| File name: | autoruni.pee |
| Full analysis: | https://app.any.run/tasks/6c79b21e-3677-43ac-9fc1-6a74874a31b6 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 17:48:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Petite compressed |
| MD5: | AAE219D4E703051D60351F73CA288D1D |
| SHA1: | 1B28CBC3D27A92281EBF4754C27B9AC4A3A8C214 |
| SHA256: | 56947C93FB17D3339FF2A778556F4A4F95516FB5112DB61AE0804ECDCF4D1307 |
| SSDEEP: | 3072:J2MWsQvnyo/CtkgEcnz7fsmqLGnQ7eMDLyPexpZ:J2jsgpYtEcnzwlLFeMD2Pex |
MALICIOUS
Disables registry editing tools (regedit)
- wins.exe (PID: 3352)
- LeChucK.exe (PID: 3356)
- autoruni.pee.exe (PID: 3432)
Disables Windows System Restore
- wins.exe (PID: 3352)
SUSPICIOUS
Starts CMD.EXE for commands execution
- autoruni.pee.exe (PID: 2132)
- autoruni.pee.exe (PID: 3432)
- LeChucK.exe (PID: 3356)
- wins.exe (PID: 3352)
Modifies the open verb of a shell class
- autoruni.pee.exe (PID: 2132)
- wins.exe (PID: 3352)
- LeChucK.exe (PID: 3356)
- autoruni.pee.exe (PID: 3432)
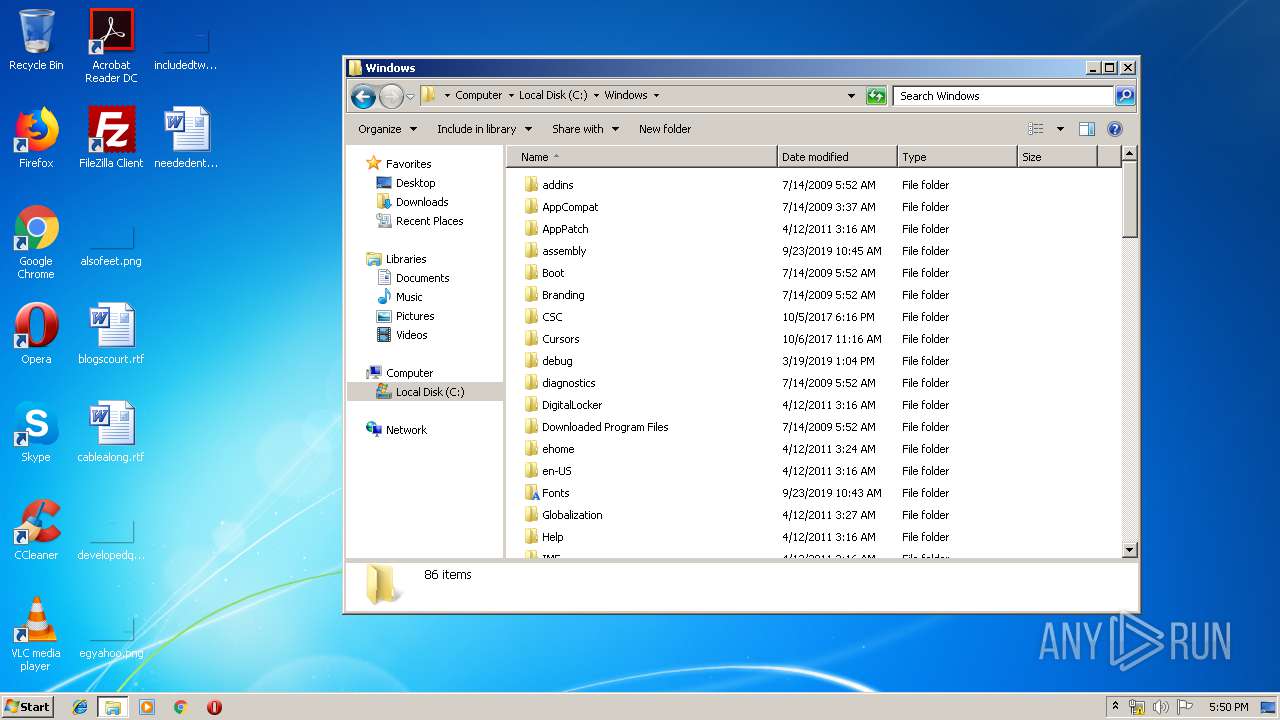
Uses ATTRIB.EXE to modify file attributes
- Cmd.exe (PID: 332)
- Cmd.exe (PID: 4056)
- Cmd.exe (PID: 2800)
- Cmd.exe (PID: 640)
- Cmd.exe (PID: 1740)
- Cmd.exe (PID: 996)
- Cmd.exe (PID: 2644)
- Cmd.exe (PID: 2384)
- Cmd.exe (PID: 2692)
- Cmd.exe (PID: 1948)
- Cmd.exe (PID: 2368)
- Cmd.exe (PID: 3256)
- Cmd.exe (PID: 656)
- Cmd.exe (PID: 3124)
- Cmd.exe (PID: 3384)
- Cmd.exe (PID: 2208)
- Cmd.exe (PID: 2968)
- Cmd.exe (PID: 2424)
- Cmd.exe (PID: 3392)
- Cmd.exe (PID: 3620)
- Cmd.exe (PID: 3780)
- Cmd.exe (PID: 2472)
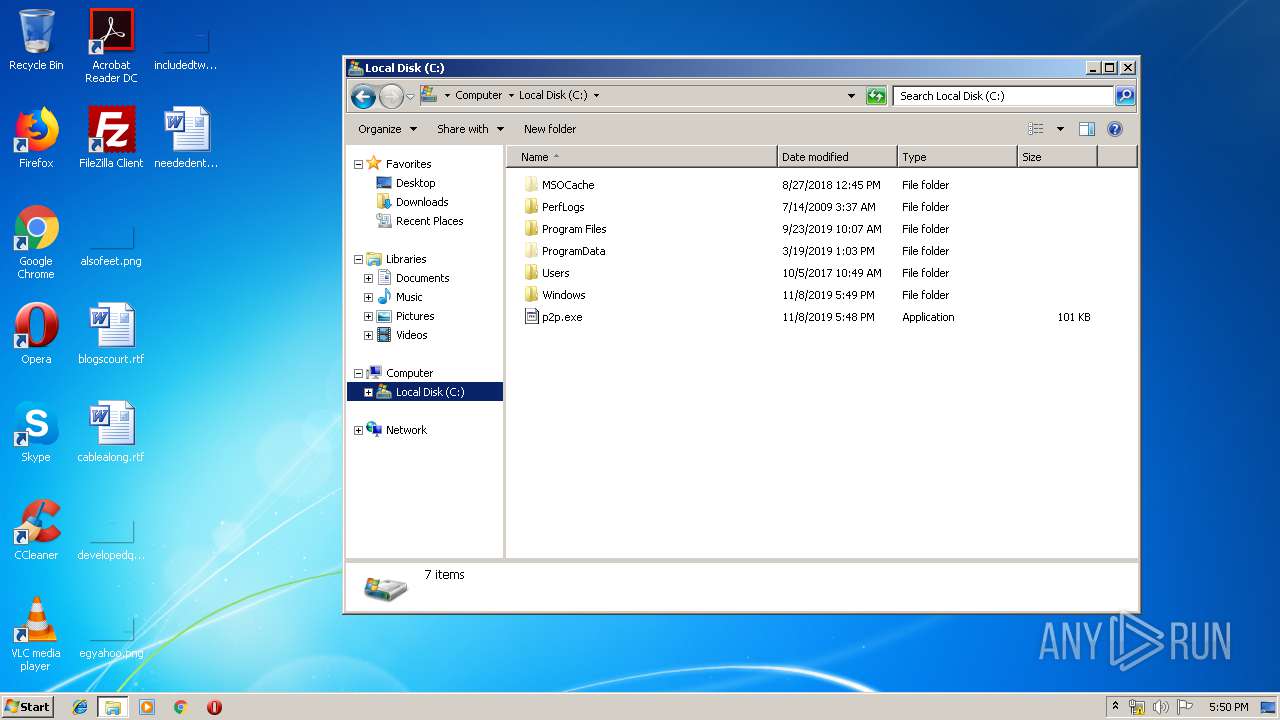
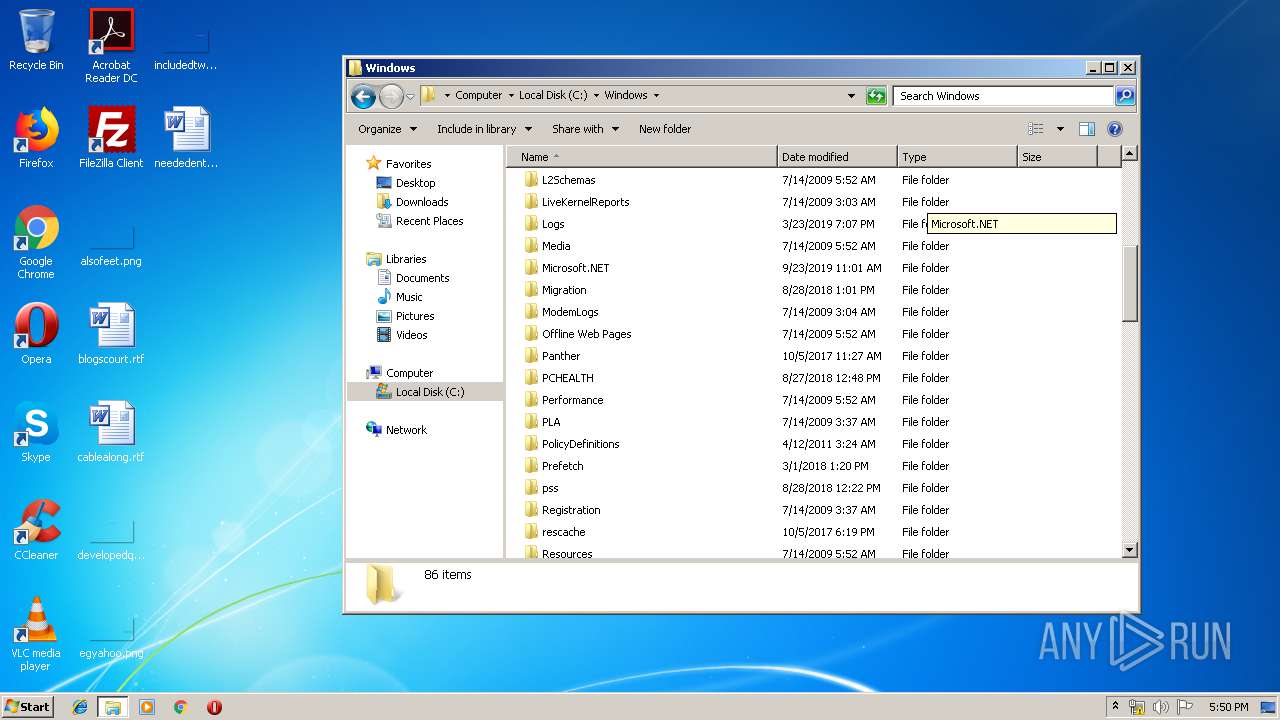
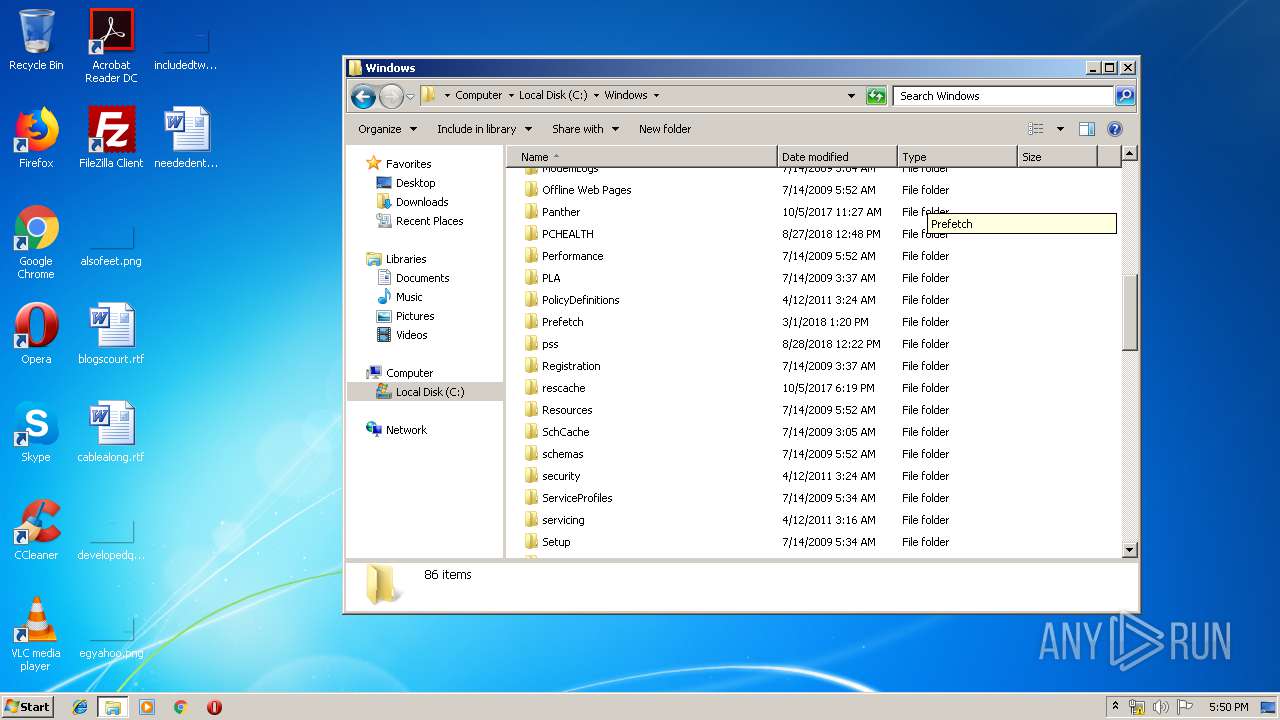
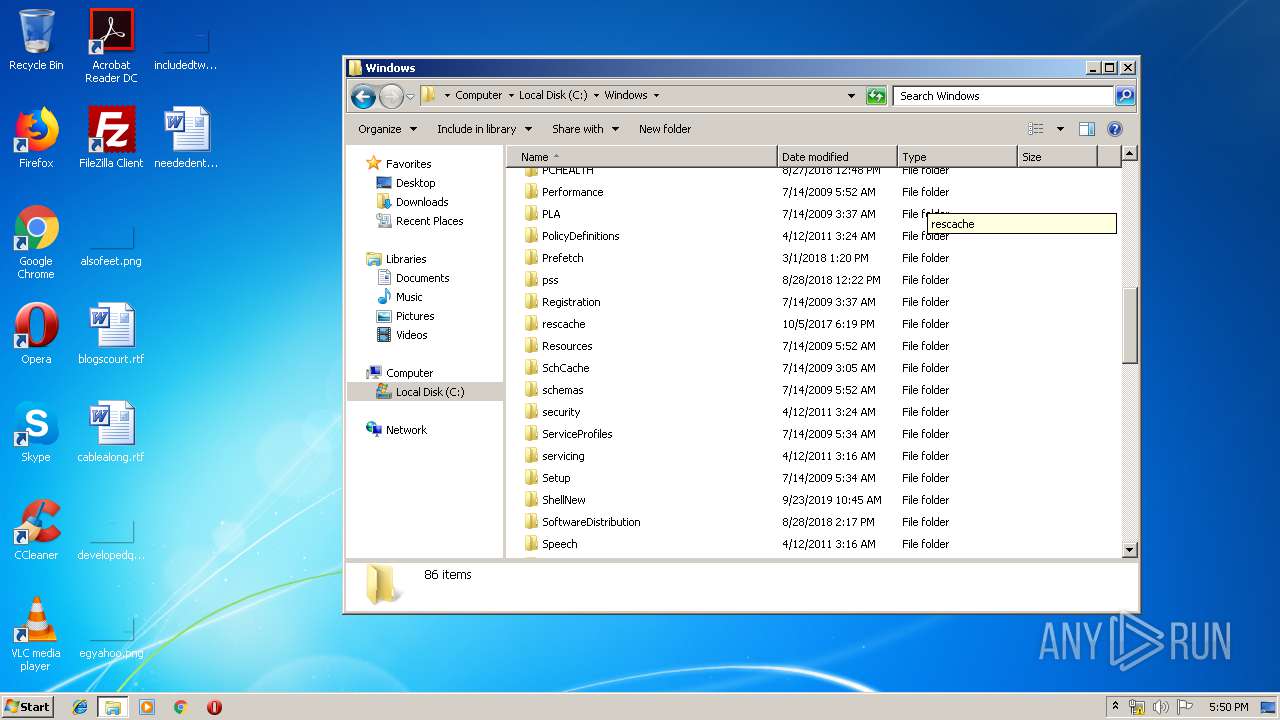
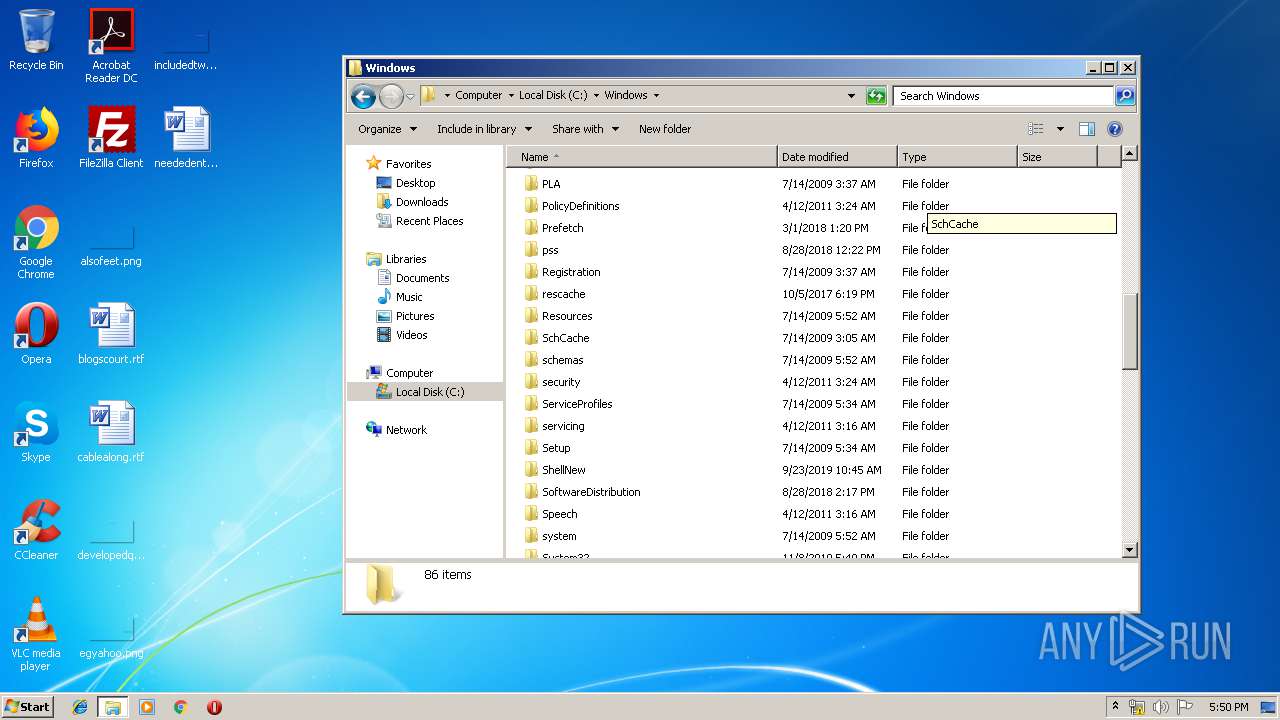
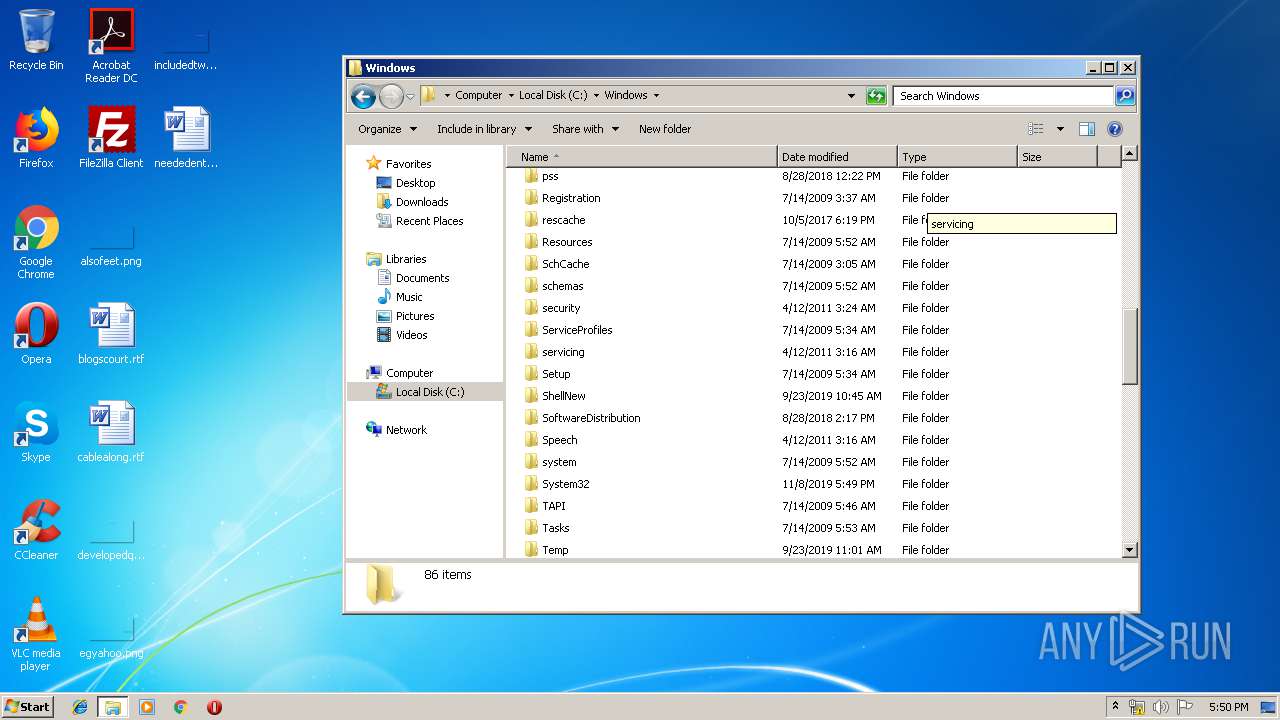
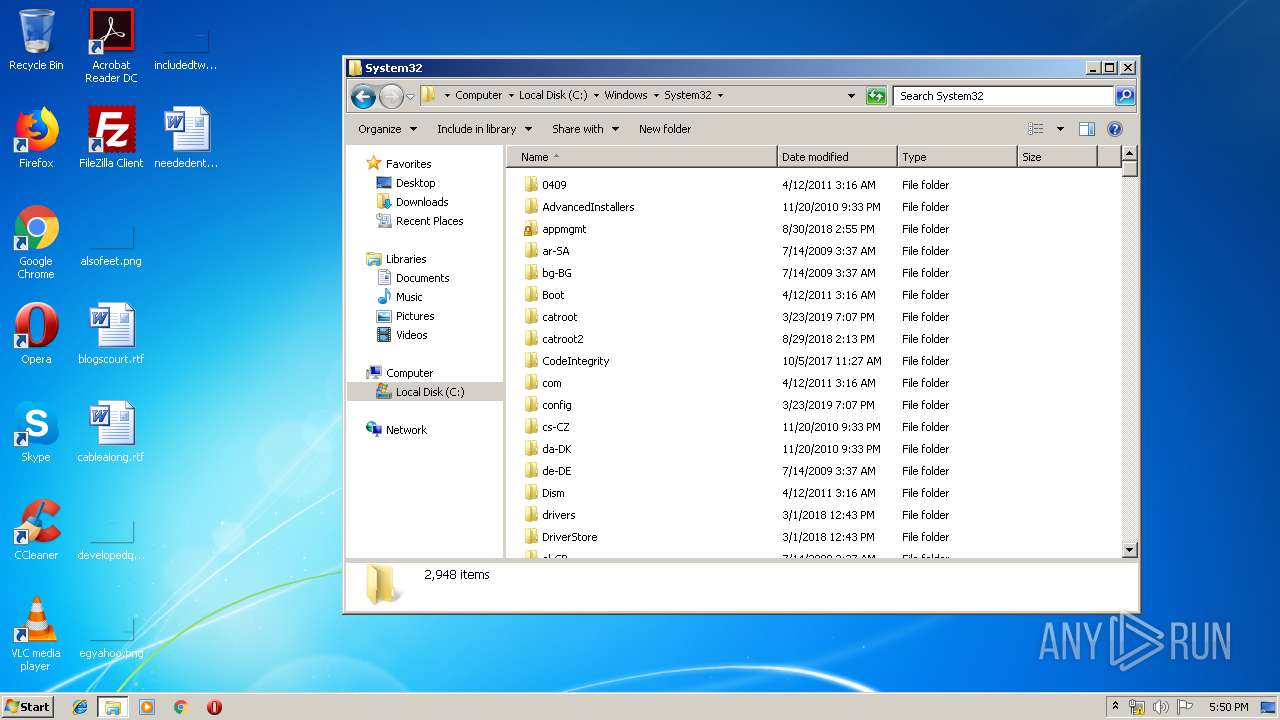
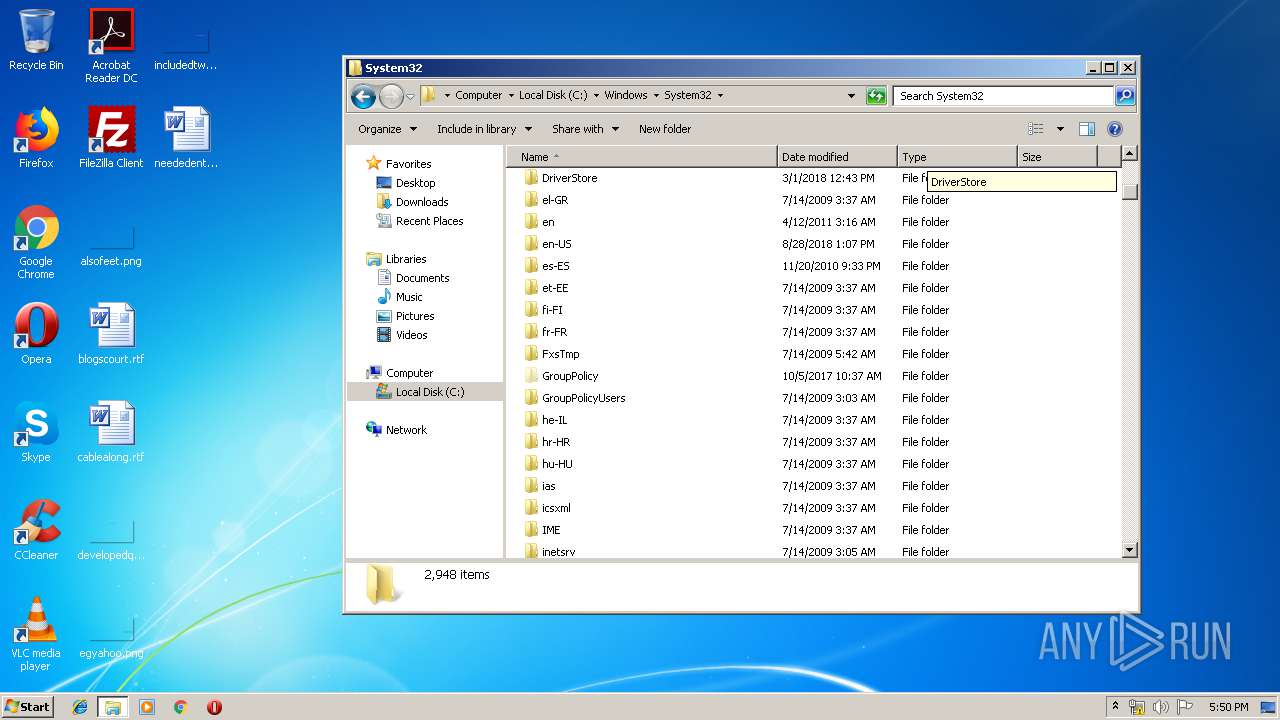
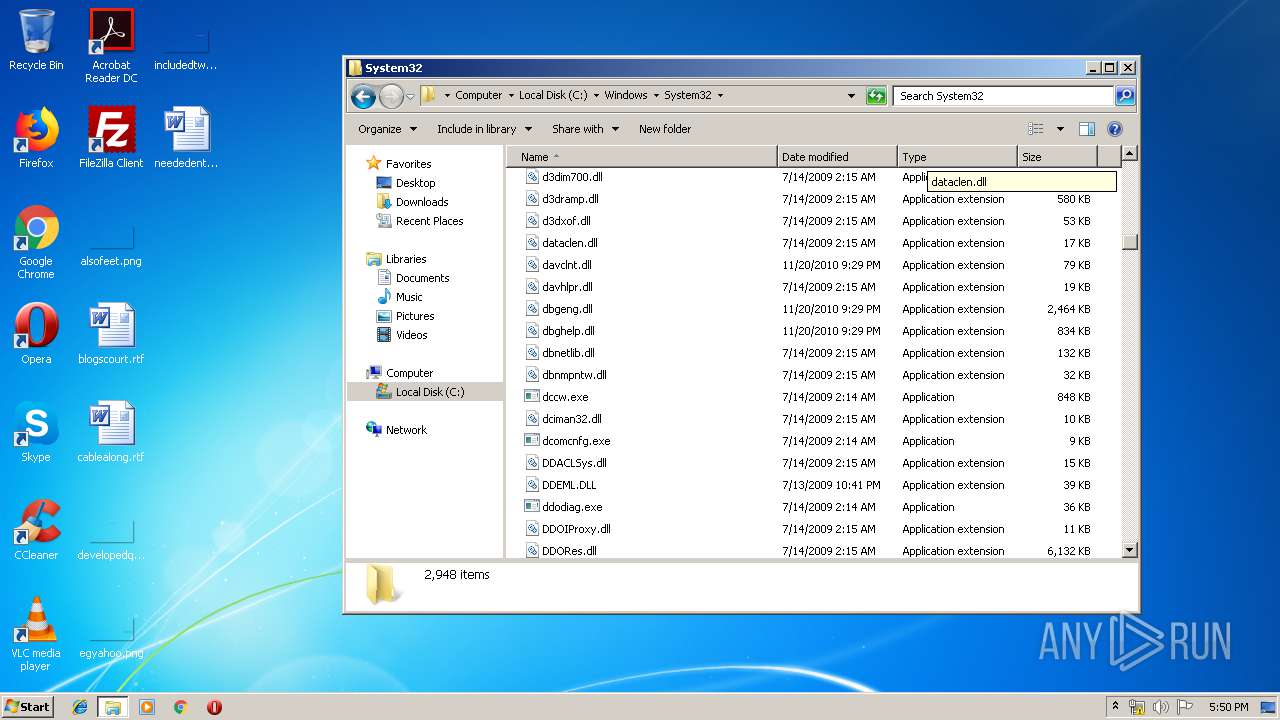
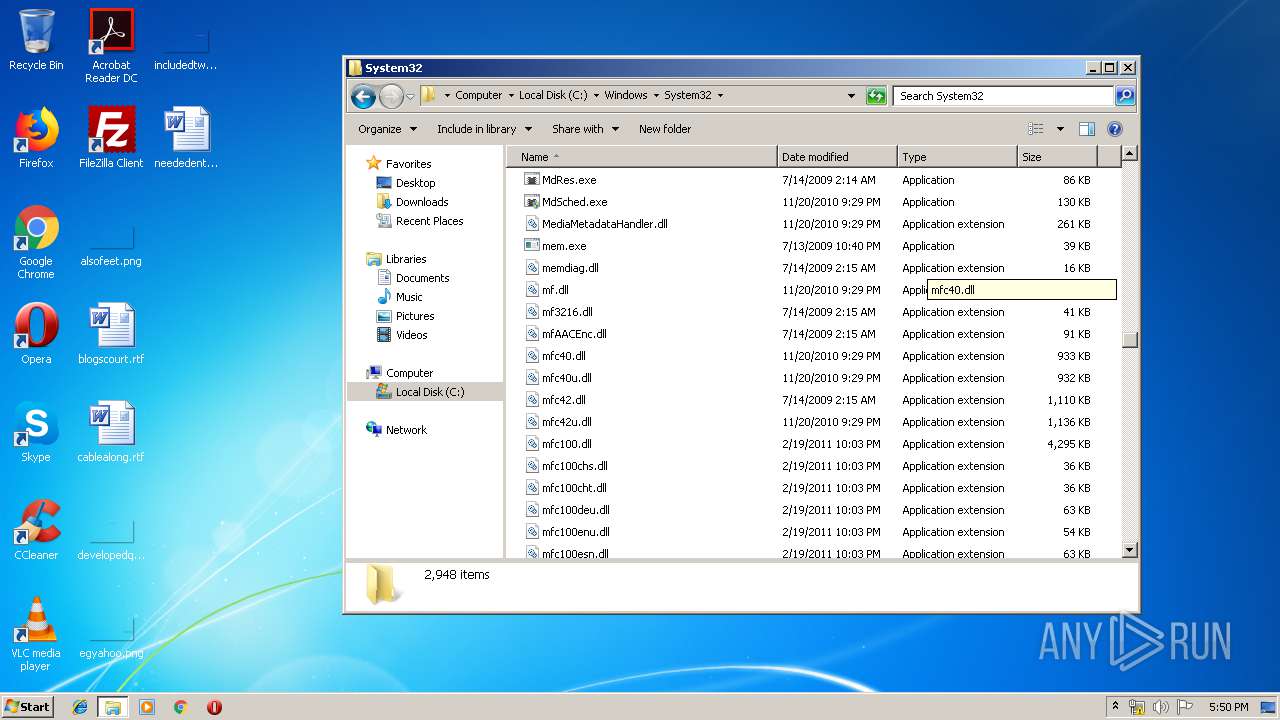
Creates files in the Windows directory
- autoruni.pee.exe (PID: 3432)
- LeChucK.exe (PID: 3356)
Executable content was dropped or overwritten
- autoruni.pee.exe (PID: 3432)
- LeChucK.exe (PID: 3356)
Application launched itself
- LeChucK.exe (PID: 3356)
- wins.exe (PID: 3352)
Starts itself from another location
- LeChucK.exe (PID: 3356)
- autoruni.pee.exe (PID: 3432)
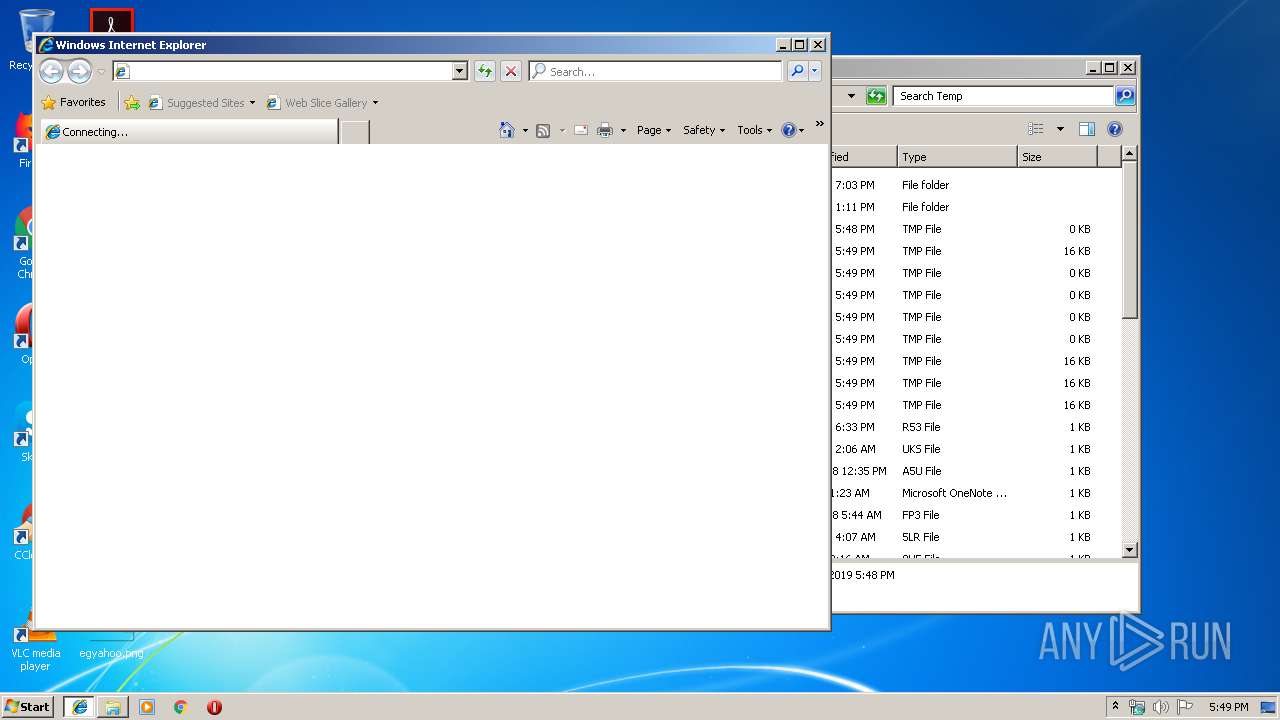
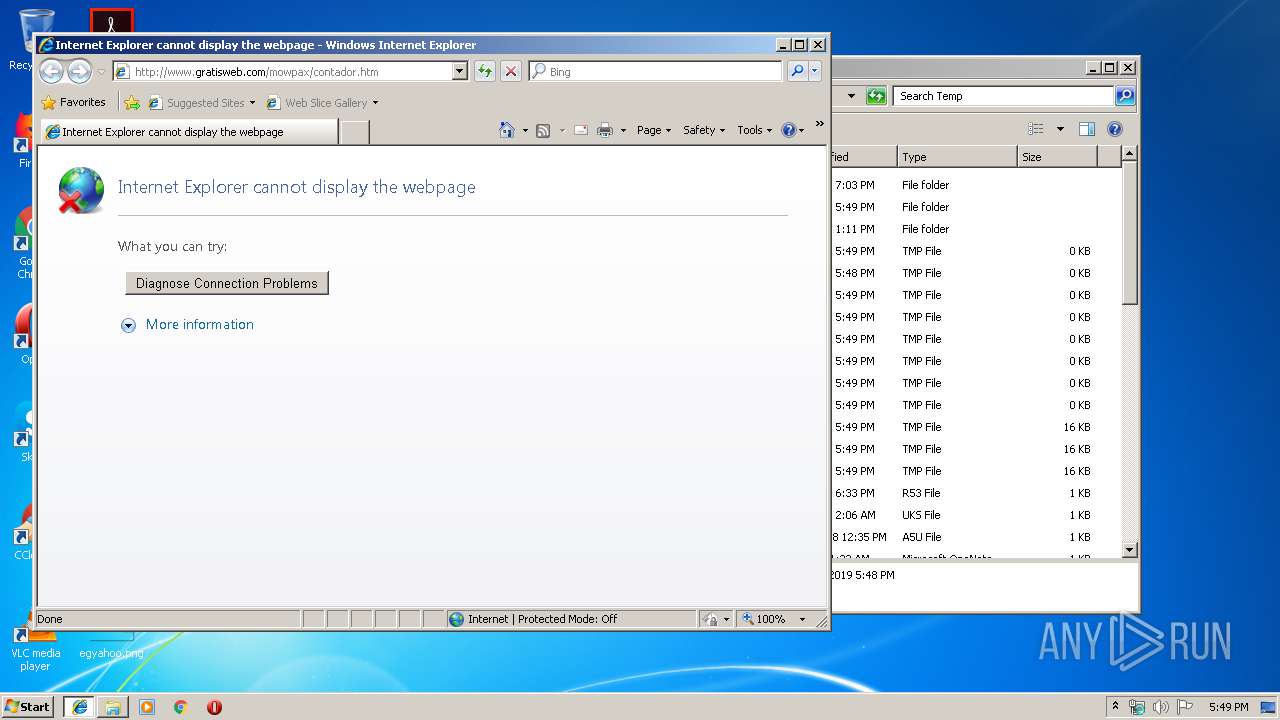
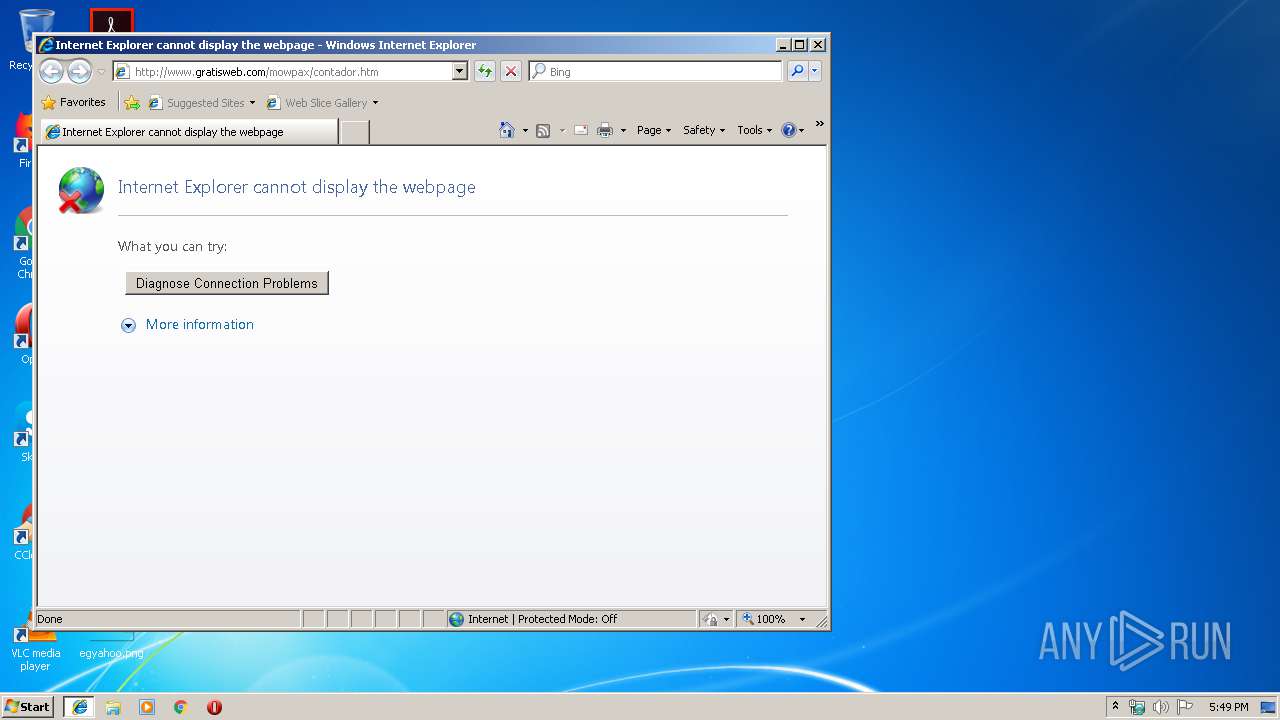
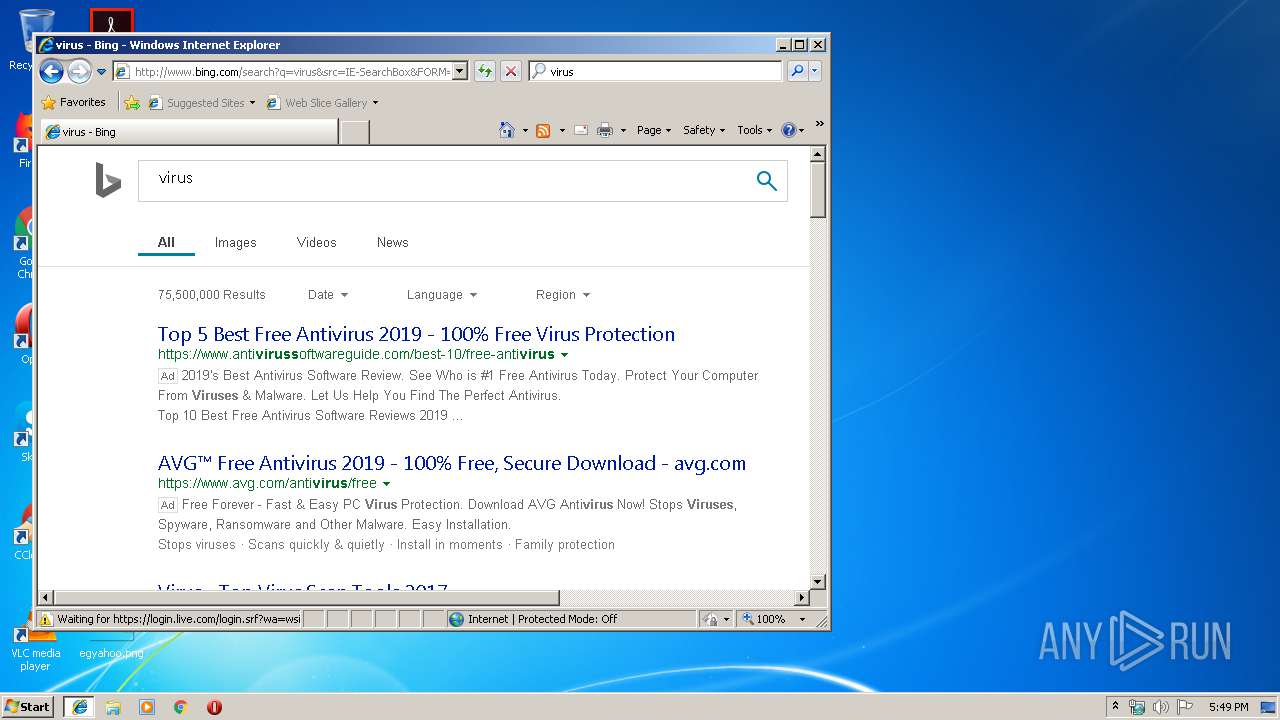
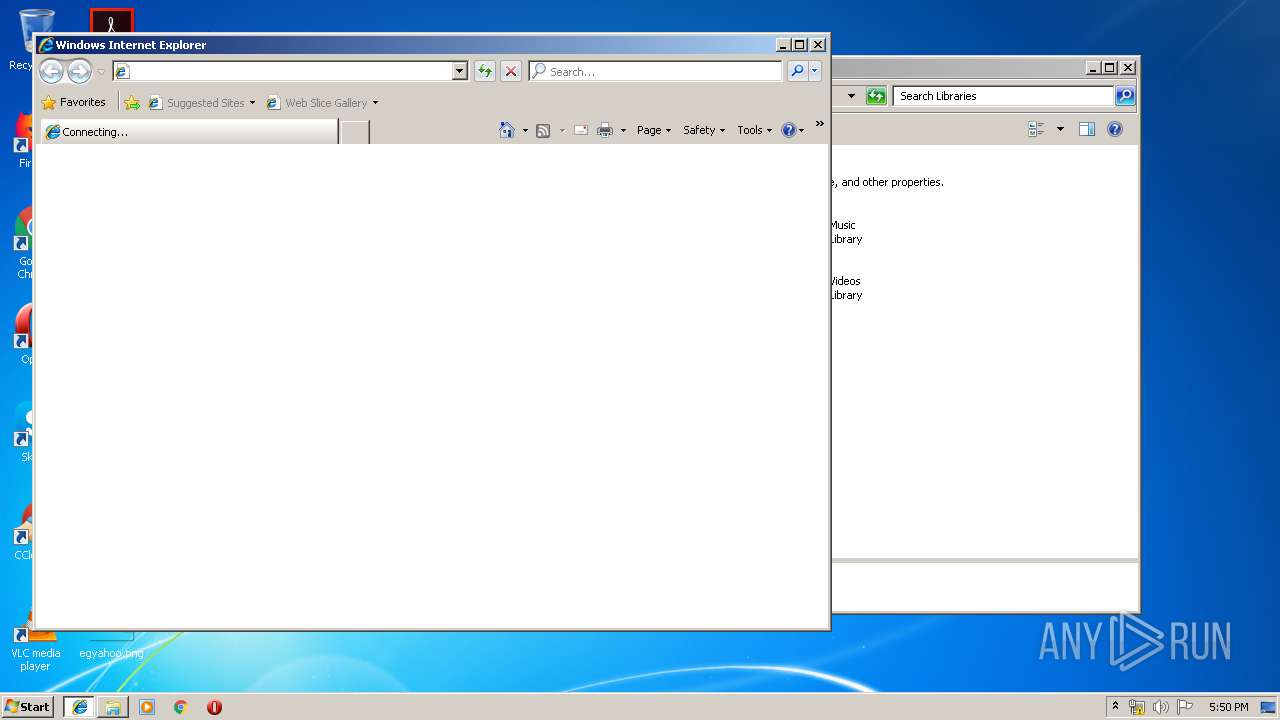
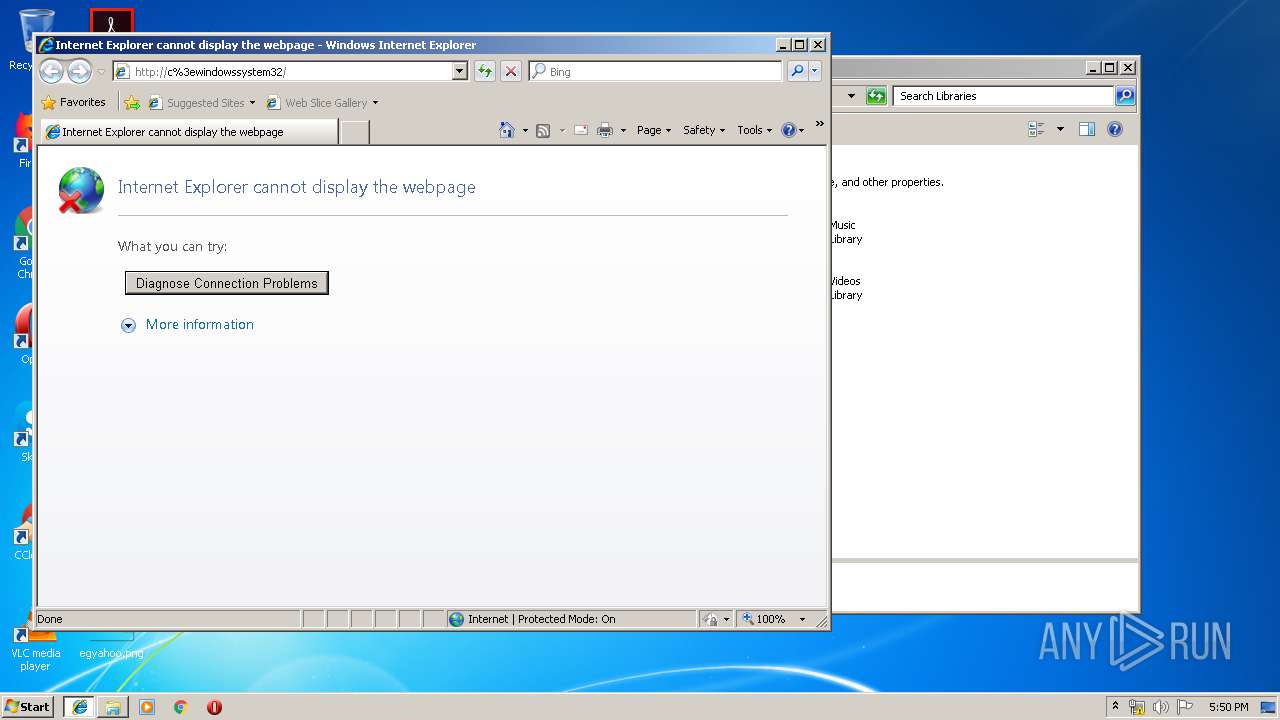
Starts Internet Explorer
- wins.exe (PID: 1748)
INFO
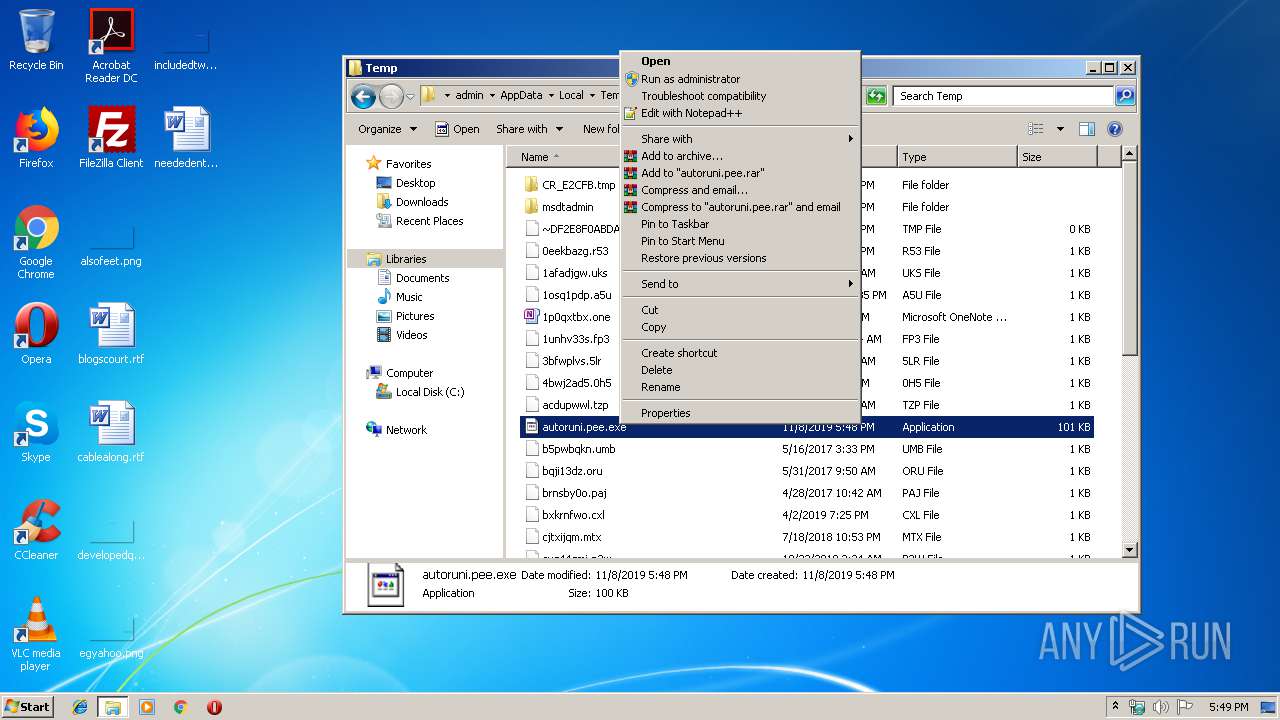
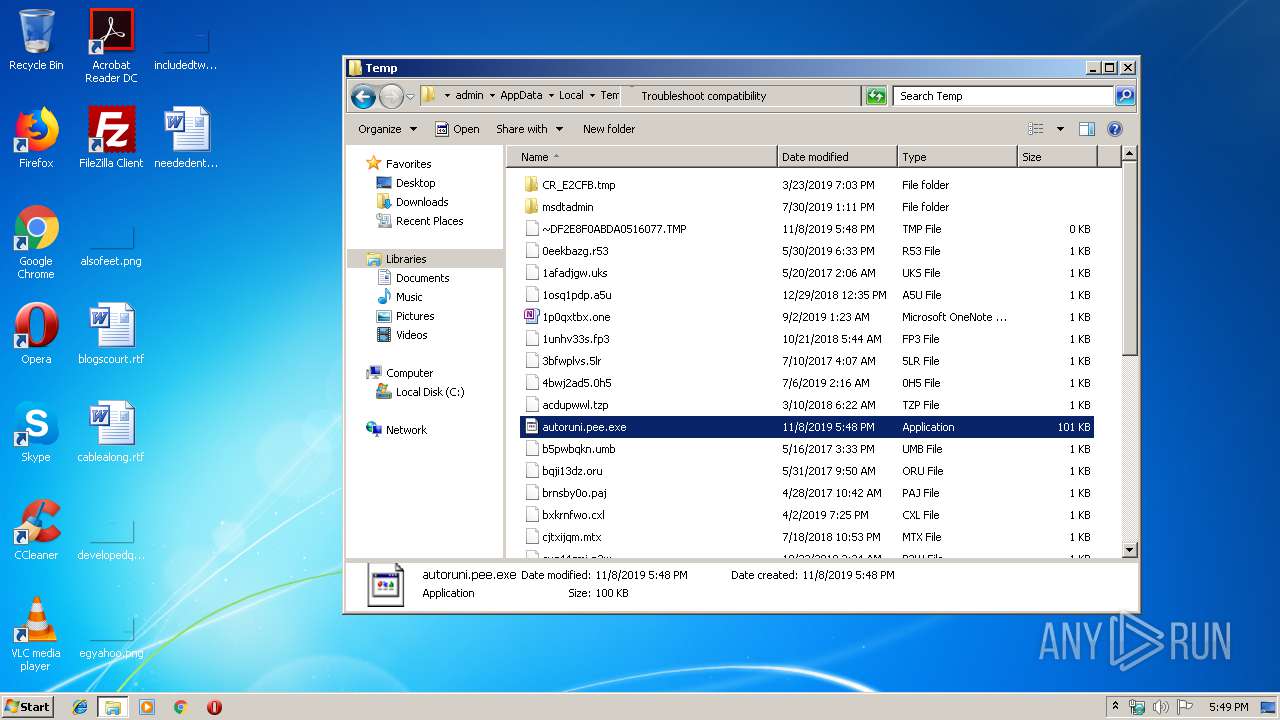
Manual execution by user
- explorer.exe (PID: 2236)
- autoruni.pee.exe (PID: 3432)
Reads internet explorer settings
- iexplore.exe (PID: 1944)
Changes internet zones settings
- iexplore.exe (PID: 2552)
Application launched itself
- iexplore.exe (PID: 2552)
Creates files in the user directory
- iexplore.exe (PID: 1944)
Reads Internet Cache Settings
- iexplore.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Petite compressed Win32 executable (53.5) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (20.2) |
| .exe | | | Win32 EXE Yoda's Crypter (19.8) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:08:08 22:19:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 144145 |
| InitializedDataSize: | 148241 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25046 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Explorer |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | vx |
| OriginalFileName: | vx.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Aug-2007 20:19:47 |
| Detected languages: |
|
| ProductName: | Explorer |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | vx |
| OriginalFilename: | vx.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Aug-2007 20:19:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.petite | 0x00001000 | 0x00023000 | 0x00009600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91302 |
.rsrc | 0x00024000 | 0x00001000 | 0x000005B8 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.60554 |
0x00025000 | 0x00000311 | 0x00000400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.712 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.08373 | 460 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.13767 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
kernel32.dll |
user32.dll |
Total processes
114
Monitored processes
56
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | Attrib +a +s +r +h C:\Windows\System32\cmd.com | C:\Windows\system32\attrib.exe | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | Cmd.exe /c Attrib +a +s +r +h C:\Windows\System32\wins.exe | C:\Windows\system32\Cmd.exe | — | autoruni.pee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 640 | Cmd.exe /c Attrib +a +s +r +h C:\Windows\spolis.exe | C:\Windows\system32\Cmd.exe | — | autoruni.pee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 656 | Cmd.exe /c Attrib +a +s +r +h C:\Windows\System32\LeChucK.exe | C:\Windows\System32\Cmd.exe | — | wins.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 996 | Cmd.exe /c Attrib +a +s +r +h C:\Windows\System32\LeChucK.exe | C:\Windows\system32\Cmd.exe | — | autoruni.pee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | Attrib +a +s +r +h C:\autorun.inf | C:\Windows\system32\attrib.exe | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | Attrib +a +s +r +h C:\Windows\regedit.com | C:\Windows\system32\attrib.exe | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | Attrib +a +s +r +h C:\Windows\spolis.exe | C:\Windows\system32\attrib.exe | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | Cmd.exe /c Attrib +a +s +r +h C:\Windows\System32\cmd.com | C:\Windows\system32\Cmd.exe | — | autoruni.pee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1748 | "C:\Windows\System32\wins.exe" "C:\Program Files\Internet Explorer\iexplore.exe" http://www.gratisweb.com/mowpax/contador.htm | C:\Windows\System32\wins.exe | — | wins.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
611
Read events
505
Write events
106
Delete events
0
Modification events
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Windows\System32\wins.exe "%1" %* | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\cmdfile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Windows\System32\wins.exe "%1" %* | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\piffile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Windows\System32\wins.exe "%1" %* | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\comfile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Windows\System32\wins.exe "%1" %* | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\batfile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Windows\System32\wins.exe "%1" %* | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell |
| Operation: | write | Name: | |
Value: Open | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\cmdfile\shell |
| Operation: | write | Name: | |
Value: Open | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\piffile\shell |
| Operation: | write | Name: | |
Value: Open | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\comfile\shell |
| Operation: | write | Name: | |
Value: Open | |||
| (PID) Process: | (2132) autoruni.pee.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\batfile\shell |
| Operation: | write | Name: | |
Value: Open | |||
Executable files
9
Suspicious files
3
Text files
49
Unknown types
3
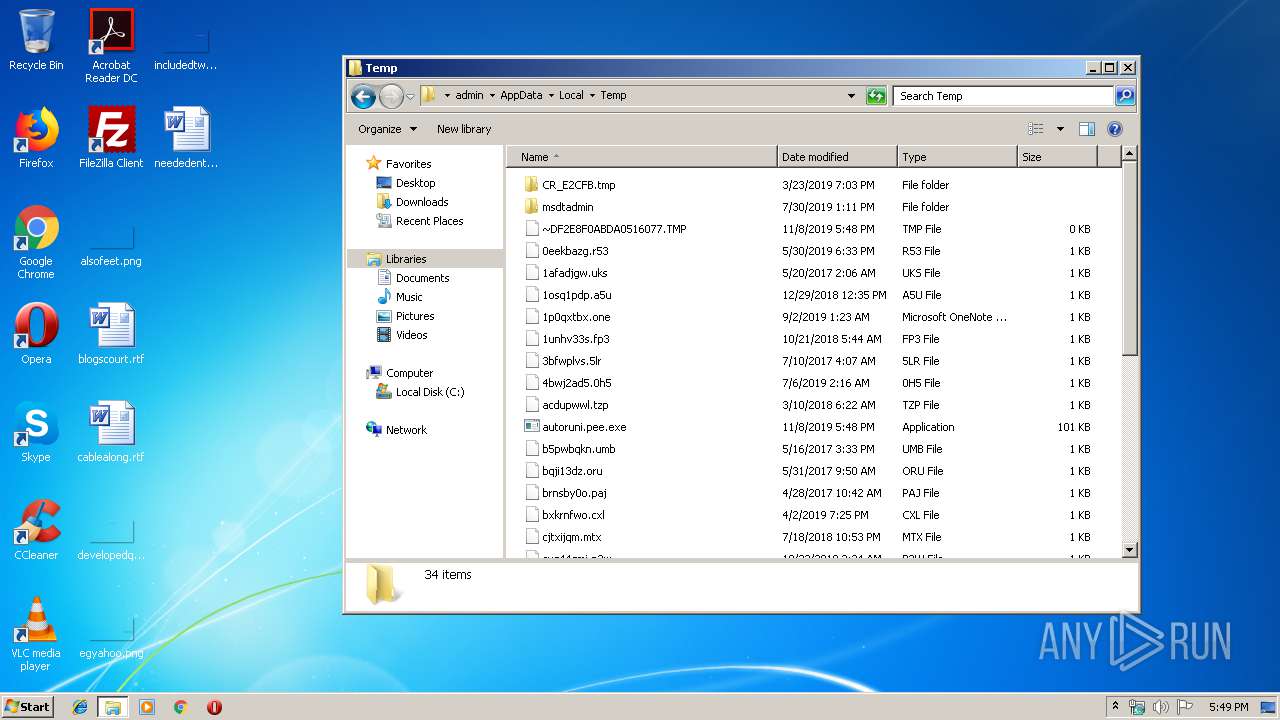
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | autoruni.pee.exe | C:\Users\admin\AppData\Local\Temp\~DF2E8F0ABDA0516077.TMP | — | |
MD5:— | SHA256:— | |||
| 4008 | LeChucK.exe | C:\Users\admin\AppData\Local\Temp\~DF9F57BF0BF7FD5937.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | LeChucK.exe | C:\Users\admin\AppData\Local\Temp\~DF74329AB7F849AB26.TMP | — | |
MD5:— | SHA256:— | |||
| 2772 | wins.exe | C:\Users\admin\AppData\Local\Temp\~DF7107E6DD2D15D69A.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | wins.exe | C:\Users\admin\AppData\Local\Temp\~DFFAC08FC93BEDD557.TMP | — | |
MD5:— | SHA256:— | |||
| 3432 | autoruni.pee.exe | C:\Users\admin\AppData\Local\Temp\~DF84A81158A0647D4B.TMP | — | |
MD5:— | SHA256:— | |||
| 1748 | wins.exe | C:\Users\admin\AppData\Local\Temp\~DF09C7914F5A5CB14A.TMP | — | |
MD5:— | SHA256:— | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3356 | LeChucK.exe | C:\Windows\spolis.exe | executable | |
MD5:AAE219D4E703051D60351F73CA288D1D | SHA256:56947C93FB17D3339FF2A778556F4A4F95516FB5112DB61AE0804ECDCF4D1307 | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
15
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=F9CC7CF4698142FA9D01CE2727B88EDA&CID=2239FC5CD899606B37AFF252D97561CF&Type=Event.CPT&DATA={"pp":{"S":"L","FC":31,"BC":248,"SE":-1,"TC":-1,"H":352,"BP":537,"CT":558,"IL":24},"ad":[164,498,772,444,1089,498,0]}&P=SERP&DA=DUB02 | US | image | 141 b | whitelisted |
— | — | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=v&maxwidth=253&rowheight=20§ionHeight=400&FORM=IE8SSC&market=en-us | US | xml | 238 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=F9CC7CF4698142FA9D01CE2727B88EDA&CID=2239FC5CD899606B37AFF252D97561CF&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"Object%20doesn%27t%20support%20this%20property%20or%20method","Meta":"http%3A//www.bing.com/search%3Fq%3Dvirus%26src%3DIE-SearchBox%26FORM%3DIE8SRC","Line":28154213,"Char":%20undefined}] | US | image | 141 b | whitelisted |
— | — | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=virus&maxwidth=253&rowheight=20§ionHeight=400&FORM=IE8SSC&market=en-us | US | xml | 226 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/chev_expref.png | US | image | 492 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6m/4G/cj,nj/9445026b/6b881c08.js | US | text | 407 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/27/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/8/2Y/cj,nj/4c10930c/19b40d8c.js | US | text | 272 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6l/5l/cj,nj/6e795a8b/1c156e04.js | US | text | 1.81 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2552 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 40.90.137.125:443 | login.live.com | Microsoft Corporation | US | unknown |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 65.52.143.224:80 | 62df03e3ad174db04eb5e6600148e9a9.clo.footprintdns.com | Microsoft Corporation | NL | whitelisted |
— | — | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
— | — | 51.5.150.212:80 | c9dece673f19299ae479b4c46bf8f20d.clo.footprintdns.com | Microsoft Deutschland MCIO GmbH | DE | whitelisted |
— | — | 13.107.6.163:80 | 63a79b53451fd4bc630b63458be3751b.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gratisweb.com |
| unknown |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
63a79b53451fd4bc630b63458be3751b.clo.footprintdns.com |
| suspicious |
62df03e3ad174db04eb5e6600148e9a9.clo.footprintdns.com |
| unknown |
c9dece673f19299ae479b4c46bf8f20d.clo.footprintdns.com |
| unknown |
fp.msedge.net |
| whitelisted |