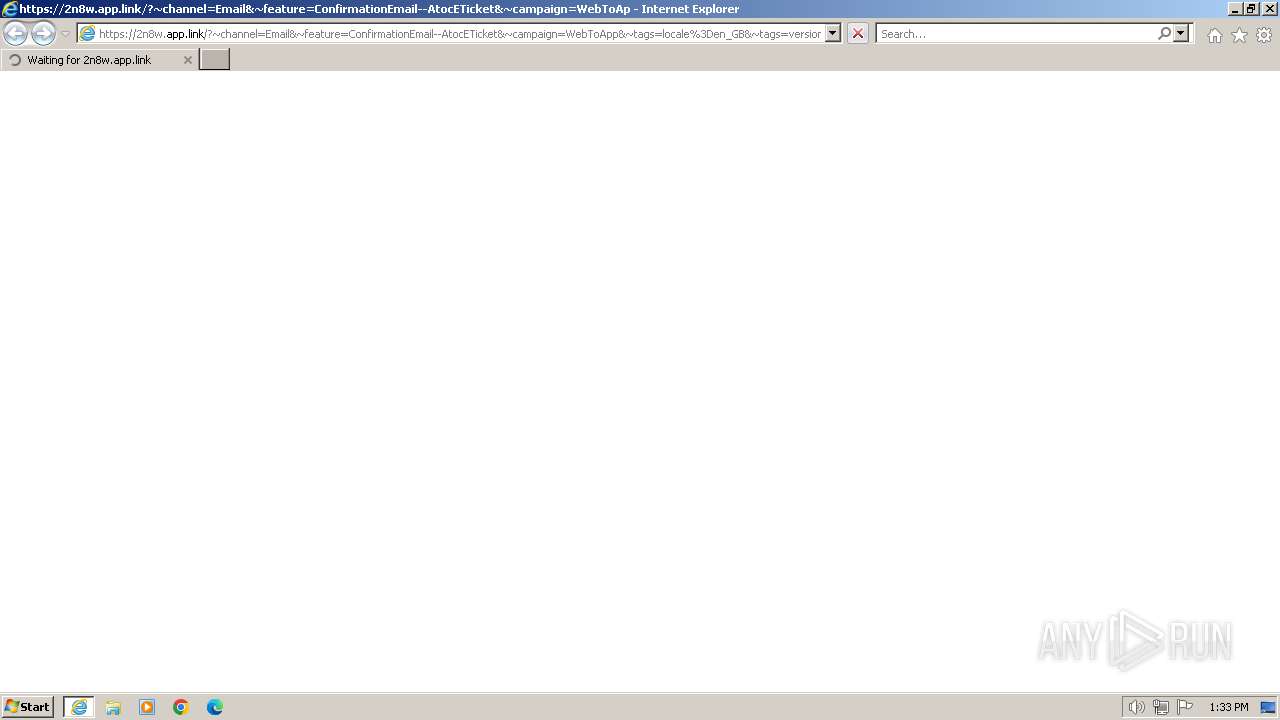
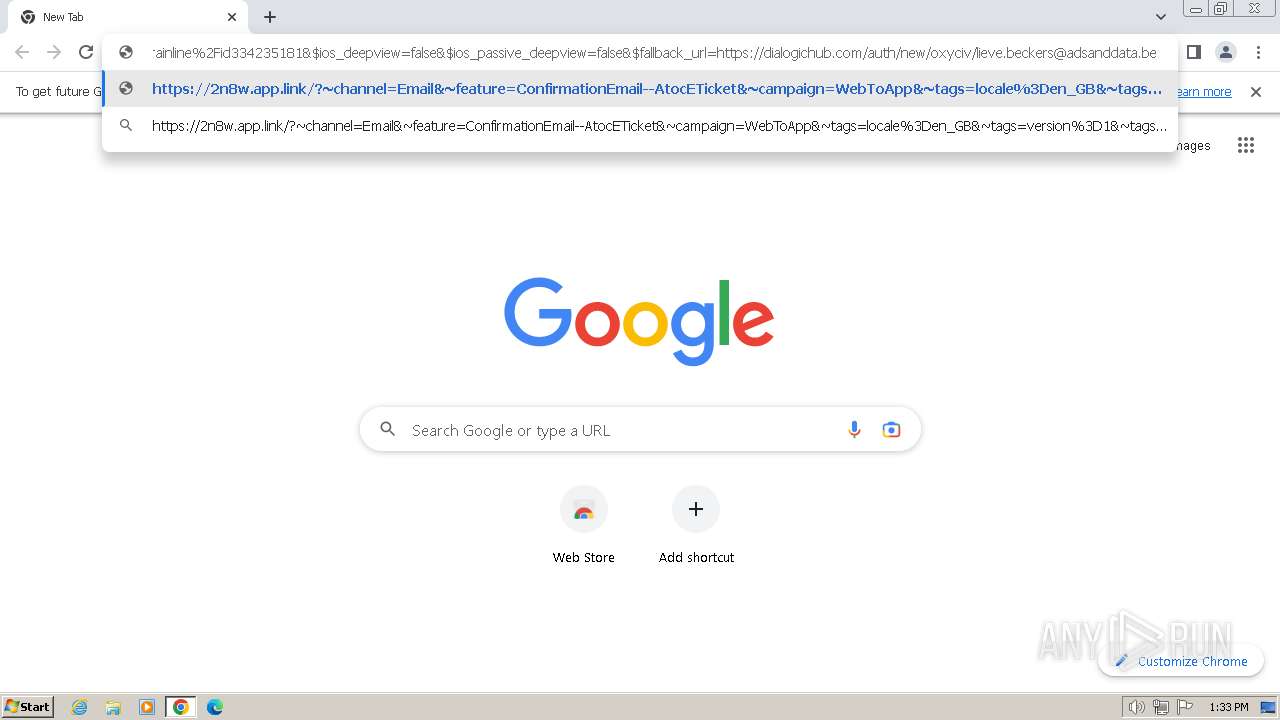
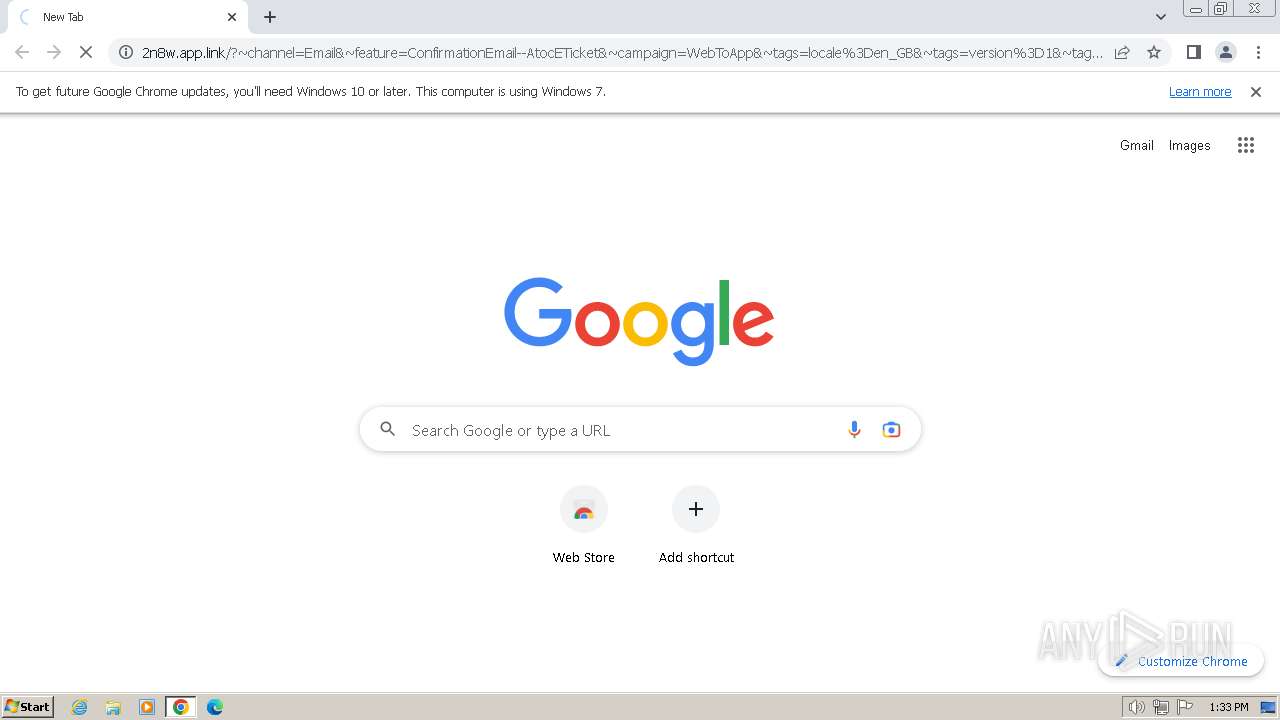
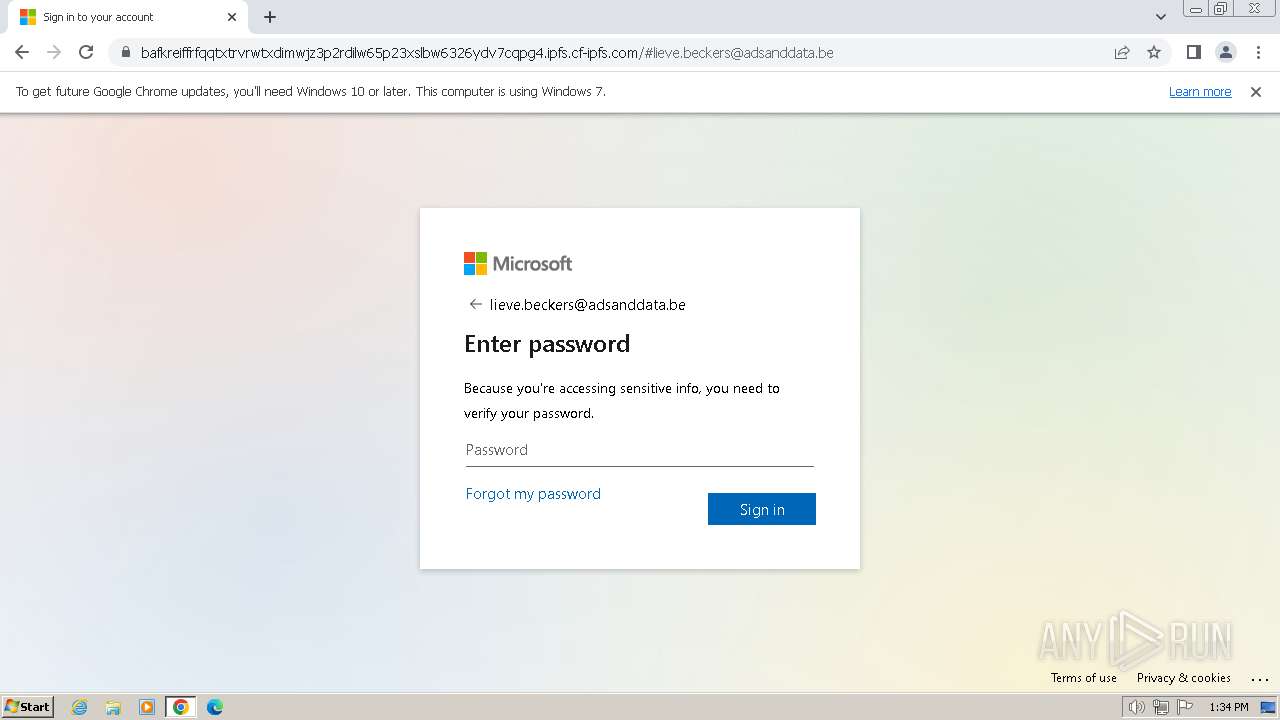
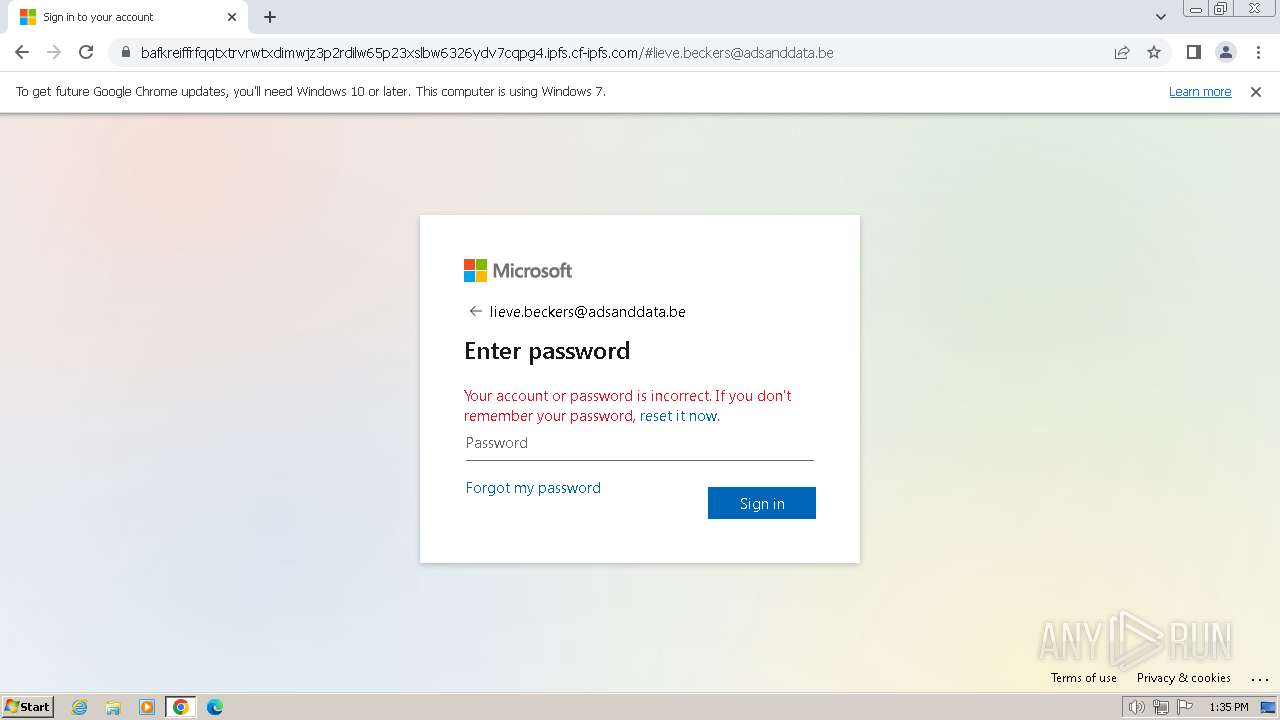
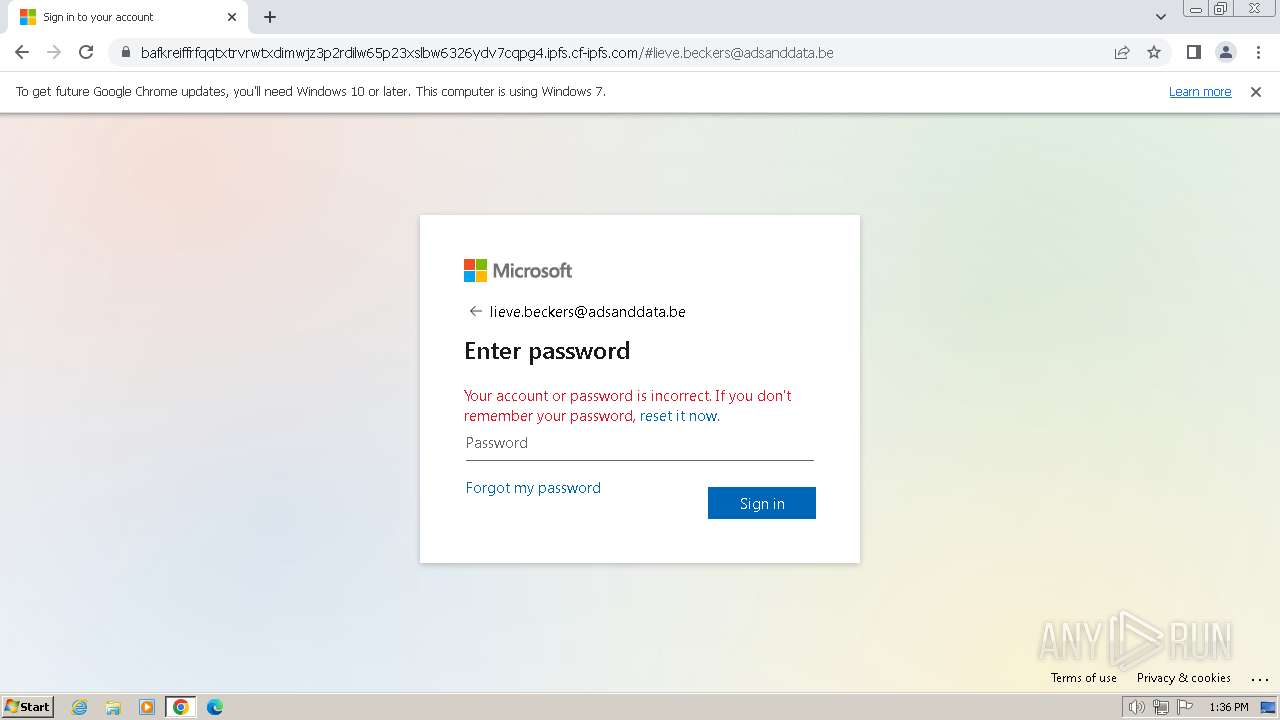
| URL: | https://2n8w.app.link/?~channel=Email&~feature=ConfirmationEmail--AtocETicket&~campaign=WebToApp&~tags=locale%3Den_GB&~tags=version%3D1&~tags=marketing_code%3DBSH3675&$android_url=https%3A%2F%2Fplay.google.com%2Fstore%2Fapps%2Fdetails%3Fid%3Dcom.thetrainline%26hl%3Den-GB&$android_deepview=false&$android_passive_deepview=false&$ios_url=https%3A%2F%2Fitunes.apple.com%2FGB%2Fapp%2Fthetrainline%2Fid334235181&$ios_deepview=false&$ios_passive_deepview=false&$fallback_url=https://dialogichub.com/auth/new/oxyciv/lieve.beckers@adsanddata.be |
| Full analysis: | https://app.any.run/tasks/9a8576a9-57a9-48d4-8c48-61cb0859fe02 |
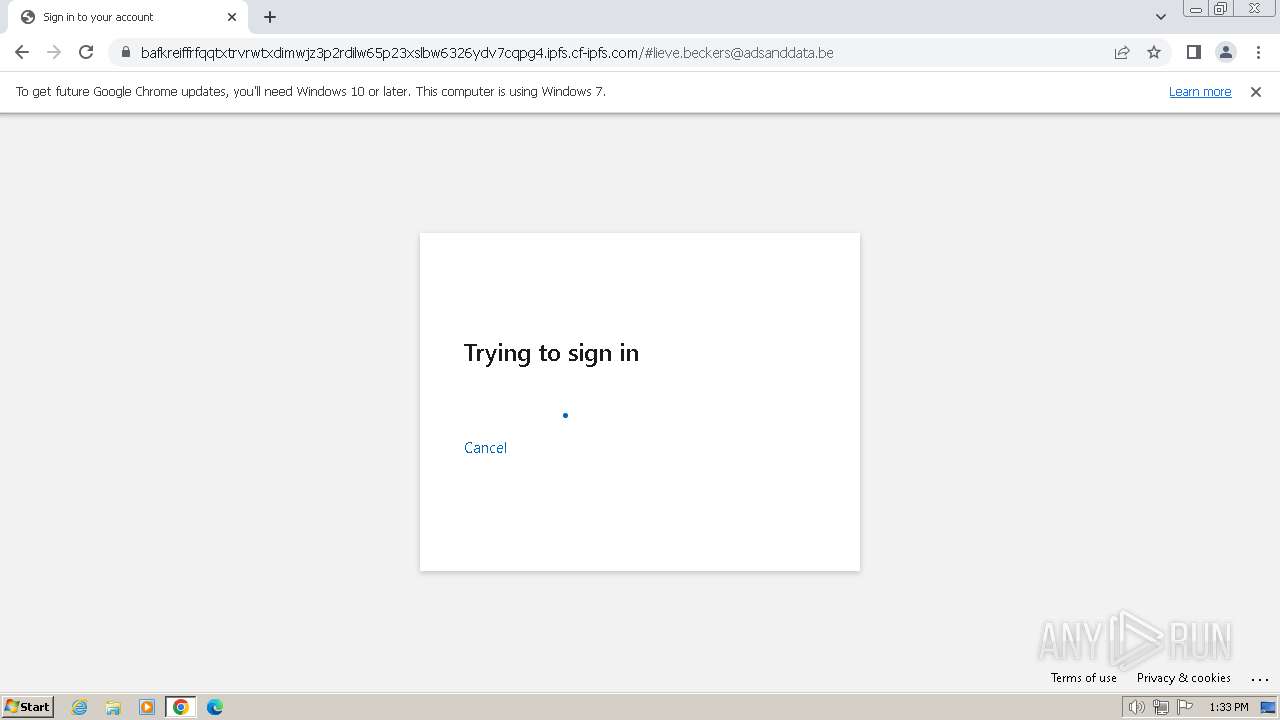
| Verdict: | Malicious activity |
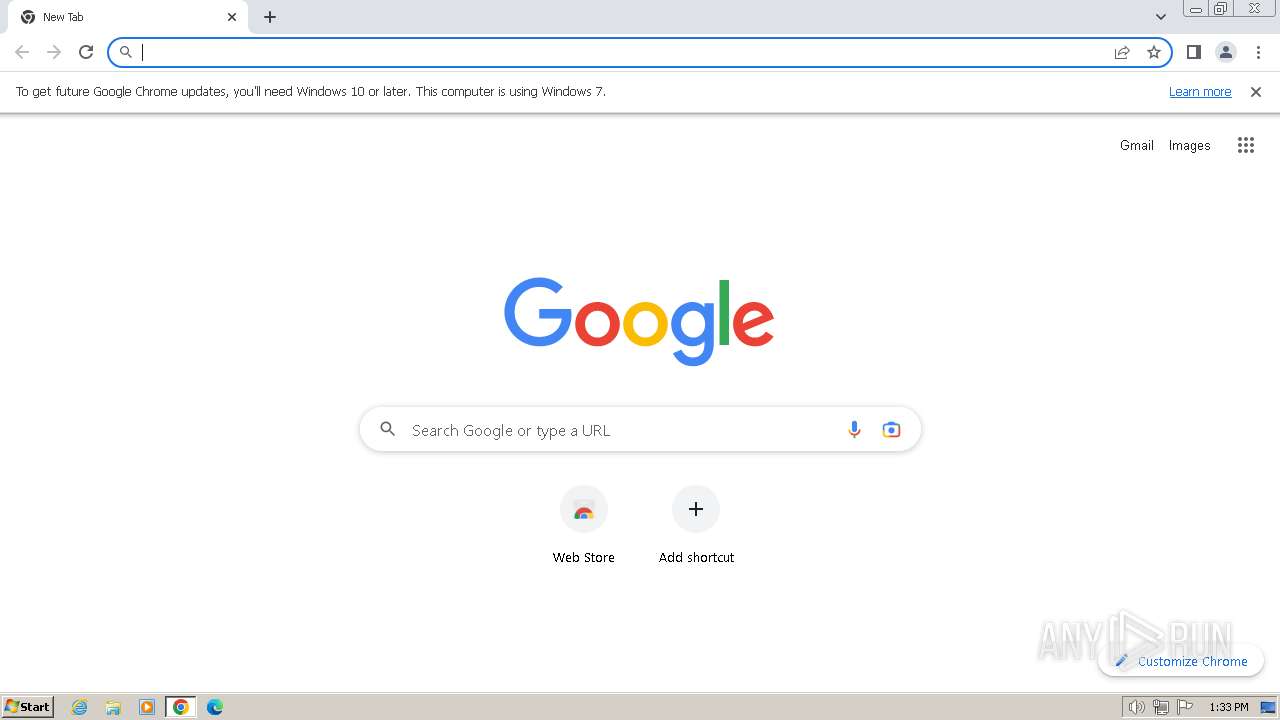
| Analysis date: | January 27, 2024, 13:33:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 089279F4866B127DF1ABE52FB494905B |
| SHA1: | 990EF7713E5B77A8D572672510DD930811B0BA94 |
| SHA256: | 56BF98CE26574EAD6D6637B1DE43B7B6CBA10556060DC67C05CA0819D9F94B2E |
| SSDEEP: | 12:2TScoHFMkd2KAEKIjSjA86x2KAZEYxt+1fYxiEYx4dHSAJJsn:2TwL/pSjt6xtKxgdYxKxMin |
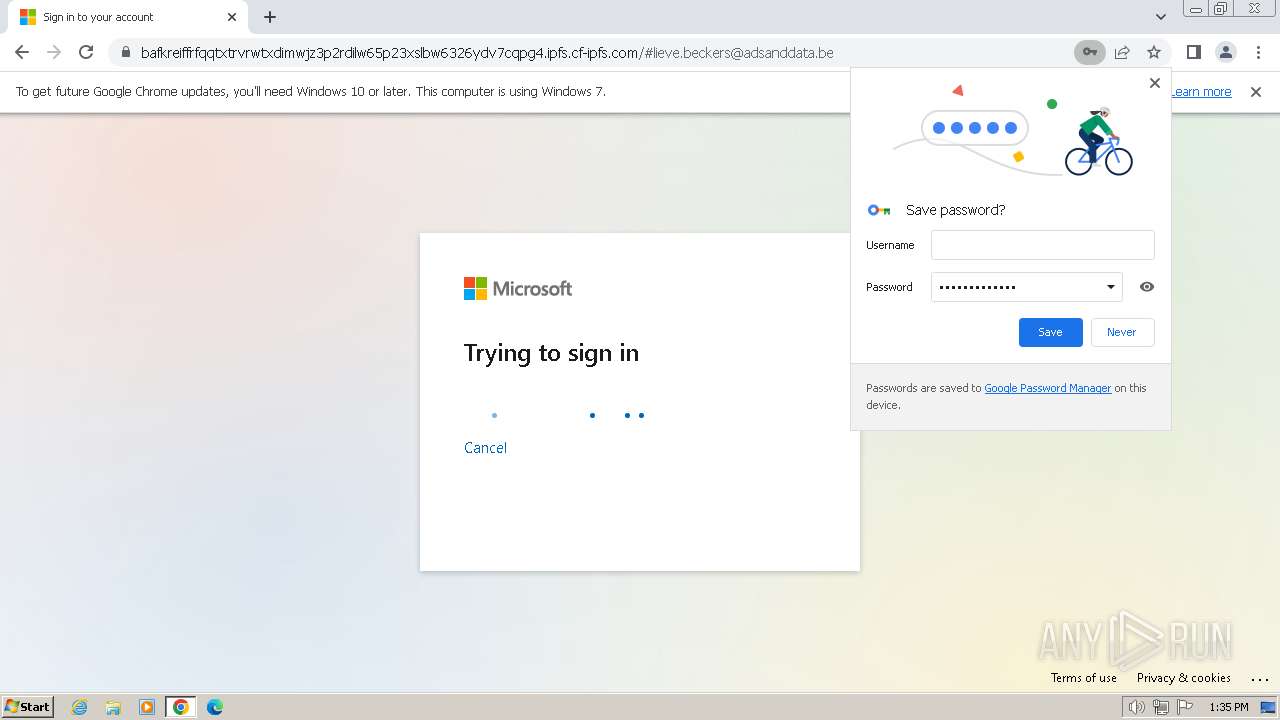
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 3016)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1936)
- chrome.exe (PID: 2028)
Executable content was dropped or overwritten
- chrome.exe (PID: 2100)
Manual execution by a user
- chrome.exe (PID: 2028)
Drops the executable file immediately after the start
- chrome.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
23
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=3696 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3416 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=1364 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=600 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://2n8w.app.link/?~channel=Email&~feature=ConfirmationEmail--AtocETicket&~campaign=WebToApp&~tags=locale%3Den_GB&~tags=version%3D1&~tags=marketing_code%3DBSH3675&$android_url=https%3A%2F%2Fplay.google.com%2Fstore%2Fapps%2Fdetails%3Fid%3Dcom.thetrainline%26hl%3Den-GB&$android_deepview=false&$android_passive_deepview=false&$ios_url=https%3A%2F%2Fitunes.apple.com%2FGB%2Fapp%2Fthetrainline%2Fid334235181&$ios_deepview=false&$ios_passive_deepview=false&$fallback_url=https://dialogichub.com/auth/new/oxyciv/lieve.beckers@adsanddata.be" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1828 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1936 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=964 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=776 --field-trial-handle=1132,i,5696076550146972916,675430680587270165,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
18 728
Read events
18 567
Write events
151
Delete events
10
Modification events
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
176
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | binary | |
MD5:9D5F8F90844722DC00044A5768557B3C | SHA256:A7C81460F96E93EC99D133A510F07120CA0468E588B95610D711A619E504B8D2 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:2FA4E6AE979F97D59A1129F987D0DFA2 | SHA256:C660F4B3CD56652EC35A3A25094CFECF643B72066CB4E4B672DE2CCF9A2A9D5E | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1E7DB96DC54EDB758A04674B3B2D3164 | SHA256:E94087EDD65C2D07F79C4527E3703569621960A6F2701CE3B6BD275D633BC108 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | binary | |
MD5:EBFA9ECC440864CDF399F26B540B0ABB | SHA256:1203D564C8C63C473041020AE416AD1717ECD32CD33F5CD2E991965F7500C616 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9A0D.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:E3E75CCD9FA450A8603ED9B87CFF1907 | SHA256:CCB81C2FD609CE33EBF77A13CBECA6877C8729CE5F734A1026027B74EF9789EF | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9A0C.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\US86LG0U.txt | text | |
MD5:C4E7956CABF88C92BCADC13224B45545 | SHA256:2077F951EC8B57482D6C66FF1524A9FA1FDEB3AF268A282574A3CD3B1EE7D969 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
59
DNS requests
67
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 6.01 Kb | unknown |
2560 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96e261c22e45b24e | DE | — | — | unknown |
2560 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f27fe043238c6b38 | DE | — | — | unknown |
2560 | iexplore.exe | GET | 200 | 18.244.96.220:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 2.02 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 18.244.98.66:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.49 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 18.244.98.66:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.37 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3ecbecc82f68617c | DE | compressed | 65.2 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?325d0c70a8af90be | DE | compressed | 65.2 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 2.19.217.103:80 | http://x1.c.lencr.org/ | NL | binary | 717 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2560 | iexplore.exe | 18.66.233.122:443 | 2n8w.app.link | — | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2560 | iexplore.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2560 | iexplore.exe | 18.244.96.220:80 | o.ss2.us | — | US | unknown |
2560 | iexplore.exe | 18.244.98.66:80 | ocsp.rootg2.amazontrust.com | — | US | unknown |
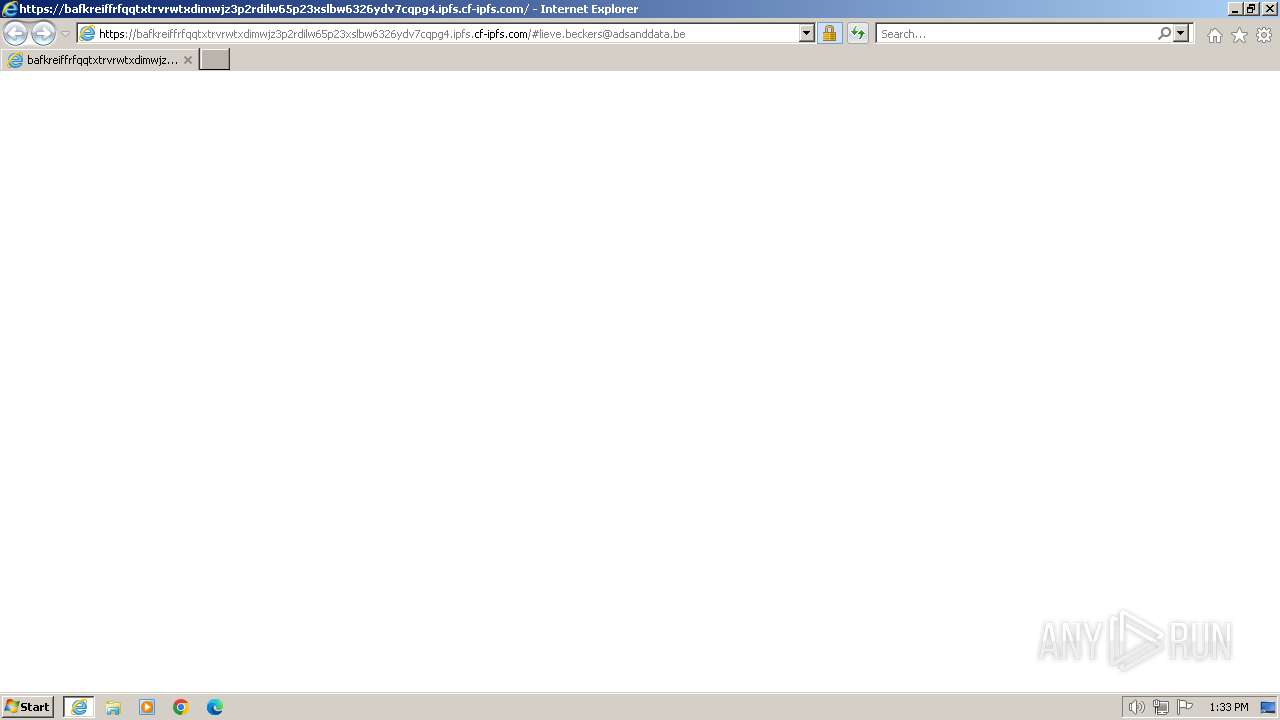
2560 | iexplore.exe | 188.114.96.3:443 | dialogichub.com | CLOUDFLARENET | NL | unknown |
2560 | iexplore.exe | 2.19.217.103:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
1936 | iexplore.exe | 188.114.96.3:443 | dialogichub.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2n8w.app.link |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
dialogichub.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
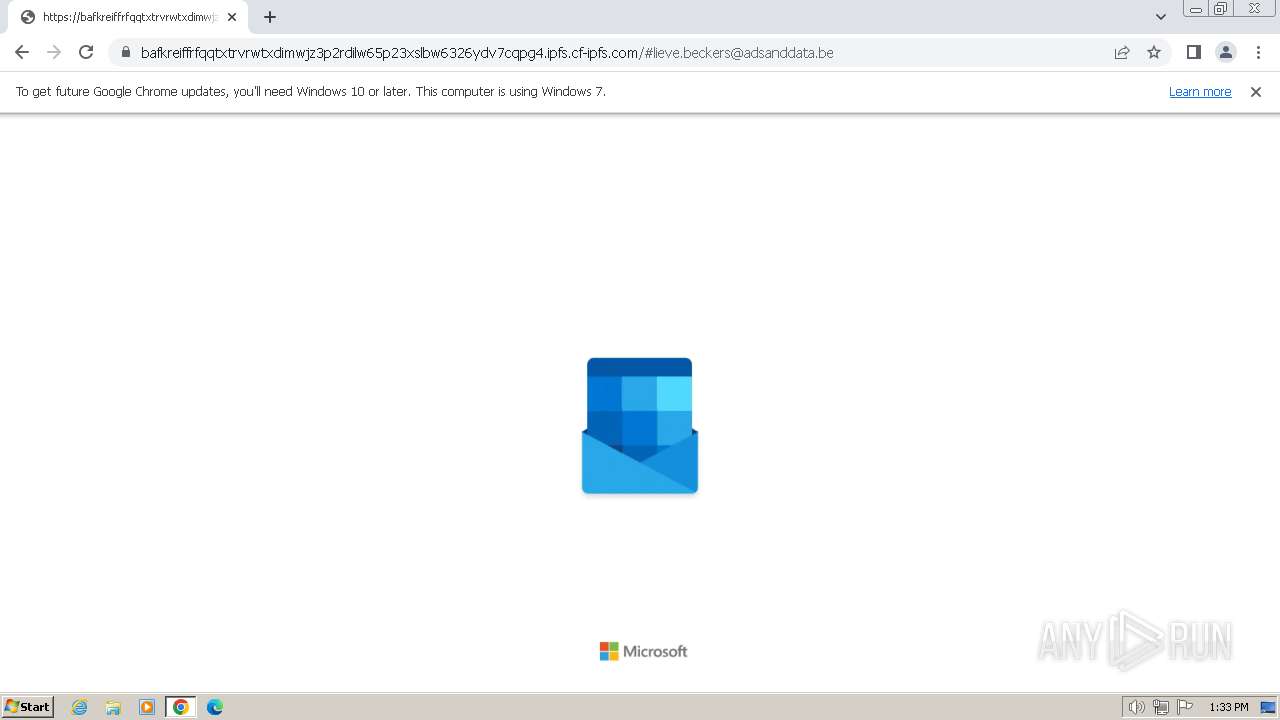
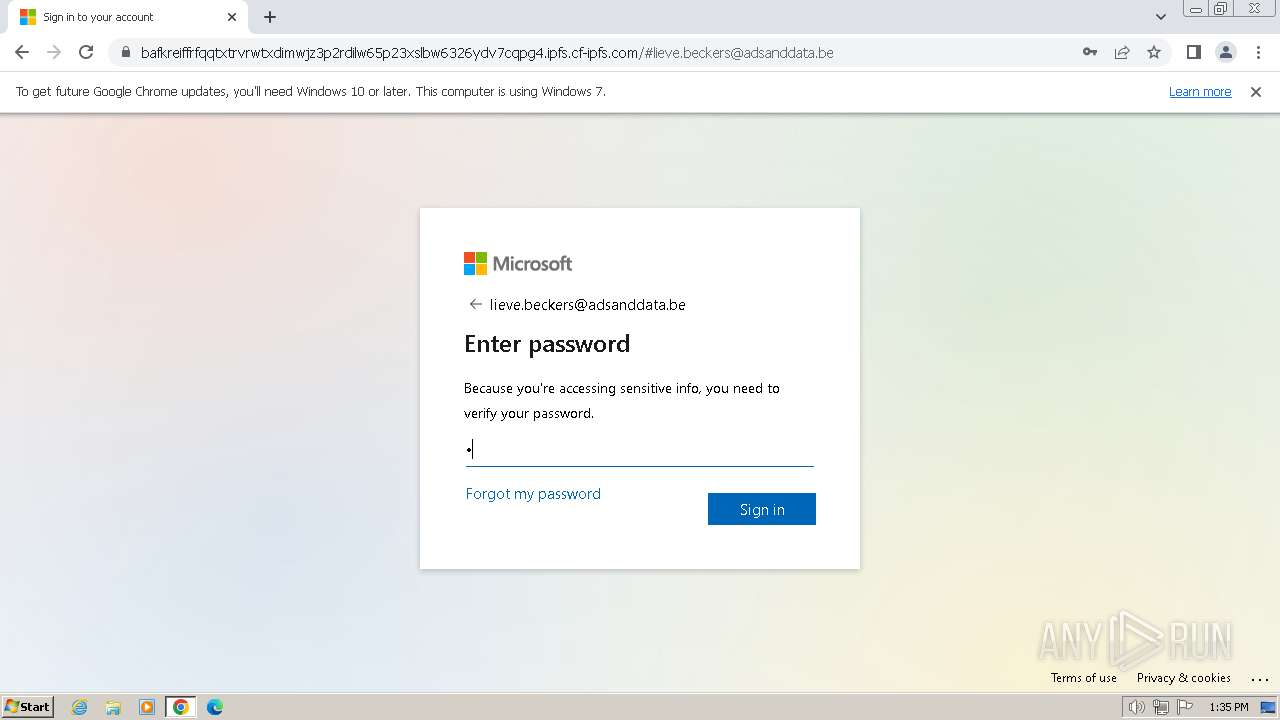
bafkreiffrfqqtxtrvrwtxdimwjz3p2rdilw65p23xslbw6326ydv7cqpg4.ipfs.cf-ipfs.com |
| unknown |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cf-ipfs .com) |
2560 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
2560 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
1936 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
1936 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
3016 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cf-ipfs .com) |
3016 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cf-ipfs .com) |
3016 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
3016 | chrome.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cf-ipfs .com) |
3016 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |