| File name: | ba3272b0-a214-4930-9eda-55ded774e4eb |
| Full analysis: | https://app.any.run/tasks/e31cf99f-eb6e-47b1-a015-04a3f533f58b |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 17:45:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 5 sections |
| MD5: | 7C9B7354279680E57E740BE0B8ABFF20 |
| SHA1: | 3781358A558E563FCD7A997A89A6BACF46641DAE |
| SHA256: | 567D56920D6C11920923CA11AD80E35A974B3001091155F67299A7A231335A73 |
| SSDEEP: | 24576:HaJ9QdPsHWYWz+xwoVFOhQOH5NYvB6hO9V8aE02:HppGWYWz+xwo2hQOH5NYvB6hO9V8aj2 |
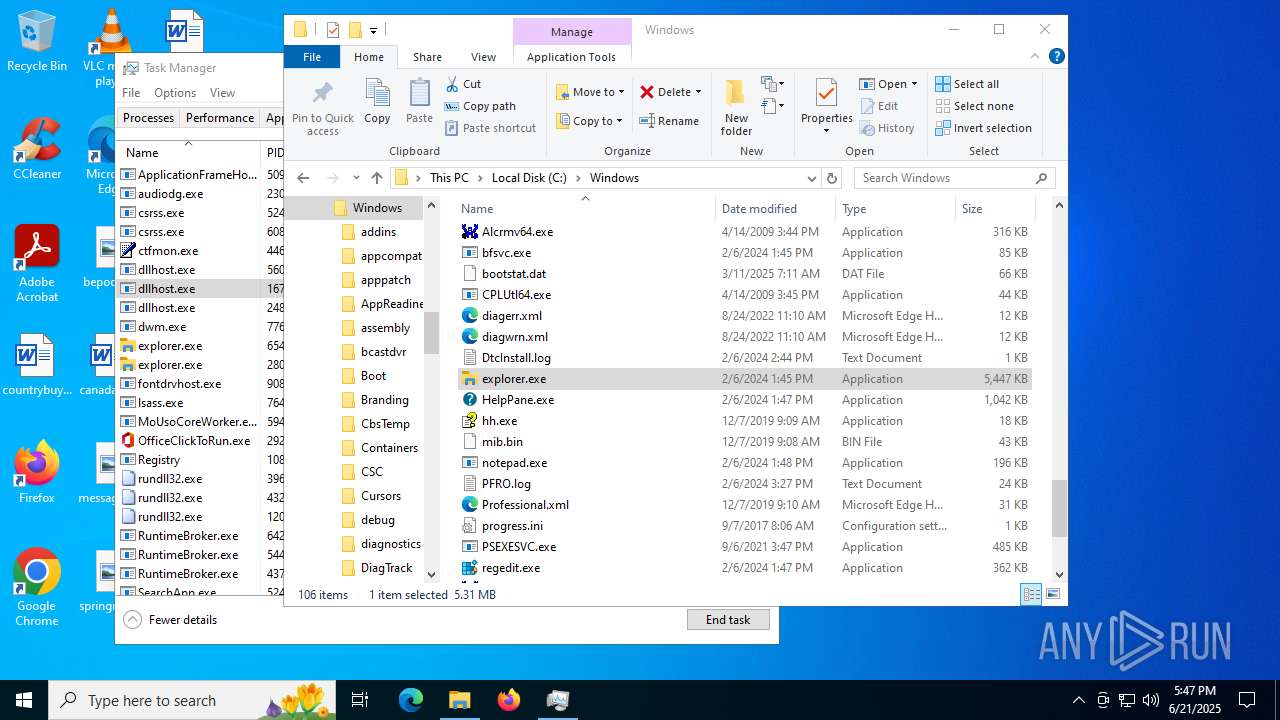
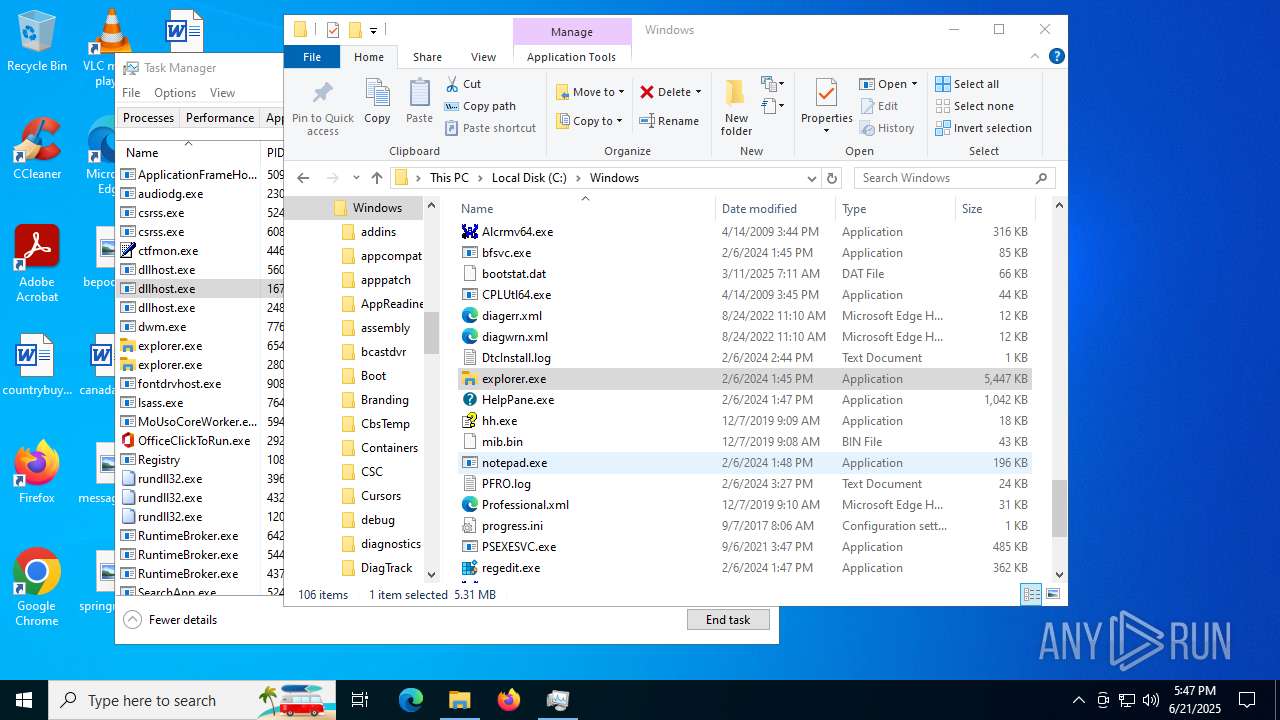
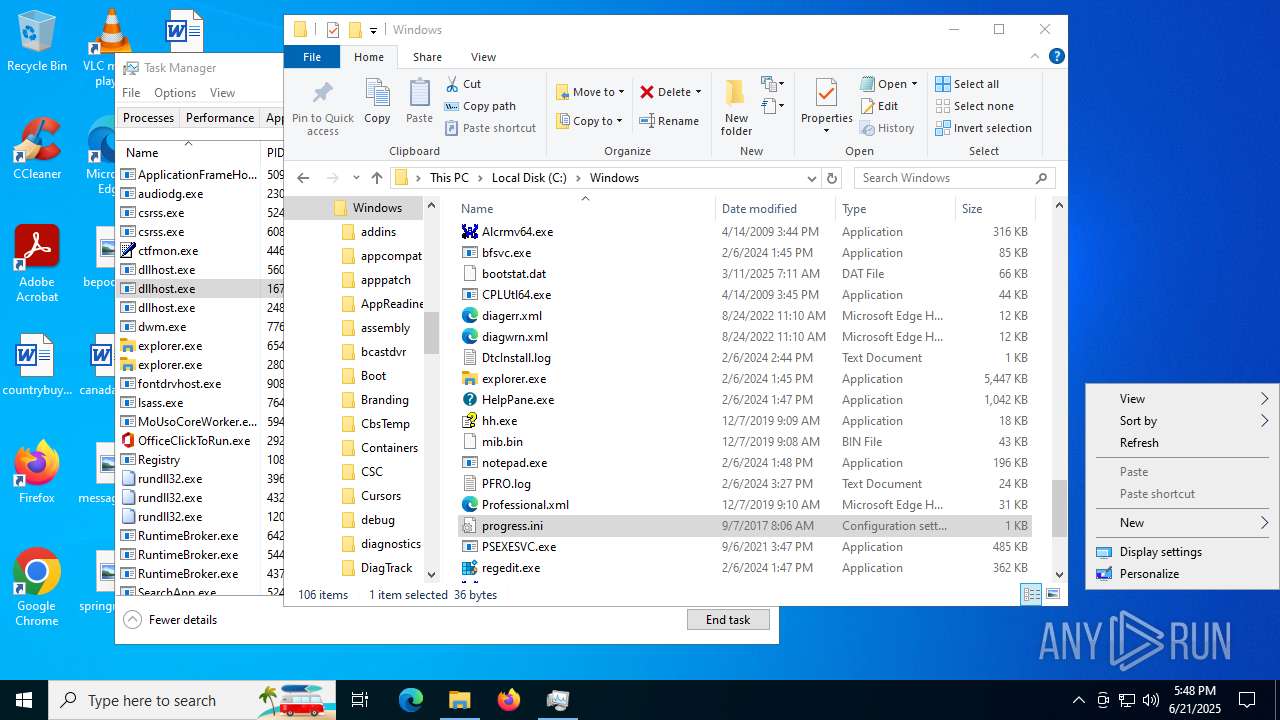
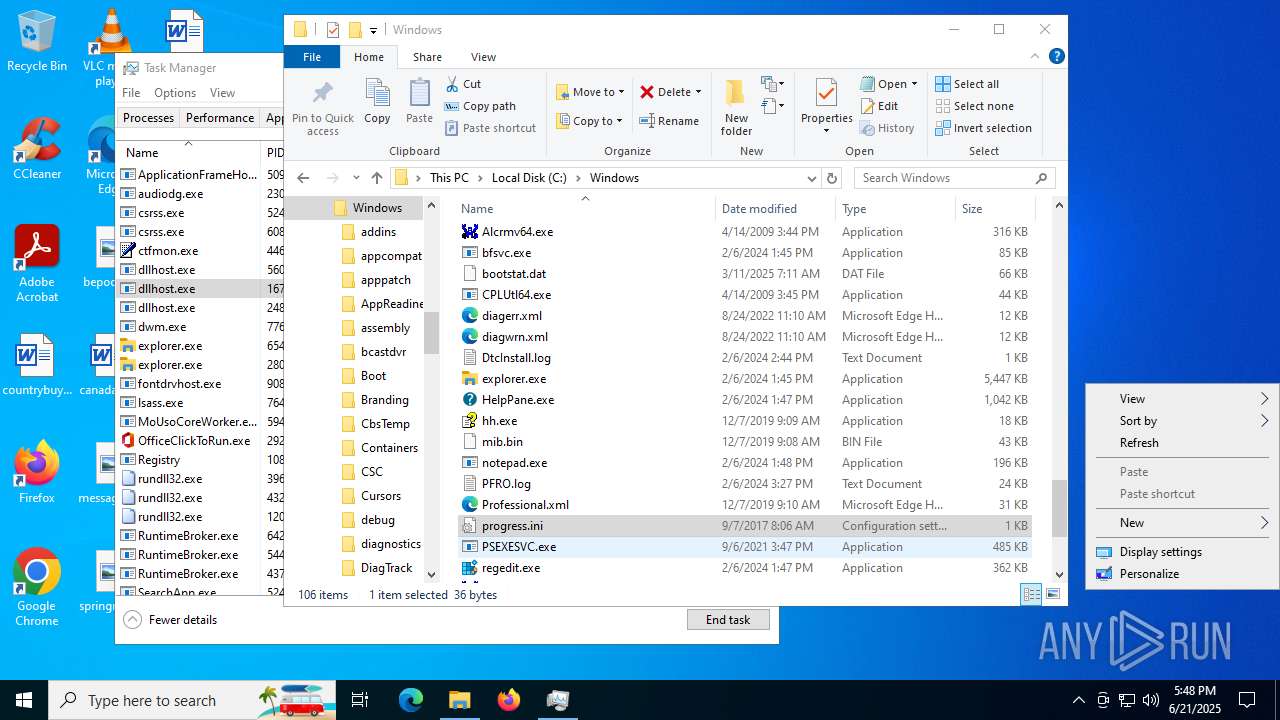
MALICIOUS
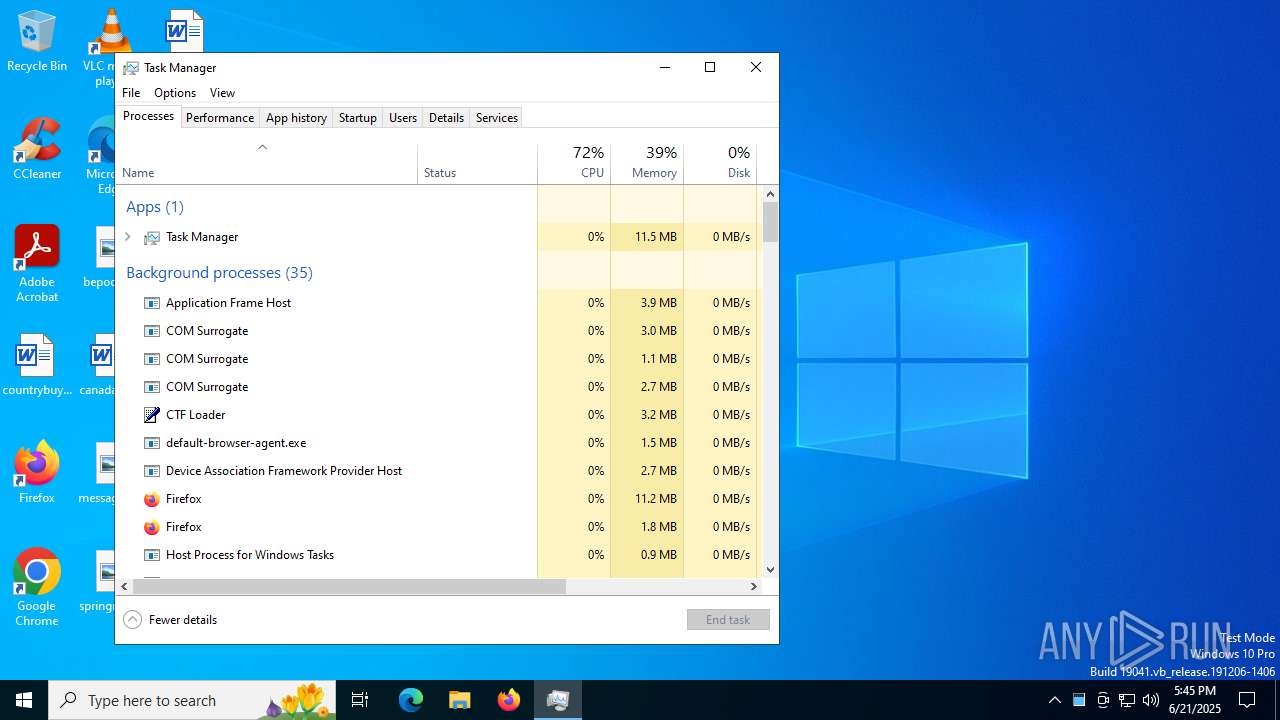
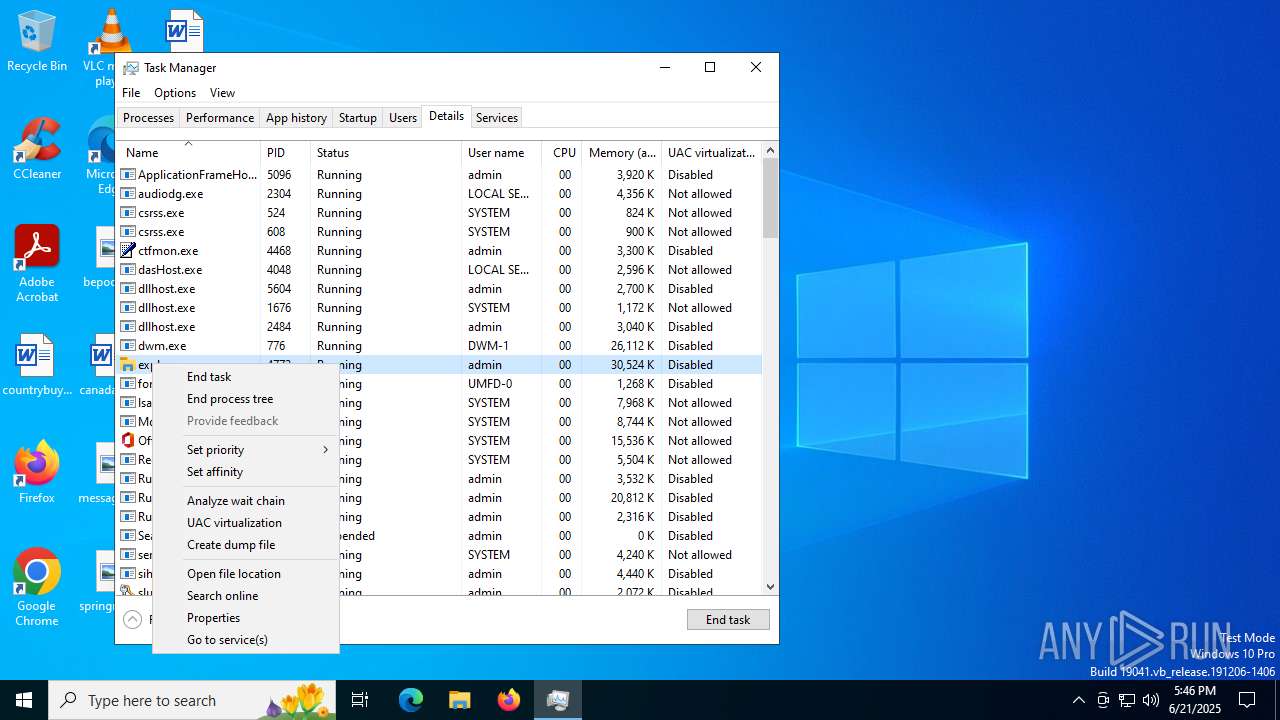
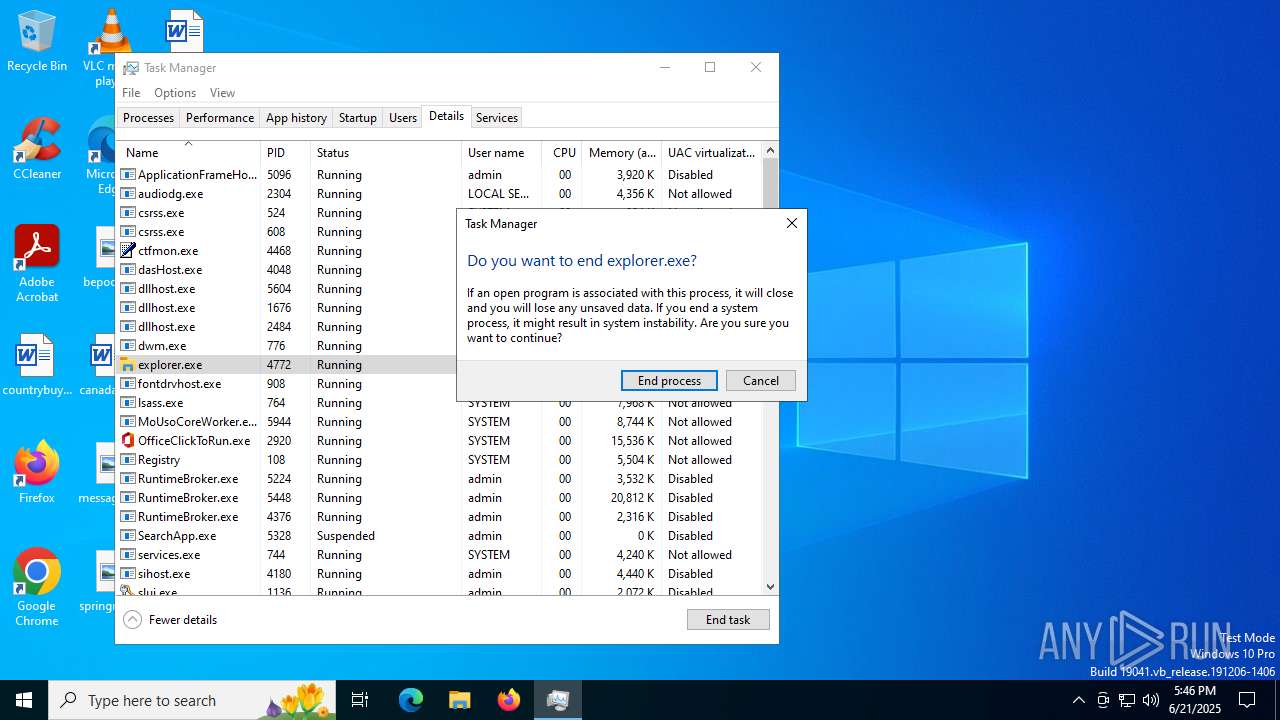
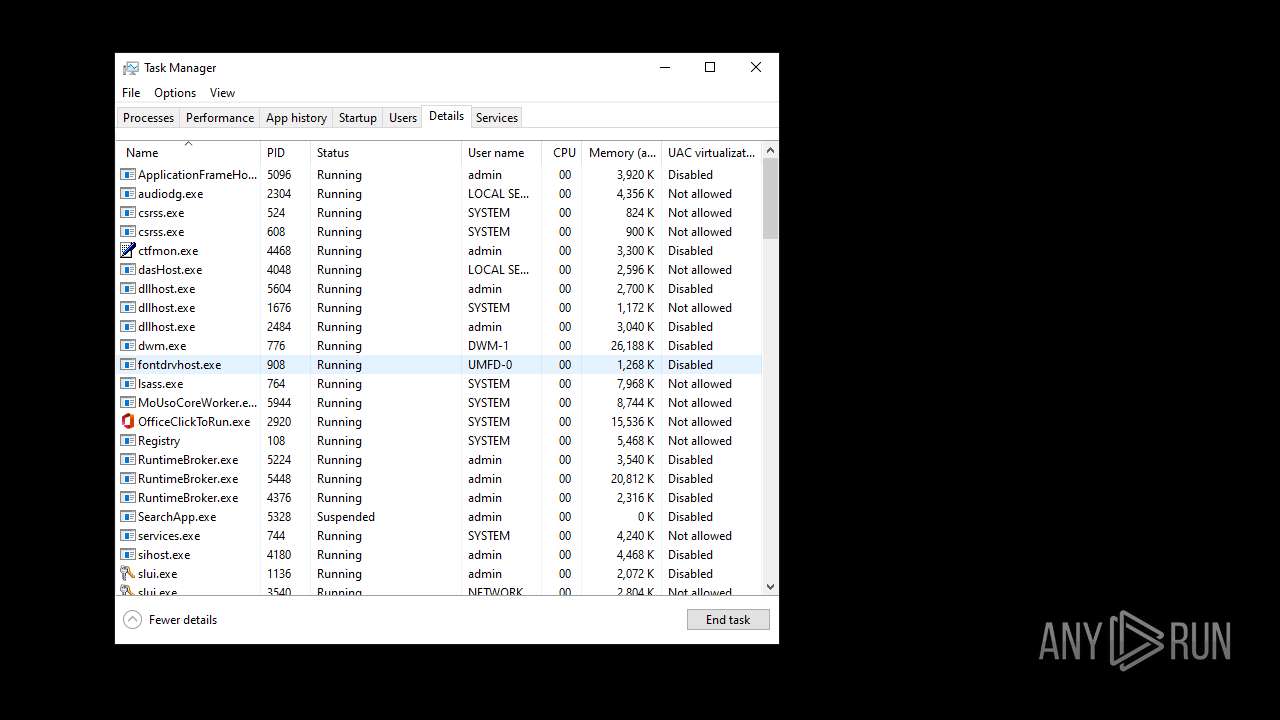
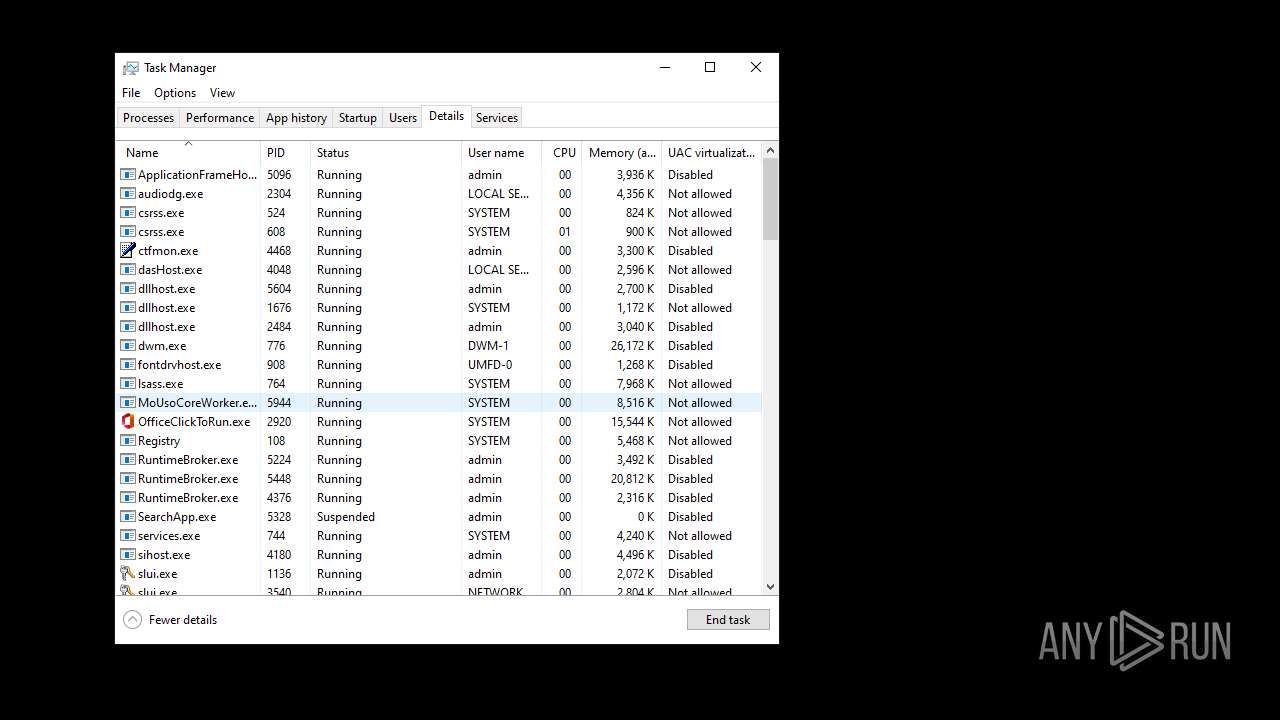
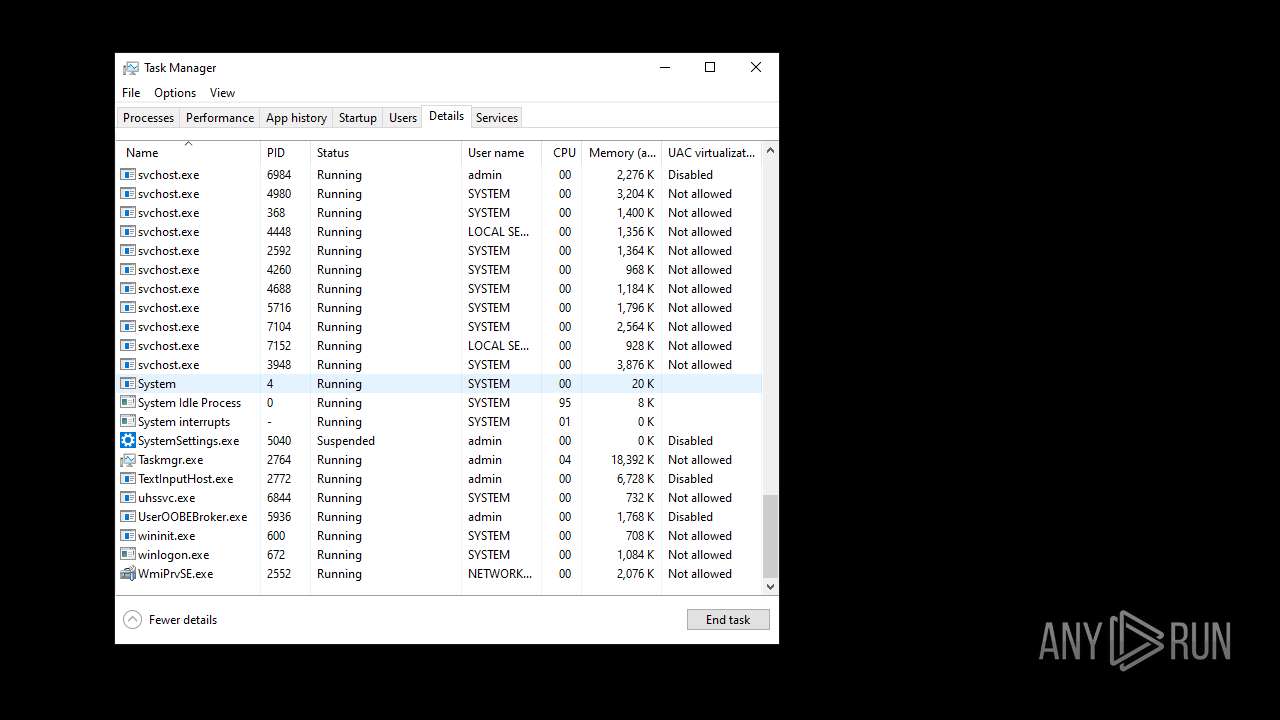
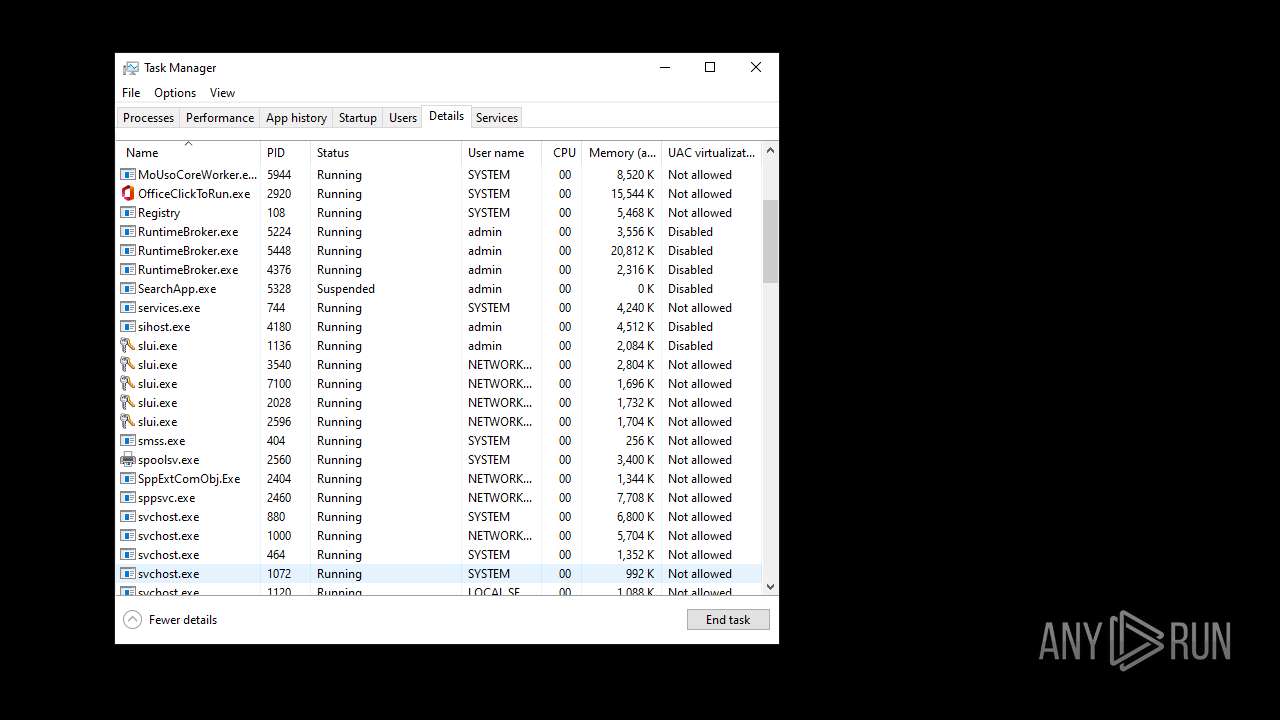
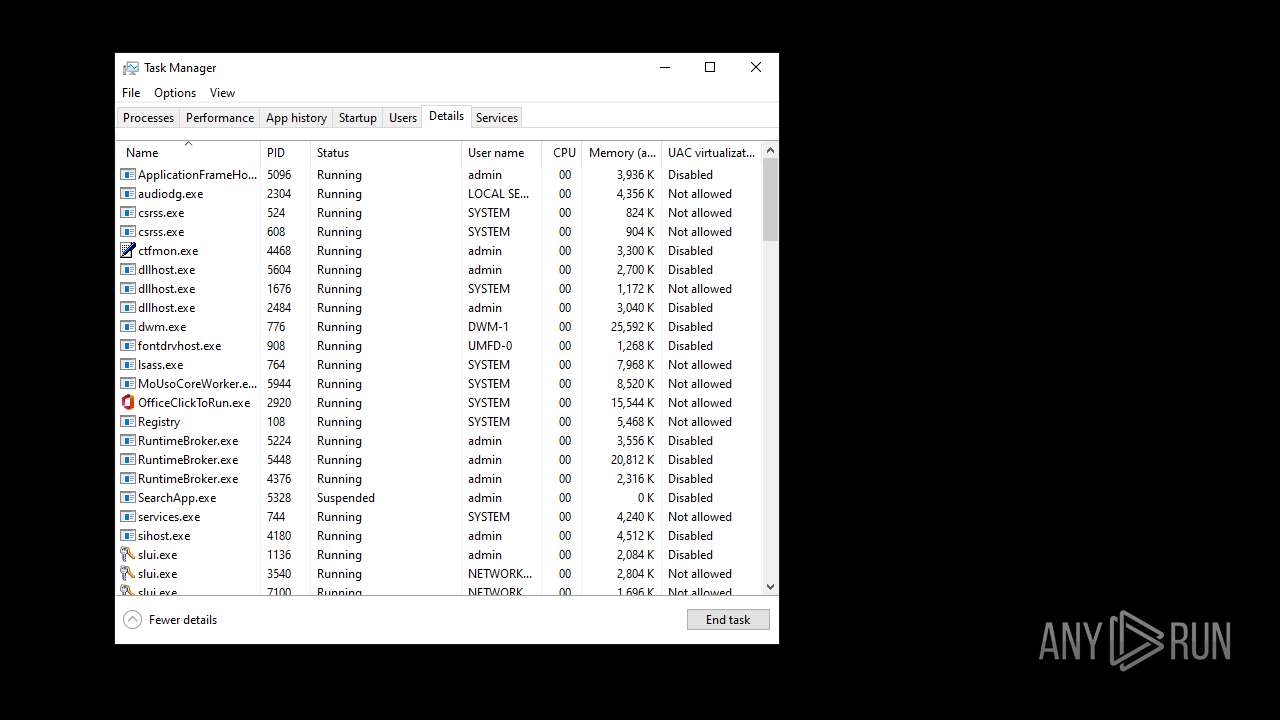
Application was injected by another process
- sihost.exe (PID: 4180)
- svchost.exe (PID: 4204)
- svchost.exe (PID: 4248)
- explorer.exe (PID: 4772)
- svchost.exe (PID: 5048)
- StartMenuExperienceHost.exe (PID: 5160)
- RuntimeBroker.exe (PID: 5224)
- SearchApp.exe (PID: 5328)
- RuntimeBroker.exe (PID: 5448)
- RuntimeBroker.exe (PID: 4376)
- dllhost.exe (PID: 5604)
- UserOOBEBroker.exe (PID: 5936)
- ApplicationFrameHost.exe (PID: 5096)
- svchost.exe (PID: 6984)
- TextInputHost.exe (PID: 2772)
- dllhost.exe (PID: 2484)
- firefox.exe (PID: 4708)
- RuntimeBroker.exe (PID: 7092)
- default-browser-agent.exe (PID: 4888)
- firefox.exe (PID: 5900)
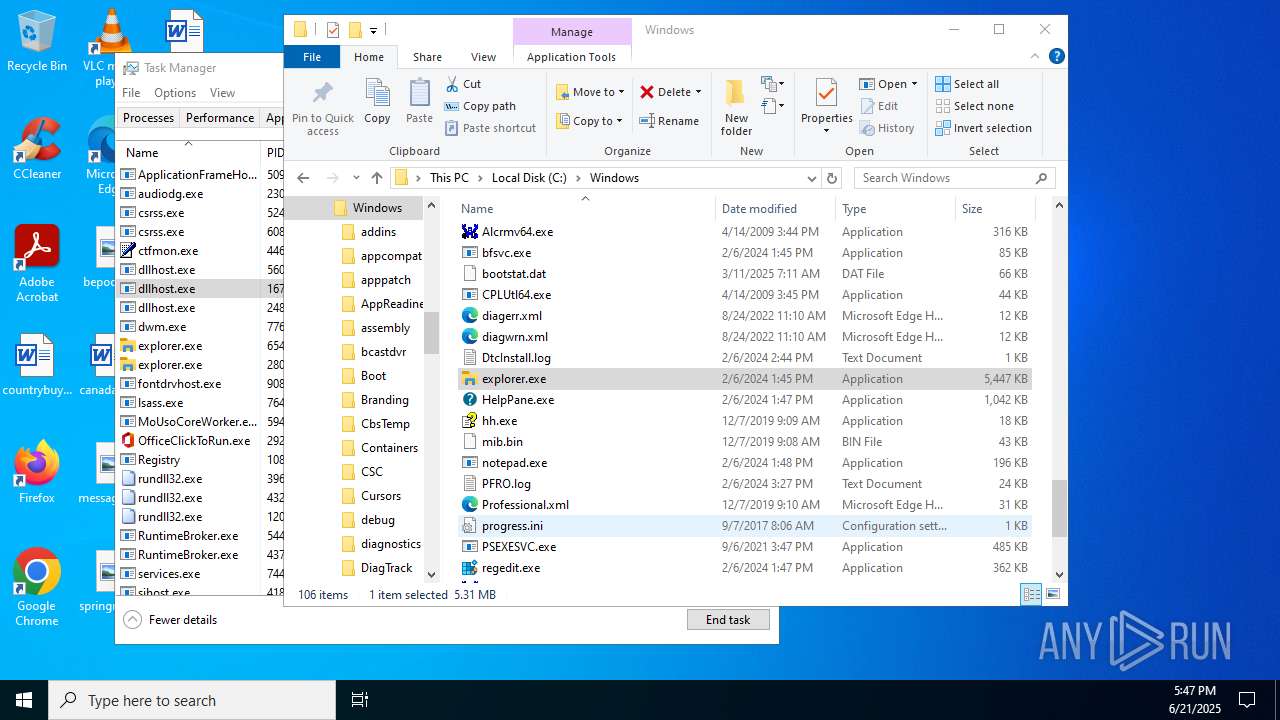
Runs injected code in another process
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
Changes the autorun value in the registry
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
- explorer.exe (PID: 4772)
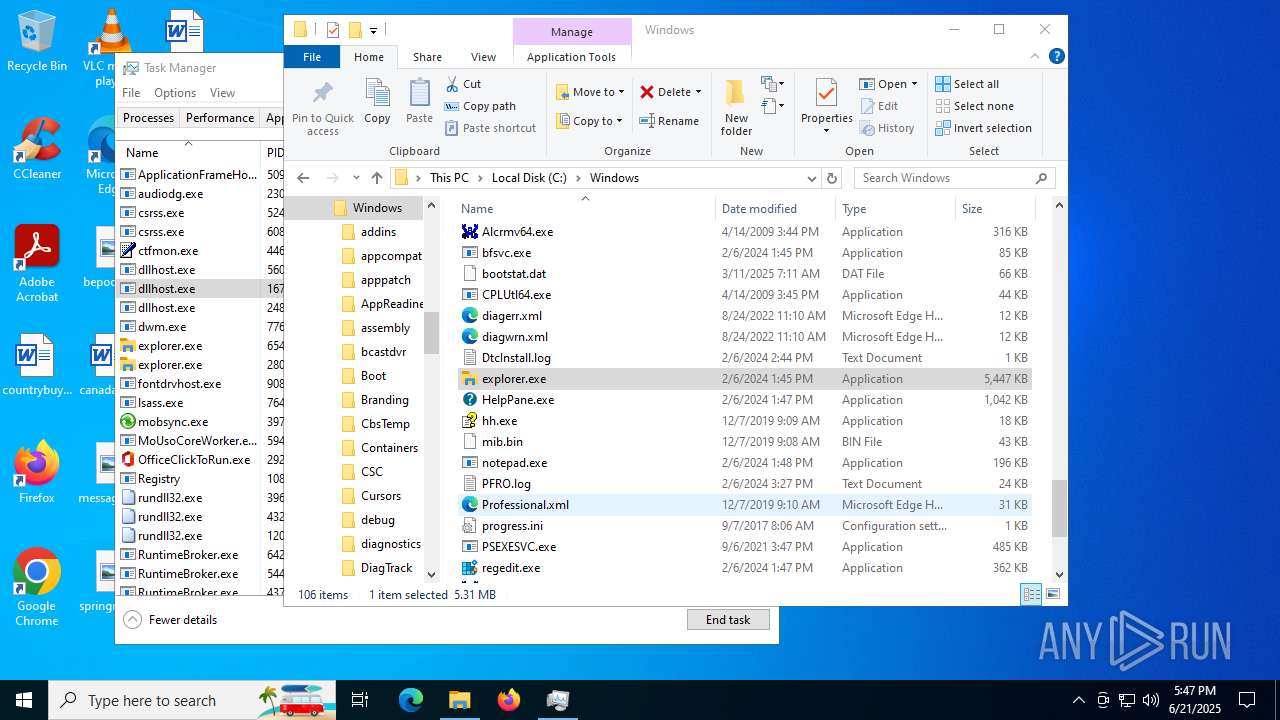
DIAMOTRIX has been detected (SURICATA)
- explorer.exe (PID: 4772)
SUSPICIOUS
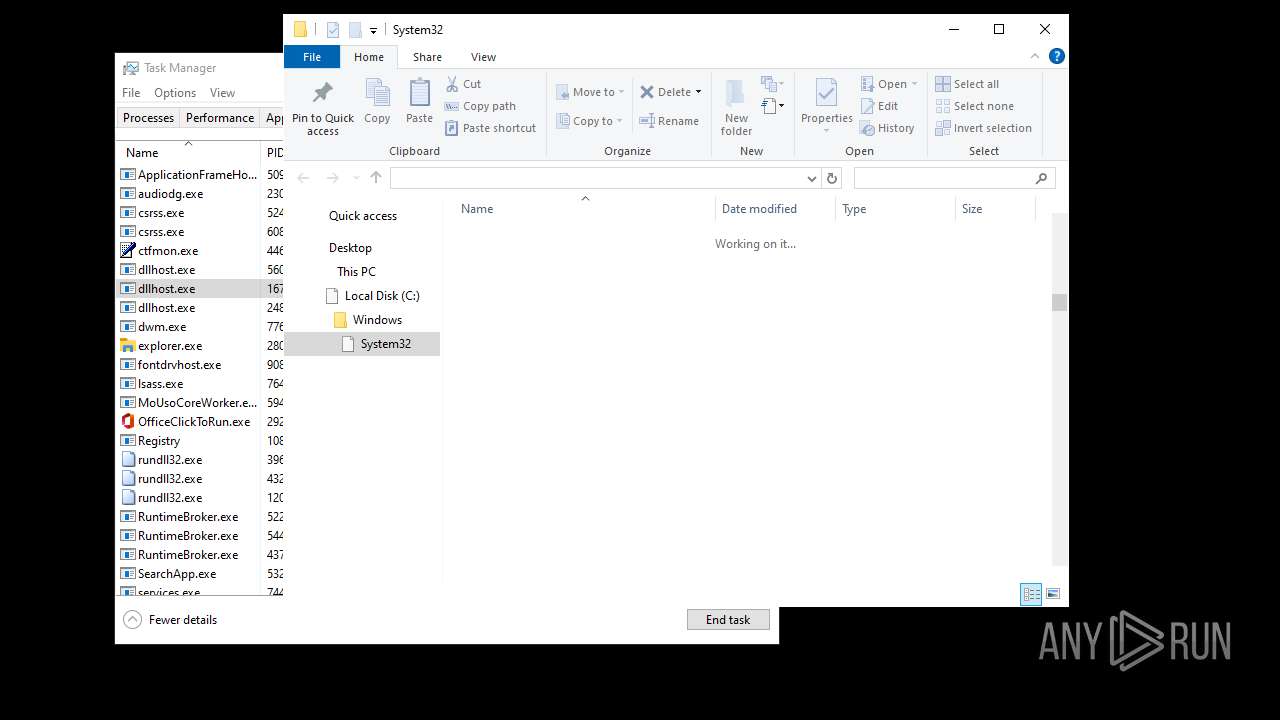
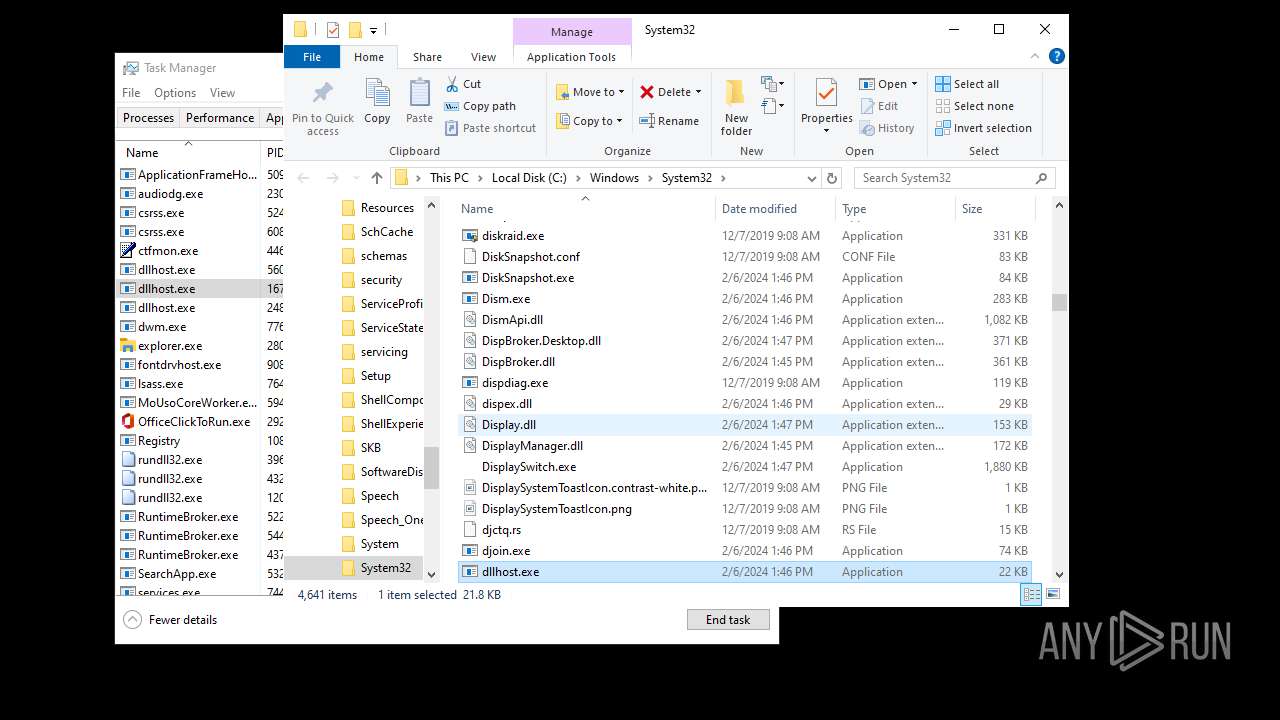
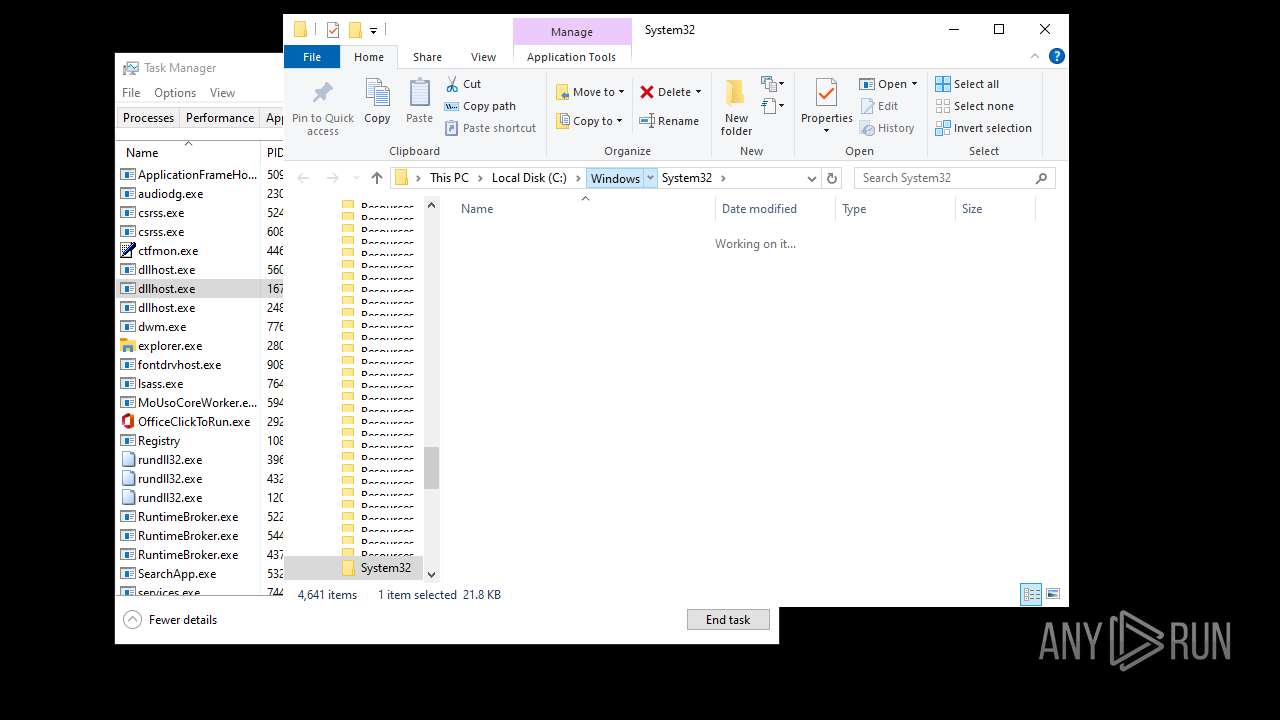
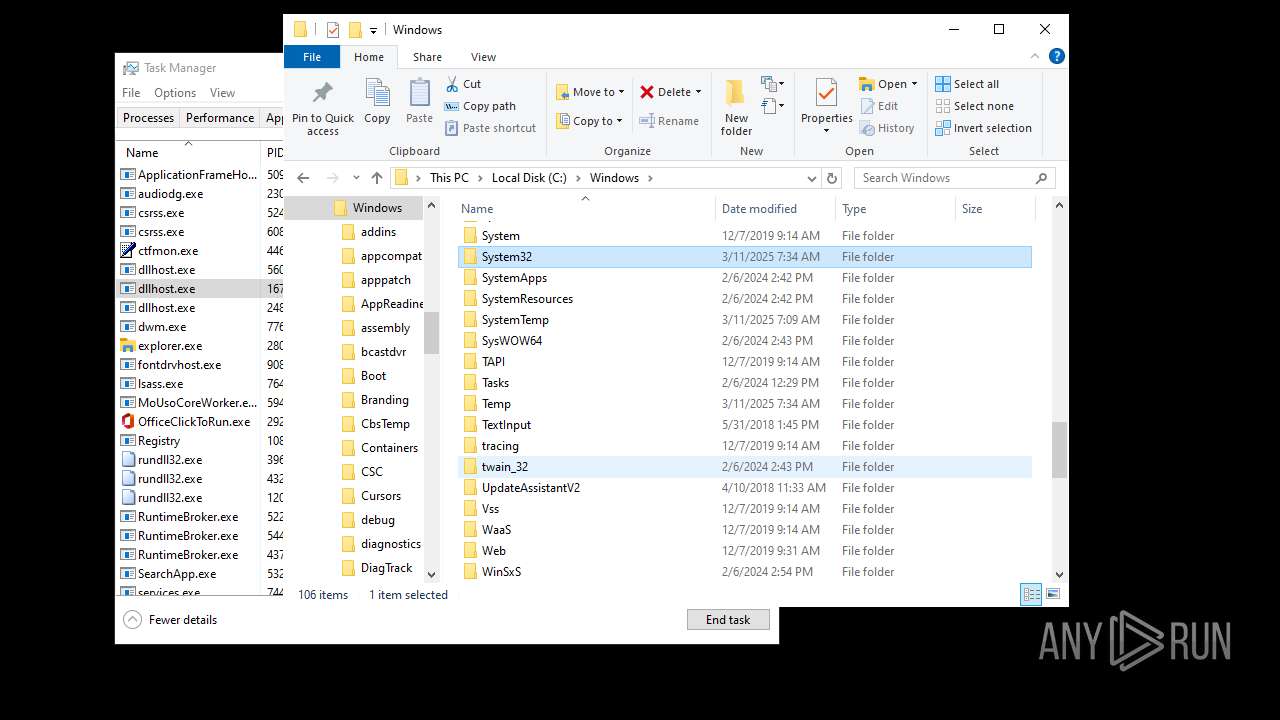
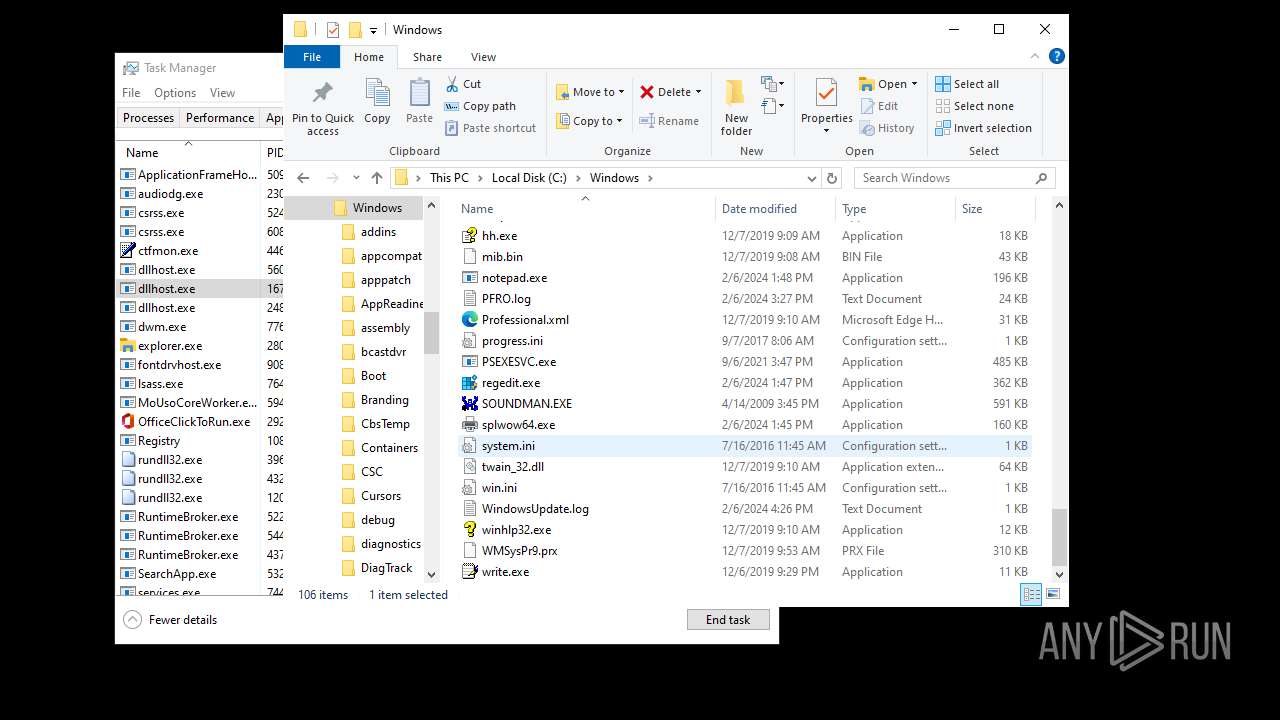
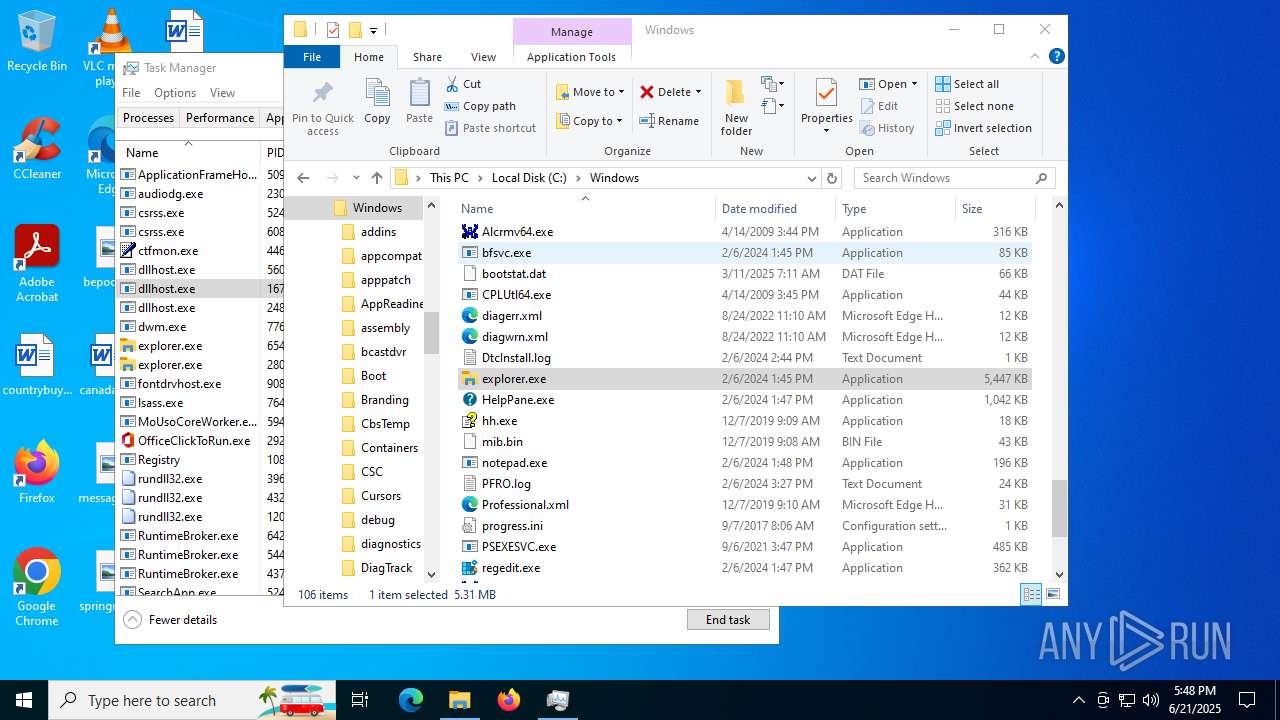
Executable content was dropped or overwritten
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
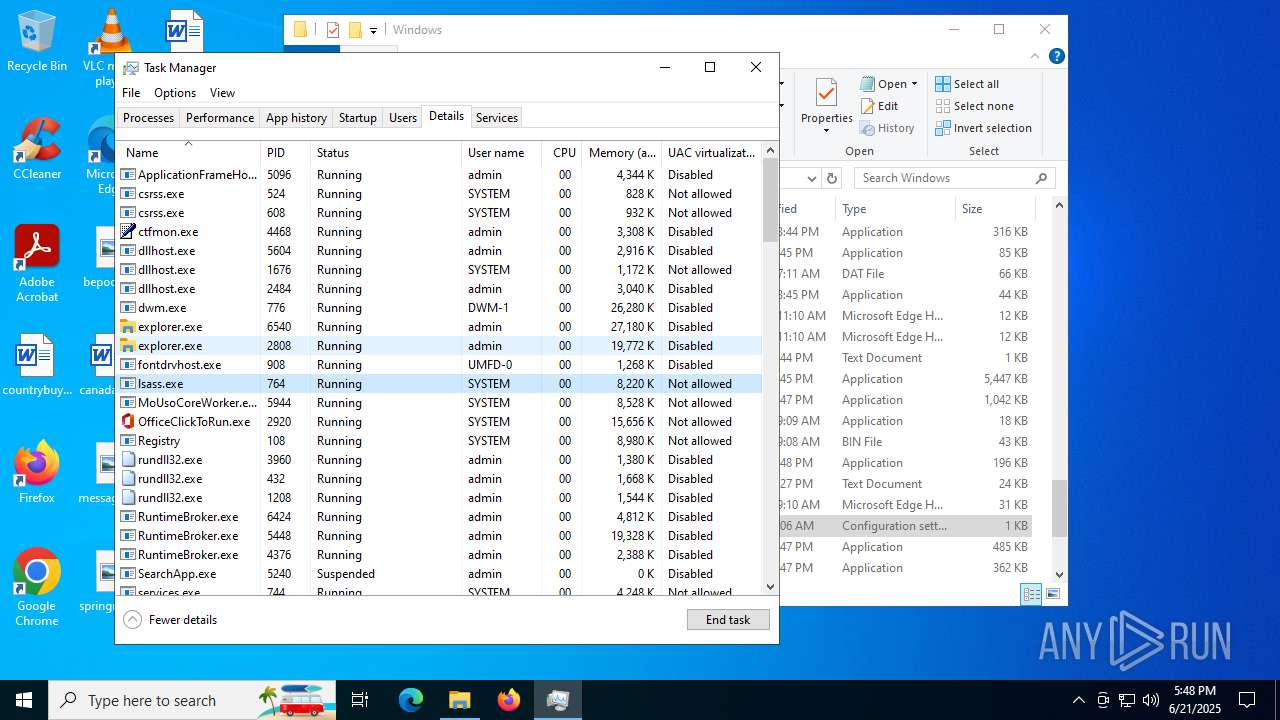
Application launched itself
- explorer.exe (PID: 2808)
Creates file in the systems drive root
- explorer.exe (PID: 2808)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 436)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 436)
- SearchApp.exe (PID: 5240)
Connects to the server without a host name
- explorer.exe (PID: 4772)
INFO
Reads the machine GUID from the registry
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
- StartMenuExperienceHost.exe (PID: 5160)
- TextInputHost.exe (PID: 2772)
- default-browser-agent.exe (PID: 4888)
- SearchApp.exe (PID: 5240)
Reads the computer name
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
- StartMenuExperienceHost.exe (PID: 436)
- SearchApp.exe (PID: 5240)
- TextInputHost.exe (PID: 4920)
Checks supported languages
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
- default-browser-agent.exe (PID: 4888)
- SearchApp.exe (PID: 5240)
- TextInputHost.exe (PID: 4920)
- StartMenuExperienceHost.exe (PID: 436)
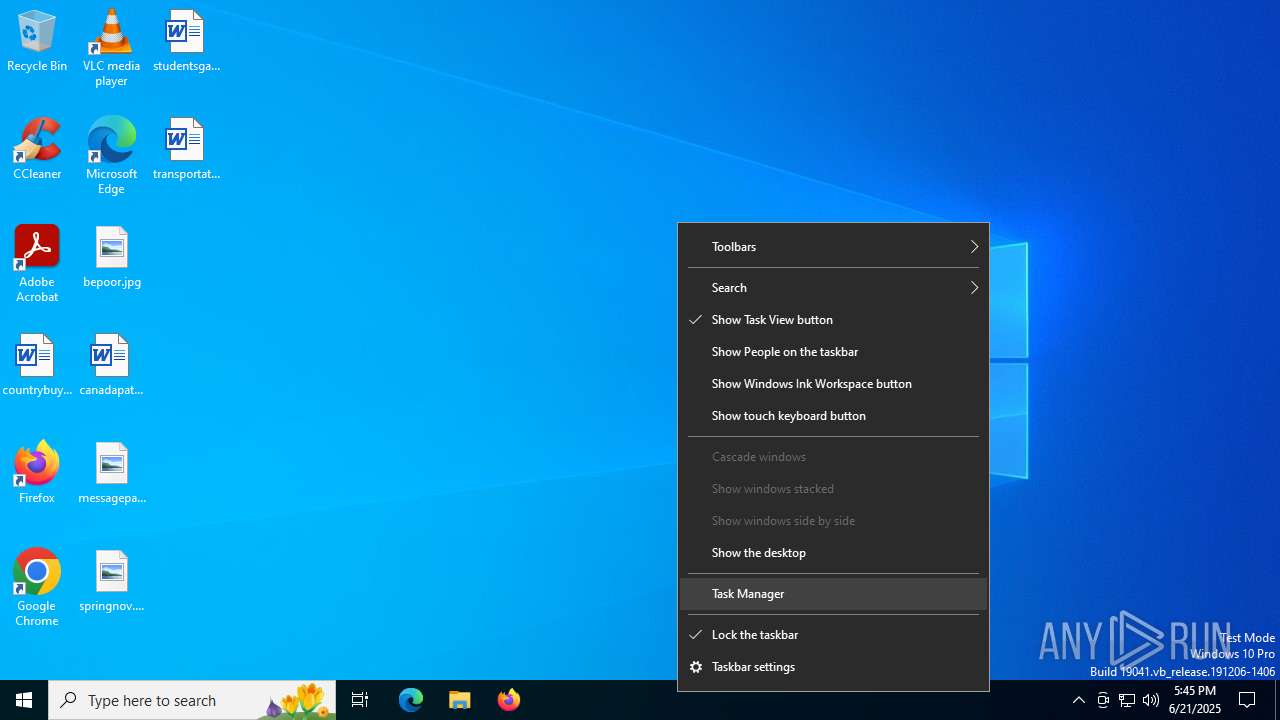
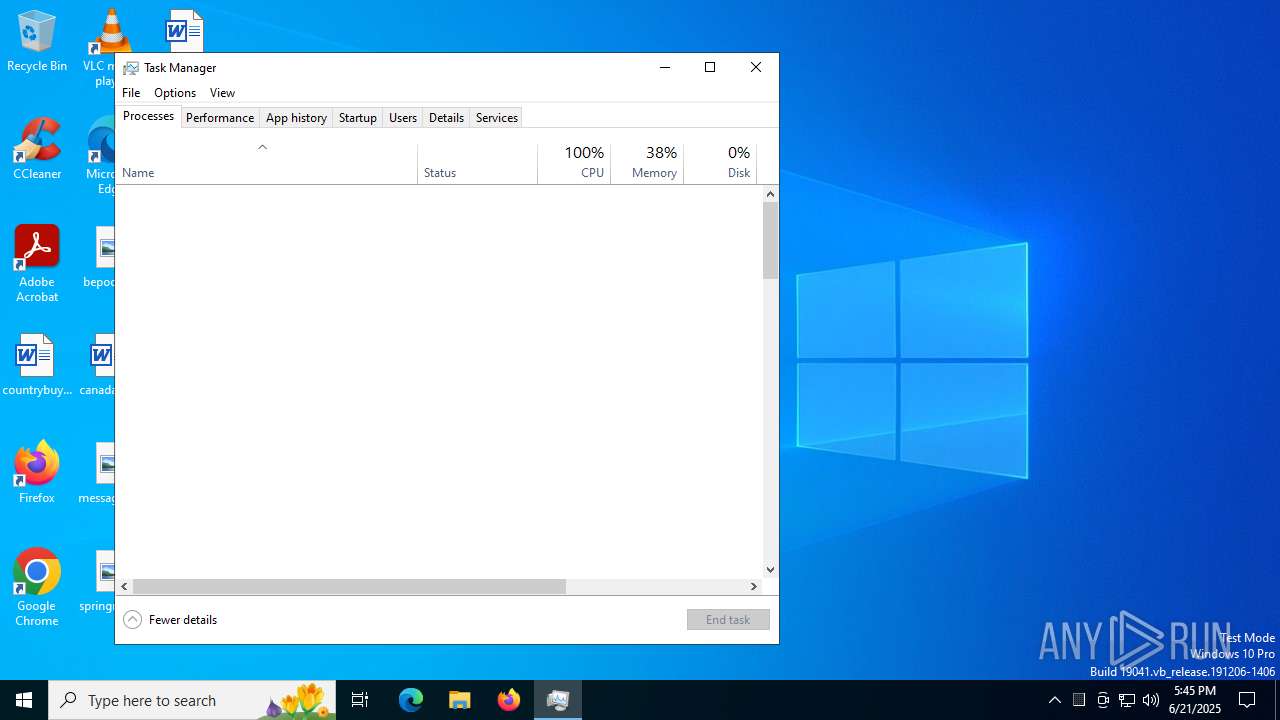
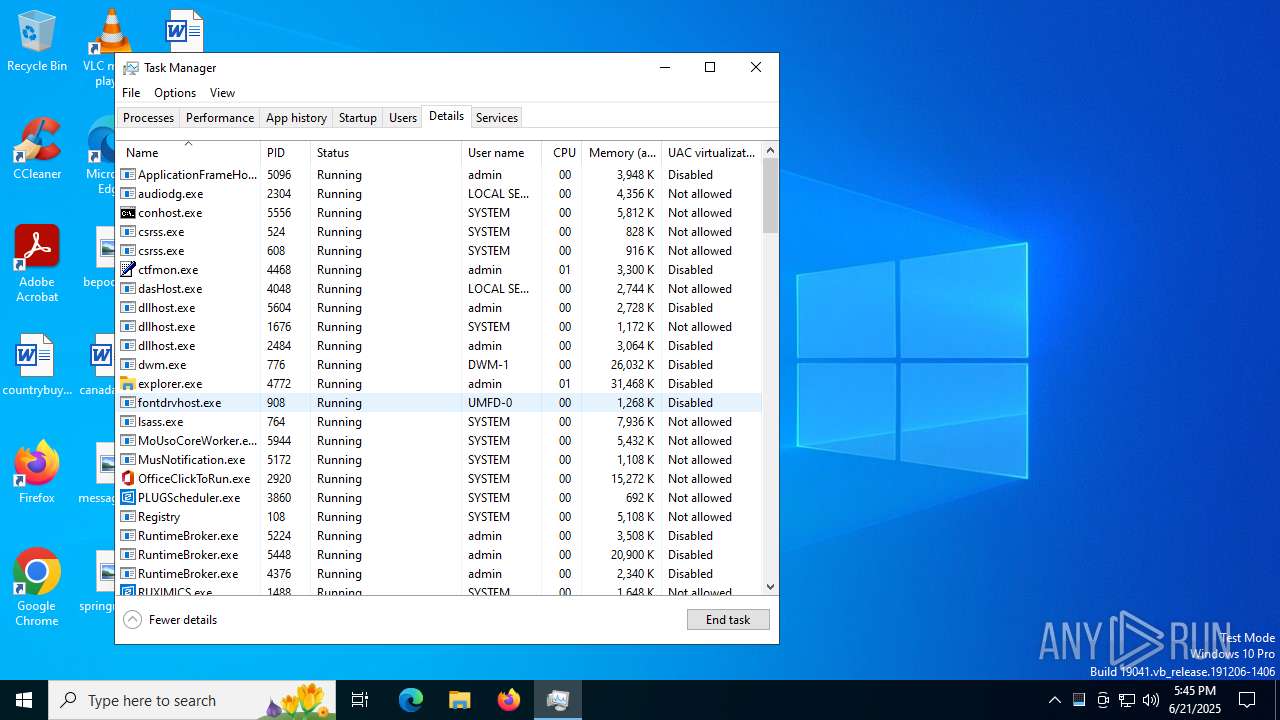
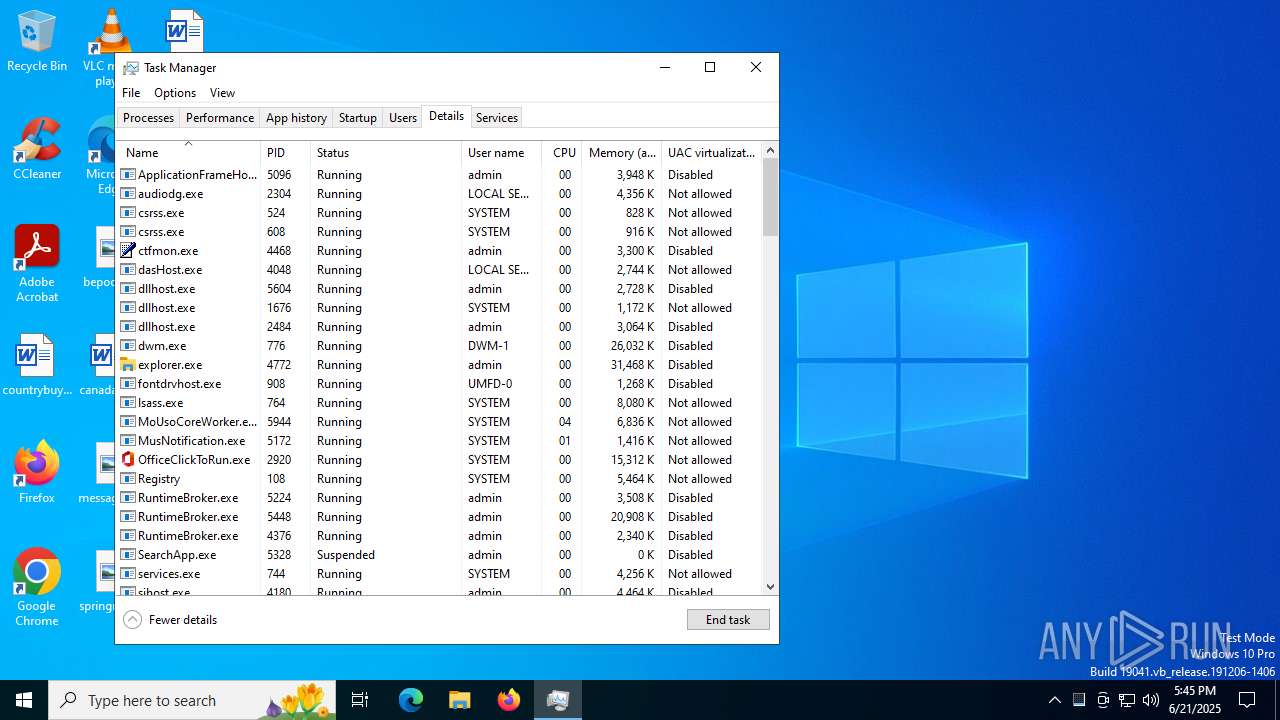
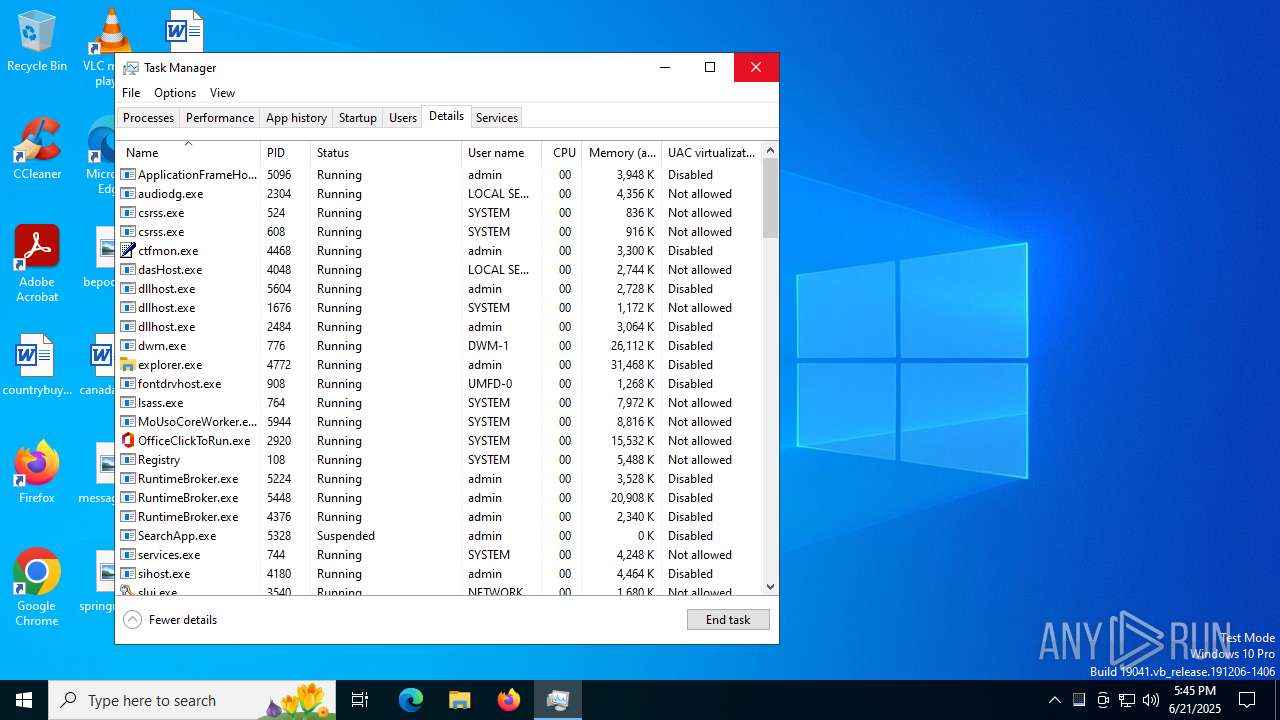
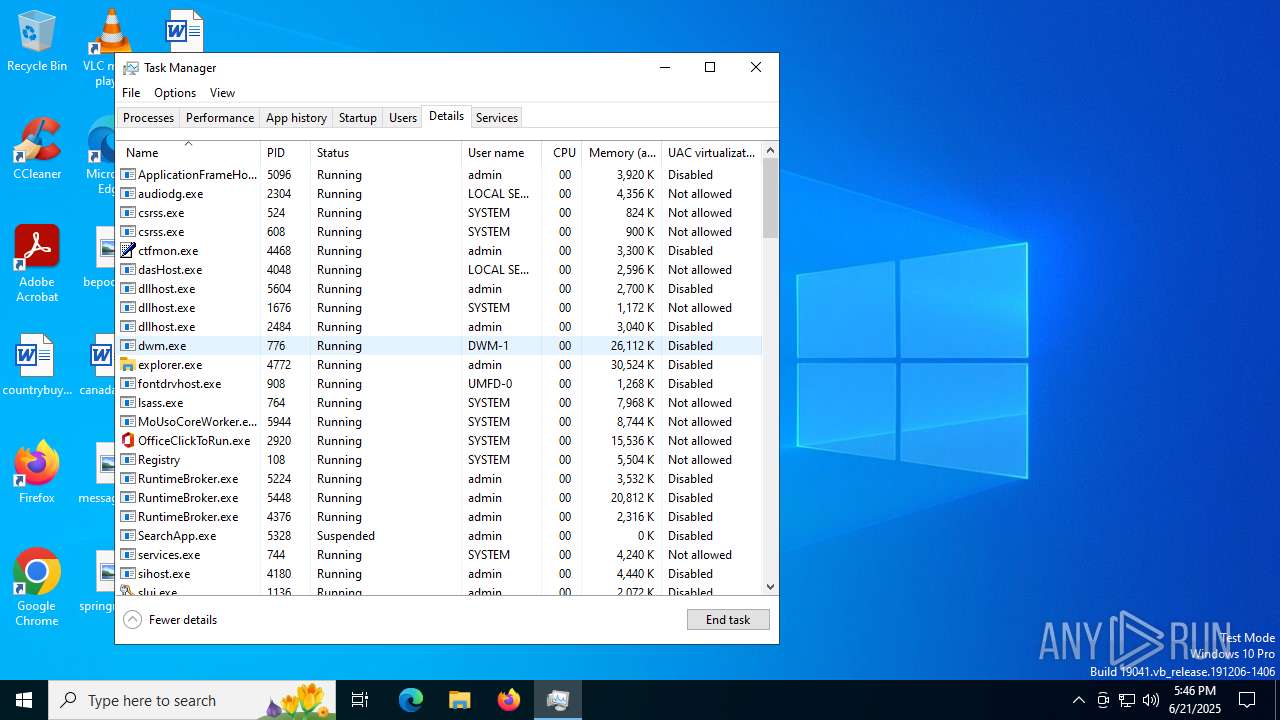
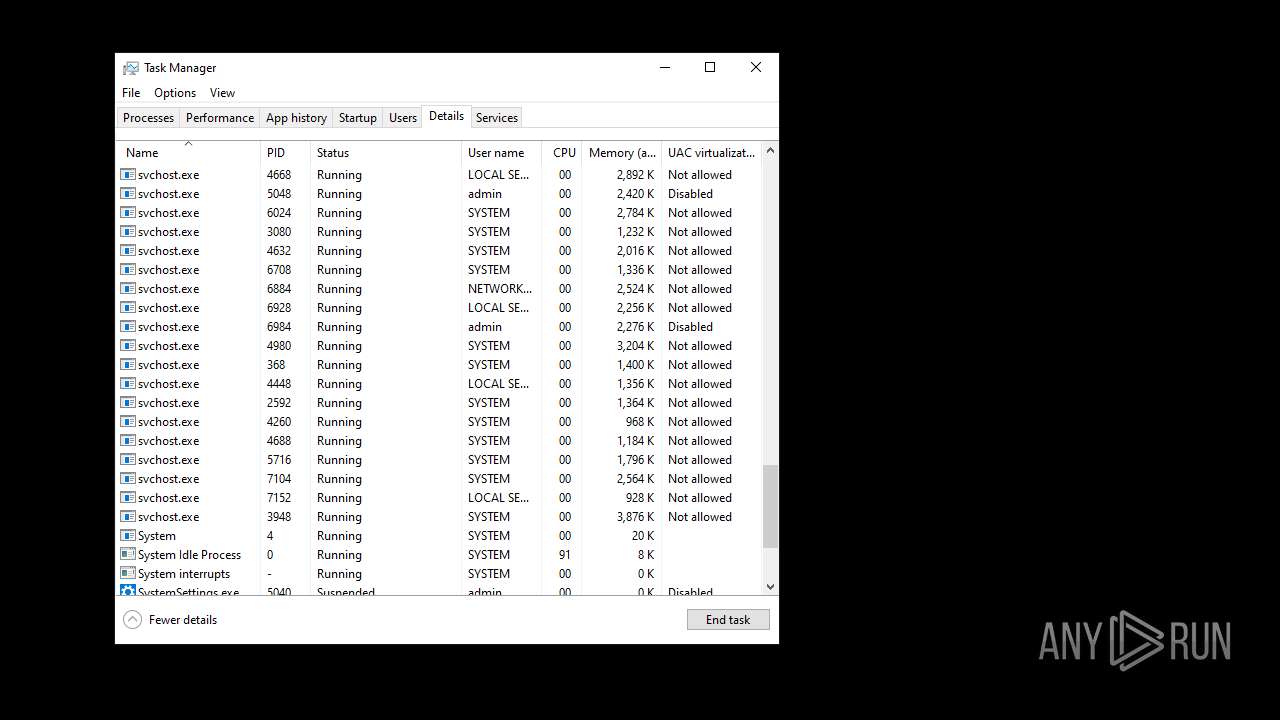
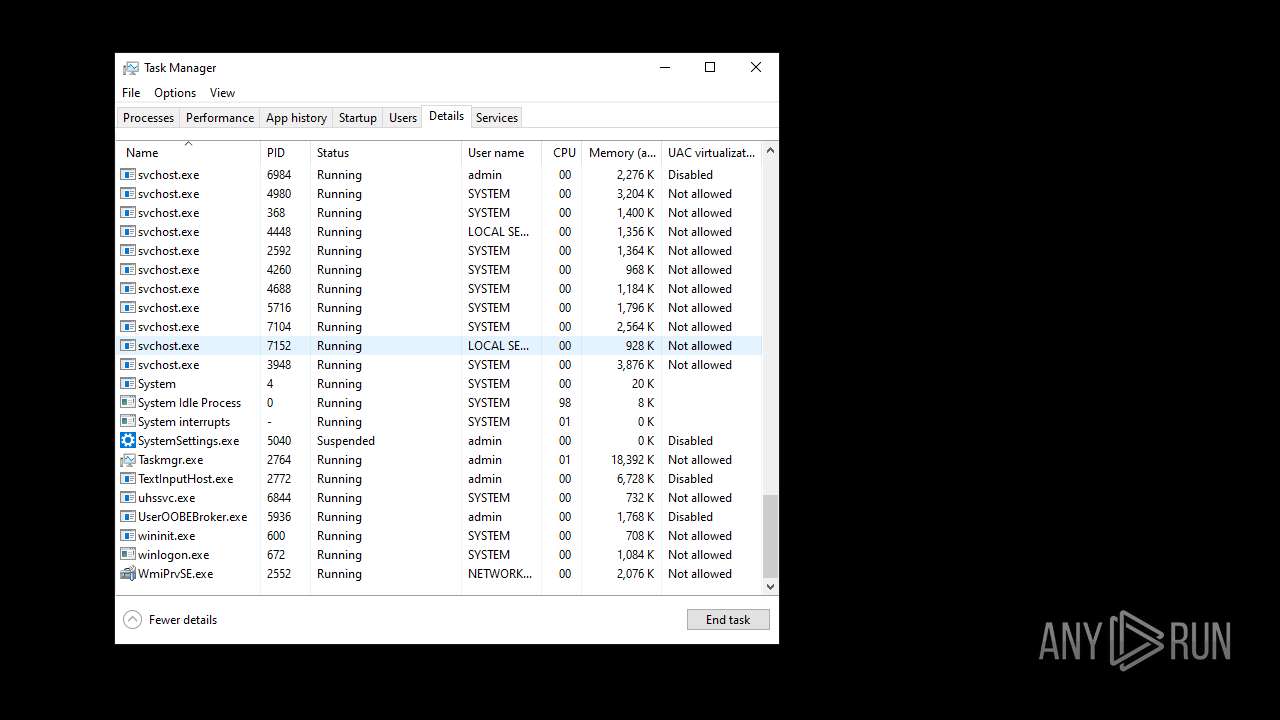
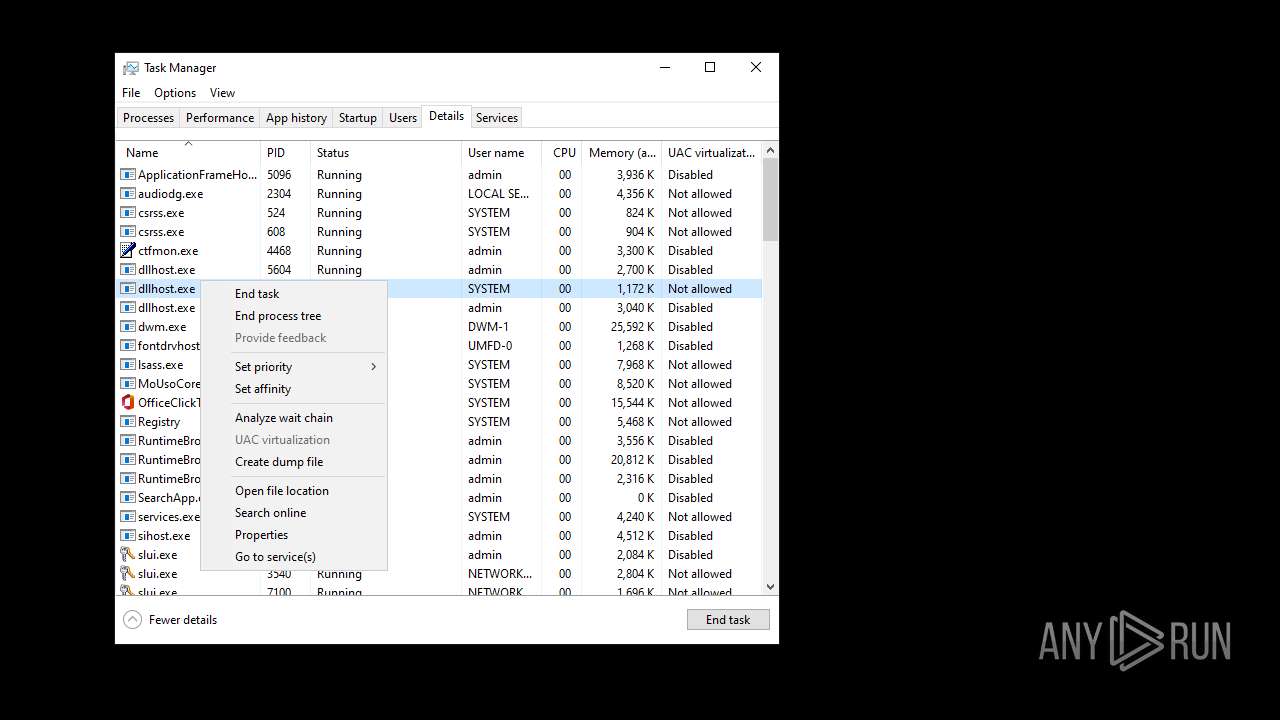
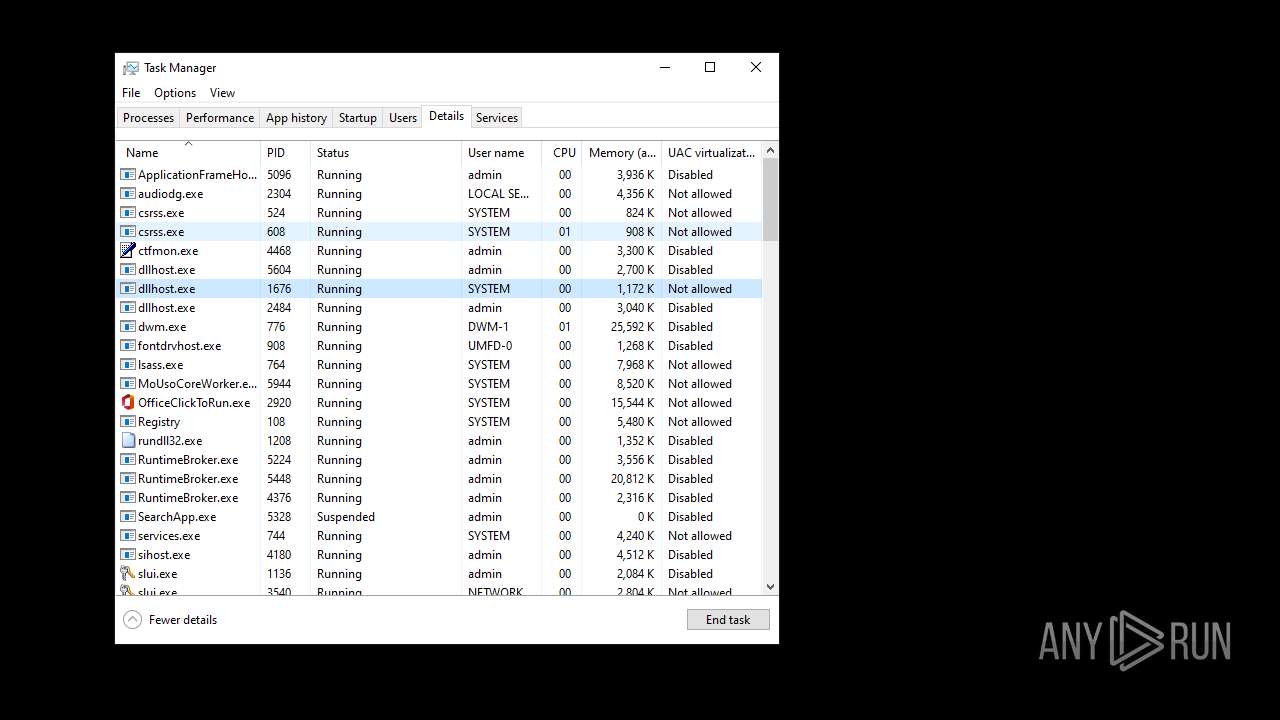
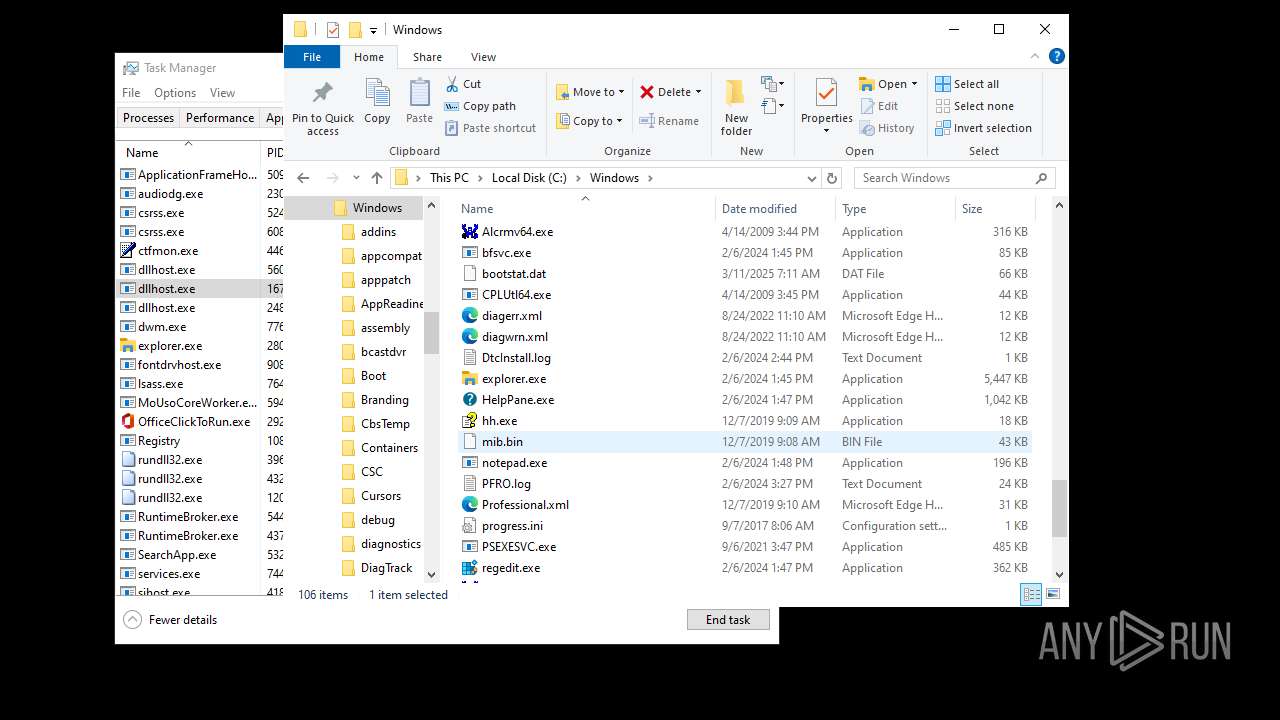
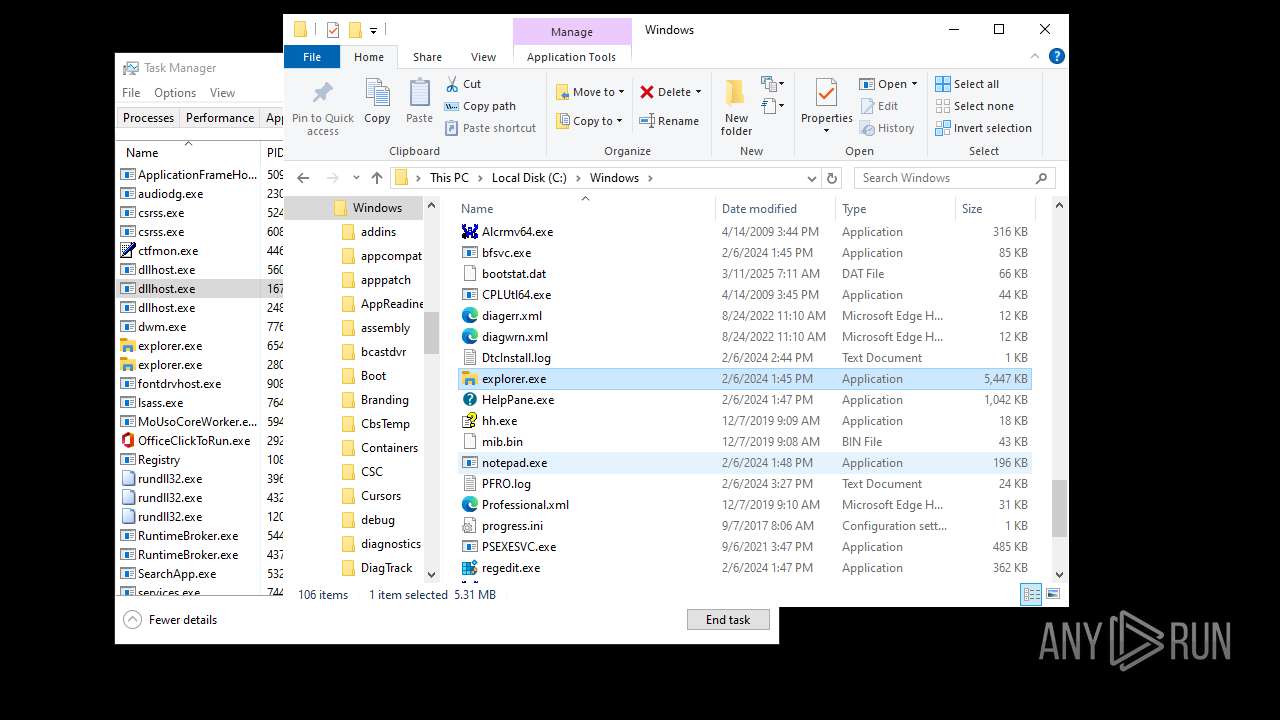
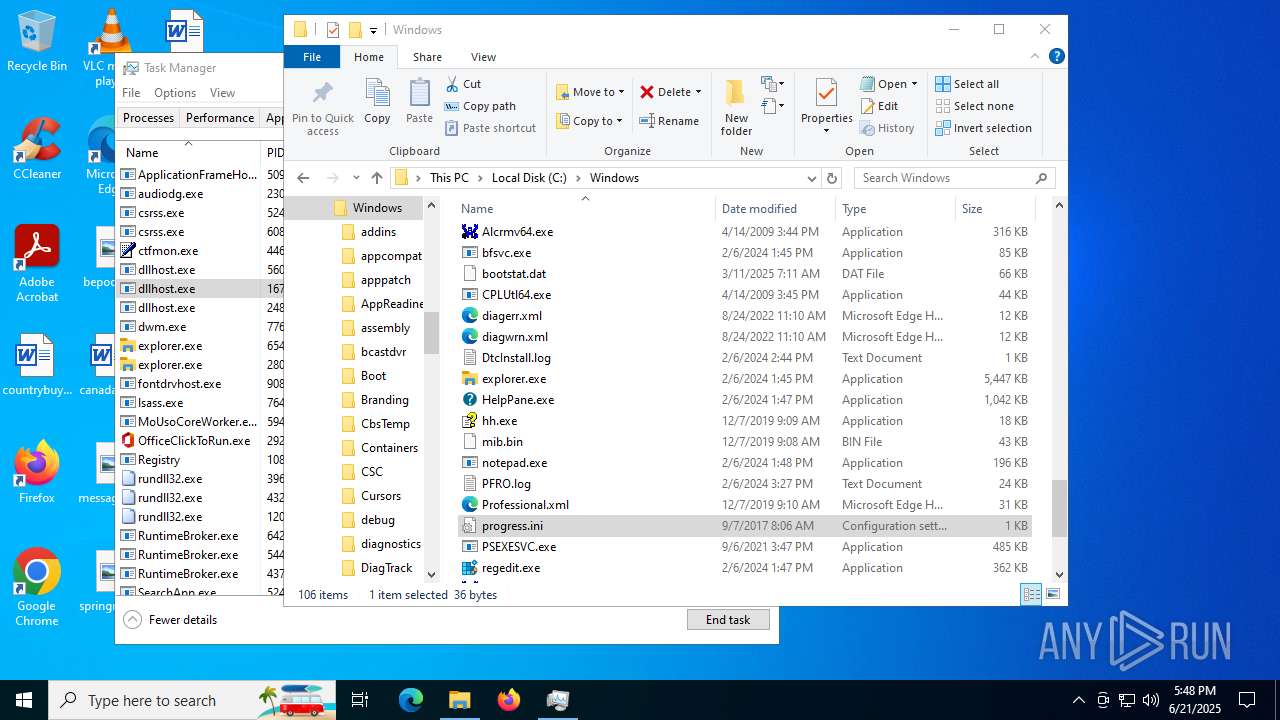
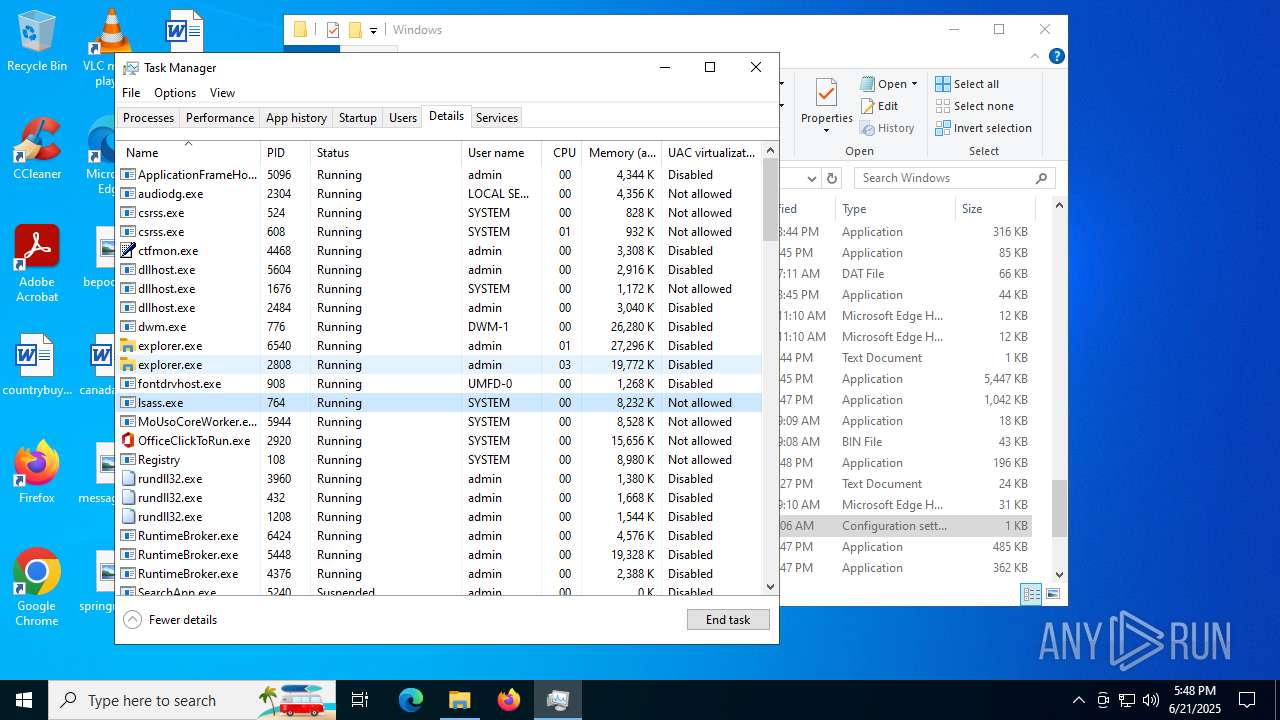
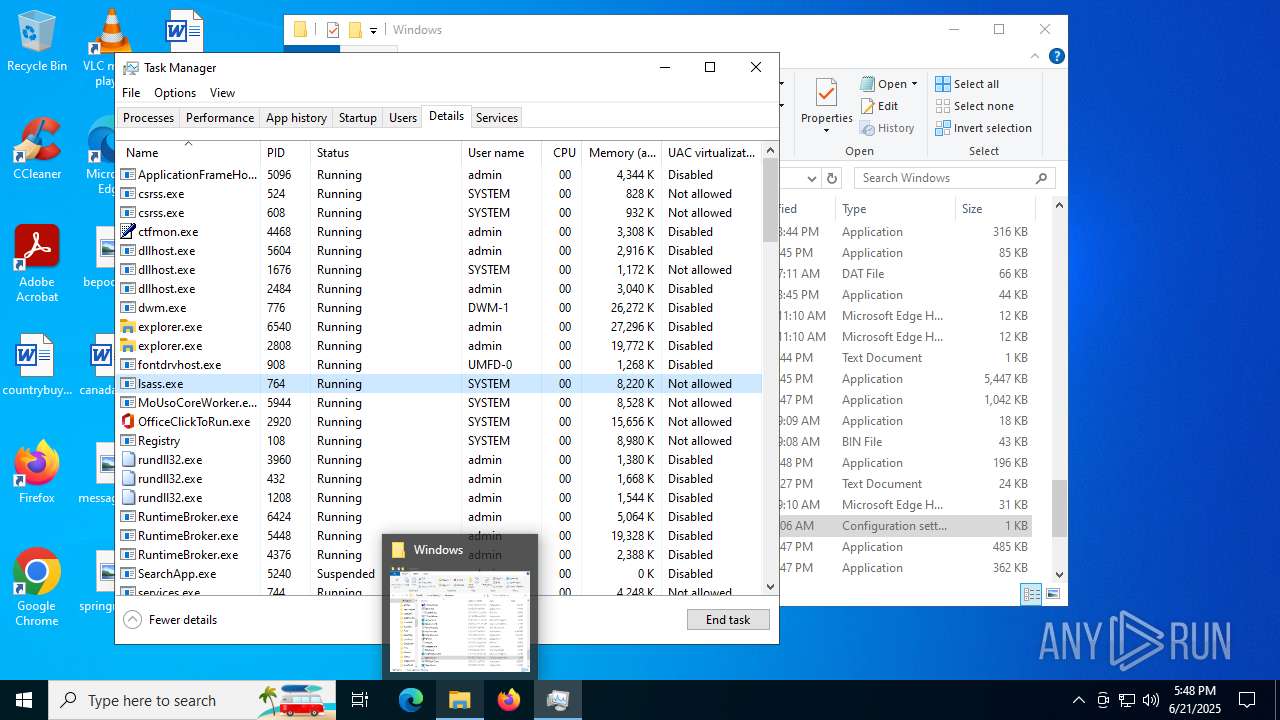
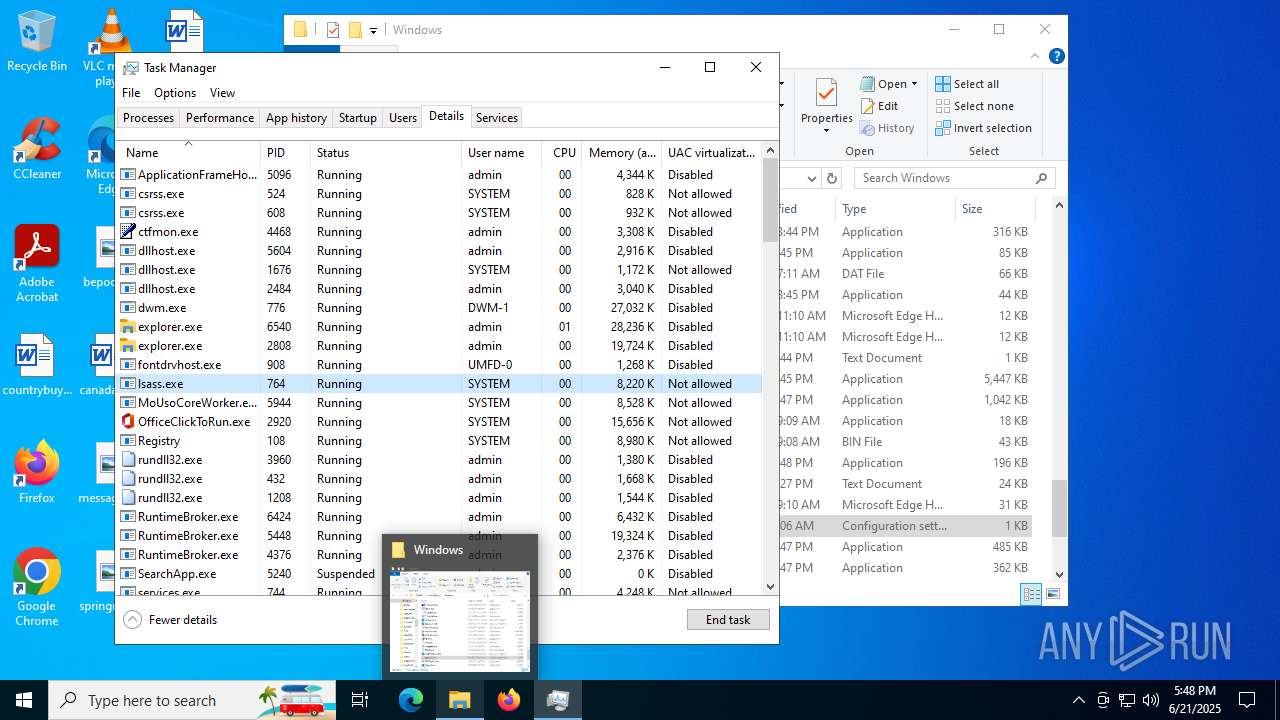
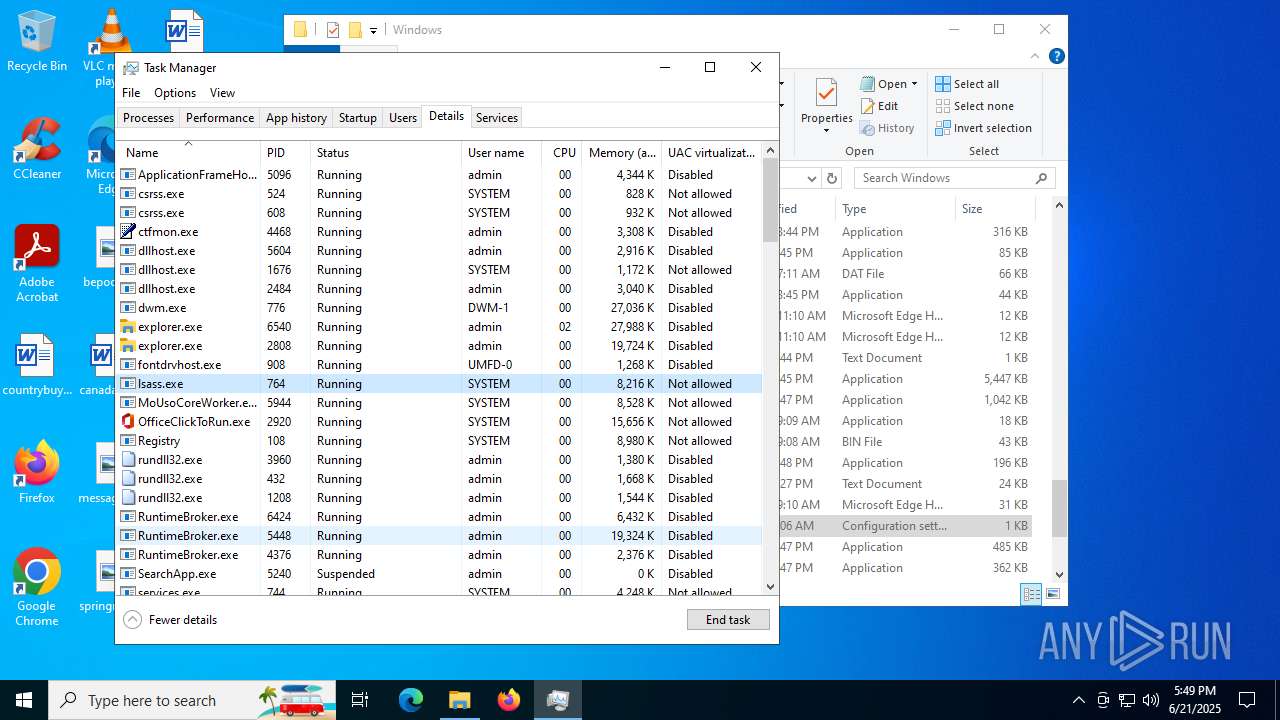
Manual execution by a user
- Taskmgr.exe (PID: 2976)
- Taskmgr.exe (PID: 2764)
Creates files in the program directory
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
Launching a file from a Registry key
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 5288)
- explorer.exe (PID: 4772)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- explorer.exe (PID: 2808)
- explorer.exe (PID: 6540)
- Taskmgr.exe (PID: 2764)
- RuntimeBroker.exe (PID: 5448)
Checks proxy server information
- explorer.exe (PID: 4772)
- SearchApp.exe (PID: 5240)
- explorer.exe (PID: 6540)
- slui.exe (PID: 1136)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 436)
- SearchApp.exe (PID: 5240)
Reads the software policy settings
- SearchApp.exe (PID: 5240)
- slui.exe (PID: 1136)
Reads Environment values
- SearchApp.exe (PID: 5240)
Creates files or folders in the user directory
- explorer.exe (PID: 6540)
- dllhost.exe (PID: 5604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33) |
| .exe | | | DOS Executable Generic (33) |
| .vxd | | | VXD Driver (0.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 17:45:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 23040 |
| InitializedDataSize: | 227840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2468 |
| OSVersion: | 5.2 |
| ImageVersion: | 1 |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
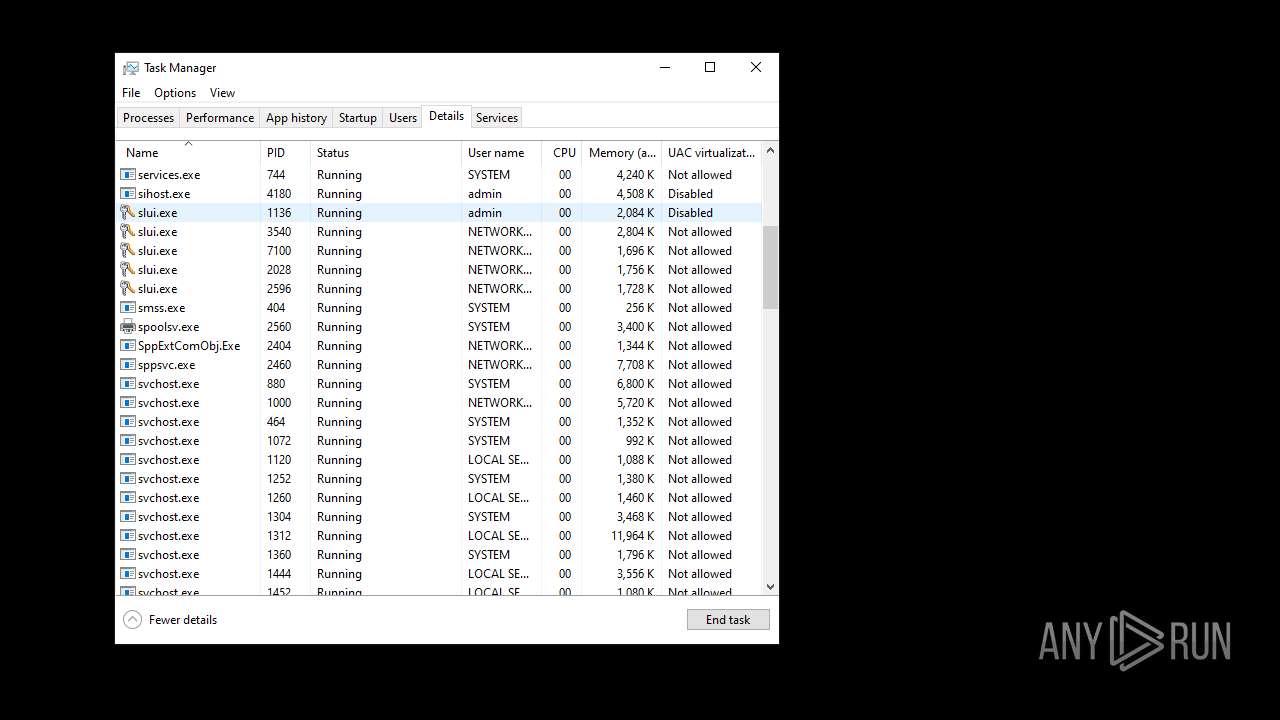
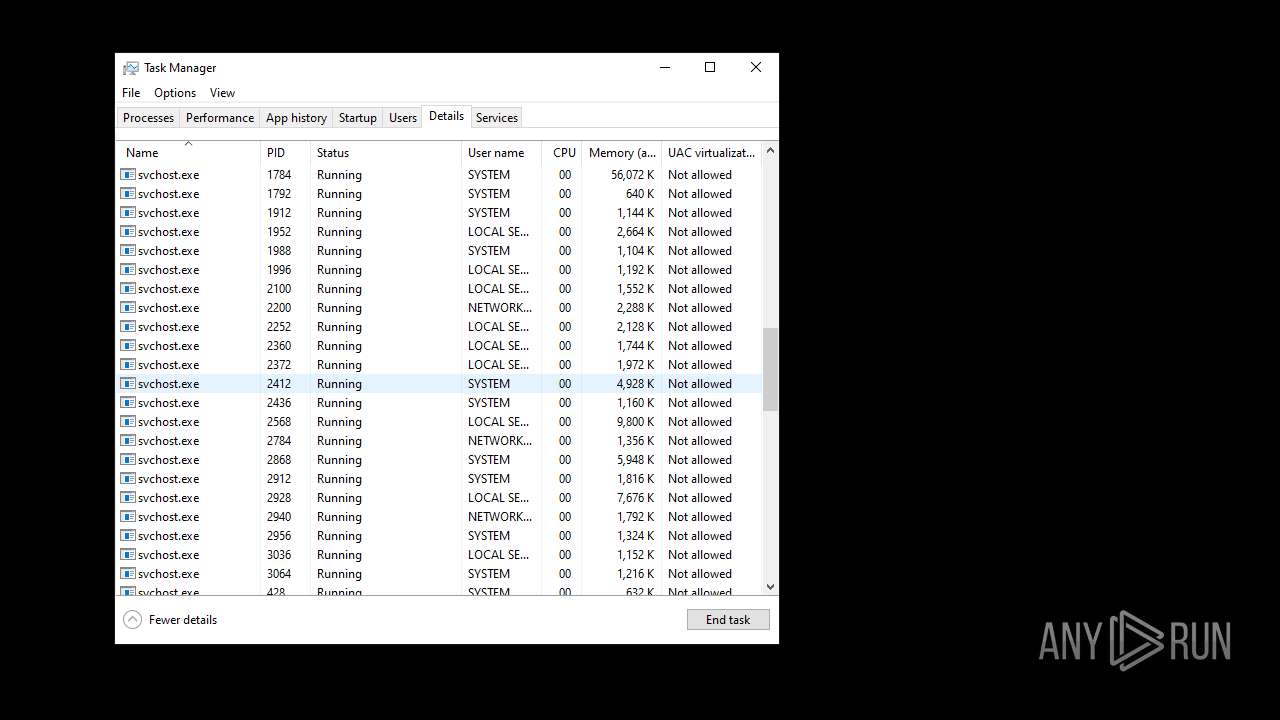
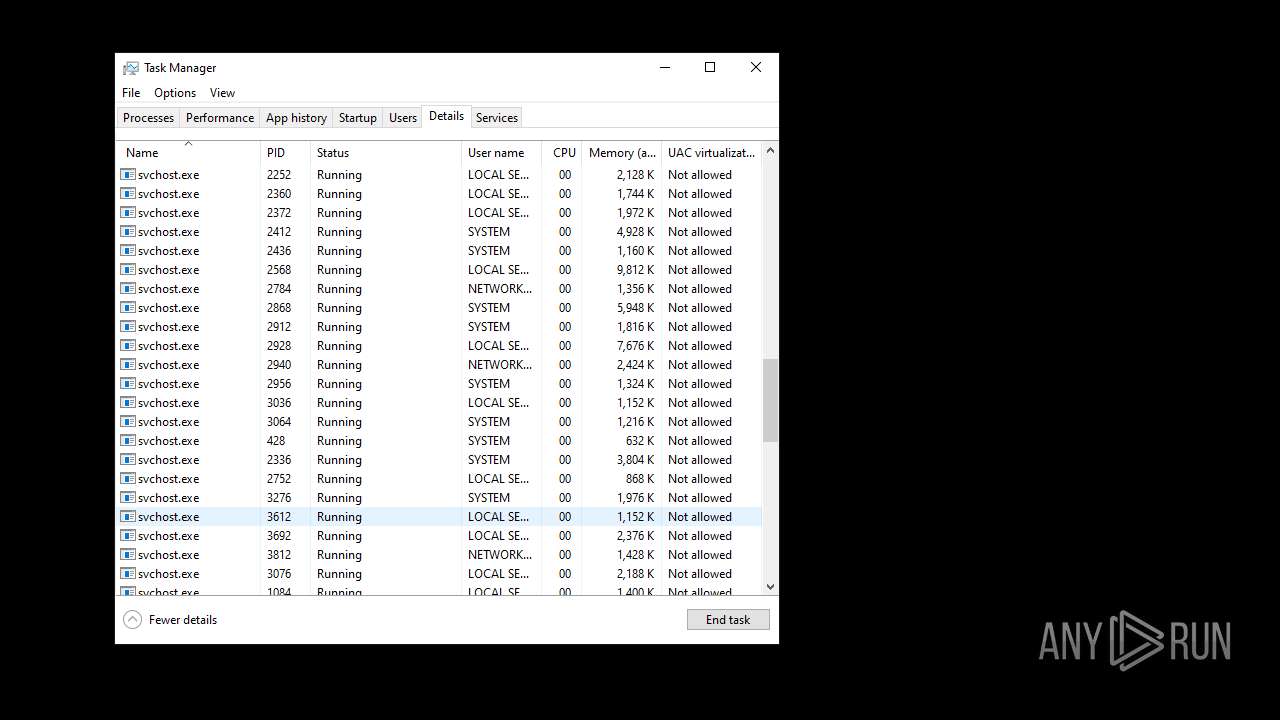
Total processes
158
Monitored processes
34
Malicious processes
3
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1136 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1208 | C:\WINDOWS\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {9BA05972-F6A8-11CF-A442-00A0C90A8F39} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2484 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2764 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2772 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Exit code: 1 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2808 | C:\WINDOWS\explorer.exe /factory,{682159d9-c321-47ca-b3f1-30e36b2ec8b9} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {3eef301f-b596-4c0b-bd92-013beafce793} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 933
Read events
50 576
Write events
332
Delete events
25
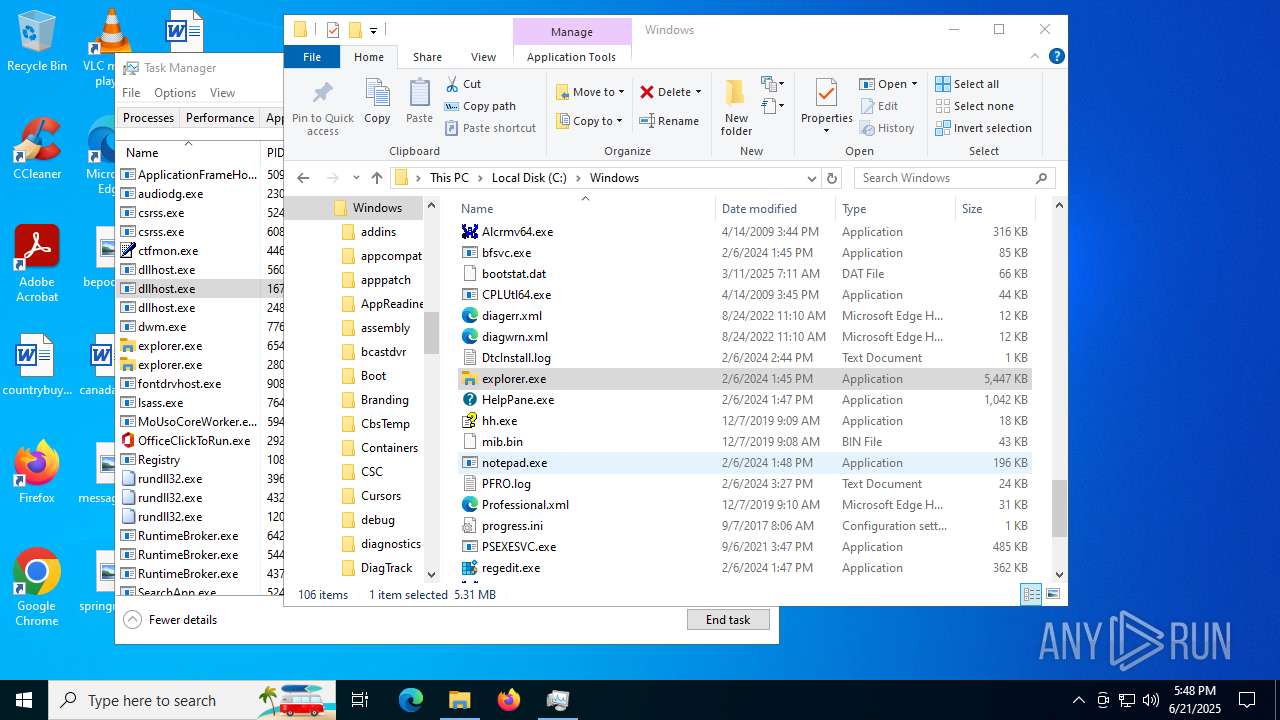
Modification events
| (PID) Process: | (5288) ba3272b0-a214-4930-9eda-55ded774e4eb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\bbeecafdaeec |
| Operation: | write | Name: | CurrentPath |
Value: C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe | |||
| (PID) Process: | (5288) ba3272b0-a214-4930-9eda-55ded774e4eb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\ProgramData\bbeecafdaeec.exe" | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisible |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisibleOnAnyMonitor |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe" | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\bbeecafdaeec |
| Operation: | write | Name: | CurrentPath |
Value: C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\StartupFolder |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\ProgramData\bbeecafdaeec.exe" | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
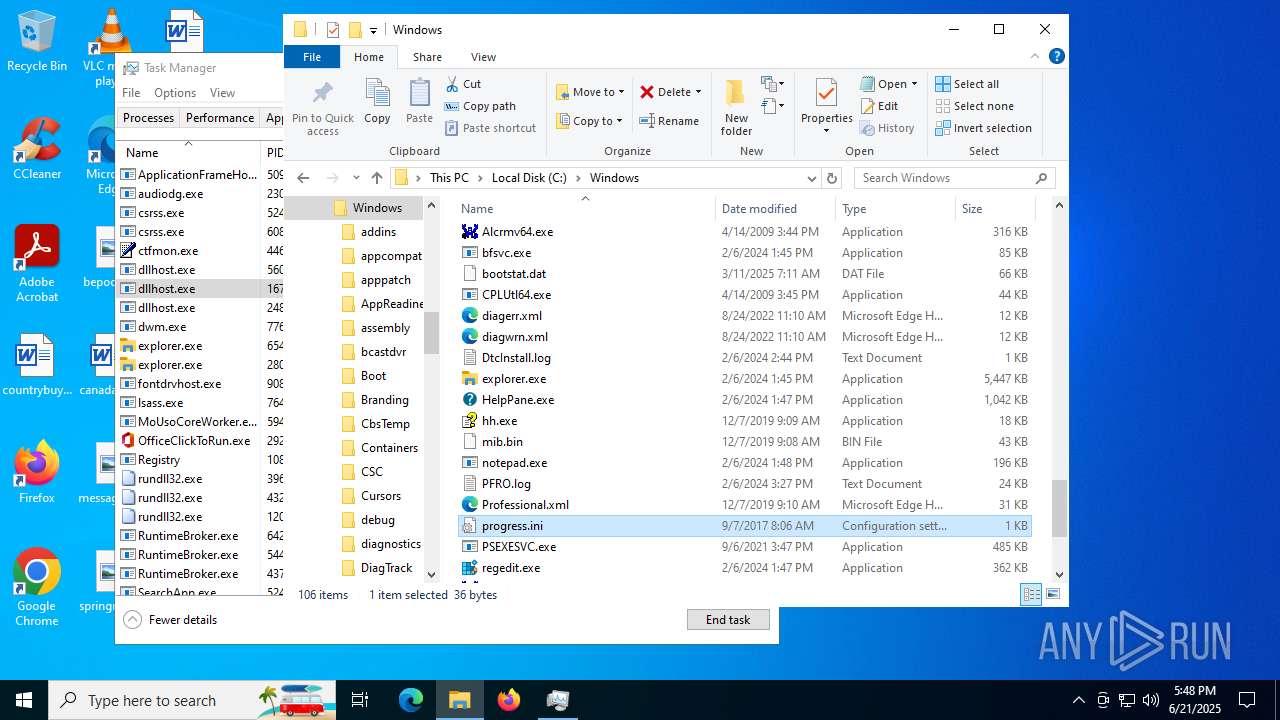
Executable files
3
Suspicious files
53
Text files
99
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5288 | ba3272b0-a214-4930-9eda-55ded774e4eb.exe | C:\ProgramData\bbeecafdaeec.exe | executable | |
MD5:7C9B7354279680E57E740BE0B8ABFF20 | SHA256:567D56920D6C11920923CA11AD80E35A974B3001091155F67299A7A231335A73 | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:DF367B9525354CC5543C9247210072ED | SHA256:68511E58CC309F2895652008EF4A7C0B18C023D5EDBC435BCE4E83F8BE640D09 | |||
| 2764 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 5900 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Background Tasks Profiles\93u99co2.MozillaBackgroundTask-308046B0AF4A39CB-defaultagent\datareporting\glean\db\data.safe.bin | binary | |
MD5:67C74ACA747B9719242F4392C44CBB8E | SHA256:F337D1806309645D9D86C75D2CCEE9008A5E396A106087D8E7EB972FD5918921 | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:BD27096743A2E1853FDF70C2FE416C15 | SHA256:CCB58026E504D32A325809D0C257011BE017D87EC82E2ABC93EB061B2FABBE7E | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:E5157DACFAFD3D3D5F3A36A8003D90DA | SHA256:56BAF825AE4E4160BC1D309CDCB4DC6028F291EC65F39720905408630964C470 | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\NajusmjIqB4kdLn9FmVxeS4xi2o[1].css | text | |
MD5:73D1CEBD8E3B6C7246F422D624EDF803 | SHA256:0674786CF9978A1F9065F57D98E986070C7CBB5177F154F40E8A924C0E0C13F2 | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\tUCiVcVWZ-go7BLlq95YW6bKHZE[1].css | text | |
MD5:445D78544E0CFC11EFC1E172DA3ECBBC | SHA256:76EFEBABB82AE8342985C99A498137C04B3E46BC59D78191F0DA44C660B980F5 | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\LJVpDXTkWDgGwVlLgxLZkLutWKw[1].css | text | |
MD5:B9727BBC2A77C4A60AADDCA163365575 | SHA256:8B23E288F4D6BF19C88B4F60AF45515C1D637D795430F150E4BC7C76FAD95CBD | |||
| 5240 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\-iNIzuEypRdgRJ6xnyVHizZ3bpM.br[1].js | binary | |
MD5:E86ABEFE45E62F7E2F865D8A344D0B6F | SHA256:5D54790C856CE13811590E18AC3B0ACEEFEFB61258852490F4C5C60748365E89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
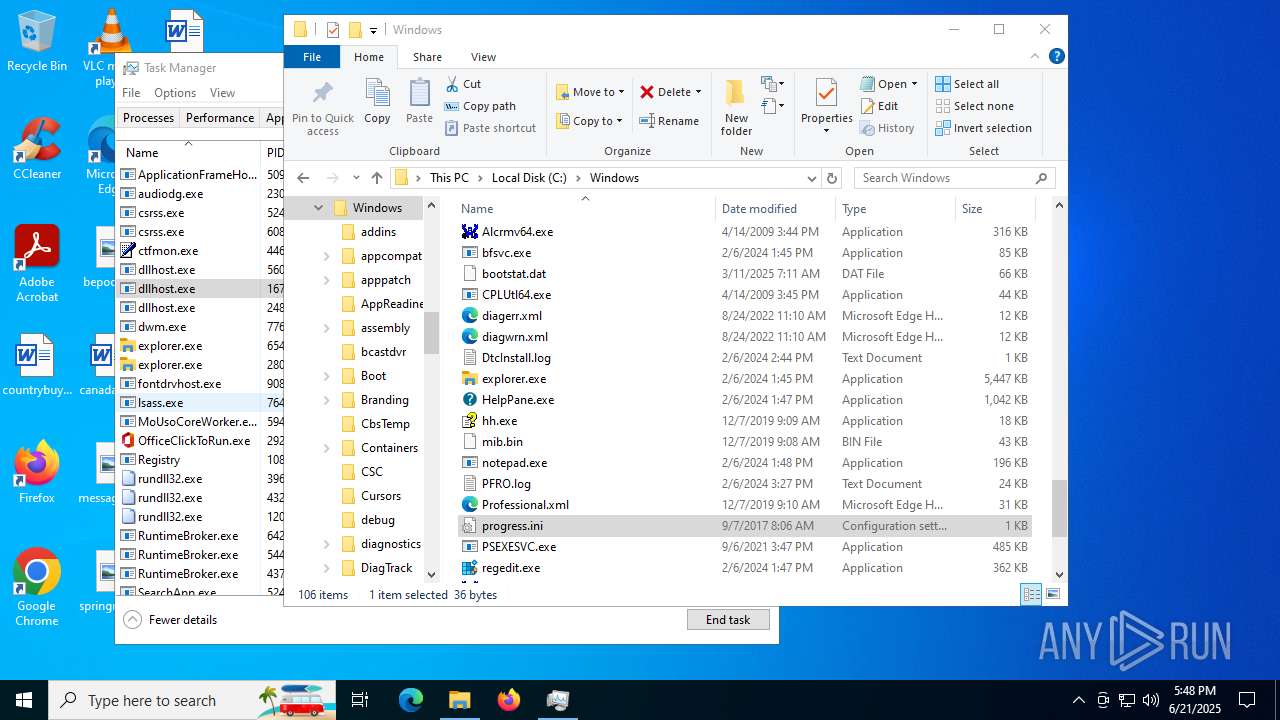
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4772 | explorer.exe | POST | 200 | 185.156.72.89:80 | http://185.156.72.89/nzcwzue/pqrfxn.php | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3932 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3932 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4772 | explorer.exe | POST | 200 | 185.156.72.89:80 | http://185.156.72.89/nzcwzue/pqrfxn.php | unknown | — | — | unknown |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5240 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1488 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4772 | explorer.exe | 185.156.72.89:80 | — | Tov Vaiz Partner | RU | unknown |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3948 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3948 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4772 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix POST Request M3 |