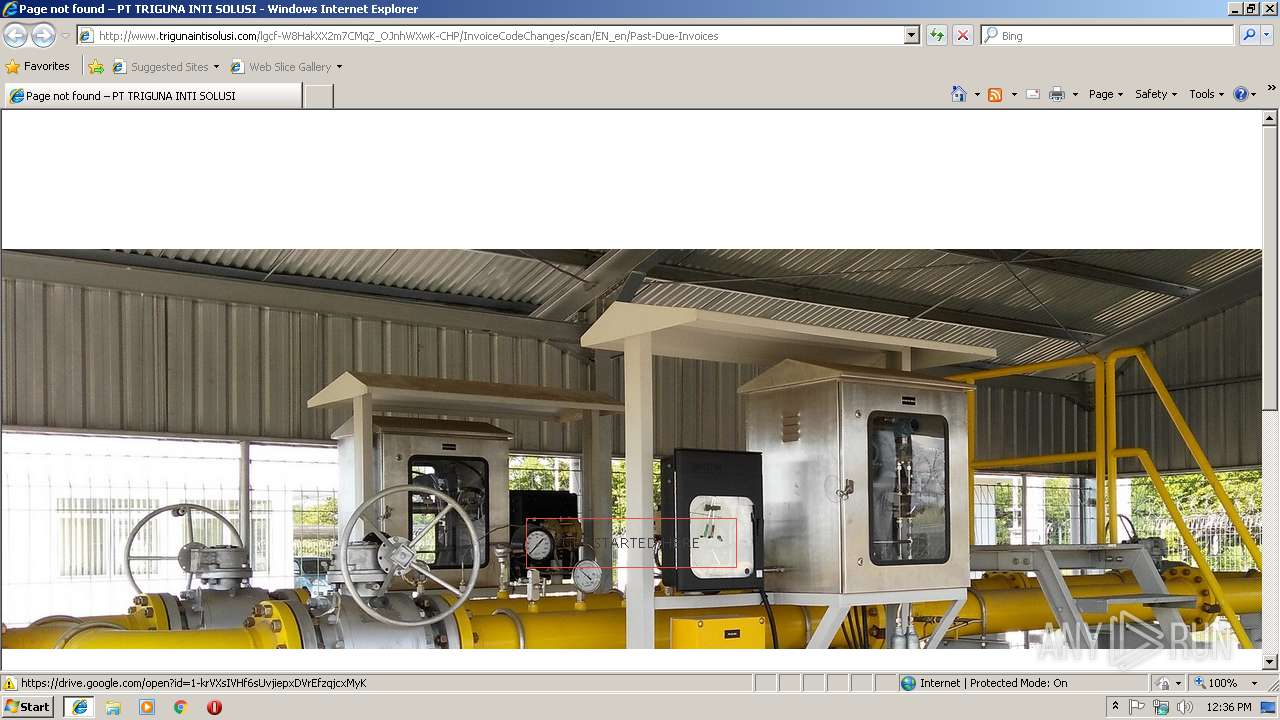
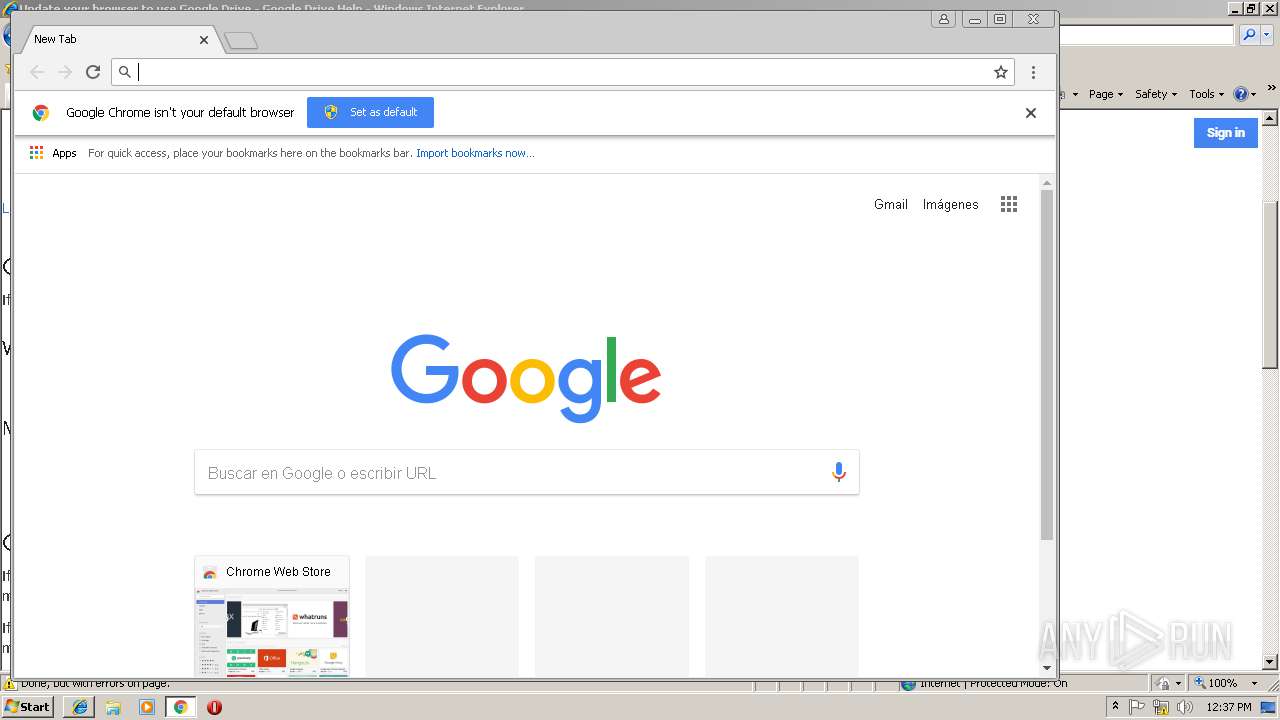
| URL: | http://trigunaintisolusi.com/lgcf-W8HakXX2m7CMqZ_OJnhWXwK-CHP/InvoiceCodeChanges/scan/EN_en/Past-Due-Invoices |
| Full analysis: | https://app.any.run/tasks/f16b0c7a-6c6b-4027-af6b-054a27f00196 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 12:36:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DD4ACD3B96466267488D4067B11F5369 |
| SHA1: | E3C50F805700E47B05B4DF29C33448FF584FDE4B |
| SHA256: | 56D1D0F859DF0D6D86F0137696776E3C6E4037D69A3C1CAE0473509A5764562C |
| SSDEEP: | 3:N1KKXMCiSQLGGDXU5vsbbH3nWAjoRWGELKuKWIoHW:CKXDi3GmXUkDnWAjpHKnIW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
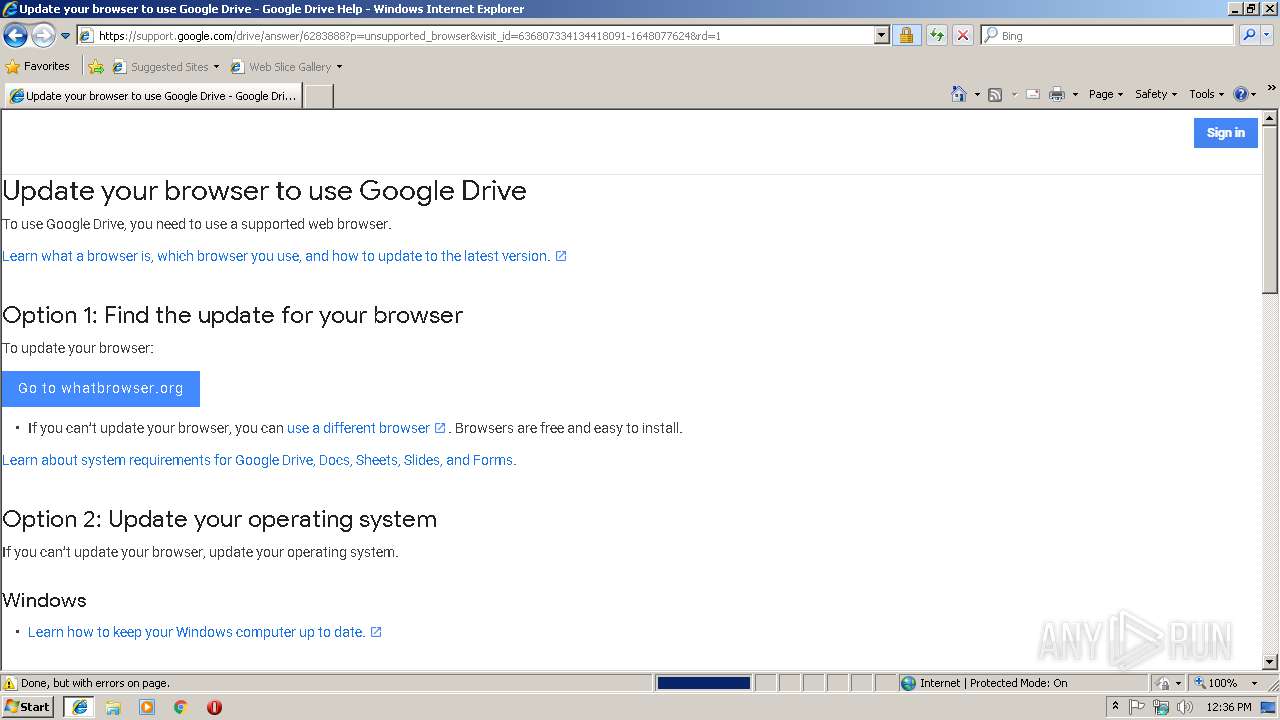
Changes internet zones settings
- iexplore.exe (PID: 2960)
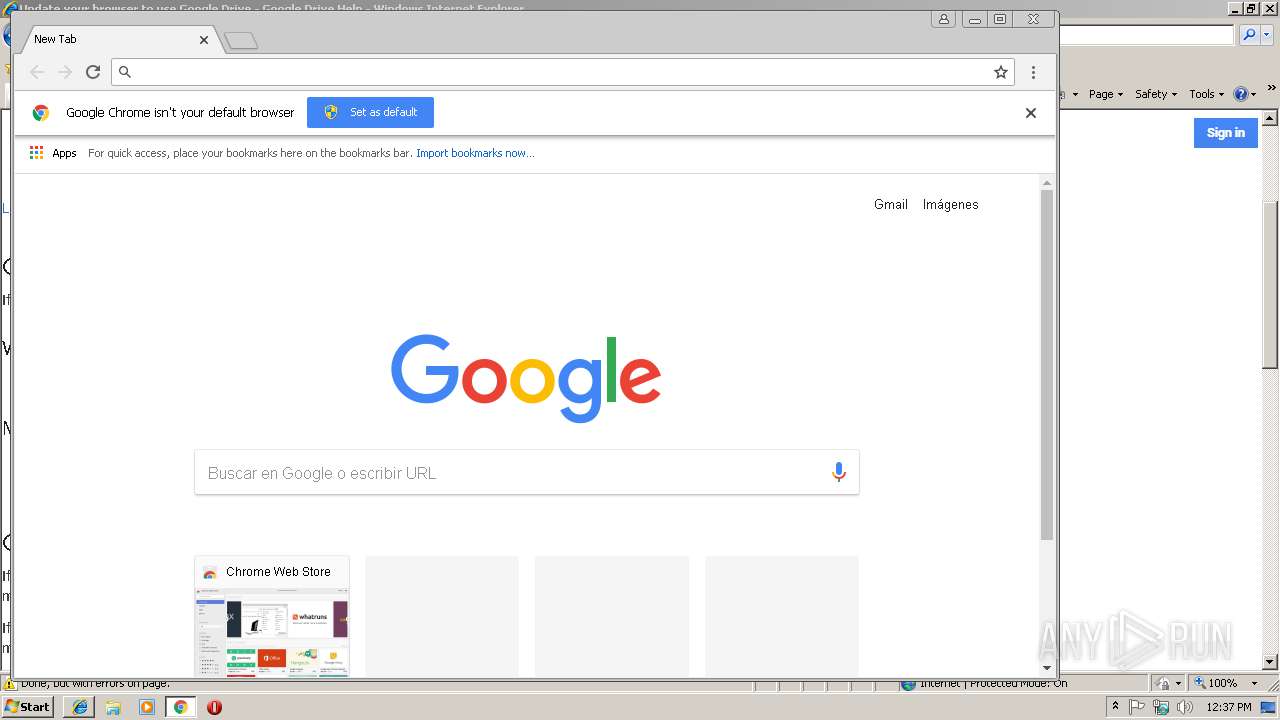
Application launched itself
- iexplore.exe (PID: 2960)
- chrome.exe (PID: 3220)
Reads settings of System Certificates
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2960)
Reads internet explorer settings
- iexplore.exe (PID: 3108)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2960)
Reads Internet Cache Settings
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2960)
Creates files in the user directory
- iexplore.exe (PID: 3108)
Changes settings of System certificates
- iexplore.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --service-pipe-token=FE1353E0737E7AAEACD9895E0CBF33D6 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FE1353E0737E7AAEACD9895E0CBF33D6 --renderer-client-id=5 --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6cf500b0,0x6cf500c0,0x6cf500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --service-pipe-token=E537554AB21132A62ACF62614EE05139 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E537554AB21132A62ACF62614EE05139 --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F31377B19EA4A2C435180C51271A15D3 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2960 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=80FC81ECB0C0B1612D6235CF70E8A5FE --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=80FC81ECB0C0B1612D6235CF70E8A5FE --renderer-client-id=6 --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2C11289B51580F995AF81FCA6F9A051A --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3244 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
626
Read events
508
Write events
111
Delete events
7
Modification events
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {871C537B-02C1-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C00020012000C00240018003A02 | |||
Executable files
0
Suspicious files
36
Text files
75
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\main[1].js | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\jquery[1].js | text | |
MD5:8610F03FE77640DEE8C4CC924E060F12 | SHA256:FC48D1D80ECE71A79A7B39877F4104D49D3DA6C3665CF6DC203000FB7DF4447E | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\6283888[1].txt | — | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\main.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\Meter-gas-orifice-1[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\styles[1].css | text | |
MD5:5AD1CFA3F5175F627385651790ED0BBD | SHA256:3AD2FCB328295F1199D593ADABA909F3EEA790F695554AC3C1DA7AA009FC0E0D | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\wp-emoji-release.min[1].js | text | |
MD5:15D0C302DC74FD87BD9CFEAB513E13E4 | SHA256:D2458B9FD9089FDCB9DE317093E004EF3A65597DC68B9ADFDEB15A7C9968D0D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
42
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3108 | iexplore.exe | GET | 301 | 103.233.102.18:80 | http://trigunaintisolusi.com/lgcf-W8HakXX2m7CMqZ_OJnhWXwK-CHP/InvoiceCodeChanges/scan/EN_en/Past-Due-Invoices | ID | — | — | malicious |
3108 | iexplore.exe | GET | 404 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/lgcf-W8HakXX2m7CMqZ_OJnhWXwK-CHP/InvoiceCodeChanges/scan/EN_en/Past-Due-Invoices | ID | html | 15.9 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-content/themes/bizworx/js/main.min.js?ver=20180213 | ID | text | 2.86 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-content/plugins/bizworx-tools/js/main.js?ver=20180228 | ID | text | 1.61 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-content/themes/bizworx/fonts/font-awesome.min.css?ver=5.0.1 | ID | text | 30.2 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-includes/js/jquery/jquery.js?ver=1.12.4 | ID | text | 94.9 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-includes/css/dist/block-library/style.min.css?ver=5.0.1 | ID | text | 24.9 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-includes/js/jquery/jquery-migrate.min.js?ver=1.4.1 | ID | text | 9.82 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-content/themes/bizworx/css/bootstrap/bootstrap.min.css?ver=1 | ID | text | 16.2 Kb | malicious |
3108 | iexplore.exe | GET | 200 | 103.233.102.18:80 | http://www.trigunaintisolusi.com/wp-content/plugins/contact-form-7/includes/js/scripts.js?ver=5.1 | ID | text | 14.1 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | iexplore.exe | 103.233.102.18:443 | trigunaintisolusi.com | PT MITRA VISIONER PRATAMA | ID | malicious |
3108 | iexplore.exe | 103.233.102.18:80 | trigunaintisolusi.com | PT MITRA VISIONER PRATAMA | ID | malicious |
3108 | iexplore.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3108 | iexplore.exe | 172.217.16.142:443 | support.google.com | Google Inc. | US | whitelisted |
3108 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3108 | iexplore.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2960 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3108 | iexplore.exe | 64.233.166.196:443 | apis.google.com | Google Inc. | US | unknown |
3108 | iexplore.exe | 172.217.22.1:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
trigunaintisolusi.com |
| malicious |
www.trigunaintisolusi.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
drive.google.com |
| shared |
support.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3108 | iexplore.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious request with 'invoice' in http uri |
3108 | iexplore.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious request with 'invoice' in http uri |