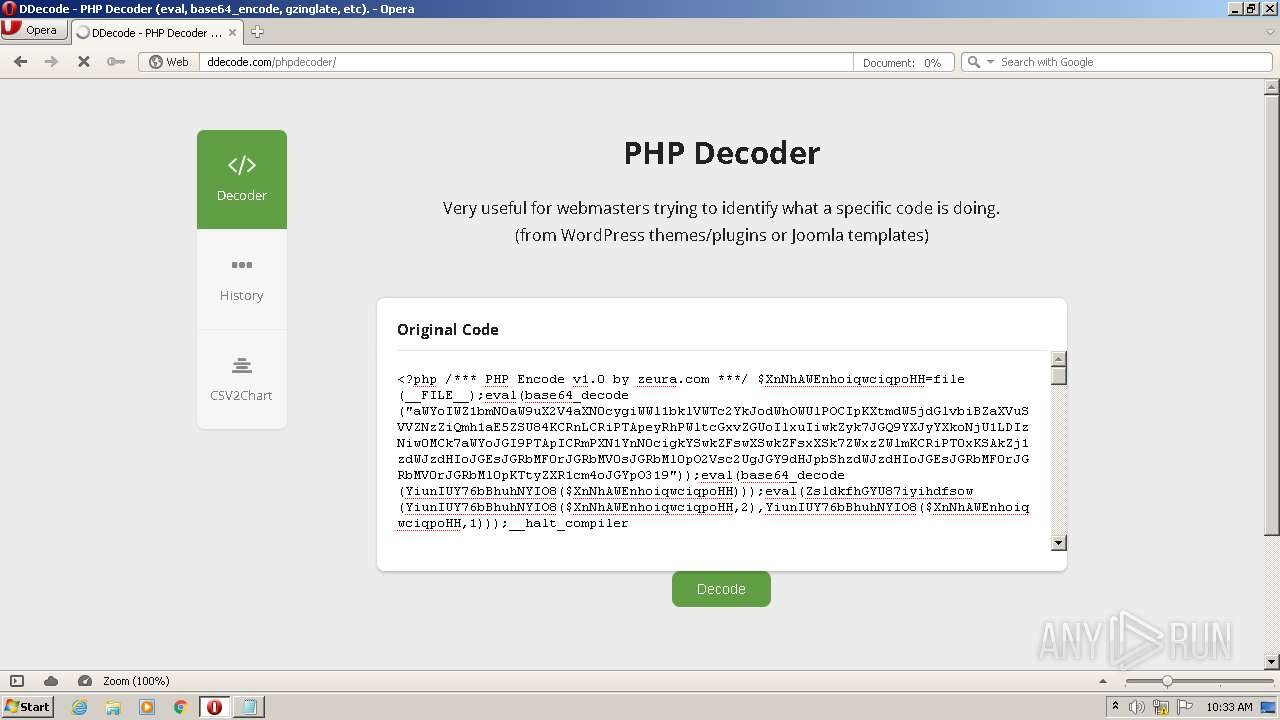
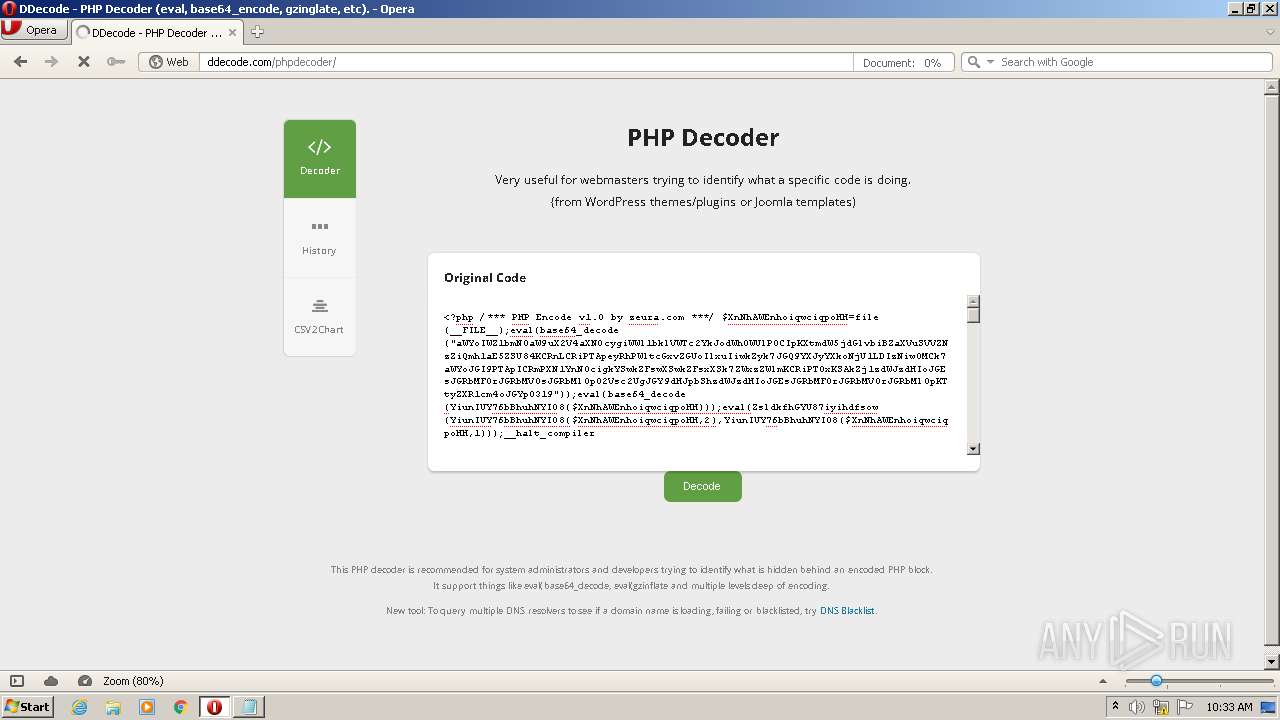
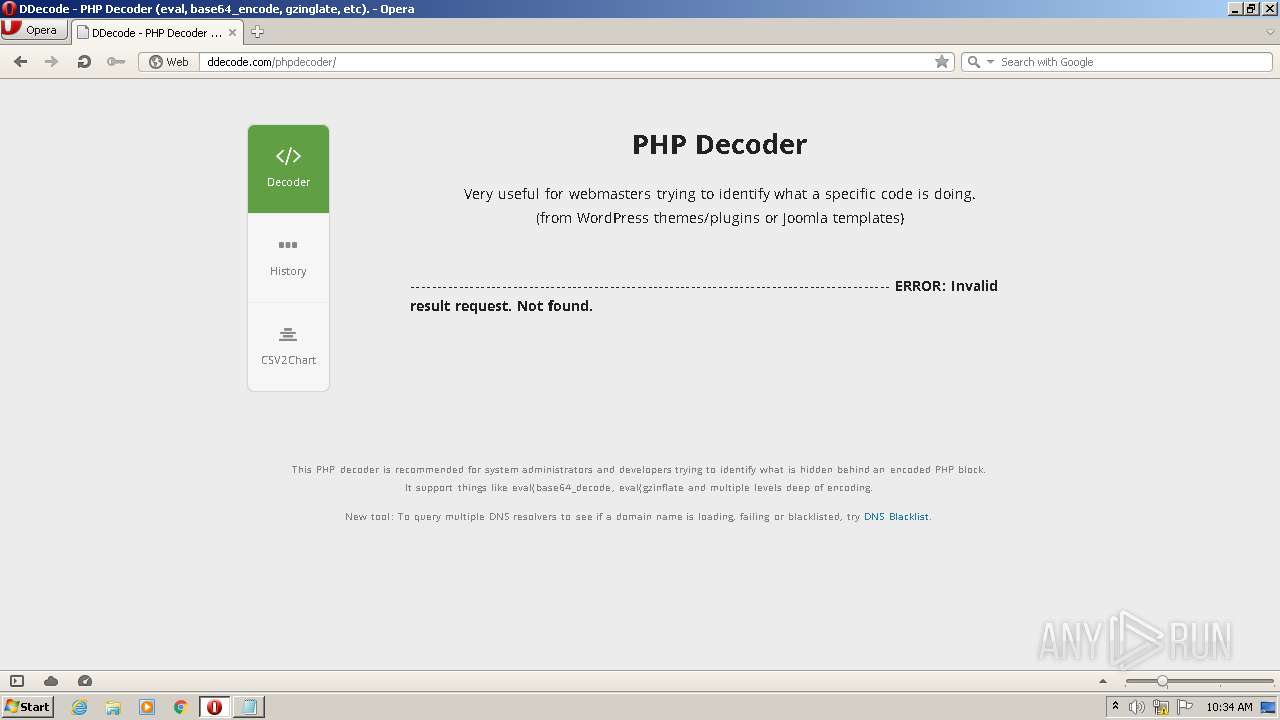
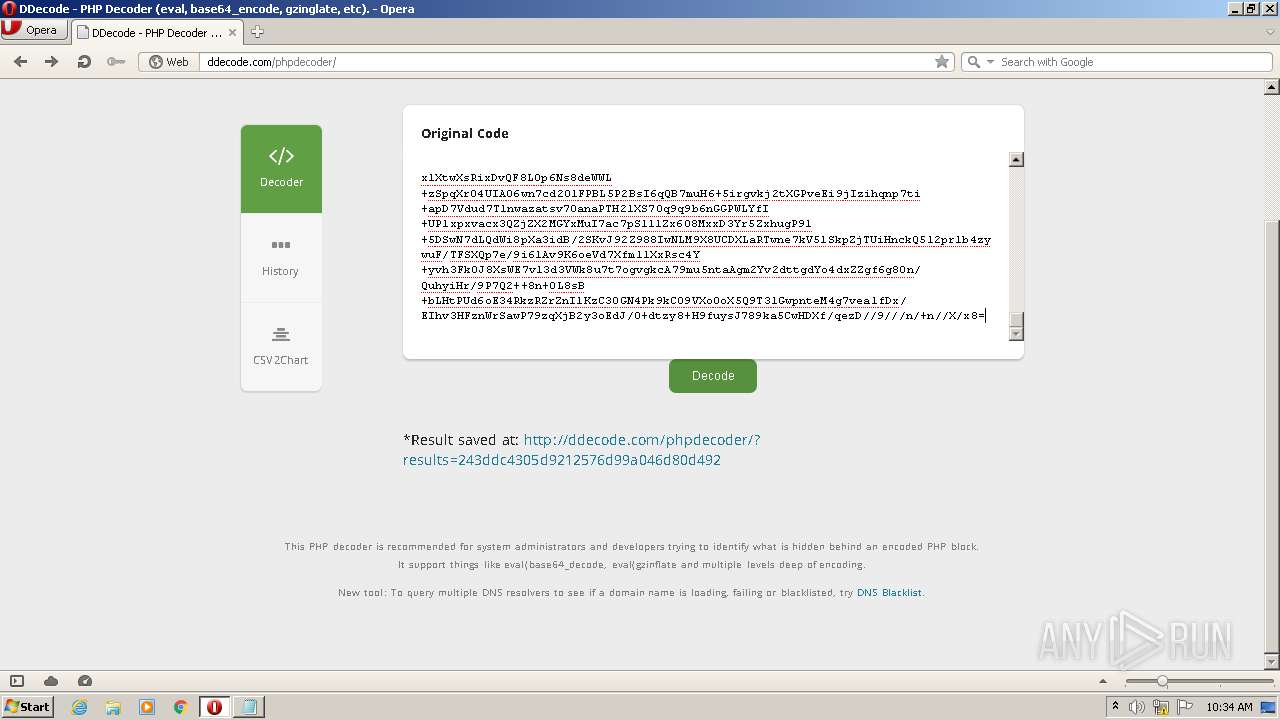
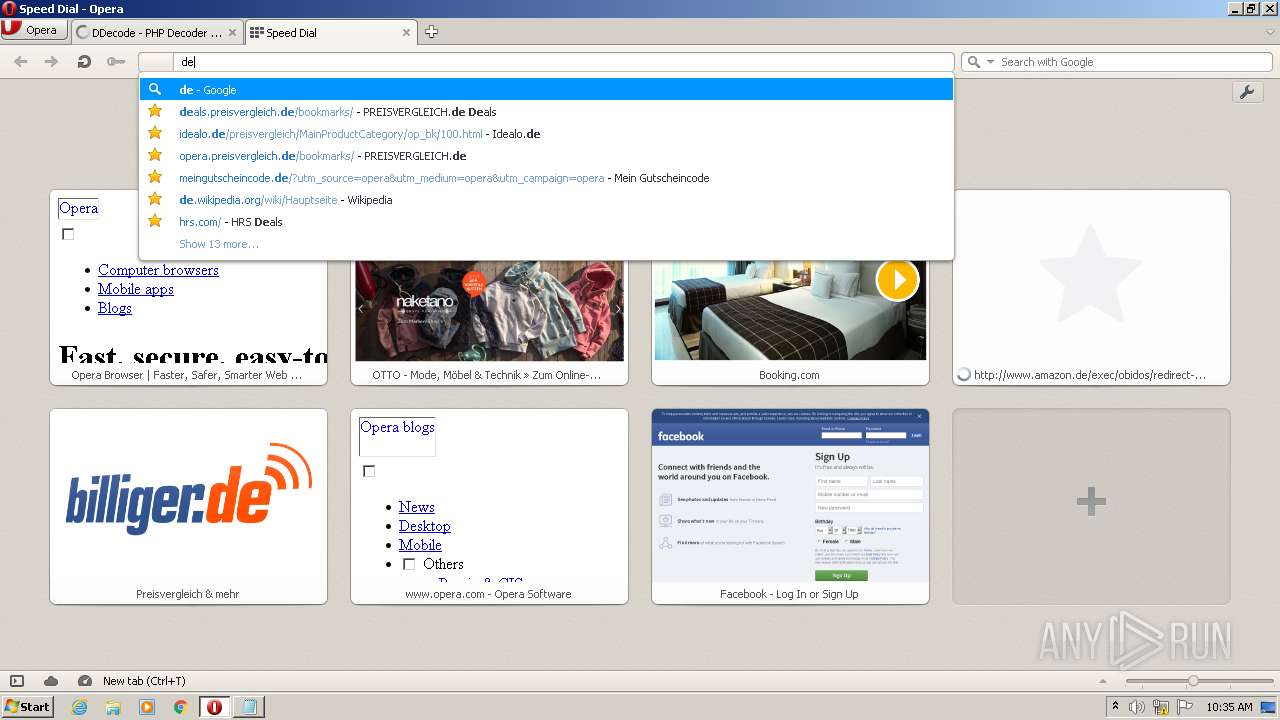
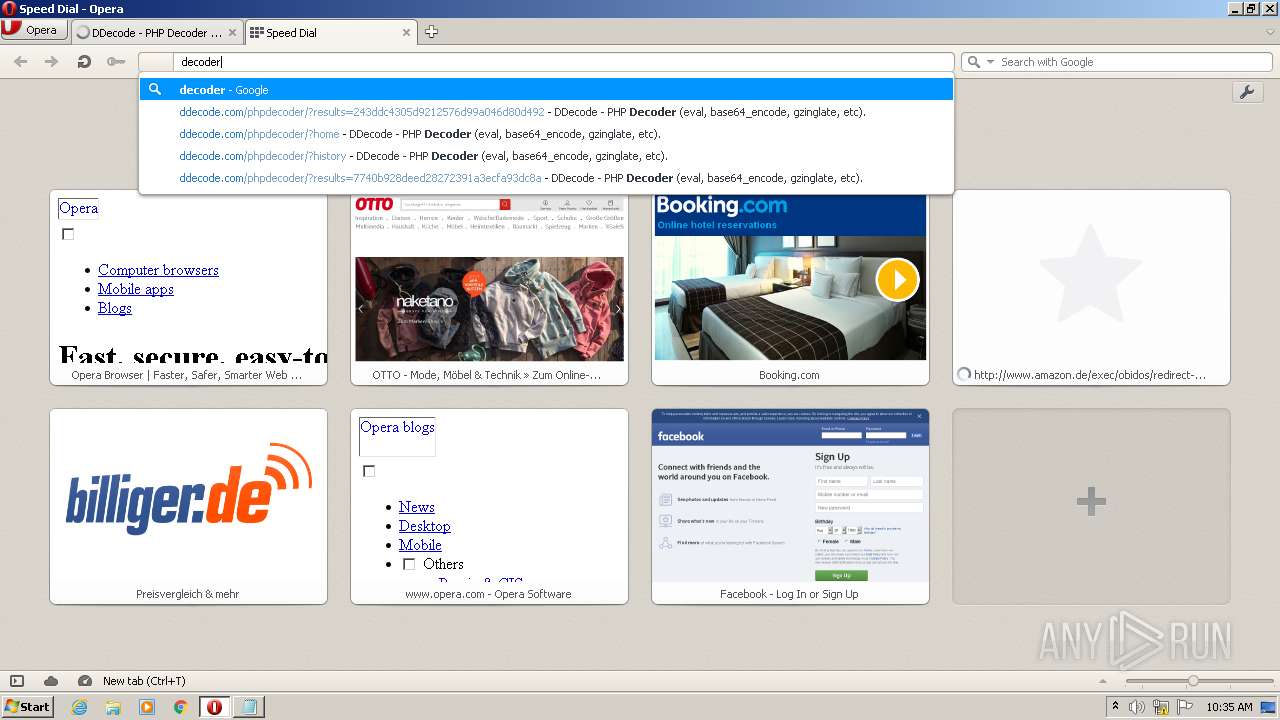
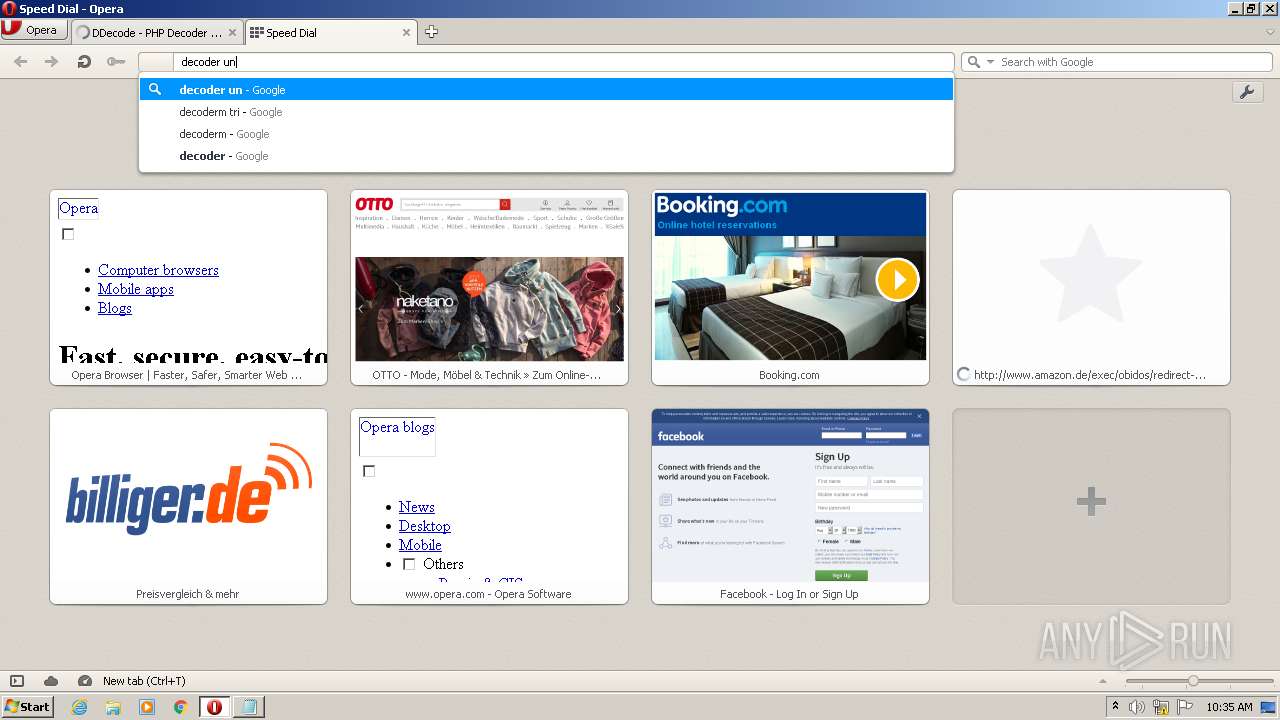
3104 | opera.exe | GET | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/?results=243ddc4305d9212576d99a046d80d492 | US | html | 1.96 Kb | whitelisted |
3104 | opera.exe | GET | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/?history | US | html | 1.80 Kb | whitelisted |
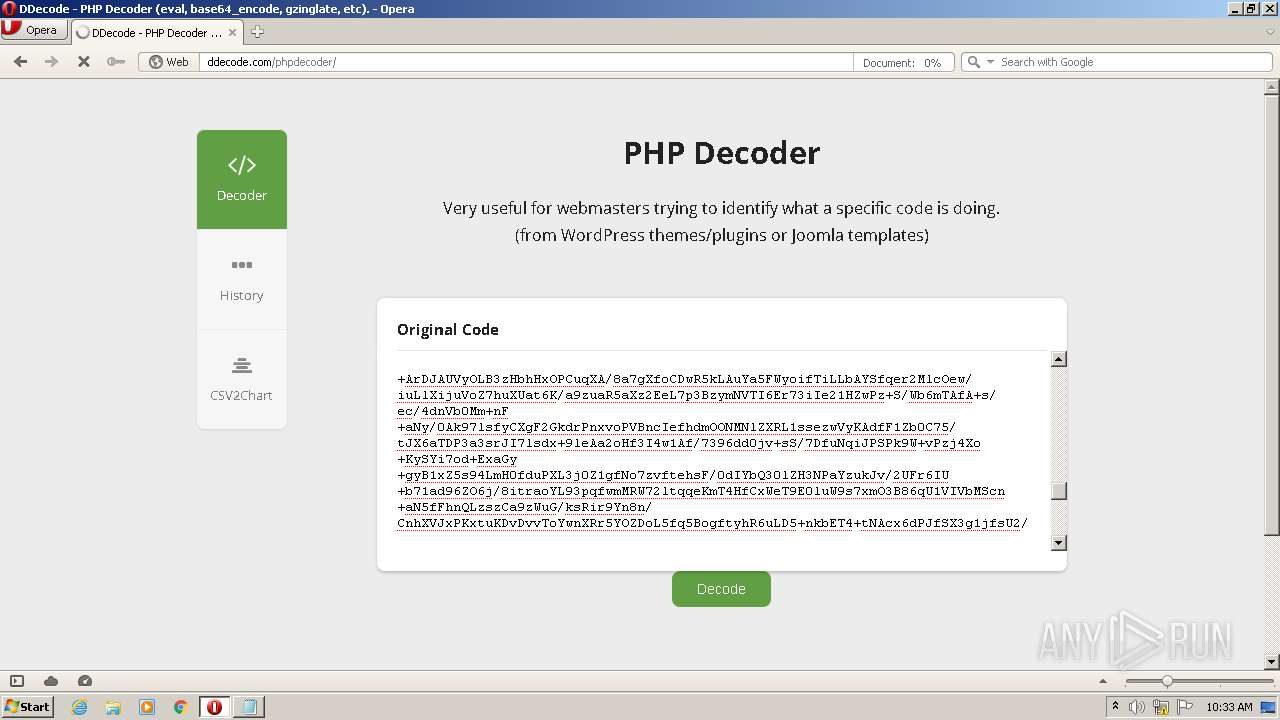
— | — | POST | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/?home | US | html | 2.21 Kb | whitelisted |
3104 | opera.exe | POST | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/?home | US | html | 2.21 Kb | whitelisted |
3104 | opera.exe | GET | 200 | 96.126.100.35:80 | http://ddecode.com/phpdecoder/?results=7740b928deed28272391a3ecfa93dc8a | US | html | 1.96 Kb | whitelisted |
3104 | opera.exe | GET | 200 | 142.250.186.67:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 835 b | whitelisted |
— | — | GET | 404 | 96.126.100.35:80 | http://ddecode.com/favicon.ico | US | html | 209 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | opera.exe | 185.26.182.109:80 | redir.opera.com | Opera Software AS | — | unknown |
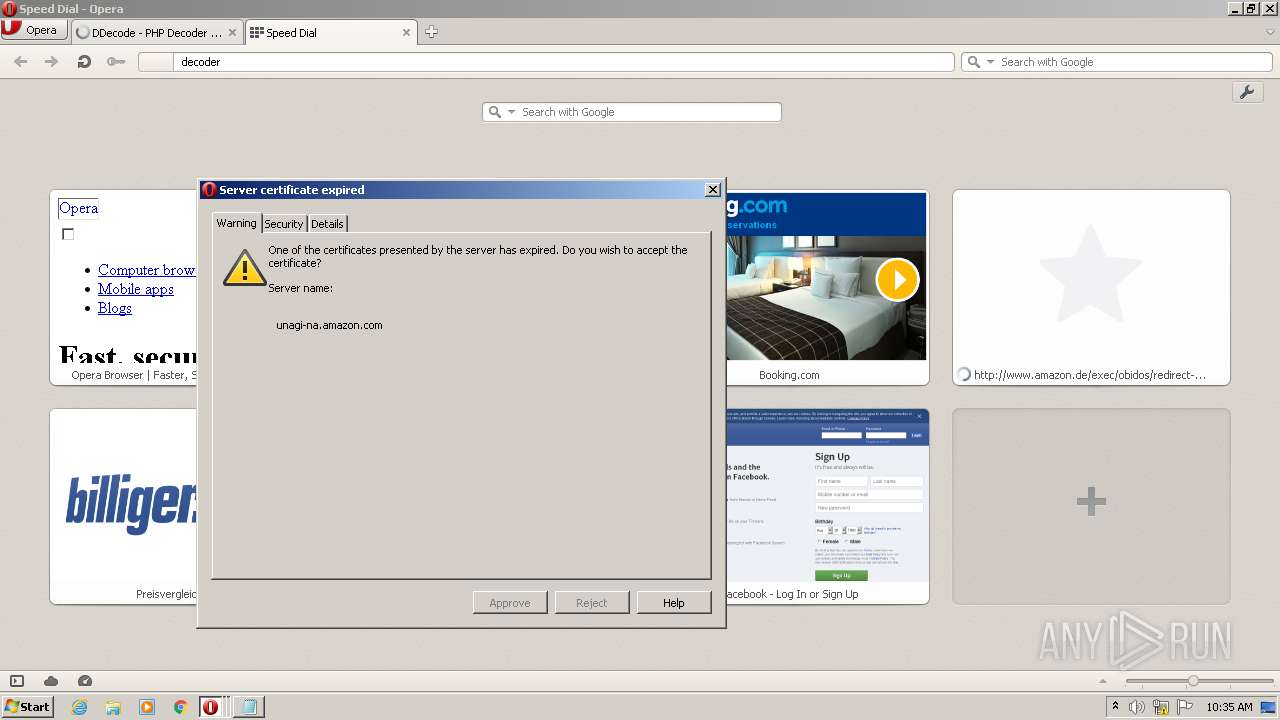
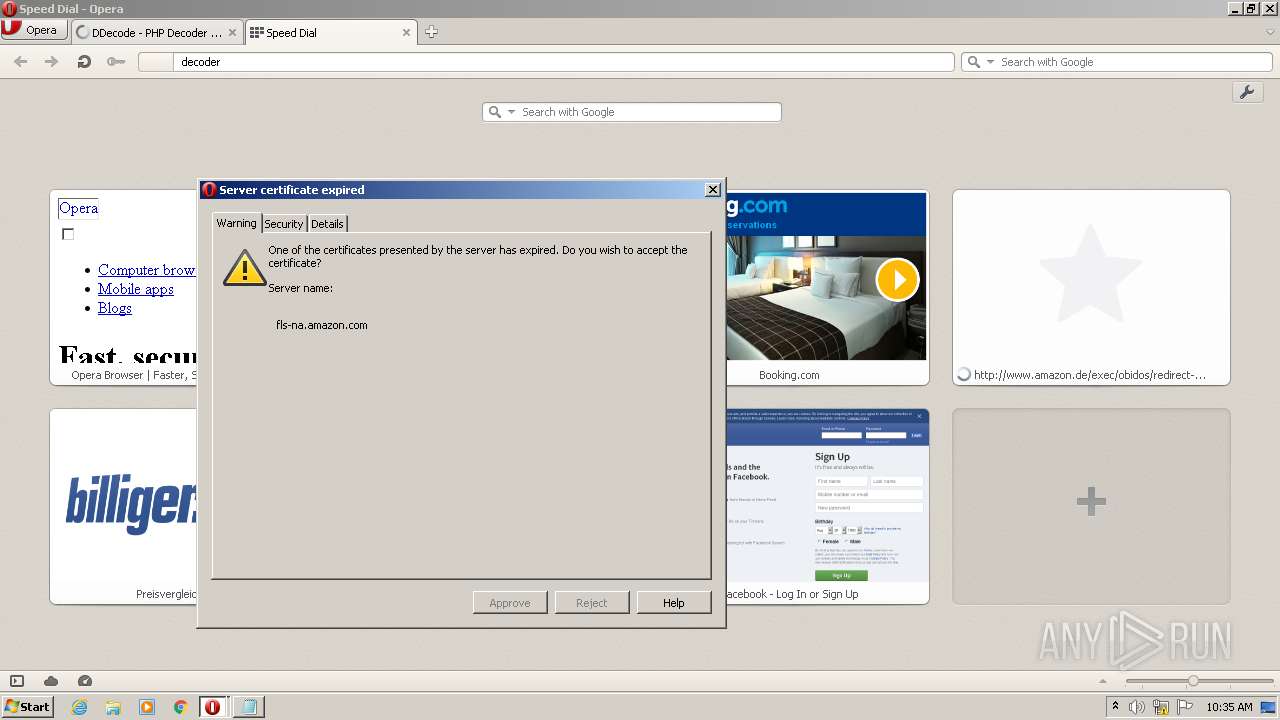
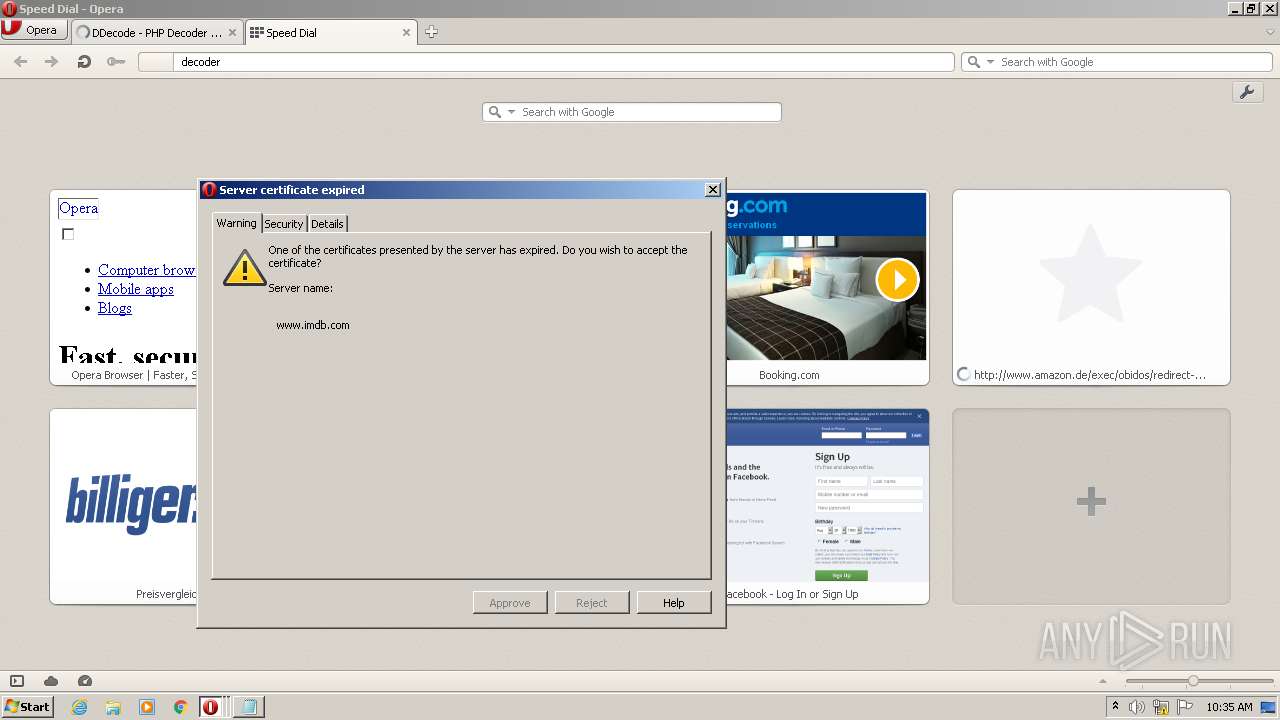
3104 | opera.exe | 108.138.5.166:80 | www.amazon.com | AMAZON-02 | US | suspicious |
3104 | opera.exe | 192.229.221.95:80 | crl4.digicert.com | EDGECAST | US | whitelisted |
3104 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3104 | opera.exe | 96.126.100.35:80 | ddecode.com | Linode, LLC | US | malicious |
3104 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
— | — | 96.126.100.35:80 | ddecode.com | Linode, LLC | US | malicious |
3104 | opera.exe | 151.101.1.16:443 | images-na.ssl-images-amazon.com | FASTLY | US | suspicious |
3104 | opera.exe | 172.217.16.142:80 | clients1.google.com | GOOGLE | US | whitelisted |
— | — | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
ddecode.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
redir.opera.com |
| whitelisted |
www.amazon.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
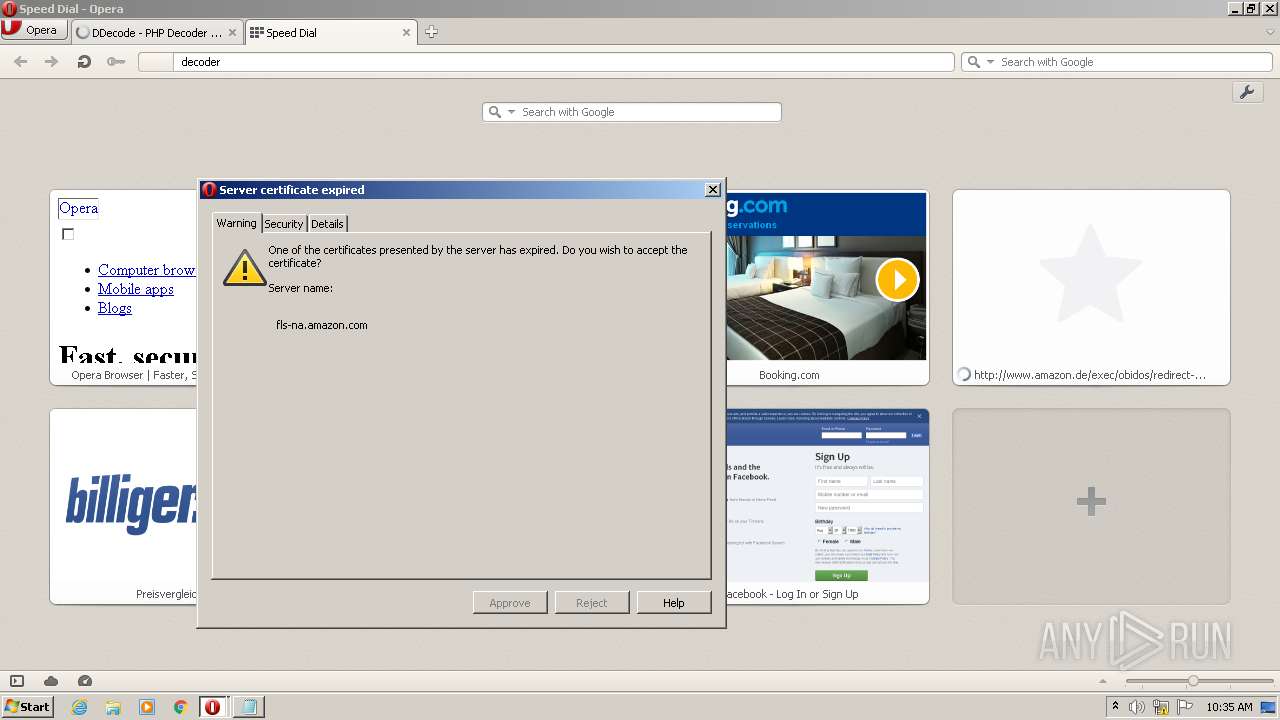
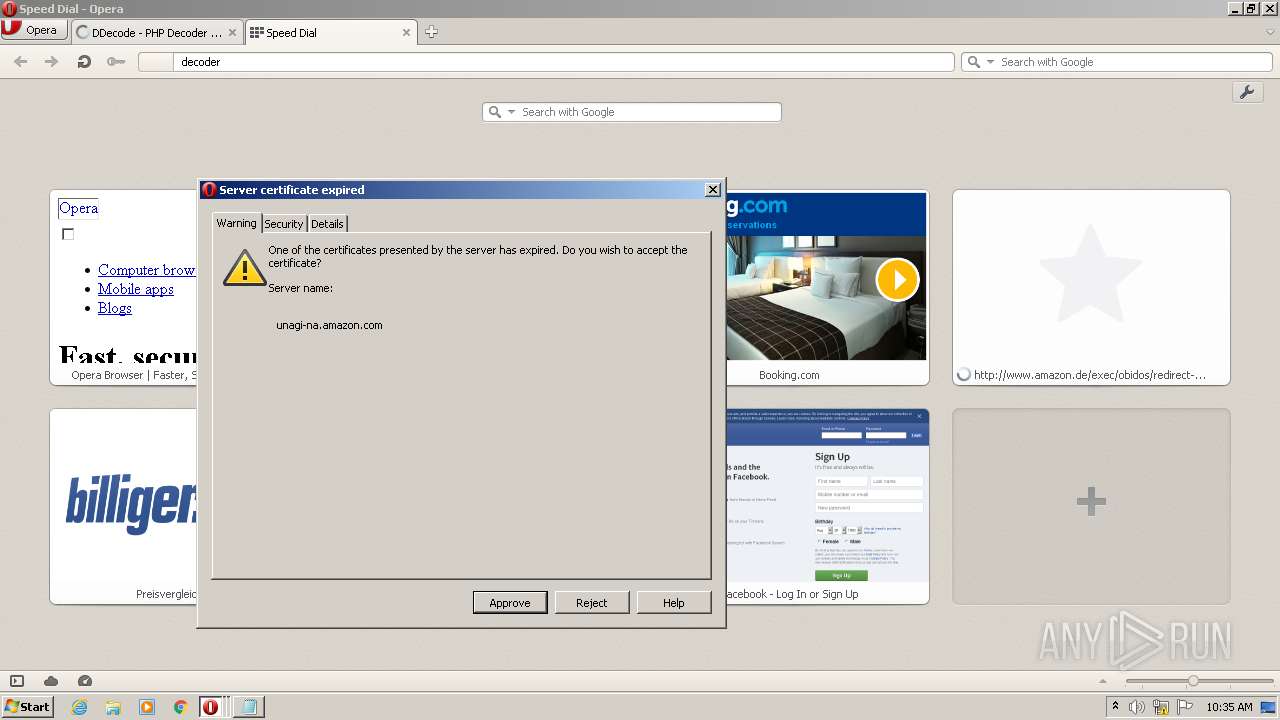
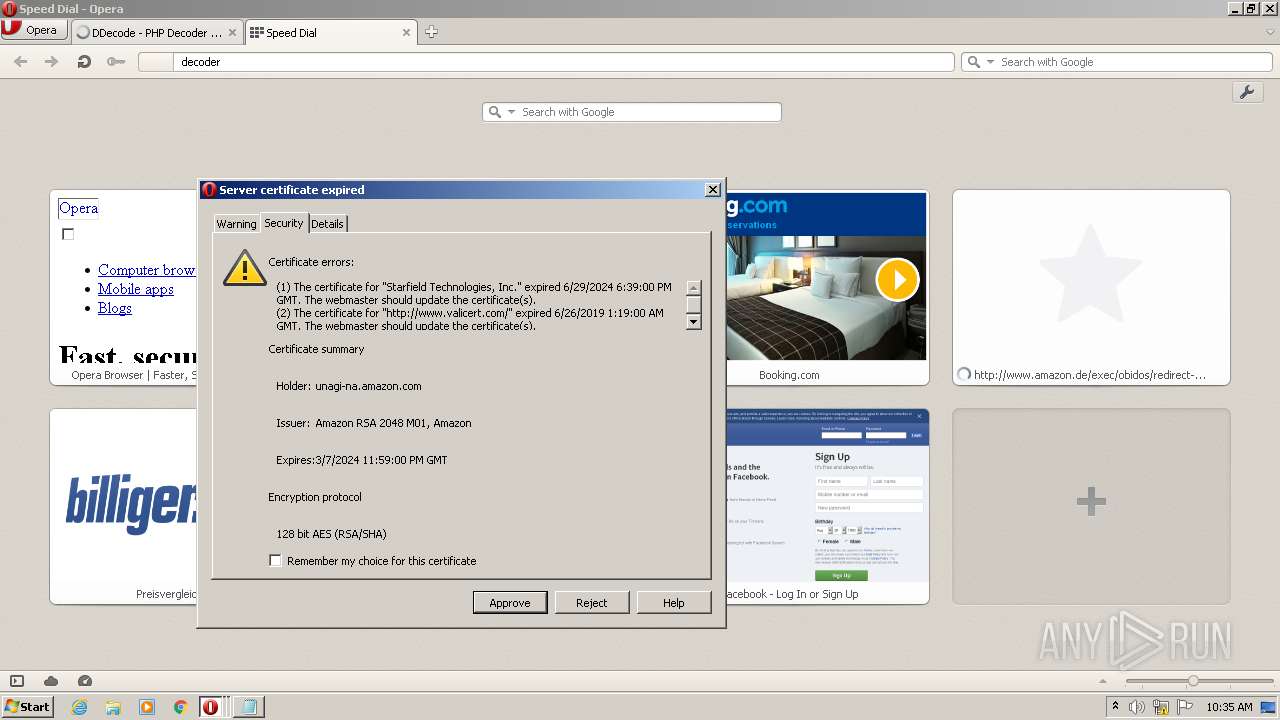
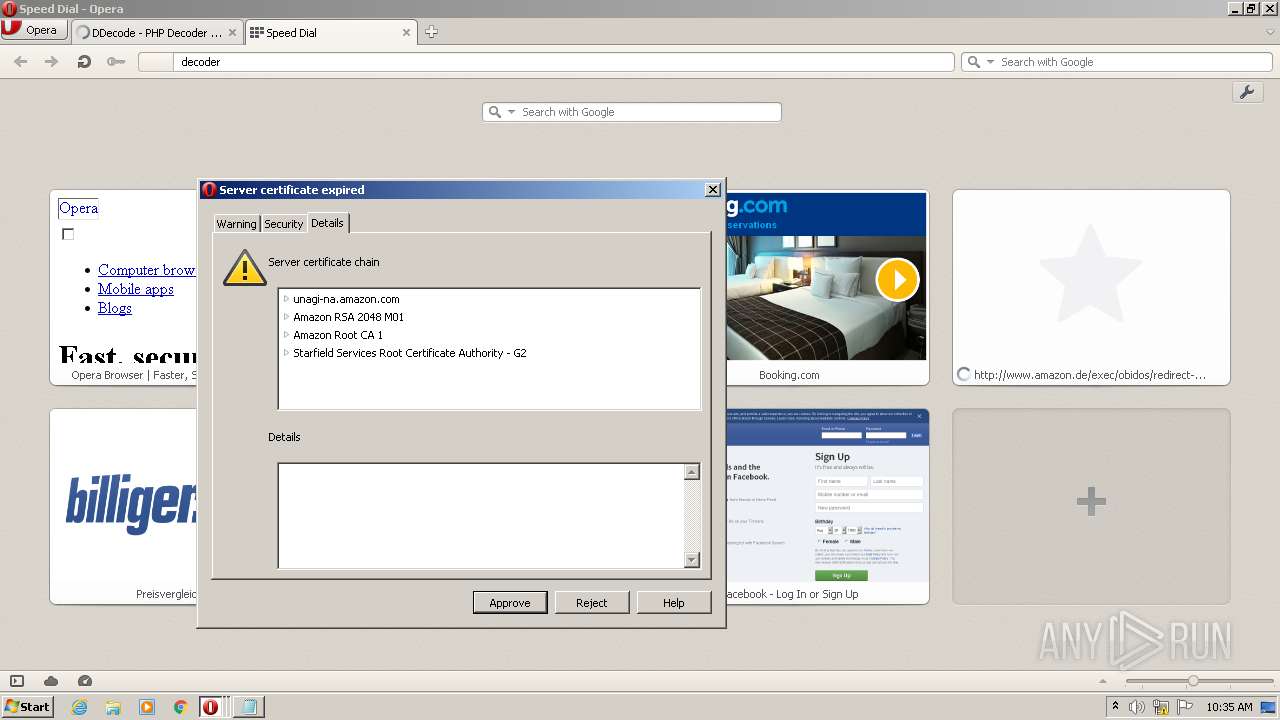
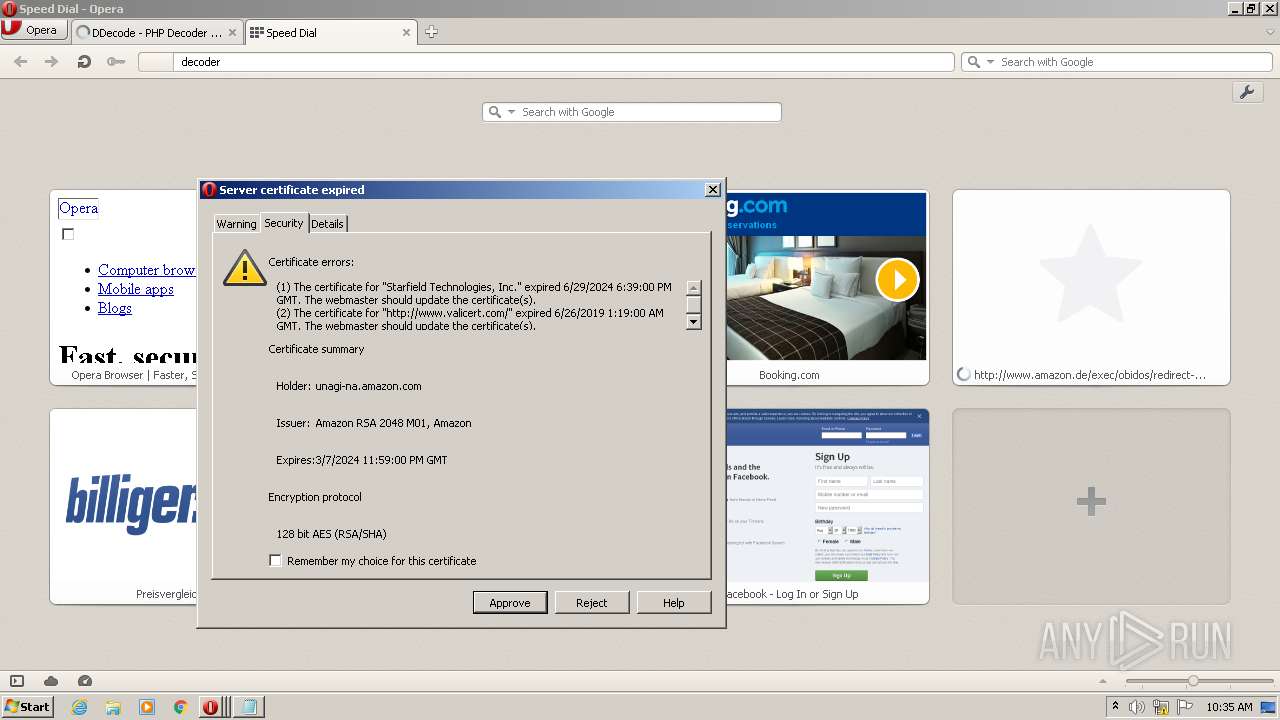
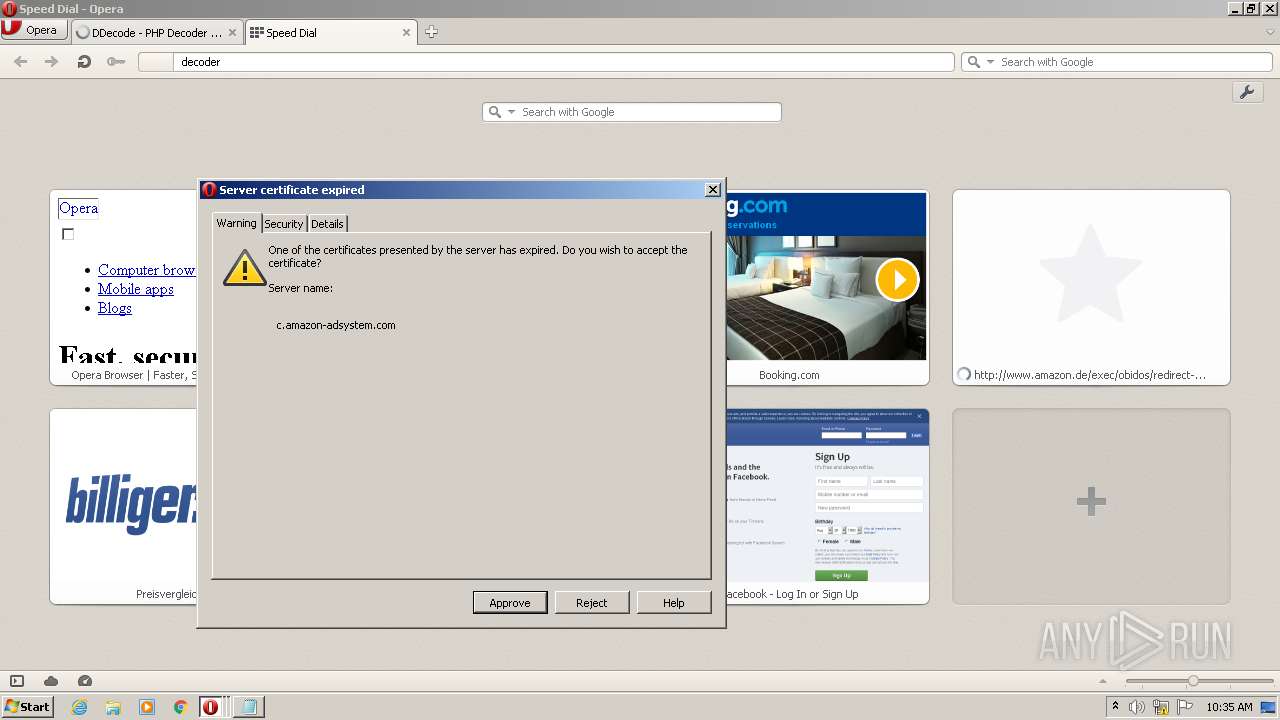
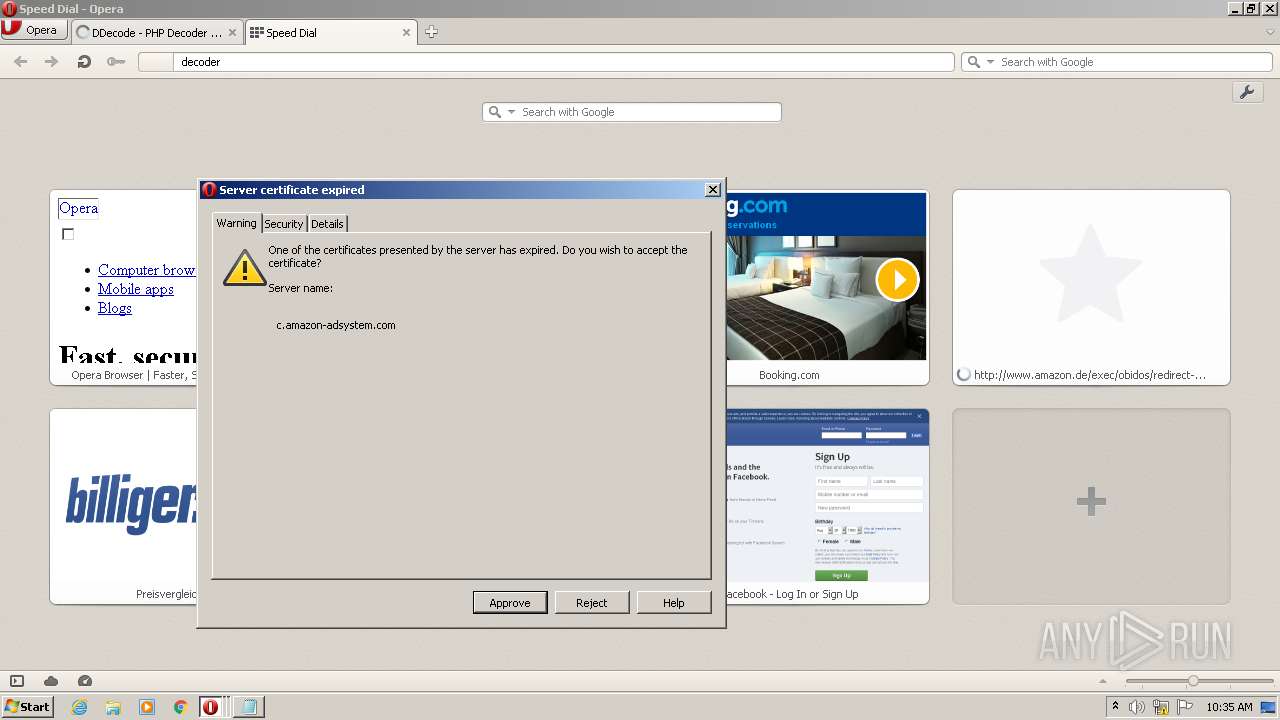
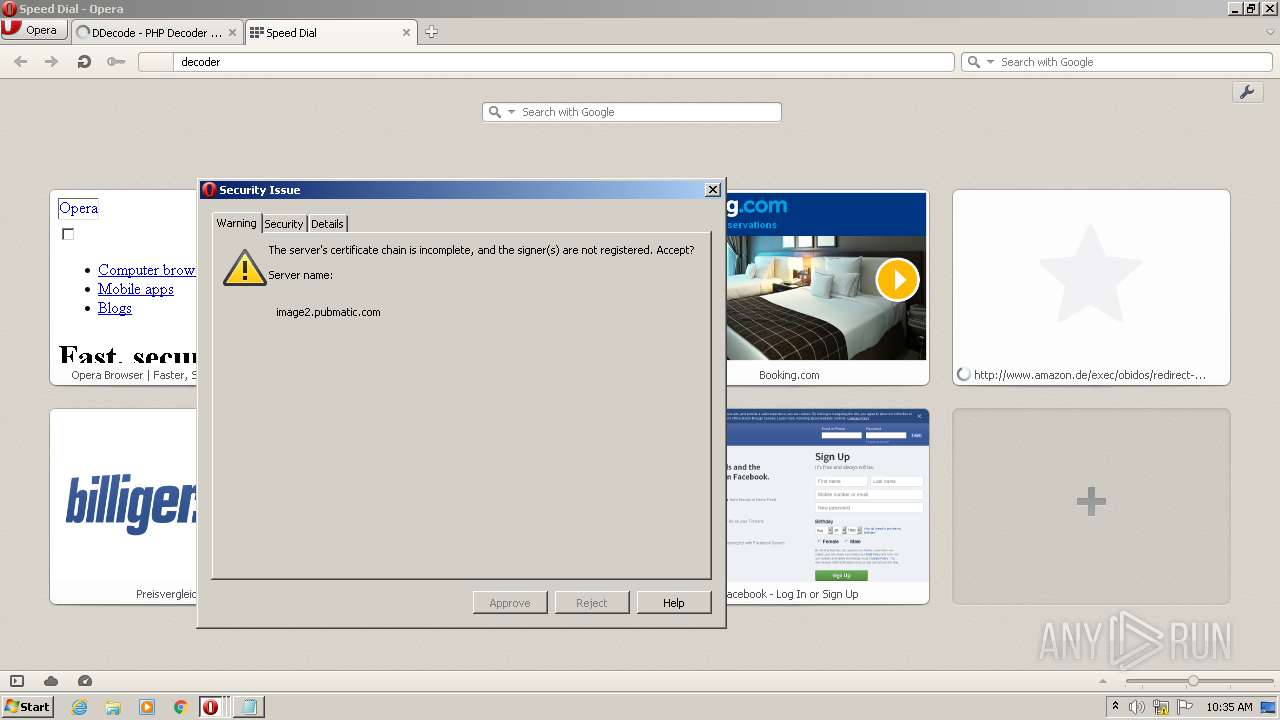
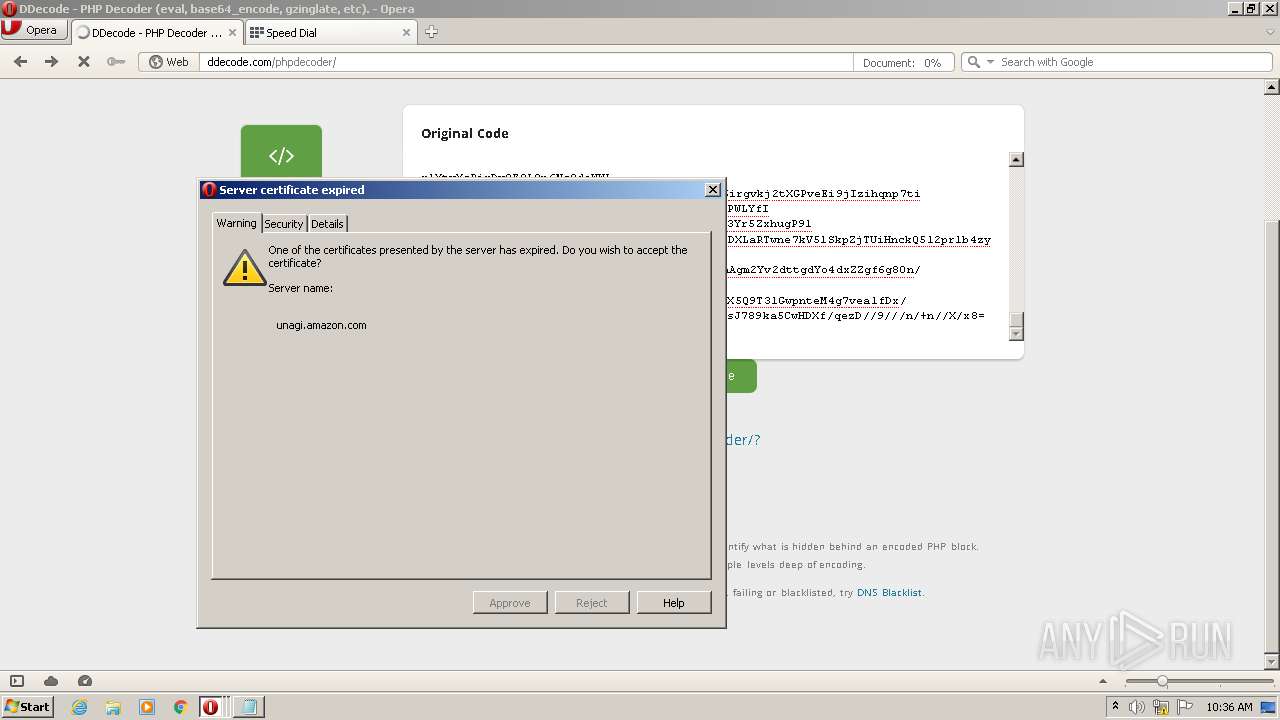
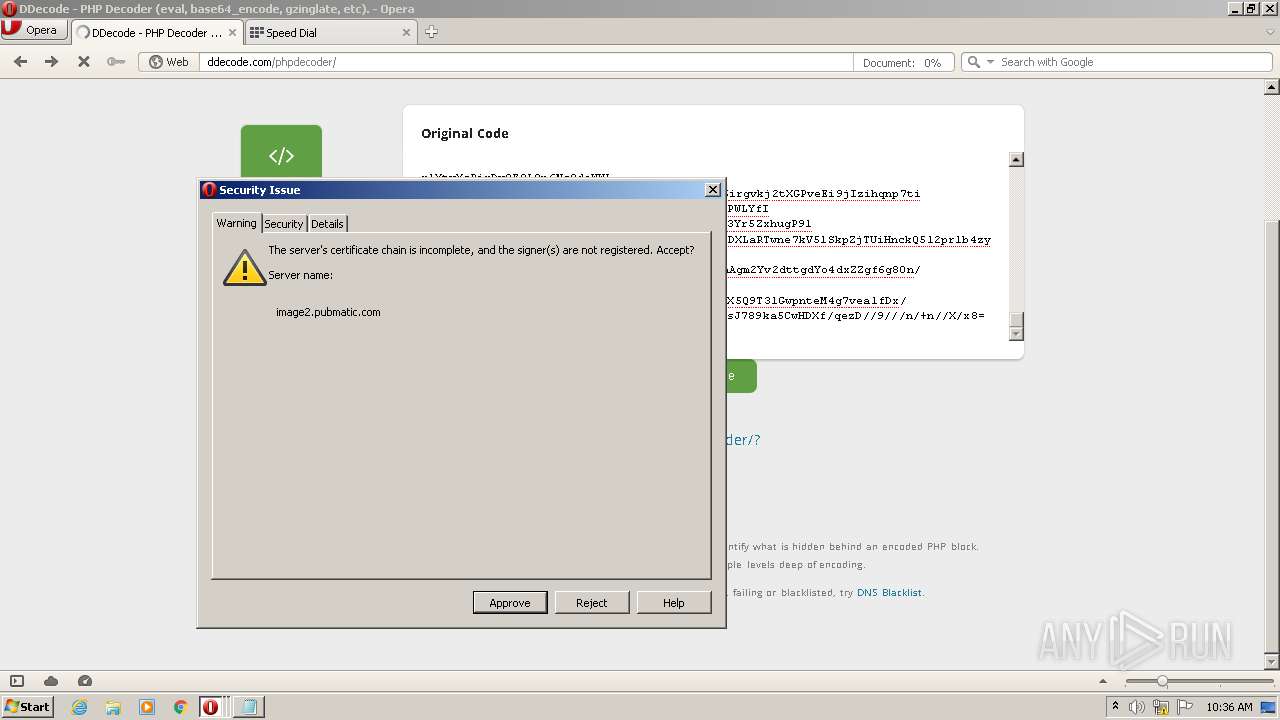
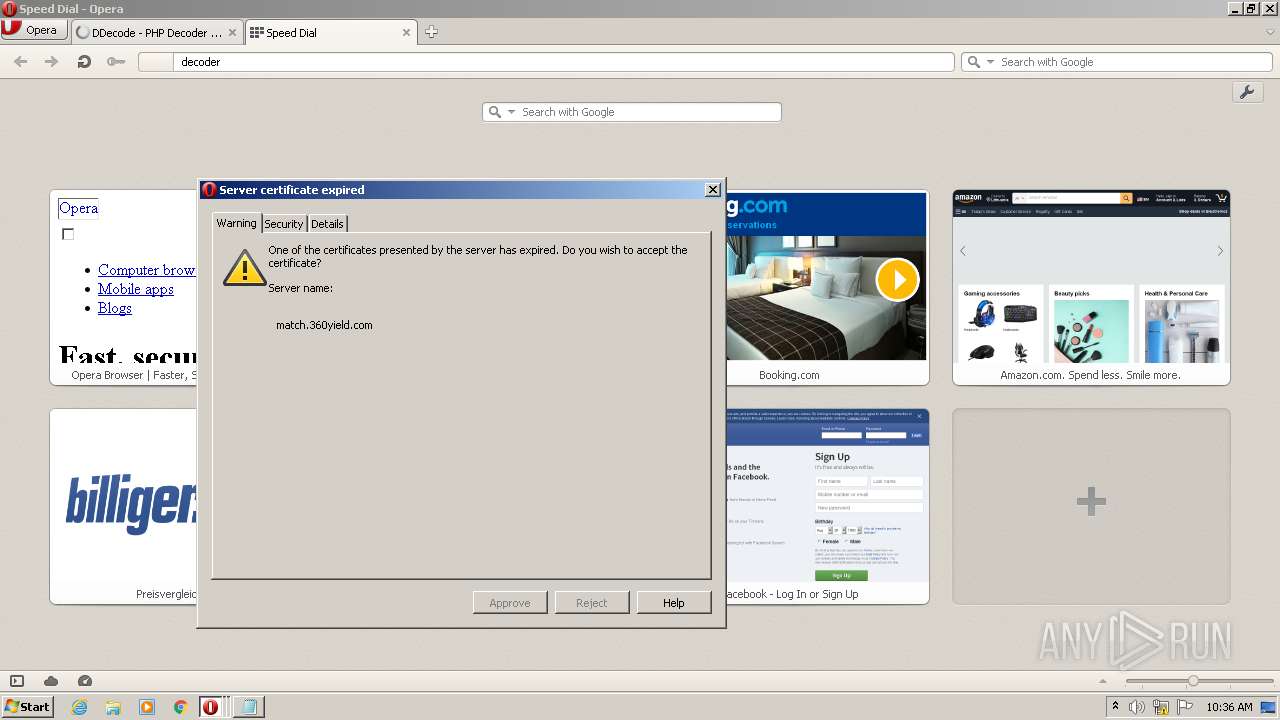
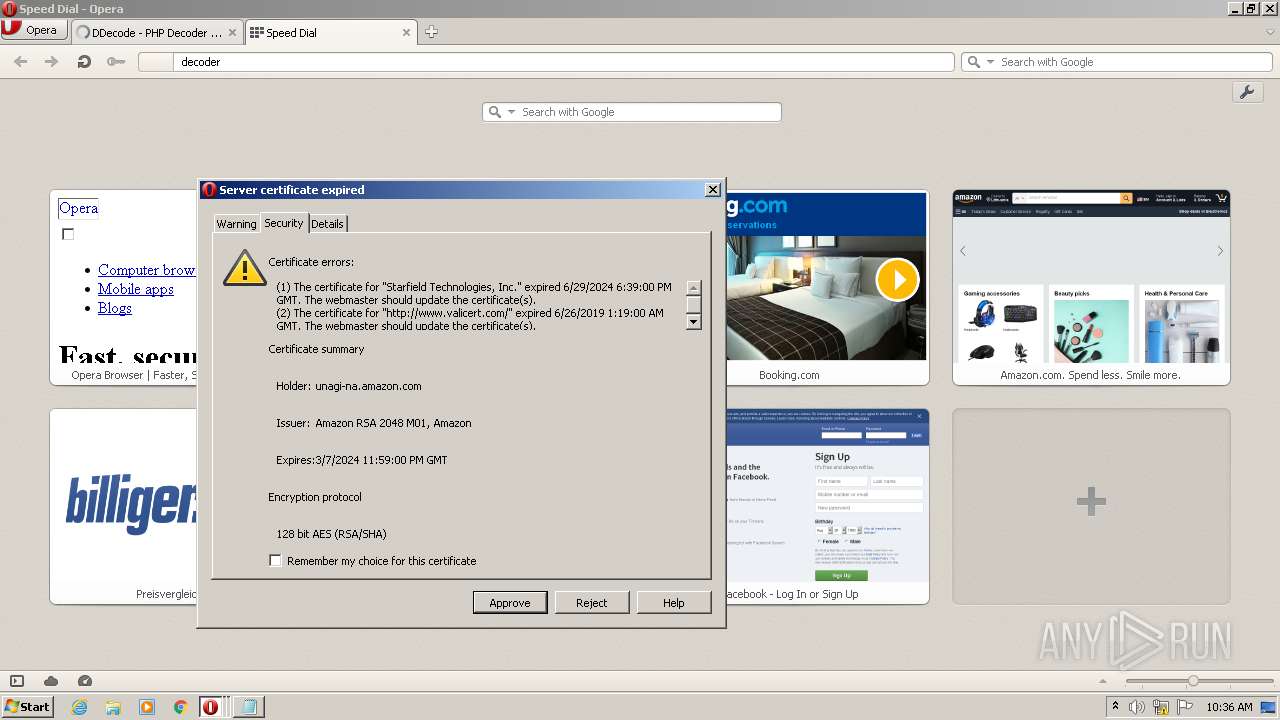
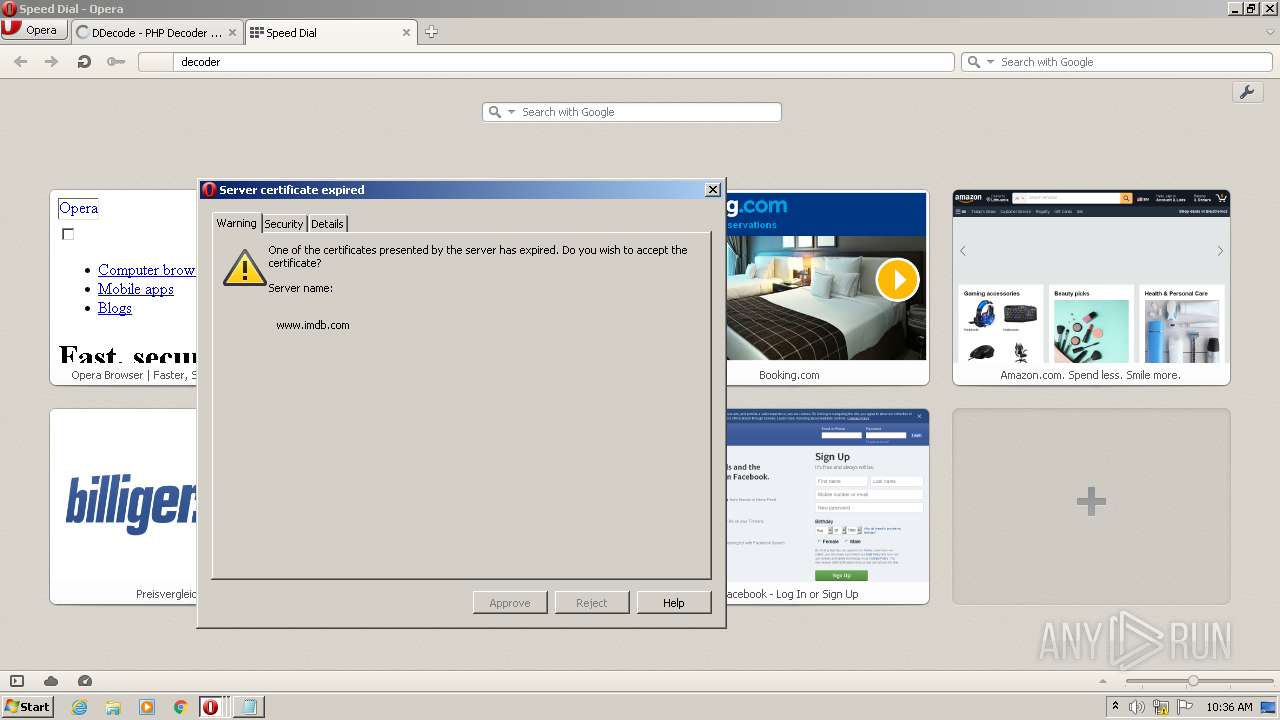
3104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of base64_decode |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of gzinflate |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of base64_decode |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of gzinflate |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of base64_decode |
3104 | opera.exe | A Network Trojan was detected | ET WEB_SERVER WebShell Generic eval of gzinflate |
1 ETPRO signatures available at the full report