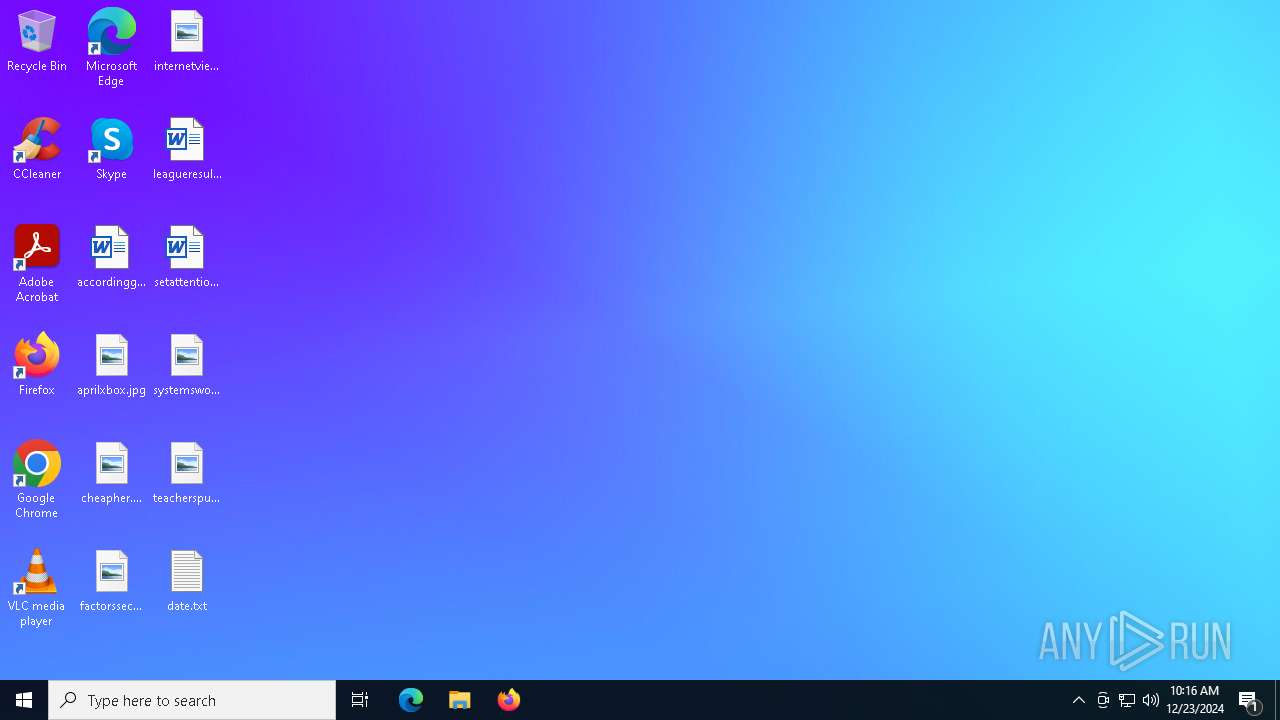
| File name: | No Escape.exe |
| Full analysis: | https://app.any.run/tasks/aaaaa007-6fc8-4bff-ac4e-a824bf2d73b0 |
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2024, 10:15:19 |
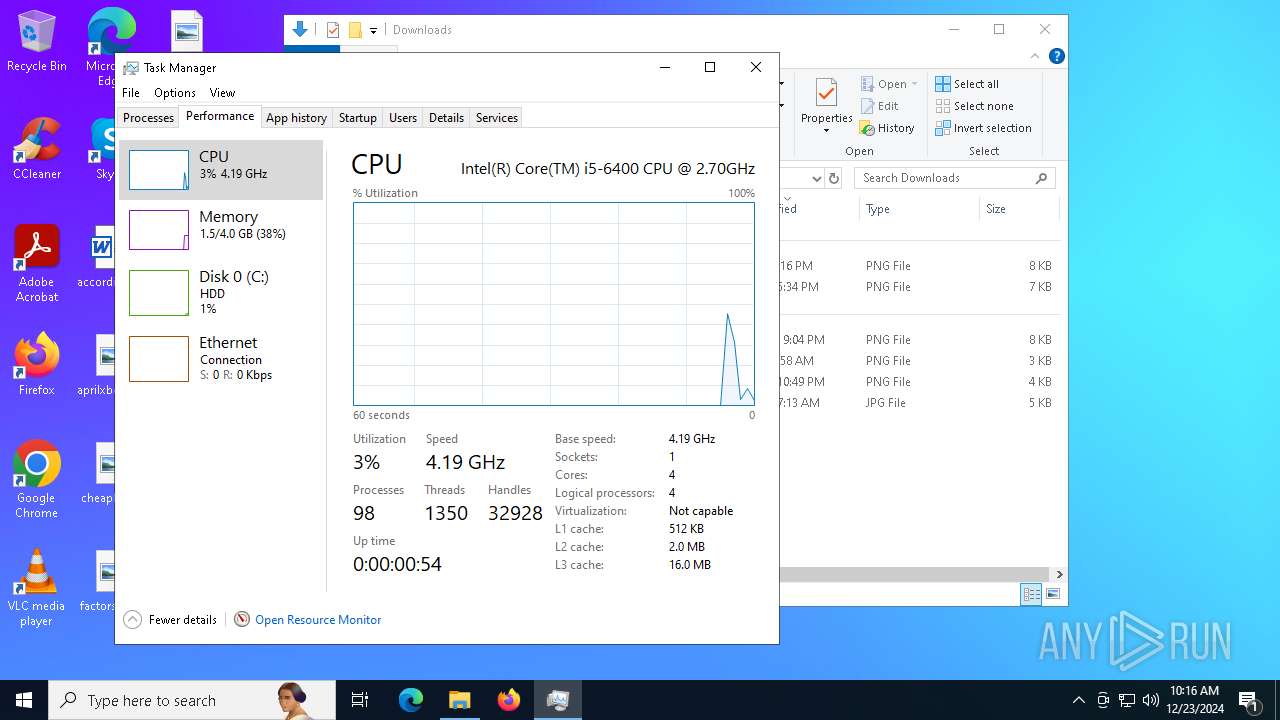
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 2782877418B44509FD306FD9AFE43E39 |
| SHA1: | B0C18BDF782CA9C4FA41074F05458CE8E0F3961B |
| SHA256: | 56D612E014504C96BB92429C31EB93F40938015D422B35765912AC4E6BD3755B |
| SSDEEP: | 24576:OeTrmlZGPL7NV9+VitFsQUxY8BGOdQSqZ:hT6KDrmIFsBJBG4XqZ |
MALICIOUS
Changes the login/logoff helper path in the registry
- reg.exe (PID: 6912)
UAC/LUA settings modification
- reg.exe (PID: 6972)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 7044)
- cmd.exe (PID: 6724)
SUSPICIOUS
Executing commands from a ".bat" file
- wscript.exe (PID: 6320)
Executable content was dropped or overwritten
- No Escape.exe (PID: 6268)
- cmd.exe (PID: 6724)
Reads security settings of Internet Explorer
- No Escape.exe (PID: 6268)
- ShellExperienceHost.exe (PID: 5836)
Runs WScript without displaying logo
- wscript.exe (PID: 6320)
- wscript.exe (PID: 4852)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6320)
The process executes VB scripts
- No Escape.exe (PID: 6268)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6320)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6724)
Creates file in the systems drive root
- attrib.exe (PID: 6820)
- attrib.exe (PID: 6844)
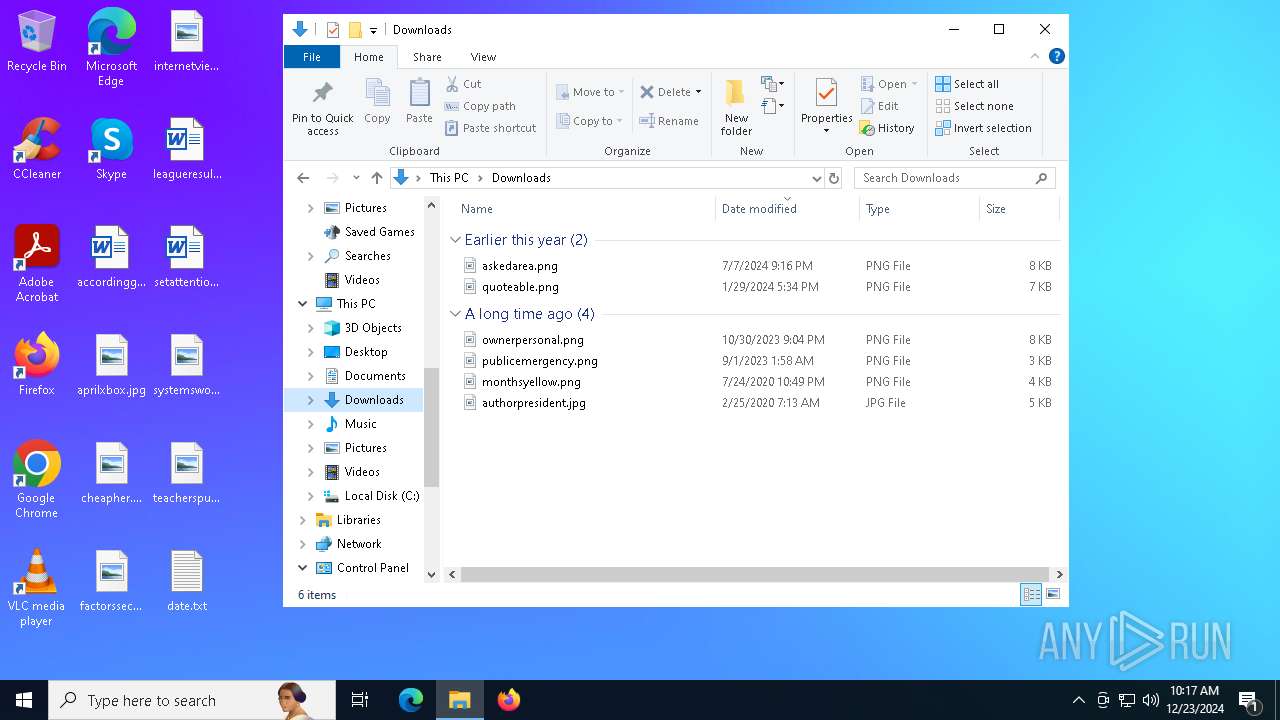
Changes the desktop background image
- reg.exe (PID: 6932)
- reg.exe (PID: 6952)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6724)
The system shut down or reboot
- cmd.exe (PID: 6724)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4164)
INFO
The sample compiled with english language support
- No Escape.exe (PID: 6268)
Checks supported languages
- No Escape.exe (PID: 6268)
- PLUGScheduler.exe (PID: 4164)
- ShellExperienceHost.exe (PID: 5836)
Reads security settings of Internet Explorer
- wscript.exe (PID: 6320)
- wscript.exe (PID: 4852)
Reads the computer name
- No Escape.exe (PID: 6268)
- ShellExperienceHost.exe (PID: 5836)
- PLUGScheduler.exe (PID: 4164)
Process checks computer location settings
- No Escape.exe (PID: 6268)
Reads the time zone
- net1.exe (PID: 7072)
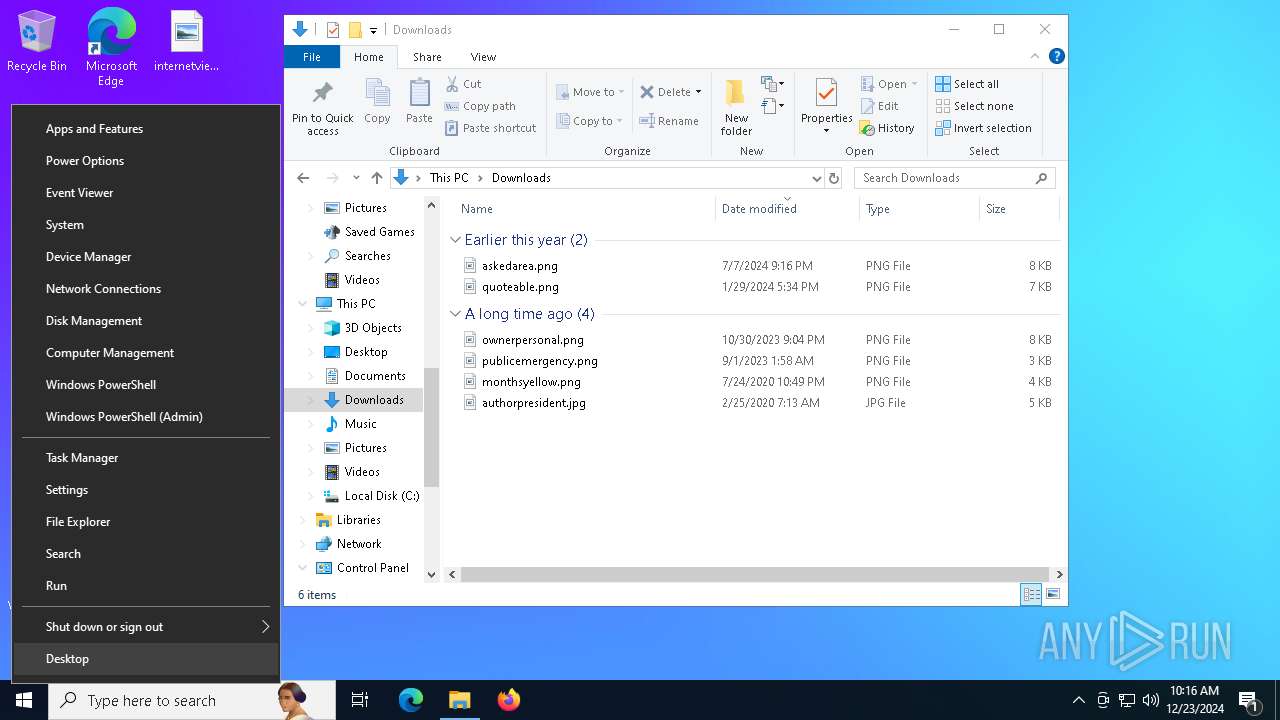
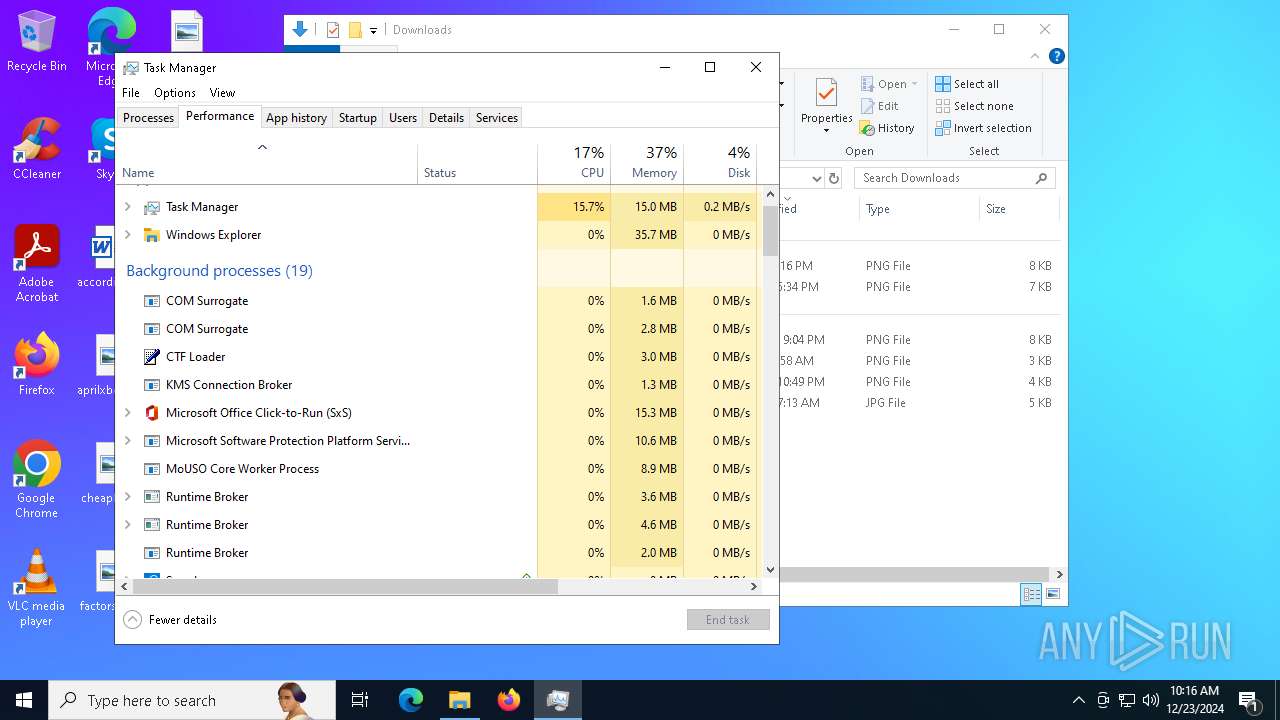
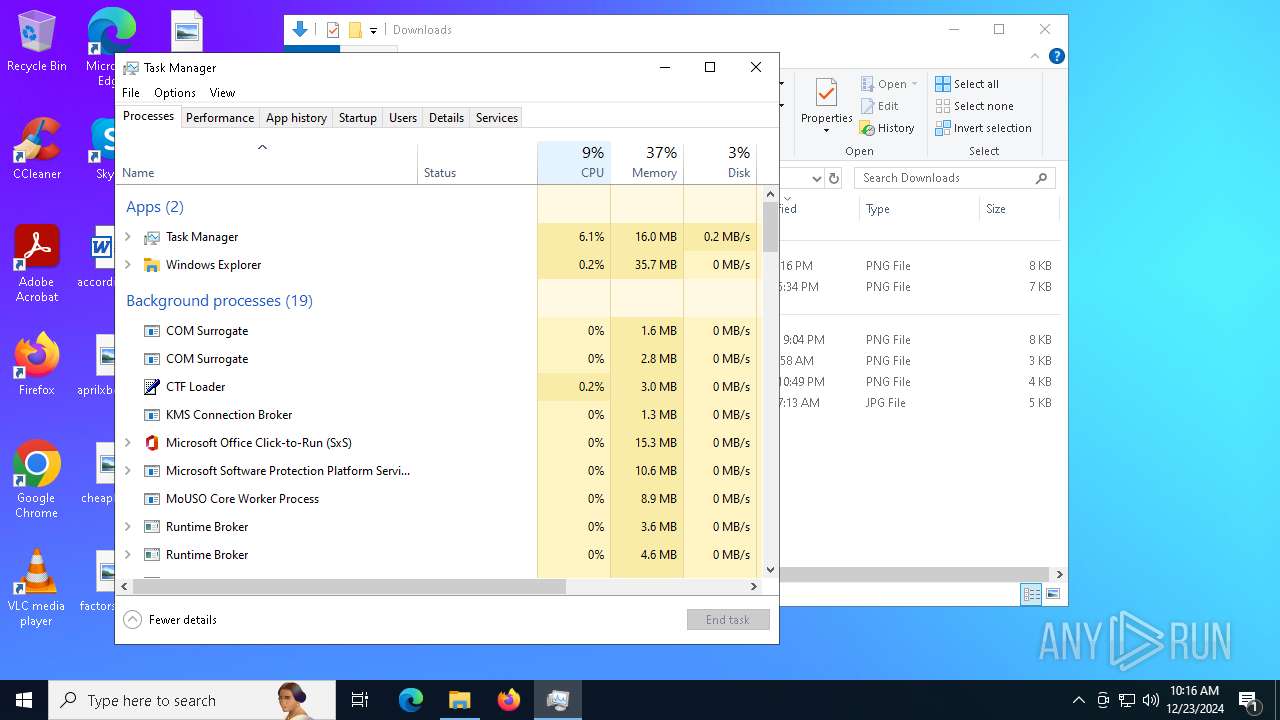
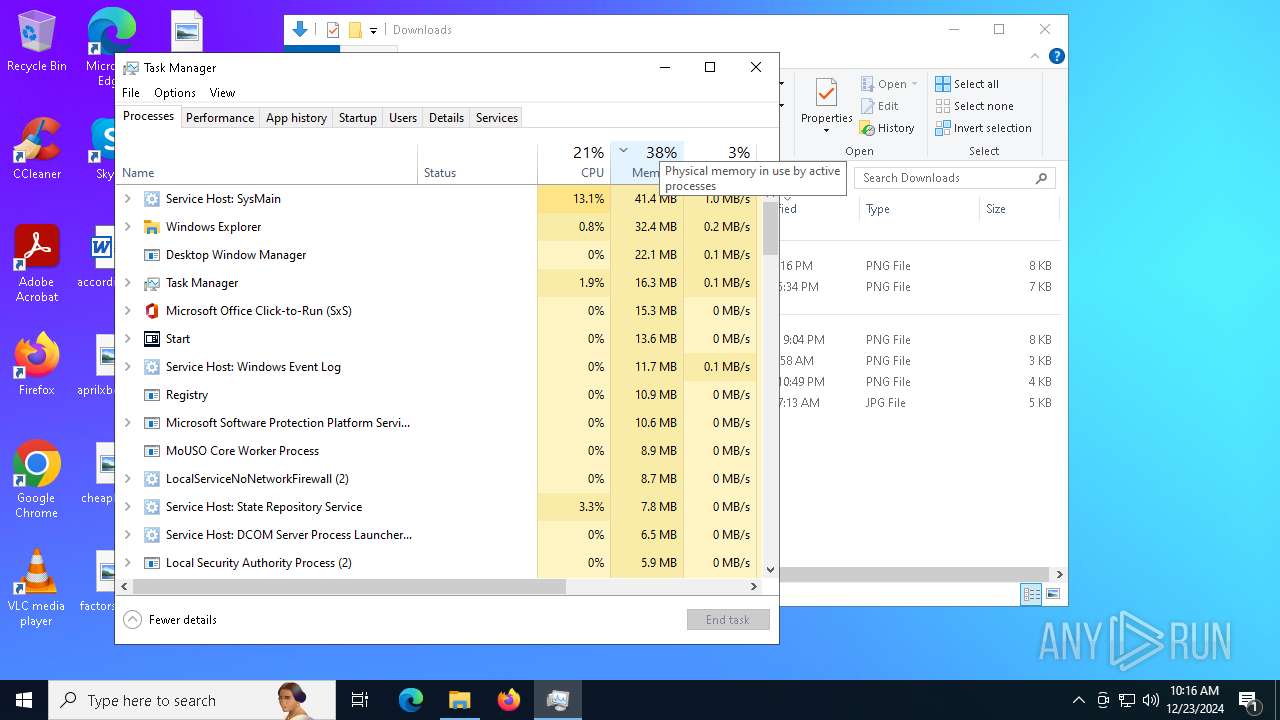
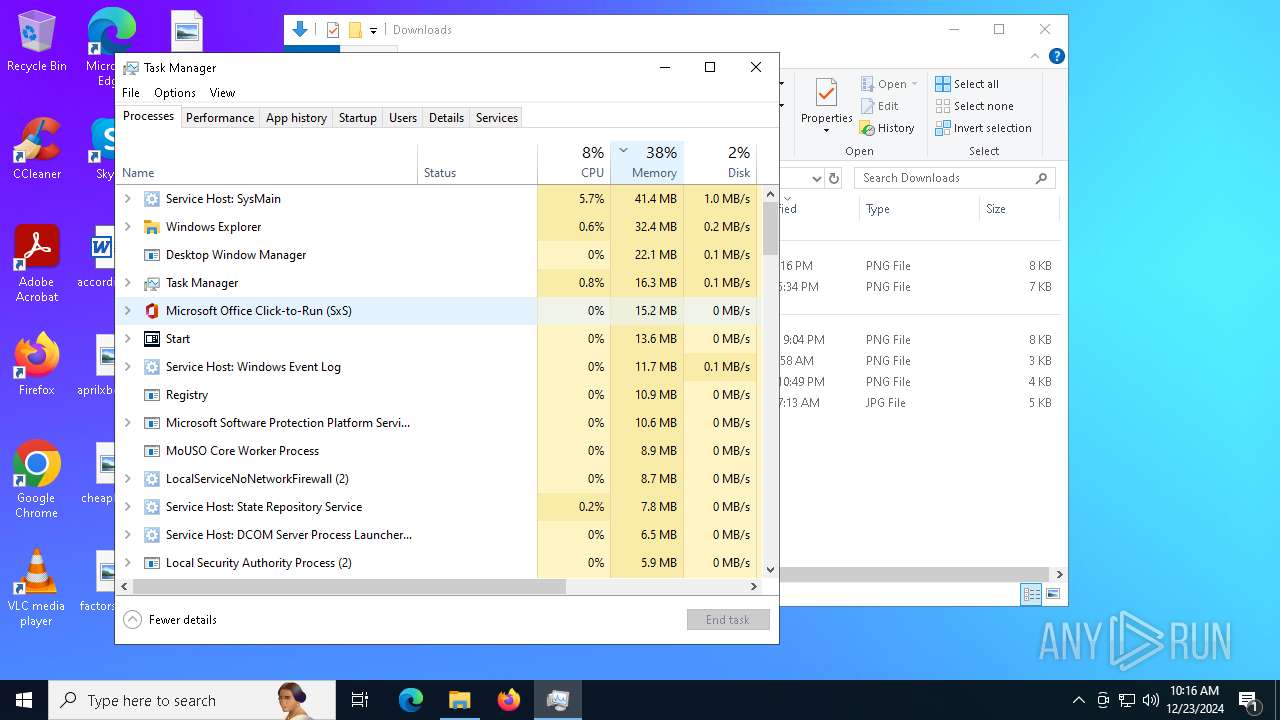
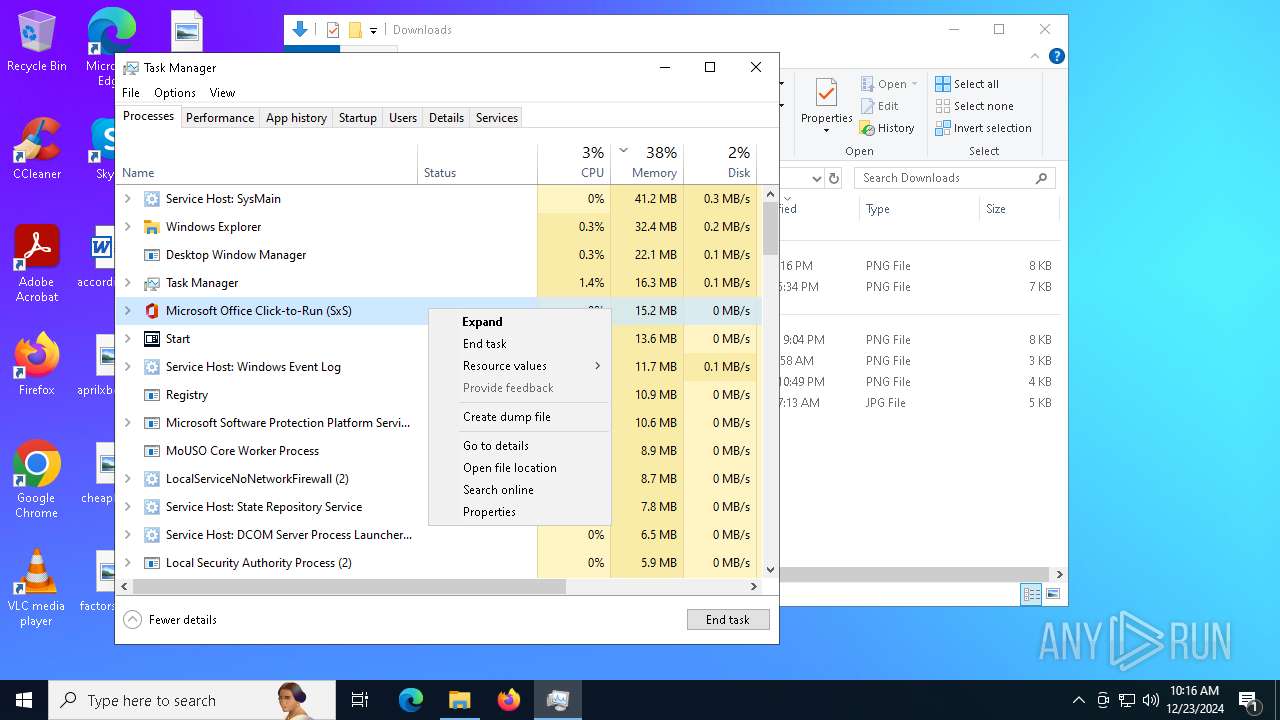
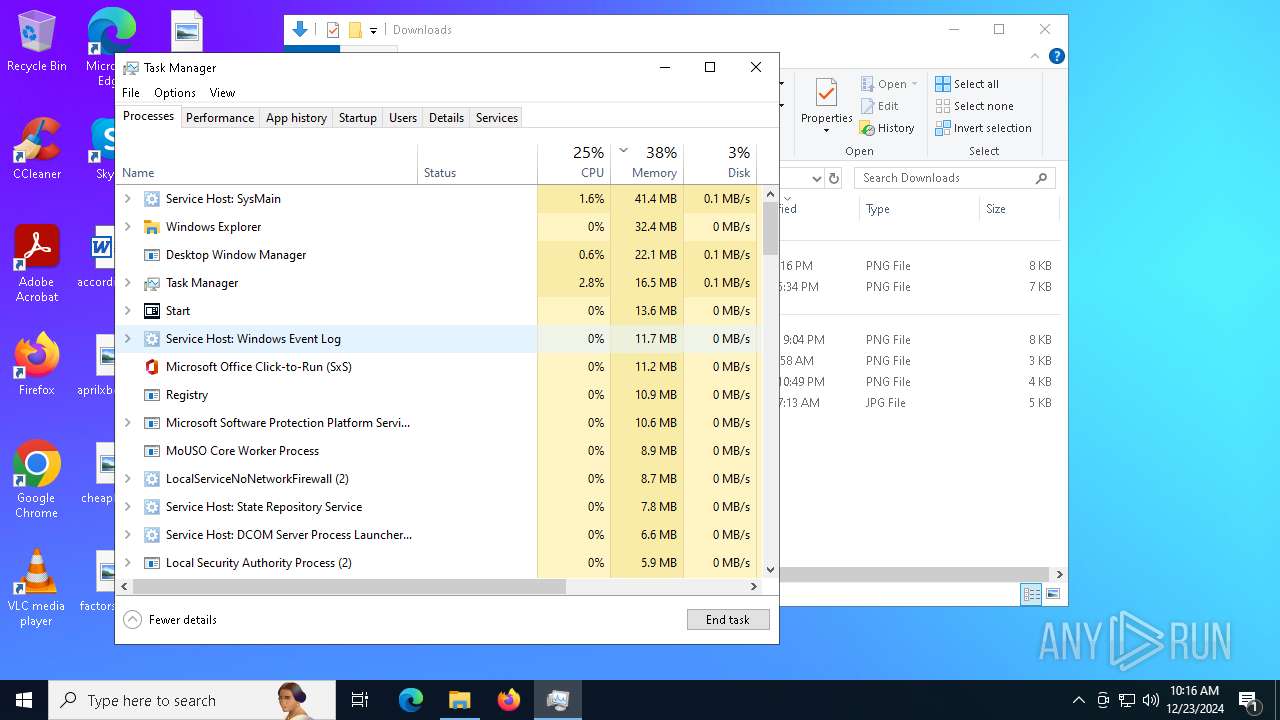
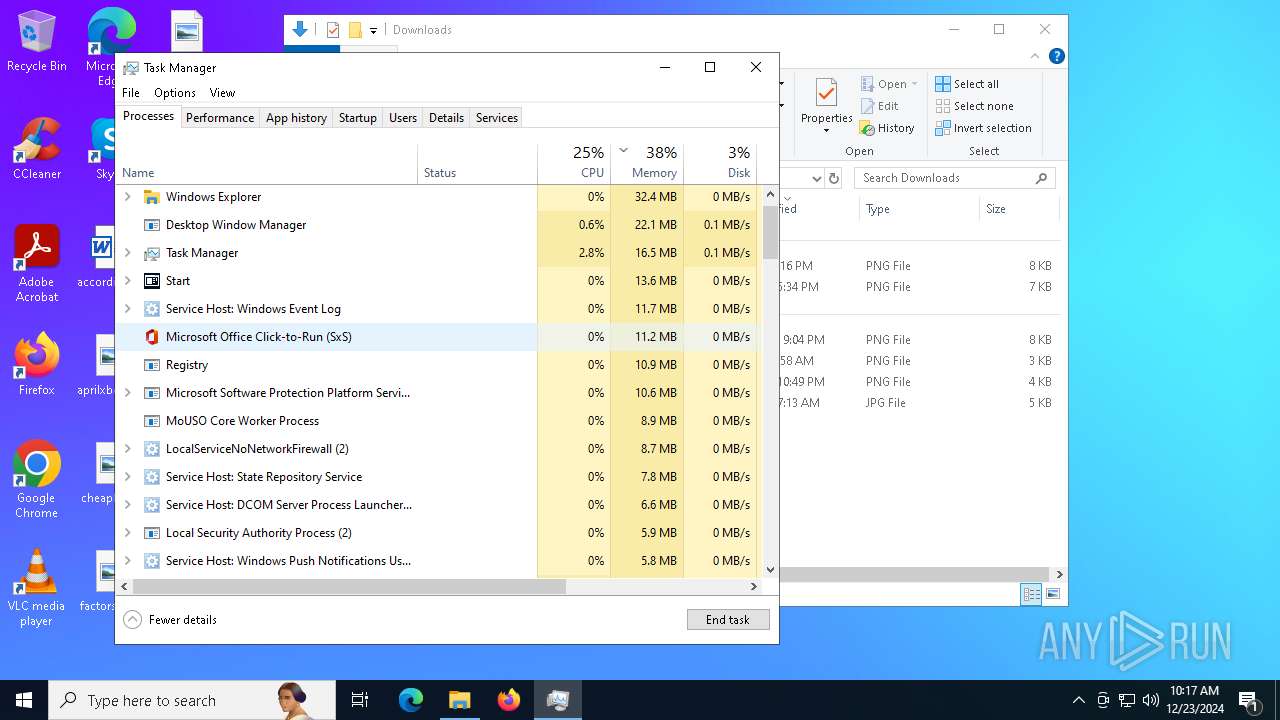
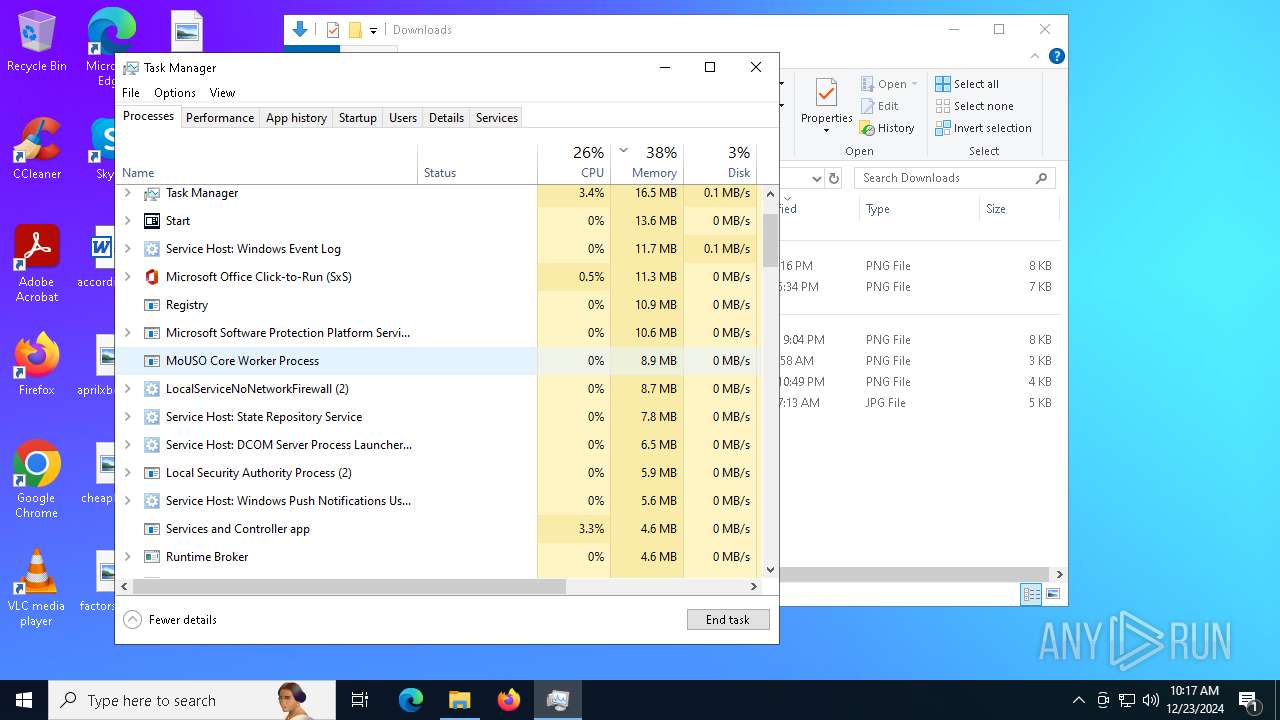
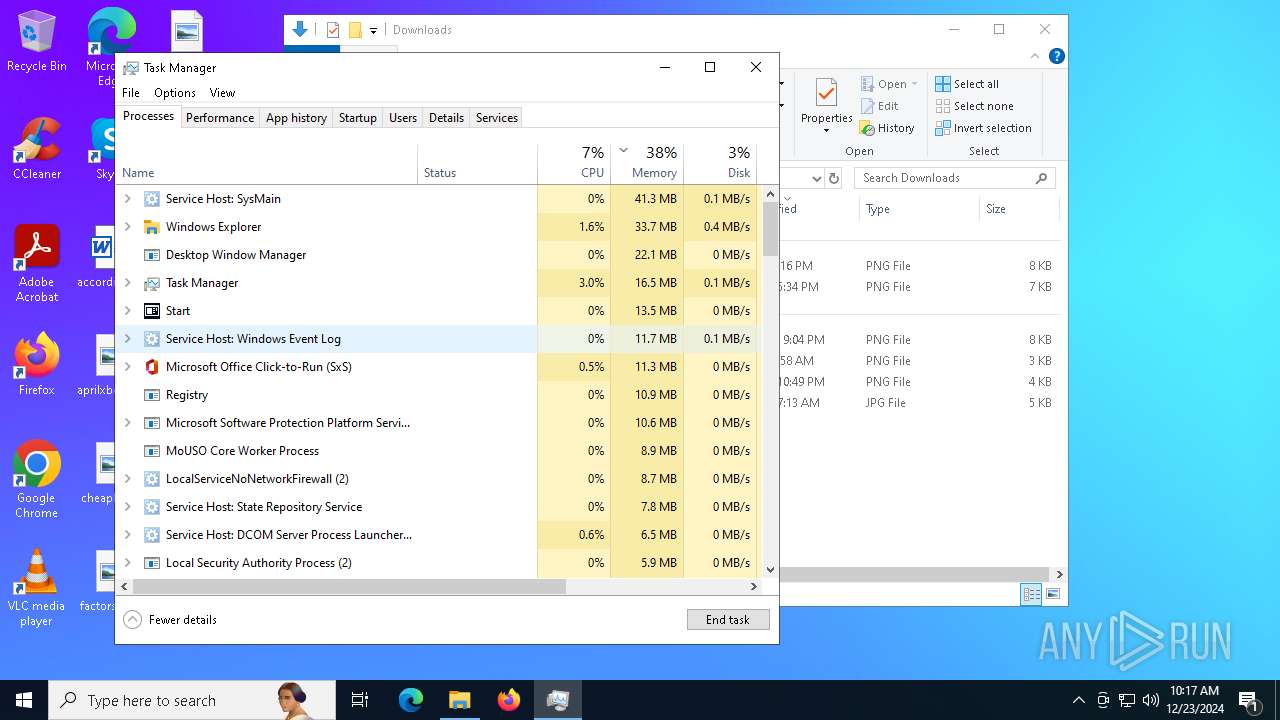
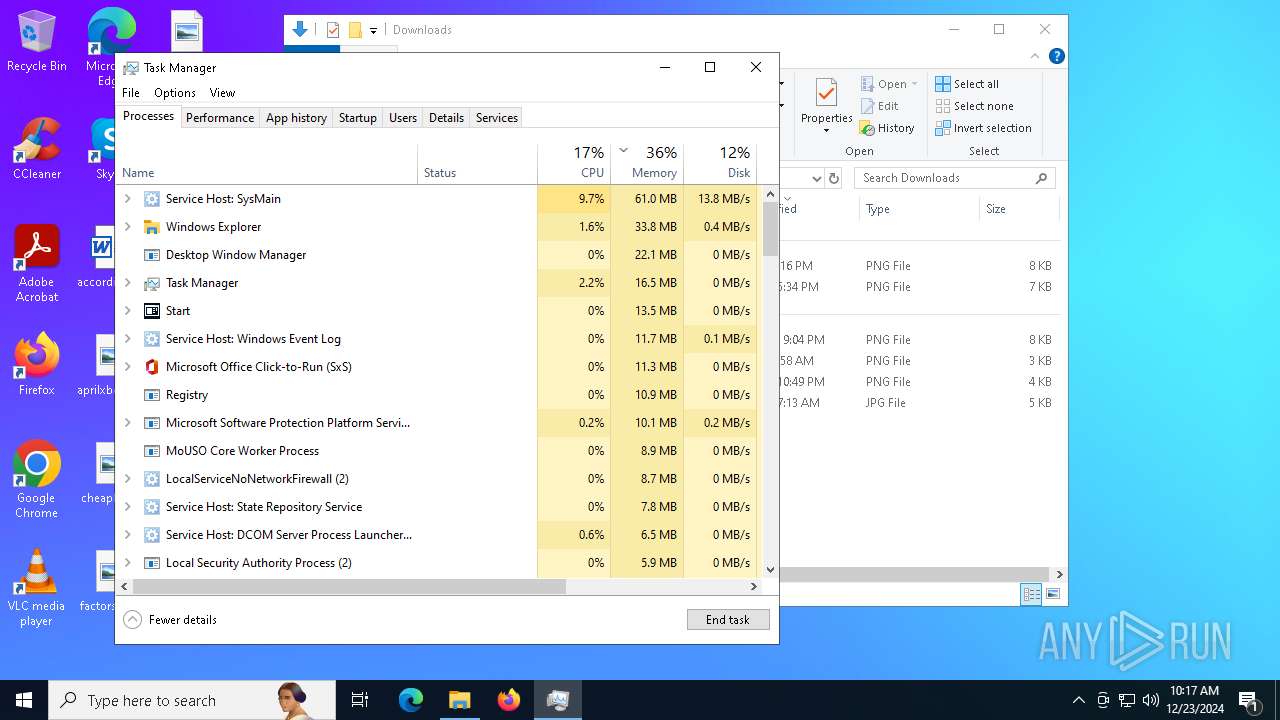
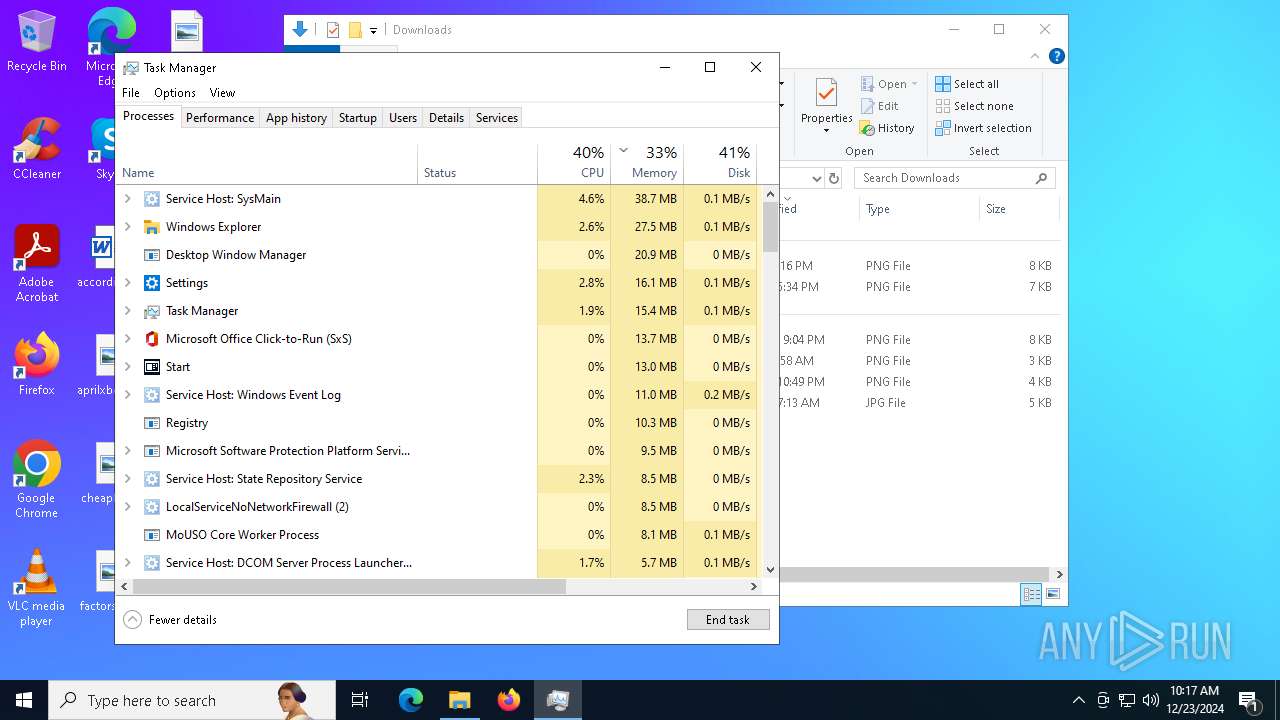
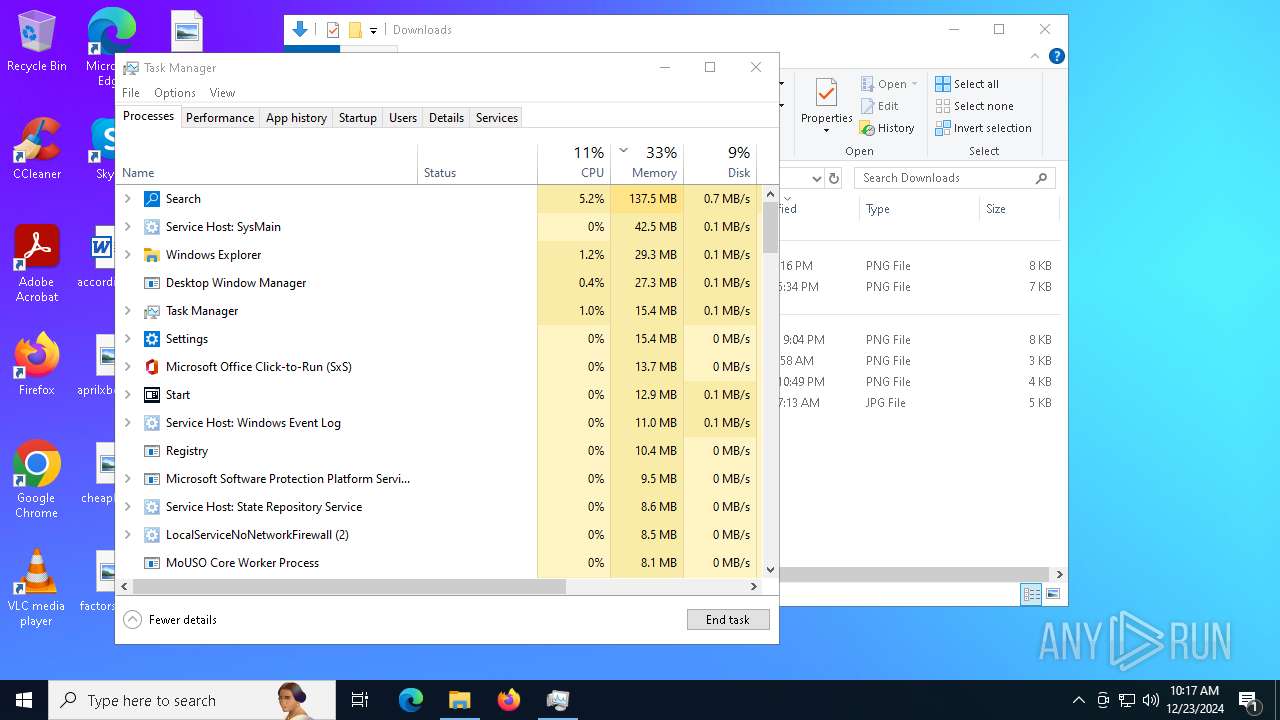
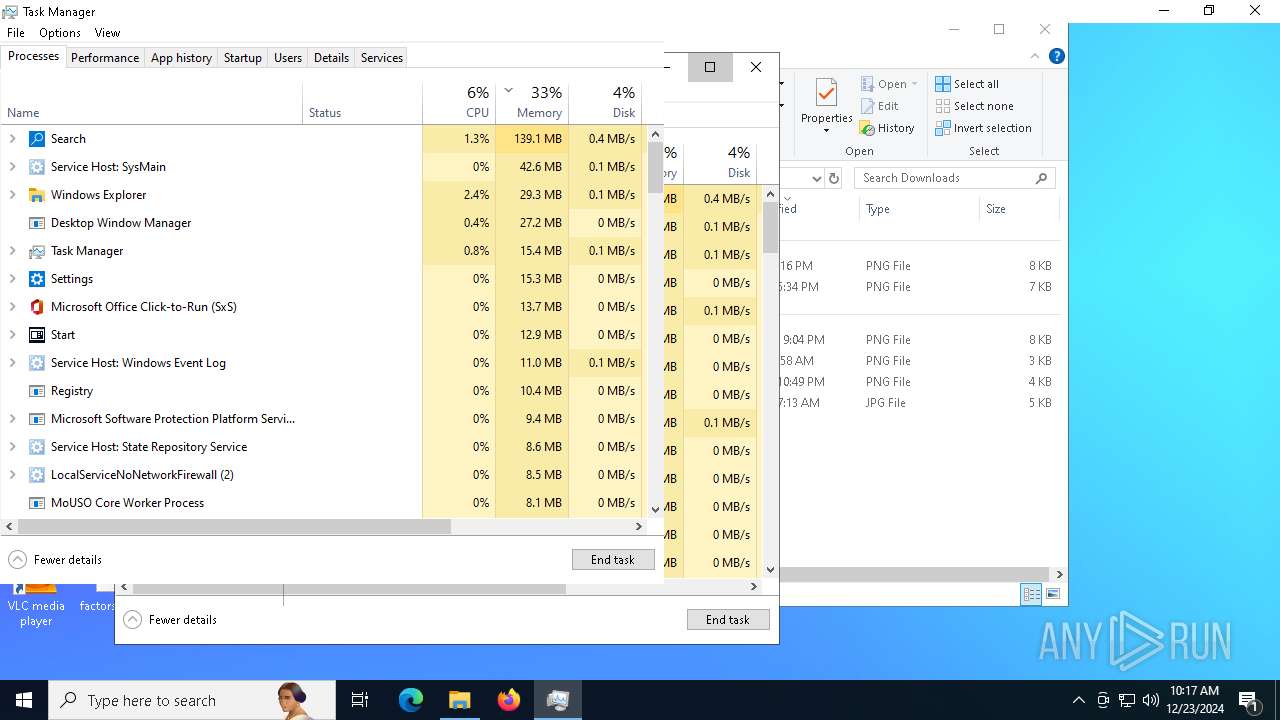
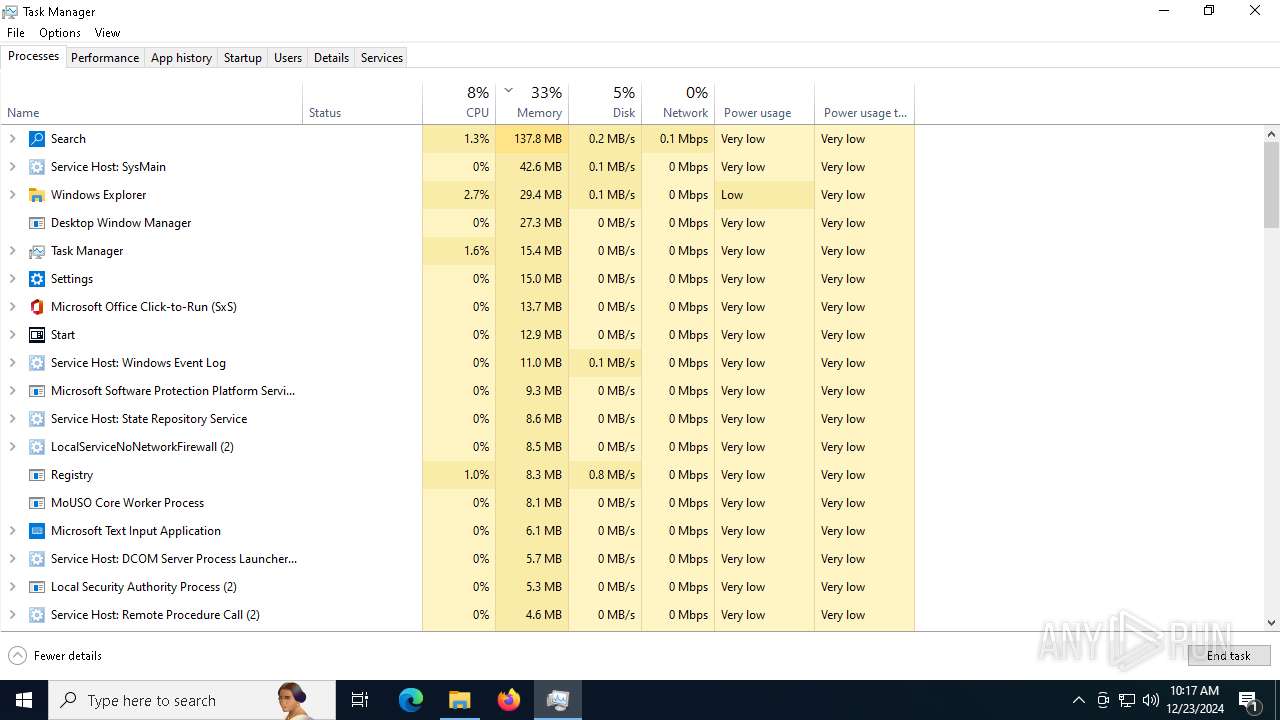
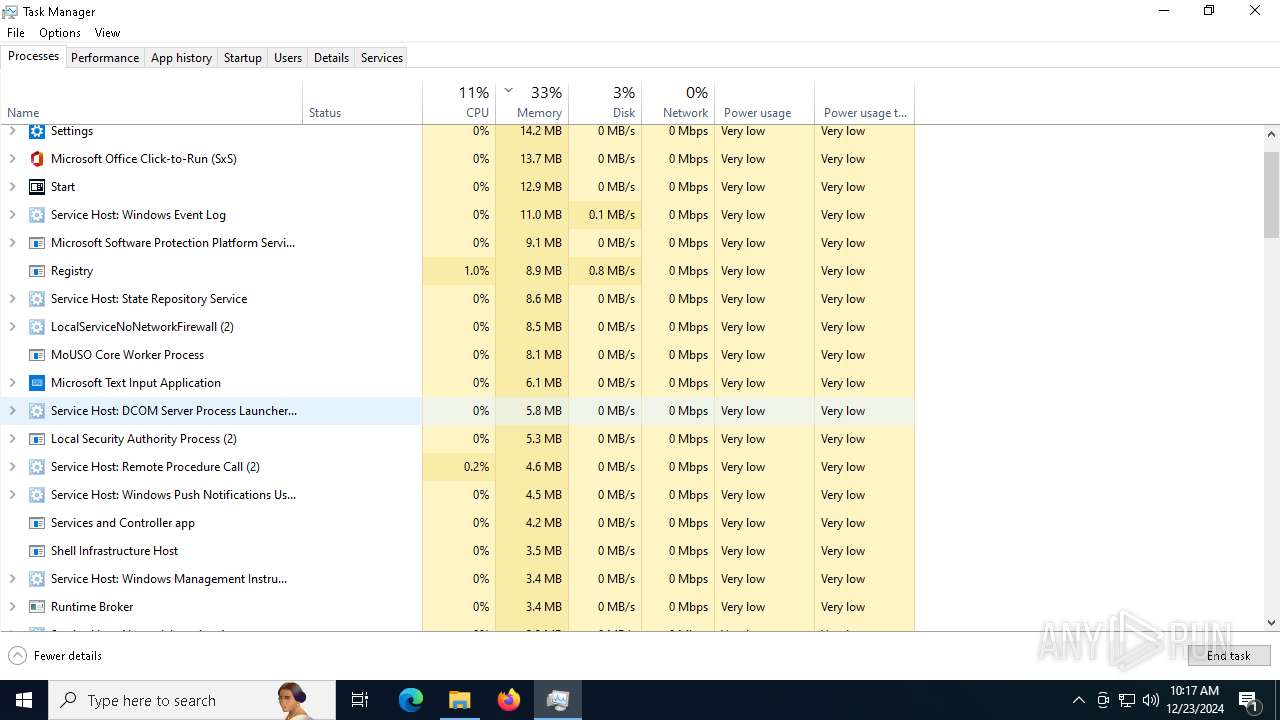
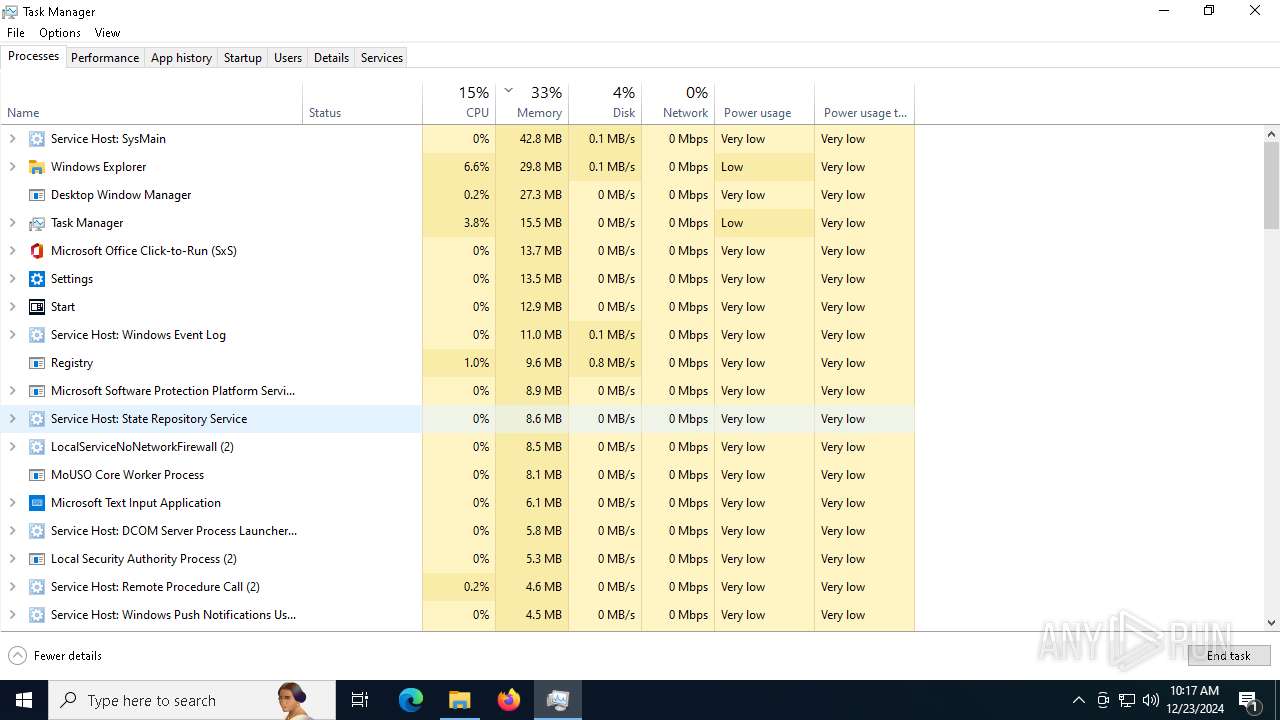
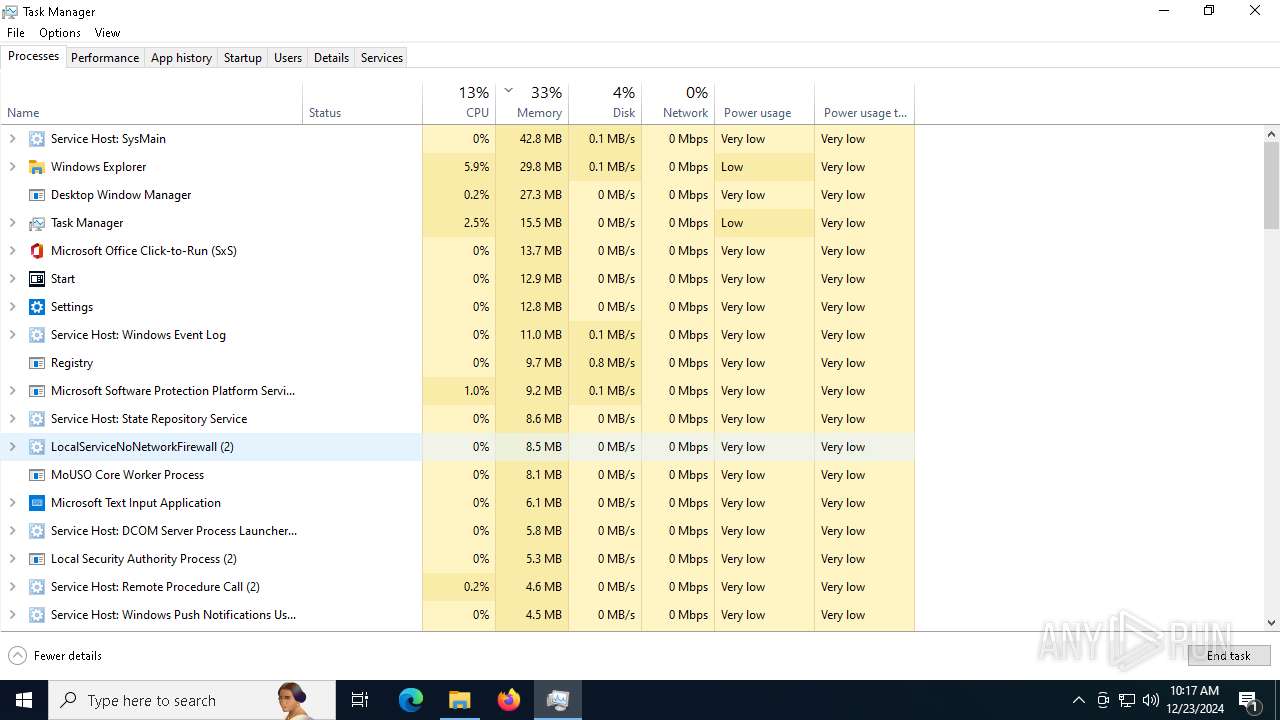
Manual execution by a user
- Taskmgr.exe (PID: 6688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 20:46:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 66048 |
| InitializedDataSize: | 722944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
| OriginalFileName: | No Escape.exe |
| CompanyName: | Maruf (C) |
| LegalCopyright: | Maruf (C) |
| Comments: | There is No Escape! |
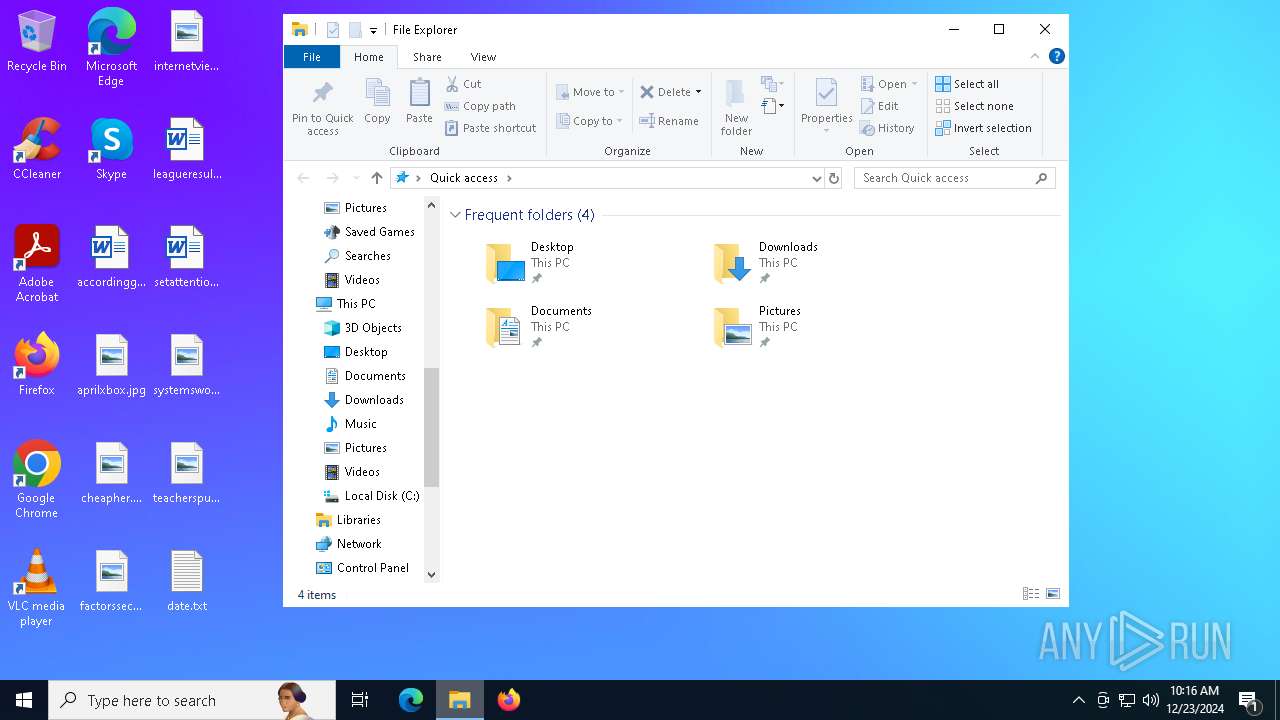
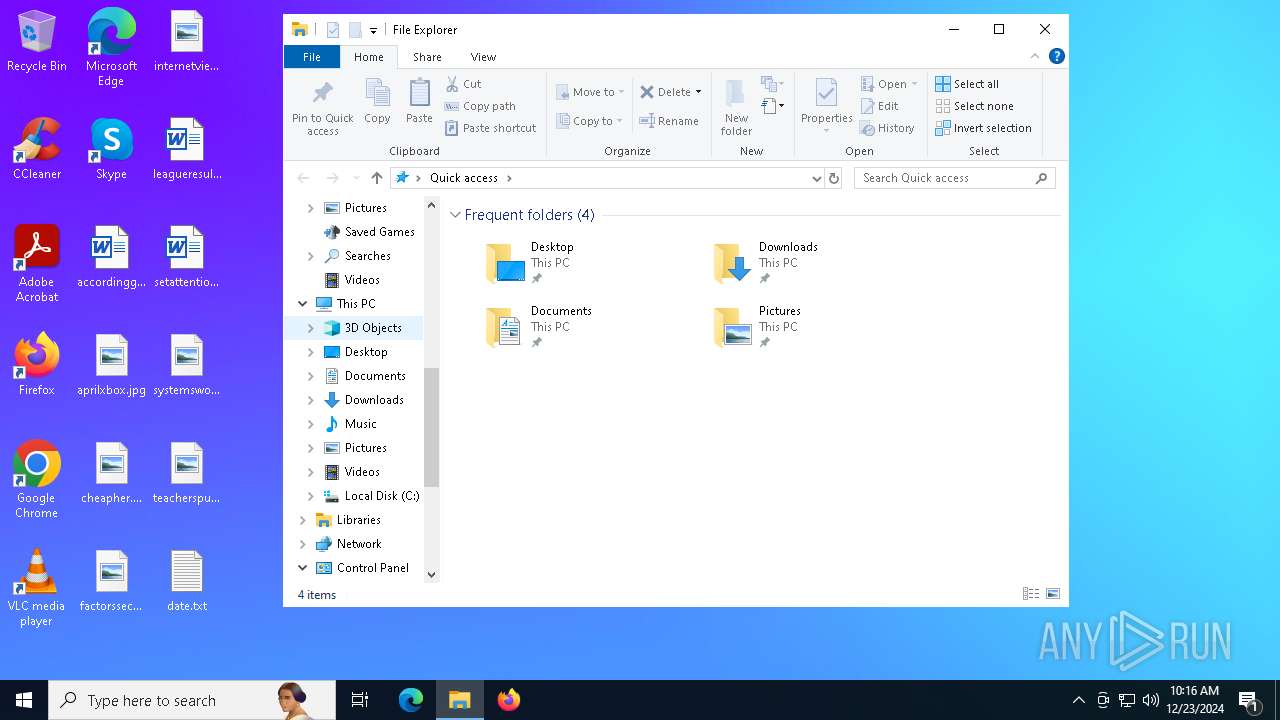
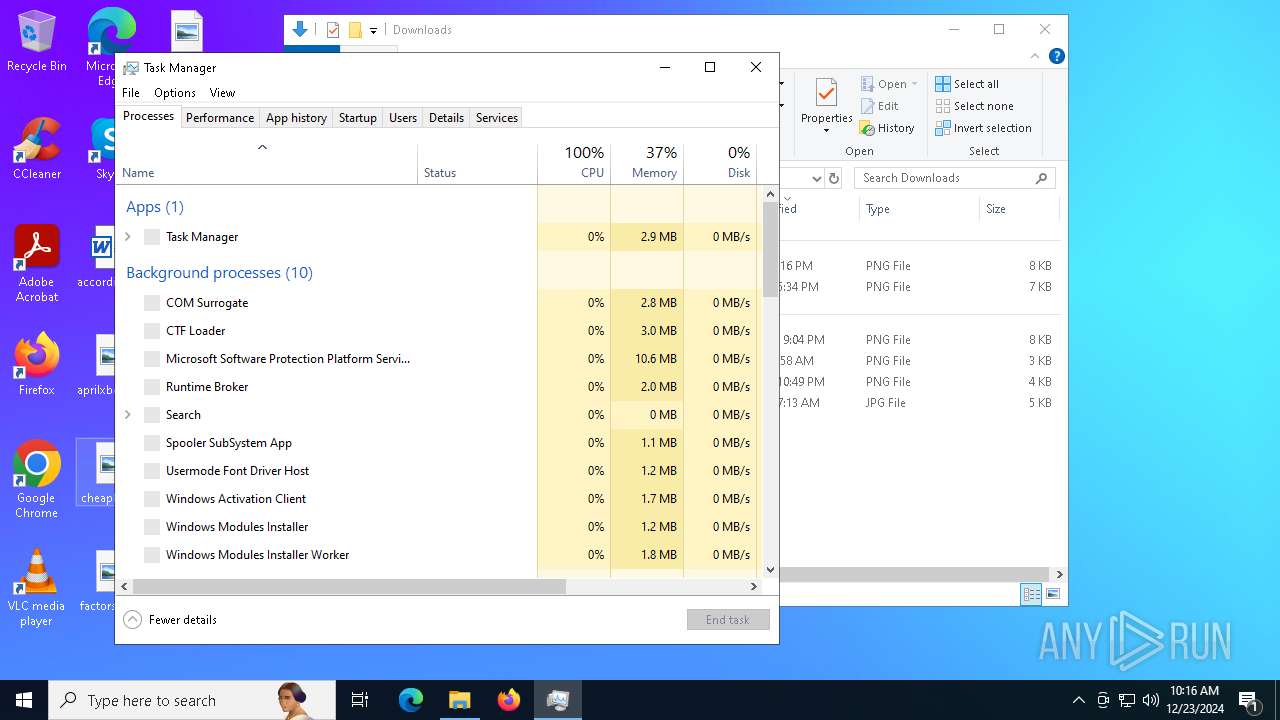
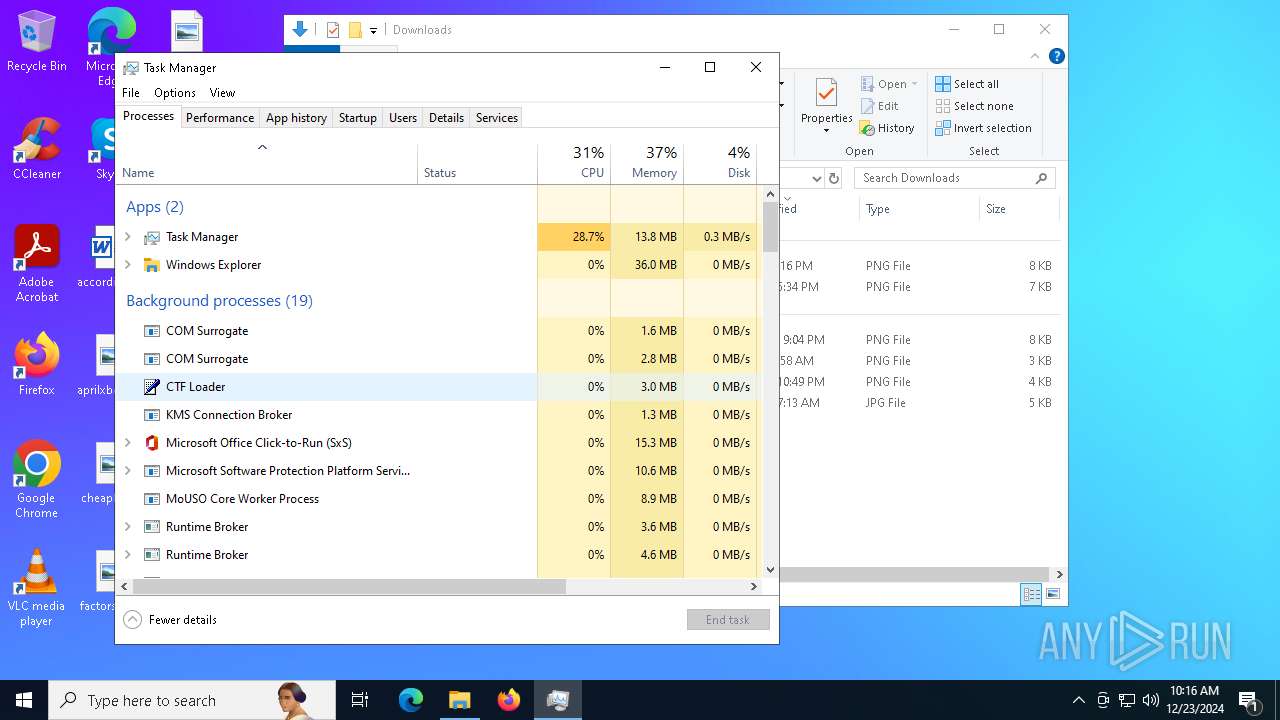
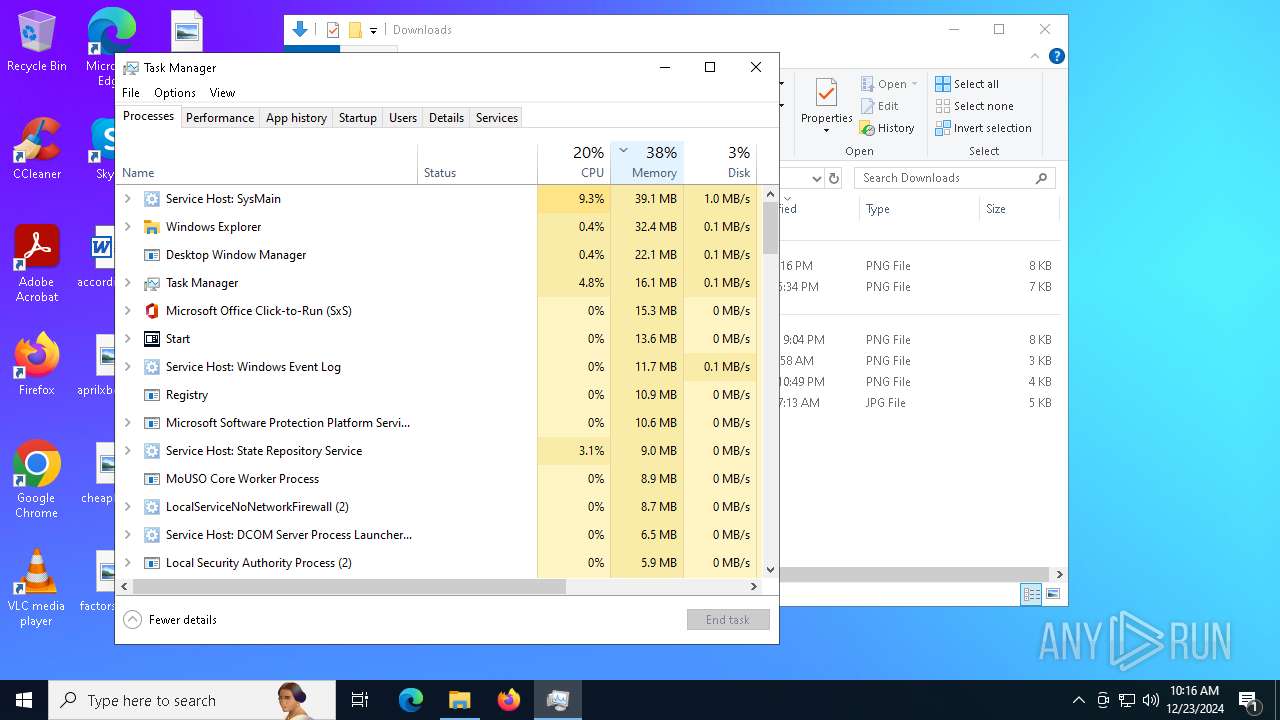
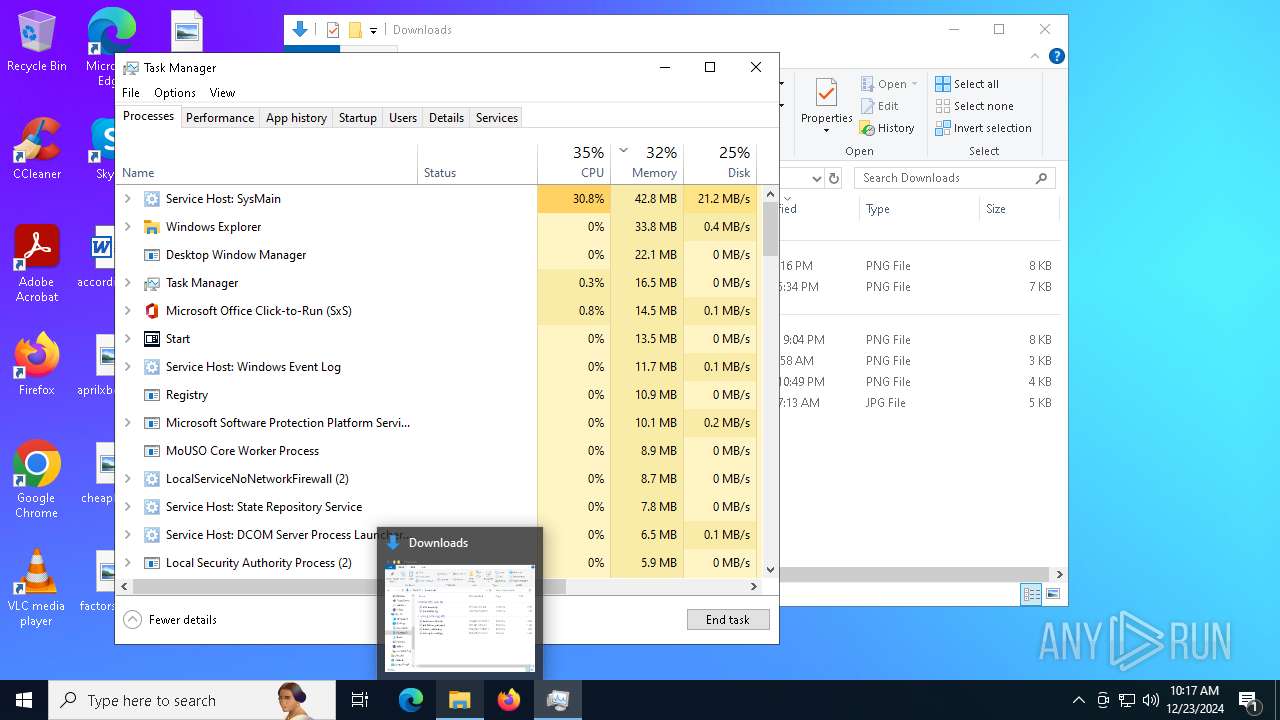
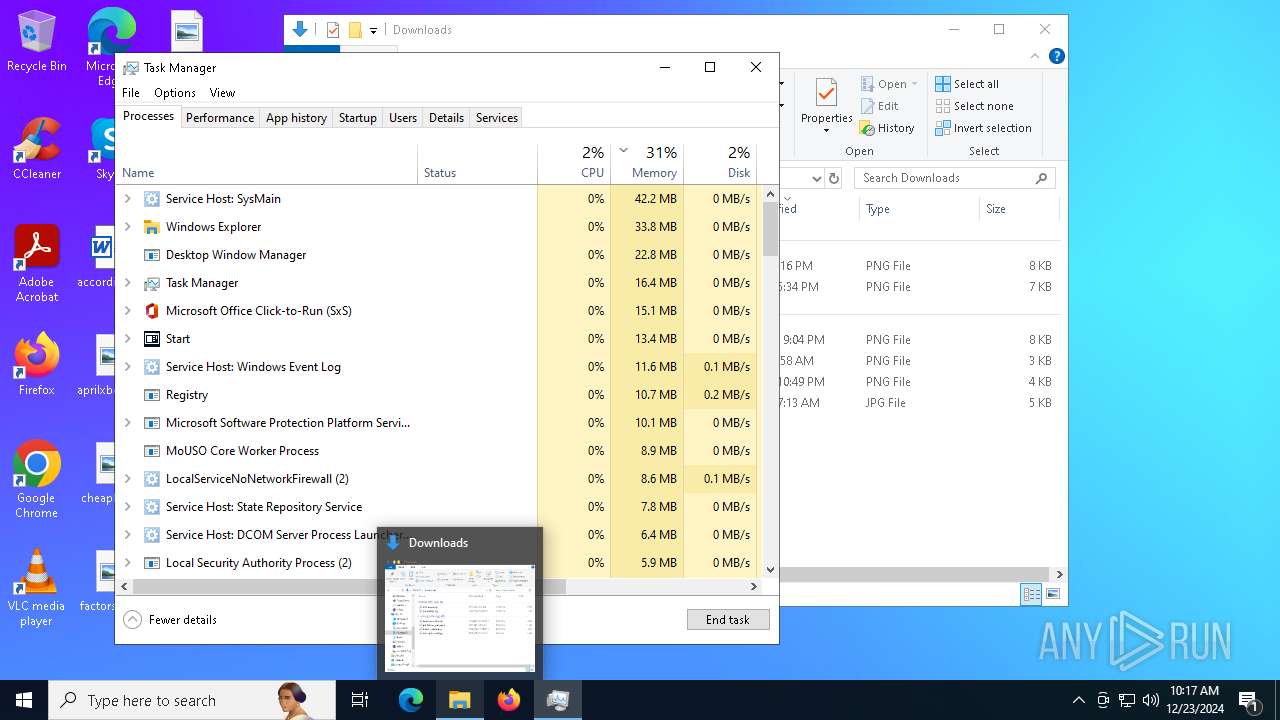
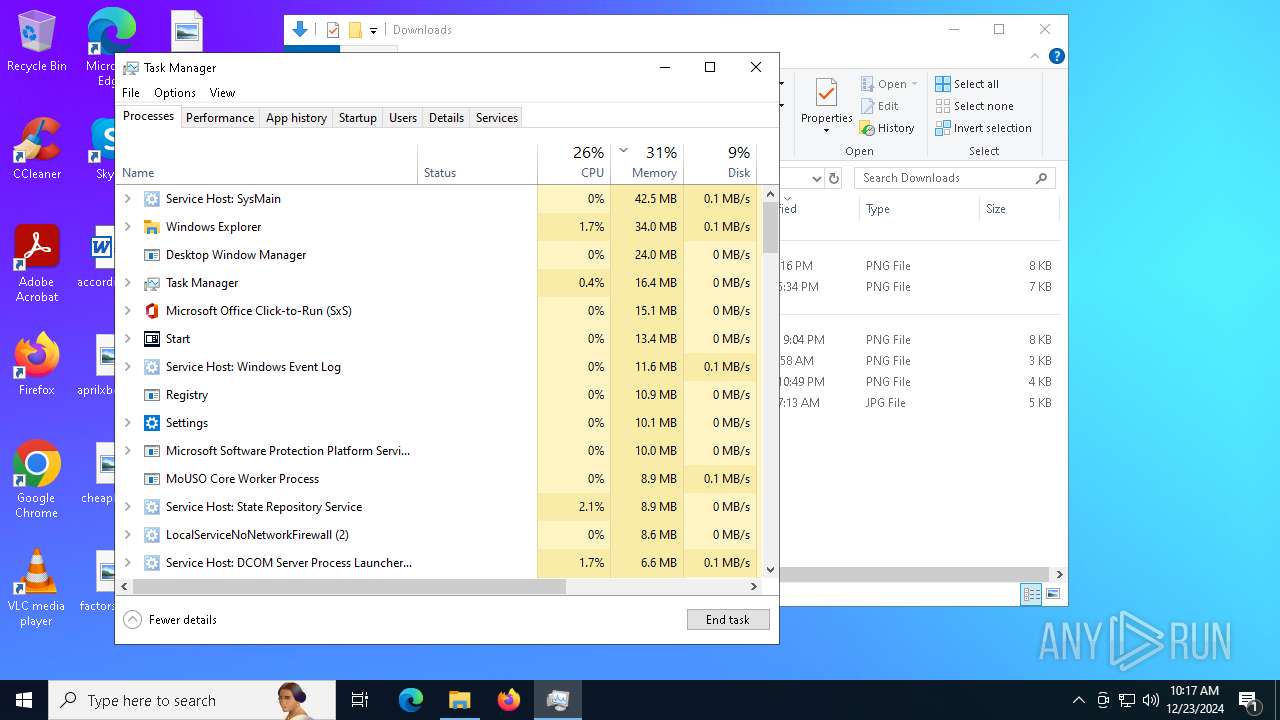
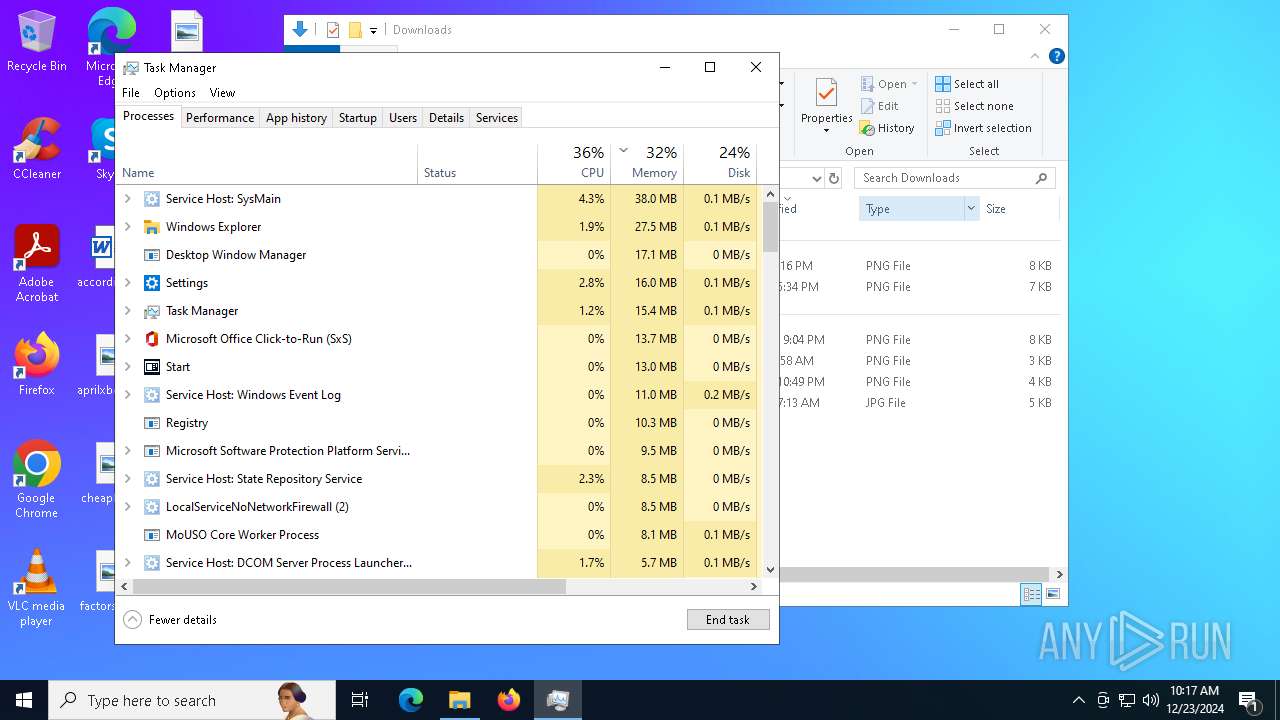
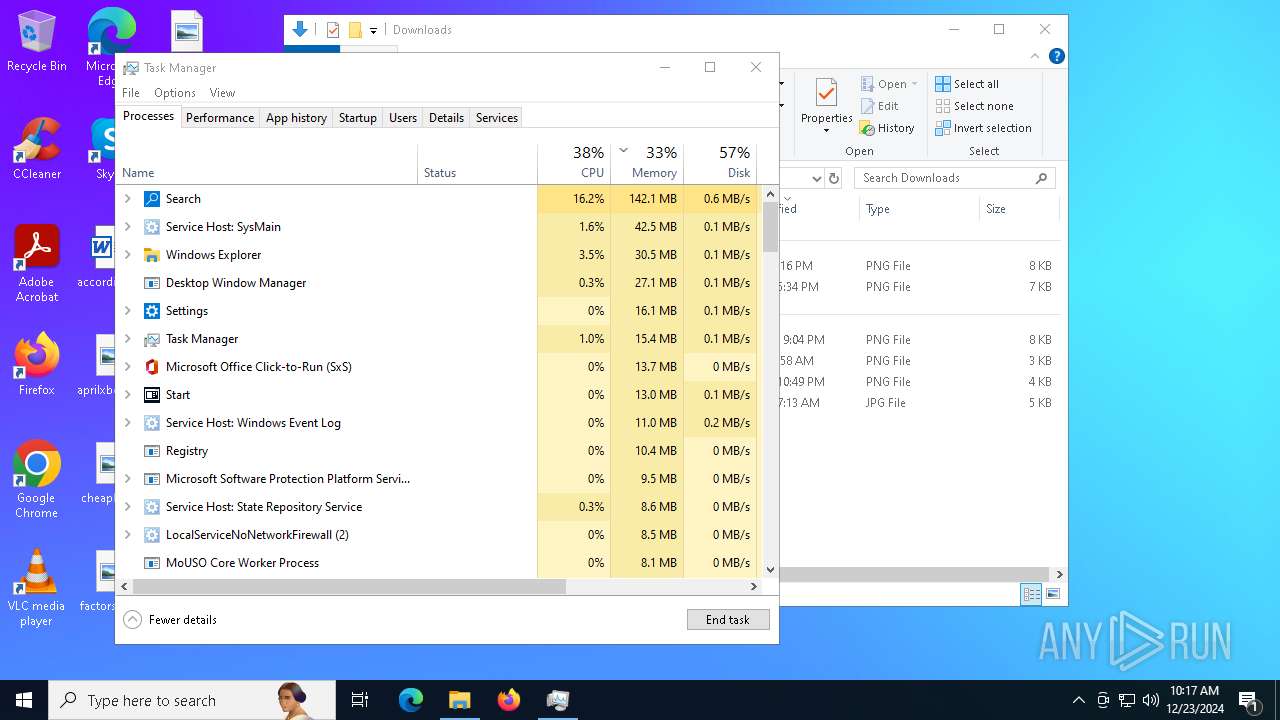
Total processes
280
Monitored processes
23
Malicious processes
3
Suspicious processes
1
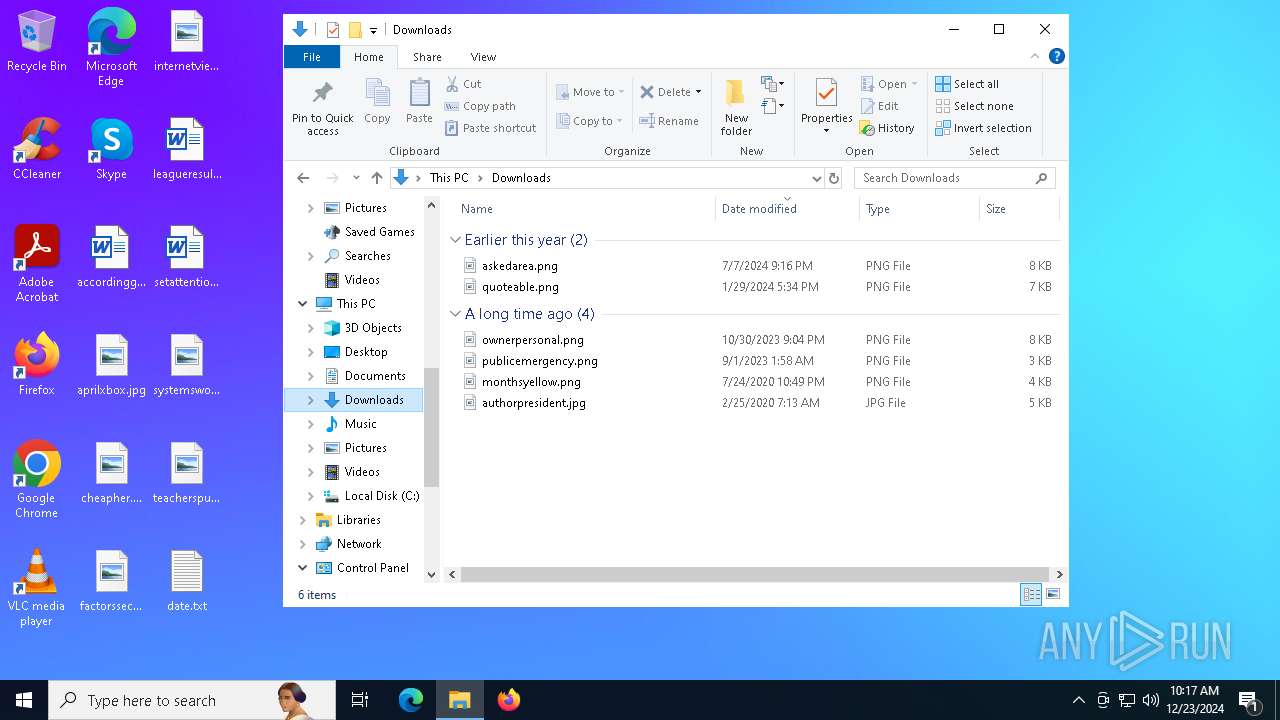
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3796 | "C:\Users\admin\AppData\Local\Temp\No Escape.exe" | C:\Users\admin\AppData\Local\Temp\No Escape.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4164 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4852 | "C:\WINDOWS\sysnative\wscript.exe" C:\Users\admin\AppData\Local\Temp\826E.tmp\826F.tmp\8270.vbs //Nologo | C:\Windows\System32\wscript.exe | — | launch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5252 | C:\WINDOWS\system32\WerFault.exe -u -p 5836 -s 1672 | C:\Windows\System32\WerFault.exe | — | ShellExperienceHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 3221226091 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5836 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 3221226107 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | "C:\Users\admin\AppData\Local\Temp\No Escape.exe" | C:\Users\admin\AppData\Local\Temp\No Escape.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6320 | "C:\WINDOWS\sysnative\wscript.exe" C:\Users\admin\AppData\Local\Temp\5595.tmp\5596.tmp\5597.vbs //Nologo | C:\Windows\System32\wscript.exe | — | No Escape.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6688 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6724 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files (x86)\hello.bat" " | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 436
Read events
3 424
Write events
11
Delete events
1
Modification events
| (PID) Process: | (6892) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | DisableLogonBackgroundImage |
Value: 1 | |||
| (PID) Process: | (6932) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | wallpaper |
Value: C:\hello.jpg | |||
| (PID) Process: | (6952) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop |
| Operation: | write | Name: | NoChangingWallPaper |
Value: 1 | |||
| (PID) Process: | (6972) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (6996) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | DisableCMD |
Value: 2 | |||
| (PID) Process: | (7016) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (6868) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout |
| Operation: | write | Name: | Scancode Map |
Value: 0000000000000000710000000000010000003B0000003C0000003D0000003E0000003F0000004000000041000000420000004300000044000000570000005800000037E000004600000052E0000047E0000049E0000051E000004FE0000053E0000048E000004BE0000050E000004DE00000520000005300000051000000500000004F0000004B0000004C0000004D0000004E0000004900000048000000470000004500000035E00000370000004A0000002900000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000F0000001000000011000000130000001600000017000000190000001A0000001B0000002B000000280000002700000026000000250000002400000022000000210000003A0000002A0000001D0000005BE00000380000002C0000002D0000002E0000002F0000003000000032000000330000003400000035000000360000001DE000005DE000005CE0000038E000005900000065E0000021E000006BE000005EE000005FE000006AE0000069E0000068E0000067E0000032E000006CE000006DE0000066E0000020E000002EE000002CE0000030E0000019E0000010E0000024E0000022E000000000 | |||
| (PID) Process: | (6912) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\system32\userinit.exe,C:\launch.exe | |||
| (PID) Process: | (5836) ShellExperienceHost.exe | Key: | \REGISTRY\A\{ddf985f4-74a0-fe1f-5b4a-fea1767aaff7}\2814751015243726\2814751014981172\App\6e7cf4b3a63cbf75113b2786943790ae |
| Operation: | write | Name: | SnapshotCaptured |
Value: 0 | |||
| (PID) Process: | (6688) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
Executable files
8
Suspicious files
40
Text files
7
Unknown types
1
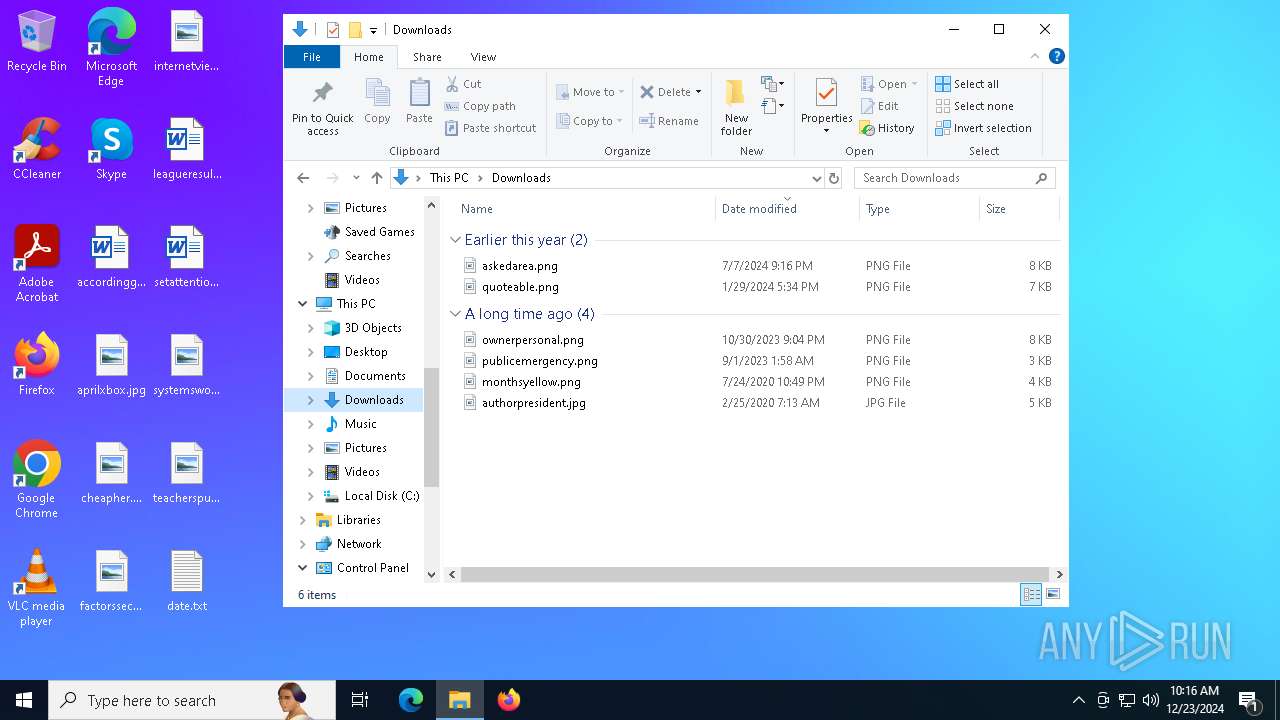
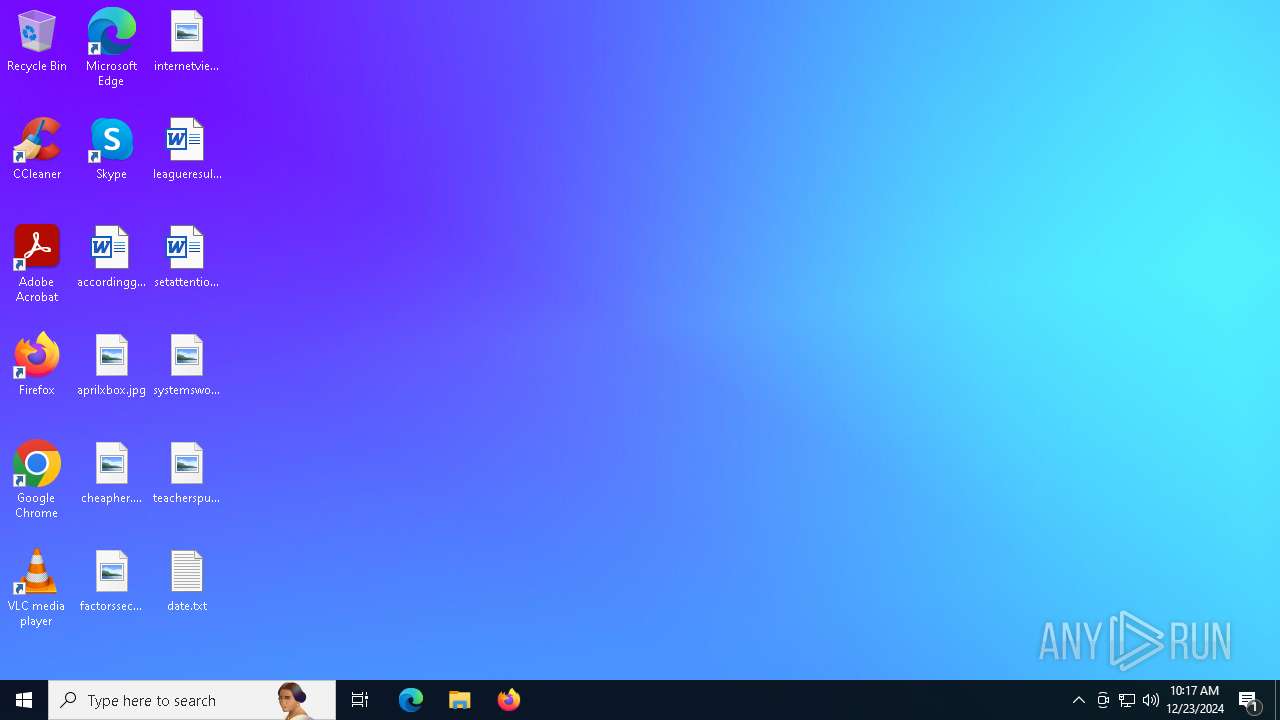
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | No Escape.exe | C:\Users\admin\AppData\Local\Temp\5595.tmp\5596.tmp\5597.vbs | binary | |
MD5:67706BCA9CEABA11530E05D351487003 | SHA256:190A0D994512ED000CF74BD40FB0502988C2AC48855B23A73FD905C0305FC30F | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\erode.exe | executable | |
MD5:918E75ECCB1E25E1D73994B975EF252C | SHA256:CBA73A620B7D4143830320F0878A473D1195D2C8AEEE65F0AEEE235A689DE48C | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\msg.exe | executable | |
MD5:331A0667B11E02330357565427DC1175 | SHA256:FC7174E44A1D34040C3BC05CE24E648742A38A3ACCCE22E8300D7059E4D12431 | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\hello.bat | text | |
MD5:B86FDDD2B764F079615BE5D4DC3E158D | SHA256:2B2114784D15B0B0D5475256851B4D0D4DA7181198C2A93A304ECEDB98EAF091 | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\mover.exe | executable | |
MD5:DDCF5D5CE2600C1137445019ED8B465B | SHA256:BFBC70655122E7F6D11EC954D8E2836771AD6AEC78E70A5564D03202DE4F07A3 | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\launch.exe | executable | |
MD5:B4ACC41D0E55B299FFEEC11A8A20CF08 | SHA256:34BC0D5B6029A74B9CDA56B72434EC1B55B6742FF5EF832D36027A987A63CD42 | |||
| 6268 | No Escape.exe | C:\Program Files (x86)\hello.jpg | image | |
MD5:057EA45C364EB2994808A47B118556A2 | SHA256:6E1115188AA00FB5FF031899100BACB0D34819707E069BCA3EB53935EBB39836 | |||
| 6724 | cmd.exe | C:\Users\admin\Desktop\date.txt | text | |
MD5:255A8E245B6AD378558B90CBE3DBC3D0 | SHA256:D3195BDE888F9B8A71F2EB840222F1586B652D0EDE9F39841A180EAD03633CA9 | |||
| 6724 | cmd.exe | C:\launch.exe | executable | |
MD5:B4ACC41D0E55B299FFEEC11A8A20CF08 | SHA256:34BC0D5B6029A74B9CDA56B72434EC1B55B6742FF5EF832D36027A987A63CD42 | |||
| 4164 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.045.etl | binary | |
MD5:673727AF7C6805E869C9F8BE1E468F4A | SHA256:6B16B7DE97F397BCEC36EB3F18C7B64CD3DB6D2974DDF319A251CE27B80D837B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5212 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6460 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6460 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5212 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3040 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |