| File name: | Creation_Made_By_Canva.mp4 - canva.com |
| Full analysis: | https://app.any.run/tasks/0ae5c49e-0b85-4439-8ff2-6d2bf80154c6 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2025, 08:31:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F71BA51C6A92519AF9537DA4CBB80CE8 |
| SHA1: | CB563B2DA789D8E9ACF943BEF12E1C89E722FBC5 |
| SHA256: | 56B540EFA56FB641D8F5C9705197422BEA0259EF5E0517661797D76FE3786B4A |
| SSDEEP: | 98304:MVJzzI0CPVRVUGOytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/W8DrRVlEbwux3H:TDAGlpHh8xBXNw |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 7580)
SUSPICIOUS
Reads security settings of Internet Explorer
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
- ScreenConnect.WindowsClient.exe (PID: 7556)
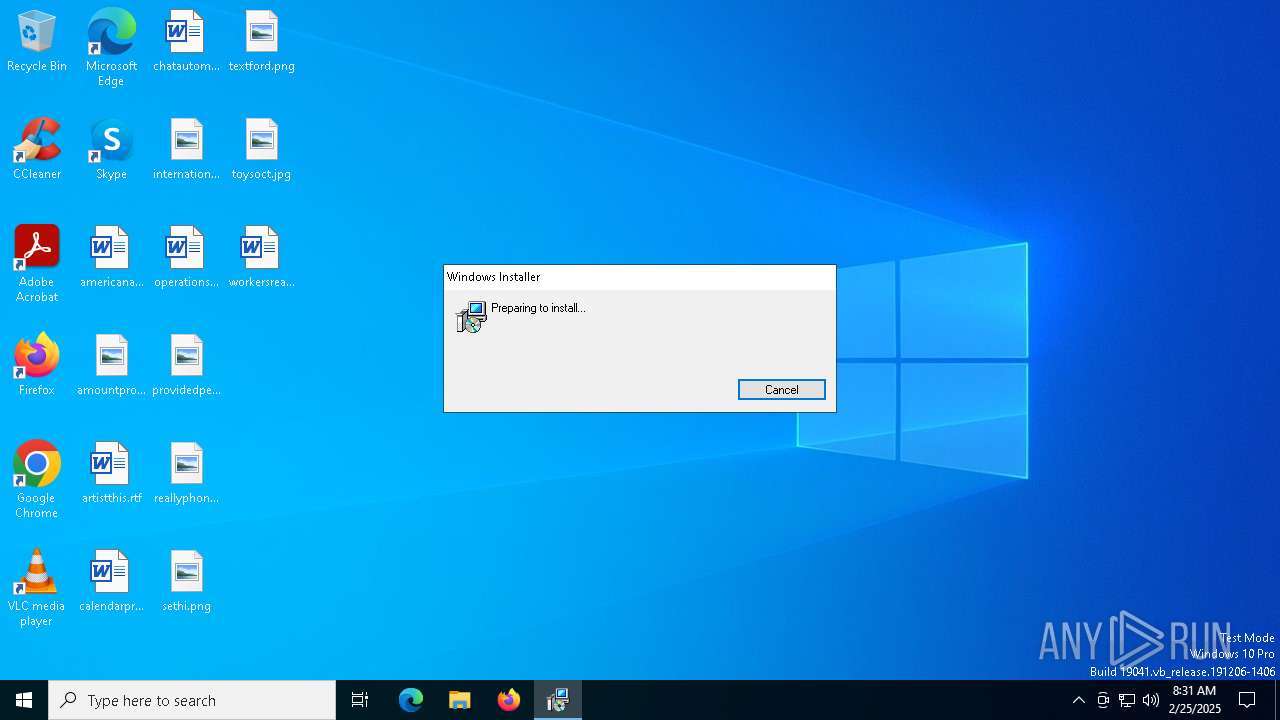
Executable content was dropped or overwritten
- rundll32.exe (PID: 2336)
Executes as Windows Service
- VSSVC.exe (PID: 6192)
- ScreenConnect.ClientService.exe (PID: 7580)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 7580)
- msiexec.exe (PID: 5232)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 5232)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 7580)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 7580)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 7580)
INFO
Checks supported languages
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
- msiexec.exe (PID: 7052)
- msiexec.exe (PID: 5232)
- msiexec.exe (PID: 7248)
- ScreenConnect.ClientService.exe (PID: 7580)
Reads the computer name
- msiexec.exe (PID: 5232)
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
- msiexec.exe (PID: 7052)
Reads the machine GUID from the registry
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
- ScreenConnect.ClientService.exe (PID: 7580)
- ScreenConnect.WindowsClient.exe (PID: 7556)
Process checks computer location settings
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
Create files in a temporary directory
- Creation_Made_By_Canva.mp4 - canva.com.exe (PID: 7084)
- rundll32.exe (PID: 2336)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5988)
- msiexec.exe (PID: 5232)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7332)
- BackgroundTransferHost.exe (PID: 7744)
- BackgroundTransferHost.exe (PID: 7964)
- BackgroundTransferHost.exe (PID: 8176)
- BackgroundTransferHost.exe (PID: 7572)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7572)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7572)
Manages system restore points
- SrTasks.exe (PID: 7540)
Creates a software uninstall entry
- msiexec.exe (PID: 5232)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5489664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
157
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2336 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI86CC.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1214250 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5232 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.4.4.9118\aeef6885fa9229dd\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | Creation_Made_By_Canva.mp4 - canva.com.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6108 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6824 | "C:\Users\admin\AppData\Local\Temp\Creation_Made_By_Canva.mp4 - canva.com.exe" | C:\Users\admin\AppData\Local\Temp\Creation_Made_By_Canva.mp4 - canva.com.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7052 | C:\Windows\syswow64\MsiExec.exe -Embedding 81F4371B65EBD994E0ECB4E3D45044E6 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7084 | "C:\Users\admin\AppData\Local\Temp\Creation_Made_By_Canva.mp4 - canva.com.exe" | C:\Users\admin\AppData\Local\Temp\Creation_Made_By_Canva.mp4 - canva.com.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7248 | C:\Windows\syswow64\MsiExec.exe -Embedding EBC3F54F286D7EDB593DF1EF243396A2 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 725
Read events
7 432
Write events
276
Delete events
17
Modification events
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000045EE1FAC5F87DB017014000070130000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000E5B624AC5F87DB017014000070130000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000BF4FC5AB5F87DB017014000070130000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000BF4FC5AB5F87DB017014000070130000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000D1271BAC5F87DB017014000070130000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000D1271BAC5F87DB017014000070130000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6192) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000007D74C4AC5F87DB0130180000501A0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000653CAAAC5F87DB017014000070130000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5232) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B99FACAC5F87DB0170140000080A0000E8030000010000000000000000000000D789D9BB8624494094BA858BA49D7A0E00000000000000000000000000000000 | |||
Executable files
20
Suspicious files
25
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7084 | Creation_Made_By_Canva.mp4 - canva.com.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.4.4.9118\aeef6885fa9229dd\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 7572 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\52f6d5b3-47fb-40cf-9123-a6cbe061ff9c.down_data | — | |
MD5:— | SHA256:— | |||
| 5232 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5232 | msiexec.exe | C:\Windows\Installer\12d588.msi | — | |
MD5:— | SHA256:— | |||
| 2336 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI86CC.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:7572B9AE2ECF5946645863A828678B5A | SHA256:BE89FE3C59FD927B3B45FEBD183FDDC1D990994D4B64D689EB04A40D8964F493 | |||
| 5988 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI86CC.tmp | executable | |
MD5:4ABAD4FD1A22BC922B457C28D1E40F1A | SHA256:DB51E4B70F27D0BF28789EA3345BF693035916461D22661C26F149C5BC8891ED | |||
| 2336 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI86CC.tmp-\Microsoft.Deployment.Compression.dll | executable | |
MD5:4717BCC62EB45D12FFBED3A35BA20E25 | SHA256:E04DE7988A2A39931831977FA22D2A4C39CF3F70211B77B618CAE9243170F1A7 | |||
| 7572 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\52f6d5b3-47fb-40cf-9123-a6cbe061ff9c.b2ab933e-0322-4622-a635-8810886f48b5.down_meta | binary | |
MD5:EB93B813D51261A96105281190662A89 | SHA256:BACF2AD5CB4BB70A3031FA9E7A0748C484047BBCCB882688898B21D96ADEEBF8 | |||
| 5232 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:F20D750448C7F51958B616307C36FACF | SHA256:151F3765B0651610723114E9E09A6148EDB1D3A9160AB465F2D5E758CCDE4D58 | |||
| 5232 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{bbd989d7-2486-4049-94ba-858ba49d7a0e}_OnDiskSnapshotProp | binary | |
MD5:F20D750448C7F51958B616307C36FACF | SHA256:151F3765B0651610723114E9E09A6148EDB1D3A9160AB465F2D5E758CCDE4D58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
36
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7572 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
7744 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 408 b | whitelisted |
7744 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2740 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
404 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.6:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4136 | backgroundTaskHost.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6760 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
jtsec.innocreed.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7580 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |