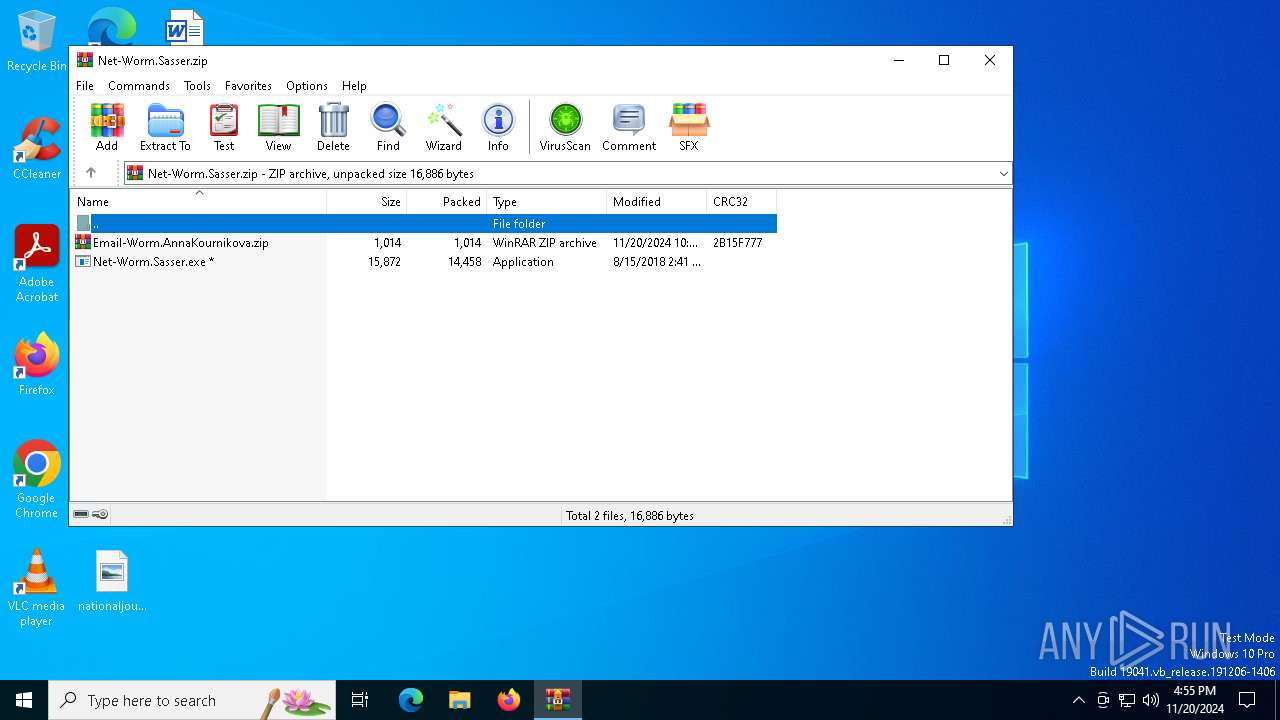
| File name: | Net-Worm.Sasser.zip |
| Full analysis: | https://app.any.run/tasks/0d939e9a-b3ca-4a7b-ba5f-6140f8dfcf6c |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 16:55:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
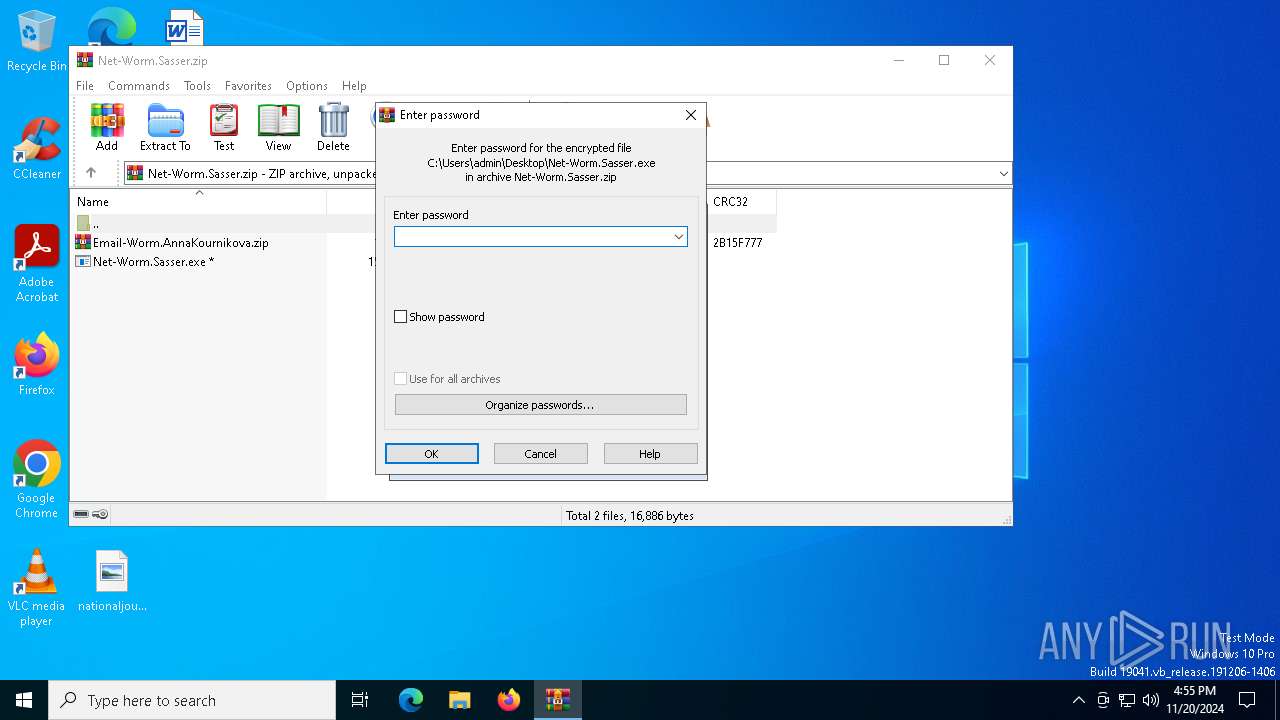
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | F6139CF3825E90B40E429CA6F0A60009 |
| SHA1: | F12363ADB76C2CE1307559CC0337A3C6EA6AD1FC |
| SHA256: | 56D78EBF518DB023E35202BC074C6EB7882D67EB04D697BFCE277E2EAEC30E65 |
| SSDEEP: | 384:JtqIrmOcpnaLEk5Mj6fDaNW2jt6mbJTW0X0lKm1Y/VPrBX:HqINcpE6YaNW2cOJ60klKm18Jd |
MALICIOUS
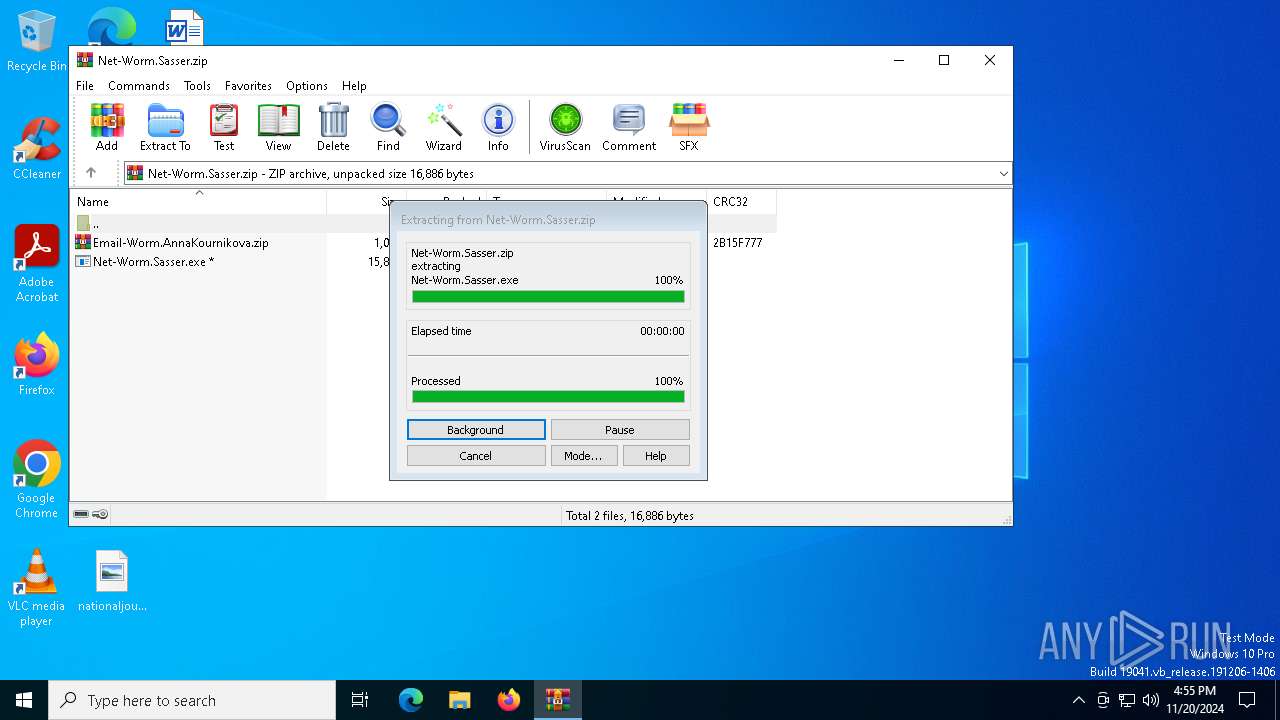
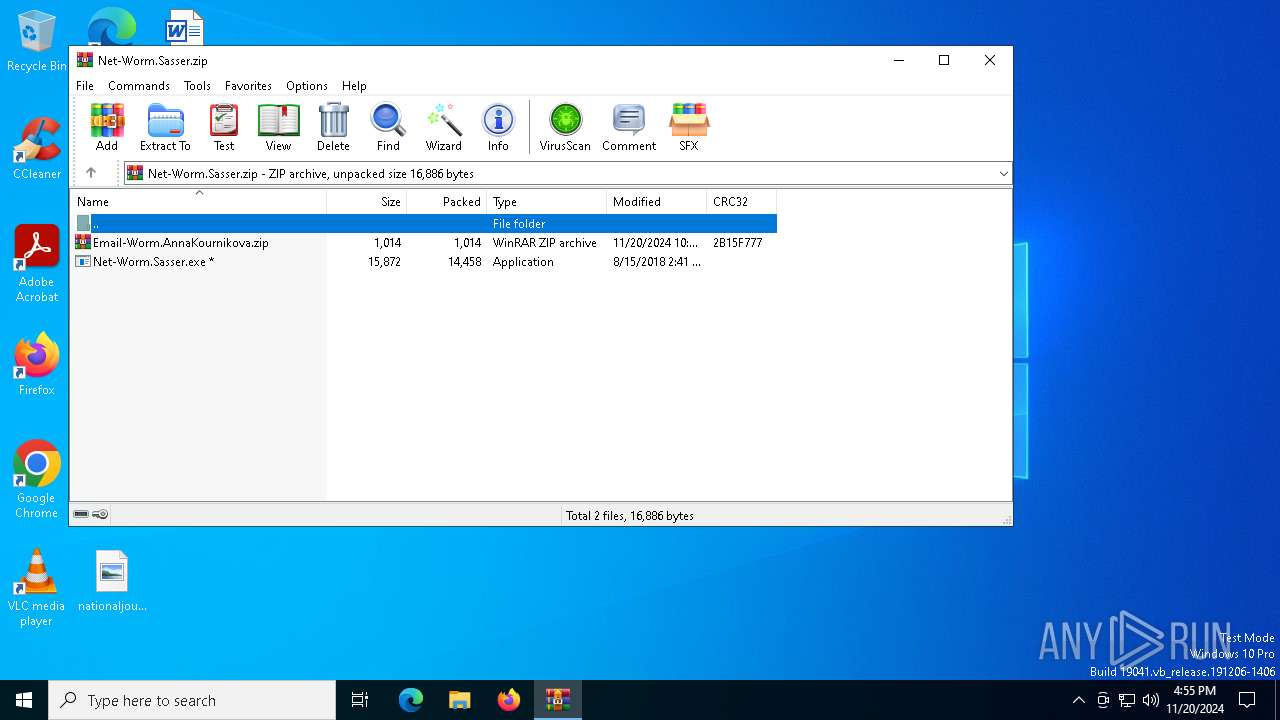
Generic archive extractor
- WinRAR.exe (PID: 4140)
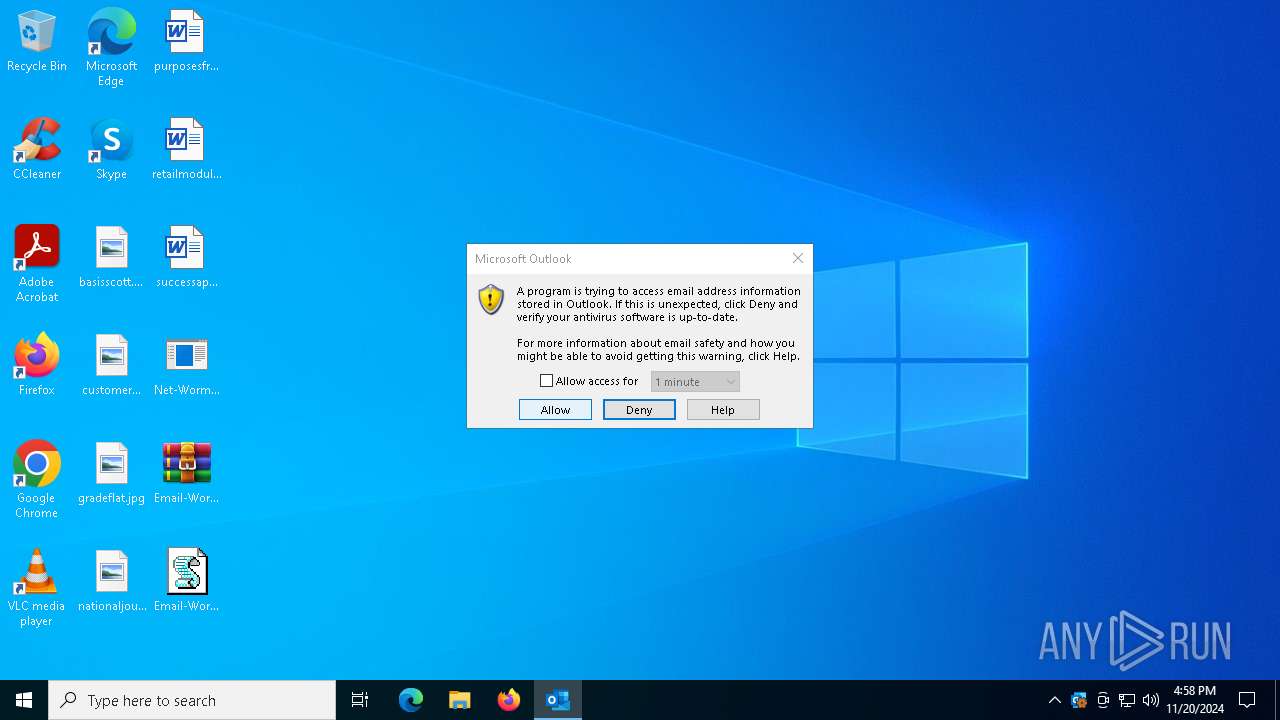
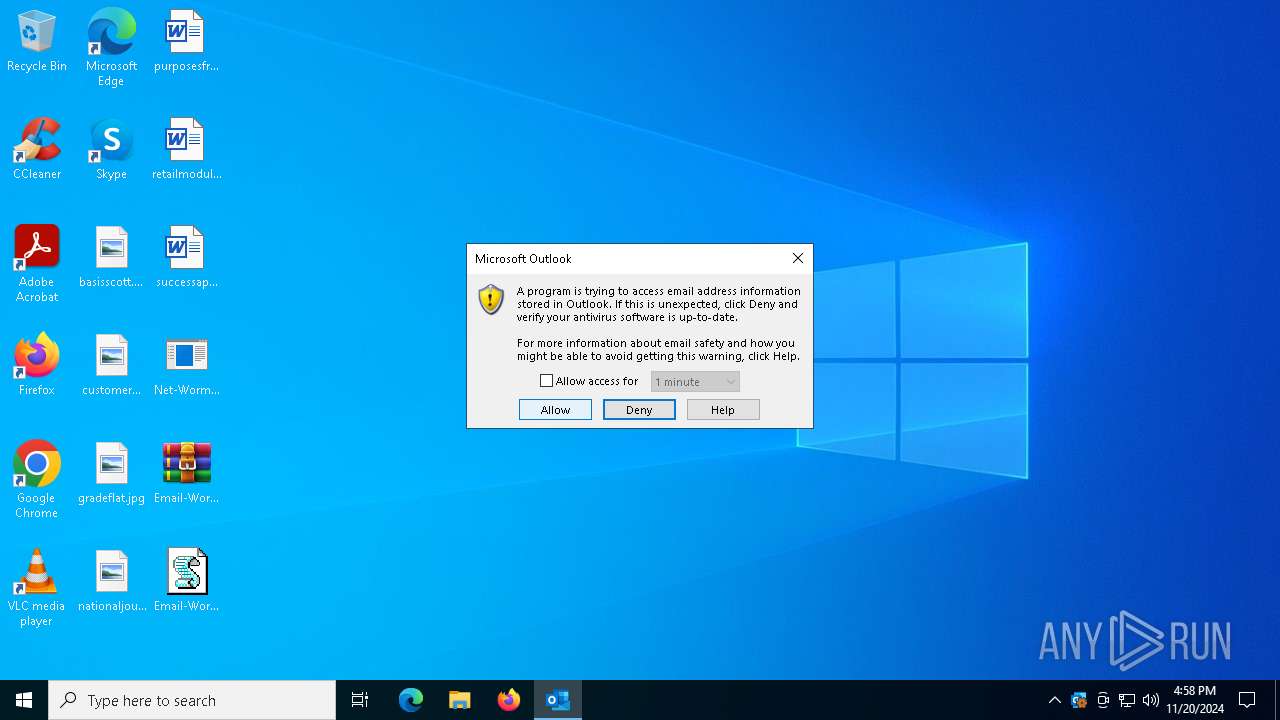
SMBSCAN has been detected (SURICATA)
- Net-Worm.Sasser.exe (PID: 6604)
Attempt to connect to SMB server
- Net-Worm.Sasser.exe (PID: 6604)
Attempting to scan the network
- Net-Worm.Sasser.exe (PID: 6604)
SUSPICIOUS
Potential Corporate Privacy Violation
- Net-Worm.Sasser.exe (PID: 6604)
Executable content was dropped or overwritten
- Net-Worm.Sasser.exe (PID: 4872)
Application launched itself
- Net-Worm.Sasser.exe (PID: 6604)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4140)
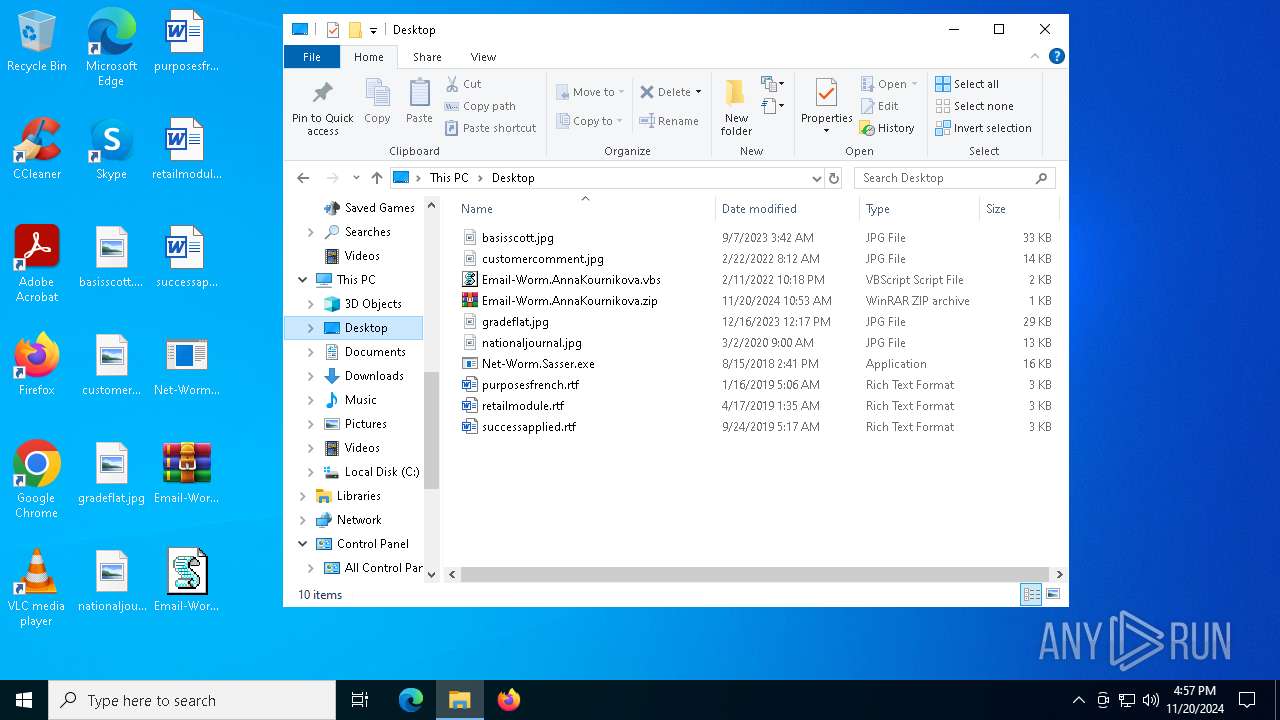
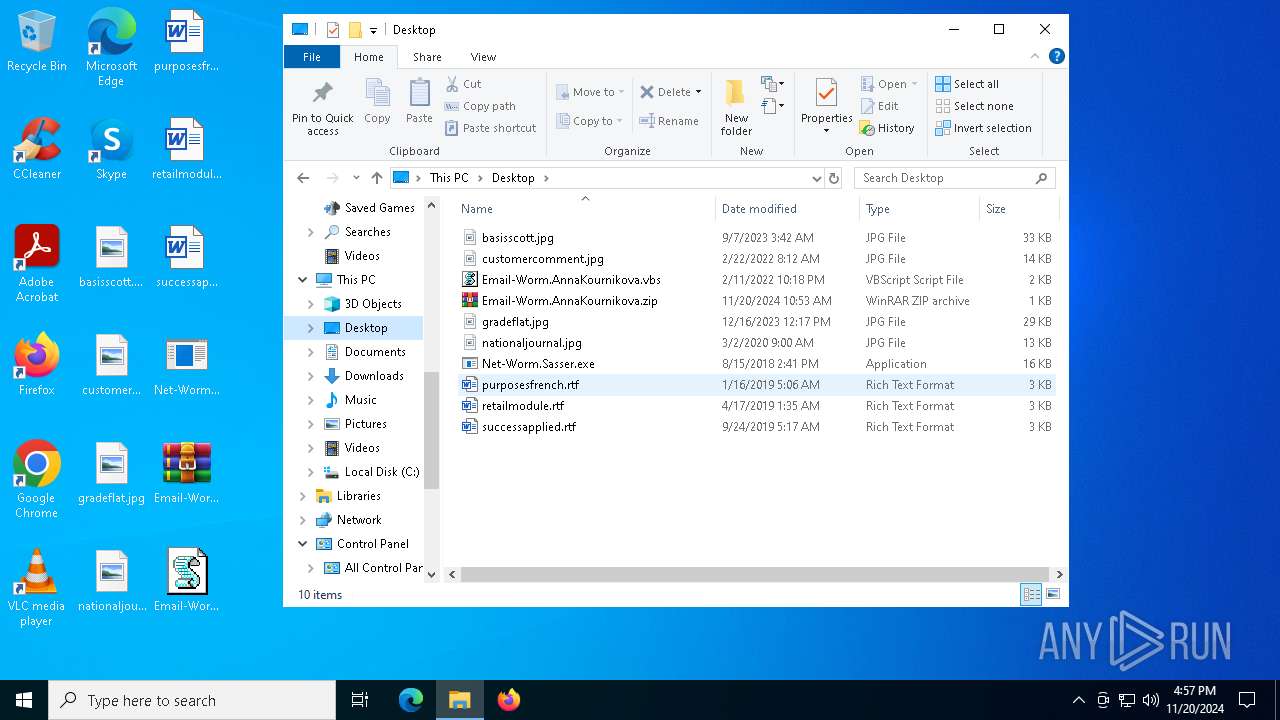
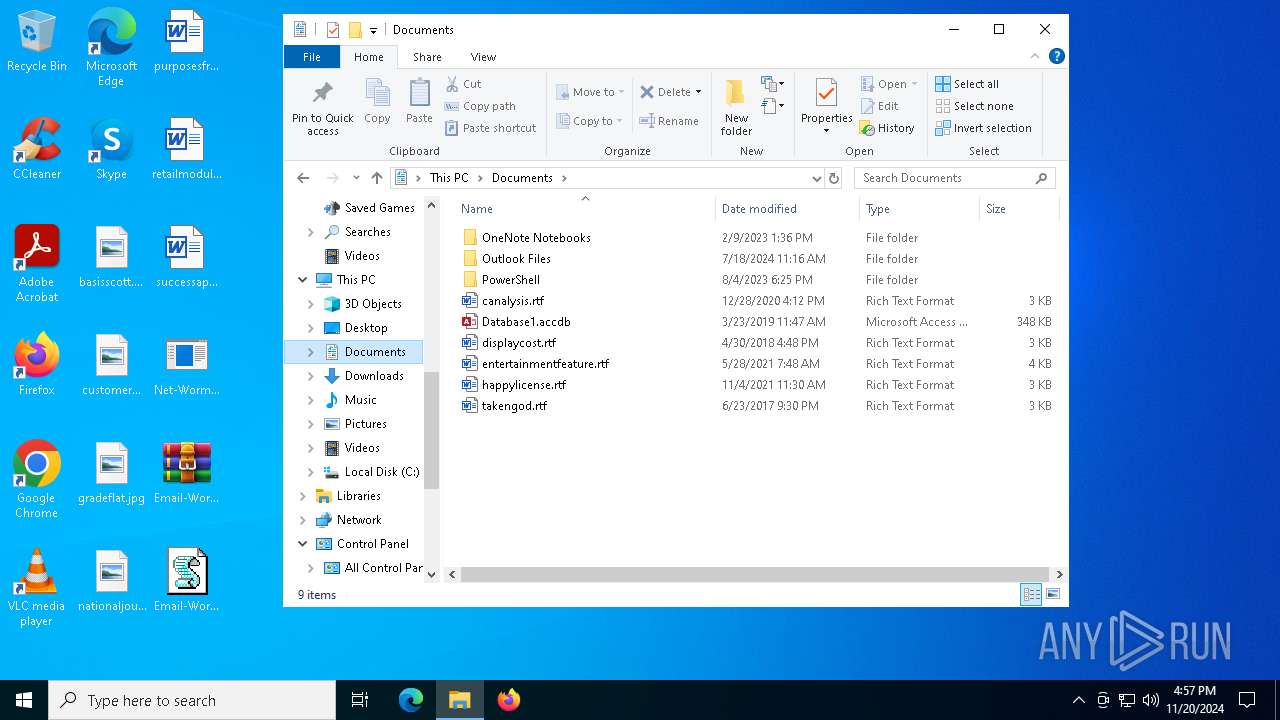
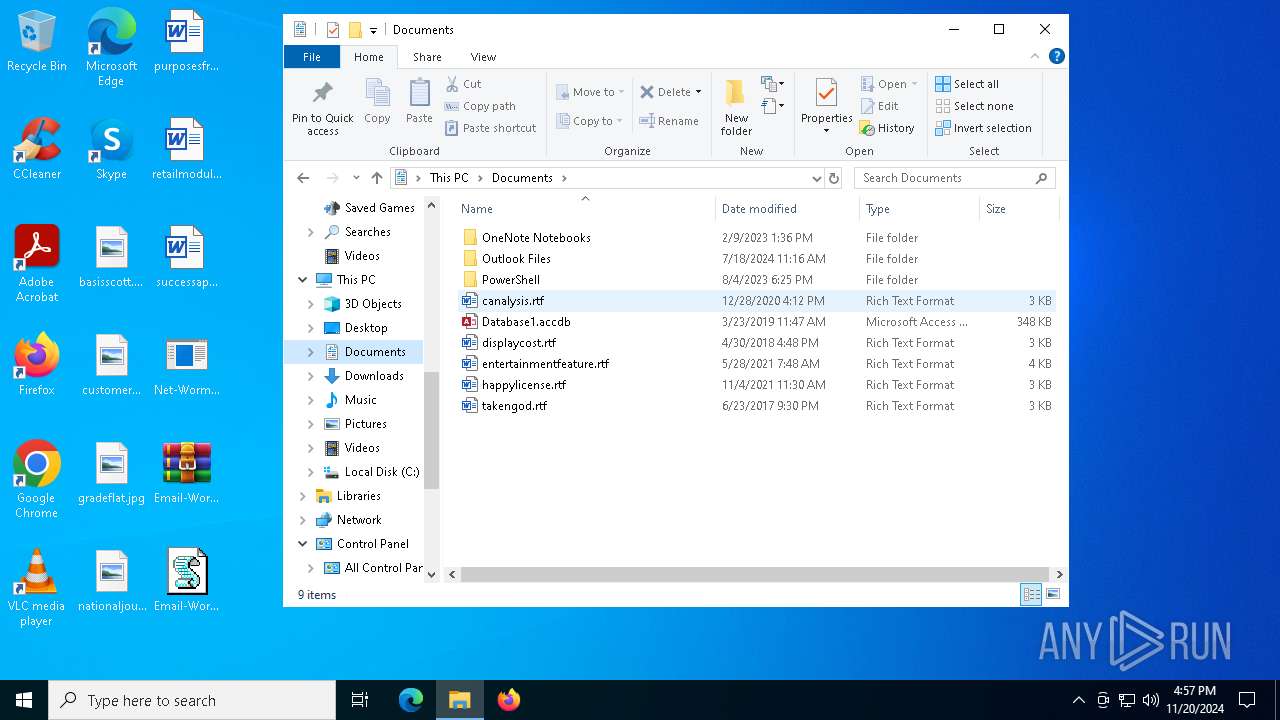
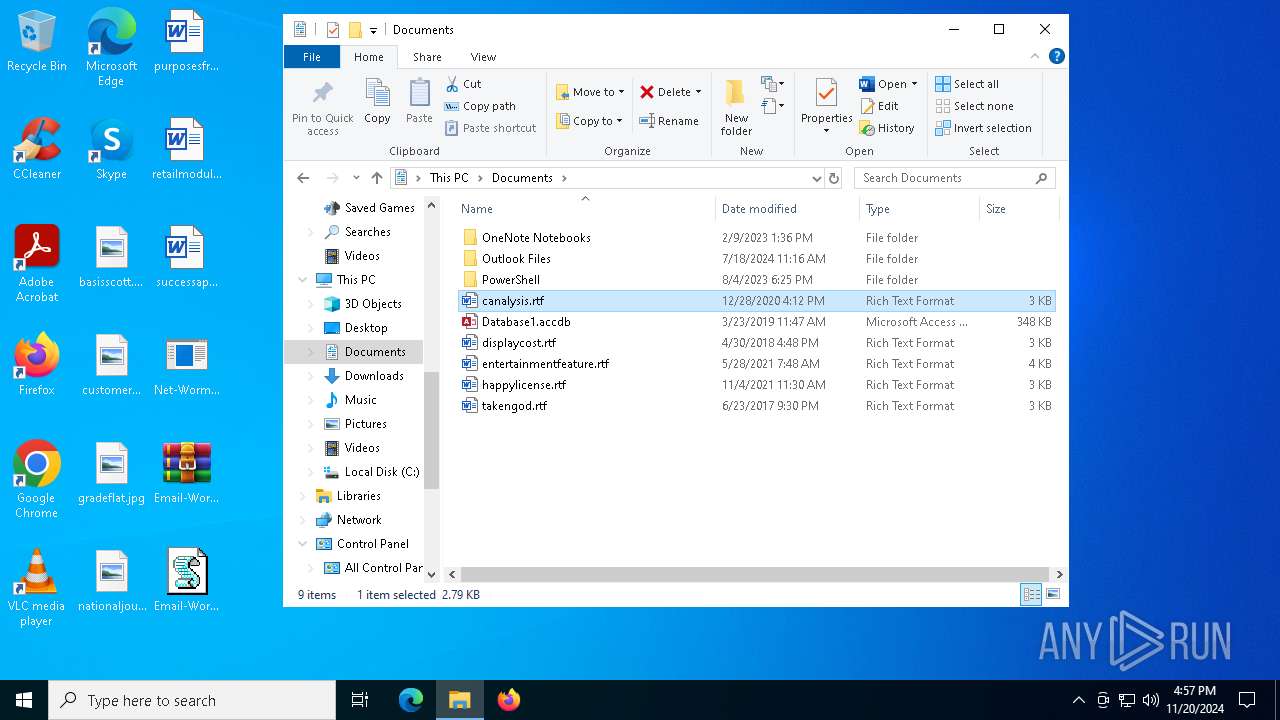
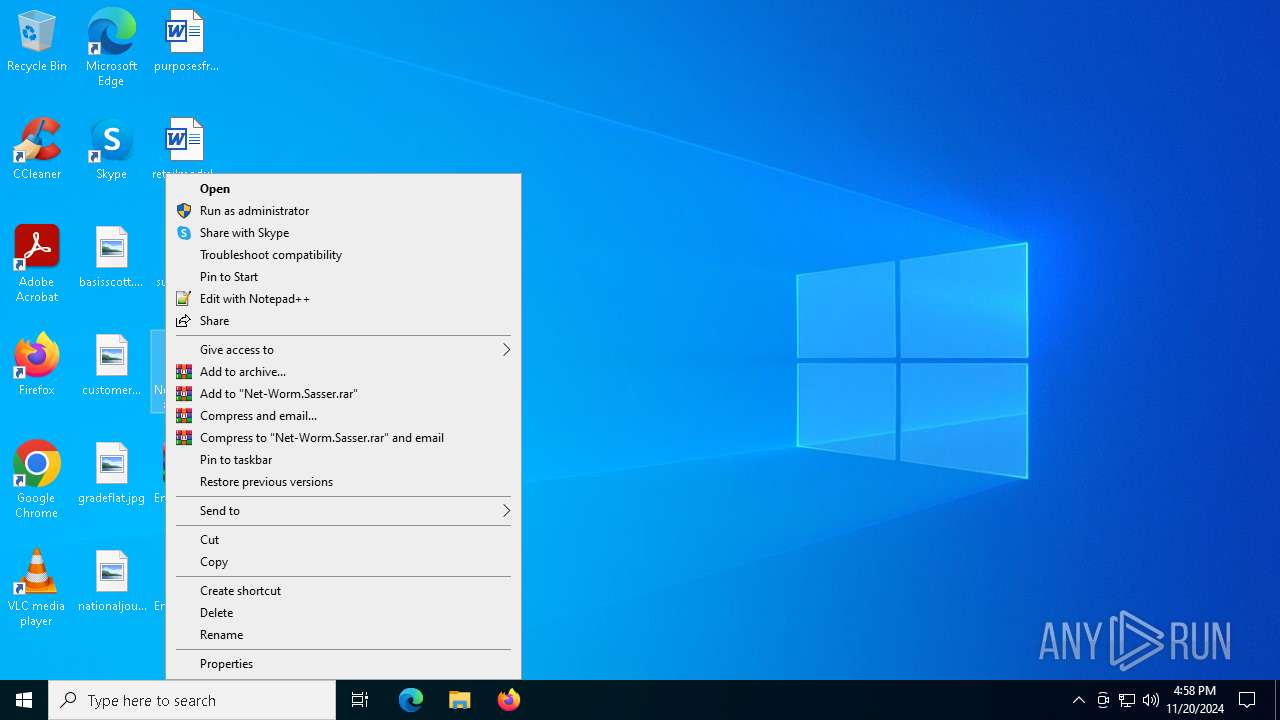
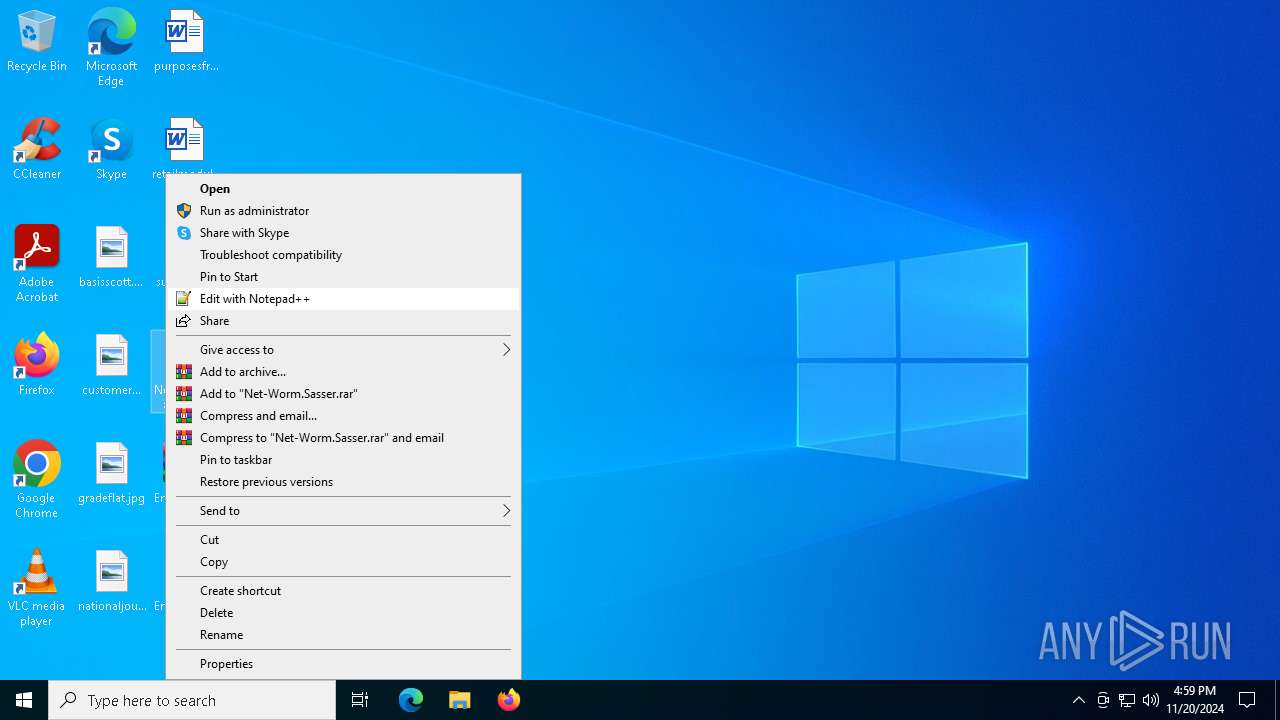
Manual execution by a user
- WinRAR.exe (PID: 6536)
- Net-Worm.Sasser.exe (PID: 6256)
- wscript.exe (PID: 5560)
- Net-Worm.Sasser.exe (PID: 6604)
- Net-Worm.Sasser.exe (PID: 6188)
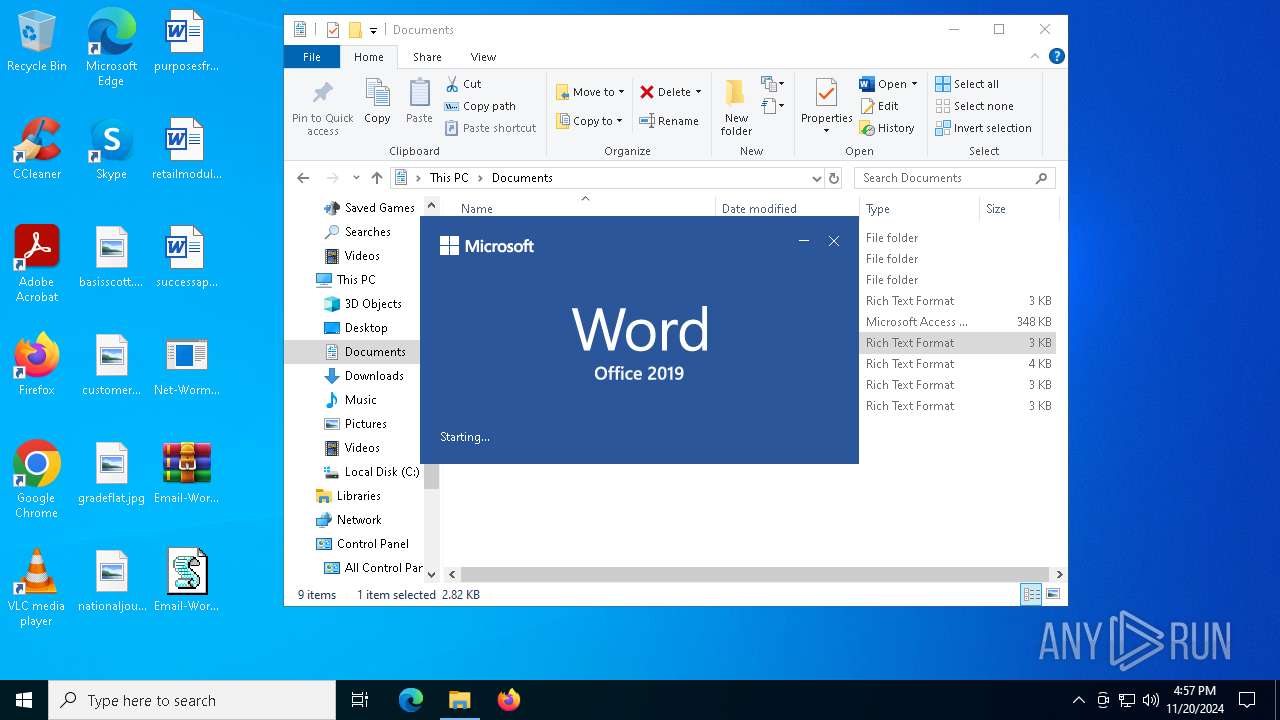
- WINWORD.EXE (PID: 2284)
- Net-Worm.Sasser.exe (PID: 4872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2018:08:15 18:41:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 14458 |
| ZipUncompressedSize: | 15872 |
| ZipFileName: | Net-Worm.Sasser.exe |
Total processes
155
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1932 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
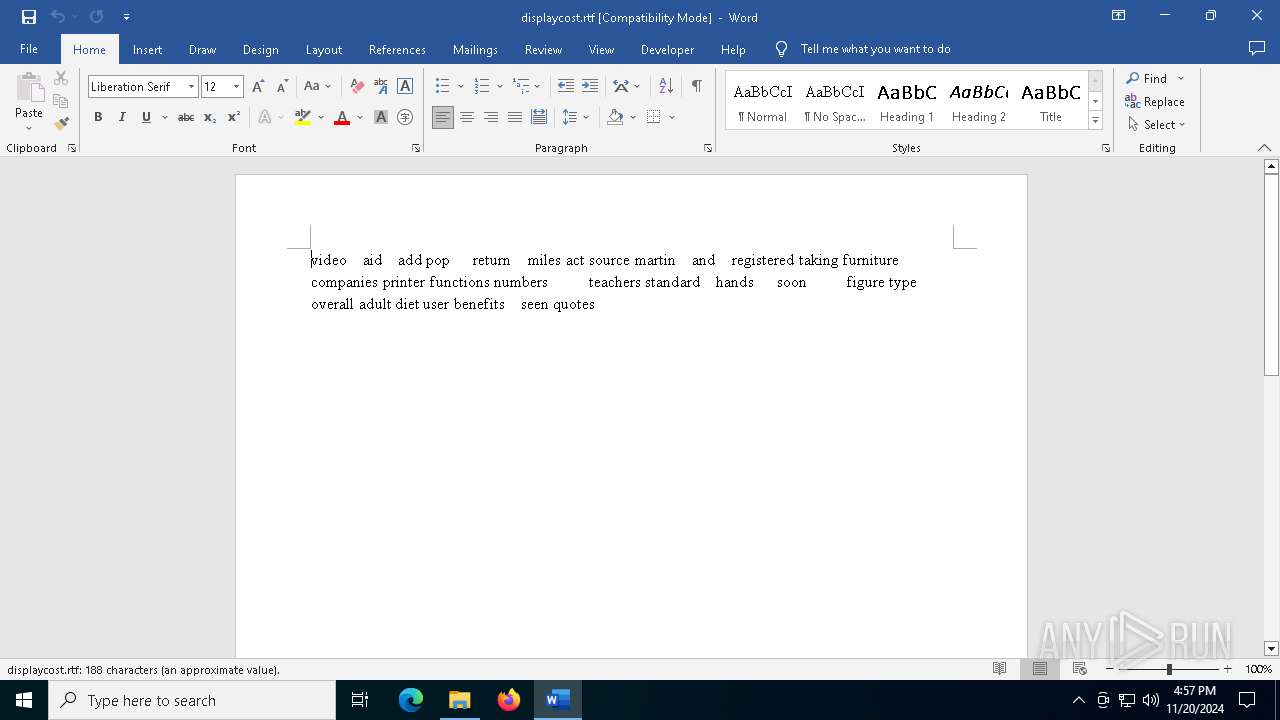
| 2284 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Documents\displaycost.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
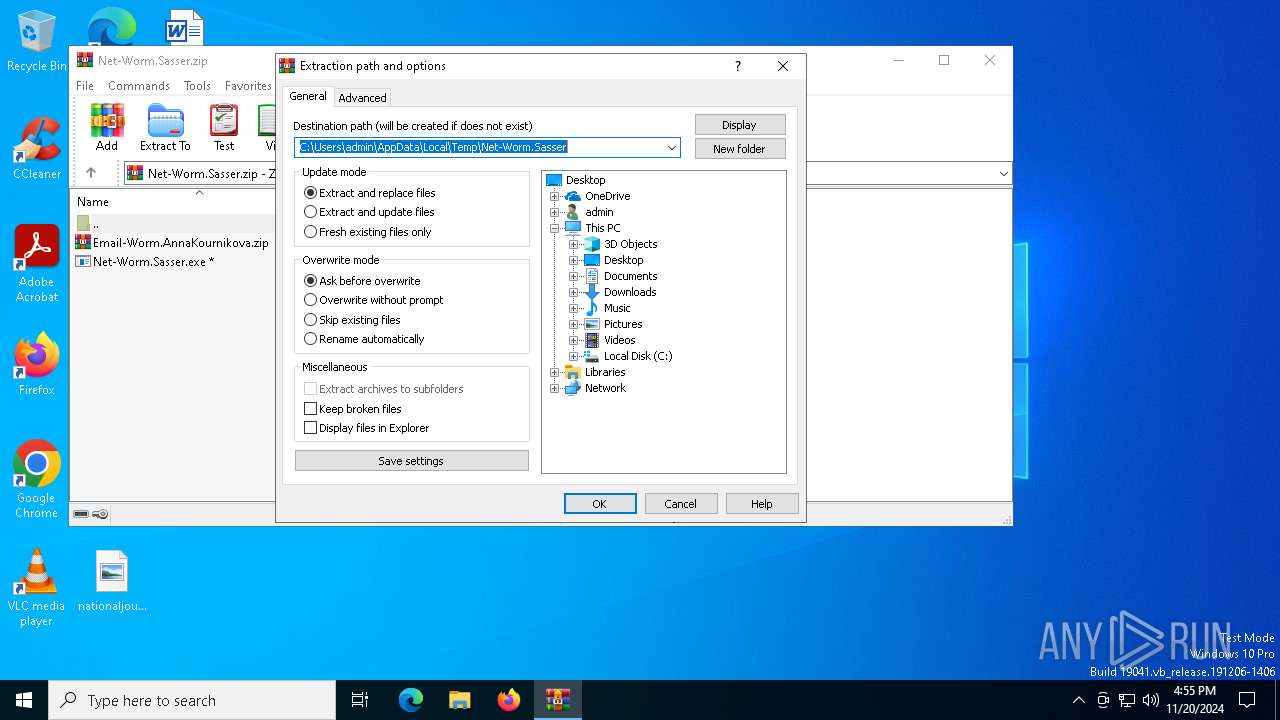
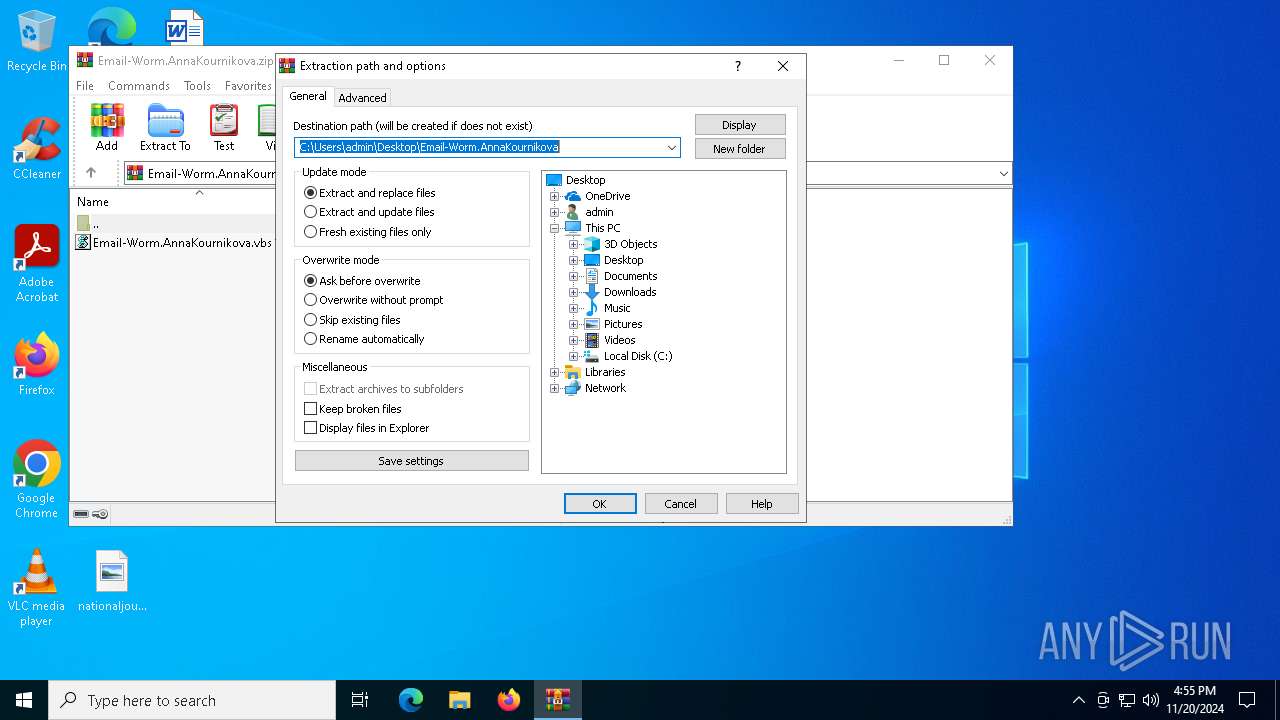
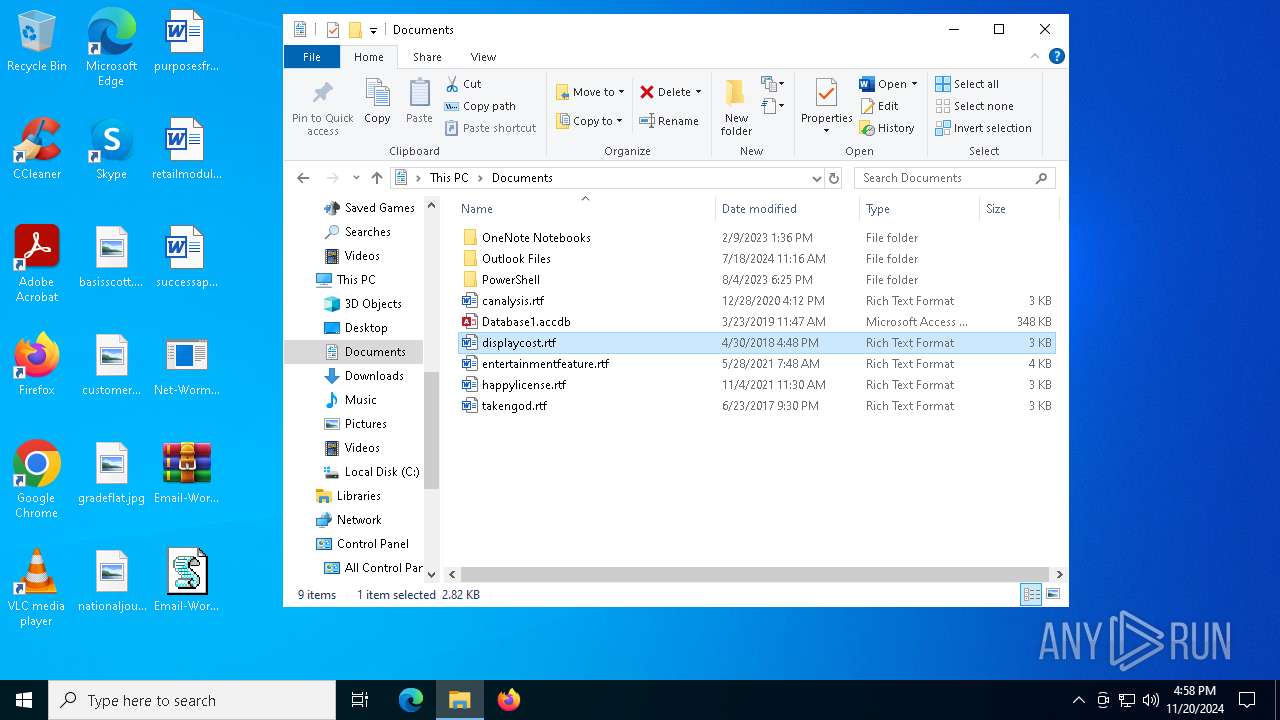
| 4140 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Net-Worm.Sasser.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4872 | "C:\Users\admin\Desktop\Net-Worm.Sasser.exe" | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 | |||||||||||||||
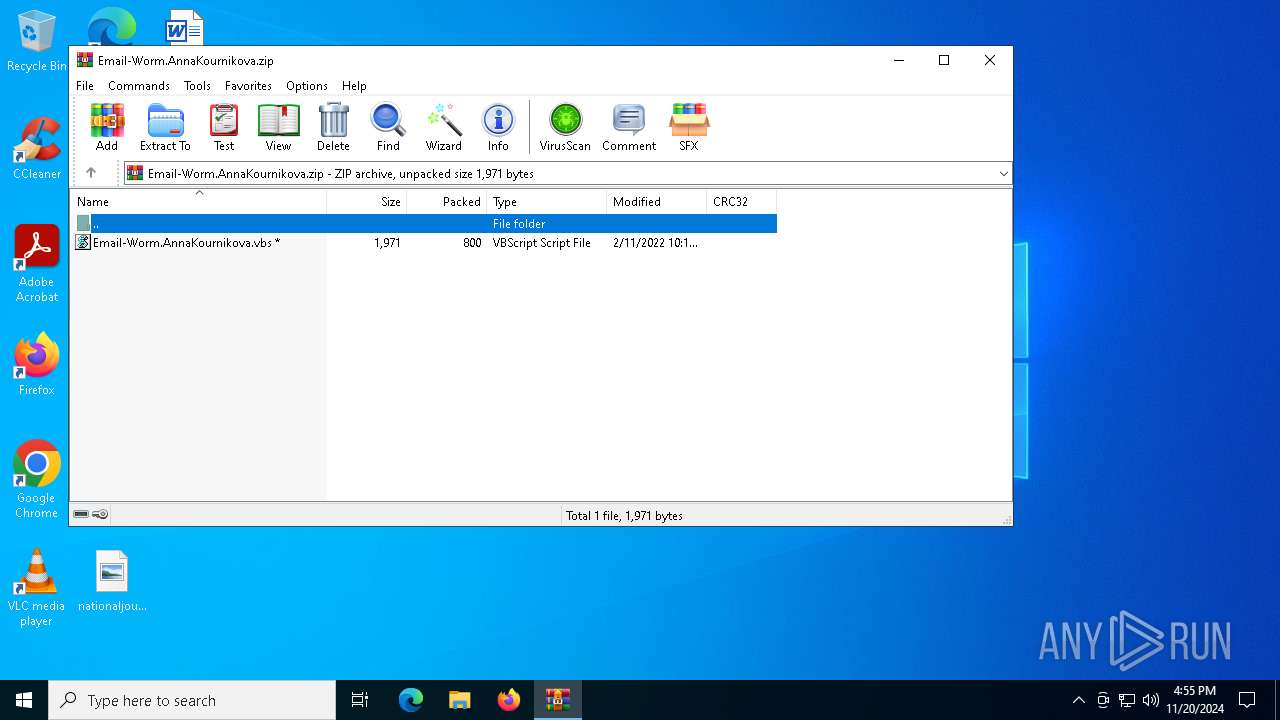
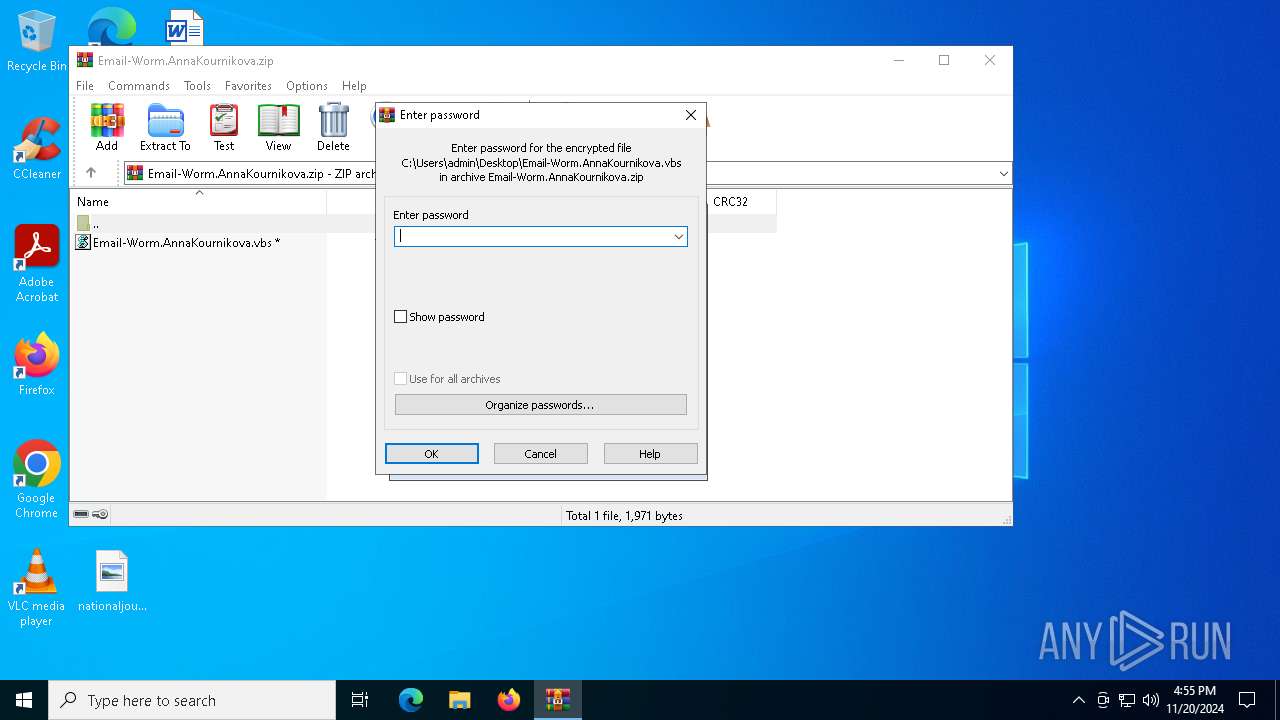
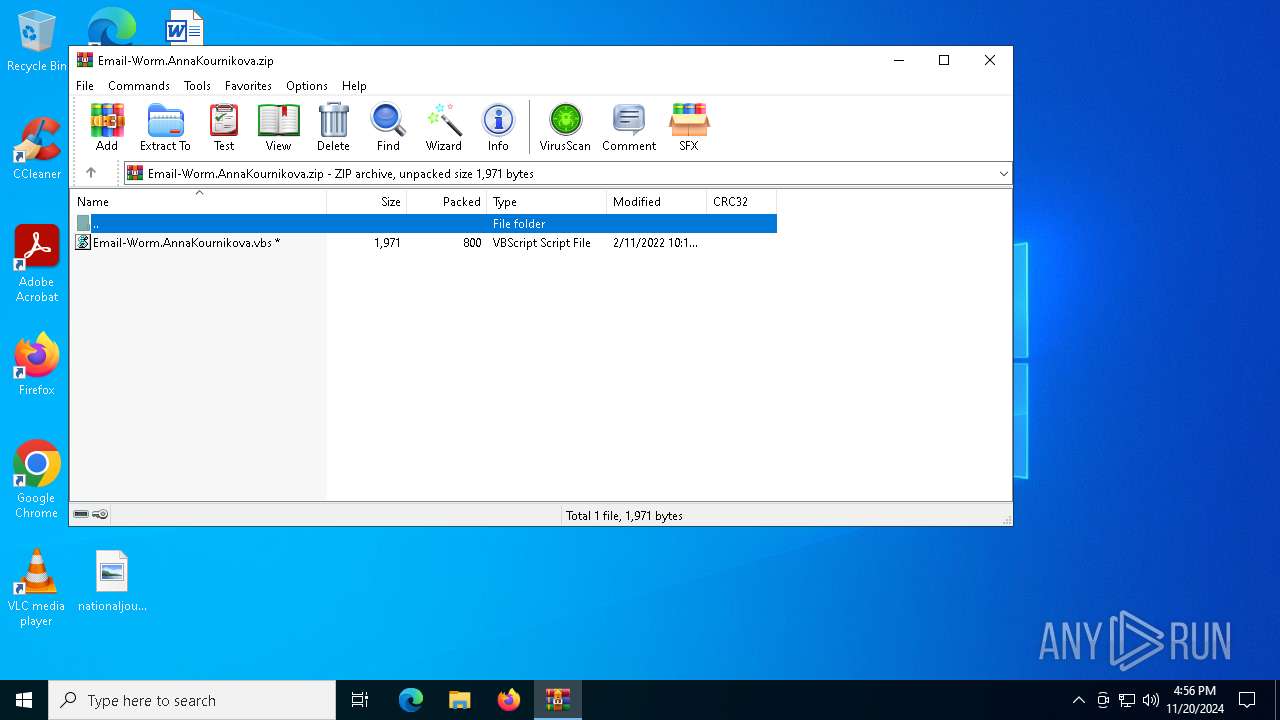
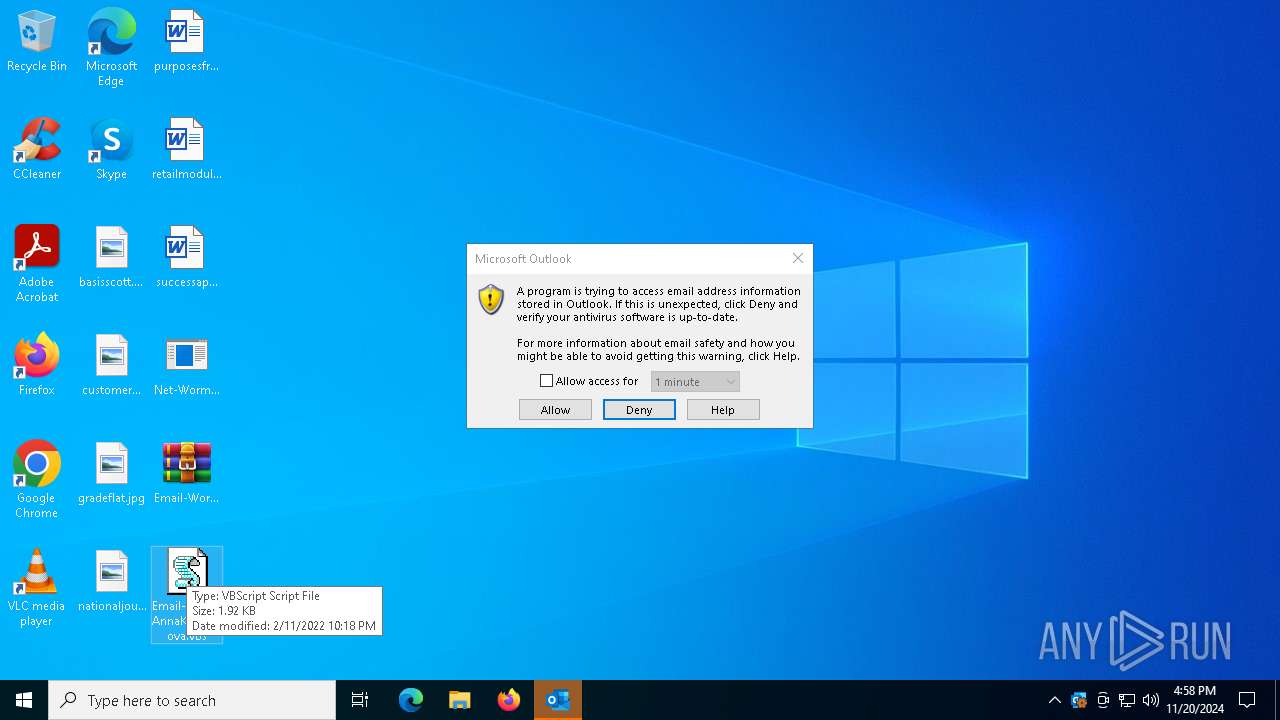
| 5560 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\Email-Worm.AnnaKournikova.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5752 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe 127.5.74.32 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | — | Net-Worm.Sasser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 5856 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe 127.16.176.84 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | — | Net-Worm.Sasser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6044 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe 192.227.219.82 | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | Net-Worm.Sasser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6188 | "C:\Users\admin\Desktop\Net-Worm.Sasser.exe" | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 6256 | "C:\Users\admin\Desktop\Net-Worm.Sasser.exe" | C:\Users\admin\Desktop\Net-Worm.Sasser.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
19 443
Read events
18 783
Write events
593
Delete events
67
Modification events
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Net-Worm.Sasser.zip | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (4140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
2
Suspicious files
35
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:60C30943A91596E612C7D0DB6007954D | SHA256:2EFB42139B1AE14EB3B61677429E4ABEB338EB33509B4AE56B09A3B9F53816C6 | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\PreviewFont\flat_officeFontsPreview_4_40.ttf | pi2 | |
MD5:4296A064B917926682E7EED650D4A745 | SHA256:E04E41C74D6C78213BA1588BACEE64B42C0EDECE85224C474A714F39960D8083 | |||
| 4140 | WinRAR.exe | C:\Users\admin\Desktop\Email-Worm.AnnaKournikova.zip | compressed | |
MD5:905DD32D9EF165CA25E97E139909C8EE | SHA256:1D537A4A7211D6FE2476BBCEDE25667D333C0CD2B1E8DEFF8317000993E8133F | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:9C812FF6EE1293E11302EBC0F12DF480 | SHA256:D29A9E527589D62354DA321D6966EC192522CA6371433EC14B7A6C93253EA53A | |||
| 2284 | WINWORD.EXE | C:\Users\admin\Documents\~$splaycost.rtf | abr | |
MD5:9AFECDBC75421E2900194BE126F30B1A | SHA256:82A6B0537ED02EB87013AC44A52A35AA4D28F92B4EA8548E2D44ED9EB00F04FC | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\displaycost.rtf.LNK | binary | |
MD5:D362DC9E99B6AA928353307FDB642DDE | SHA256:41D3B364C5B4014B9927AD06F5A0923DDB8C6A83438F4C7B1A66BD2D7875581F | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:05C386DDE8AC677E987B3D3020AFD86B | SHA256:8BF463114A2791D1B0D6A4726E0DE87831B537CD06FCB3C3E4A0761FC5EF3000 | |||
| 2284 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:000B925A9FDE721E8652A9599BCAD4AF | SHA256:156E225ABFC967A2E8E35DB88550FFB15B77B1DB003FCBD3D8E2D595370BE1F3 | |||
| 6536 | WinRAR.exe | C:\Users\admin\Desktop\Email-Worm.AnnaKournikova.vbs | text | |
MD5:A312DC3504108FCFD1B1AE5D32B3E1FE | SHA256:2C7964292FA38B6EC52F6C2D8197EBC119392FBC2254243125D133A3AE8B9A84 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
1 529
DNS requests
34
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5124 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2284 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2284 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6380 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6380 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5492 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4932 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.16.110.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
6604 | Net-Worm.Sasser.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|