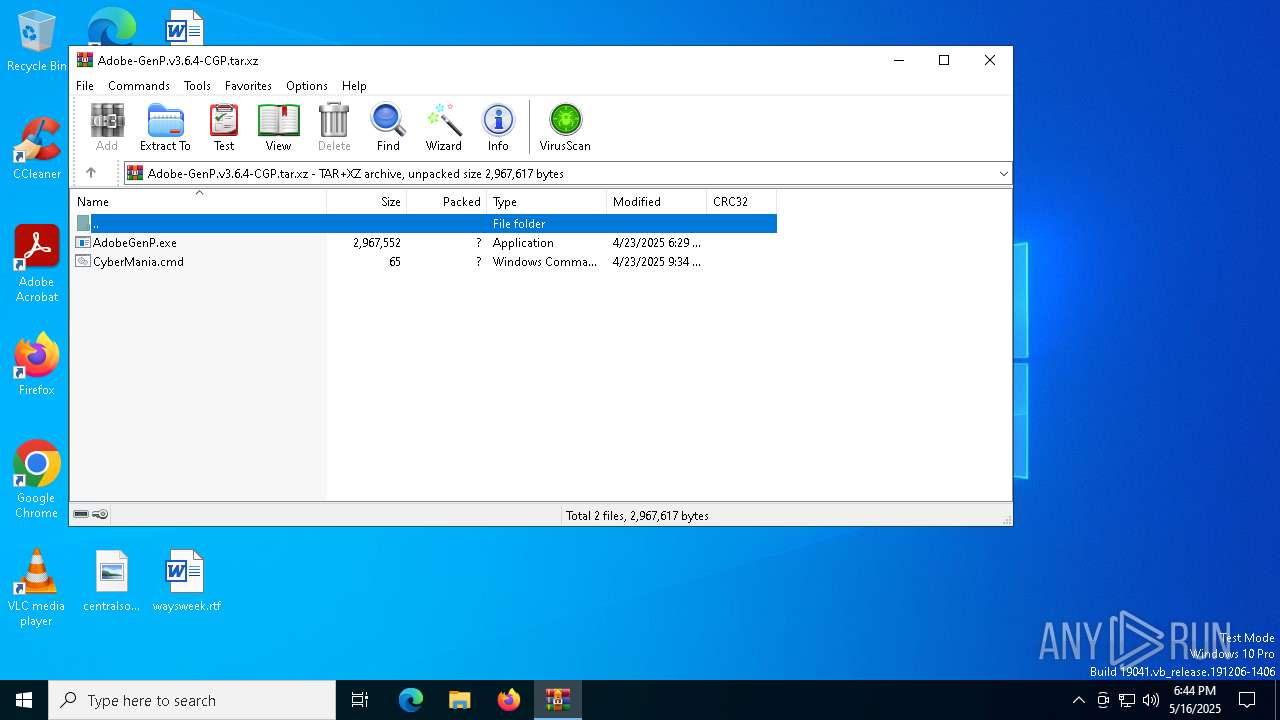
| File name: | Adobe-GenP.v3.6.4-CGP.tar.xz |
| Full analysis: | https://app.any.run/tasks/79129196-32a5-4c9c-9526-316b691654f8 |
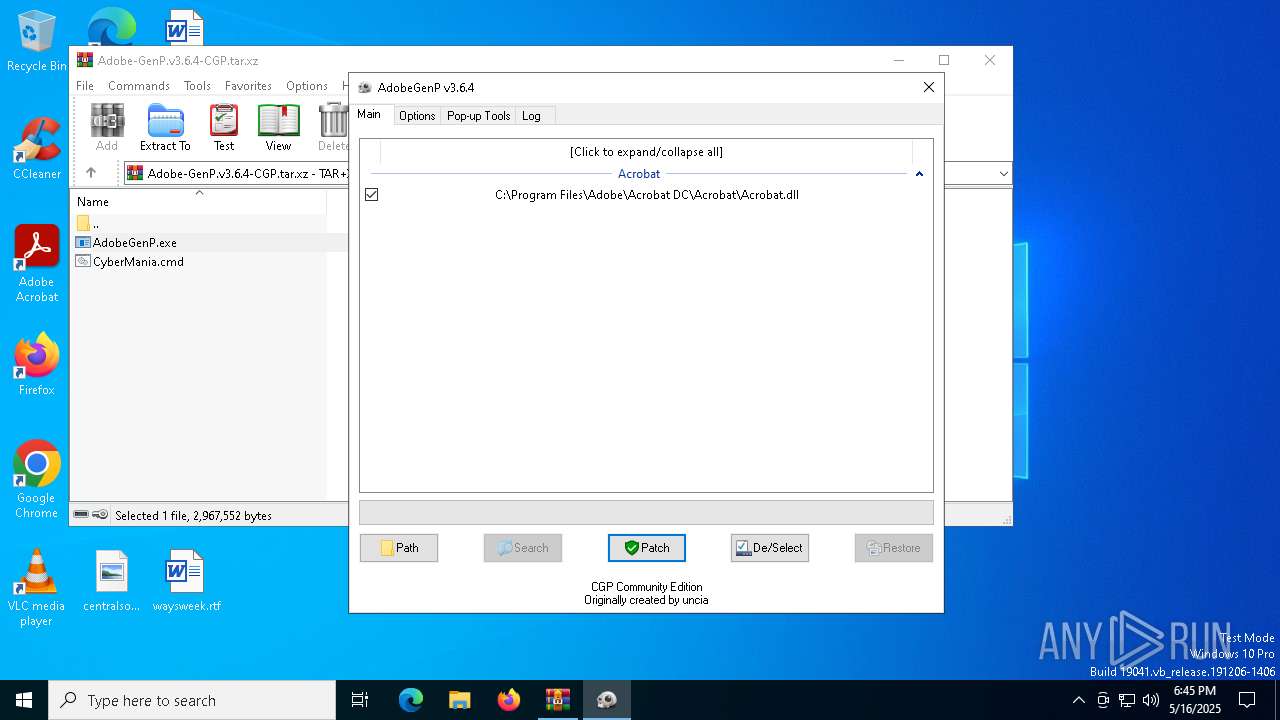
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 18:44:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-xz |
| File info: | XZ compressed data, checksum CRC32 |
| MD5: | A184AA359490BD6D8E90A28885C72B8A |
| SHA1: | FF793B1E978EAEE696558B3DB48FD36ECB3407F3 |
| SHA256: | 56B573417C4656025F46AF90EFE46AF652DF3D7D8E3DA0C6E93C2295CC027B73 |
| SSDEEP: | 98304:jsAgI2hSwHdwR2I7sE33UVZ6lmUG8jC7LfUUBmk8QXkozvuWVdaPelIVgVtBhxPo:Z7vfyS |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7276)
GENERIC has been found (auto)
- WinRAR.exe (PID: 7276)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7276)
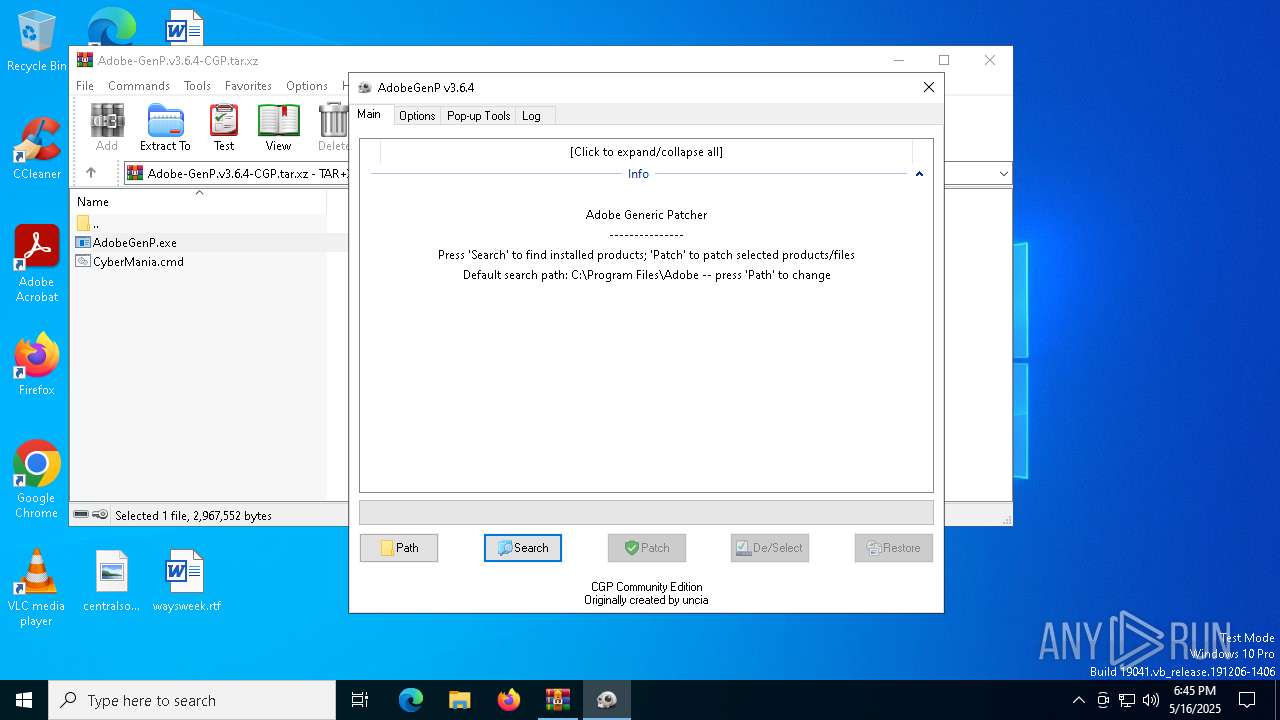
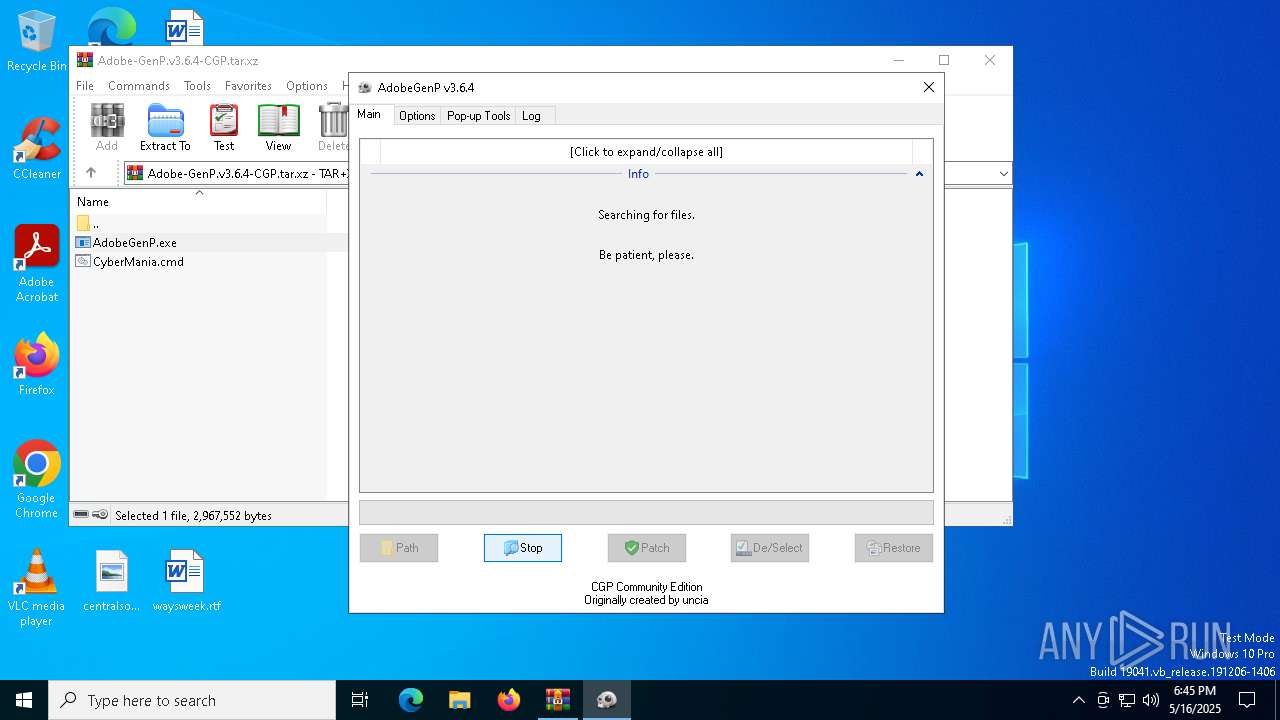
ADOBEGENP mutex has been found
- AdobeGenP.exe (PID: 4880)
INFO
Reads mouse settings
- AdobeGenP.exe (PID: 4880)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7276)
Checks supported languages
- AdobeGenP.exe (PID: 4880)
Create files in a temporary directory
- AdobeGenP.exe (PID: 4880)
Reads the computer name
- AdobeGenP.exe (PID: 4880)
The sample compiled with english language support
- WinRAR.exe (PID: 7276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xz | | | xz compressed container (85.7) |
|---|
Total processes
134
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
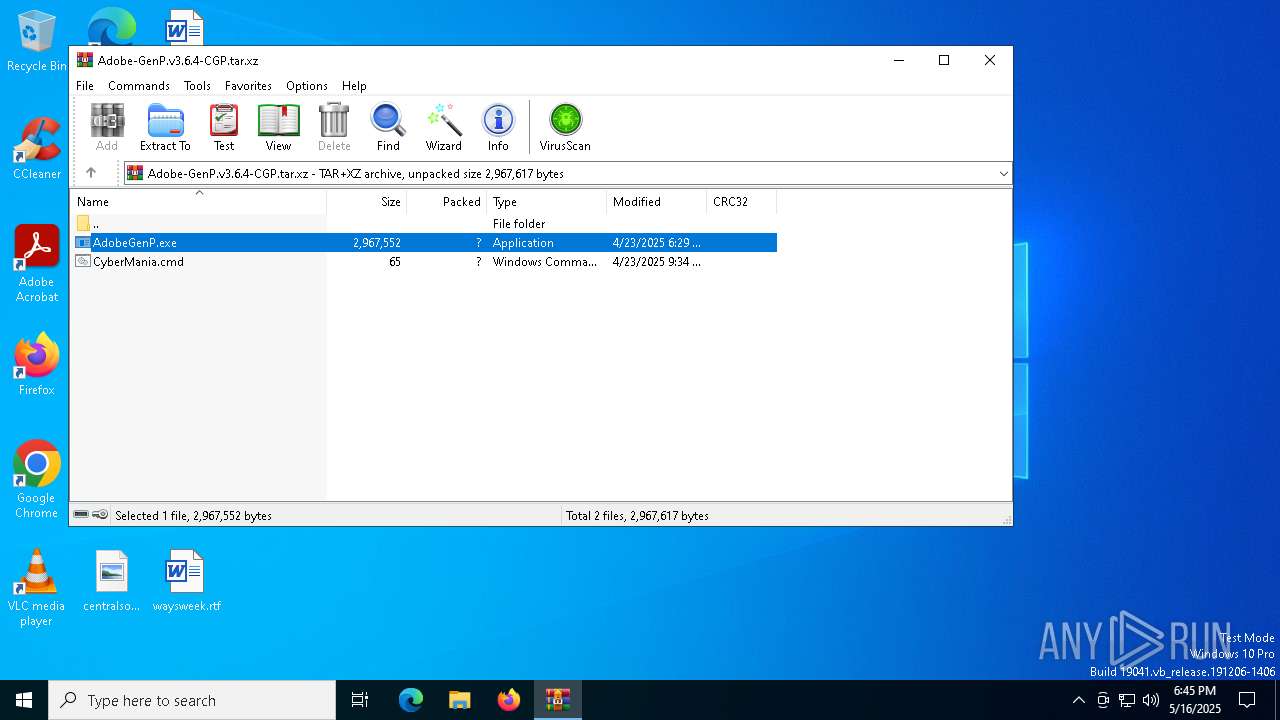
| 496 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\AdobeGenP.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\AdobeGenP.exe | — | WinRAR.exe | |||||||||||
User: admin Company: AdobeGenp Integrity Level: MEDIUM Description: Adobe Generic Patcher Exit code: 3221226540 Version: 3.6.4.0 Modules
| |||||||||||||||
| 4880 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\AdobeGenP.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\AdobeGenP.exe | WinRAR.exe | ||||||||||||
User: admin Company: AdobeGenp Integrity Level: HIGH Description: Adobe Generic Patcher Version: 3.6.4.0 Modules
| |||||||||||||||
| 7276 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Adobe-GenP.v3.6.4-CGP.tar.xz | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7448 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7488 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 984
Read events
1 976
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Adobe-GenP.v3.6.4-CGP.tar.xz | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\CyberMania.cmd | text | |
MD5:56A47F2231E05274B54A18B9B33713FB | SHA256:6912D7554AD3851B8EB3996D205B3CE149AE26088E87FEDA9A2707E6D09EE13D | |||
| 4880 | AdobeGenP.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\config.ini | text | |
MD5:FABC1F7F0E77C6882B9A16851E7D7E77 | SHA256:5E9A06AB44D12EC8AAAF3918859E8ED807E76CC58B7FEEB9B25741DE8AC4C56D | |||
| 7276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7276.44796\AdobeGenP.exe | executable | |
MD5:859E24EAF9E2B231CF7FADF25D8DB232 | SHA256:B92860632A6DDAE2532206833CC0C4A18548D469136271ACDBD760E4986E260B | |||
| 4880 | AdobeGenP.exe | C:\Users\admin\AppData\Local\Temp\aut83A4.tmp | binary | |
MD5:FC28D09F35A6D32EAE8D4CAF9BFF09D1 | SHA256:5B3003EE371F41596FBB89A40B0126BA3980E8D8FAF1DBE4B7388E462BF44442 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |